15194cfff8e495d7184efc12ae011ecd.ppt
- Количество слайдов: 65
 RADIUS Sunil Vallamkonda Oct. 25, 2006 RADIUS presentation by Sunil Vallamkonda 1
RADIUS Sunil Vallamkonda Oct. 25, 2006 RADIUS presentation by Sunil Vallamkonda 1
 What is AAA ? • Authentication • Authorization • Accounting RADIUS presentation by Sunil Vallamkonda 2
What is AAA ? • Authentication • Authorization • Accounting RADIUS presentation by Sunil Vallamkonda 2
 Authentication • Verify a person’s or machine’s declared identity. • Mechanisms: passwords, PKI. • Key aspect is Trust relationships between servers. RADIUS presentation by Sunil Vallamkonda 3
Authentication • Verify a person’s or machine’s declared identity. • Mechanisms: passwords, PKI. • Key aspect is Trust relationships between servers. RADIUS presentation by Sunil Vallamkonda 3
 Authorization • Rules or templates on what a authenticated user can do on a system. • Dial up user requests can be one link or multiple. RADIUS presentation by Sunil Vallamkonda 4
Authorization • Rules or templates on what a authenticated user can do on a system. • Dial up user requests can be one link or multiple. RADIUS presentation by Sunil Vallamkonda 4
 Accounting • Measures and tracks resources a user accesses. • Include time, amount of data, session statistics, resource utilization etc. • Logs sent and analyzed for billing, security servers. RADIUS presentation by Sunil Vallamkonda 5
Accounting • Measures and tracks resources a user accesses. • Include time, amount of data, session statistics, resource utilization etc. • Logs sent and analyzed for billing, security servers. RADIUS presentation by Sunil Vallamkonda 5
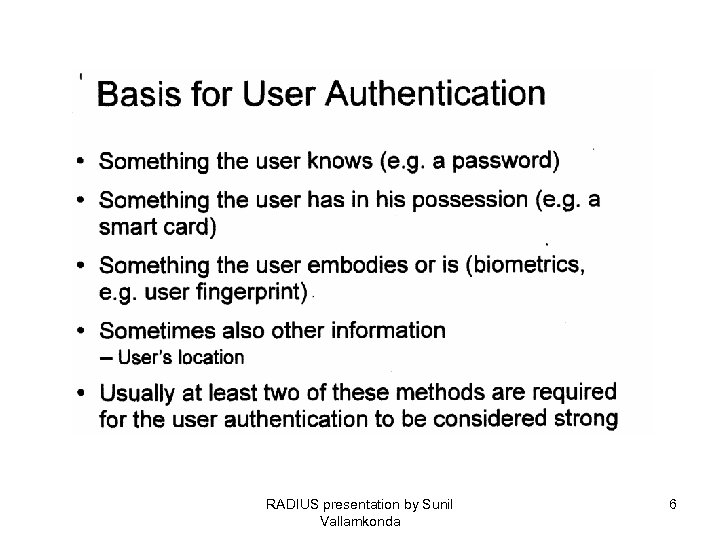 RADIUS presentation by Sunil Vallamkonda 6
RADIUS presentation by Sunil Vallamkonda 6
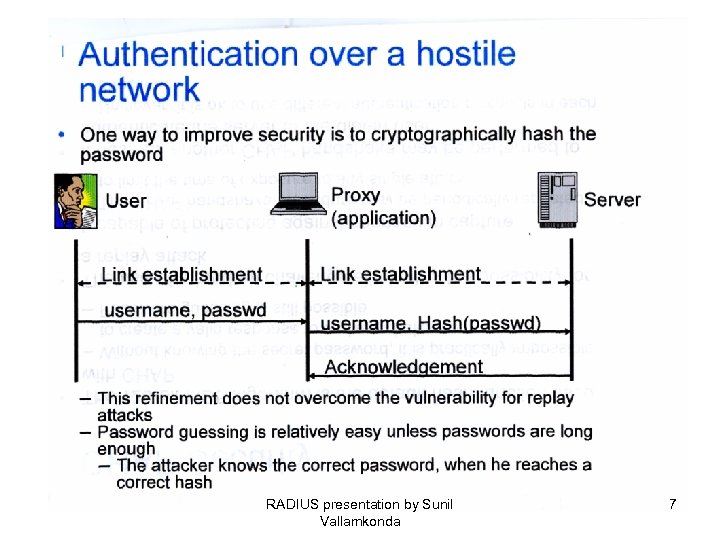 RADIUS presentation by Sunil Vallamkonda 7
RADIUS presentation by Sunil Vallamkonda 7
 RADIUS presentation by Sunil Vallamkonda 8
RADIUS presentation by Sunil Vallamkonda 8
 Properties • • Client/server model UDP based Hop by hop security Stateless Uses MD 5 for password hiding. A-V pairs PAP/CHAP via PPP RADIUS presentation by Sunil Vallamkonda 9
Properties • • Client/server model UDP based Hop by hop security Stateless Uses MD 5 for password hiding. A-V pairs PAP/CHAP via PPP RADIUS presentation by Sunil Vallamkonda 9
 Packet format • • ACCESS-REQUEST (1) ACCESS-RESPONSE (2) ACCESS-REJECT (3) ACCESS-CHALLENGE (11) ACCOUNTING-REQUEST (4) ACCOUNTING-RESPONSE (5) STATUS-SERVER (12) STATUS-CLIENT (13) RADIUS presentation by Sunil Vallamkonda 10
Packet format • • ACCESS-REQUEST (1) ACCESS-RESPONSE (2) ACCESS-REJECT (3) ACCESS-CHALLENGE (11) ACCOUNTING-REQUEST (4) ACCOUNTING-RESPONSE (5) STATUS-SERVER (12) STATUS-CLIENT (13) RADIUS presentation by Sunil Vallamkonda 10
 RADIUS Packet • Header : Code (1), Identifier (1), length (2), Authenticator (16), payload • Code: as above • Identifier: used to perform auto linking of initial requests and subsequent replies. • Length: valid range: 20 – 4096. • Authenticator: used to conceal passwords using one way MD 5. Request (random number) / Response authenticators. RADIUS presentation by Sunil Vallamkonda 11
RADIUS Packet • Header : Code (1), Identifier (1), length (2), Authenticator (16), payload • Code: as above • Identifier: used to perform auto linking of initial requests and subsequent replies. • Length: valid range: 20 – 4096. • Authenticator: used to conceal passwords using one way MD 5. Request (random number) / Response authenticators. RADIUS presentation by Sunil Vallamkonda 11
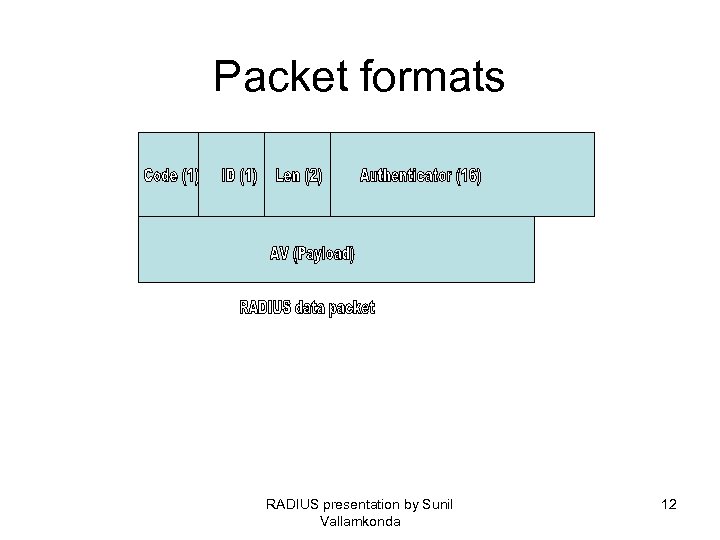 Packet formats RADIUS presentation by Sunil Vallamkonda 12
Packet formats RADIUS presentation by Sunil Vallamkonda 12
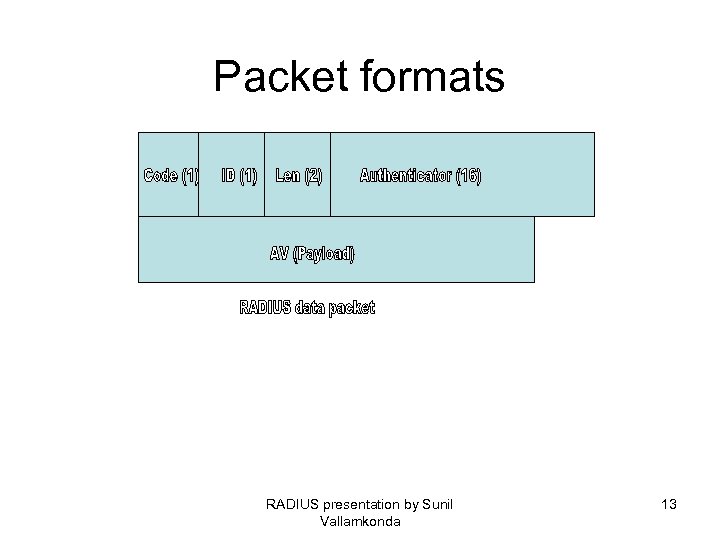 Packet formats RADIUS presentation by Sunil Vallamkonda 13
Packet formats RADIUS presentation by Sunil Vallamkonda 13
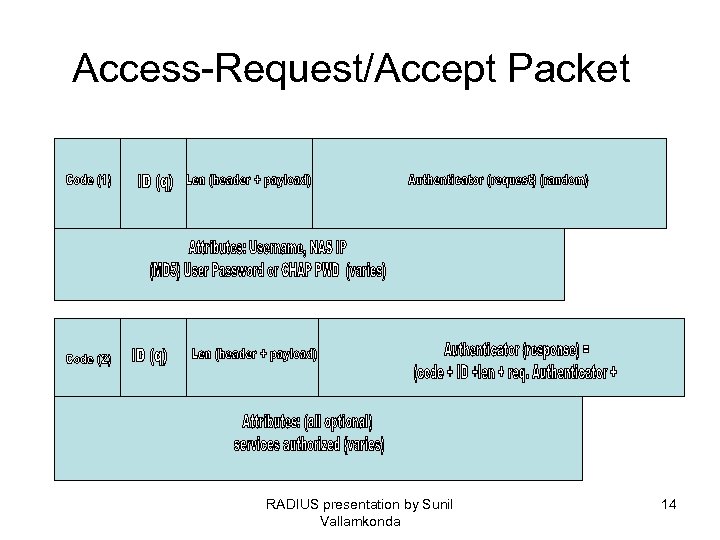 Access-Request/Accept Packet RADIUS presentation by Sunil Vallamkonda 14
Access-Request/Accept Packet RADIUS presentation by Sunil Vallamkonda 14
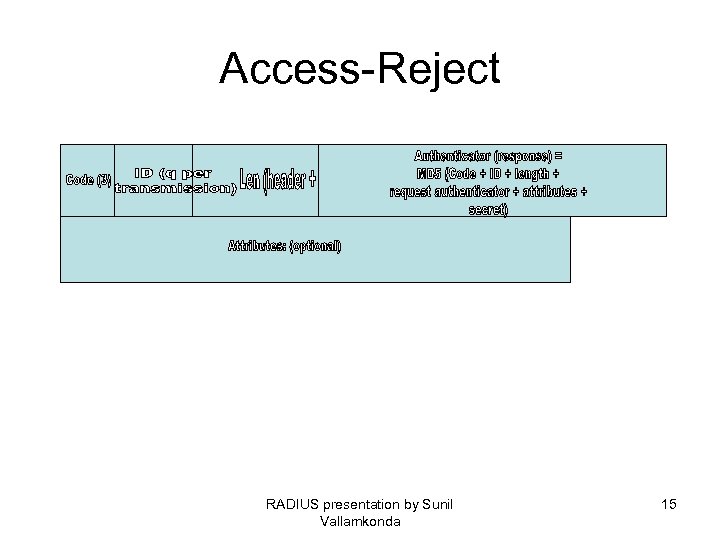 Access-Reject RADIUS presentation by Sunil Vallamkonda 15
Access-Reject RADIUS presentation by Sunil Vallamkonda 15
 Authentication methods • PAP: Password Authentication Protocol (MD 5/XOR). • CHAP: Challenge Access protocol: password is never sent on wire. • PAP is preferred sometimes in cases where authorization must travel outside the realm of control RADIUS presentation by Sunil Vallamkonda 16
Authentication methods • PAP: Password Authentication Protocol (MD 5/XOR). • CHAP: Challenge Access protocol: password is never sent on wire. • PAP is preferred sometimes in cases where authorization must travel outside the realm of control RADIUS presentation by Sunil Vallamkonda 16
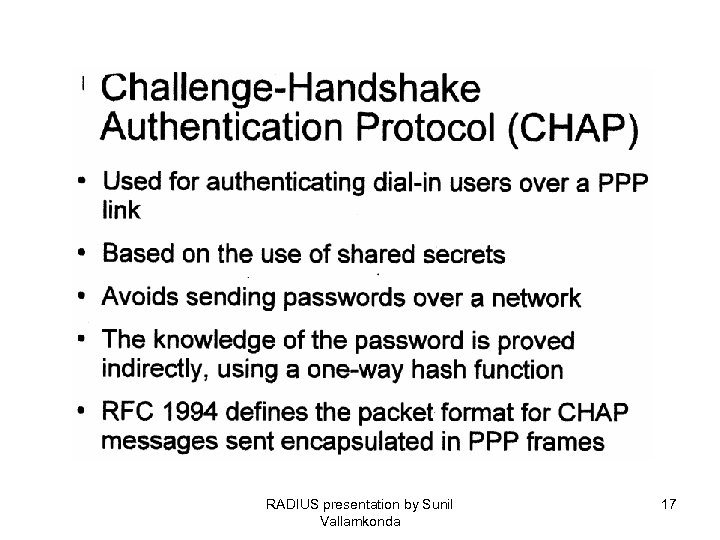 RADIUS presentation by Sunil Vallamkonda 17
RADIUS presentation by Sunil Vallamkonda 17
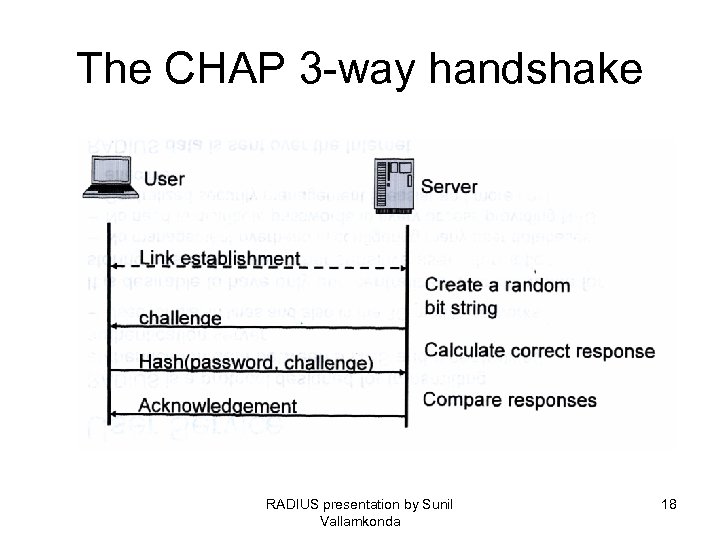 The CHAP 3 -way handshake RADIUS presentation by Sunil Vallamkonda 18
The CHAP 3 -way handshake RADIUS presentation by Sunil Vallamkonda 18
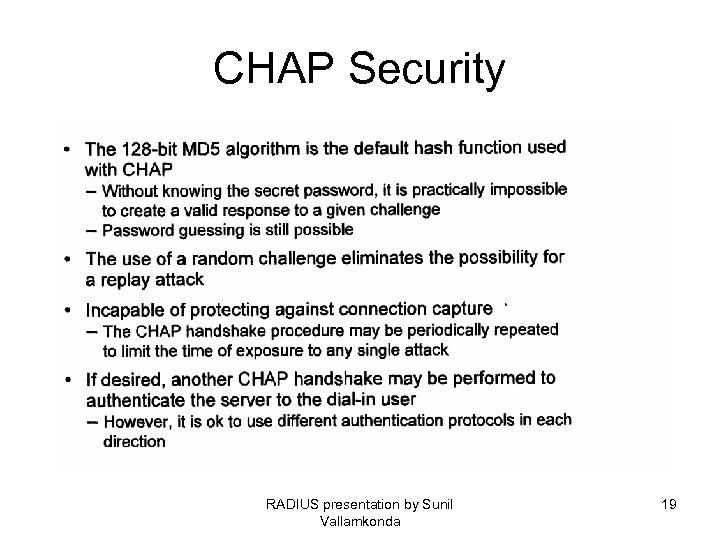 CHAP Security RADIUS presentation by Sunil Vallamkonda 19
CHAP Security RADIUS presentation by Sunil Vallamkonda 19
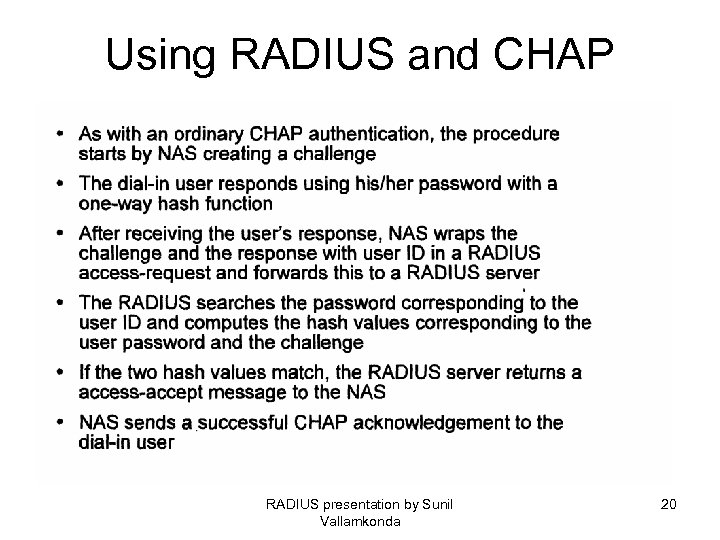 Using RADIUS and CHAP RADIUS presentation by Sunil Vallamkonda 20
Using RADIUS and CHAP RADIUS presentation by Sunil Vallamkonda 20
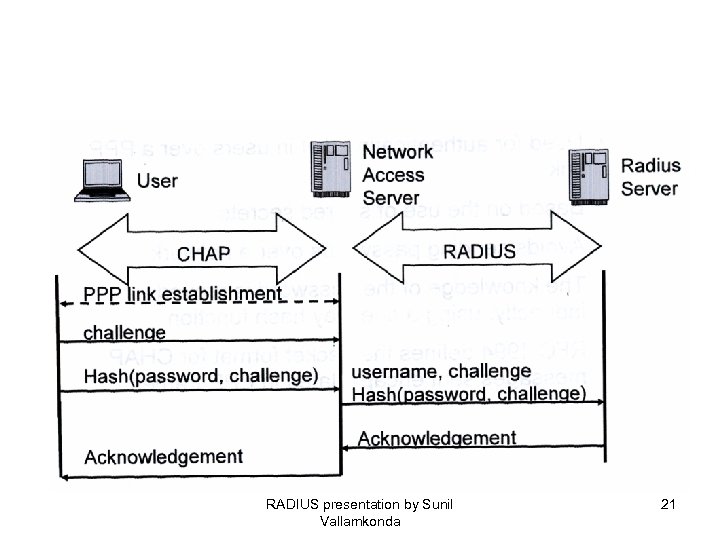 RADIUS presentation by Sunil Vallamkonda 21
RADIUS presentation by Sunil Vallamkonda 21
 Realm • Identifiers placed before or after values normally contained in User-Name attribute for server to identify which server to contact. • Examples: prefix realm such as @, , / as CSIjohn. • Suffix realms as: james@itmm RADIUS presentation by Sunil Vallamkonda 22
Realm • Identifiers placed before or after values normally contained in User-Name attribute for server to identify which server to contact. • Examples: prefix realm such as @, , / as CSIjohn. • Suffix realms as: james@itmm RADIUS presentation by Sunil Vallamkonda 22
 Hints • RADIUS can be setup to handle service authorizations based on hints. • To controls resources needed to provision service for client • Example: specific IP address, IP pool. • If NAS cannot allocate, service is disconnected. • Can be temporary, optional or extra characteristics. RADIUS presentation by Sunil Vallamkonda 23
Hints • RADIUS can be setup to handle service authorizations based on hints. • To controls resources needed to provision service for client • Example: specific IP address, IP pool. • If NAS cannot allocate, service is disconnected. • Can be temporary, optional or extra characteristics. RADIUS presentation by Sunil Vallamkonda 23
 Attributes • • • Describe a property of type of service. RADIUS attributes vs VSA. RADIUS attribute types (RFC): INT (4, 32 bit unsigned), ENUM(4, 32 bit unsigned), IPADDR (4, 32 bit) , STRING (1 -253, variable), DATE (4, 32 -bit unsigned), BINARY (1, 1 bit). Examples: INT: 6, 256 ENUM: 3 = callback-login, 4 = callback-Framed. STRING: “Charlotte”, “San Jose” IPADDR: 0 x 1954 ff 8 e DATE: 0 x 00000 a BINARY: 1 RADIUS presentation by Sunil Vallamkonda 24
Attributes • • • Describe a property of type of service. RADIUS attributes vs VSA. RADIUS attribute types (RFC): INT (4, 32 bit unsigned), ENUM(4, 32 bit unsigned), IPADDR (4, 32 bit) , STRING (1 -253, variable), DATE (4, 32 -bit unsigned), BINARY (1, 1 bit). Examples: INT: 6, 256 ENUM: 3 = callback-login, 4 = callback-Framed. STRING: “Charlotte”, “San Jose” IPADDR: 0 x 1954 ff 8 e DATE: 0 x 00000 a BINARY: 1 RADIUS presentation by Sunil Vallamkonda 24
 Attributes - example Standard: Example – call back-number Number: 19 Length: 3 or more octets Value: String Allowed in: Access-Request, Access-Accept Prohibited in: Access-Reject, Access-Challenge Maximum Iterations: 1 Presence in packet: not required RADIUS presentation by Sunil Vallamkonda 25
Attributes - example Standard: Example – call back-number Number: 19 Length: 3 or more octets Value: String Allowed in: Access-Request, Access-Accept Prohibited in: Access-Reject, Access-Challenge Maximum Iterations: 1 Presence in packet: not required RADIUS presentation by Sunil Vallamkonda 25
 Dictionary • Server machines has a way of relating which attribute corresponds to which attribute number and expected type. • Example: • Attribute-Name: User-Name, Type: String • Attribute-Name: NAS-IP-ADDR, Type: IPADDR • Attribute-Name: Service-Type, Type: ENUM RADIUS presentation by Sunil Vallamkonda 26
Dictionary • Server machines has a way of relating which attribute corresponds to which attribute number and expected type. • Example: • Attribute-Name: User-Name, Type: String • Attribute-Name: NAS-IP-ADDR, Type: IPADDR • Attribute-Name: Service-Type, Type: ENUM RADIUS presentation by Sunil Vallamkonda 26
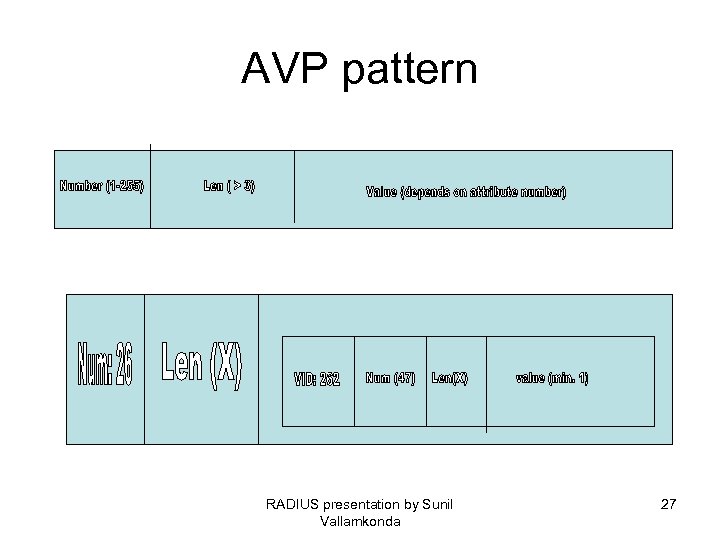 AVP pattern RADIUS presentation by Sunil Vallamkonda 27
AVP pattern RADIUS presentation by Sunil Vallamkonda 27
 Accounting • Client/Server model. • Extensible: proxy, defined and qualified by AVPs. • Packet: Accounting-Request Start/Stop. • Accounting- Response. RADIUS presentation by Sunil Vallamkonda 28
Accounting • Client/Server model. • Extensible: proxy, defined and qualified by AVPs. • Packet: Accounting-Request Start/Stop. • Accounting- Response. RADIUS presentation by Sunil Vallamkonda 28
 Ports • Authentication: udp/1812 • Accounting: udp/1813 RADIUS presentation by Sunil Vallamkonda 29
Ports • Authentication: udp/1812 • Accounting: udp/1813 RADIUS presentation by Sunil Vallamkonda 29
 Implementations • • Livingston GNU Free. RADIUS Cistron Radiator Alepo Juniper: Steel Belt. RADIUS presentation by Sunil Vallamkonda 30
Implementations • • Livingston GNU Free. RADIUS Cistron Radiator Alepo Juniper: Steel Belt. RADIUS presentation by Sunil Vallamkonda 30
 Performance • • Logons per second Logoffs per second Reject cause threshold Total packets per second per interface Load average Memory, disk usage RADIUS presentation by Sunil Vallamkonda 31
Performance • • Logons per second Logoffs per second Reject cause threshold Total packets per second per interface Load average Memory, disk usage RADIUS presentation by Sunil Vallamkonda 31
 EAP • Extensible Authentication Protocol • Used over links running on PPP • Authentication schemes such as public key, smart cards, OTP, Kerberos etc. are supported over PPP when EAP is used. • RADIUS includes 2 new attributes: EAPMessage and Message-Authenticator. RADIUS presentation by Sunil Vallamkonda 32
EAP • Extensible Authentication Protocol • Used over links running on PPP • Authentication schemes such as public key, smart cards, OTP, Kerberos etc. are supported over PPP when EAP is used. • RADIUS includes 2 new attributes: EAPMessage and Message-Authenticator. RADIUS presentation by Sunil Vallamkonda 32
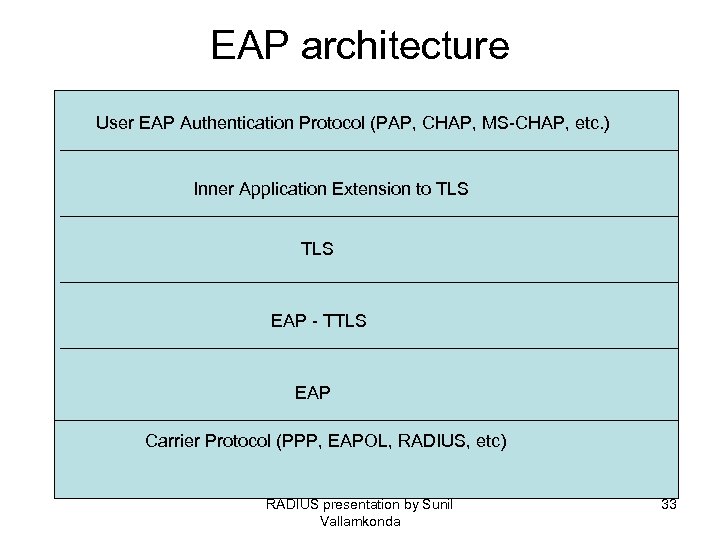 EAP architecture User EAP Authentication Protocol (PAP, CHAP, MS-CHAP, etc. ) Inner Application Extension to TLS EAP - TTLS EAP Carrier Protocol (PPP, EAPOL, RADIUS, etc) RADIUS presentation by Sunil Vallamkonda 33
EAP architecture User EAP Authentication Protocol (PAP, CHAP, MS-CHAP, etc. ) Inner Application Extension to TLS EAP - TTLS EAP Carrier Protocol (PPP, EAPOL, RADIUS, etc) RADIUS presentation by Sunil Vallamkonda 33
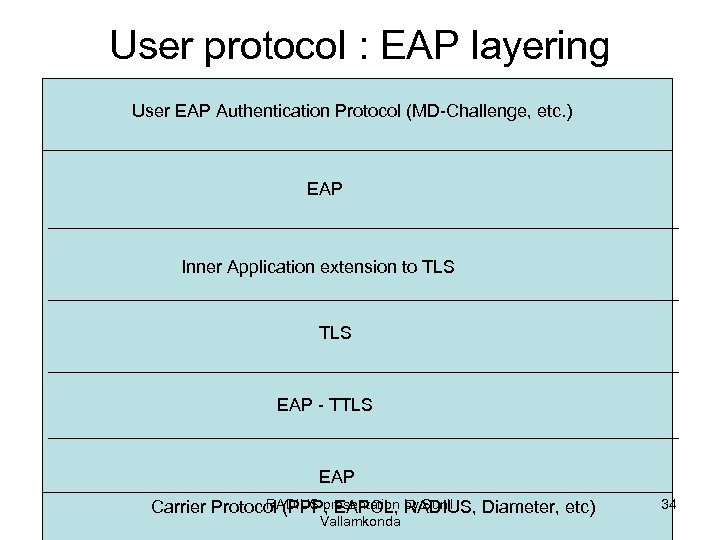 User protocol : EAP layering User EAP Authentication Protocol (MD-Challenge, etc. ) EAP Inner Application extension to TLS EAP - TTLS EAP RADIUS presentation RADIUS, Diameter, etc) Carrier Protocol (PPP, EAPOL, by Sunil Vallamkonda 34
User protocol : EAP layering User EAP Authentication Protocol (MD-Challenge, etc. ) EAP Inner Application extension to TLS EAP - TTLS EAP RADIUS presentation RADIUS, Diameter, etc) Carrier Protocol (PPP, EAPOL, by Sunil Vallamkonda 34
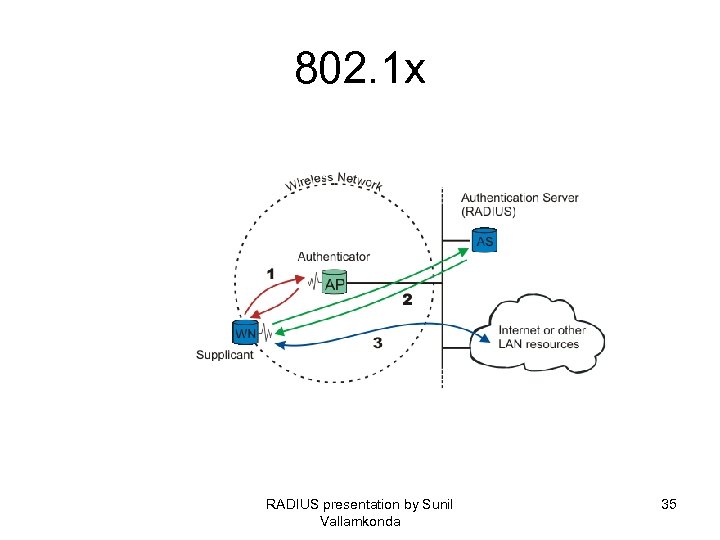 802. 1 x RADIUS presentation by Sunil Vallamkonda 35
802. 1 x RADIUS presentation by Sunil Vallamkonda 35
 Port based authentication • Why is it called "port"-based authentication? The Authenticator deals with controlled and uncontrolled ports. Both the controlled and the uncontrolled port are logical entities (virtual ports), but use the same physical connection to the LAN (same point of attachment). RADIUS presentation by Sunil Vallamkonda 36
Port based authentication • Why is it called "port"-based authentication? The Authenticator deals with controlled and uncontrolled ports. Both the controlled and the uncontrolled port are logical entities (virtual ports), but use the same physical connection to the LAN (same point of attachment). RADIUS presentation by Sunil Vallamkonda 36
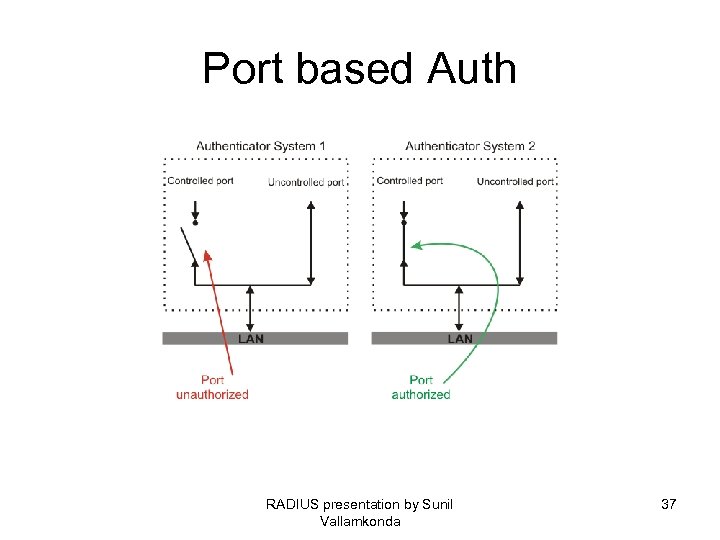 Port based Auth RADIUS presentation by Sunil Vallamkonda 37
Port based Auth RADIUS presentation by Sunil Vallamkonda 37
 contd • Figure port: The authorization state of the controlled port. • Before authentication, only the uncontrolled port is "open". The only traffic allowed is EAPOL; see Authenticator System 1 on figure port. After the Supplicant has been authenticated, the controlled port is opened, and access to other LAN resources are granted; see Authenticator System 2 on figure port. • 802. 1 X plays a major role in the new IEEE wireless standard 802. 11 i. RADIUS presentation by Sunil Vallamkonda 38
contd • Figure port: The authorization state of the controlled port. • Before authentication, only the uncontrolled port is "open". The only traffic allowed is EAPOL; see Authenticator System 1 on figure port. After the Supplicant has been authenticated, the controlled port is opened, and access to other LAN resources are granted; see Authenticator System 2 on figure port. • 802. 1 X plays a major role in the new IEEE wireless standard 802. 11 i. RADIUS presentation by Sunil Vallamkonda 38
 WEP • Wired Equivalent Privacy (WEP), which is part of the original 802. 11 standard, should provide confidentiality. Unfortunately WEP is poorly designed and easily cracked. There is no authentication mechanism, only a weak form of access control (must have the shared key to communicate). • As a response to WEP broken security, IEEE has come up with a new wireless security standard named 802. 11 i. 802. 1 X plays a major role in this new standard. • RADIUS presentation by Sunil Vallamkonda 39
WEP • Wired Equivalent Privacy (WEP), which is part of the original 802. 11 standard, should provide confidentiality. Unfortunately WEP is poorly designed and easily cracked. There is no authentication mechanism, only a weak form of access control (must have the shared key to communicate). • As a response to WEP broken security, IEEE has come up with a new wireless security standard named 802. 11 i. 802. 1 X plays a major role in this new standard. • RADIUS presentation by Sunil Vallamkonda 39
 802. 11 • The new security standard, 802. 11 i, which was ratified in June 2004, fixes all WEP weaknesses. It is divided into three main categories: • Temporary Key Integrity Protocol (TKIP) is a short-term solution that fixes all WEP weaknesses. TKIP can be used with old 802. 11 equipment (after a driver/firmware upgrade) and provides integrity and confidentiality. • Counter Mode with CBC-MAC Protocol (CCMP) [RFC 2610] is a new protocol, designed from ground up. It uses AES [FIPS 197] as its cryptographic algorithm, and, since this is more CPU intensive than RC 4 (used in WEP and TKIP), new 802. 11 hardware may be required. Some drivers can implement CCMP in software. CCMP provides integrity and confidentiality. • 802. 1 X Port-Based Network Access Control: Either when using TKIP or CCMP, 802. 1 X is used for authentication. In addition, an optional encryption method called "Wireless Robust Authentication Protocol" (WRAP) may be used instead of CCMP. WRAP was the original AES-based proposal for 802. 11 i, but was replaced by CCMP since it became plagued by property encumbrances. Support for WRAP is optional, but CCMP support is mandatory in 802. 11 i also has an extended key presentation by Sunil derivation/management. RADIUS 40 • • Vallamkonda
802. 11 • The new security standard, 802. 11 i, which was ratified in June 2004, fixes all WEP weaknesses. It is divided into three main categories: • Temporary Key Integrity Protocol (TKIP) is a short-term solution that fixes all WEP weaknesses. TKIP can be used with old 802. 11 equipment (after a driver/firmware upgrade) and provides integrity and confidentiality. • Counter Mode with CBC-MAC Protocol (CCMP) [RFC 2610] is a new protocol, designed from ground up. It uses AES [FIPS 197] as its cryptographic algorithm, and, since this is more CPU intensive than RC 4 (used in WEP and TKIP), new 802. 11 hardware may be required. Some drivers can implement CCMP in software. CCMP provides integrity and confidentiality. • 802. 1 X Port-Based Network Access Control: Either when using TKIP or CCMP, 802. 1 X is used for authentication. In addition, an optional encryption method called "Wireless Robust Authentication Protocol" (WRAP) may be used instead of CCMP. WRAP was the original AES-based proposal for 802. 11 i, but was replaced by CCMP since it became plagued by property encumbrances. Support for WRAP is optional, but CCMP support is mandatory in 802. 11 i also has an extended key presentation by Sunil derivation/management. RADIUS 40 • • Vallamkonda
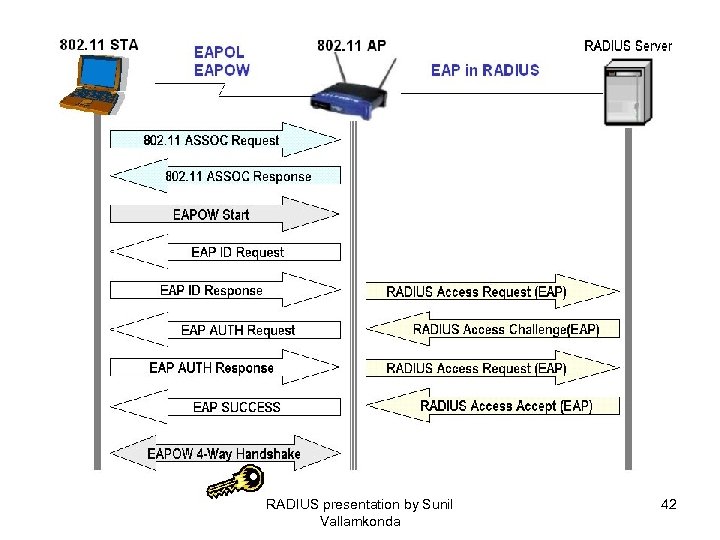
 802. 1 x • 802. 1 X takes advantage of an existing authentication protocol known as the Extensible Authentication Protocol (EAP [RFC 2284]). 802. 1 X takes EAP, which is written around PPP, and ties it to the physical medium, be it Ethernet, Token Ring or wireless LAN. EAP messages are encapsulated in 802. 1 X messages and referred to as EAPOL, or EAP over LAN. • 802. 1 X authentication for wireless LANs has three main components: The supplicant (usually the client software); the authenticator (usually the access point); and the authentication server (usually a Remote Authentication Dial-In User Service server, although RADIUS is not specifically required by 802. 1 X). RADIUS presentation by Sunil Vallamkonda 41
802. 1 x • 802. 1 X takes advantage of an existing authentication protocol known as the Extensible Authentication Protocol (EAP [RFC 2284]). 802. 1 X takes EAP, which is written around PPP, and ties it to the physical medium, be it Ethernet, Token Ring or wireless LAN. EAP messages are encapsulated in 802. 1 X messages and referred to as EAPOL, or EAP over LAN. • 802. 1 X authentication for wireless LANs has three main components: The supplicant (usually the client software); the authenticator (usually the access point); and the authentication server (usually a Remote Authentication Dial-In User Service server, although RADIUS is not specifically required by 802. 1 X). RADIUS presentation by Sunil Vallamkonda 41
 RADIUS presentation by Sunil Vallamkonda 42
RADIUS presentation by Sunil Vallamkonda 42
 8021. X and RADIUS • Remote Authentication Dial-In User Service (RADIUS) is defined in [RFC 2865] (with friends), and was primarily used by ISPs who authenticated username and password before the user got authorized to use the ISP's network. • 802. 1 X does not specify what kind of back-end authentication server must be present, but RADIUS is the "de-facto" back-end authentication server used in 802. 1 X. • There are not many AAA protocols available, but both RADIUS and DIAMETER [RFC 3588] (including their extensions) conform to full AAA support. AAA stands for Authentication, Authorization, and Accounting (IETF's AAA Working Group RADIUS presentation by Sunil Vallamkonda 43
8021. X and RADIUS • Remote Authentication Dial-In User Service (RADIUS) is defined in [RFC 2865] (with friends), and was primarily used by ISPs who authenticated username and password before the user got authorized to use the ISP's network. • 802. 1 X does not specify what kind of back-end authentication server must be present, but RADIUS is the "de-facto" back-end authentication server used in 802. 1 X. • There are not many AAA protocols available, but both RADIUS and DIAMETER [RFC 3588] (including their extensions) conform to full AAA support. AAA stands for Authentication, Authorization, and Accounting (IETF's AAA Working Group RADIUS presentation by Sunil Vallamkonda 43
 EAP methods • EAP-MD 5: MD 5 -Challenge requires username/password, and is equivalent to the PPP CHAP protocol [RFC 1994]. This method does not provide dictionary attack resistance, mutual authentication, or key derivation, and has therefore little use in a wireless authentication enviroment. • Lightweight EAP (LEAP): A username/password combination is sent to a Authentication Server (RADIUS) for authentication. Leap is a proprietary protocol developed by Cisco, and is not considered secure. Cisco is phasing out LEAP in favor of PEAP. Ref: http: //lists. cistron. nl/pipermail/cistron-radius/2001 September/002042. html RADIUS presentation by Sunil Vallamkonda 44
EAP methods • EAP-MD 5: MD 5 -Challenge requires username/password, and is equivalent to the PPP CHAP protocol [RFC 1994]. This method does not provide dictionary attack resistance, mutual authentication, or key derivation, and has therefore little use in a wireless authentication enviroment. • Lightweight EAP (LEAP): A username/password combination is sent to a Authentication Server (RADIUS) for authentication. Leap is a proprietary protocol developed by Cisco, and is not considered secure. Cisco is phasing out LEAP in favor of PEAP. Ref: http: //lists. cistron. nl/pipermail/cistron-radius/2001 September/002042. html RADIUS presentation by Sunil Vallamkonda 44
 EAP- methods (contd) • EAP-TLS: Creates a TLS session within EAP, between the Supplicant and the Authentication Server. Both the server and the client(s) need a valid (x 509) certificate, and therefore a PKI. This method provides authentication both ways. EAPTLS is described in [RFC 2716]. • EAP-TTLS: Sets up a encrypted TLS-tunnel for safe transport of authentication data. Within the TLS tunnel, (any) other authentication methods may be used. Developed by Funk Software and Meetinghouse, and is currently an IETF draft. RADIUS presentation by Sunil Vallamkonda 45
EAP- methods (contd) • EAP-TLS: Creates a TLS session within EAP, between the Supplicant and the Authentication Server. Both the server and the client(s) need a valid (x 509) certificate, and therefore a PKI. This method provides authentication both ways. EAPTLS is described in [RFC 2716]. • EAP-TTLS: Sets up a encrypted TLS-tunnel for safe transport of authentication data. Within the TLS tunnel, (any) other authentication methods may be used. Developed by Funk Software and Meetinghouse, and is currently an IETF draft. RADIUS presentation by Sunil Vallamkonda 45
 Methods (contd) • Protected EAP (PEAP): Uses, as EAP-TTLS, an encrypted TLS-tunnel. Supplicant certificates for both EAP-TTLS and EAP-PEAP are optional, but server (AS) certificates are required. Developed by Microsoft, Cisco, and RSA Security, and is currently an IETF draft. • EAP-MSCHAPv 2: Requires username/password, and is basically an EAP encapsulation of MS-CHAP-v 2 [RFC 2759]. Usually used inside of a PEAP-encrypted tunnel. Developed by Microsoft, and is currently an IETF draft. RADIUS presentation by Sunil Vallamkonda 46
Methods (contd) • Protected EAP (PEAP): Uses, as EAP-TTLS, an encrypted TLS-tunnel. Supplicant certificates for both EAP-TTLS and EAP-PEAP are optional, but server (AS) certificates are required. Developed by Microsoft, Cisco, and RSA Security, and is currently an IETF draft. • EAP-MSCHAPv 2: Requires username/password, and is basically an EAP encapsulation of MS-CHAP-v 2 [RFC 2759]. Usually used inside of a PEAP-encrypted tunnel. Developed by Microsoft, and is currently an IETF draft. RADIUS presentation by Sunil Vallamkonda 46
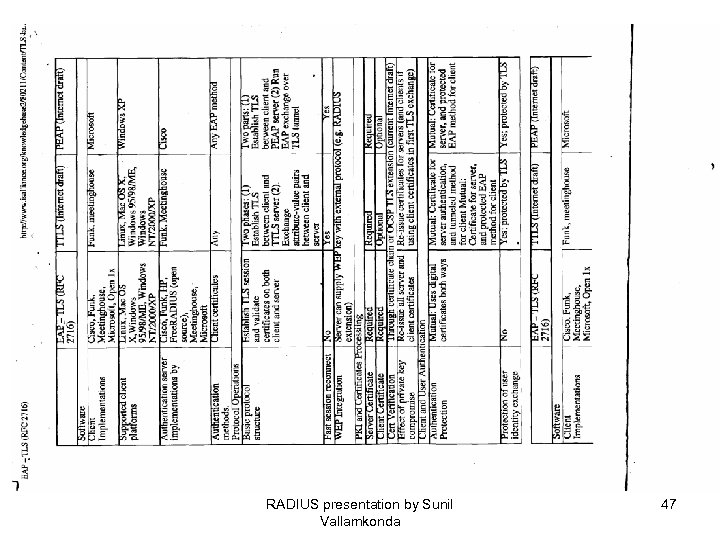 RADIUS presentation by Sunil Vallamkonda 47
RADIUS presentation by Sunil Vallamkonda 47
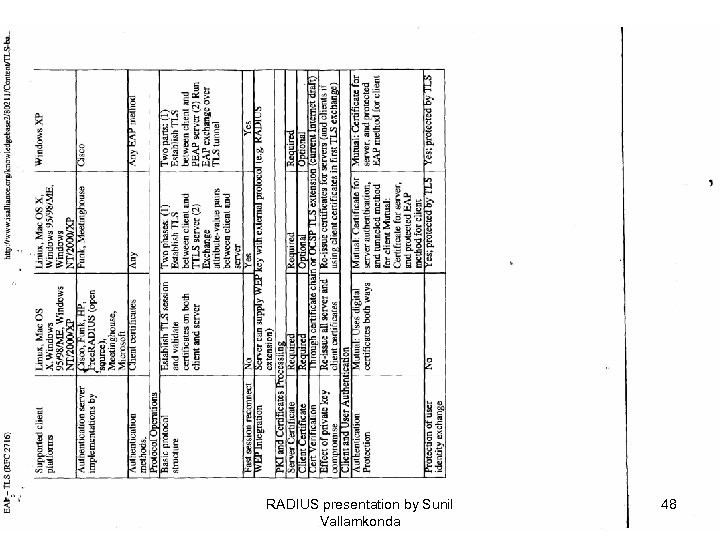 RADIUS presentation by Sunil Vallamkonda 48
RADIUS presentation by Sunil Vallamkonda 48
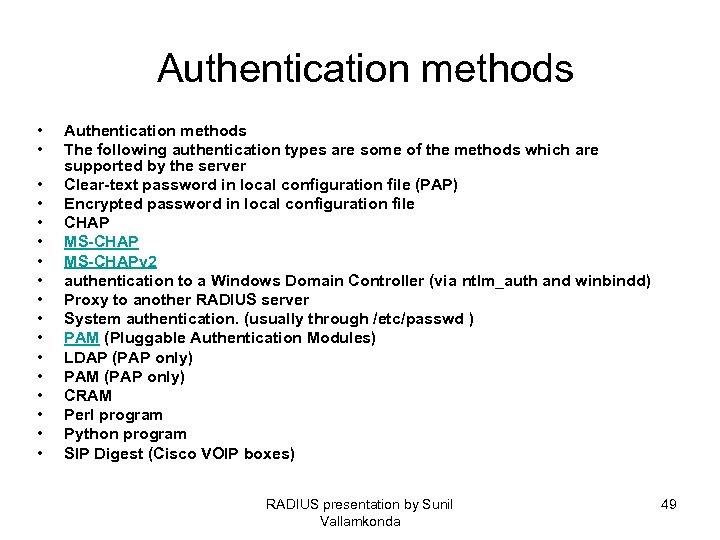 Authentication methods • • • • • Authentication methods The following authentication types are some of the methods which are supported by the server Clear-text password in local configuration file (PAP) Encrypted password in local configuration file CHAP MS-CHAPv 2 authentication to a Windows Domain Controller (via ntlm_auth and winbindd) Proxy to another RADIUS server System authentication. (usually through /etc/passwd ) PAM (Pluggable Authentication Modules) LDAP (PAP only) PAM (PAP only) CRAM Perl program Python program SIP Digest (Cisco VOIP boxes) RADIUS presentation by Sunil Vallamkonda 49
Authentication methods • • • • • Authentication methods The following authentication types are some of the methods which are supported by the server Clear-text password in local configuration file (PAP) Encrypted password in local configuration file CHAP MS-CHAPv 2 authentication to a Windows Domain Controller (via ntlm_auth and winbindd) Proxy to another RADIUS server System authentication. (usually through /etc/passwd ) PAM (Pluggable Authentication Modules) LDAP (PAP only) PAM (PAP only) CRAM Perl program Python program SIP Digest (Cisco VOIP boxes) RADIUS presentation by Sunil Vallamkonda 49
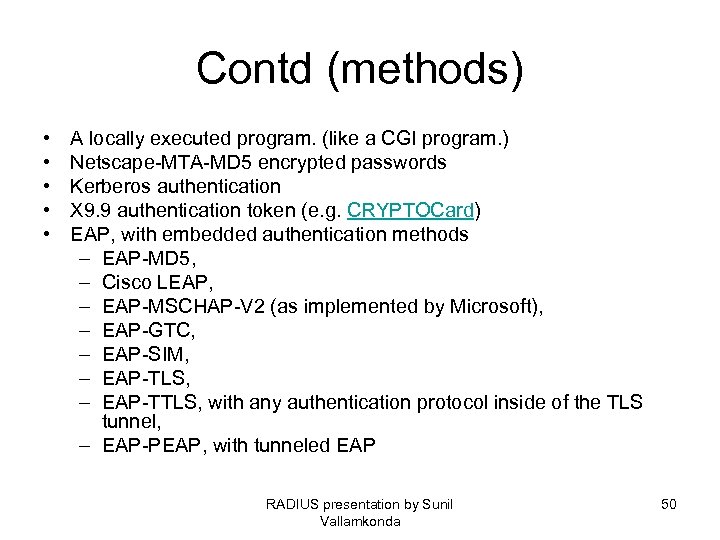 Contd (methods) • • • A locally executed program. (like a CGI program. ) Netscape-MTA-MD 5 encrypted passwords Kerberos authentication X 9. 9 authentication token (e. g. CRYPTOCard) EAP, with embedded authentication methods – EAP-MD 5, – Cisco LEAP, – EAP-MSCHAP-V 2 (as implemented by Microsoft), – EAP-GTC, – EAP-SIM, – EAP-TLS, – EAP-TTLS, with any authentication protocol inside of the TLS tunnel, – EAP-PEAP, with tunneled EAP RADIUS presentation by Sunil Vallamkonda 50
Contd (methods) • • • A locally executed program. (like a CGI program. ) Netscape-MTA-MD 5 encrypted passwords Kerberos authentication X 9. 9 authentication token (e. g. CRYPTOCard) EAP, with embedded authentication methods – EAP-MD 5, – Cisco LEAP, – EAP-MSCHAP-V 2 (as implemented by Microsoft), – EAP-GTC, – EAP-SIM, – EAP-TLS, – EAP-TTLS, with any authentication protocol inside of the TLS tunnel, – EAP-PEAP, with tunneled EAP RADIUS presentation by Sunil Vallamkonda 50
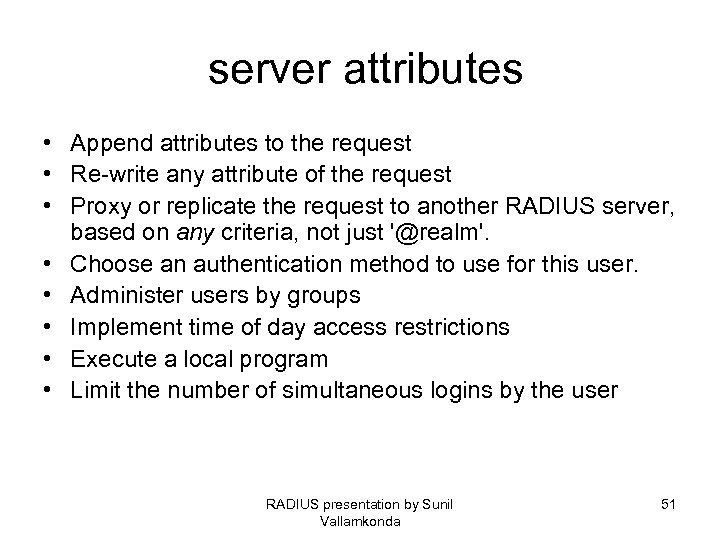 server attributes • Append attributes to the request • Re-write any attribute of the request • Proxy or replicate the request to another RADIUS server, based on any criteria, not just '@realm'. • Choose an authentication method to use for this user. • Administer users by groups • Implement time of day access restrictions • Execute a local program • Limit the number of simultaneous logins by the user RADIUS presentation by Sunil Vallamkonda 51
server attributes • Append attributes to the request • Re-write any attribute of the request • Proxy or replicate the request to another RADIUS server, based on any criteria, not just '@realm'. • Choose an authentication method to use for this user. • Administer users by groups • Implement time of day access restrictions • Execute a local program • Limit the number of simultaneous logins by the user RADIUS presentation by Sunil Vallamkonda 51
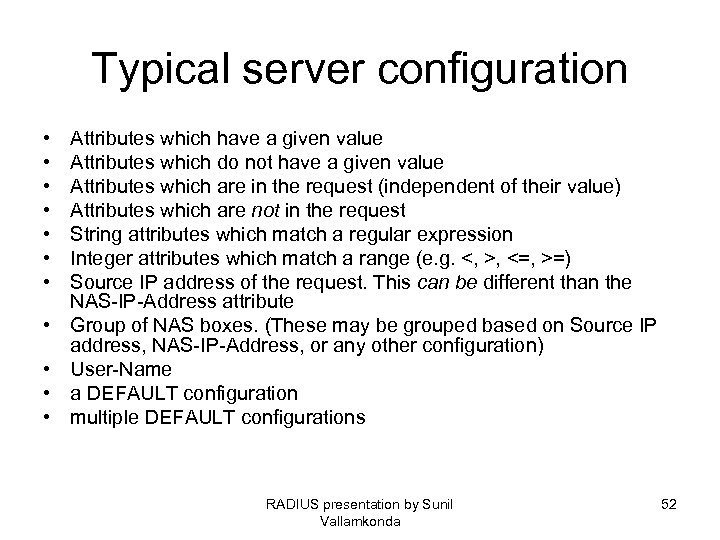 Typical server configuration • • • Attributes which have a given value Attributes which do not have a given value Attributes which are in the request (independent of their value) Attributes which are not in the request String attributes which match a regular expression Integer attributes which match a range (e. g. <, >, <=, >=) Source IP address of the request. This can be different than the NAS-IP-Address attribute Group of NAS boxes. (These may be grouped based on Source IP address, NAS-IP-Address, or any other configuration) User-Name a DEFAULT configuration multiple DEFAULT configurations RADIUS presentation by Sunil Vallamkonda 52
Typical server configuration • • • Attributes which have a given value Attributes which do not have a given value Attributes which are in the request (independent of their value) Attributes which are not in the request String attributes which match a regular expression Integer attributes which match a range (e. g. <, >, <=, >=) Source IP address of the request. This can be different than the NAS-IP-Address attribute Group of NAS boxes. (These may be grouped based on Source IP address, NAS-IP-Address, or any other configuration) User-Name a DEFAULT configuration multiple DEFAULT configurations RADIUS presentation by Sunil Vallamkonda 52
 Databases • • • Oracle Informix Sybase m. SQL My. SQL Microsoft SQL including versions 6. 5, 7 and 2000 ODBC Interbase SAP Postgre. SQLite RADIUS presentation by Sunil Vallamkonda 53
Databases • • • Oracle Informix Sybase m. SQL My. SQL Microsoft SQL including versions 6. 5, 7 and 2000 ODBC Interbase SAP Postgre. SQLite RADIUS presentation by Sunil Vallamkonda 53
 Authorization methods • • • Local files Local DB/DBM database LDAP A locally executed program. (like a CGI program. ) Perl program Python program My. SQL DB Postgre. SQL DB Oracle SQL DB any IODBC SQL DB IBM's DB 2 RADIUS presentation by Sunil Vallamkonda 54
Authorization methods • • • Local files Local DB/DBM database LDAP A locally executed program. (like a CGI program. ) Perl program Python program My. SQL DB Postgre. SQL DB Oracle SQL DB any IODBC SQL DB IBM's DB 2 RADIUS presentation by Sunil Vallamkonda 54
 Accounting methods • • • Local 'detail' files Local 'wtmp' and 'utmp' files Proxy to another RADIUS server Replicate to one or more RADIUS servers SQL (Oracle, My. SQL, Postgre. SQL, Sybase, IODBC, etc) RADIUS presentation by Sunil Vallamkonda 55
Accounting methods • • • Local 'detail' files Local 'wtmp' and 'utmp' files Proxy to another RADIUS server Replicate to one or more RADIUS servers SQL (Oracle, My. SQL, Postgre. SQL, Sybase, IODBC, etc) RADIUS presentation by Sunil Vallamkonda 55
 Tools • Users in LDAP database • Users and Groups in SQL database (My. SQL or Postgre. SQL) • Create, test, delete, change personal information, check accounting and change dialup settings for a user • Accounting Report Generator • Bad Users facility to keep a record of users creating problems • Online finger facility , Test radius server • Online Usage Statistics • Perl, Python • Configufration GUI RADIUS presentation by Sunil Vallamkonda 56
Tools • Users in LDAP database • Users and Groups in SQL database (My. SQL or Postgre. SQL) • Create, test, delete, change personal information, check accounting and change dialup settings for a user • Accounting Report Generator • Bad Users facility to keep a record of users creating problems • Online finger facility , Test radius server • Online Usage Statistics • Perl, Python • Configufration GUI RADIUS presentation by Sunil Vallamkonda 56
 Other features • Can optionally act as a TACACS+ server, converting TACACS+ requests into RADIUS requests • Optional tunnelling of Radius requests using SOAP over HTTP or HTTPS for improved security. • SNMP support for the IETF Radius Server MIB: gather server stats with SNMP RADIUS presentation by Sunil Vallamkonda 57
Other features • Can optionally act as a TACACS+ server, converting TACACS+ requests into RADIUS requests • Optional tunnelling of Radius requests using SOAP over HTTP or HTTPS for improved security. • SNMP support for the IETF Radius Server MIB: gather server stats with SNMP RADIUS presentation by Sunil Vallamkonda 57
 Features (contd) • Web reports for usage analysis users sessions details. Allows your administrators and customers to see usage information on a web page and drill down to connection details. • Block authentication according to time of day and day of week, and force disconnection at the end of valid time blocks. RADIUS presentation by Sunil Vallamkonda 58
Features (contd) • Web reports for usage analysis users sessions details. Allows your administrators and customers to see usage information on a web page and drill down to connection details. • Block authentication according to time of day and day of week, and force disconnection at the end of valid time blocks. RADIUS presentation by Sunil Vallamkonda 58
 Token based • • Encotone tel. ID RSA Secur. ID Safeword VASCO Digipass RADIUS presentation by Sunil Vallamkonda 59
Token based • • Encotone tel. ID RSA Secur. ID Safeword VASCO Digipass RADIUS presentation by Sunil Vallamkonda 59
 Platforms • Solaris • Unix including Linux (Red Hat, Debian, Mandrake, Su. SE, Lindows, Slackware, Ubuntu etc on Intel, Sparc, PPC, HP-PA etc), Solaris (Intel and Sparc), Free. BSD, Net. BSD, Sun. OS, AIX, IRIX, SCO Open Server, Digital, HP-UX, etc • Windows 95, 98, NT, 2000, ME, XP, 2003, etc. • Mac OS 9, Mac OS X. • Novell Open Enterprise Server (Net. Ware) 6. 5 • VMS RADIUS presentation by Sunil Vallamkonda 60
Platforms • Solaris • Unix including Linux (Red Hat, Debian, Mandrake, Su. SE, Lindows, Slackware, Ubuntu etc on Intel, Sparc, PPC, HP-PA etc), Solaris (Intel and Sparc), Free. BSD, Net. BSD, Sun. OS, AIX, IRIX, SCO Open Server, Digital, HP-UX, etc • Windows 95, 98, NT, 2000, ME, XP, 2003, etc. • Mac OS 9, Mac OS X. • Novell Open Enterprise Server (Net. Ware) 6. 5 • VMS RADIUS presentation by Sunil Vallamkonda 60
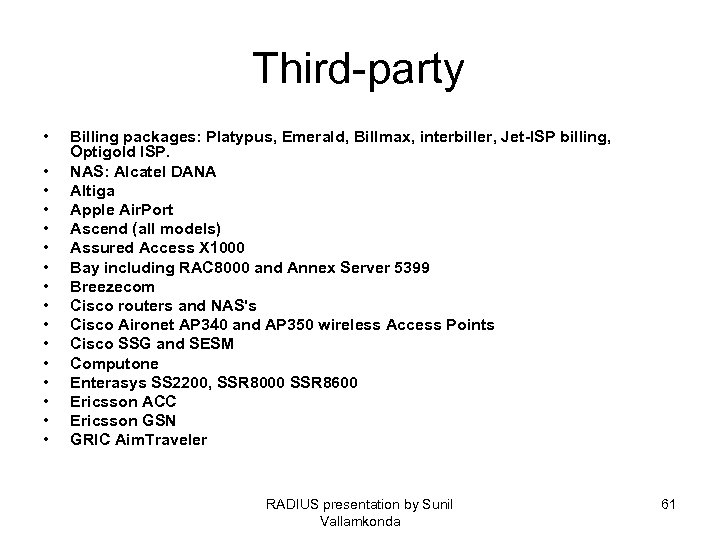 Third-party • • • • Billing packages: Platypus, Emerald, Billmax, interbiller, Jet-ISP billing, Optigold ISP. NAS: Alcatel DANA Altiga Apple Air. Port Ascend (all models) Assured Access X 1000 Bay including RAC 8000 and Annex Server 5399 Breezecom Cisco routers and NAS's Cisco Aironet AP 340 and AP 350 wireless Access Points Cisco SSG and SESM Computone Enterasys SS 2200, SSR 8000 SSR 8600 Ericsson ACC Ericsson GSN GRIC Aim. Traveler RADIUS presentation by Sunil Vallamkonda 61
Third-party • • • • Billing packages: Platypus, Emerald, Billmax, interbiller, Jet-ISP billing, Optigold ISP. NAS: Alcatel DANA Altiga Apple Air. Port Ascend (all models) Assured Access X 1000 Bay including RAC 8000 and Annex Server 5399 Breezecom Cisco routers and NAS's Cisco Aironet AP 340 and AP 350 wireless Access Points Cisco SSG and SESM Computone Enterasys SS 2200, SSR 8000 SSR 8600 Ericsson ACC Ericsson GSN GRIC Aim. Traveler RADIUS presentation by Sunil Vallamkonda 61
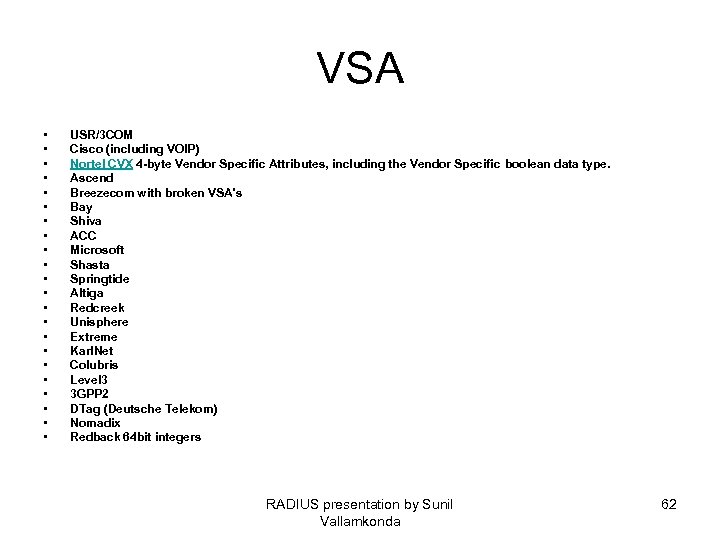 VSA • • • • • • USR/3 COM Cisco (including VOIP) Nortel CVX 4 -byte Vendor Specific Attributes, including the Vendor Specific boolean data type. Ascend Breezecom with broken VSA's Bay Shiva ACC Microsoft Shasta Springtide Altiga Redcreek Unisphere Extreme Karl. Net Colubris Level 3 3 GPP 2 DTag (Deutsche Telekom) Nomadix Redback 64 bit integers RADIUS presentation by Sunil Vallamkonda 62
VSA • • • • • • USR/3 COM Cisco (including VOIP) Nortel CVX 4 -byte Vendor Specific Attributes, including the Vendor Specific boolean data type. Ascend Breezecom with broken VSA's Bay Shiva ACC Microsoft Shasta Springtide Altiga Redcreek Unisphere Extreme Karl. Net Colubris Level 3 3 GPP 2 DTag (Deutsche Telekom) Nomadix Redback 64 bit integers RADIUS presentation by Sunil Vallamkonda 62
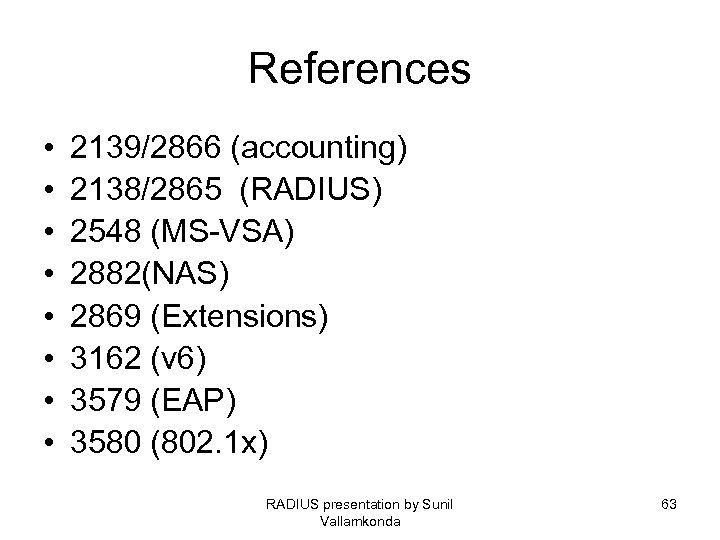 References • • 2139/2866 (accounting) 2138/2865 (RADIUS) 2548 (MS-VSA) 2882(NAS) 2869 (Extensions) 3162 (v 6) 3579 (EAP) 3580 (802. 1 x) RADIUS presentation by Sunil Vallamkonda 63
References • • 2139/2866 (accounting) 2138/2865 (RADIUS) 2548 (MS-VSA) 2882(NAS) 2869 (Extensions) 3162 (v 6) 3579 (EAP) 3580 (802. 1 x) RADIUS presentation by Sunil Vallamkonda 63
 References (contd) • http: //tools. ietf. org/wg/eap/draft-funk-eapttls-v 1 -01. txt • http: //www. microsoft. com/technet/commun ity/columns/cableguy/cg 0702. mspx • http: //www. oreillynet. com/pub/a/wireless/2 002/10/17/peap. html • http: //www. wifiplanet. com/tutorials/article. php/3073201 RADIUS presentation by Sunil Vallamkonda 64
References (contd) • http: //tools. ietf. org/wg/eap/draft-funk-eapttls-v 1 -01. txt • http: //www. microsoft. com/technet/commun ity/columns/cableguy/cg 0702. mspx • http: //www. oreillynet. com/pub/a/wireless/2 002/10/17/peap. html • http: //www. wifiplanet. com/tutorials/article. php/3073201 RADIUS presentation by Sunil Vallamkonda 64
 Future • Diameter: RFC 3588 • IPv 6 and RADIUS: RFC 3162 Contact: sunil_vall@yahoo. com RADIUS presentation by Sunil Vallamkonda 65
Future • Diameter: RFC 3588 • IPv 6 and RADIUS: RFC 3162 Contact: sunil_vall@yahoo. com RADIUS presentation by Sunil Vallamkonda 65


