67b5a220b4fcfaa554566c6b6b994380.ppt
- Количество слайдов: 39
Sécurité des Réseaux, Master CSI 2 J. Bétréma, La. BRI, Université Bordeaux 1 IKE : Internet Key Exchange • RFC 2409 (novembre 1998) • ISAKMP (Internet Security Association and Key Management Protocol, RFC 2408) • Do. I (IPSec Domain of Interpretation for ISAKMP, RFC 2407)
Architecture There are two ways to design a system: • One is to make it so simple there are obviously no deficiencies. • The other is to make it so complex there are no obvious deficiencies. C. A. R. Hoare Miraculously, people were able to implement IKE, and even interoperate… Kaufman, Perlman, Speciner Network Security
RFC 2409, section 4. Introduction IKE : phases • Phase 1 is where the two ISAKMP peers establish a secure, authenticated channel with which to communicate. This is called the ISAKMP Security Association (SA). • Phase 2 is where Security Associations are negotiated on behalf of services such as IPsec or any other service which needs key material and/or parameter negotiation. • With the use of ISAKMP phases, an implementation can accomplish very fast keying when necessary. A single phase 1 negotiation may be used for more than one phase 2 negotiation. Additionally a single phase 2 negotiation can request multiple Security Associations. With these optimizations, an implementation can see less than one round trip per SA as well as less than one DH exponentiation per SA.
IKE : modes • La phase 1 peut se dérouler en « mode principal » (main mode, 6 messages) ou en « mode agressif » (aggressive mode, 3 messages). • La phase 2 se déroule en « mode rapide » (quick mode).
RFC 2409, section 5. Exchanges Phase 1, main mode Main Mode is an instantiation of the ISAKMP Identity Protect Exchange: • The first two messages negotiate policy; • the next two exchange Diffie-Hellman public values and ancillary data (e. g. nonces) necessary for the exchange; • and the last two messages authenticate the Diffie-Hellman Exchange. The authentication method negotiated as part of the initial ISAKMP exchange influences the composition of the payloads but not their purpose. The XCHG for Main Mode is ISAKMP Identity Protect.
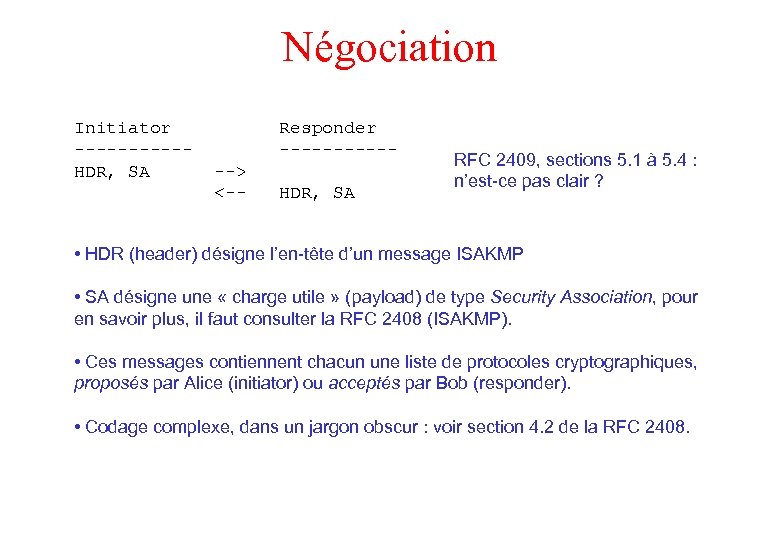
Négociation Initiator -----HDR, SA Responder ------> <-- HDR, SA RFC 2409, sections 5. 1 à 5. 4 : n’est-ce pas clair ? • HDR (header) désigne l’en-tête d’un message ISAKMP • SA désigne une « charge utile » (payload) de type Security Association, pour en savoir plus, il faut consulter la RFC 2408 (ISAKMP). • Ces messages contiennent chacun une liste de protocoles cryptographiques, proposés par Alice (initiator) ou acceptés par Bob (responder). • Codage complexe, dans un jargon obscur : voir section 4. 2 de la RFC 2408.
RFC 2409, section 4. Introduction Négociation (2) The following attributes are used by IKE and are negotiated as part of the ISAKMP Security Association. • encryption algorithm • hash algorithm • authentication method • information about a group over which to do Diffie-Hellman. All of these attributes are mandatory and MUST be negotiated.
RFC 2409, section 4. Introduction Négociation (3) IKE implementations MUST support the following attribute values: • DES in CBC mode with a weak, and semi-weak, key check (weak and semi-weak keys are listed in Appendix A). The key is derived according to Appendix B. • MD 5 and SHA. • Authentication via pre-shared keys. • MODP over default group number one.
RFC 2409, section 4. Introduction Négociation (4) In addition, IKE implementations SHOULD support: • 3 DES for encryption; • Tiger for hash; • the Digital Signature Standard, RSA signatures and authentication with RSA public key encryption; • and MODP group number 2. IKE implementations MAY support any additional encryption algorithms defined in Appendix A and MAY support ECP and EC 2 N groups.
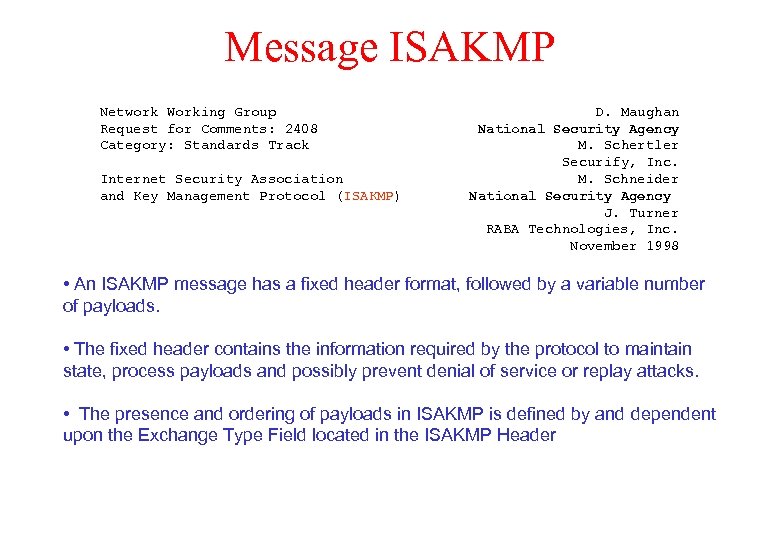
Message ISAKMP Network Working Group Request for Comments: 2408 Category: Standards Track Internet Security Association and Key Management Protocol (ISAKMP) D. Maughan National Security Agency M. Schertler Securify, Inc. M. Schneider National Security Agency J. Turner RABA Technologies, Inc. November 1998 • An ISAKMP message has a fixed header format, followed by a variable number of payloads. • The fixed header contains the information required by the protocol to maintain state, process payloads and possibly prevent denial of service or replay attacks. • The presence and ordering of payloads in ISAKMP is defined by and dependent upon the Exchange Type Field located in the ISAKMP Header
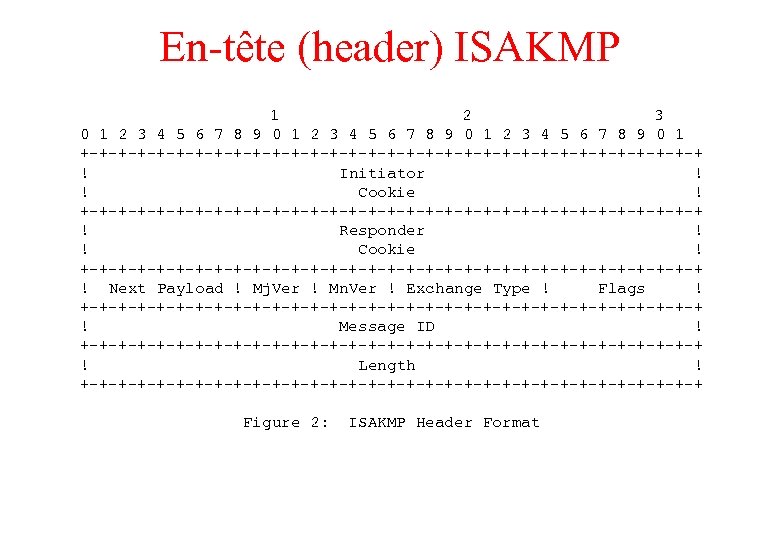
En-tête (header) ISAKMP 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ ! Initiator ! ! Cookie ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ ! Responder ! ! Cookie ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ ! Next Payload ! Mj. Ver ! Mn. Ver ! Exchange Type ! Flags ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ ! Message ID ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ ! Length ! +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ Figure 2: ISAKMP Header Format
Cookies • Anti-Clogging Token (to clog = obstruer, encrasser) : pour gêner les attaques Do. S (déni de service). • La requête initiale peut être falsifiée (IP spoofing), le serveur ne doit pas consommer de ressource (mémoire, temps de calcul) avant réception du message suivant de la part du client (supposé), codé selon les règles ISAKMP. • Pour que le serveur ne consomme aucune ressource prématurément, il doit pouvoir vérifier le « responder cookie » en mode « stateless » : Karn's suggested method for creating the cookie is to perform a fast hash (e. g. MD 5) over the IP Source and Destination Address, the UDP Source and Destination Ports and a locally generated secret random value. • Impossible ici, car il faut mémoriser les termes de la négociation, inclus dans les deux premiers messages…
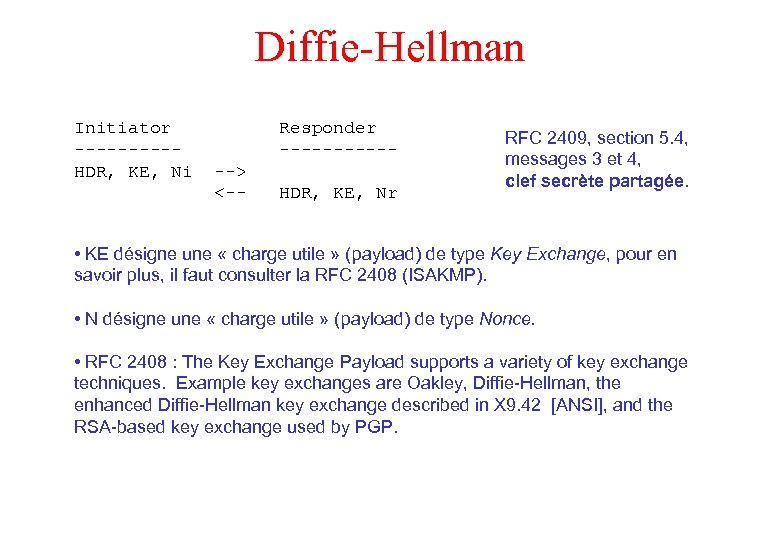
Diffie-Hellman Initiator -----HDR, KE, Ni Responder ------> <-- HDR, KE, Nr RFC 2409, section 5. 4, messages 3 et 4, clef secrète partagée. • KE désigne une « charge utile » (payload) de type Key Exchange, pour en savoir plus, il faut consulter la RFC 2408 (ISAKMP). • N désigne une « charge utile » (payload) de type Nonce. • RFC 2408 : The Key Exchange Payload supports a variety of key exchange techniques. Example key exchanges are Oakley, Diffie-Hellman, the enhanced Diffie-Hellman key exchange described in X 9. 42 [ANSI], and the RSA-based key exchange used by PGP.
RFC 2409, section 6. Oakley groups Diffie-Hellman (2) With IKE, the group in which to do the Diffie-Hellman exchange is negotiated. Four groups -- values 1 through 4 -- are defined below. These groups originated with the Oakley protocol and are therefore called "Oakley Groups". These groups were all generated by Richard Schroeppel at the University of Arizona.
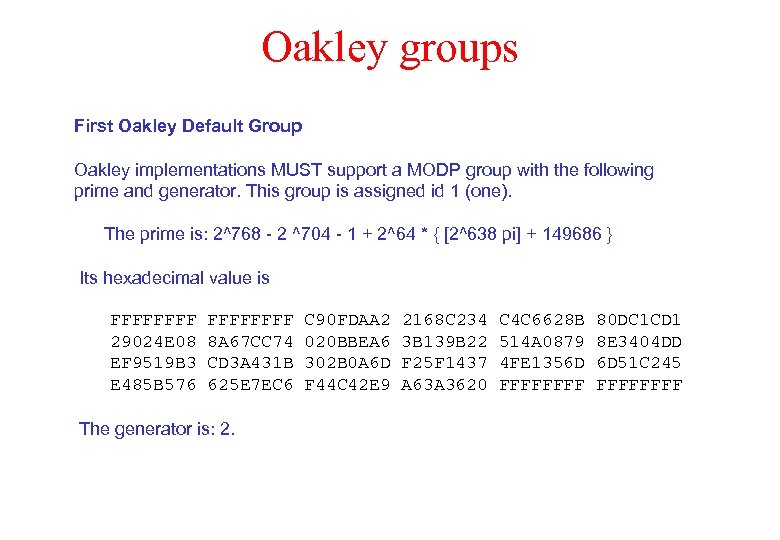
Oakley groups First Oakley Default Group Oakley implementations MUST support a MODP group with the following prime and generator. This group is assigned id 1 (one). The prime is: 2^768 - 2 ^704 - 1 + 2^64 * { [2^638 pi] + 149686 } Its hexadecimal value is FFFF 29024 E 08 EF 9519 B 3 E 485 B 576 FFFF 8 A 67 CC 74 CD 3 A 431 B 625 E 7 EC 6 The generator is: 2. C 90 FDAA 2 020 BBEA 6 302 B 0 A 6 D F 44 C 42 E 9 2168 C 234 3 B 139 B 22 F 25 F 1437 A 63 A 3620 C 4 C 6628 B 514 A 0879 4 FE 1356 D FFFF 80 DC 1 CD 1 8 E 3404 DD 6 D 51 C 245 FFFF
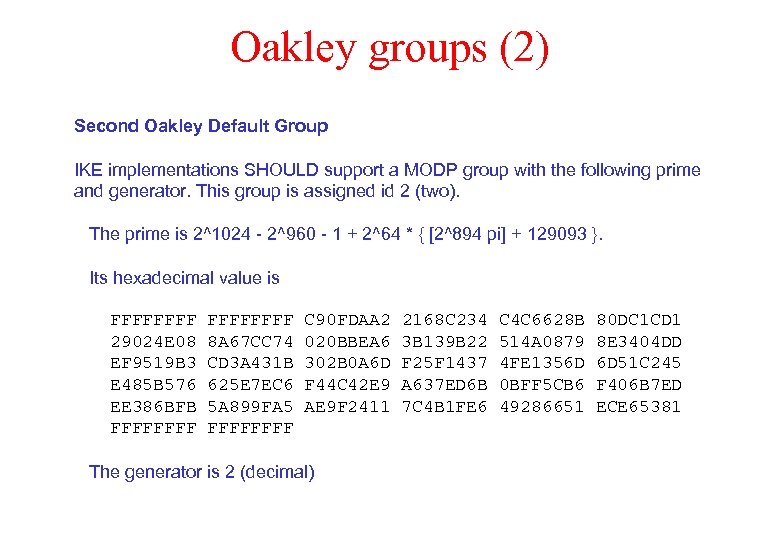
Oakley groups (2) Second Oakley Default Group IKE implementations SHOULD support a MODP group with the following prime and generator. This group is assigned id 2 (two). The prime is 2^1024 - 2^960 - 1 + 2^64 * { [2^894 pi] + 129093 }. Its hexadecimal value is FFFF 29024 E 08 EF 9519 B 3 E 485 B 576 EE 386 BFB FFFFFFFF 8 A 67 CC 74 CD 3 A 431 B 625 E 7 EC 6 5 A 899 FA 5 FFFF C 90 FDAA 2 020 BBEA 6 302 B 0 A 6 D F 44 C 42 E 9 AE 9 F 2411 The generator is 2 (decimal) 2168 C 234 3 B 139 B 22 F 25 F 1437 A 637 ED 6 B 7 C 4 B 1 FE 6 C 4 C 6628 B 514 A 0879 4 FE 1356 D 0 BFF 5 CB 6 49286651 80 DC 1 CD 1 8 E 3404 DD 6 D 51 C 245 F 406 B 7 ED ECE 65381
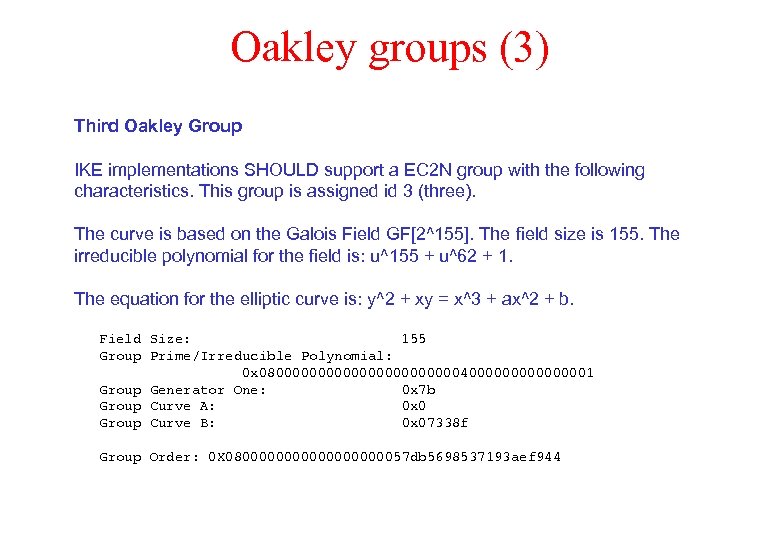
Oakley groups (3) Third Oakley Group IKE implementations SHOULD support a EC 2 N group with the following characteristics. This group is assigned id 3 (three). The curve is based on the Galois Field GF[2^155]. The field size is 155. The irreducible polynomial for the field is: u^155 + u^62 + 1. The equation for the elliptic curve is: y^2 + xy = x^3 + ax^2 + b. Field Size: 155 Group Prime/Irreducible Polynomial: 0 x 0800000000000400000001 Group Generator One: 0 x 7 b Group Curve A: 0 x 0 Group Curve B: 0 x 07338 f Group Order: 0 X 0800000000057 db 5698537193 aef 944
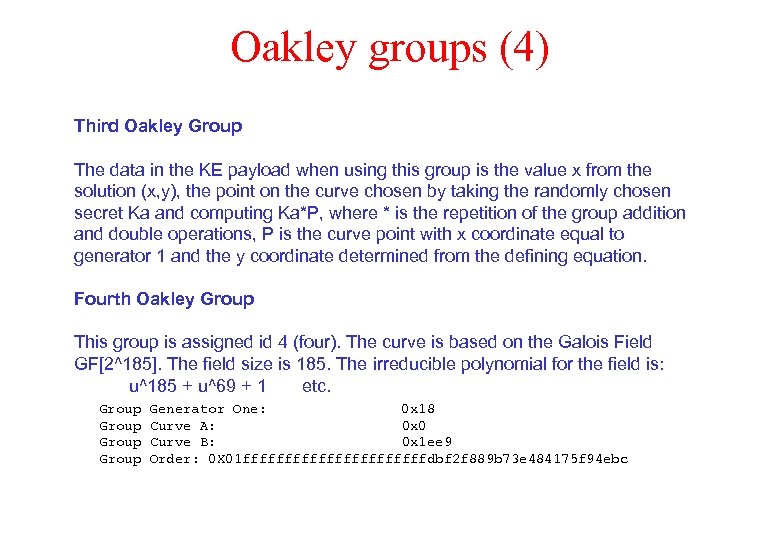
Oakley groups (4) Third Oakley Group The data in the KE payload when using this group is the value x from the solution (x, y), the point on the curve chosen by taking the randomly chosen secret Ka and computing Ka*P, where * is the repetition of the group addition and double operations, P is the curve point with x coordinate equal to generator 1 and the y coordinate determined from the defining equation. Fourth Oakley Group This group is assigned id 4 (four). The curve is based on the Galois Field GF[2^185]. The field size is 185. The irreducible polynomial for the field is: u^185 + u^69 + 1 etc. Group Generator One: 0 x 18 Group Curve A: 0 x 0 Group Curve B: 0 x 1 ee 9 Group Order: 0 X 01 fffffffffffdbf 2 f 889 b 73 e 484175 f 94 ebc
Nonces Nonce Payload (RFC 2408) The Nonce Payload contains random data used to guarantee liveness (sic) during an exchange and protect against replay attacks. The nonces may be transmitted as part of the key exchange data, or as a separate payload. However, this is defined by the key exchange, not by ISAKMP.
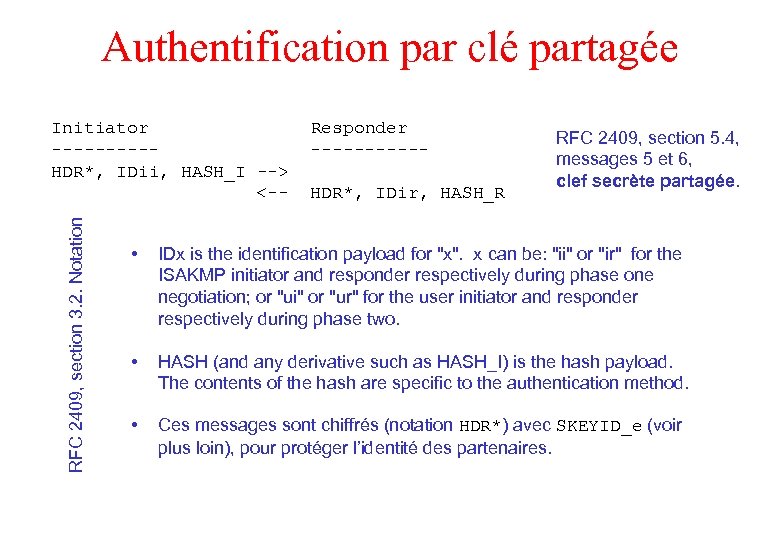
Authentification par clé partagée RFC 2409, section 3. 2. Notation Initiator -----HDR*, IDii, HASH_I --> <-- Responder -----HDR*, IDir, HASH_R RFC 2409, section 5. 4, messages 5 et 6, clef secrète partagée. • IDx is the identification payload for "x". x can be: "ii" or "ir" for the ISAKMP initiator and responder respectively during phase one negotiation; or "ui" or "ur" for the user initiator and responder respectively during phase two. • HASH (and any derivative such as HASH_I) is the hash payload. The contents of the hash are specific to the authentication method. • Ces messages sont chiffrés (notation HDR*) avec SKEYID_e (voir plus loin), pour protéger l’identité des partenaires.
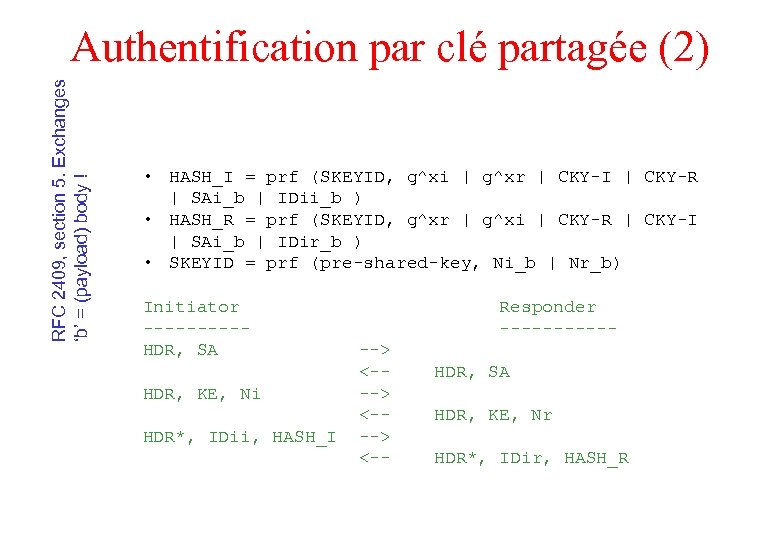
RFC 2409, section 5. Exchanges ‘b’ = (payload) body ! Authentification par clé partagée (2) • HASH_I = prf (SKEYID, g^xi | g^xr | CKY-I | CKY-R | SAi_b | IDii_b ) • HASH_R = prf (SKEYID, g^xr | g^xi | CKY-R | CKY-I | SAi_b | IDir_b ) • SKEYID = prf (pre-shared-key, Ni_b | Nr_b) Initiator -----HDR, SA HDR, KE, Ni HDR*, IDii, HASH_I Responder ------> <---> <-- HDR, SA HDR, KE, Nr HDR*, IDir, HASH_R
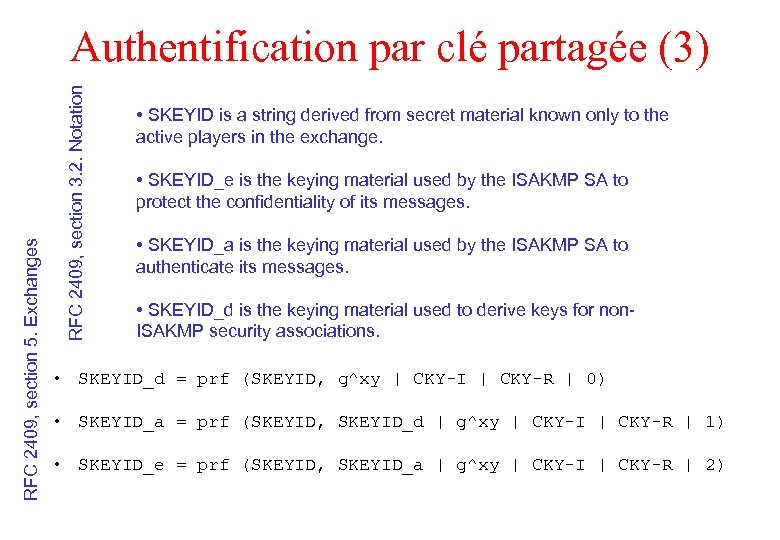
RFC 2409, section 3. 2. Notation RFC 2409, section 5. Exchanges Authentification par clé partagée (3) • SKEYID is a string derived from secret material known only to the active players in the exchange. • SKEYID_e is the keying material used by the ISAKMP SA to protect the confidentiality of its messages. • SKEYID_a is the keying material used by the ISAKMP SA to authenticate its messages. • SKEYID_d is the keying material used to derive keys for non. ISAKMP security associations. • SKEYID_d = prf (SKEYID, g^xy | CKY-I | CKY-R | 0) • SKEYID_a = prf (SKEYID, SKEYID_d | g^xy | CKY-I | CKY-R | 1) • SKEYID_e = prf (SKEYID, SKEYID_a | g^xy | CKY-I | CKY-R | 2)
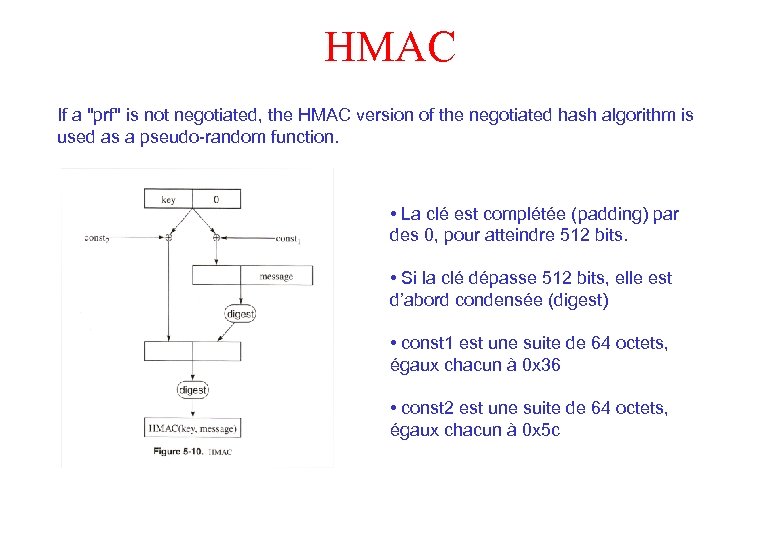
HMAC If a "prf" is not negotiated, the HMAC version of the negotiated hash algorithm is used as a pseudo-random function. • La clé est complétée (padding) par des 0, pour atteindre 512 bits. • Si la clé dépasse 512 bits, elle est d’abord condensée (digest) • const 1 est une suite de 64 octets, égaux chacun à 0 x 36 • const 2 est une suite de 64 octets, égaux chacun à 0 x 5 c
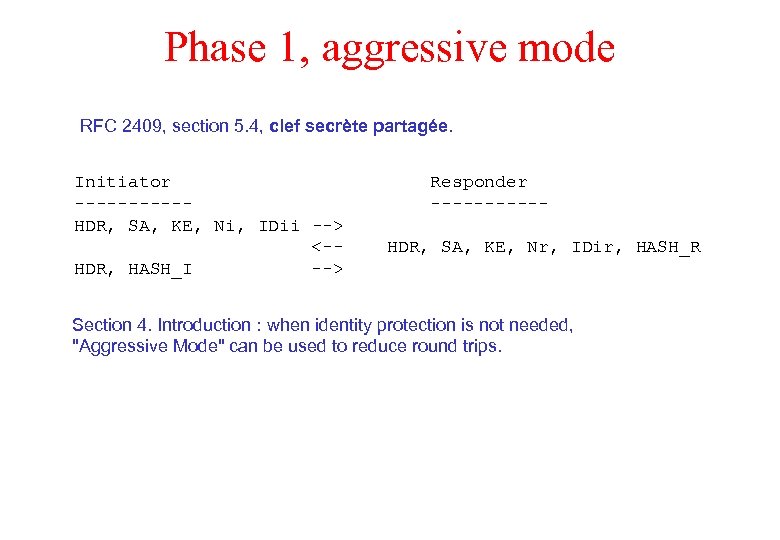
Phase 1, aggressive mode RFC 2409, section 5. 4, clef secrète partagée. Initiator -----HDR, SA, KE, Ni, IDii --> <-HDR, HASH_I --> Responder -----HDR, SA, KE, Nr, IDir, HASH_R Section 4. Introduction : when identity protection is not needed, "Aggressive Mode" can be used to reduce round trips.
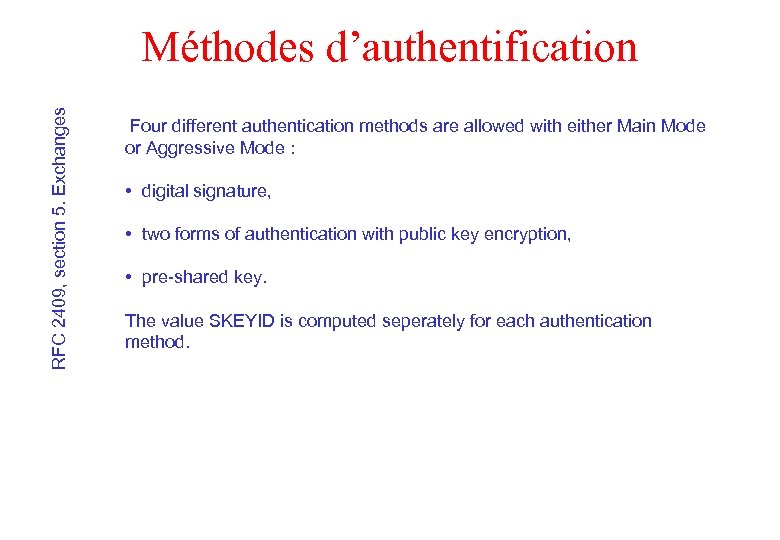
RFC 2409, section 5. Exchanges Méthodes d’authentification Four different authentication methods are allowed with either Main Mode or Aggressive Mode : • digital signature, • two forms of authentication with public key encryption, • pre-shared key. The value SKEYID is computed seperately for each authentication method.
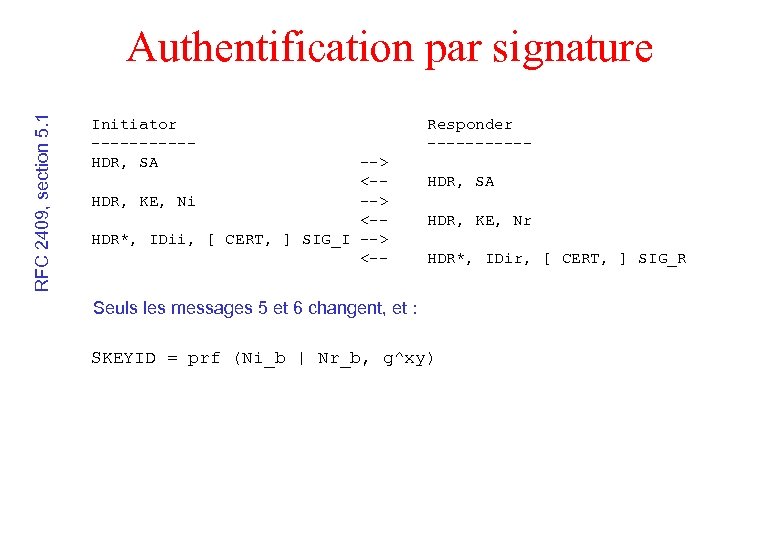
RFC 2409, section 5. 1 Authentification par signature Initiator -----HDR, SA --> <-HDR, KE, Ni --> <-HDR*, IDii, [ CERT, ] SIG_I --> <-- Responder -----HDR, SA HDR, KE, Nr HDR*, IDir, [ CERT, ] SIG_R Seuls les messages 5 et 6 changent, et : SKEYID = prf (Ni_b | Nr_b, g^xy)
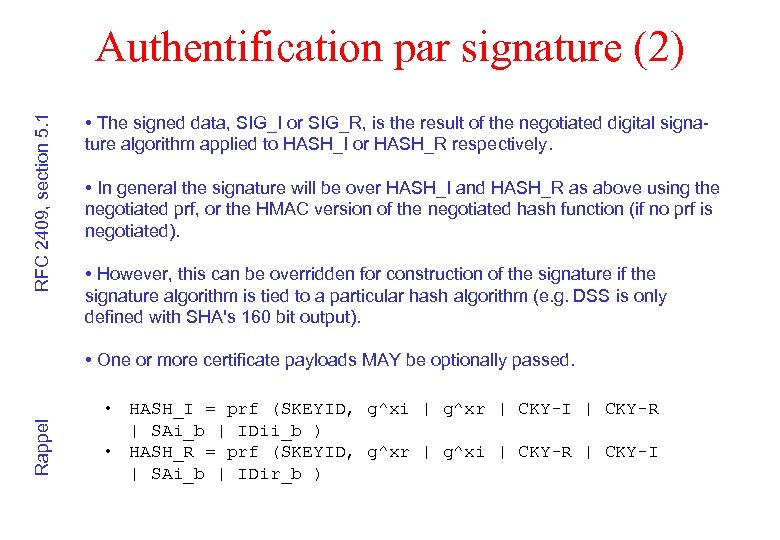
RFC 2409, section 5. 1 Authentification par signature (2) • The signed data, SIG_I or SIG_R, is the result of the negotiated digital signature algorithm applied to HASH_I or HASH_R respectively. • In general the signature will be over HASH_I and HASH_R as above using the negotiated prf, or the HMAC version of the negotiated hash function (if no prf is negotiated). • However, this can be overridden for construction of the signature if the signature algorithm is tied to a particular hash algorithm (e. g. DSS is only defined with SHA's 160 bit output). Rappel • One or more certificate payloads MAY be optionally passed. • HASH_I = prf (SKEYID, g^xi | g^xr | CKY-I | CKY-R | SAi_b | IDii_b ) • HASH_R = prf (SKEYID, g^xr | g^xi | CKY-R | CKY-I | SAi_b | IDir_b )
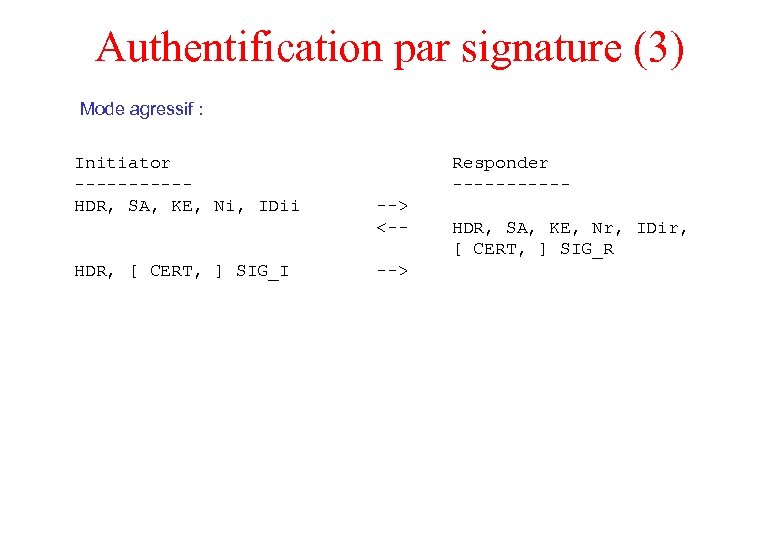
Authentification par signature (3) Mode agressif : Initiator -----HDR, SA, KE, Ni, IDii HDR, [ CERT, ] SIG_I Responder ------> <---> HDR, SA, KE, Nr, IDir, [ CERT, ] SIG_R
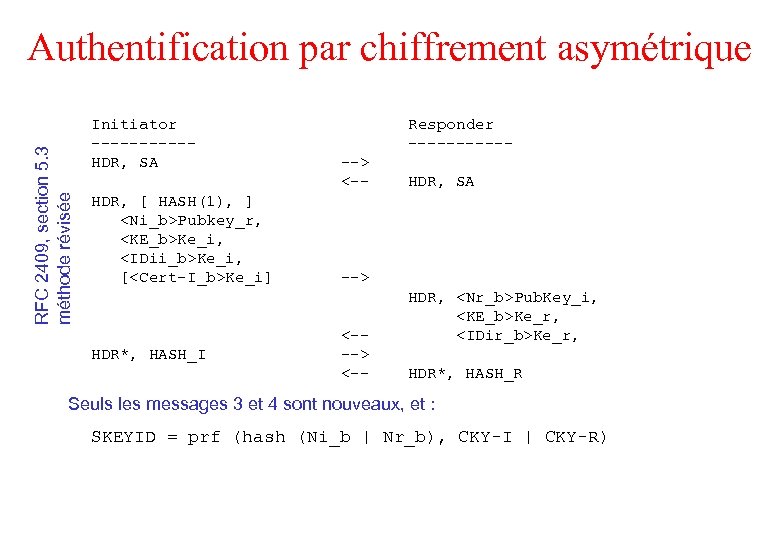
RFC 2409, section 5. 3 méthode révisée Authentification par chiffrement asymétrique Initiator -----HDR, SA HDR, [ HASH(1), ] <Ni_b>Pubkey_r, <KE_b>Ke_i, <IDii_b>Ke_i, [<Cert-I_b>Ke_i] HDR*, HASH_I Responder ------> <-- HDR, SA --> <-- HDR, <Nr_b>Pub. Key_i, <KE_b>Ke_r, <IDir_b>Ke_r, HDR*, HASH_R Seuls les messages 3 et 4 sont nouveaux, et : SKEYID = prf (hash (Ni_b | Nr_b), CKY-I | CKY-R)
RFC 2409, section 5. 2 Authentification par chiffrement asymétrique (2) • Using encryption for authentication provides for a plausably deniable exchange. There is no proof (as with a digital signature) that the conversation ever took place since each party can completely reconstruct both sides of the exchange. • In addition, security is added to secret generation since an attacker would have to successfully break not only the Diffie-Hellman exchange but also both RSA encryptions. • This exchange was motivated by [SKEME].
RFC 2409, section 5. 3 Authentification par chiffrement asymétrique (3) • In this mode, the nonce is still encrypted using the public key of the peer, however the peer's identity (and the certificate if it is sent) is encrypted using the negotiated symmetric encryption algorithm (from the SA payload) with a key derived from the nonce. • This solution adds minimal complexity and state yet saves two costly public key operations on each side. In addition, the Key Exchange payload is also encrypted using the same derived key. This provides additional protection against cryptanalysis of the Diffie-Hellman exchange. • A HASH payload may be sent to identify a certificate if the responder has multiple certificates which contain useable public keys (e. g. if the certificate is not for signatures only, either due to certificate restrictions or algorithmic restrictions).
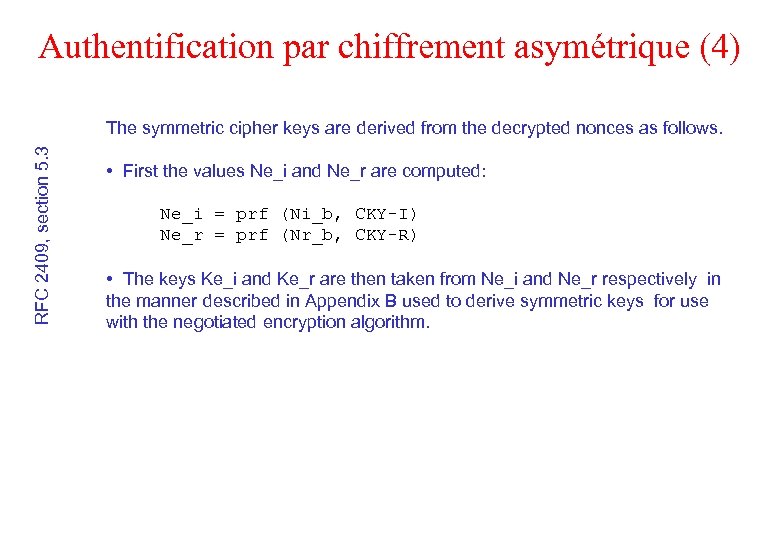
Authentification par chiffrement asymétrique (4) RFC 2409, section 5. 3 The symmetric cipher keys are derived from the decrypted nonces as follows. • First the values Ne_i and Ne_r are computed: Ne_i = prf (Ni_b, CKY-I) Ne_r = prf (Nr_b, CKY-R) • The keys Ke_i and Ke_r are then taken from Ne_i and Ne_r respectively in the manner described in Appendix B used to derive symmetric keys for use with the negotiated encryption algorithm.
![Authentification par chiffrement asymétrique (5) Mode agressif : Initiator -----HDR, SA, [ HASH(1), ] Authentification par chiffrement asymétrique (5) Mode agressif : Initiator -----HDR, SA, [ HASH(1), ]](https://present5.com/presentation/67b5a220b4fcfaa554566c6b6b994380/image-33.jpg)
Authentification par chiffrement asymétrique (5) Mode agressif : Initiator -----HDR, SA, [ HASH(1), ] <Ni_b>Pubkey_r, <KE_b>Ke_i, <IDii_b>Ke_i [, <Cert-I_b>Ke_i ] --> HDR, HASH_I <---> Responder ------ HDR, SA, <Nr_b>Pub. Key_i, <KE_b>Ke_r, <IDir_b>Ke_r, HASH_R
Phase 2 (Quick Mode) • Quick Mode is not a complete exchange itself (in that it is bound to a phase 1 exchange), but is used as part of the SA negotiation process (phase 2) to derive keying material and negotiate shared policy for non-ISAKMP SAs. • The information exchanged along with Quick Mode MUST be protected by the ISAKMP SA -- i. e. all payloads except the ISAKMP header are encrypted. • In Quick Mode, a HASH payload MUST immediately follow the ISAKMP header and a SA payload MUST immediately follow the HASH. This HASH authenticates the message and also provides liveliness proofs.
Quick Mode (2) • Quick Mode is essentially a SA negotiation and an exchange of nonces that provides replay protection. • The nonces are used to generate fresh key material and prevent replay attacks from generating bogus security associations. • An optional Key Exchange payload can be exchanged to allow for an additional Diffie-Hellman exchange and exponentiation per Quick Mode. • Base Quick Mode (without the KE payload) refreshes the keying material derived from the exponentiation in phase 1. This does not provide PFS. Using the optional KE payload, an additional exponentiation is performed and PFS is provided for the keying material.
![Quick Mode (3) Initiator -----HDR*, HASH(1), SA, Ni [, KE ] [, IDci, IDcr Quick Mode (3) Initiator -----HDR*, HASH(1), SA, Ni [, KE ] [, IDci, IDcr](https://present5.com/presentation/67b5a220b4fcfaa554566c6b6b994380/image-36.jpg)
Quick Mode (3) Initiator -----HDR*, HASH(1), SA, Ni [, KE ] [, IDci, IDcr ] --> <-HDR*, HASH(3) --> Responder -----HDR*, HASH(2), SA, Nr [, KE ] [, IDci, IDcr]
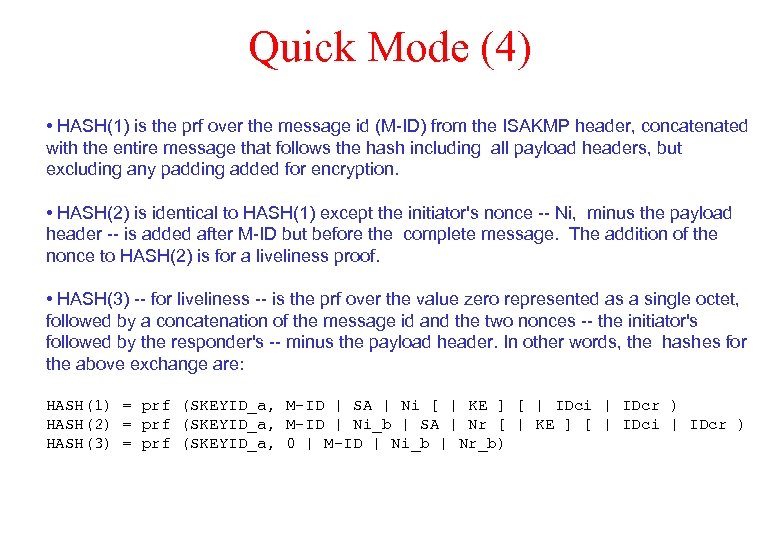
Quick Mode (4) • HASH(1) is the prf over the message id (M-ID) from the ISAKMP header, concatenated with the entire message that follows the hash including all payload headers, but excluding any padding added for encryption. • HASH(2) is identical to HASH(1) except the initiator's nonce -- Ni, minus the payload header -- is added after M-ID but before the complete message. The addition of the nonce to HASH(2) is for a liveliness proof. • HASH(3) -- for liveliness -- is the prf over the value zero represented as a single octet, followed by a concatenation of the message id and the two nonces -- the initiator's followed by the responder's -- minus the payload header. In other words, the hashes for the above exchange are: HASH(1) = prf (SKEYID_a, M-ID | SA | Ni [ | KE ] [ | IDci | IDcr ) HASH(2) = prf (SKEYID_a, M-ID | Ni_b | SA | Nr [ | KE ] [ | IDci | IDcr ) HASH(3) = prf (SKEYID_a, 0 | M-ID | Ni_b | Nr_b)
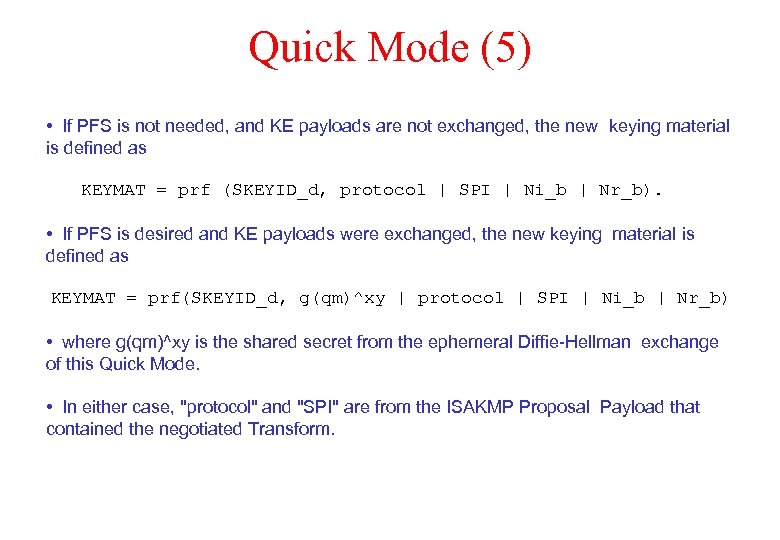
Quick Mode (5) • If PFS is not needed, and KE payloads are not exchanged, the new keying material is defined as KEYMAT = prf (SKEYID_d, protocol | SPI | Ni_b | Nr_b). • If PFS is desired and KE payloads were exchanged, the new keying material is defined as KEYMAT = prf(SKEYID_d, g(qm)^xy | protocol | SPI | Ni_b | Nr_b) • where g(qm)^xy is the shared secret from the ephemeral Diffie-Hellman exchange of this Quick Mode. • In either case, "protocol" and "SPI" are from the ISAKMP Proposal Payload that contained the negotiated Transform.
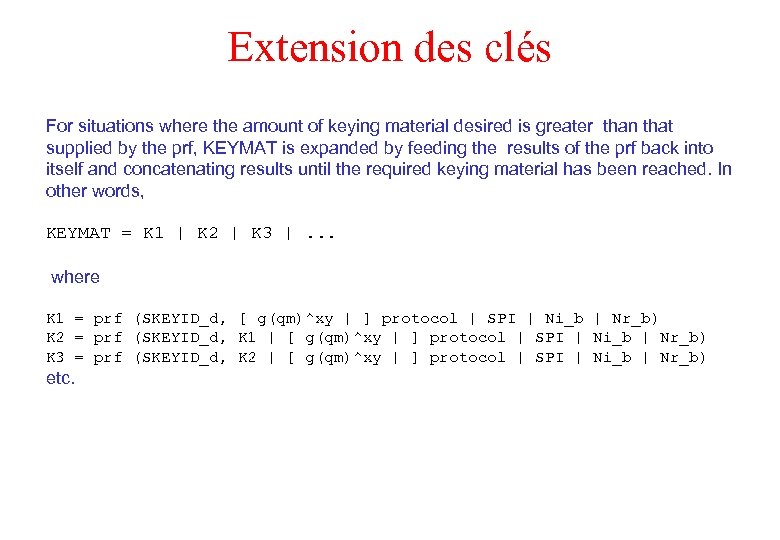
Extension des clés For situations where the amount of keying material desired is greater than that supplied by the prf, KEYMAT is expanded by feeding the results of the prf back into itself and concatenating results until the required keying material has been reached. In other words, KEYMAT = K 1 | K 2 | K 3 |. . . where K 1 = prf (SKEYID_d, [ g(qm)^xy | ] protocol | SPI | Ni_b | Nr_b) K 2 = prf (SKEYID_d, K 1 | [ g(qm)^xy | ] protocol | SPI | Ni_b | Nr_b) K 3 = prf (SKEYID_d, K 2 | [ g(qm)^xy | ] protocol | SPI | Ni_b | Nr_b) etc.
67b5a220b4fcfaa554566c6b6b994380.ppt