b4c21e528dcc768780249d2c71a7258d.ppt
- Количество слайдов: 28
 Regular Expression Denial of Service Alex Roichman Chief Architect, Checkmarx Adar Weidman OWASP Senior Programmer, Checkmarx Israel 2009 Copyright © The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the OWASP License. The OWASP Foundation http: //www. owasp. org
Regular Expression Denial of Service Alex Roichman Chief Architect, Checkmarx Adar Weidman OWASP Senior Programmer, Checkmarx Israel 2009 Copyright © The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the OWASP License. The OWASP Foundation http: //www. owasp. org
 Agenda < Do. S attack < Regex and Do. S - Re. Do. S < Exploiting Re. Do. S: Why, Where & How < Leveraging Re. Do. S to Web attacks 4 Server-side Re. Do. S 4 Client-side Re. Do. S < Preventing Re. Do. S < Conclusions OWASP
Agenda < Do. S attack < Regex and Do. S - Re. Do. S < Exploiting Re. Do. S: Why, Where & How < Leveraging Re. Do. S to Web attacks 4 Server-side Re. Do. S 4 Client-side Re. Do. S < Preventing Re. Do. S < Conclusions OWASP
 Do. S Attack
Do. S Attack
 Brute-Force Do. S
Brute-Force Do. S
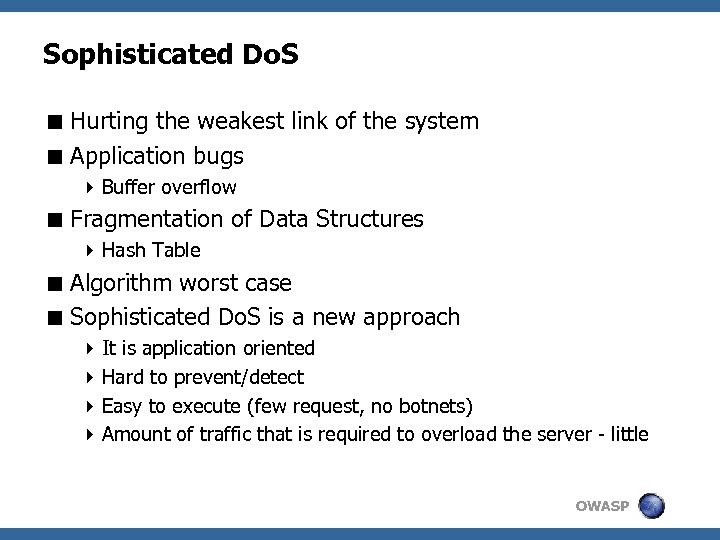 Sophisticated Do. S < Hurting the weakest link of the system < Application bugs 4 Buffer overflow < Fragmentation of Data Structures 4 Hash Table < Algorithm worst case < Sophisticated Do. S is a new approach 4 It is application oriented 4 Hard to prevent/detect 4 Easy to execute (few request, no botnets) 4 Amount of traffic that is required to overload the server - little OWASP
Sophisticated Do. S < Hurting the weakest link of the system < Application bugs 4 Buffer overflow < Fragmentation of Data Structures 4 Hash Table < Algorithm worst case < Sophisticated Do. S is a new approach 4 It is application oriented 4 Hard to prevent/detect 4 Easy to execute (few request, no botnets) 4 Amount of traffic that is required to overload the server - little OWASP
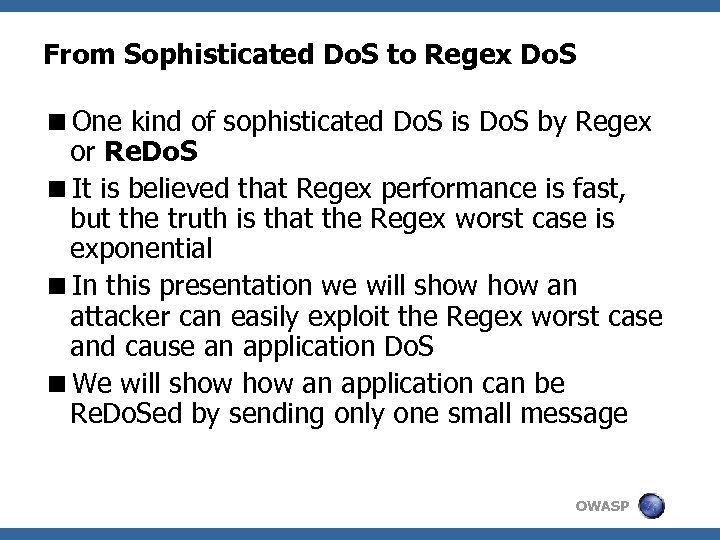 From Sophisticated Do. S to Regex Do. S
From Sophisticated Do. S to Regex Do. S
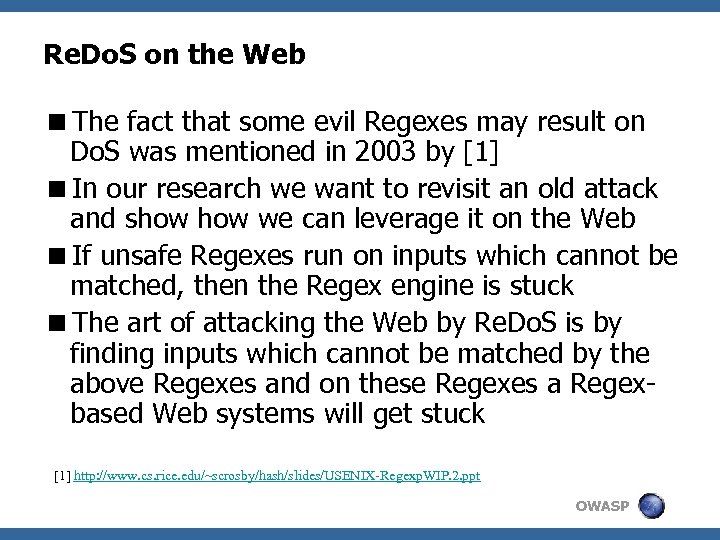 Re. Do. S on the Web
Re. Do. S on the Web
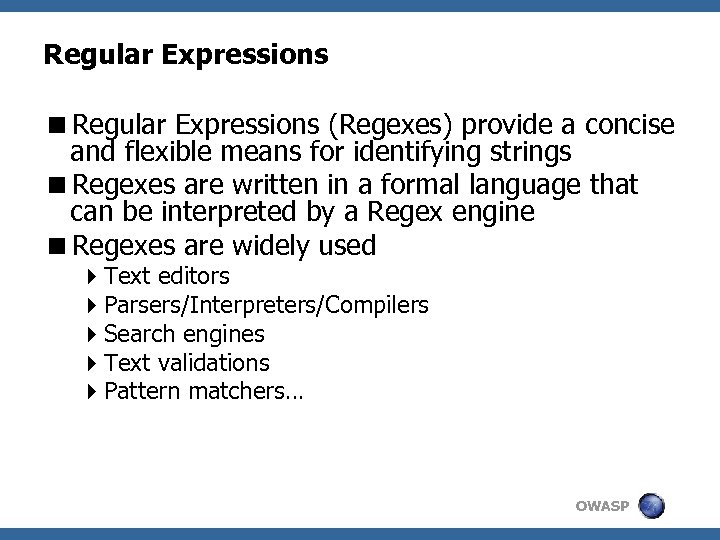 Regular Expressions
Regular Expressions
 Regex engine algorithm
Regex engine algorithm
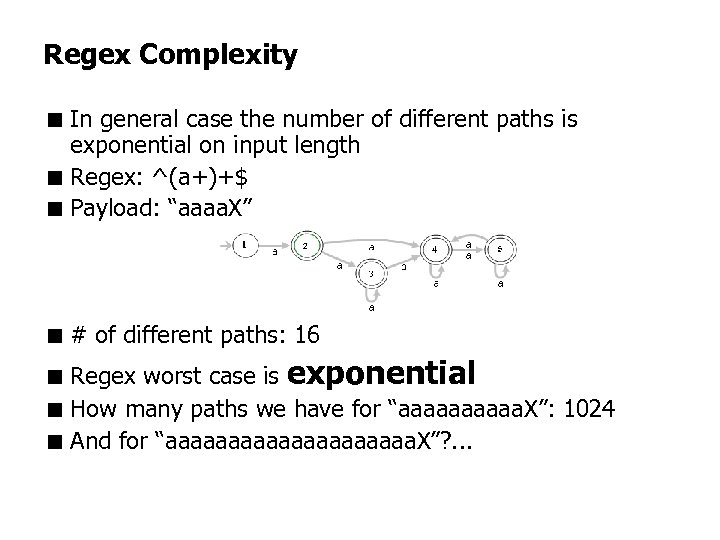 Regex Complexity < In general case the number of different paths is exponential on input length < Regex: ^(a+)+$ < Payload: “aaaa. X” < # of different paths: 16 < Regex worst case is exponential < How many paths we have for “aaaaa. X”: 1024 < And for “aaaaaaaaaa. X”? . . .
Regex Complexity < In general case the number of different paths is exponential on input length < Regex: ^(a+)+$ < Payload: “aaaa. X” < # of different paths: 16 < Regex worst case is exponential < How many paths we have for “aaaaa. X”: 1024 < And for “aaaaaaaaaa. X”? . . .
 Evil Regex Patterns < Regex is called evil if it can be stuck on specially crafted input < Each evil Regex pattern should contain: 4 Grouping construct with repetition 4 Inside the repeated group should appear § Repetition § Alternation with overlapping < Evil Regex pattern examples 1. 2. 3. 4. 5. (a+)+ ([a-z. A-Z]+)* (a|aa)+ (a|a? )+ (. *a){x} | for x > 10 Payload: “aaaaaaaaa. X” OWASP
Evil Regex Patterns < Regex is called evil if it can be stuck on specially crafted input < Each evil Regex pattern should contain: 4 Grouping construct with repetition 4 Inside the repeated group should appear § Repetition § Alternation with overlapping < Evil Regex pattern examples 1. 2. 3. 4. 5. (a+)+ ([a-z. A-Z]+)* (a|aa)+ (a|a? )+ (. *a){x} | for x > 10 Payload: “aaaaaaaaa. X” OWASP
![Real examples of Re. Do. S <OWASP Validation Regex Repository [2] 4 Person Name Real examples of Re. Do. S <OWASP Validation Regex Repository [2] 4 Person Name](https://present5.com/presentation/b4c21e528dcc768780249d2c71a7258d/image-12.jpg) Real examples of Re. Do. S
Real examples of Re. Do. S
![Real examples of Re. Do. S <Regex Library [3] 4 Email Validation § Regex: Real examples of Re. Do. S <Regex Library [3] 4 Email Validation § Regex:](https://present5.com/presentation/b4c21e528dcc768780249d2c71a7258d/image-13.jpg) Real examples of Re. Do. S
Real examples of Re. Do. S
 Exploiting Re. Do. S: Why
Exploiting Re. Do. S: Why
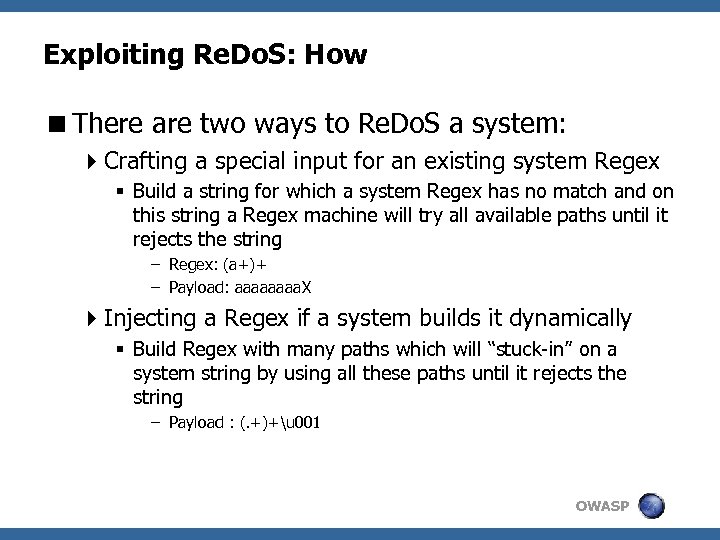 Exploiting Re. Do. S: How
Exploiting Re. Do. S: How
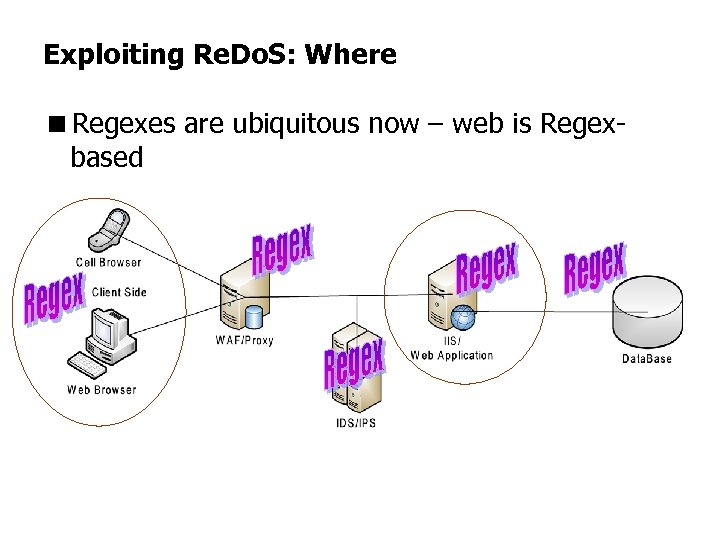 Exploiting Re. Do. S: Where
Exploiting Re. Do. S: Where
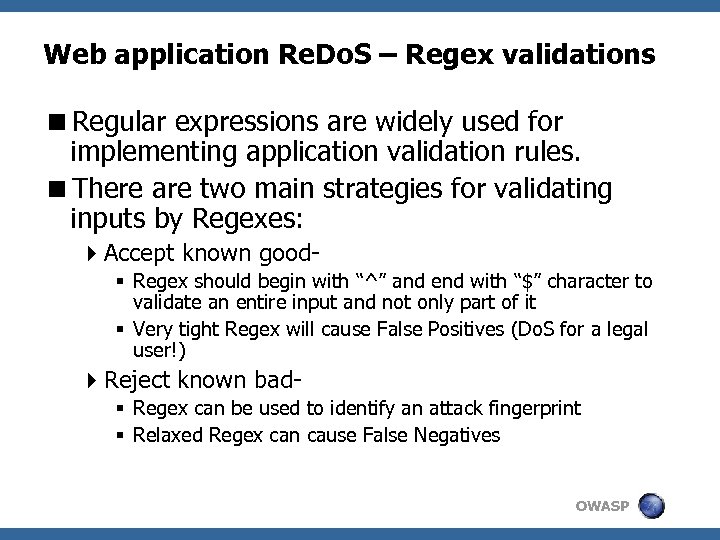 Web application Re. Do. S – Regex validations
Web application Re. Do. S – Regex validations
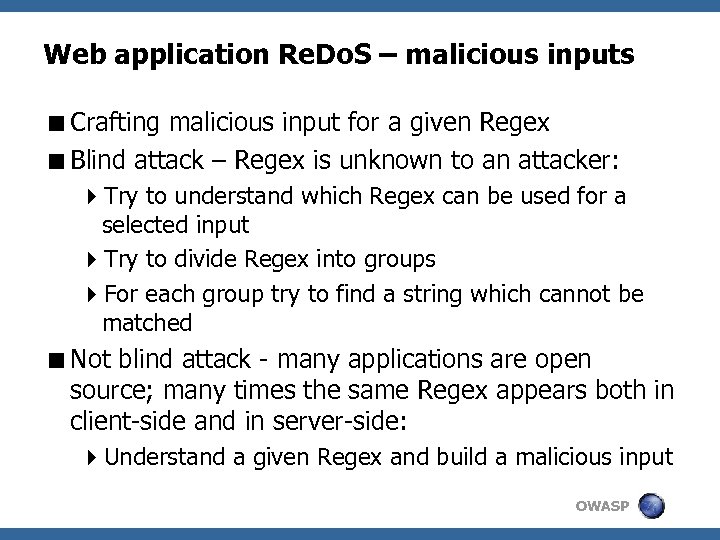 Web application Re. Do. S – malicious inputs
Web application Re. Do. S – malicious inputs
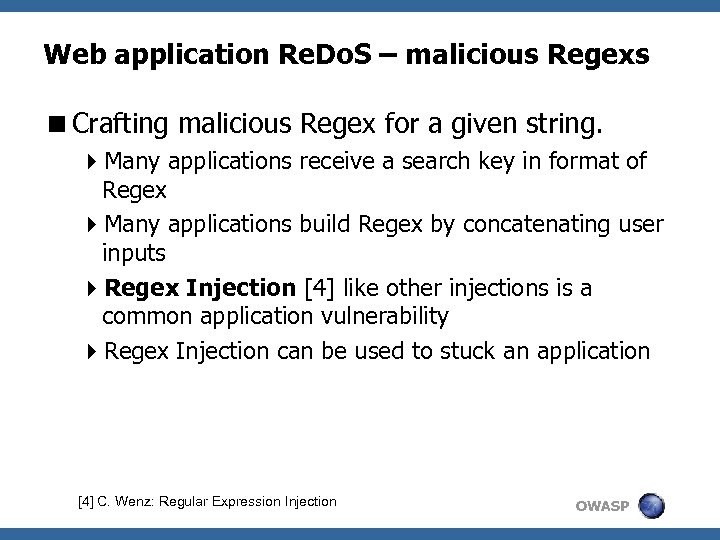 Web application Re. Do. S – malicious Regexs
Web application Re. Do. S – malicious Regexs
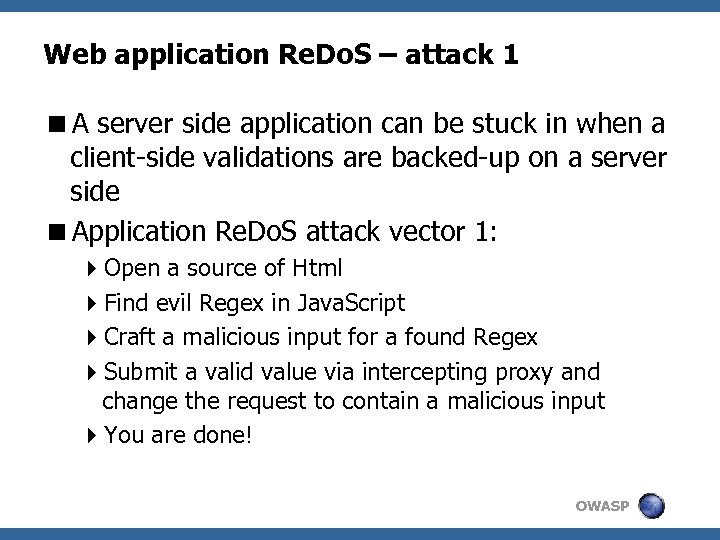
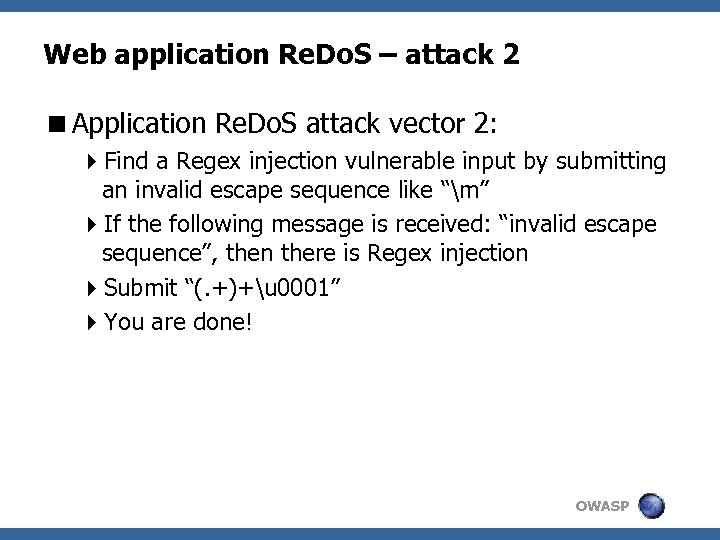 Web application Re. Do. S – attack 2
Web application Re. Do. S – attack 2
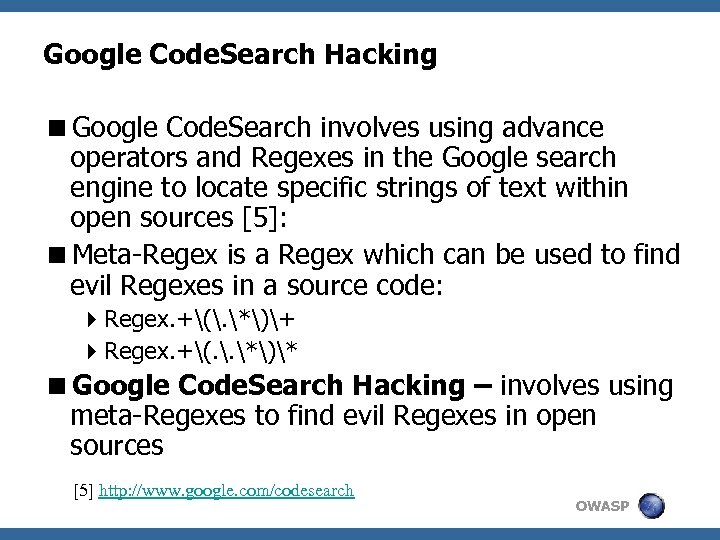 Google Code. Search Hacking
Google Code. Search Hacking
![Web application Re. Do. S Example <Data. Vault [6]: 4 Regex: ^[(, . *)*]$ Web application Re. Do. S Example <Data. Vault [6]: 4 Regex: ^[(, . *)*]$](https://present5.com/presentation/b4c21e528dcc768780249d2c71a7258d/image-23.jpg) Web application Re. Do. S Example
Web application Re. Do. S Example
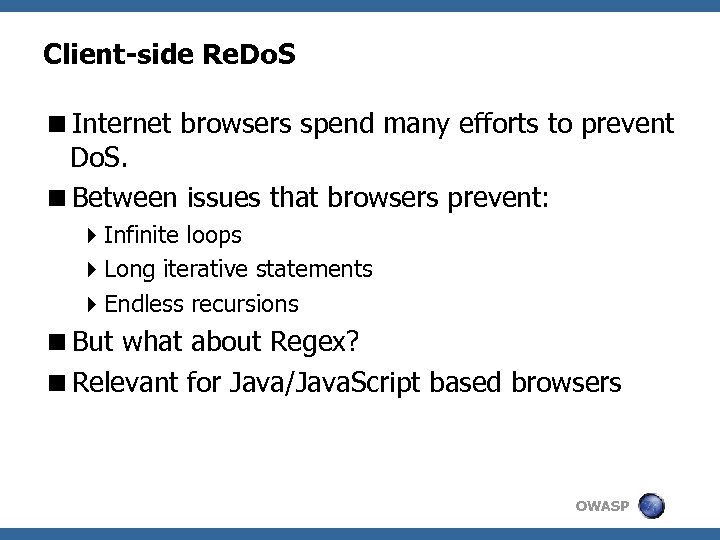 Client-side Re. Do. S
Client-side Re. Do. S
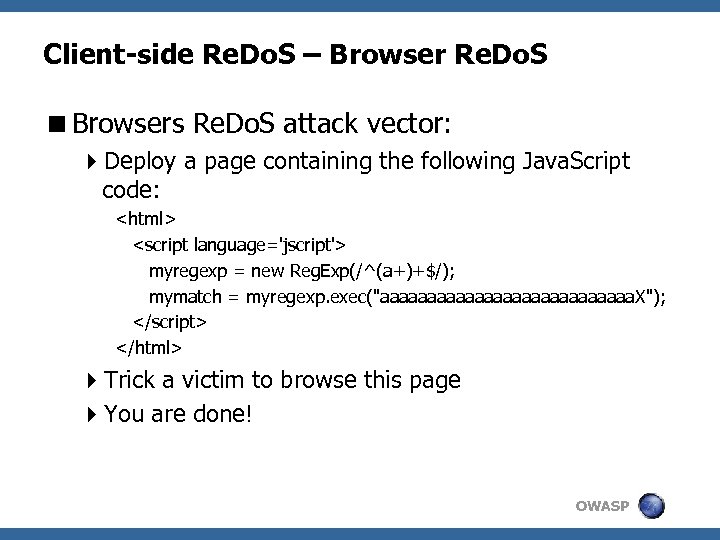 Client-side Re. Do. S – Browser Re. Do. S
Client-side Re. Do. S – Browser Re. Do. S