f95cfedc5a75335c18959bebe9018b27.ppt
- Количество слайдов: 33
Public Key Infrastructure and Authentication Mark Norman DCOCE Oxford University Computing Services 03 December 2003
DCOCE Der-kot-chee Digital Certificate Operation in a Complex Environment 03 December 2003
Authentication • The act of verifying that an electronic identity (username, login name etc. ) is being employed by the person to whom it was issued – Strictly it should mean "establishing the validity of something, such as an identity". (The procedure as indicated by the definition above is very difficult indeed. ) 03 December 2003
Authorisation • Associating rights or capabilities with a subject • Authorisation usually comes after authentication – i. e. once the service knows who it is (Authenticated), it then proceeds to decide what that person/subject can do (Authorisation) 03 December 2003
The DCOCE project • DCOCE is about authentication with digital certificates • Digital certificates use Public Key Infrastructure (PKI) – PKI is very secure – but can be difficult to administer – and a lot of people don't understand it too well 03 December 2003
The DCOCE project • Digital certificates and PKI rely upon trust • Trust relies upon co-operation (or understanding) between organisations • Oxford University is a Complex Environment – DCOCE – If it can work here. . . • But let's get back to PKI and how it works 03 December 2003
PKI • (Public Key Infrastructure) • A key is like a code sheet • A public key is an odd concept – why would you reveal your secret code in public? • We need to understand symmetric keys and asymmetric keys 03 December 2003
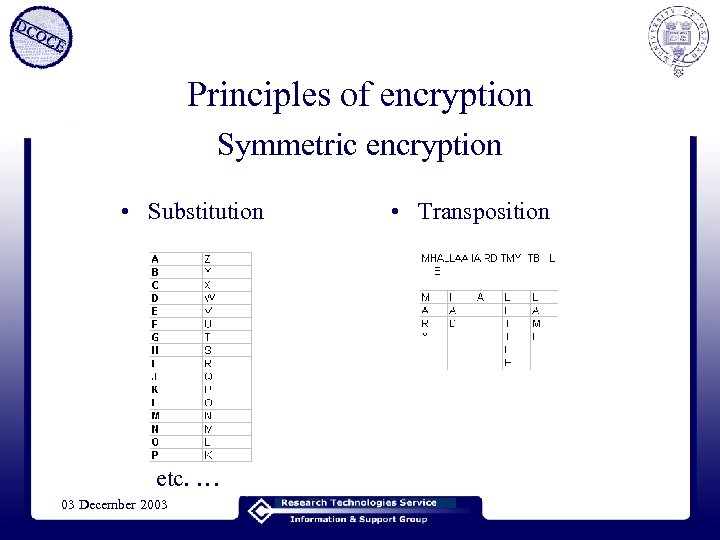
Principles of encryption Symmetric encryption • Substitution etc. … 03 December 2003 • Transposition
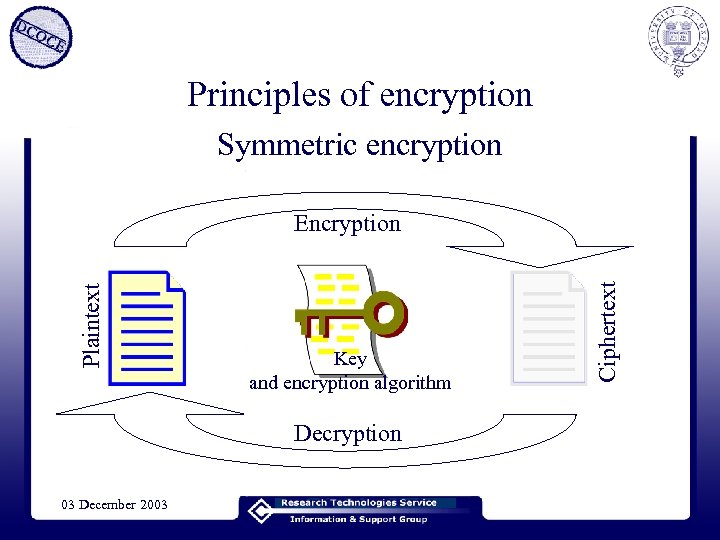
Principles of encryption Symmetric encryption Key and encryption algorithm Decryption 03 December 2003 Ciphertext Plaintext Encryption
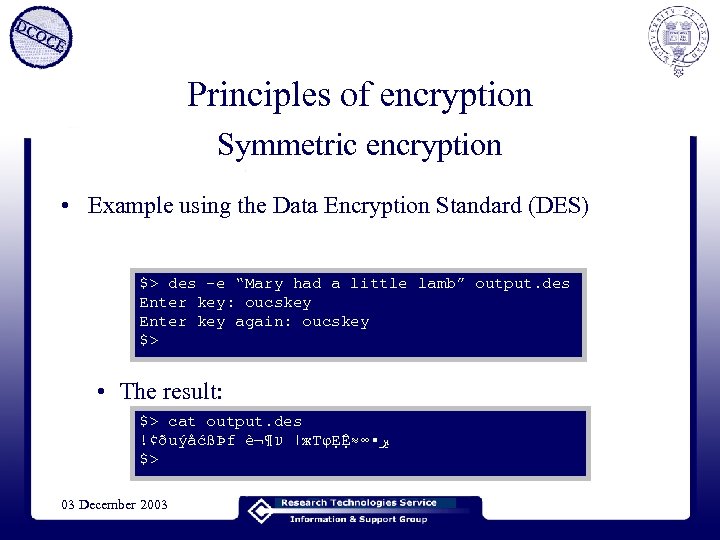
Principles of encryption Symmetric encryption • Example using the Data Encryption Standard (DES) $> des -e “Mary had a little lamb” output. des Enter key: oucskey Enter key again: oucskey $> • The result: $> cat output. des !¢ðuýåćßÞf 謶 ׀ ע ж. ТφẸỆ≈∞▪ ﲑ $> 03 December 2003
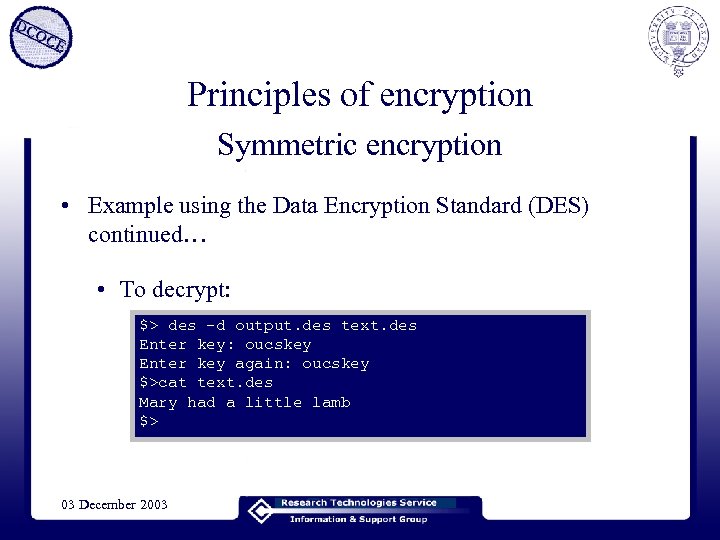
Principles of encryption Symmetric encryption • Example using the Data Encryption Standard (DES) continued… • To decrypt: $> des -d output. des text. des Enter key: oucskey Enter key again: oucskey $>cat text. des Mary had a little lamb $> 03 December 2003
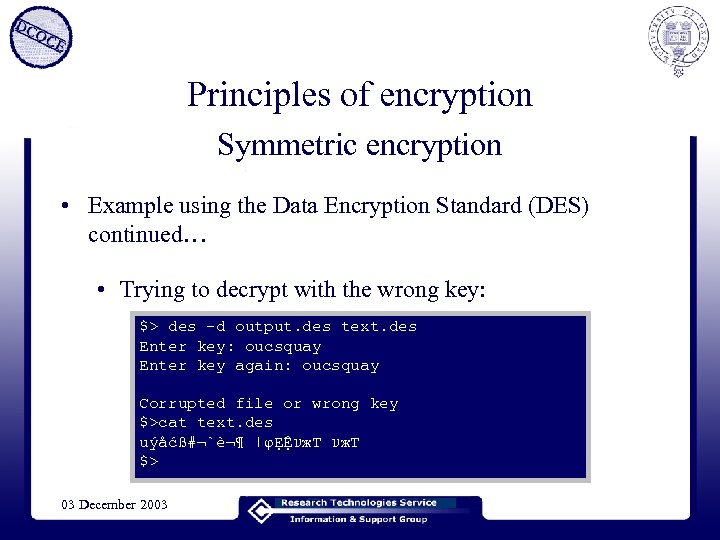
Principles of encryption Symmetric encryption • Example using the Data Encryption Standard (DES) continued… • Trying to decrypt with the wrong key: $> des -d output. des text. des Enter key: oucsquay Enter key again: oucsquay Corrupted file or wrong key $>cat text. des uýåćß#¬`謶 ׀ φẸỆ ע ж. Т $> 03 December 2003
Principles of encryption Symmetric encryption • So you have to have the same key as your correspondent – how do you send the key safely? • You also have to tell your correspondent the algorithm! – (not necessarily a problem) • How do you transmit these things in the first place? 03 December 2003
Principles of encryption Symmetric encryption • How safe are encryption algorithms anyway? • Example using (DES) continued… • What about a ‘brute force’ attack? i. e. ‘guessing’ at the key “oucskey” • DES algorithm has a 56 -bit key. Therefore, there are 256 = 72, 057, 594, 037, 900, 000 different keys • 834 days at a billion keys per second • But for a typed key, effectively 968 (83 days) 03 December 2003
Principles of encryption Symmetric encryption • How safe are encryption algorithms anyway? – A good algorithm is sound – Safety is dependent on key length • Key distribution is problematic – but if you can, symmetric is fine! – except that you need a key for everyone you communicate with!! 03 December 2003
Principles of encryption • Then there was asymmetric encryption – Whitfield Diffie and Martin Hellman (1975) – Each party has two keys (public and private) – Anything encrypted with key 1 can only be decrypted with key 2 – Asymmetric! 03 December 2003
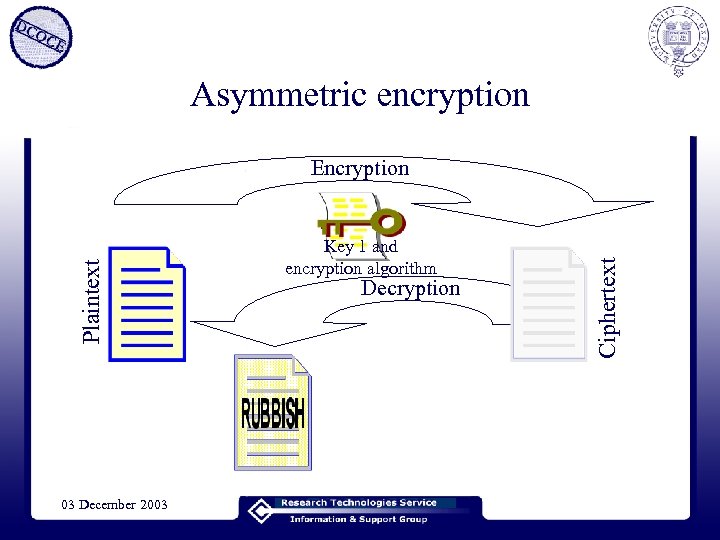
Asymmetric encryption 03 December 2003 Key 1 and encryption algorithm Decryption Ciphertext Plaintext Encryption
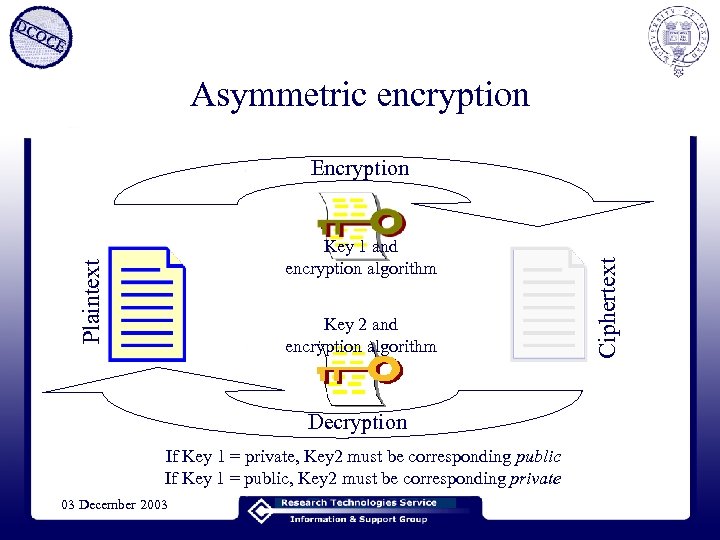
Asymmetric encryption Plaintext Key 1 and encryption algorithm Key 2 and encryption algorithm Decryption If Key 1 = private, Key 2 must be corresponding public If Key 1 = public, Key 2 must be corresponding private 03 December 2003 Ciphertext Encryption
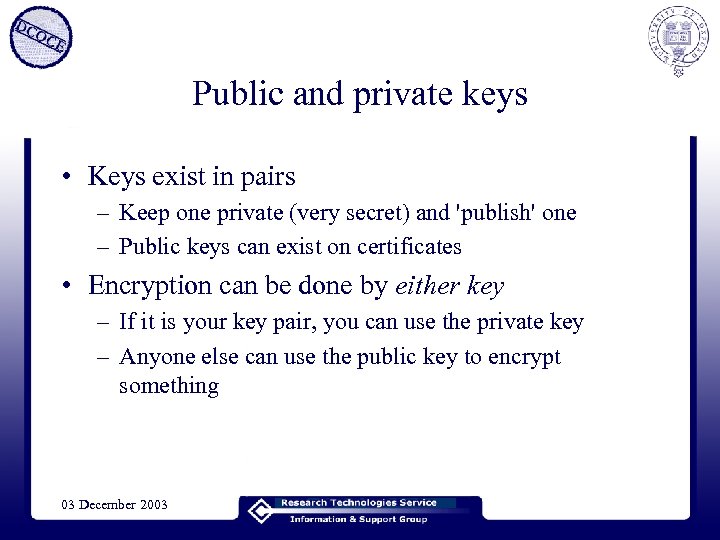
Public and private keys • Keys exist in pairs – Keep one private (very secret) and 'publish' one – Public keys can exist on certificates • Encryption can be done by either key – If it is your key pair, you can use the private key – Anyone else can use the public key to encrypt something 03 December 2003
Private keys • Extremely secret! • If you send something encrypted by a private key, it can be read by everyone, but they know it came from you. – Authentication 03 December 2003
Public keys • Not at all secret! – Widely available, but must be trusted – May be supplied as part of a certificate • If you send something using a public key, it can only be read by the entity to which it is addressed. – Secure communications • (But secure communications (e. g. SSL) isn’t quite as simple as that!) 03 December 2003
How can I trust a public key? • Someone can use a public key to prove their identity to me – but only if I trust that public key – there's public keys out there that say they belong to George Bush etc. • So if someone I trusted endorsed (signed) that public key – hold that thought for a moment. . . 03 December 2003
Signing things with keys • Keys can be used to sign things – encrypt a bit of text with your private key (can be attached 'securely' to the 'document') – people can de-crypt it with the public key and know that it was signed by you 03 December 2003
How can I trust a public key? • Put that public key on a certificate • Get someone you trust to sign the certificate – If the certificate is tampered with, the signature is broken • Organisations who sign public keys/certificates are called Certification Authorities (CA) 03 December 2003
Public Key Infrastructure • • You create a key pair Put one key of the pair on a certificate Send the certificate (request) to the CA Present yourself or identify yourself to the Registration Authority (RA) • The RA tells the CA that you are OK • The CA sends you the signed certificate 03 December 2003
Public Key Infrastructure • Now you have a signed certificate, people and services can trust that you are who you say you are • Present your certificate to a service • Tell them something encrypted by your private key • They like your certificate and know it is you 03 December 2003
Public Key Infrastructure • You keep your private key very secret – Obey the rules for this! • Your public key is on the certificate • Services must trust the CA • Your certificate will have an expiry date – after which you may have to re-visit the RA • Your certificate can be revoked at any time 03 December 2003
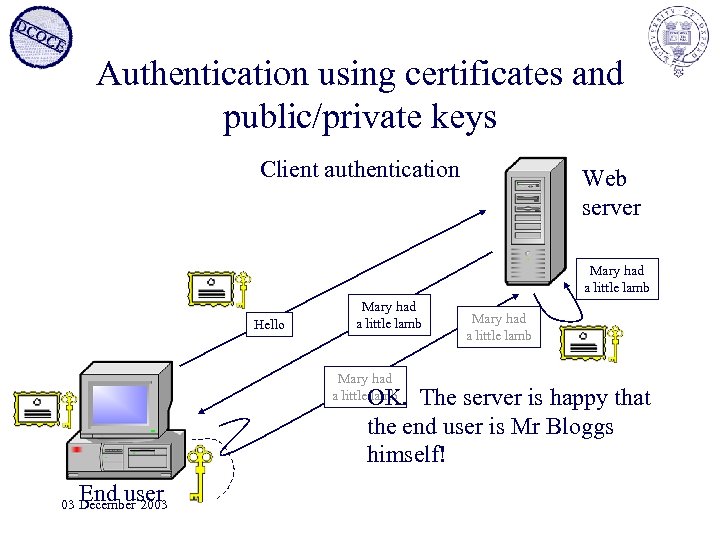
Authentication using certificates and public/private keys Client authentication Web server Mary had a little lamb Hello Mary had a little lamb OK. The server is happy that the end user is Mr Bloggs himself! End user 03 December 2003
Public Key Infrastructure • Asymmetric encryption = public/private keys • Symmetric encryption is faster – but how do you deliver the keys • Asymmetric encryption is used in SSL – Secure Sockets Layer, very common • Also used in client authentication (less common, at the moment) 03 December 2003
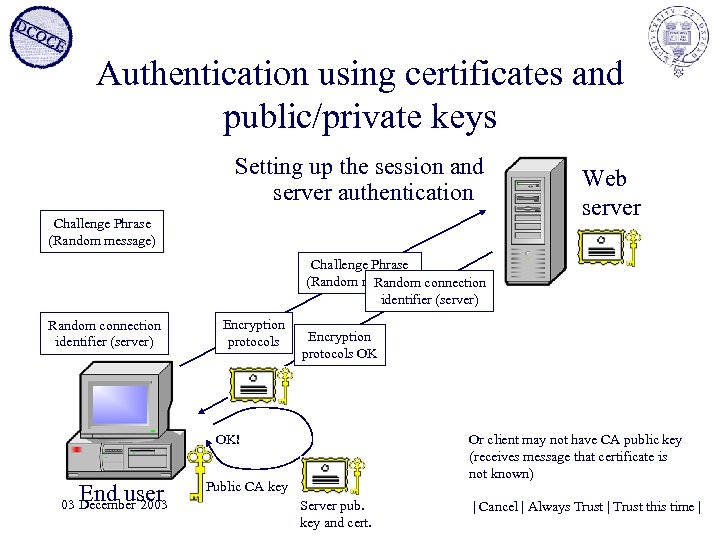
Authentication using certificates and public/private keys Setting up the session and server authentication Challenge Phrase (Random message) Web server Challenge Phrase (Random message) connection Random identifier (server) Random connection identifier (server) Encryption protocols OK OK! End user 03 December 2003 Or client may not have CA public key (receives message that certificate is not known) Public CA key Server pub. key and cert. | Cancel | Always Trust | Trust this time |
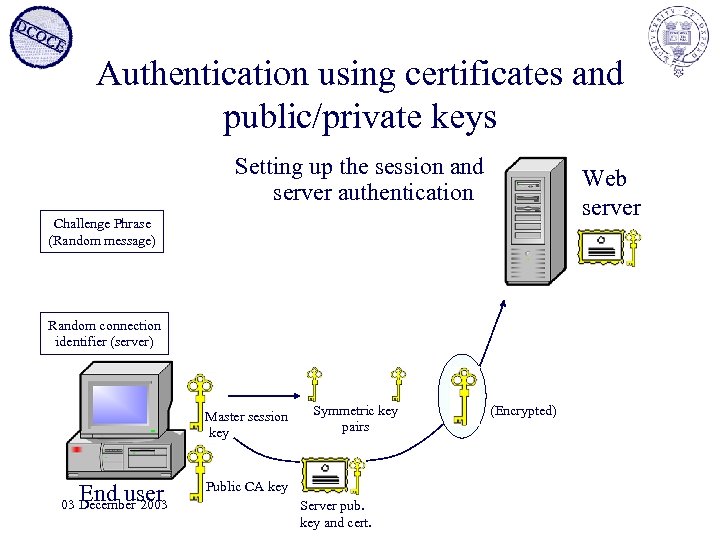
Authentication using certificates and public/private keys Setting up the session and server authentication Web server Challenge Phrase (Random message) Random connection identifier (server) Master session key End user 03 December 2003 Symmetric key pairs Public CA key Server pub. key and cert. (Encrypted)
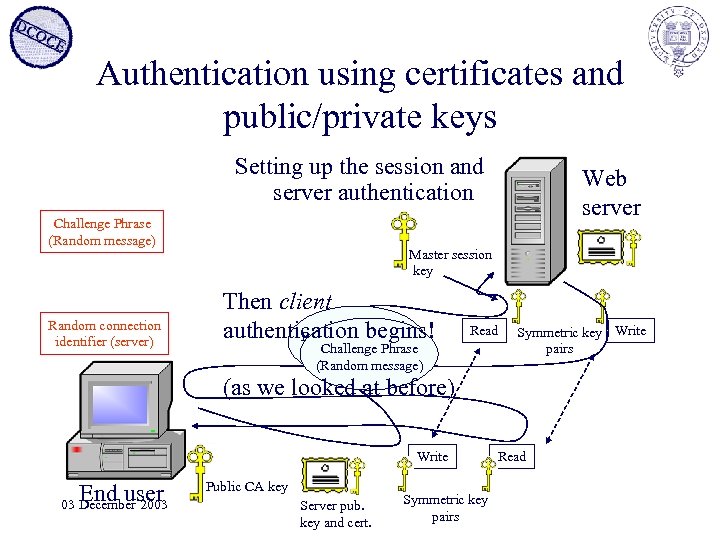
Authentication using certificates and public/private keys Setting up the session and server authentication Challenge Phrase (Random message) Random connection identifier (server) Web server Master session key Then client authentication begins! Random connection Read Challenge Phrase identifier (server) (Random message) Symmetric key Write pairs (as we looked at before) Write End user 03 December 2003 Public CA key Server pub. key and cert. Symmetric key pairs Read
Public Key Infrastructure and Authentication Mark Norman DCOCE Oxford University Computing Services 03 December 2003
f95cfedc5a75335c18959bebe9018b27.ppt