e0b2272804ffd74be26ff6f0933b8343.ppt
- Количество слайдов: 51
Secret-Ballot Receipts True Voter-Verifiable Elections David Chaum
Main Points • • WOTE I and Standardization workshop (Focus on polling-place elections) Don’t have to trust computers with integrity Four system examples – – • • Janken High-registration printing Subtractive light Additive light Mixing with bitmaps and its audit Provisional voting & adjudication Comparison of current proposals (Paper instruments can be modified before recount)
OUTLINE • Introduction • • WOTE and WEST Polling-place election background Receipt system introduction Educational example receipt system • Three example receipt systems • Comparison with non-receipt systems • Comments on Standardization
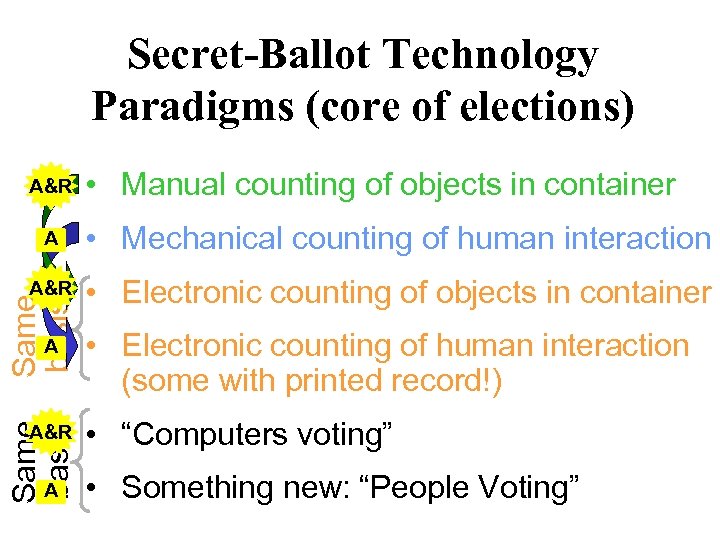
Secret-Ballot Technology Paradigms (core of elections) A&R • Manual counting of objects in container • Mechanical counting of human interaction A&R • Electronic counting of objects in container Same basis A A&R A • Electronic counting of human interaction (some with printed record!) • “Computers voting” • Something new: “People Voting”
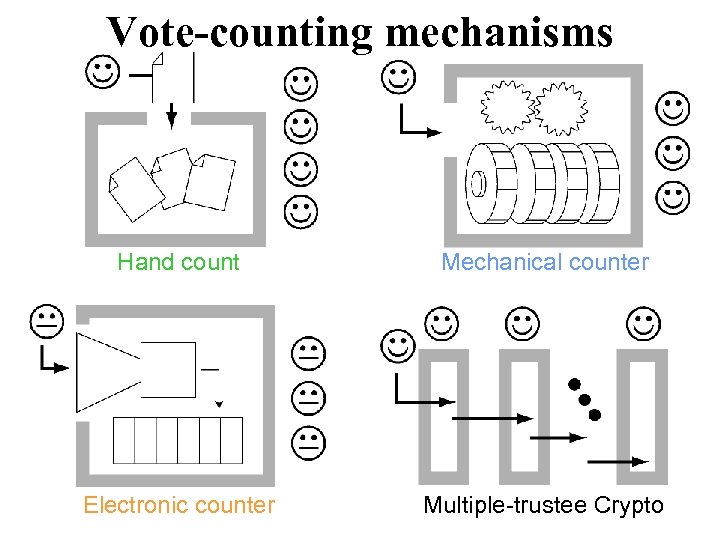
Vote-counting mechanisms Hand count Mechanical counter Electronic counter Multiple-trustee Crypto
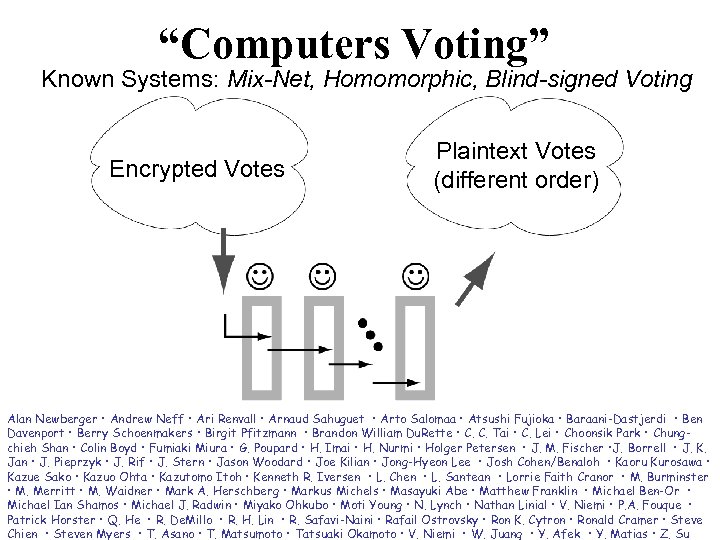
“Computers Voting” Known Systems: Mix-Net, Homomorphic, Blind-signed Voting Encrypted Votes Plaintext Votes (different order) Alan Newberger • Andrew Neff • Ari Renvall • Arnaud Sahuguet • Arto Salomaa • Atsushi Fujioka • Baraani-Dastjerdi • Ben Davenport • Berry Schoenmakers • Birgit Pfitzmann • Brandon William Du. Rette • C. C. Tai • C. Lei • Choonsik Park • Chungchieh Shan • Colin Boyd • Fumiaki Miura • G. Poupard • H. Imai • H. Nurmi • Holger Petersen • J. M. Fischer • J. Borrell • J. K. Jan • J. Pieprzyk • J. Rif • J. Stern • Jason Woodard • Joe Kilian • Jong-Hyeon Lee • Josh Cohen/Benaloh • Kaoru Kurosawa • Kazue Sako • Kazuo Ohta • Kazutomo Itoh • Kenneth R. Iversen • L. Chen • L. Santean • Lorrie Faith Cranor • M. Burminster • M. Merritt • M. Waidner • Mark A. Herschberg • Markus Michels • Masayuki Abe • Matthew Franklin • Michael Ben-Or • Michael Ian Shamos • Michael J. Radwin • Miyako Ohkubo • Moti Young • N. Lynch • Nathan Linial • V. Niemi • P. A. Fouque • Patrick Horster • Q. He • R. De. Millo • R. H. Lin • R. Safavi-Naini • Rafail Ostrovsky • Ron K. Cytron • Ronald Cramer • Steve Chien • Steven Myers • T. Asano • T. Matsumoto • Tatsuaki Okamoto • V. Niemi • W. Juang • Y. Afek • Y. Matias • Z. Su
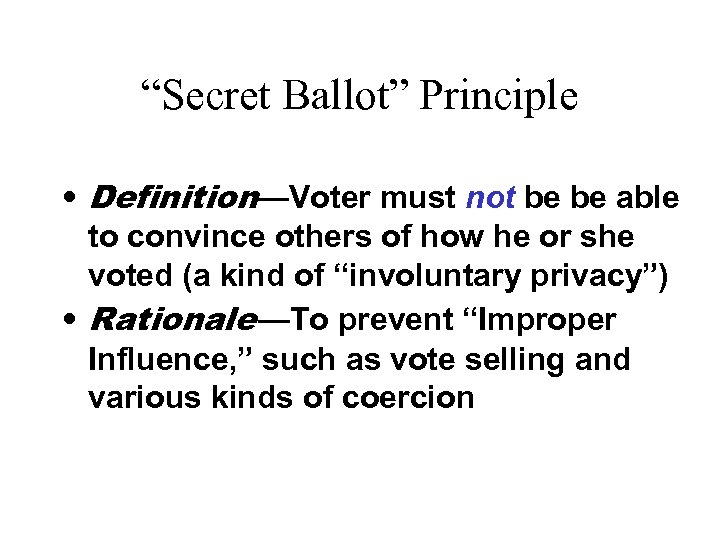
“Secret Ballot” Principle • Definition—Voter must not be be able to convince others of how he or she voted (a kind of “involuntary privacy”) • Rationale —To prevent “Improper Influence, ” such as vote selling and various kinds of coercion
“Unconditional Integrity” • Definition—Even infinite computing power should not allow incorrect tally (except with negligible probability) – privacy may have to be computational… • Rationale—Integrity should take priority over privacy (since changing outcome allows privacy rules to be changed!)
OUTLINE • Introduction • • WOTE and WEST Polling-place election background Receipt system introduction Educational example receipt system • Three example receipt systems • Comparison with non-receipt systems • Comments on Standardization
Two truisms are false 1. Receipts including who you voted for violate the “Secret Ballot” principle. Not if they are readable in the voting booth but unreadable once taken outside. 2. The computers used to vote and to tally the votes must be trusted with the correctness of the tally. Not if copies of encrypted votes on voters’ receipts can be posted along with proofs of corectness for the tally process.
First True “Voter-Verifiable” Election System Voters can directly verify that their votes are included in the tally without needing to trust any procedures, computers, or cryptography used by those conducting the election
The new scheme presented is of practical interest • Integrity is much higher but less costly – Reduced need for physical security, audit, observing, testing, etc. • Robustness is much higher but less costly – Receipts sufficient to count the votes • Hardware cost may even be lower – “Ordinary” hardware costs less than “special” – Though, printer/viewer has additional cost • Example system parts will be demoed
OUTLINE • Introduction • • WOTE and WEST Polling-place election background Receipt system introduction Educational example receipt system • Three example receipt systems • Comparison with non-receipt systems • Comments on Standardization
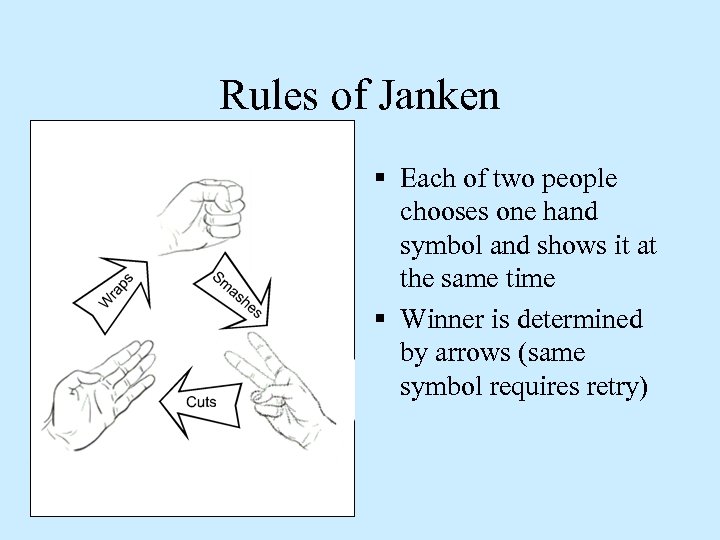
Rules of Janken § Each of two people chooses one hand symbol and shows it at the same time § Winner is determined by arrows (same symbol requires retry)
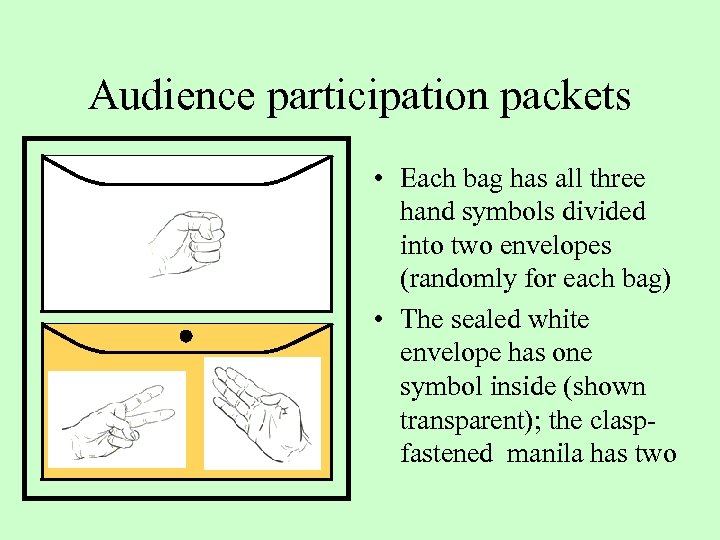
Audience participation packets • Each bag has all three hand symbols divided into two envelopes (randomly for each bag) • The sealed white envelope has one symbol inside (shown transparent); the claspfastened manila has two
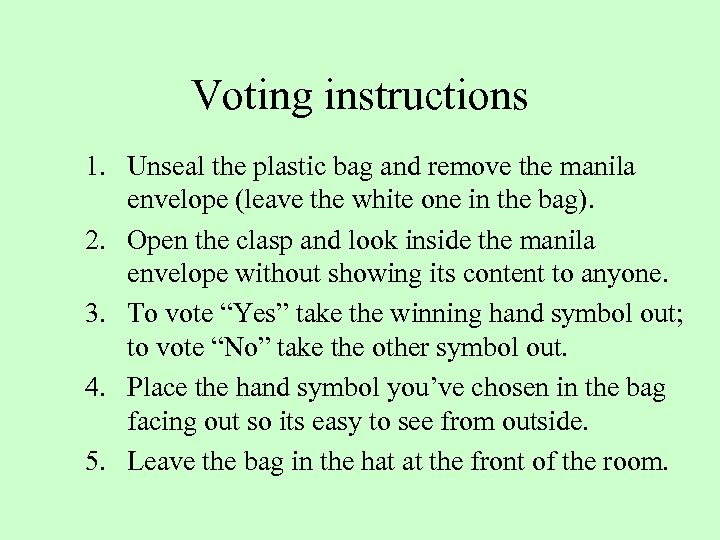
Voting instructions 1. Unseal the plastic bag and remove the manila envelope (leave the white one in the bag). 2. Open the clasp and look inside the manila envelope without showing its content to anyone. 3. To vote “Yes” take the winning hand symbol out; to vote “No” take the other symbol out. 4. Place the hand symbol you’ve chosen in the bag facing out so its easy to see from outside. 5. Leave the bag in the hat at the front of the room.
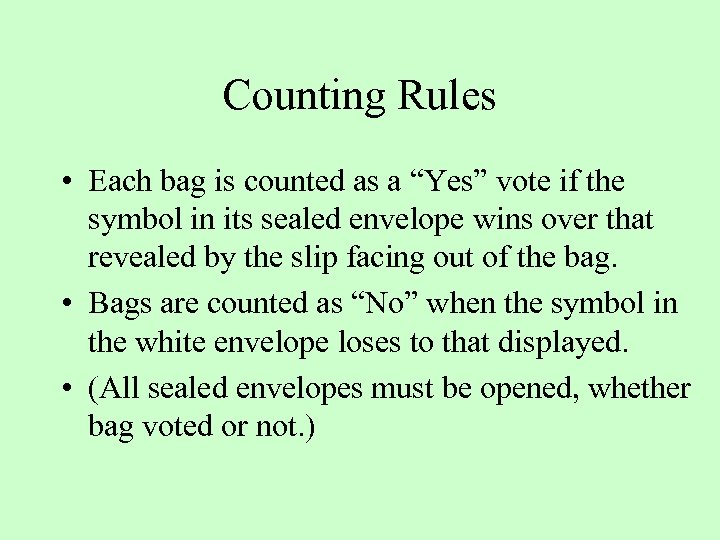
Counting Rules • Each bag is counted as a “Yes” vote if the symbol in its sealed envelope wins over that revealed by the slip facing out of the bag. • Bags are counted as “No” when the symbol in the white envelope loses to that displayed. • (All sealed envelopes must be opened, whether bag voted or not. )
Your vote was encrypted (neat thing #1) • • Everyone could see the symbol you chose Symbol encodes your vote Still, only you know how you voted! You have just used an “encrypted vote”
The dealer could not cheat (neat thing #2) • Each bag has two envelopes with correct number of slips—easy to see • No duplications per bag – Within envelope (voter sees) – Across envelopes (at count—depends on vote) • Distribution of “hands” uniform – Each hand should appear in sealed envelopes the same number of times
“Bulletin Board Voting”— Beyond the “room voting” model • “Not what they do, just what they post” • Applies to real polling place elections • Booths are watched to ensure the desired degree of ballot secrecy
OUTLINE • Introduction • Example receipt systems 1. High-registration systems 2. Subtractive optical systems 3. Additive optical systems • Overview of properties/mechanisms • Comparison with non-receipt systems • Comments on Standardization
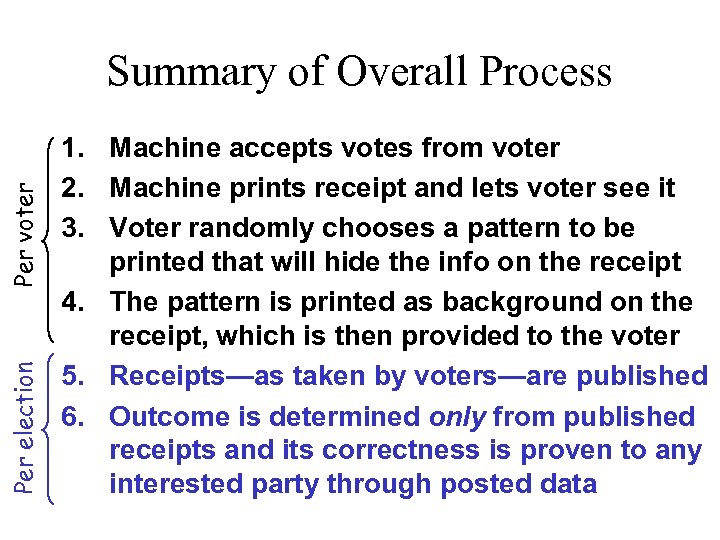
Per election Per voter Summary of Overall Process 1. Machine accepts votes from voter 2. Machine prints receipt and lets voter see it 3. Voter randomly chooses a pattern to be printed that will hide the info on the receipt 4. The pattern is printed as background on the receipt, which is then provided to the voter 5. Receipts—as taken by voters—are published 6. Outcome is determined only from published receipts and its correctness is proven to any interested party through posted data
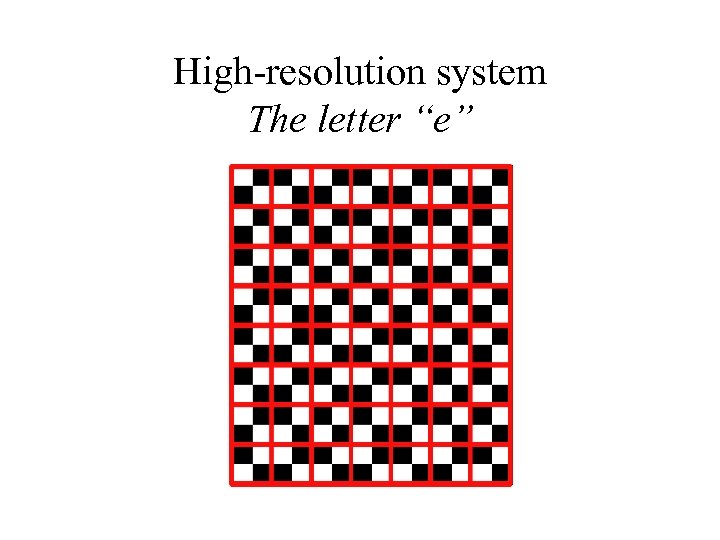
High-resolution system The letter “e”
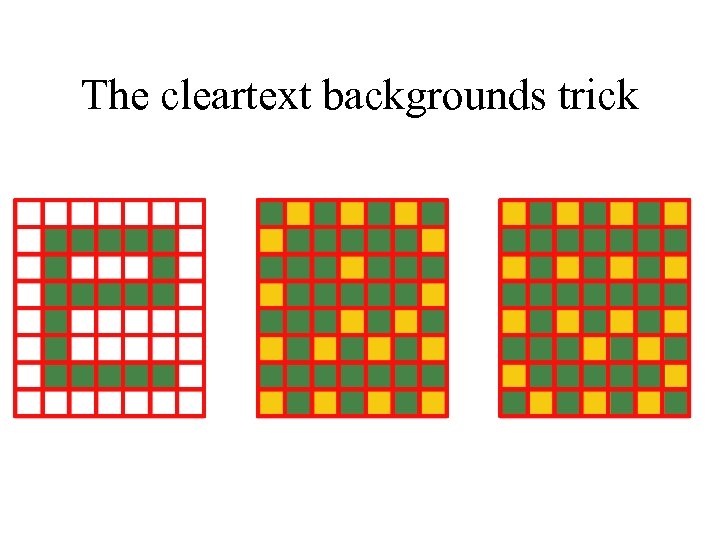
The cleartext backgrounds trick
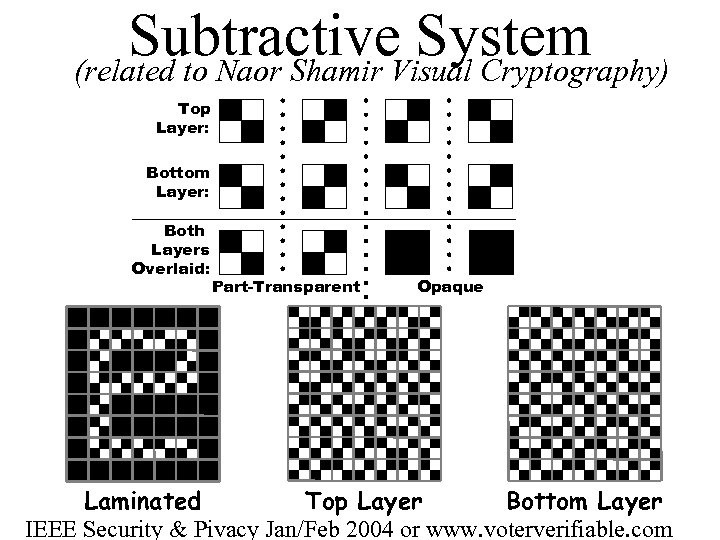
Subtractive. Visual Cryptography) System (related to Naor Shamir Top Layer: Bottom Layer: Both Layers Overlaid: Part-Transparent Opaque Laminated Top Layer Bottom Layer IEEE Security & Pivacy Jan/Feb 2004 or www. voterverifiable. com
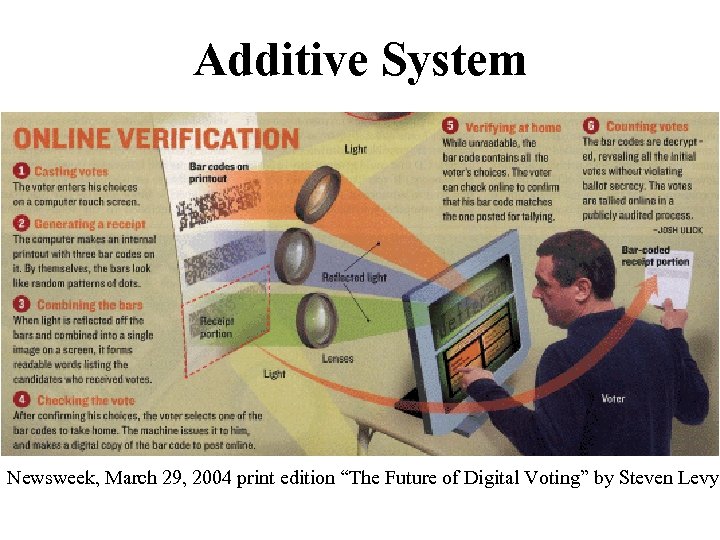
Additive System Newsweek, March 29, 2004 print edition “The Future of Digital Voting” by Steven Levy
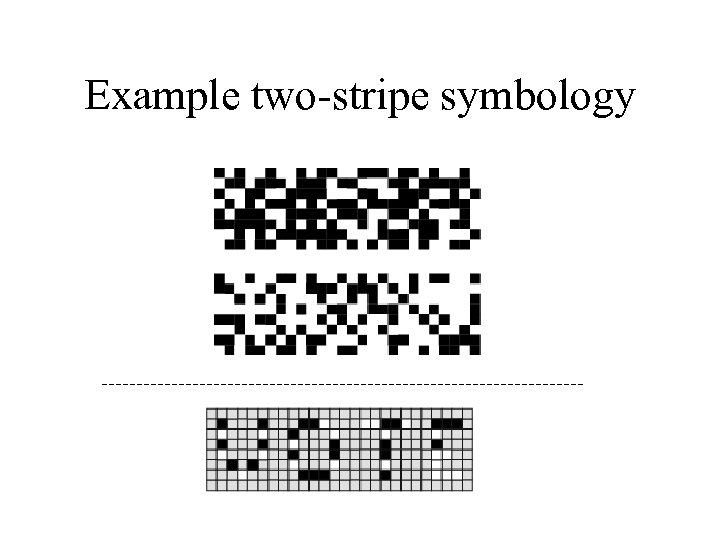
Example two-stripe symbology
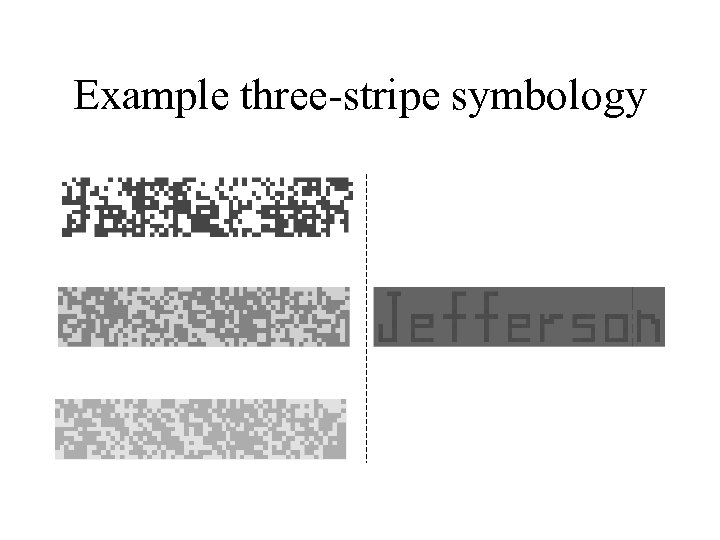
Example three-stripe symbology
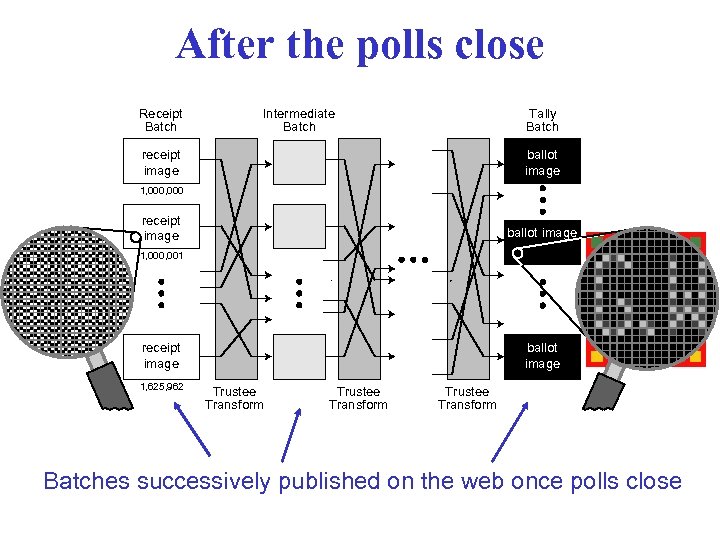
After the polls close Receipt Batch Intermediate Batch Tally Batch receipt image ballot image 1, 000, 001 receipt image 1, 625, 962 ballot image Trustee Transform Batches successively published on the web once polls close
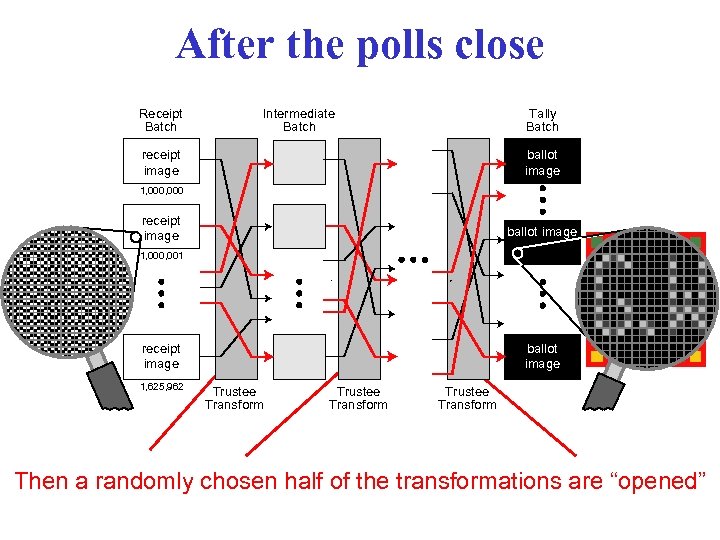
After the polls close Receipt Batch Intermediate Batch Tally Batch receipt image ballot image 1, 000, 001 receipt image 1, 625, 962 ballot image Trustee Transform Then a randomly chosen half of the transformations are “opened”

Introducing the properties (proofs in the paper at www. voterverifiable. com)
![Properties [1 of 4] • If your receipt is properly posted, you can be Properties [1 of 4] • If your receipt is properly posted, you can be](https://present5.com/presentation/e0b2272804ffd74be26ff6f0933b8343/image-33.jpg)
Properties [1 of 4] • If your receipt is properly posted, you can be sure that your vote is included in the final tally [see also property 3] • If your receipt is not properly posted, you should be able to demonstrate this (because it should have document security attributes including a digital signature)
![Properties [2 of 4] • No matter how incorrectly a system operates, there are Properties [2 of 4] • No matter how incorrectly a system operates, there are](https://present5.com/presentation/e0b2272804ffd74be26ff6f0933b8343/image-34.jpg)
Properties [2 of 4] • No matter how incorrectly a system operates, there are only two ways it can change a correctly-posted ballot without being detected: – printing text from a guessed pattern and hoping that the voter chooses that pattern; or – incorrectly performing a step among the tally process steps and hoping that this step is not among the half selected for audit.
![Properties [3 of 4] Changing n ballots means: • Chance that no cheating is Properties [3 of 4] Changing n ballots means: • Chance that no cheating is](https://present5.com/presentation/e0b2272804ffd74be26ff6f0933b8343/image-35.jpg)
Properties [3 of 4] Changing n ballots means: • Chance that no cheating is detected is at most 1/2 n • Chance of getting caught cheating is at least 1– 1/2 n
![Properties [4 of 4] • Your receipt cannot be decrypted by anyone, or otherwise Properties [4 of 4] • Your receipt cannot be decrypted by anyone, or otherwise](https://present5.com/presentation/e0b2272804ffd74be26ff6f0933b8343/image-36.jpg)
Properties [4 of 4] • Your receipt cannot be decrypted by anyone, or otherwise linked to your vote [more later], except by decrypting with (or breaking) sufficiently many secret keys (of which each trustee has its own).
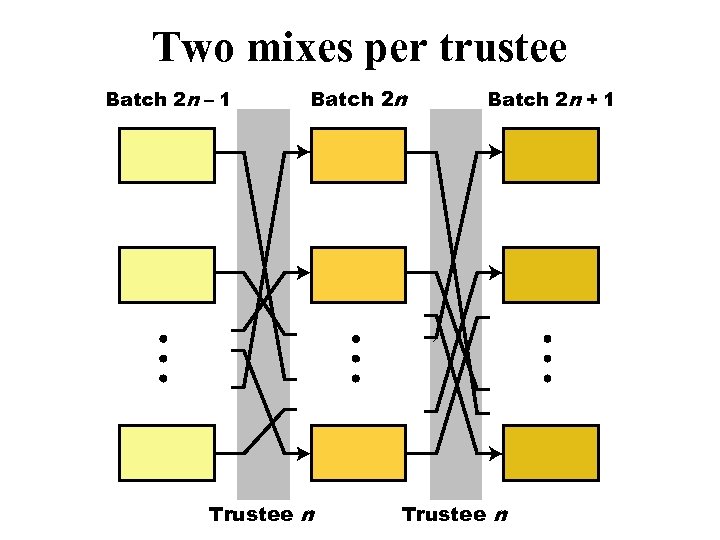
Two mixes per trustee Batch 2 n – 1 Batch 2 n Trustee n Batch 2 n + 1 Trustee n
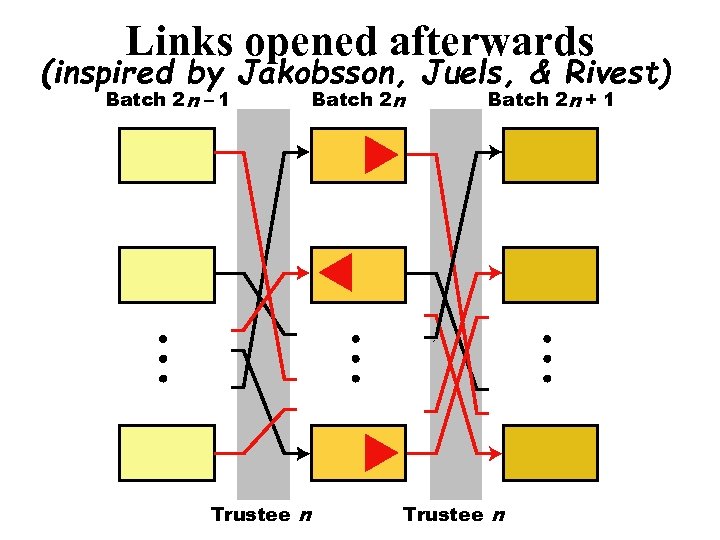
Links opened afterwards (inspired by Jakobsson, Juels, & Rivest) Batch 2 n – 1 Trustee n Batch 2 n + 1 Trustee n
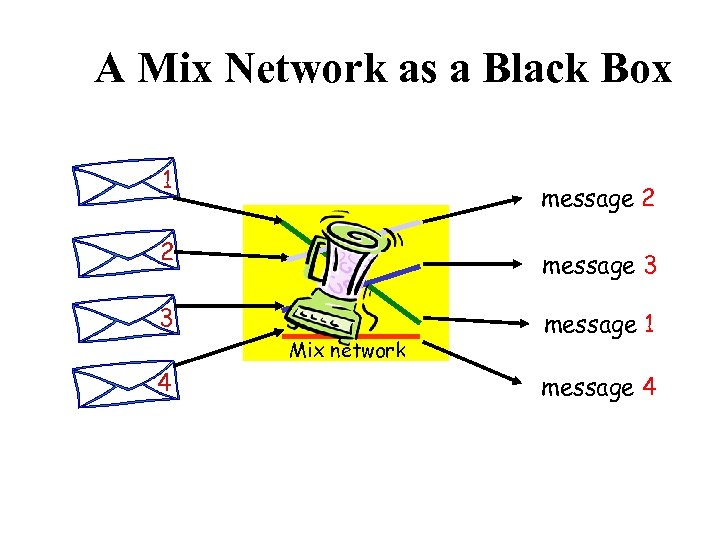
A Mix Network as a Black Box 1 message 2 2 message 3 3 Mix network 4 message 1 message 4
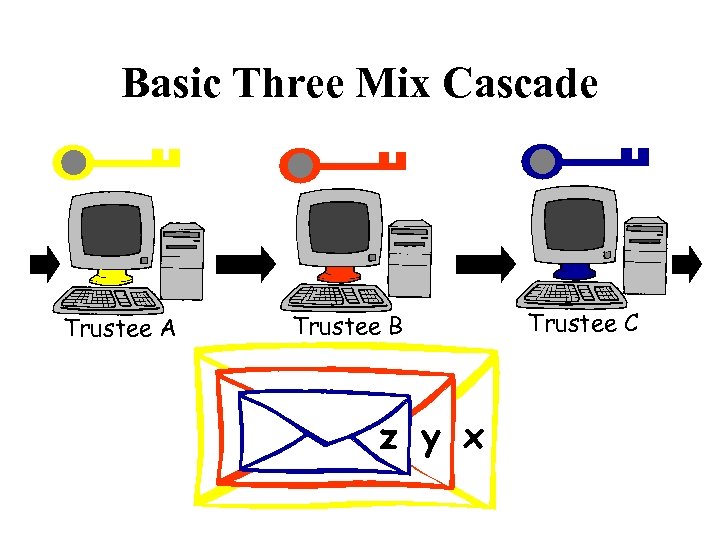
Basic Three Mix Cascade Trustee A Trustee B z y x Trustee C
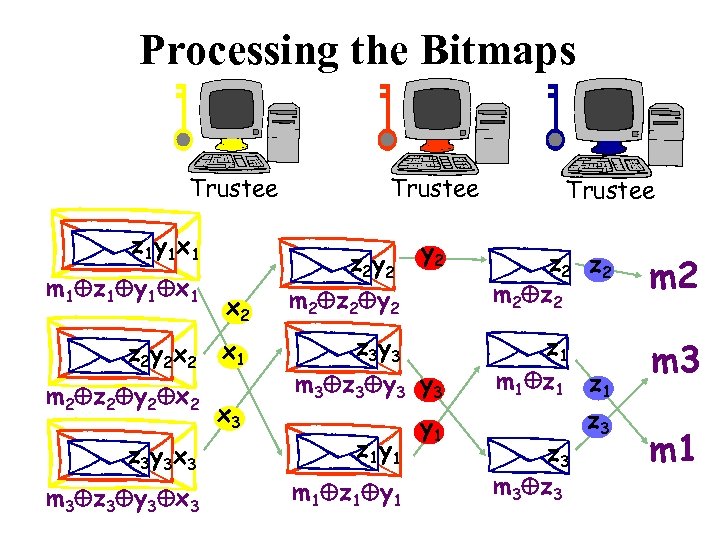
Processing the Bitmaps Trustee z 1 y 1 x 1 m 1 z 1 y 1 x 1 z 2 y 2 x 2 m 2 z 2 y 2 x 2 z 3 y 3 x 3 m 3 z 3 y 3 x 3 Trustee y 2 x 2 m 2 z 2 y 2 z 2 m 2 x 1 z 3 y 3 m 3 z 3 y 3 z 1 m 1 z 1 m 3 z 2 y 2 x 3 z 1 y 1 m 1 z 1 y 1 z 3 m 3 z 3 m 1
OUTLINE • Introduction • Example receipt systems • Comparison with non-receipt systems – Four classes of non-receipt systems – Table of properties: Integrity, Privacy, Secrecy, Robustness and Costs – Additional features/properties • Comments on Standardization
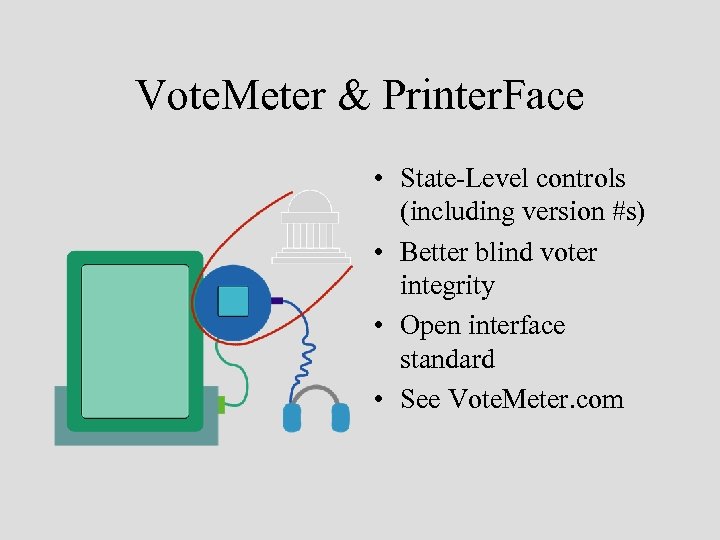
Vote. Meter & Printer. Face • State-Level controls (including version #s) • Better blind voter integrity • Open interface standard • See Vote. Meter. com
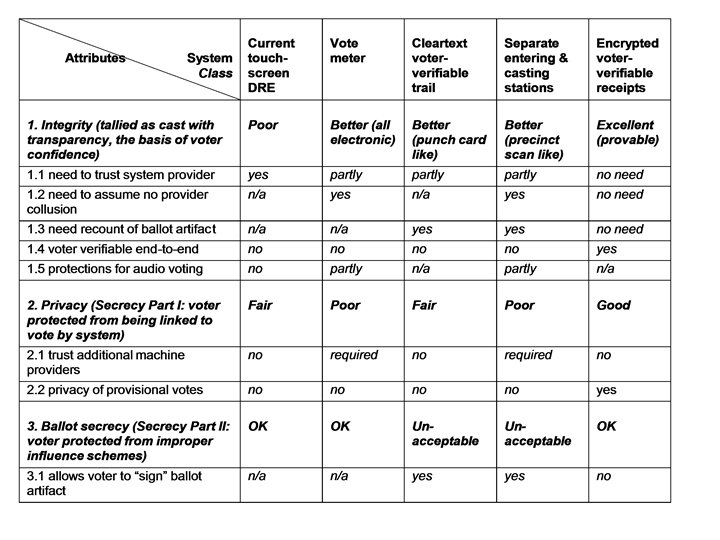
Other aspects for comparsion 1. 2. 3. 4. Adjudicating which ballots to count Reliably capturing voter intent Preventing Ballot-style fraud Creating/repairing voter confidence
OUTLINE • • Introduction Example receipt systems Comparison with non-receipt systems Comments on Standardization
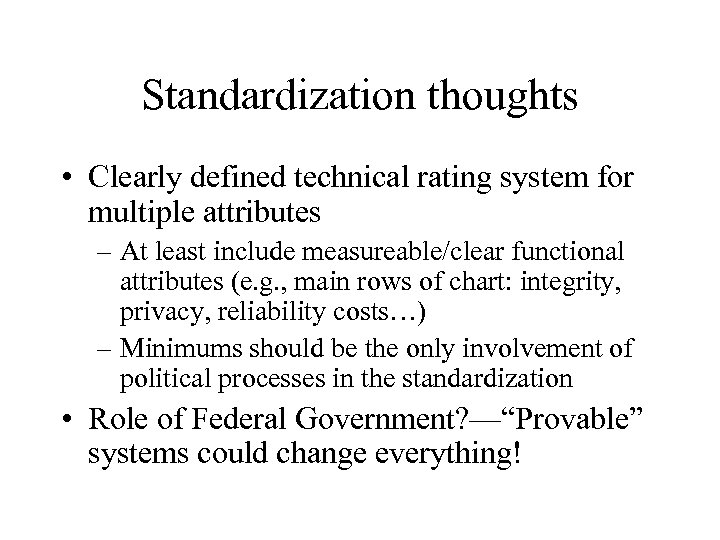
Standardization thoughts • Clearly defined technical rating system for multiple attributes – At least include measureable/clear functional attributes (e. g. , main rows of chart: integrity, privacy, reliability costs…) – Minimums should be the only involvement of political processes in the standardization • Role of Federal Government? —“Provable” systems could change everything!
Conclusion
e0b2272804ffd74be26ff6f0933b8343.ppt