36a7c8732e25af5b83628b6094dbdaef.ppt
- Количество слайдов: 40
 Secure Human-Computer Identification against Peeping Attacks (Sec. HCI): A Survey Shujun Li, Harry Shum Visual Computing Group Microsoft Research Asia Sep. 2002
Secure Human-Computer Identification against Peeping Attacks (Sec. HCI): A Survey Shujun Li, Harry Shum Visual Computing Group Microsoft Research Asia Sep. 2002
 Outline Introduction A User Study Sec. HCI: General Model Sec. HCI: A Comprehensive Survey Sec. HCI: Other Related Works Our Opinions
Outline Introduction A User Study Sec. HCI: General Model Sec. HCI: A Comprehensive Survey Sec. HCI: Other Related Works Our Opinions
 1. Introduction Outline Human-Computer Identification Problems of Widely-Used Fixed Passwords Yet Another Danger: Peeping Attack In the real world ü In theoretical world ü Known Solutions to Peeping Attack
1. Introduction Outline Human-Computer Identification Problems of Widely-Used Fixed Passwords Yet Another Danger: Peeping Attack In the real world ü In theoretical world ü Known Solutions to Peeping Attack
 1. 1 Human-Computer Identification Three Identifications Knowledge-based: What do you know? ü ü Fixed (textual/visual) password / PIN Pass-phase / Pass-algorithm / word-association Challenge-response identification protocol Zero-knowledge identification protocol Token-based: What do you have? ü ü Magnetic-striped card / Smart card Hand-held one-time password generator Biometrics-based: Who are you? ü Face / Fingerprint / Iris / …
1. 1 Human-Computer Identification Three Identifications Knowledge-based: What do you know? ü ü Fixed (textual/visual) password / PIN Pass-phase / Pass-algorithm / word-association Challenge-response identification protocol Zero-knowledge identification protocol Token-based: What do you have? ü ü Magnetic-striped card / Smart card Hand-held one-time password generator Biometrics-based: Who are you? ü Face / Fingerprint / Iris / …
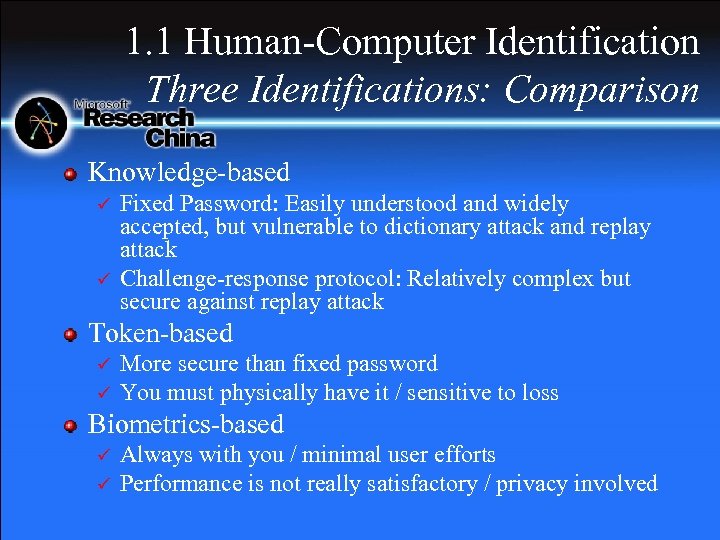 1. 1 Human-Computer Identification Three Identifications: Comparison Knowledge-based ü ü Fixed Password: Easily understood and widely accepted, but vulnerable to dictionary attack and replay attack Challenge-response protocol: Relatively complex but secure against replay attack Token-based ü ü More secure than fixed password You must physically have it / sensitive to loss Biometrics-based ü ü Always with you / minimal user efforts Performance is not really satisfactory / privacy involved
1. 1 Human-Computer Identification Three Identifications: Comparison Knowledge-based ü ü Fixed Password: Easily understood and widely accepted, but vulnerable to dictionary attack and replay attack Challenge-response protocol: Relatively complex but secure against replay attack Token-based ü ü More secure than fixed password You must physically have it / sensitive to loss Biometrics-based ü ü Always with you / minimal user efforts Performance is not really satisfactory / privacy involved
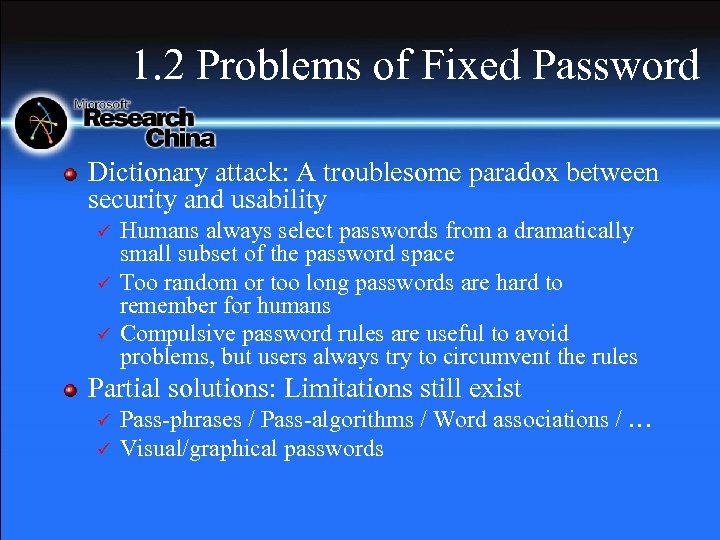 1. 2 Problems of Fixed Password Dictionary attack: A troublesome paradox between security and usability ü ü ü Humans always select passwords from a dramatically small subset of the password space Too random or too long passwords are hard to remember for humans Compulsive password rules are useful to avoid problems, but users always try to circumvent the rules Partial solutions: Limitations still exist ü ü Pass-phrases / Pass-algorithms / Word associations / … Visual/graphical passwords
1. 2 Problems of Fixed Password Dictionary attack: A troublesome paradox between security and usability ü ü ü Humans always select passwords from a dramatically small subset of the password space Too random or too long passwords are hard to remember for humans Compulsive password rules are useful to avoid problems, but users always try to circumvent the rules Partial solutions: Limitations still exist ü ü Pass-phrases / Pass-algorithms / Word associations / … Visual/graphical passwords
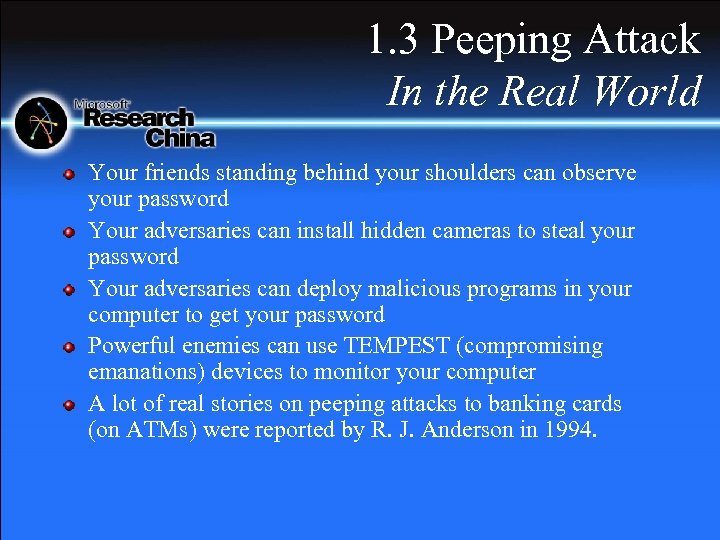 1. 3 Peeping Attack In the Real World Your friends standing behind your shoulders can observe your password Your adversaries can install hidden cameras to steal your password Your adversaries can deploy malicious programs in your computer to get your password Powerful enemies can use TEMPEST (compromising emanations) devices to monitor your computer A lot of real stories on peeping attacks to banking cards (on ATMs) were reported by R. J. Anderson in 1994.
1. 3 Peeping Attack In the Real World Your friends standing behind your shoulders can observe your password Your adversaries can install hidden cameras to steal your password Your adversaries can deploy malicious programs in your computer to get your password Powerful enemies can use TEMPEST (compromising emanations) devices to monitor your computer A lot of real stories on peeping attacks to banking cards (on ATMs) were reported by R. J. Anderson in 1994.
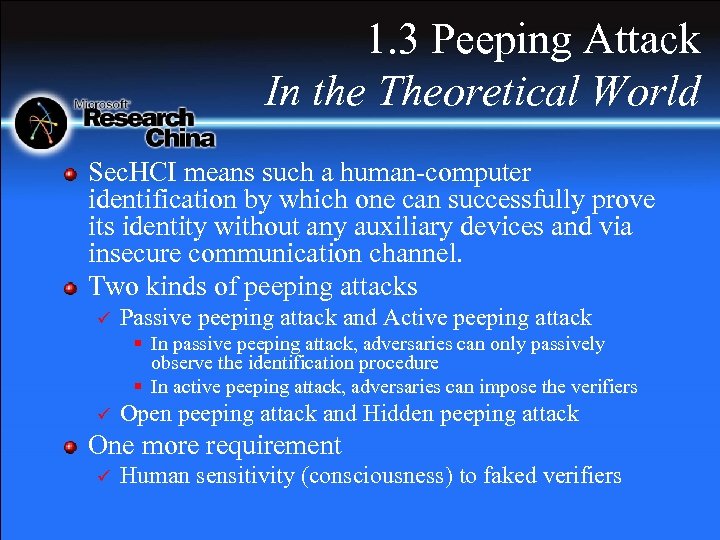 1. 3 Peeping Attack In the Theoretical World Sec. HCI means such a human-computer identification by which one can successfully prove its identity without any auxiliary devices and via insecure communication channel. Two kinds of peeping attacks ü Passive peeping attack and Active peeping attack § In passive peeping attack, adversaries can only passively observe the identification procedure § In active peeping attack, adversaries can impose the verifiers ü Open peeping attack and Hidden peeping attack One more requirement ü Human sensitivity (consciousness) to faked verifiers
1. 3 Peeping Attack In the Theoretical World Sec. HCI means such a human-computer identification by which one can successfully prove its identity without any auxiliary devices and via insecure communication channel. Two kinds of peeping attacks ü Passive peeping attack and Active peeping attack § In passive peeping attack, adversaries can only passively observe the identification procedure § In active peeping attack, adversaries can impose the verifiers ü Open peeping attack and Hidden peeping attack One more requirement ü Human sensitivity (consciousness) to faked verifiers
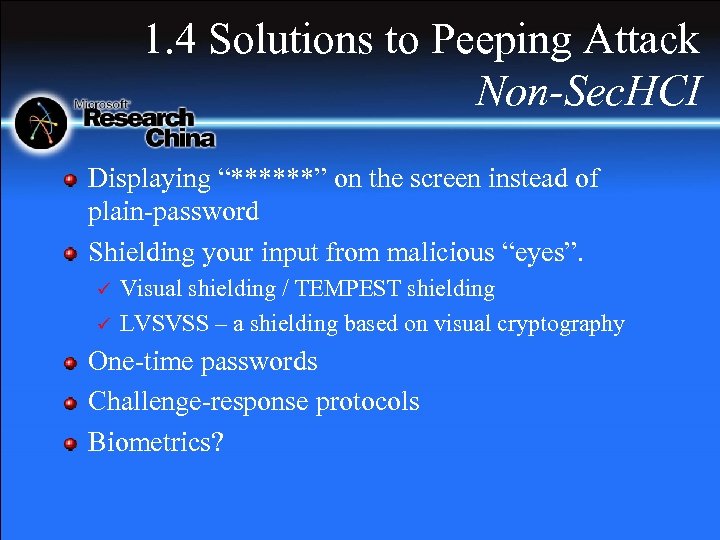 1. 4 Solutions to Peeping Attack Non-Sec. HCI Displaying “******” on the screen instead of plain-password Shielding your input from malicious “eyes”. ü ü Visual shielding / TEMPEST shielding LVSVSS – a shielding based on visual cryptography One-time passwords Challenge-response protocols Biometrics?
1. 4 Solutions to Peeping Attack Non-Sec. HCI Displaying “******” on the screen instead of plain-password Shielding your input from malicious “eyes”. ü ü Visual shielding / TEMPEST shielding LVSVSS – a shielding based on visual cryptography One-time passwords Challenge-response protocols Biometrics?
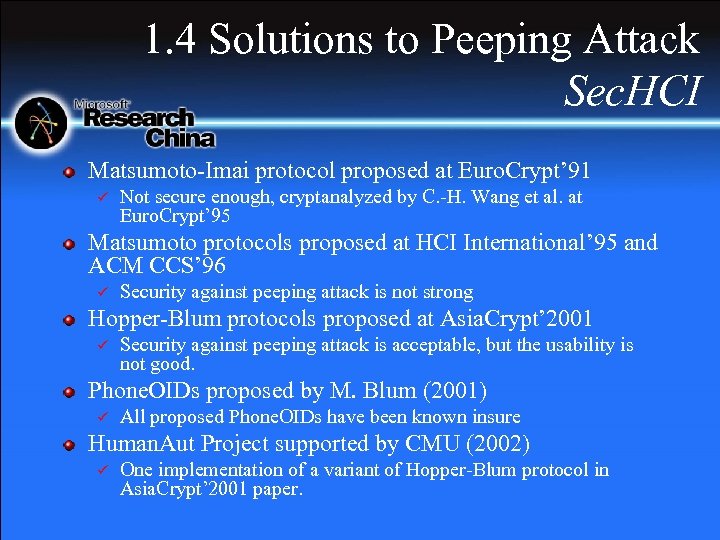 1. 4 Solutions to Peeping Attack Sec. HCI Matsumoto-Imai protocol proposed at Euro. Crypt’ 91 ü Not secure enough, cryptanalyzed by C. -H. Wang et al. at Euro. Crypt’ 95 Matsumoto protocols proposed at HCI International’ 95 and ACM CCS’ 96 ü Security against peeping attack is not strong Hopper-Blum protocols proposed at Asia. Crypt’ 2001 ü Security against peeping attack is acceptable, but the usability is not good. Phone. OIDs proposed by M. Blum (2001) ü All proposed Phone. OIDs have been known insure Human. Aut Project supported by CMU (2002) ü One implementation of a variant of Hopper-Blum protocol in Asia. Crypt’ 2001 paper.
1. 4 Solutions to Peeping Attack Sec. HCI Matsumoto-Imai protocol proposed at Euro. Crypt’ 91 ü Not secure enough, cryptanalyzed by C. -H. Wang et al. at Euro. Crypt’ 95 Matsumoto protocols proposed at HCI International’ 95 and ACM CCS’ 96 ü Security against peeping attack is not strong Hopper-Blum protocols proposed at Asia. Crypt’ 2001 ü Security against peeping attack is acceptable, but the usability is not good. Phone. OIDs proposed by M. Blum (2001) ü All proposed Phone. OIDs have been known insure Human. Aut Project supported by CMU (2002) ü One implementation of a variant of Hopper-Blum protocol in Asia. Crypt’ 2001 paper.
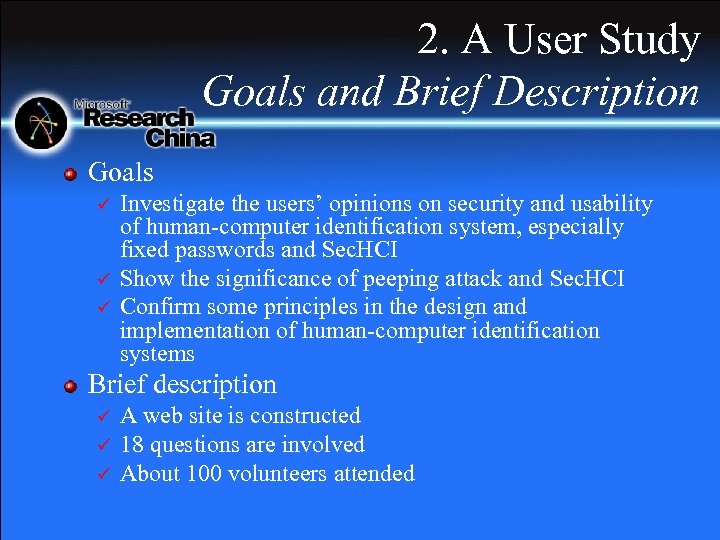 2. A User Study Goals and Brief Description Goals ü ü ü Investigate the users’ opinions on security and usability of human-computer identification system, especially fixed passwords and Sec. HCI Show the significance of peeping attack and Sec. HCI Confirm some principles in the design and implementation of human-computer identification systems Brief description ü ü ü A web site is constructed 18 questions are involved About 100 volunteers attended
2. A User Study Goals and Brief Description Goals ü ü ü Investigate the users’ opinions on security and usability of human-computer identification system, especially fixed passwords and Sec. HCI Show the significance of peeping attack and Sec. HCI Confirm some principles in the design and implementation of human-computer identification systems Brief description ü ü ü A web site is constructed 18 questions are involved About 100 volunteers attended
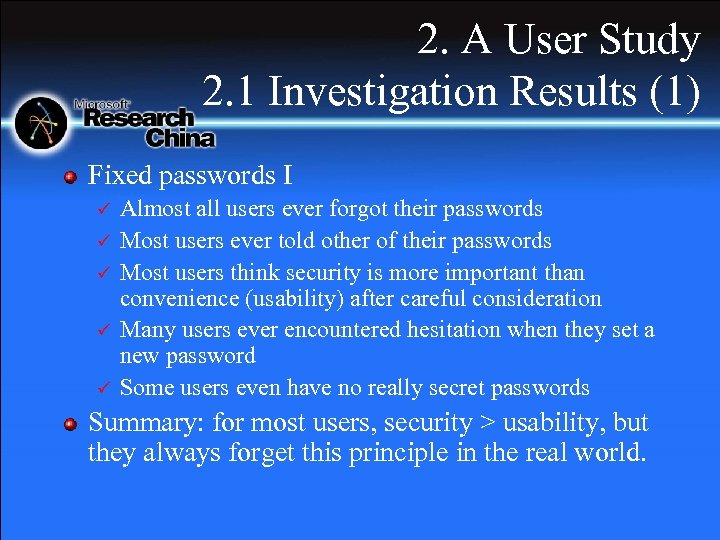 2. A User Study 2. 1 Investigation Results (1) Fixed passwords I ü ü ü Almost all users ever forgot their passwords Most users ever told other of their passwords Most users think security is more important than convenience (usability) after careful consideration Many users ever encountered hesitation when they set a new password Some users even have no really secret passwords Summary: for most users, security > usability, but they always forget this principle in the real world.
2. A User Study 2. 1 Investigation Results (1) Fixed passwords I ü ü ü Almost all users ever forgot their passwords Most users ever told other of their passwords Most users think security is more important than convenience (usability) after careful consideration Many users ever encountered hesitation when they set a new password Some users even have no really secret passwords Summary: for most users, security > usability, but they always forget this principle in the real world.
 2. A User Study 2. 1 Investigation Results (2) Fixed passwords II ü ü ü All users have two or more different passwords Most users have <=6 different passwords Most users use 6~10 -length passwords Most users also think 6~10 is the best password length Most users think 15 (about) is the upper bound of the password length for all security applications Summary: for most users, 6~10 -length passwords are good, and >16 length is unendurable.
2. A User Study 2. 1 Investigation Results (2) Fixed passwords II ü ü ü All users have two or more different passwords Most users have <=6 different passwords Most users use 6~10 -length passwords Most users also think 6~10 is the best password length Most users think 15 (about) is the upper bound of the password length for all security applications Summary: for most users, 6~10 -length passwords are good, and >16 length is unendurable.
 2. A User Study 2. 2 Investigation Results (3) Peeping attack Most users think peeping attack is a real danger in the security world, especially when their money and privacy is endangered. ü Most users will follows at least partial warns from security experts and technical news. ü Summary: the significance of peeping attack is confirmed, especially for electronic financial applications.
2. A User Study 2. 2 Investigation Results (3) Peeping attack Most users think peeping attack is a real danger in the security world, especially when their money and privacy is endangered. ü Most users will follows at least partial warns from security experts and technical news. ü Summary: the significance of peeping attack is confirmed, especially for electronic financial applications.
 2. A User Study 2. 2 Investigation Results (4) Sec. HCI ü ü Most users wish the identification procedure can be finished within 1 minute Most users think security and usability should be balanced in the design of secure human-computer identification Summary: a good Sec. HCI must balance security and usability, and the consuming time for one identification should be <= 1 minute.
2. A User Study 2. 2 Investigation Results (4) Sec. HCI ü ü Most users wish the identification procedure can be finished within 1 minute Most users think security and usability should be balanced in the design of secure human-computer identification Summary: a good Sec. HCI must balance security and usability, and the consuming time for one identification should be <= 1 minute.
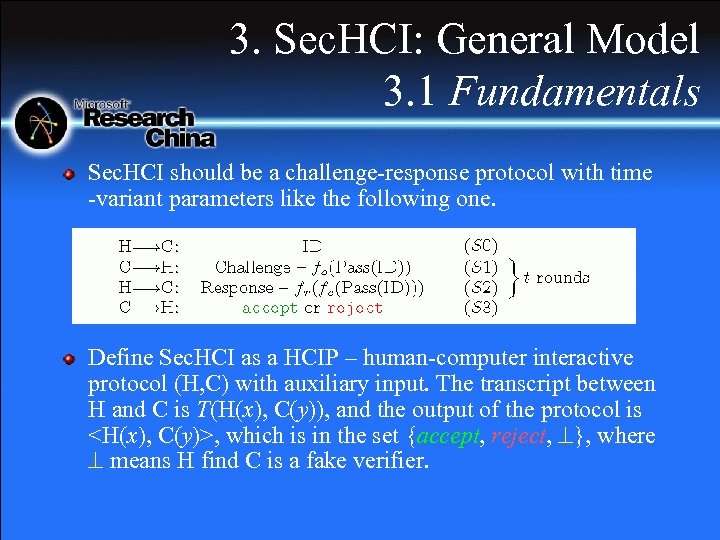 3. Sec. HCI: General Model 3. 1 Fundamentals Sec. HCI should be a challenge-response protocol with time -variant parameters like the following one. Define Sec. HCI as a HCIP – human-computer interactive protocol (H, C) with auxiliary input. The transcript between H and C is T(H(x), C(y)), and the output of the protocol is
3. Sec. HCI: General Model 3. 1 Fundamentals Sec. HCI should be a challenge-response protocol with time -variant parameters like the following one. Define Sec. HCI as a HCIP – human-computer interactive protocol (H, C) with auxiliary input. The transcript between H and C is T(H(x), C(y)), and the output of the protocol is
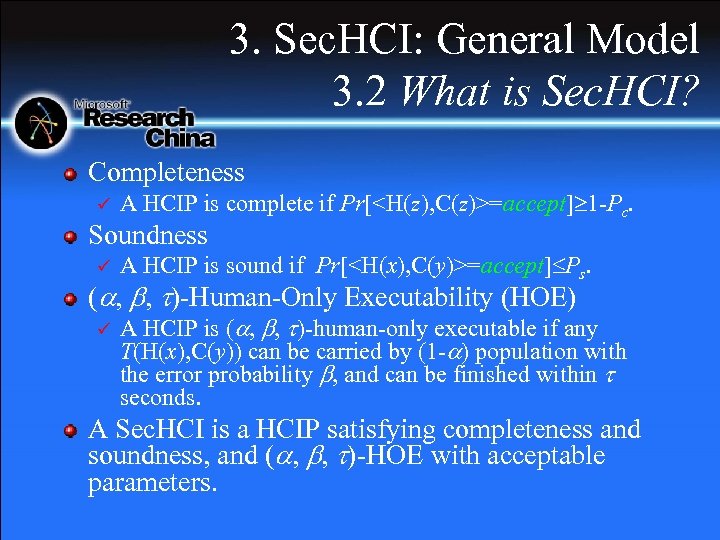 3. Sec. HCI: General Model 3. 2 What is Sec. HCI? Completeness ü A HCIP is complete if Pr[
3. Sec. HCI: General Model 3. 2 What is Sec. HCI? Completeness ü A HCIP is complete if Pr[
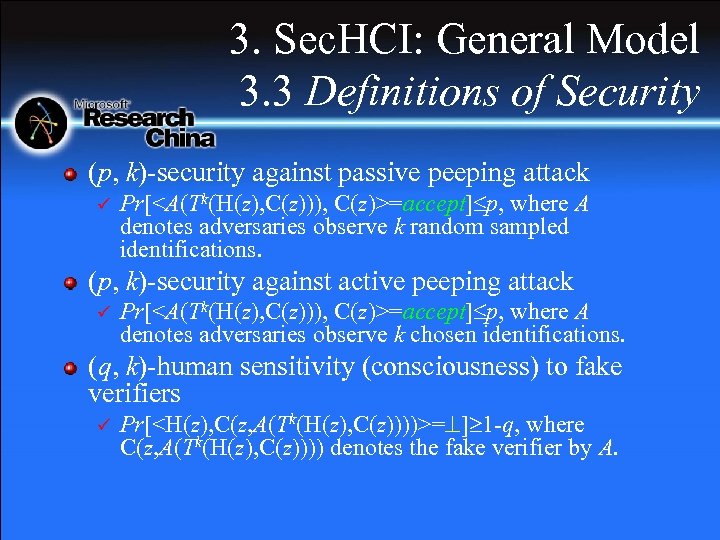 3. Sec. HCI: General Model 3. 3 Definitions of Security (p, k)-security against passive peeping attack ü Pr[
3. Sec. HCI: General Model 3. 3 Definitions of Security (p, k)-security against passive peeping attack ü Pr[
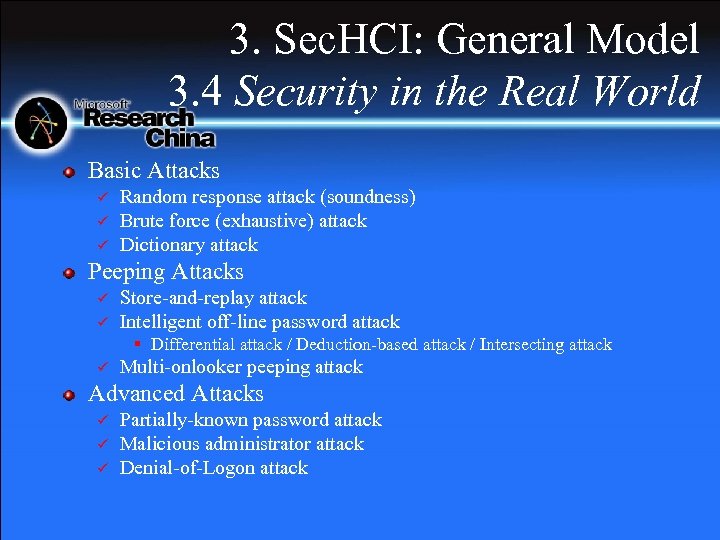 3. Sec. HCI: General Model 3. 4 Security in the Real World Basic Attacks ü ü ü Random response attack (soundness) Brute force (exhaustive) attack Dictionary attack Peeping Attacks ü ü Store-and-replay attack Intelligent off-line password attack § Differential attack / Deduction-based attack / Intersecting attack ü Multi-onlooker peeping attack Advanced Attacks ü ü ü Partially-known password attack Malicious administrator attack Denial-of-Logon attack
3. Sec. HCI: General Model 3. 4 Security in the Real World Basic Attacks ü ü ü Random response attack (soundness) Brute force (exhaustive) attack Dictionary attack Peeping Attacks ü ü Store-and-replay attack Intelligent off-line password attack § Differential attack / Deduction-based attack / Intersecting attack ü Multi-onlooker peeping attack Advanced Attacks ü ü ü Partially-known password attack Malicious administrator attack Denial-of-Logon attack
![4. A Comprehensive Survey 4. 1 Matsumoto-Imai Protocol Matsumoto-Imai protocol [Euro. Crypt’ 91] ü 4. A Comprehensive Survey 4. 1 Matsumoto-Imai Protocol Matsumoto-Imai protocol [Euro. Crypt’ 91] ü](https://present5.com/presentation/36a7c8732e25af5b83628b6094dbdaef/image-20.jpg) 4. A Comprehensive Survey 4. 1 Matsumoto-Imai Protocol Matsumoto-Imai protocol [Euro. Crypt’ 91] ü An simple example to show the basic idea: ={1, 2, …, 9, 0}, ={1, 2, …, 8} , the password is ={1, 2, 4, 6} , ={1, 2, 3, 4} , W=3124. Assume =#( )=8 and =#( )=4, the challenge q is a bijection from to , and the response is a -length word a=(a 1, …, a ) whose characters are all in . The accepted responses should satisfy the following requirement: extract all characters in q and also in , and record their order in q to compose a list f=(f 1, …, f ), then i=1~ , af(i)=W(i).
4. A Comprehensive Survey 4. 1 Matsumoto-Imai Protocol Matsumoto-Imai protocol [Euro. Crypt’ 91] ü An simple example to show the basic idea: ={1, 2, …, 9, 0}, ={1, 2, …, 8} , the password is ={1, 2, 4, 6} , ={1, 2, 3, 4} , W=3124. Assume =#( )=8 and =#( )=4, the challenge q is a bijection from to , and the response is a -length word a=(a 1, …, a ) whose characters are all in . The accepted responses should satisfy the following requirement: extract all characters in q and also in , and record their order in q to compose a list f=(f 1, …, f ), then i=1~ , af(i)=W(i).
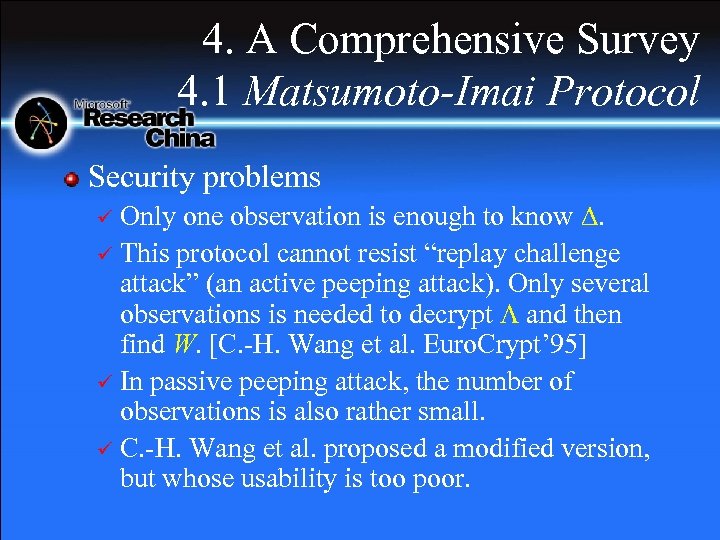 4. A Comprehensive Survey 4. 1 Matsumoto-Imai Protocol Security problems Only one observation is enough to know . ü This protocol cannot resist “replay challenge attack” (an active peeping attack). Only several observations is needed to decrypt and then find W. [C. -H. Wang et al. Euro. Crypt’ 95] ü In passive peeping attack, the number of observations is also rather small. ü C. -H. Wang et al. proposed a modified version, but whose usability is too poor. ü
4. A Comprehensive Survey 4. 1 Matsumoto-Imai Protocol Security problems Only one observation is enough to know . ü This protocol cannot resist “replay challenge attack” (an active peeping attack). Only several observations is needed to decrypt and then find W. [C. -H. Wang et al. Euro. Crypt’ 95] ü In passive peeping attack, the number of observations is also rather small. ü C. -H. Wang et al. proposed a modified version, but whose usability is too poor. ü
![4. A Comprehensive Survey 4. 2 Matsumoto Protocols Matsumoto Protocol 0 [ACM CCS’ 96] 4. A Comprehensive Survey 4. 2 Matsumoto Protocols Matsumoto Protocol 0 [ACM CCS’ 96]](https://present5.com/presentation/36a7c8732e25af5b83628b6094dbdaef/image-22.jpg) 4. A Comprehensive Survey 4. 2 Matsumoto Protocols Matsumoto Protocol 0 [ACM CCS’ 96] ü ü Fs is a finite field of order s. The password is u vectors k 1~ku, where ki is vdimensional vector in Fsv. The challenge is a non-zero v-dimensional vector qi in Fsv-{0}; the response ai is a element in Fs. If i=1~u, ai=qi ki, the user is accepted. Matsumoto Protocol 1 and 2 [ACM CCS’ 96] ü Non-essential variants of Protocol 0.
4. A Comprehensive Survey 4. 2 Matsumoto Protocols Matsumoto Protocol 0 [ACM CCS’ 96] ü ü Fs is a finite field of order s. The password is u vectors k 1~ku, where ki is vdimensional vector in Fsv. The challenge is a non-zero v-dimensional vector qi in Fsv-{0}; the response ai is a element in Fs. If i=1~u, ai=qi ki, the user is accepted. Matsumoto Protocol 1 and 2 [ACM CCS’ 96] ü Non-essential variants of Protocol 0.
 4. A Comprehensive Survey 4. 2 Matsumoto Protocols Usability Issues ü ü ü Protocol 1 can make implementations easier. Protocol 2 can provide a better trade-off between security and usability. Some graphical implementations of Protocol 1 and 2 are given in Matsumoto’s paper. Security Issues ü To break the password, only O(u) observations are needed for both passive and active peeping attack.
4. A Comprehensive Survey 4. 2 Matsumoto Protocols Usability Issues ü ü ü Protocol 1 can make implementations easier. Protocol 2 can provide a better trade-off between security and usability. Some graphical implementations of Protocol 1 and 2 are given in Matsumoto’s paper. Security Issues ü To break the password, only O(u) observations are needed for both passive and active peeping attack.
![4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Hopper-Blum Protocol 1 [Asia. Crypt’ 2001] 4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Hopper-Blum Protocol 1 [Asia. Crypt’ 2001]](https://present5.com/presentation/36a7c8732e25af5b83628b6094dbdaef/image-24.jpg) 4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Hopper-Blum Protocol 1 [Asia. Crypt’ 2001] The password is a (0, 1)-vector x {0, 1}n whose weight is k. ü The challenge is also a (0, 1)-vector c {0, 1}n. The response r is 0 or 1. ü For total m challenge, if r=c x holds for at least (1 - )m challenges, the user is accepted. ü
4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Hopper-Blum Protocol 1 [Asia. Crypt’ 2001] The password is a (0, 1)-vector x {0, 1}n whose weight is k. ü The challenge is also a (0, 1)-vector c {0, 1}n. The response r is 0 or 1. ü For total m challenge, if r=c x holds for at least (1 - )m challenges, the user is accepted. ü
 4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Security Issues ü Hopper-Blum Protocol 1 cannot resist replay challenge attack (active peeping attack). Some Errors and More Problems The result of Theorem 1 is wrong. ü The masquerading probability of random response attack is slightly overestimated. ü Paradox exists between security and usability, especially on the value of k. ü
4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Security Issues ü Hopper-Blum Protocol 1 cannot resist replay challenge attack (active peeping attack). Some Errors and More Problems The result of Theorem 1 is wrong. ü The masquerading probability of random response attack is slightly overestimated. ü Paradox exists between security and usability, especially on the value of k. ü
![4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Hopper-Blum Protocol 2 [Asia. Crypt’ 2001] 4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Hopper-Blum Protocol 2 [Asia. Crypt’ 2001]](https://present5.com/presentation/36a7c8732e25af5b83628b6094dbdaef/image-26.jpg) 4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Hopper-Blum Protocol 2 [Asia. Crypt’ 2001] Basically, Protocol 2 is similar to Protocol 1 with two chief modifications. ü Modification 1: the response is calculated with sum of k mins. ü Modification 2: the linear error-correcting mechanism is introduced to avoid malicious change of legal challenges. ü
4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Hopper-Blum Protocol 2 [Asia. Crypt’ 2001] Basically, Protocol 2 is similar to Protocol 1 with two chief modifications. ü Modification 1: the response is calculated with sum of k mins. ü Modification 2: the linear error-correcting mechanism is introduced to avoid malicious change of legal challenges. ü
 4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Merits Protocol 2 can resist active peeping attack. ü Protocol 2 has 0. 1 -human sensitive to fake verifiers. ü Problems Usability of Protocol 2 is even more poor than Protocol 1. ü Some problems in Protocol 1 still exist in Protocol 2. ü
4. A Comprehensive Survey 4. 3 Hopper-Blum Protocols Merits Protocol 2 can resist active peeping attack. ü Protocol 2 has 0. 1 -human sensitive to fake verifiers. ü Problems Usability of Protocol 2 is even more poor than Protocol 1. ü Some problems in Protocol 1 still exist in Protocol 2. ü
 4. A Comprehensive Survey 4. 4 Human. OIDs@CMU Human. Aut@CMU ü ü ü An image-based Sec. HCI, n images are involved and n/2 images compose the password. A non-essential variant of Hopper-Blum Protocol 1. The challenge is always a vector with fixed weight. Usability is poor when n is too large. Pass-Rules ü ü You can freely change all n images. Then you can use some meaningful features of the n/2 pass-images to remember so many pictures.
4. A Comprehensive Survey 4. 4 Human. OIDs@CMU Human. Aut@CMU ü ü ü An image-based Sec. HCI, n images are involved and n/2 images compose the password. A non-essential variant of Hopper-Blum Protocol 1. The challenge is always a vector with fixed weight. Usability is poor when n is too large. Pass-Rules ü ü You can freely change all n images. Then you can use some meaningful features of the n/2 pass-images to remember so many pictures.
 4. A Comprehensive Survey 4. 4 Human. OIDs@CMU Phone. OIDs is “challenge-response protocols for use over the phone”, which means Sec. HCI protocols of two parties with limited computation capabilities. ü Many Phone. OIDs have been proposed, but all are insecure. ü
4. A Comprehensive Survey 4. 4 Human. OIDs@CMU Phone. OIDs is “challenge-response protocols for use over the phone”, which means Sec. HCI protocols of two parties with limited computation capabilities. ü Many Phone. OIDs have been proposed, but all are insecure. ü
 5. Other Related Works 5. 1 Visual/Graphical Passwords Selective pictures based passwords ü ü Passface. TM: In each round, select your pass-face from 9 candidate faces. Déjà Vu: Select m portfolio images from n candidate images. Point-and-click passwords ü ü Pass. Pic: Click your pass-positions with your pass-order Graphical Password Windows in Passlogix v-GOTM SSO: Click several things to construct your password. Drawing-based passwords ü Draw-a-Secret (DAS): Draw your pass-strokes on a m n grid.
5. Other Related Works 5. 1 Visual/Graphical Passwords Selective pictures based passwords ü ü Passface. TM: In each round, select your pass-face from 9 candidate faces. Déjà Vu: Select m portfolio images from n candidate images. Point-and-click passwords ü ü Pass. Pic: Click your pass-positions with your pass-order Graphical Password Windows in Passlogix v-GOTM SSO: Click several things to construct your password. Drawing-based passwords ü Draw-a-Secret (DAS): Draw your pass-strokes on a m n grid.
 5. Other Related Works 5. 2 CAPTCHAs CAPTCHA stands for “Completely Automated Public Turing Test to Tell Computers and Humans Apart”, also called Reverse Turing Test by some researchers. The chief application of CAPTCHA is to foil malicious online robots, and can also be used to relax the security against random response attack in Sec. HCI protocols. The first paper on CAPTCHA occurred in 1996 (by M. Naor). The first implementation of CAPTCHA is designed in 1997. The initial booming of interests on CAPTCHAs is promoted by the occurrence of Gimpy, a CAPTCHA designed by M. Blum et al. at CMU in 2000. Now a CAPTCHA project is supported by Aladdin Center of CMU.
5. Other Related Works 5. 2 CAPTCHAs CAPTCHA stands for “Completely Automated Public Turing Test to Tell Computers and Humans Apart”, also called Reverse Turing Test by some researchers. The chief application of CAPTCHA is to foil malicious online robots, and can also be used to relax the security against random response attack in Sec. HCI protocols. The first paper on CAPTCHA occurred in 1996 (by M. Naor). The first implementation of CAPTCHA is designed in 1997. The initial booming of interests on CAPTCHAs is promoted by the occurrence of Gimpy, a CAPTCHA designed by M. Blum et al. at CMU in 2000. Now a CAPTCHA project is supported by Aladdin Center of CMU.
 5. Other Related Works 5. 2 CAPTCHAs Distorted texts based CAPTCHAs ü ü ü Gimpy@CMU Another Gimpy-like CAPTCHA@Alta. Vista Pessimal print Visual pattern based CAPTCHAs ü Bongo@CMU Image based CAPTCHAs ü ü ü PIX@CMU CAPTCHAs based on image search problem More image processing techniques can be used to distort involved images
5. Other Related Works 5. 2 CAPTCHAs Distorted texts based CAPTCHAs ü ü ü Gimpy@CMU Another Gimpy-like CAPTCHA@Alta. Vista Pessimal print Visual pattern based CAPTCHAs ü Bongo@CMU Image based CAPTCHAs ü ü ü PIX@CMU CAPTCHAs based on image search problem More image processing techniques can be used to distort involved images
 5. Other Related Works 5. 2 CAPTCHAs Sound/Speech based CAPTCHAs Sounds@CMU ü Byan@City. UHK ü Text-only CAPTCHAs Impossibility of text-only CAPTCHAs under six assumptions ü “Find the Bogus Word” ü Chinese CAPTCHAs?
5. Other Related Works 5. 2 CAPTCHAs Sound/Speech based CAPTCHAs Sounds@CMU ü Byan@City. UHK ü Text-only CAPTCHAs Impossibility of text-only CAPTCHAs under six assumptions ü “Find the Bogus Word” ü Chinese CAPTCHAs?
 5. Other Related Works 5. 3 More Topics on HIPs HIP means “Human Interactive Proof”, which covers many topics, such as Sec. HCI protocol, CAPTCHA, and visual/graphical password. There is a HIP project at Aladdin Center of CMU to support research and product transfer of theoretical results.
5. Other Related Works 5. 3 More Topics on HIPs HIP means “Human Interactive Proof”, which covers many topics, such as Sec. HCI protocol, CAPTCHA, and visual/graphical password. There is a HIP project at Aladdin Center of CMU to support research and product transfer of theoretical results.
 5. Other Related Works 5. 3 More Topics on HIPs Formal Studies on Security and Complexity of HIPs Computer Vision and HIPs Biometrics Visual Cryptography Human-Error-Tolerant Passwords (or Fuzzy Commitment) Other Sides?
5. Other Related Works 5. 3 More Topics on HIPs Formal Studies on Security and Complexity of HIPs Computer Vision and HIPs Biometrics Visual Cryptography Human-Error-Tolerant Passwords (or Fuzzy Commitment) Other Sides?
 5. Other Related Works 5. 4 ZK Identification Protocol Many Zero-Knowledge based identification protocols have been proposed. The basic idea used in ZK protocols may be useful for the design of Sec. HCI protocols. The general model of ZK identification protocols: 1) P=>V: a public (random) witness; 2) V=>P: a (random) challenge; 3) P=>V: a response (dependent on the witness and the challenge).
5. Other Related Works 5. 4 ZK Identification Protocol Many Zero-Knowledge based identification protocols have been proposed. The basic idea used in ZK protocols may be useful for the design of Sec. HCI protocols. The general model of ZK identification protocols: 1) P=>V: a public (random) witness; 2) V=>P: a (random) challenge; 3) P=>V: a response (dependent on the witness and the challenge).
 6. Our Opinion on Sec. HCI 6. 1 A Comparison By security against passive peeping attack ü Matsumoto-Imai Protocol < Matsumoto Protocols < Hopper-Blum Protocol 2 < Hopper-Blum Protocol 1; By security against active peeping attack ü Matsumoto-Imai Protocol < Matsumoto Protocols < Hopper-Blum Protocol 1 < Hopper-Blum Protocol 2; By usability ü Hopper-Blum Protocol 2 < Matsumoto-Imai Protocol < (0, 1)-version of Hopper-Blum Protocol 1 decimal version of Hopper-Blum Protocol 1 Matsumoto Protocols.
6. Our Opinion on Sec. HCI 6. 1 A Comparison By security against passive peeping attack ü Matsumoto-Imai Protocol < Matsumoto Protocols < Hopper-Blum Protocol 2 < Hopper-Blum Protocol 1; By security against active peeping attack ü Matsumoto-Imai Protocol < Matsumoto Protocols < Hopper-Blum Protocol 1 < Hopper-Blum Protocol 2; By usability ü Hopper-Blum Protocol 2 < Matsumoto-Imai Protocol < (0, 1)-version of Hopper-Blum Protocol 1 decimal version of Hopper-Blum Protocol 1 Matsumoto Protocols.
 6. Our Opinion on Sec. HCI 6. 2 Our Opinion Three principles Intentional errors ü Redundancies ü Balance ü Two desired requirements The password length <= 16 ü The identification time <= 1 minute. ü
6. Our Opinion on Sec. HCI 6. 2 Our Opinion Three principles Intentional errors ü Redundancies ü Balance ü Two desired requirements The password length <= 16 ü The identification time <= 1 minute. ü
 6. Our Opinion on Sec. HCI 6. 3 A Prototype Protocol Following our opinions on Sec. HCI, we can give a prototype protocol as follows The password is a (0, 1)-vector x {0, 1}n whose weight is k. ü The challenge is 2 m (0, 1)-vectors c 1, …, c 2 m {0, 1}n. The response is 2 m bits r 1, …r 2 m. ü If i=1~m, (r 2 i-1 -c 2 i-1 x)+(r 2 i-c 2 i x)=1 (mod 2), then the user is accepted. ü Such a protocol may be OK as a new solution of Sec. HCI. ü
6. Our Opinion on Sec. HCI 6. 3 A Prototype Protocol Following our opinions on Sec. HCI, we can give a prototype protocol as follows The password is a (0, 1)-vector x {0, 1}n whose weight is k. ü The challenge is 2 m (0, 1)-vectors c 1, …, c 2 m {0, 1}n. The response is 2 m bits r 1, …r 2 m. ü If i=1~m, (r 2 i-1 -c 2 i-1 x)+(r 2 i-c 2 i x)=1 (mod 2), then the user is accepted. ü Such a protocol may be OK as a new solution of Sec. HCI. ü
 Thanks for watching!
Thanks for watching!


