d3d6ab2c913362730860e641368b29c3.ppt
- Количество слайдов: 25
SEARCH ENGINES, ADVERTISING, Web Transaction Logs Cookies, web bugs, payment systems
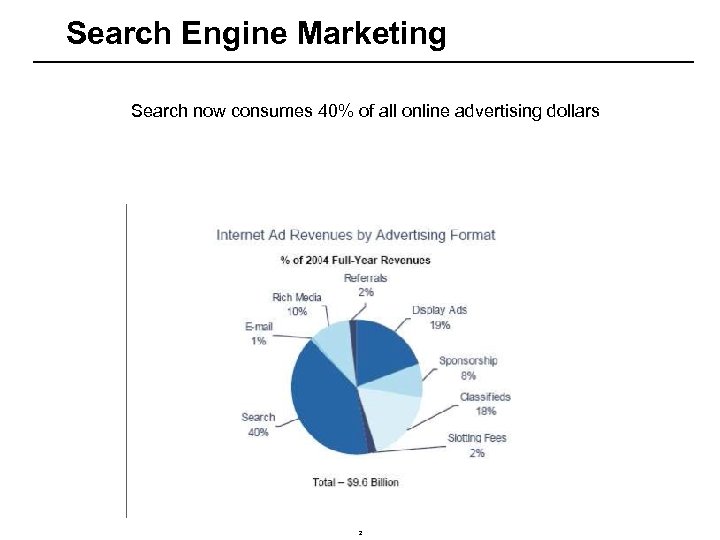
Search Engine Marketing Search now consumes 40% of all online advertising dollars 2
Why Search engine marketing --Whether you are shopping for a car, shoes, gift, or doing research for class, you are likely to start with Google, Yahoo, MSN or Ask Jeeves. --Research shows that unless you have a destination in mind and know the URL, you are likely to use a search engine
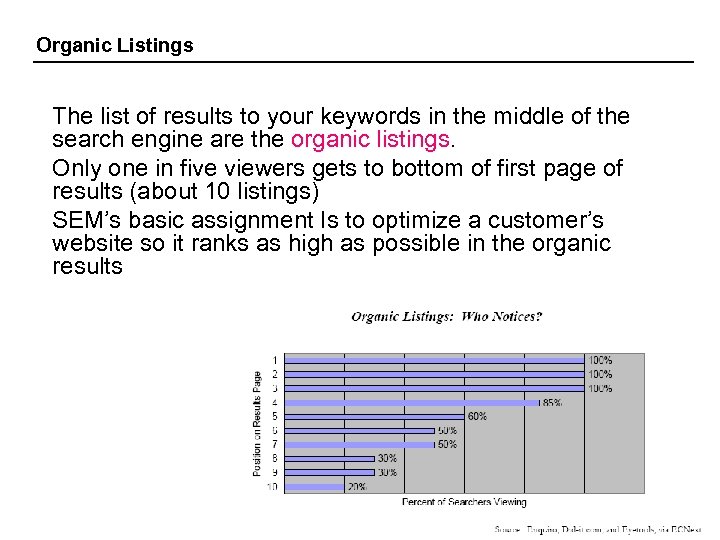
Organic Listings The list of results to your keywords in the middle of the search engine are the organic listings. Only one in five viewers gets to bottom of first page of results (about 10 listings) SEM’s basic assignment Is to optimize a customer’s website so it ranks as high as possible in the organic results

Paid ads Alongside or above or below the organic results are the paid ads. The typical user is far less likely to click on those. However, for these, ranking is even more important
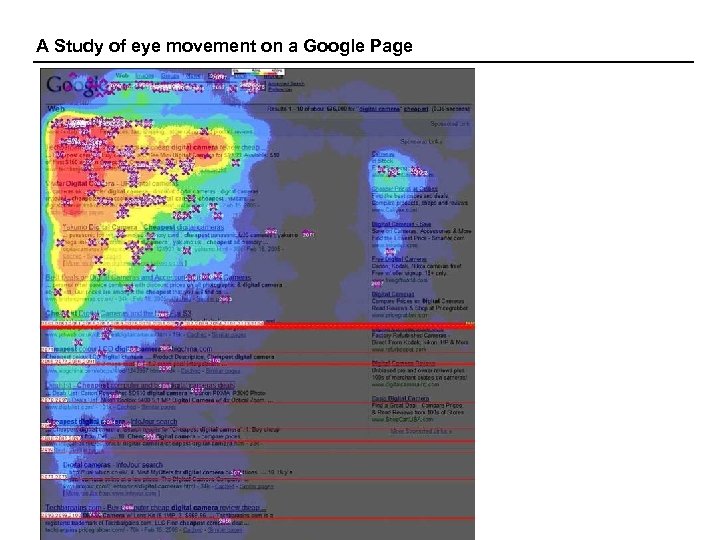
A Study of eye movement on a Google Page
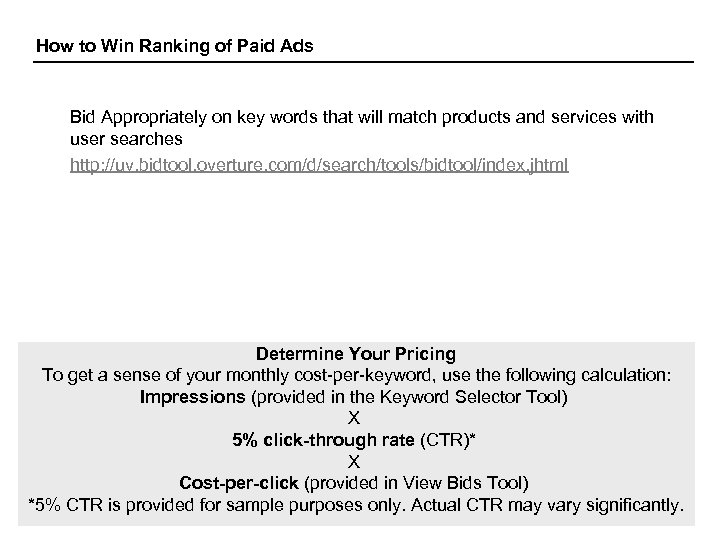
How to Win Ranking of Paid Ads Bid Appropriately on key words that will match products and services with user searches http: //uv. bidtool. overture. com/d/search/tools/bidtool/index. jhtml Determine Your Pricing To get a sense of your monthly cost-per-keyword, use the following calculation: Impressions (provided in the Keyword Selector Tool) X 5% click-through rate (CTR)* X Cost-per-click (provided in View Bids Tool) *5% CTR is provided for sample purposes only. Actual CTR may vary significantly.
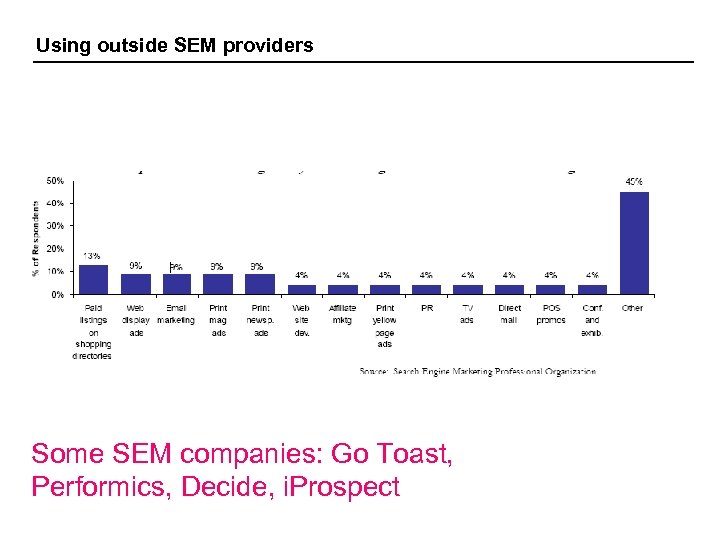
Using outside SEM providers Some SEM companies: Go Toast, Performics, Decide, i. Prospect
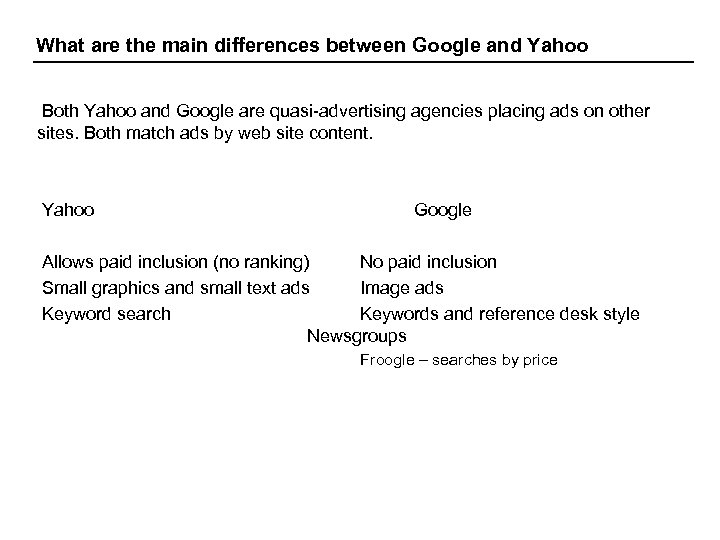
What are the main differences between Google and Yahoo Both Yahoo and Google are quasi-advertising agencies placing ads on other sites. Both match ads by web site content. Yahoo Google Allows paid inclusion (no ranking) No paid inclusion Small graphics and small text ads Image ads Keyword search Keywords and reference desk style Newsgroups Froogle – searches by price
Google Ad. Sense offers two ways for you to earn money: 1. Targeted advertising for your content pages 2. Google search box to your site and show targeted ads on search results pages. When visitors click on these ads, Google pays you. The Google ads you are able to display on your content pages and Ad. Sense for search results pages are cost-per-click (CPC) ads. This means that advertisers pay only when users click on ads. You'll receive a portion of the amount paid for clicks on Google ads on your website (amount not disclosed).
How much will I get/pay for a Google Ad https: //adwords. google. com/select/
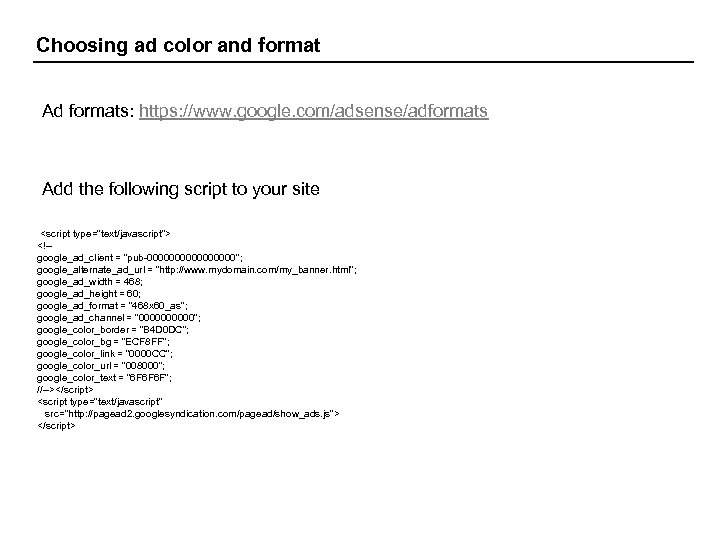
Choosing ad color and format Ad formats: https: //www. google. com/adsense/adformats Add the following script to your site <script type="text/javascript"> <!-- google_ad_client = "pub-00000000"; google_alternate_ad_url = "http: //www. mydomain. com/my_banner. html"; google_ad_width = 468; google_ad_height = 60; google_ad_format = "468 x 60_as"; google_ad_channel = "00000"; google_color_border = "B 4 D 0 DC"; google_color_bg = "ECF 8 FF"; google_color_link = "0000 CC"; google_color_url = "008000"; google_color_text = "6 F 6 F 6 F"; //--></script> <script type="text/javascript" src="http: //pagead 2. googlesyndication. com/pagead/show_ads. js"> </script>
Google Ad. Sense: Tips 1. Show your ads above the fold (the section of your page that is visible without scrolling). 2. Try different ad formats. 3. Customize ad color combinations. Try using custom color combinations for your ad units. This allows you to ensure that the text, background, and border colors of your ads complement your website. l Background color of the ad similar to the background color of your page. l The border of the ad a color that is prominent on your page. 4. Allow the Google bot to access your site content. If you have a robots. txt file, remove the file. 6. Filter out ads you don't want displayed on your site. From within the Settings section of your account, Ad. Sense gives you the ability to create a URL filter list. 6. Place Ad. Sense ads on text-rich pages. Only text is used to determine a page's content. 7. Create pages that are simple and clean. People typically skim a website for less than a minute. Ensure that visitors to your site can find what they are looking for and are not overloaded with clutter.
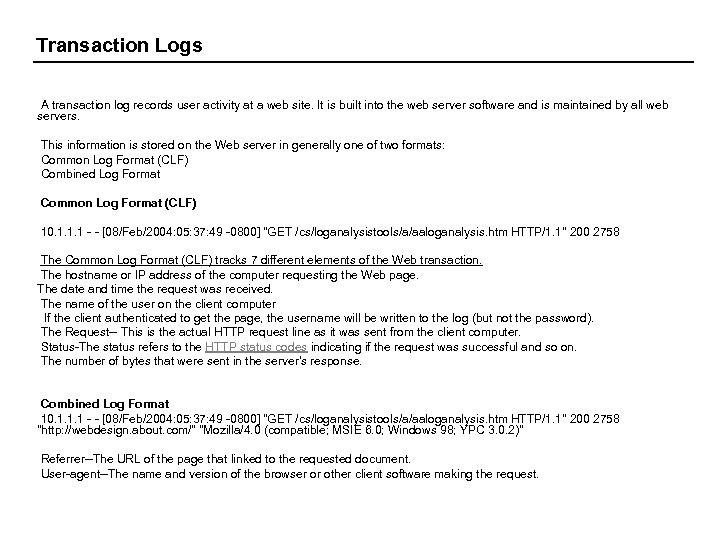
Transaction Logs A transaction log records user activity at a web site. It is built into the web server software and is maintained by all web servers. This information is stored on the Web server in generally one of two formats: Common Log Format (CLF) Combined Log Format Common Log Format (CLF) 10. 1. 1. 1 - - [08/Feb/2004: 05: 37: 49 -0800] "GET /cs/loganalysistools/a/aaloganalysis. htm HTTP/1. 1" 200 2758 The Common Log Format (CLF) tracks 7 different elements of the Web transaction. The hostname or IP address of the computer requesting the Web page. The date and time the request was received. The name of the user on the client computer If the client authenticated to get the page, the username will be written to the log (but not the password). The Request-- This is the actual HTTP request line as it was sent from the client computer. Status-The status refers to the HTTP status codes indicating if the request was successful and so on. The number of bytes that were sent in the server's response. Combined Log Format 10. 1. 1. 1 - - [08/Feb/2004: 05: 37: 49 -0800] "GET /cs/loganalysistools/a/aaloganalysis. htm HTTP/1. 1" 200 2758 "http: //webdesign. about. com/" "Mozilla/4. 0 (compatible; MSIE 6. 0; Windows 98; YPC 3. 0. 2)" Referrer--The URL of the page that linked to the requested document. User-agent--The name and version of the browser or other client software making the request.
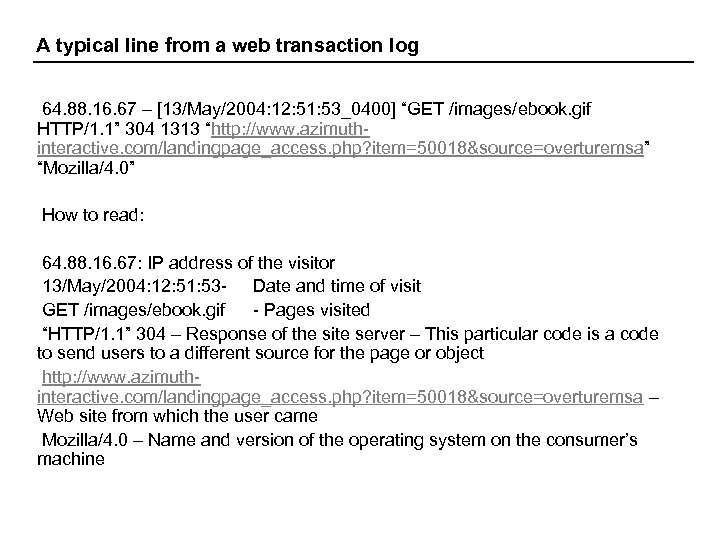
A typical line from a web transaction log 64. 88. 16. 67 – [13/May/2004: 12: 51: 53_0400] “GET /images/ebook. gif HTTP/1. 1” 304 1313 “http: //www. azimuthinteractive. com/landingpage_access. php? item=50018&source=overturemsa” “Mozilla/4. 0” How to read: 64. 88. 16. 67: IP address of the visitor 13/May/2004: 12: 51: 53 - Date and time of visit GET /images/ebook. gif - Pages visited “HTTP/1. 1” 304 – Response of the site server – This particular code is a code to send users to a different source for the page or object http: //www. azimuthinteractive. com/landingpage_access. php? item=50018&source=overturemsa – Web site from which the user came Mozilla/4. 0 – Name and version of the operating system on the consumer’s machine
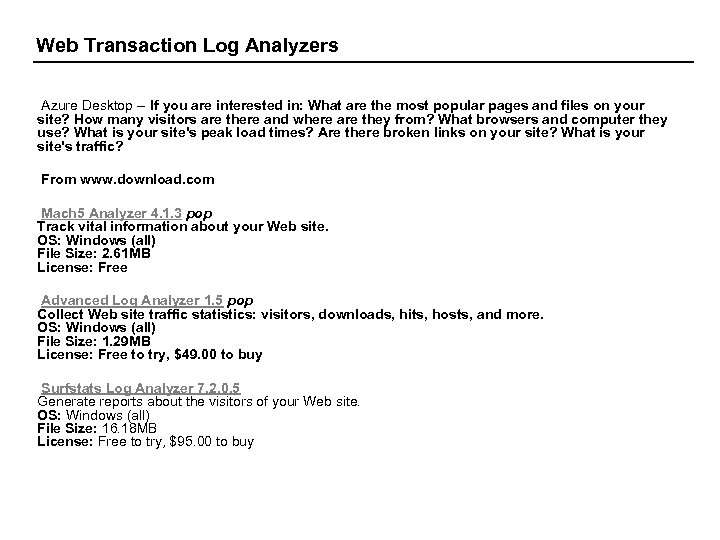
Web Transaction Log Analyzers Azure Desktop -- If you are interested in: What are the most popular pages and files on your site? How many visitors are there and where are they from? What browsers and computer they use? What is your site's peak load times? Are there broken links on your site? What is your site's traffic? From www. download. com Mach 5 Analyzer 4. 1. 3 pop Track vital information about your Web site. OS: Windows (all) File Size: 2. 61 MB License: Free Advanced Log Analyzer 1. 5 pop Collect Web site traffic statistics: visitors, downloads, hits, hosts, and more. OS: Windows (all) File Size: 1. 29 MB License: Free to try, $49. 00 to buy Surfstats Log Analyzer 7. 2. 0. 5 Generate reports about the visitors of your Web site. OS: Windows (all) File Size: 16. 18 MB License: Free to try, $95. 00 to buy
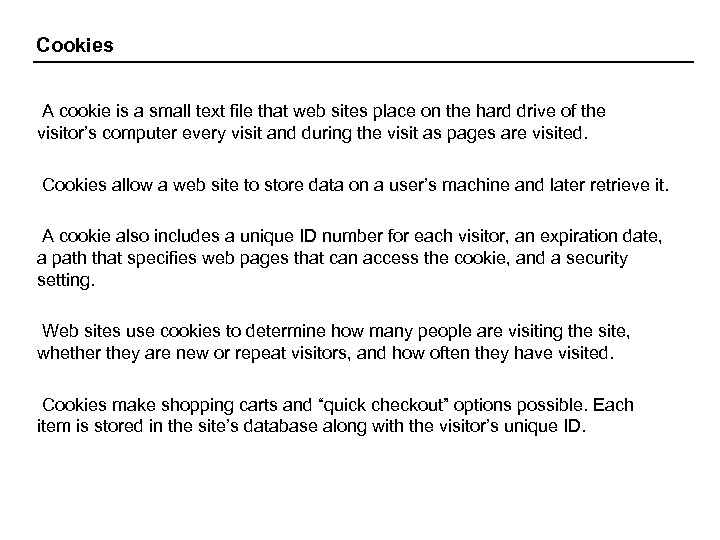
Cookies A cookie is a small text file that web sites place on the hard drive of the visitor’s computer every visit and during the visit as pages are visited. Cookies allow a web site to store data on a user’s machine and later retrieve it. A cookie also includes a unique ID number for each visitor, an expiration date, a path that specifies web pages that can access the cookie, and a security setting. Web sites use cookies to determine how many people are visiting the site, whether they are new or repeat visitors, and how often they have visited. Cookies make shopping carts and “quick checkout” options possible. Each item is stored in the site’s database along with the visitor’s unique ID.
Web bugs are tiny graphic files embedded in email messages and on web sites. Web bugs are used to automatically transmit information about the user and the page being viewed to a monitoring server. When a recipient opens an email in HTML format, a message is sent to a server calling for graphics information. This tells you that the message was opened and so the recipient is interested.
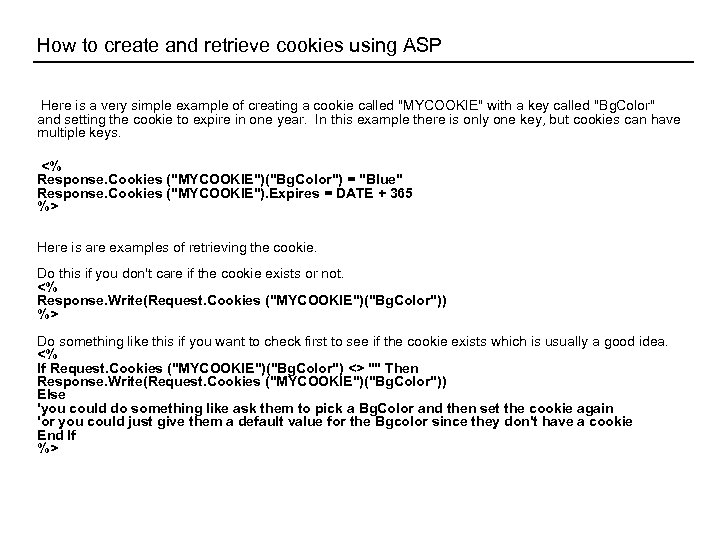
How to create and retrieve cookies using ASP Here is a very simple example of creating a cookie called "MYCOOKIE" with a key called "Bg. Color" and setting the cookie to expire in one year. In this example there is only one key, but cookies can have multiple keys. <% Response. Cookies ("MYCOOKIE")("Bg. Color") = "Blue" Response. Cookies ("MYCOOKIE"). Expires = DATE + 365 %> Here is are examples of retrieving the cookie. Do this if you don't care if the cookie exists or not. <% Response. Write(Request. Cookies ("MYCOOKIE")("Bg. Color")) %> Do something like this if you want to check first to see if the cookie exists which is usually a good idea. <% If Request. Cookies ("MYCOOKIE")("Bg. Color") <> "" Then Response. Write(Request. Cookies ("MYCOOKIE")("Bg. Color")) Else 'you could do something like ask them to pick a Bg. Color and then set the cookie again 'or you could just give them a default value for the Bgcolor since they don't have a cookie End If %>

Payment Systems Credit Cards – The difference between a credit card transaction online and offline is that online merchants never see the actual credit card, no card impression is taken, and no signature is available– high potential for dispute (even if the user has downloaded the product). Secure Sockets Layer (SSL)– Using encryption, SSL secures the session and protects the information from hackers. SSL does not authenticate either merchant or buyer. They have to trust each other. Veri. Sign – an Internet payment service provider. Veri. Sign will help you secure an account with one of its merchant account provider partners and then provide payment processing software for installation on your server. The software collects the transaction information from your site and then routes it via Veri. Sign to the appropriate bank, ensuring the funds are authorized. The funds are then transferred to your merchant account.
Limitations of Online Credit Card Systems Security for consumer, merchant risk, and cost. Cost of transaction – 3. 5% of the purchase plus 20 -30 cents per transaction, plus set-up fees. High costs make it undesirable to sell goods that cost less than $10 on the web. Solution: Aggregate purchases over time before charging (e. g. , Apple i. Tunes Music Store, 99 cents a song, Real. com).
Peer-to-Peer Payment Systmes Pay. Pal Yahoo Pay. Direct Money. Zap (Western Union)
TEENS? The average teen spends $85 to $100 a week on clothing, CDs, books, toys, etc. Most teens don’t have a credit card even though 80% of them are online. Rocketcash. com is a site that enables teens to buy products online through an online account. Parents and teens can deposit money in a Rocket. Cash account which functions like a credit card and is accepted at numerous sites. As of 2003, Rocket. Cash had signed up close to 2. 5 million customers. Rocket. Cash was purchased in 2002 by the Coca Cola company, which uses the functionality of Rocket. Cash to promote youth-oriented consumer products. Commissions of 5% to 15% plus fees for helping develop incentive programs with merchants.
China? 80 Million internet users Problems: Currency conversion Credit cards not widely used Alternatives: Courier Payments Mail Payments Local Debit Card (issued by local Chinese banks) Local Credit Card (issued by local Chinese banks) Bank Transfer (Consumers transfer funds from their bank account to a service) Cash over the Counter -- pay by cash for online purchases at local bank branches.

Established China payment sites Billto. Bill provides an end to end transaction service enabling websites to sell in China using a variety of online and offline payment services. Strategic partnerships with banking and local payment providers. Currency conversion. http: //www. billtobill. com/ Easecard is a prepaid card distributed widely in China by Guangzhou Icarus Network Technologies Co. , Ltd. Easecard is helping revolutionize Internet purchasing in China by creating an easy to use, secure, and anonymous payment platform Western Union Quick. Pay™ Customers worldwide can elect to use Western Union Quick. Pay and transfer their payment within 1 -3 hours.
d3d6ab2c913362730860e641368b29c3.ppt