864906df9f55ca6e9bf40de38df523d9.ppt
- Количество слайдов: 64
Remote Access
Objectives • Secure Remote Access • Harden File Transfer Protocol (FTP) • Protect Directory Services cs 490 ns-cotter 2
Remote Access – into Linux • vnc – (Virtual Network Connection) – vnc-server (Fedora / Cent. OS) – tigervnc-server • • Establish password for communications Decide which ports to use (multiple channels available) Channel 0 = 5900; channel 1 = 5901, etc. Start service “vncserver : 1” – vnc clients • Linux: vncviewer • Windows: tight. VNC, ultra. VNC, etc.
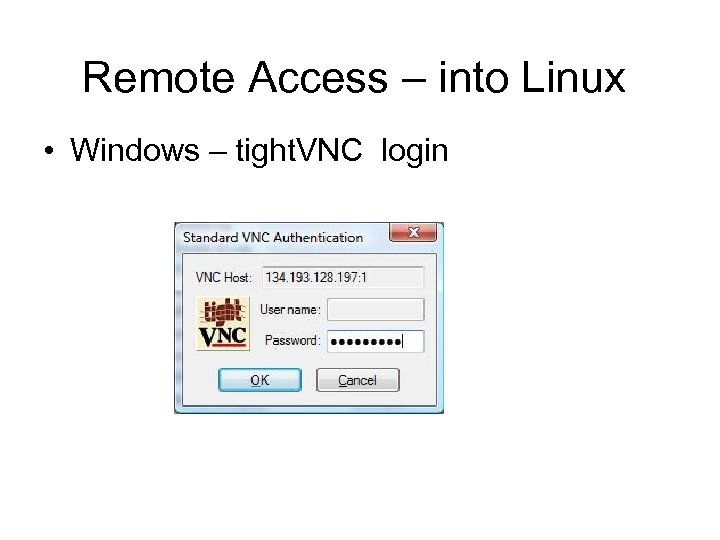
Remote Access – into Linux • Windows – tight. VNC login
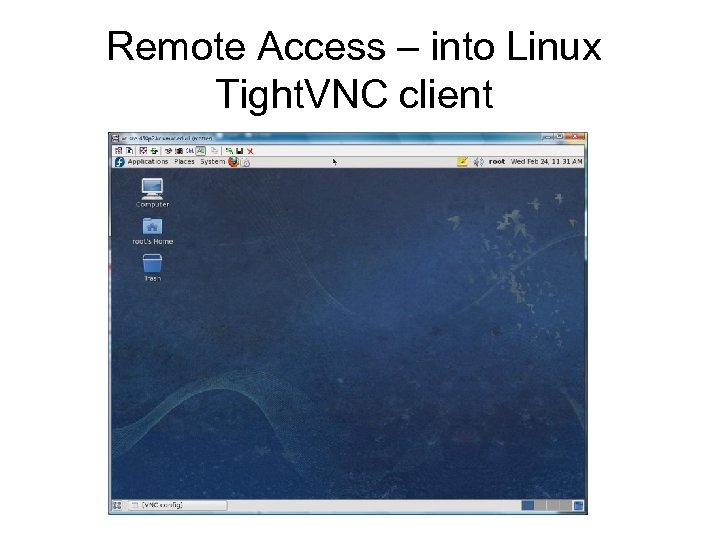
Remote Access – into Linux Tight. VNC client
Remote Access – into Linux • no. Machine nx – nx server available from No. Machine. com • Uses SSH for data transport • Runs on port 7100, but all data goes through SSH (22) • Uses SSH login (regular user) – Nx clients • Linux • Windows
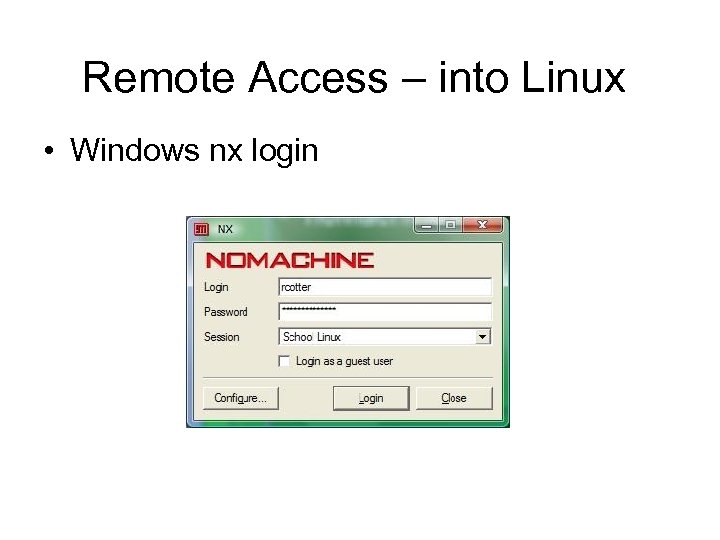
Remote Access – into Linux • Windows nx login
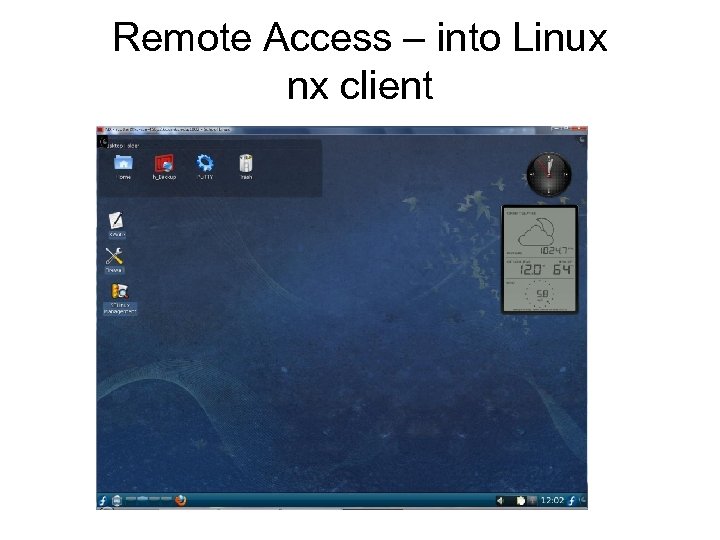
Remote Access – into Linux nx client
Secure Remote Access • Windows NT includes User Manager to allow dial-in access, while Windows 2003 uses Computer Management for Workgroup access and Active Directory for configuring access to the domain • Windows XP, 2003 Remote Access Policies can lock down a remote access system to ensure that only those intended to have access are actually granted it cs 490 ns-cotter 9
Secure Remote Access • Linux – Remote access is not part of the kernel. Available as support programs. – Unsecured – telnet, ftp – Secured – SSH, Pu. TTY, etc. cs 490 ns-cotter 10
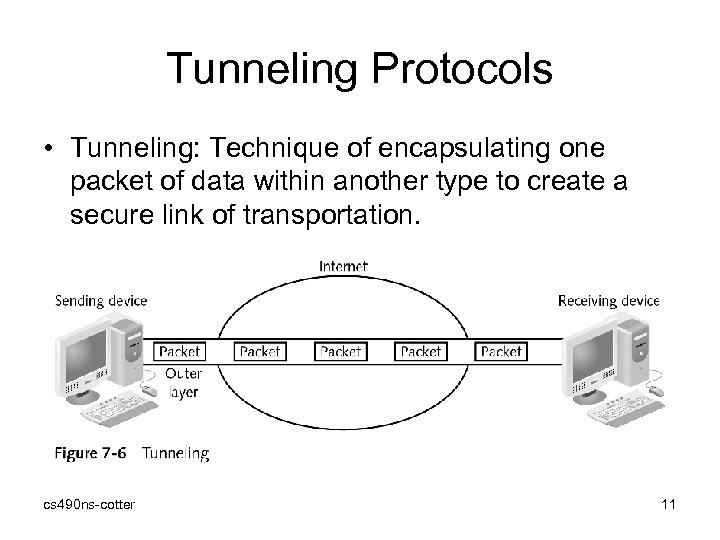
Tunneling Protocols • Tunneling: Technique of encapsulating one packet of data within another type to create a secure link of transportation. cs 490 ns-cotter 11
Secure Transmission Protocols • PPTP and other similar protocols provide a secure mechanism for preventing eavesdroppers from viewing transmissions • PPTP derived from Point-to-Point Protocol cs 490 ns-cotter 12
Point-to-Point Protocol • Initially designed to support serial connections (modems) to the Internet – Standard serial port provides only layer 1 protocol support (no layer 2 – data link) – PPP (and the earlier Serial Line Internet Protocol) were designed as a layer 2 protocol that can carry IP datagrams through a serial (modem) connection. • Functions: – – Encapsulation Link Control Protocol Authentication Network Control Protocols cs 490 ns-cotter 13
Point-to-Point Tunneling Protocol (PPTP) • Widely deployed tunneling protocol • Developed by Microsoft • Based on the Point-to-Point Protocol (PPP) • Client connects to a network access server (NAS) to initiate connection • Extension to PPTP is Link Control Protocol (LCP), which establishes, configures, and tests the connection cs 490 ns-cotter 14
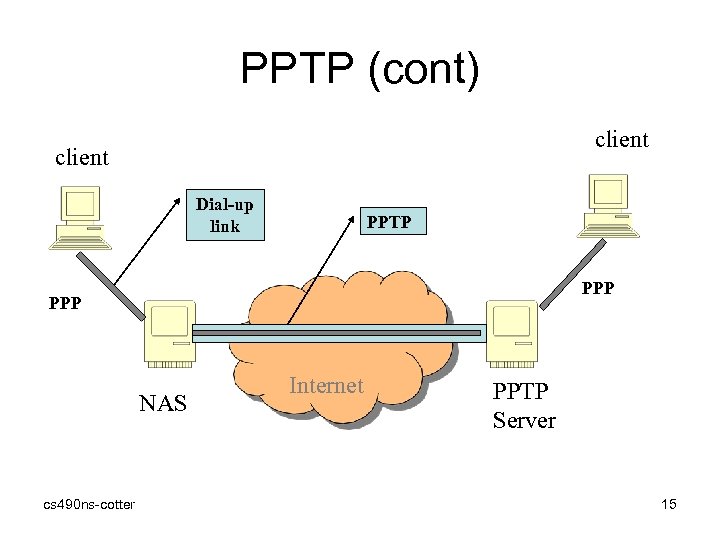
PPTP (cont) client Dial-up link PPTP PPP NAS cs 490 ns-cotter Internet PPTP Server 15
PPTP (cont) • Used to encapsulate network protocols over a TCP/IP network – Used to carry PPP (which can encapsulate IP, IPX, Net BEUI, etc. ) – Control messages • Manages VPN connections – Supports Authentication, Encryption – Data packets cs 490 ns-cotter 16
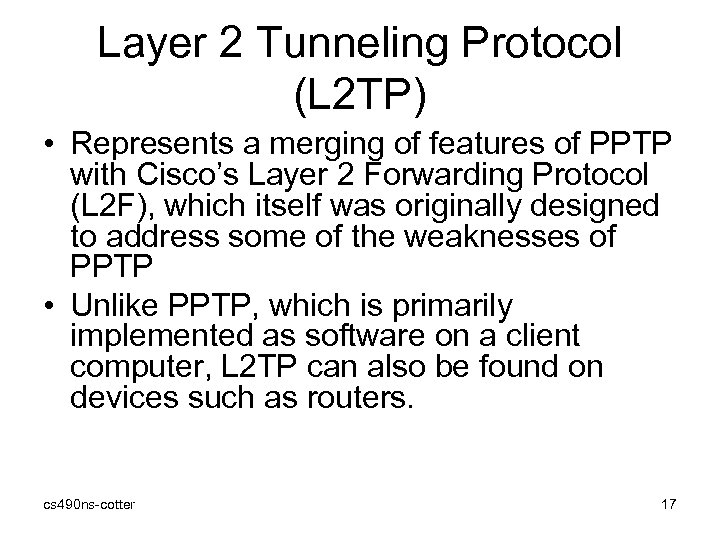
Layer 2 Tunneling Protocol (L 2 TP) • Represents a merging of features of PPTP with Cisco’s Layer 2 Forwarding Protocol (L 2 F), which itself was originally designed to address some of the weaknesses of PPTP • Unlike PPTP, which is primarily implemented as software on a client computer, L 2 TP can also be found on devices such as routers. cs 490 ns-cotter 17
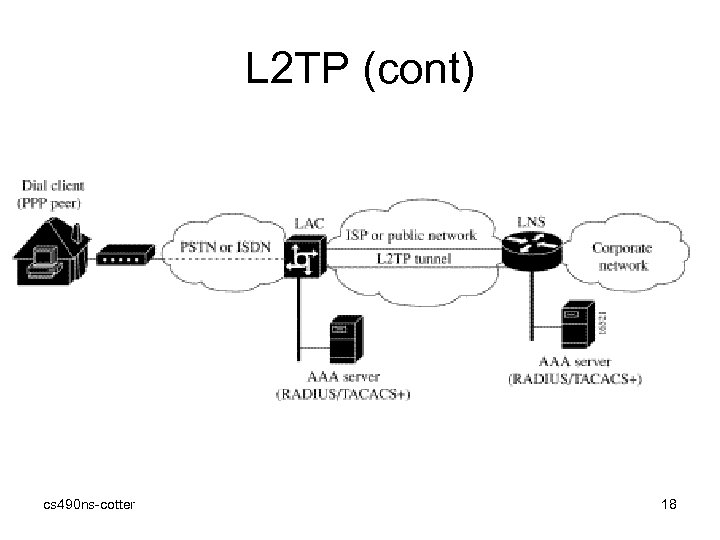
L 2 TP (cont) cs 490 ns-cotter 18
L 2 TP (cont) 1. User initiates a PPP connection to the ISP, using the analog telephone system or ISDN. 2. The ISP network L 2 TP Access Concentrator (LAC) accepts the connection at the POP and the PPP link is established. 3. After the end user and the L 2 TP Network Server (LNS) negotiate Link protocol, the LAC partially authenticates the end user with CHAP or PAP. If the user is not a Virtual Private dialup Network (VPDN) client, authentication continues, and the client will access the Internet or other contacted service. If the username is a VPDN client, the mapping will name a specific endpoint (the LNS). 4. The tunnel end points, the LAC and the LNS, authenticate each other before any sessions are attempted within a tunnel. Alternatively, the LNS can accept tunnel creation without any tunnel authentication of the LAC. 5. Once the tunnel exists, an L 2 TP session is created for the end user. 6. The LAC will propagate the LCP negotiated options and the partially authenticated CHAP/PAP information to the LNS. The LNS will funnel the negotiated options and authentication information directly to the virtual access interface. If the options configured on the virtual template interface does not match the negotiated options with the LAC, the connection will fail, and a disconnect is sent to the LAC. cs 490 ns-cotter 19
PPPo. E: PPP over Ethernet • Point to Point Protocol over Ethernet • RFC 2516 • Only Ethernet Framing and MAC address are relevant (Nothing from CSMA/CD protocol!) • Ability to connect a collection of hosts over a simple bridging access device to a remote access concentrator • Access control, billing and Type of service: on a per user basis • Each PPP session learns Ethernet address of remote peer with a unique session identifier cs 490 ns-cotter 20
PPPo. E: cont’d • Revisit Ethernet Frame – Dest. Addr | Source. Addr | Ether_type | Payload | Checksum • Dest. Addr, Source. Addr: 6 byte MAC address (universally unique) • Ether_type: 2 bytes • Payload 46 – 1500 bytes • Checksum (FCS) 4 bytes cs 490 ns-cotter 21
Two stages of PPPo. E: Discovery Stage – Host (client) may discover all Remote access concentrators and select one • A session_id is established • Ether_type: 0 x 8863 – Four messages: • • Initiation (from host to RAC) Offer from (RAC to host) Request from (host to RAC) Confirm (from RAC to host): contains session ID cs 490 ns-cotter 22
Session Stage – Now transmit PPP-LCP message to establish PPP session – First generated by host • • Dest. Addr: Access Concentrator Source. Addr: host Ether_type: 0 x 8864 Session. ID: as obtained from Discovery Stage Length: <rest of packet> PPP protocol: 0 xc 021 (PPP-LCP) Now PPP payload! – Continue with other PPP messages (PAP, IP-CP etc) to get to the IP datagram transmission phase cs 490 ns-cotter 23
Authentication Technologies • Authenticating a transmission to ensure that it comes from an approved sender can provide an increased level of security for remote access users • Examples: – Radius – Tacacs+ cs 490 ns-cotter 24
(RADIUS) • Remote Authentication Dial-In User Service • Originally defined to enable centralized authentication and access control for PPP sessions • Requests are forwarded to a single RADIUS server • Supports authentication, authorization, and auditing functions • After connection is made, RADIUS server adds an accounting record to its log and acknowledges the request • Allows company to maintain user profiles in a central database that all remote servers can share cs 490 ns-cotter 25
(TACACS+) • Terminal Access Control System • Industry standard protocol specification that forwards username and password information to a centralized server • Whereas communication between a NAS and a TACACS+ server is encrypted, communication between a client and a NAS is not cs 490 ns-cotter 26
IPSec • Designed to create and support a cryptographically protected communication channel • This connection is called a Security Association. – SA defined by a set of security parameters referenced in a Security Parameter Index (SPI) and a destination host address.
IP Security (IPSec) • Considered to be a transparent security protocol operating at layer 3 – Transparent to applications, users, and software • Provides three areas of protection that correspond to three IPSec protocols: – Key management (ISAKMP/IKE - Oakley) • A way to establish an SA – Authentication (AH) • A way to ensure the integrity of the communication – Confidentiality (ESP) • A way to ensure the privacy of the communication. cs 490 ns-cotter 28
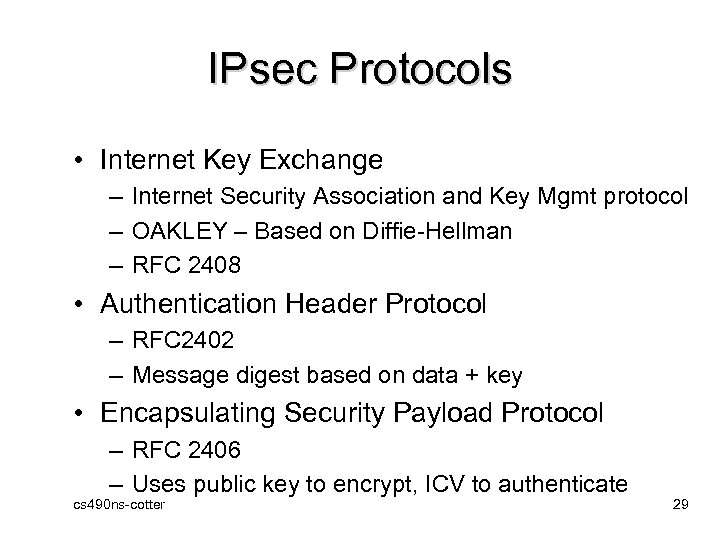
IPsec Protocols • Internet Key Exchange – Internet Security Association and Key Mgmt protocol – OAKLEY – Based on Diffie-Hellman – RFC 2408 • Authentication Header Protocol – RFC 2402 – Message digest based on data + key • Encapsulating Security Payload Protocol – RFC 2406 – Uses public key to encrypt, ICV to authenticate cs 490 ns-cotter 29
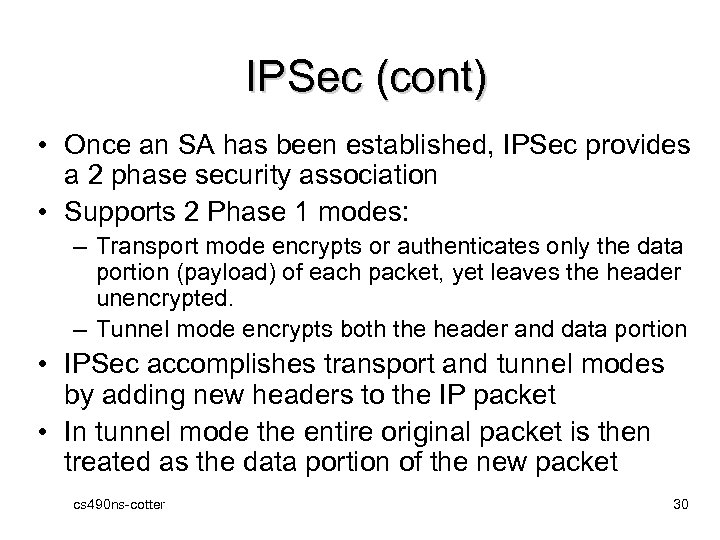
IPSec (cont) • Once an SA has been established, IPSec provides a 2 phase security association • Supports 2 Phase 1 modes: – Transport mode encrypts or authenticates only the data portion (payload) of each packet, yet leaves the header unencrypted. – Tunnel mode encrypts both the header and data portion • IPSec accomplishes transport and tunnel modes by adding new headers to the IP packet • In tunnel mode the entire original packet is then treated as the data portion of the new packet cs 490 ns-cotter 30
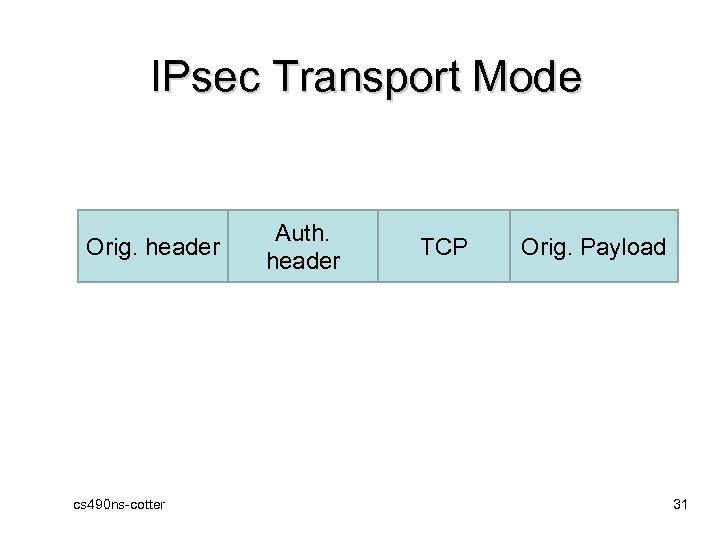
IPsec Transport Mode Orig. header cs 490 ns-cotter Auth. header TCP Orig. Payload 31
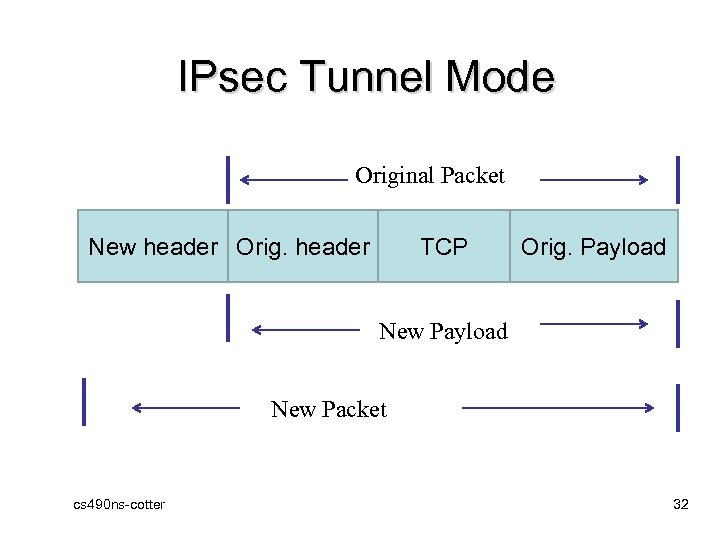
IPsec Tunnel Mode Original Packet New header Orig. header TCP Orig. Payload New Packet cs 490 ns-cotter 32
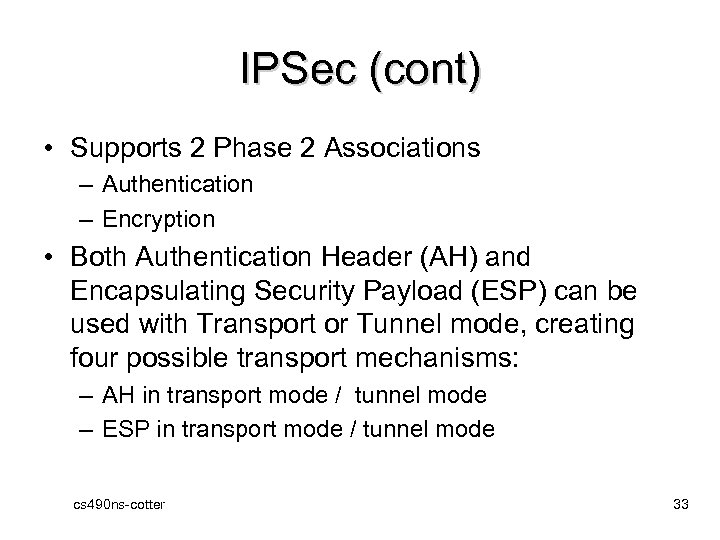
IPSec (cont) • Supports 2 Phase 2 Associations – Authentication – Encryption • Both Authentication Header (AH) and Encapsulating Security Payload (ESP) can be used with Transport or Tunnel mode, creating four possible transport mechanisms: – AH in transport mode / tunnel mode – ESP in transport mode / tunnel mode cs 490 ns-cotter 33
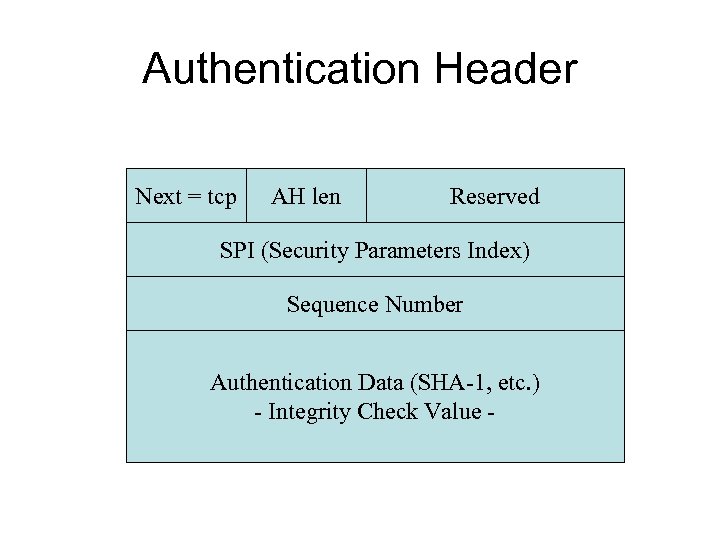
Authentication Header Next = tcp AH len Reserved SPI (Security Parameters Index) Sequence Number Authentication Data (SHA-1, etc. ) - Integrity Check Value -
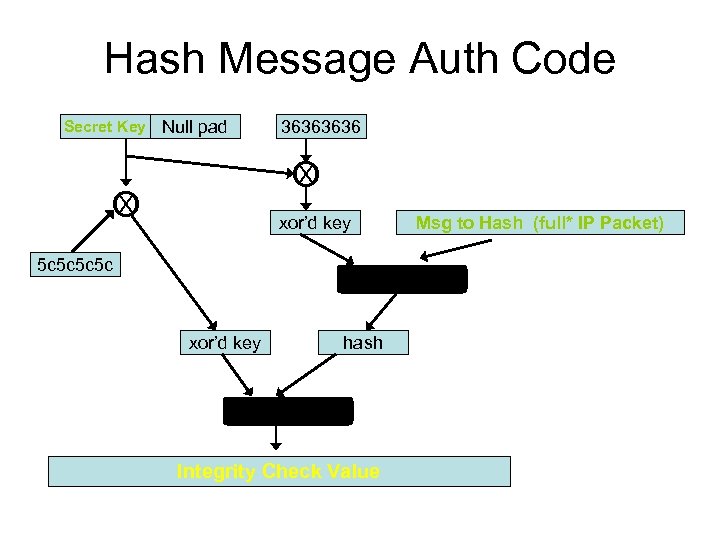
Hash Message Auth Code Secret Key Null pad 3636 X O xor’d key 5 c 5 c Msg to Hash (full* IP Packet) Hash Function xor’d key hash Hash Function Integrity Check Value
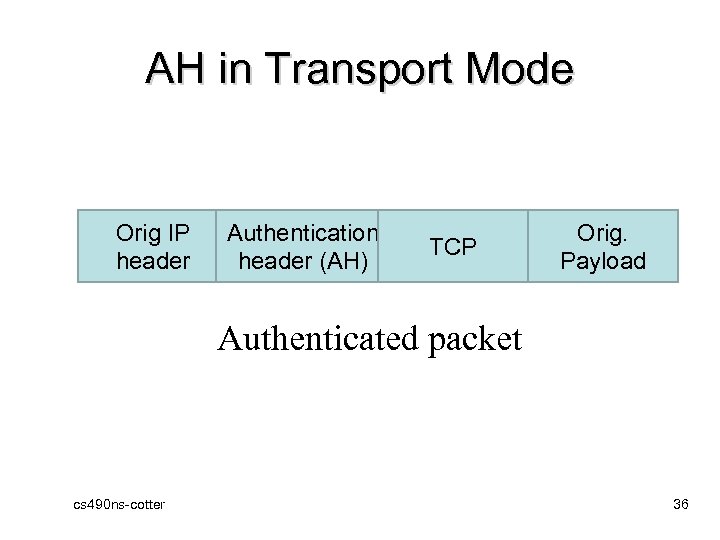
AH in Transport Mode Orig IP header Authentication header (AH) TCP Orig. Payload Authenticated packet cs 490 ns-cotter 36
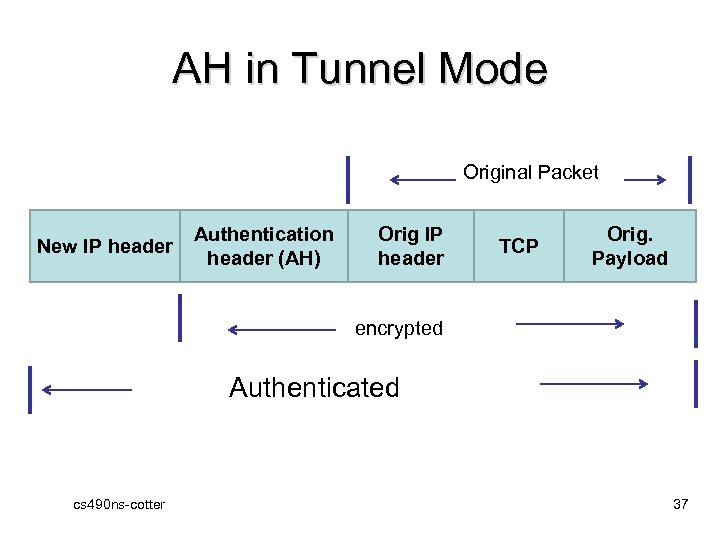
AH in Tunnel Mode Original Packet New IP header Authentication header (AH) Orig IP header TCP Orig. Payload encrypted Authenticated cs 490 ns-cotter 37
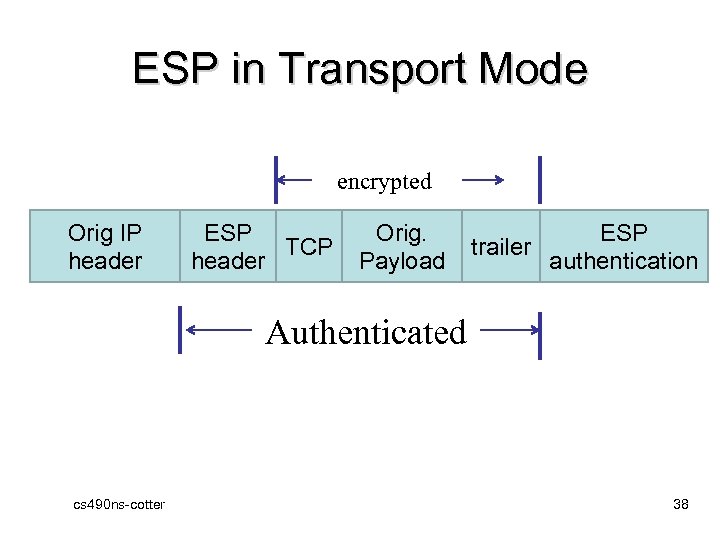
ESP in Transport Mode encrypted Orig IP header ESP TCP header Orig. Payload trailer ESP authentication Authenticated cs 490 ns-cotter 38
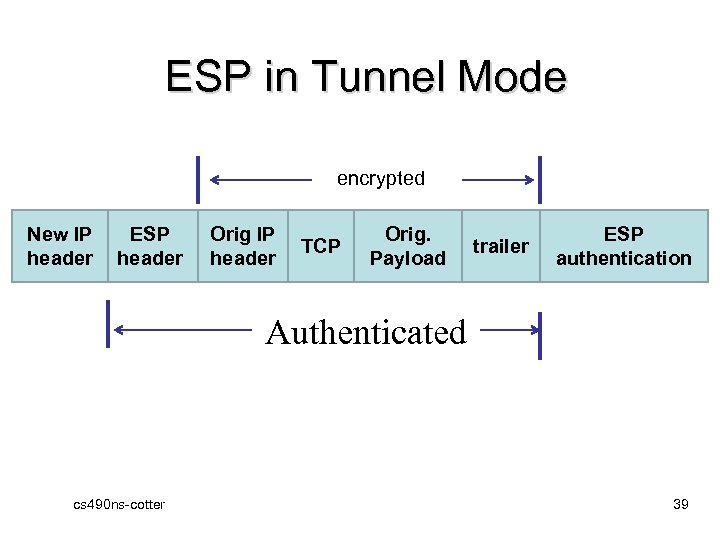
ESP in Tunnel Mode encrypted New IP header ESP header Orig IP header TCP Orig. Payload trailer ESP authentication Authenticated cs 490 ns-cotter 39
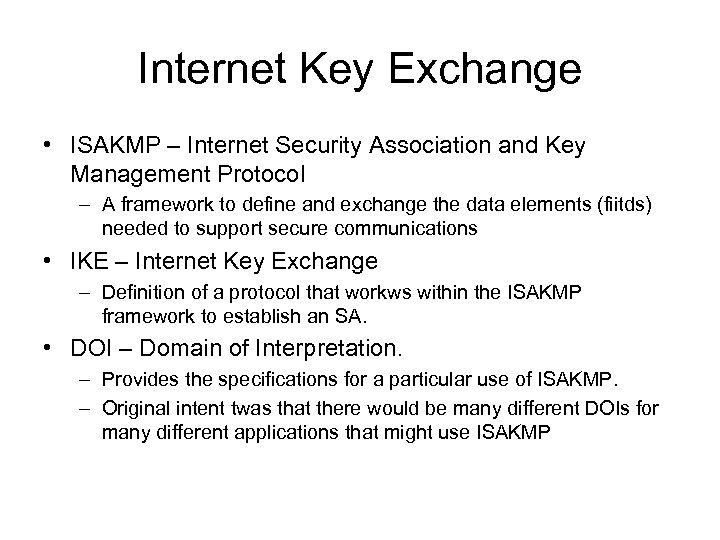
Internet Key Exchange • ISAKMP – Internet Security Association and Key Management Protocol – A framework to define and exchange the data elements (fiitds) needed to support secure communications • IKE – Internet Key Exchange – Definition of a protocol that workws within the ISAKMP framework to establish an SA. • DOI – Domain of Interpretation. – Provides the specifications for a particular use of ISAKMP. – Original intent twas that there would be many different DOIs for many different applications that might use ISAKMP
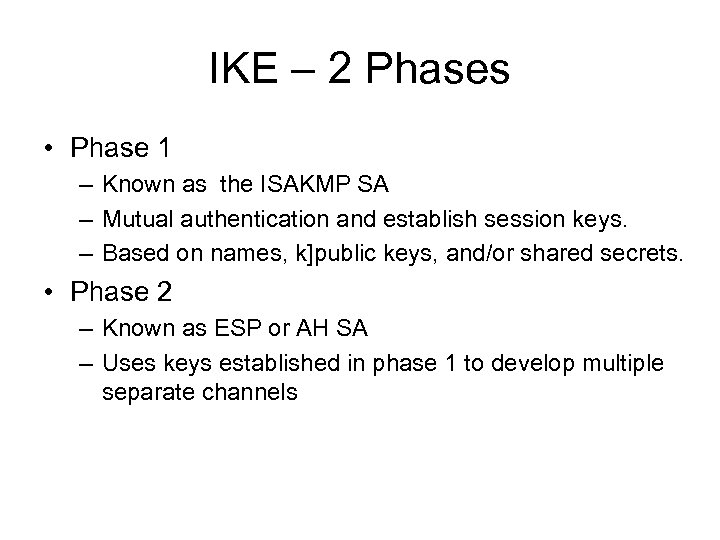
IKE – 2 Phases • Phase 1 – Known as the ISAKMP SA – Mutual authentication and establish session keys. – Based on names, k]public keys, and/or shared secrets. • Phase 2 – Known as ESP or AH SA – Uses keys established in phase 1 to develop multiple separate channels
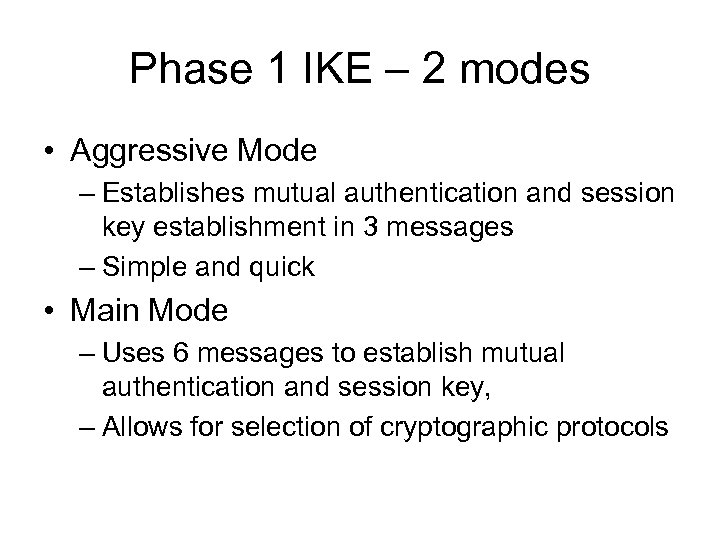
Phase 1 IKE – 2 modes • Aggressive Mode – Establishes mutual authentication and session key establishment in 3 messages – Simple and quick • Main Mode – Uses 6 messages to establish mutual authentication and session key, – Allows for selection of cryptographic protocols
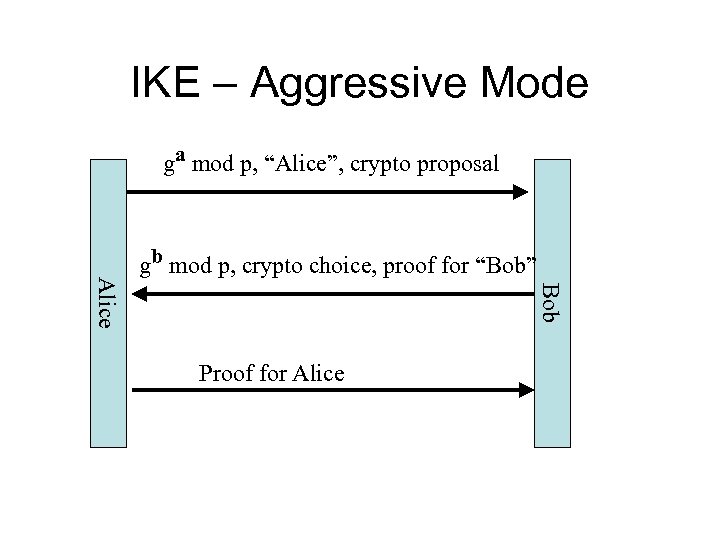
IKE – Aggressive Mode ga mod p, “Alice”, crypto proposal Bob Alice gb mod p, crypto choice, proof for “Bob” Proof for Alice
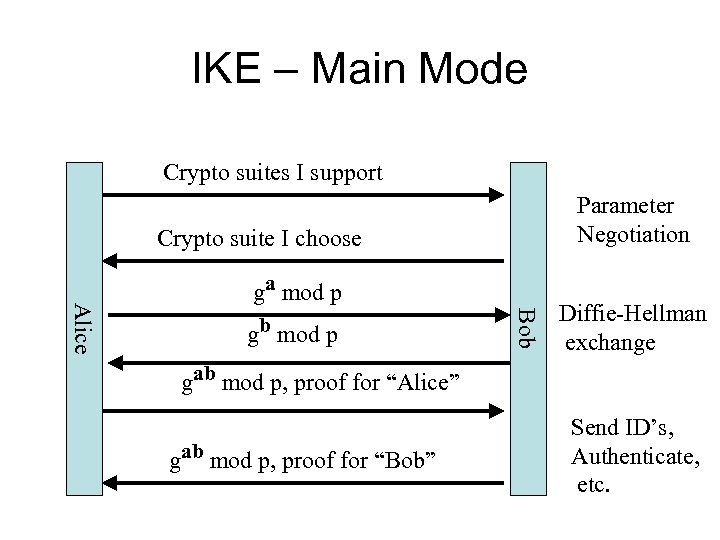
IKE – Main Mode Crypto suites I support Parameter Negotiation Crypto suite I choose gb mod p Bob Alice ga mod p Diffie-Hellman exchange gab mod p, proof for “Alice” gab mod p, proof for “Bob” Send ID’s, Authenticate, etc.
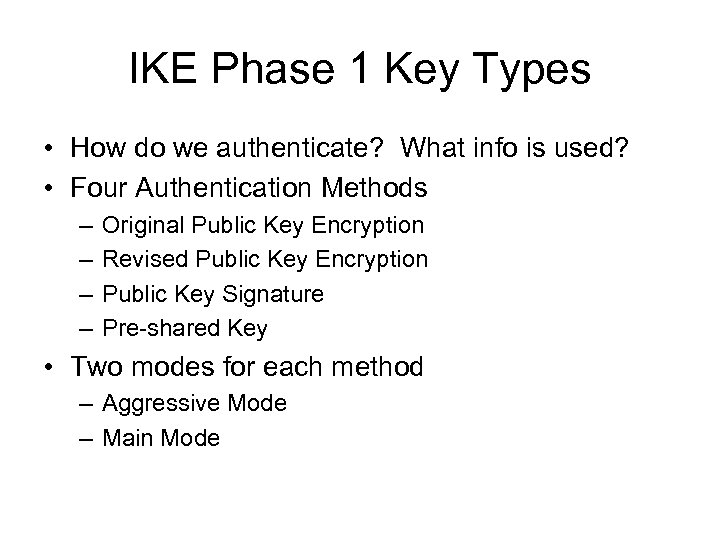
IKE Phase 1 Key Types • How do we authenticate? What info is used? • Four Authentication Methods – – Original Public Key Encryption Revised Public Key Encryption Public Key Signature Pre-shared Key • Two modes for each method – Aggressive Mode – Main Mode
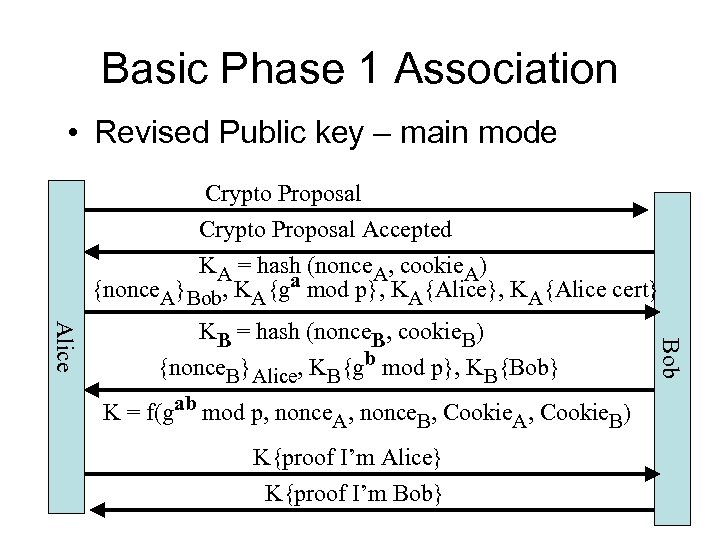
Basic Phase 1 Association • Revised Public key – main mode Crypto Proposal Accepted KA = hash (nonce. A, cookie. A) {nonce. A}Bob, KA{ga mod p}, KA{Alice cert} K = f(gab mod p, nonce. A, nonce. B, Cookie. A, Cookie. B) K{proof I’m Alice} K{proof I’m Bob} Bob Alice KB = hash (nonce. B, cookie. B) {nonce. B}Alice, KB{gb mod p}, KB{Bob}
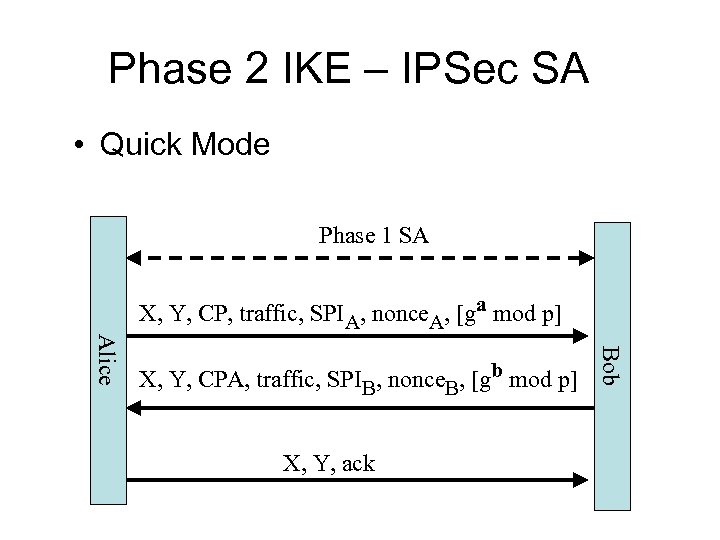
Phase 2 IKE – IPSec SA • Quick Mode Phase 1 SA X, Y, CP, traffic, SPIA, nonce. A, [ga mod p] X, Y, ack Bob Alice X, Y, CPA, traffic, SPIB, nonce. B, [gb mod p]
Virtual Private Networks (VPNs) • Takes advantage of using the public Internet as if it were a private network • Allow the public Internet to be used privately • Prior to VPNs, organizations were forced to lease expensive data connections from private carriers so employees could remotely connect to the organization’s network cs 490 ns-cotter 48
VPNs (cont) • Two common types of VPNs include: – Remote-access VPN or virtual private dial-up network (VPDN): user-to-LAN connection used by remote users – Site-to-site VPN: multiple sites can connect to other sites over the Internet • VPN transmissions achieved through communicating with endpoints – An endpoint can be software on a local computer, a dedicated hardware device such as a VPN concentrator, or even a firewall cs 490 ns-cotter 49
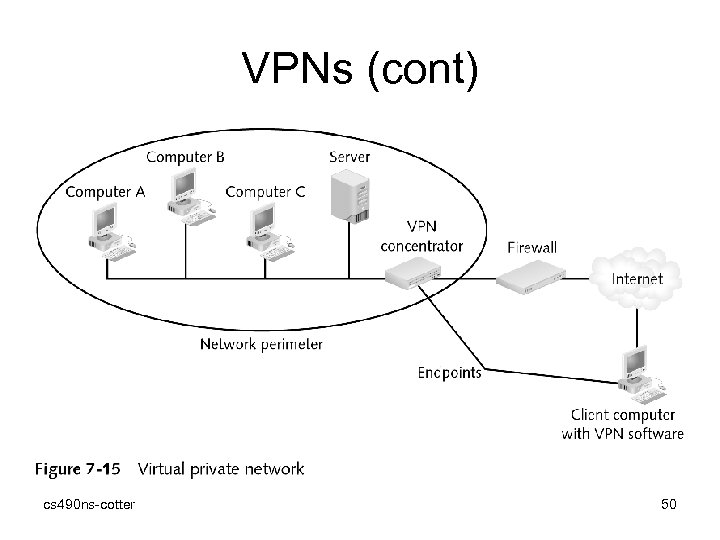
VPNs (cont) cs 490 ns-cotter 50
VPN (IPSec) Issues - NAT • NAT objective is to change (map) private IP addresses into public IP addresses • AH includes IP addrs in hash. • ESP encrypts original header, but not new header • Possible with ESP in tunnel mode, but issues with IKE • If possible, do IPSec outside of NAT, or in a shared box.
Hardening File Transfer Protocol (FTP) • Three ways to work with FTP: – Web browser – FTP client – Command line • FTP servers can be configured to allow unauthenticated users to transfer files (called anonymous FTP or blind FTP) cs 490 ns-cotter 52
FTP (cont) • Vulnerabilities associated with using FTP – FTP does not use encryption – Files being transferred by FTP are vulnerable to man-in-the-middle attacks • Use secure FTP to reduce risk of attack – Secure FTP is a term used by vendors to describe encrypting FTP transmissions • Most secure FTP products use Secure Socket Layers (SSL) to perform the encryption cs 490 ns-cotter 53
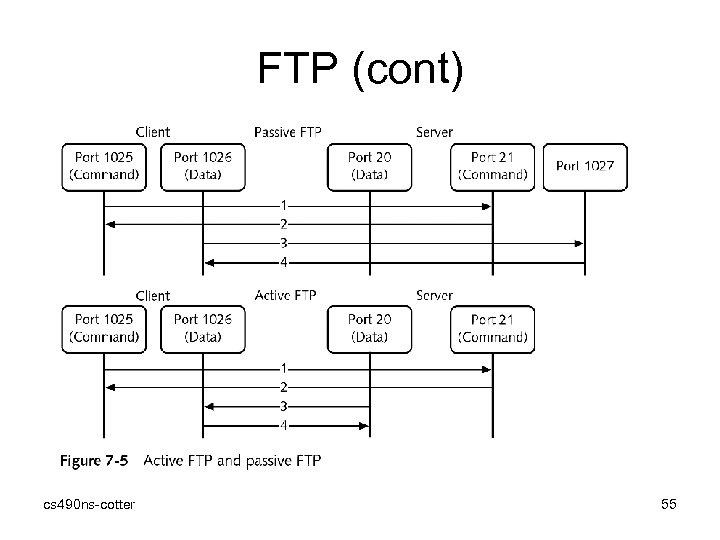
FTP (cont) • FTP active mode – Client connects from any random port >1, 024 (PORT N) to FTP server’s command port, port 21 (Step 1) – Client starts listening to PORT N+1 and sends the FTP command PORT N+1 to the FTP server • FTP passive mode – Client initiates both connections to server – When opening an FTP connection, client opens two local random unprivileged ports >1, 024 cs 490 ns-cotter 54
FTP (cont) cs 490 ns-cotter 55
FTP (Implicit / Explicit Encryption) • Implicit Encryption – FTP server / client assume an encryption mechanism (TLS / sslv 1, sslv 2, sslv 3, etc. ) – No option to use non-encrypted channel provided – Control port: 990; Data port: 989 – More secure – less flexible • Explicit Encryption – FTP server / client negotiates over encryption. May choose encryption or not – More flexible – potentially less secure cs 490 ns-cotter 56
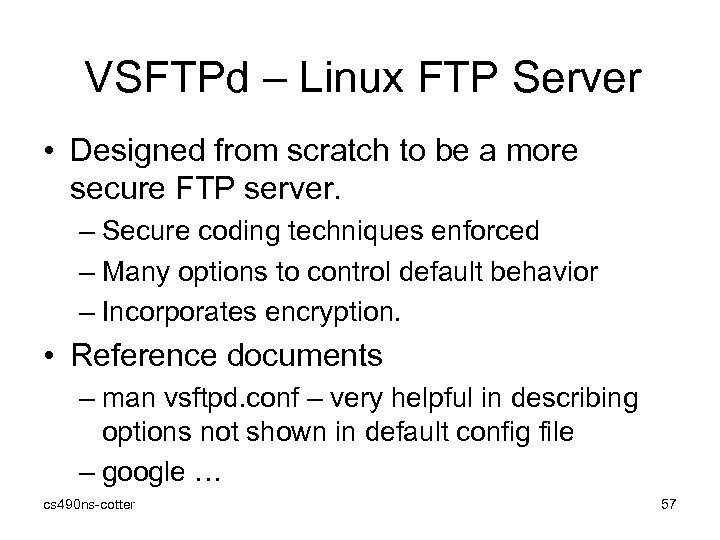
VSFTPd – Linux FTP Server • Designed from scratch to be a more secure FTP server. – Secure coding techniques enforced – Many options to control default behavior – Incorporates encryption. • Reference documents – man vsftpd. conf – very helpful in describing options not shown in default config file – google … cs 490 ns-cotter 57
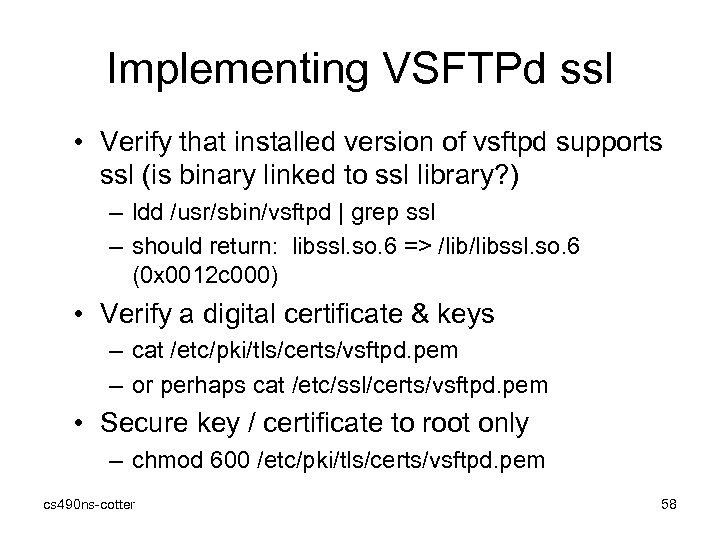
Implementing VSFTPd ssl • Verify that installed version of vsftpd supports ssl (is binary linked to ssl library? ) – ldd /usr/sbin/vsftpd | grep ssl – should return: libssl. so. 6 => /libssl. so. 6 (0 x 0012 c 000) • Verify a digital certificate & keys – cat /etc/pki/tls/certs/vsftpd. pem – or perhaps cat /etc/ssl/certs/vsftpd. pem • Secure key / certificate to root only – chmod 600 /etc/pki/tls/certs/vsftpd. pem cs 490 ns-cotter 58
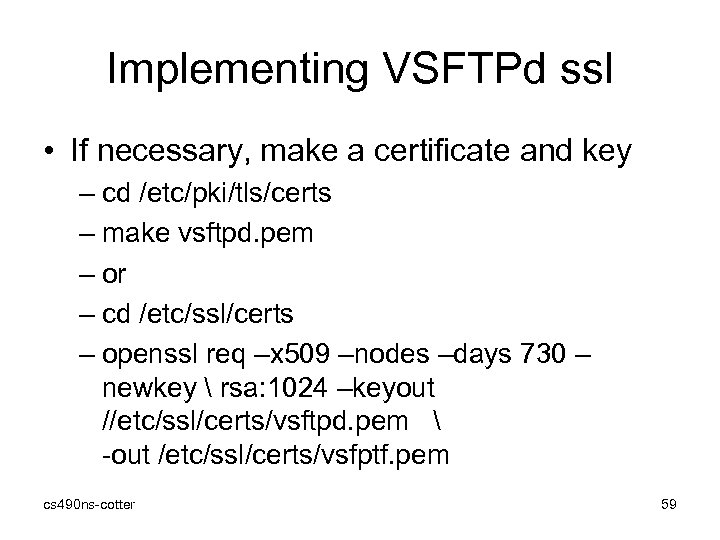
Implementing VSFTPd ssl • If necessary, make a certificate and key – cd /etc/pki/tls/certs – make vsftpd. pem – or – cd /etc/ssl/certs – openssl req –x 509 –nodes –days 730 – newkey rsa: 1024 –keyout //etc/ssl/certs/vsftpd. pem -out /etc/ssl/certs/vsfptf. pem cs 490 ns-cotter 59
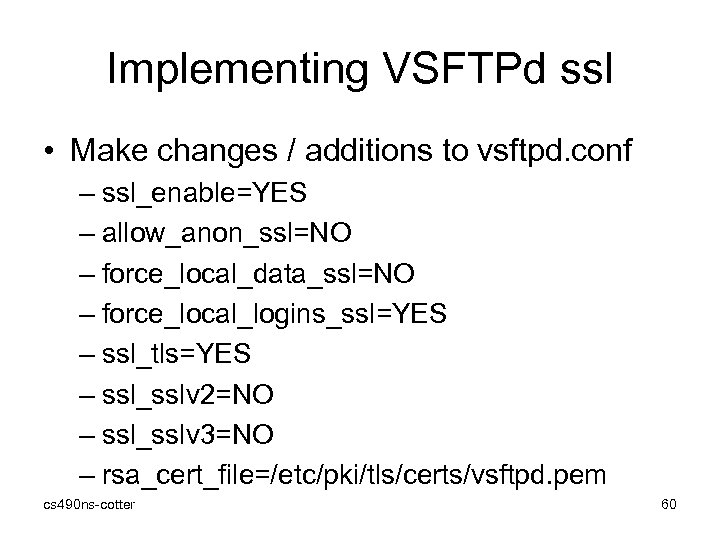
Implementing VSFTPd ssl • Make changes / additions to vsftpd. conf – ssl_enable=YES – allow_anon_ssl=NO – force_local_data_ssl=NO – force_local_logins_ssl=YES – ssl_tls=YES – ssl_sslv 2=NO – ssl_sslv 3=NO – rsa_cert_file=/etc/pki/tls/certs/vsftpd. pem cs 490 ns-cotter 60
Get an FTP Client • Windows – – core. FTP lite – free smart. FTP - $ turbo. FTP - $ many others … • Linux – – cs 490 ns-cotter Kftpgrabber – ssl/tls Kasablanca – ssl/tls gftp – ssh etc. 61
References: • • PPP – rfc 1661, 1663, (Forouzan, Ch 15) PPTP – rfc 2637, Microsoft PPPo. E – rfc 2516 L 2 TP – rfc 2661, 3931, Cisco RADIUS – rfc 2865 IPSec – rfc 2411 (2401 – 2412) Google… cs 490 ns-cotter 62
Summary • FTP protocol has several security vulnerabilities - it does not natively use encryption and is vulnerable to man-in-the-middle attacks • FTP can be hardened by using secure FTP (which encrypts using SSL) • Protecting remote access transmissions is particularly important in today’s environment as more users turn to the Internet as the infrastructure for accessing protected information cs 490 ns-cotter 63
Summary • Authenticating a transmission to ensure it came from the sender can provide increased security for remote access users • SSH is a UNIX-based command interface and protocol for securely accessing a remote computer cs 490 ns-cotter 64
864906df9f55ca6e9bf40de38df523d9.ppt