462ce853db69810db7104009537784a6.ppt
- Количество слайдов: 25
 Protecting Your Company, Employees and Customers from Identity Theft Presented by: Bill Morrow CSIdentity Chairman and CEO
Protecting Your Company, Employees and Customers from Identity Theft Presented by: Bill Morrow CSIdentity Chairman and CEO
 Agenda • Risks Businesses Face Today • Identity Theft Overview • Identity Theft Protection and Data Security • Questions & Answers 1 • Proprietary and Confidential
Agenda • Risks Businesses Face Today • Identity Theft Overview • Identity Theft Protection and Data Security • Questions & Answers 1 • Proprietary and Confidential
 Risk and The Opportunity Cost • Risk: to expose oneself to the chance of injury or loss, to venture upon, take or run the chance of an outcome; put oneself in danger or hazard. • With RISK taking there is an opportunity or payback for a sacrifice OR consequences to pay for not taking a risk. In today’s business environment and with identity theft, there is an opportunity cost -- the cost of doing nothing. • There is no payback for accepting or allowing the RISK to occur. • Consequences for inaction are greater than ever before – not just from a lost revenue perspective but also from a legislative point of view with state and federal regulations setting compliance standards. 2 • Proprietary and Confidential
Risk and The Opportunity Cost • Risk: to expose oneself to the chance of injury or loss, to venture upon, take or run the chance of an outcome; put oneself in danger or hazard. • With RISK taking there is an opportunity or payback for a sacrifice OR consequences to pay for not taking a risk. In today’s business environment and with identity theft, there is an opportunity cost -- the cost of doing nothing. • There is no payback for accepting or allowing the RISK to occur. • Consequences for inaction are greater than ever before – not just from a lost revenue perspective but also from a legislative point of view with state and federal regulations setting compliance standards. 2 • Proprietary and Confidential
 Managing Risk • Identity theft is ever-evolving and criminals are becoming more sophisticated, scheming ways to infiltrate businesses, find the gaps in security, manipulate the system and discover ways to further deceive consumers. • Businesses need to be ahead of the curve, and stay ahead of criminals, to protect their assets including revenue, customer base and employees. • Legislation is established as a result of incidents - reacting to discovered threats. However, today there are unrealized threats and areas where your company is unknowingly unprotected. • It’s important to be proactive versus reactive when it comes to fraud and identity theft. • Manage risk & close the gaps. 3 • Proprietary and Confidential
Managing Risk • Identity theft is ever-evolving and criminals are becoming more sophisticated, scheming ways to infiltrate businesses, find the gaps in security, manipulate the system and discover ways to further deceive consumers. • Businesses need to be ahead of the curve, and stay ahead of criminals, to protect their assets including revenue, customer base and employees. • Legislation is established as a result of incidents - reacting to discovered threats. However, today there are unrealized threats and areas where your company is unknowingly unprotected. • It’s important to be proactive versus reactive when it comes to fraud and identity theft. • Manage risk & close the gaps. 3 • Proprietary and Confidential
 Identity Theft and Related Fraud Risks • Hiring employees who use false identity data to mask a criminal history and gain access to your networks and data from the inside • Retaining employees who have committed criminal offenses after being hired and screened • Employee errors, loose policies or internal fraud causing data breaches of company, customer and employee data • Thieves or hackers externally accessing your network and data • Criminals buying and selling your company and customer data to other criminals who use it to commit more crimes • Maintaining incomplete current safeguards that may allow for gaps in security 4 • Proprietary and Confidential
Identity Theft and Related Fraud Risks • Hiring employees who use false identity data to mask a criminal history and gain access to your networks and data from the inside • Retaining employees who have committed criminal offenses after being hired and screened • Employee errors, loose policies or internal fraud causing data breaches of company, customer and employee data • Thieves or hackers externally accessing your network and data • Criminals buying and selling your company and customer data to other criminals who use it to commit more crimes • Maintaining incomplete current safeguards that may allow for gaps in security 4 • Proprietary and Confidential
 Spear-phishing & Whaling Do you know who your colleagues report suspicious e-mails to? Would you or your senior management team recognize a whaling e-mail or use a USB from an unknown source? 5 • Proprietary and Confidential
Spear-phishing & Whaling Do you know who your colleagues report suspicious e-mails to? Would you or your senior management team recognize a whaling e-mail or use a USB from an unknown source? 5 • Proprietary and Confidential
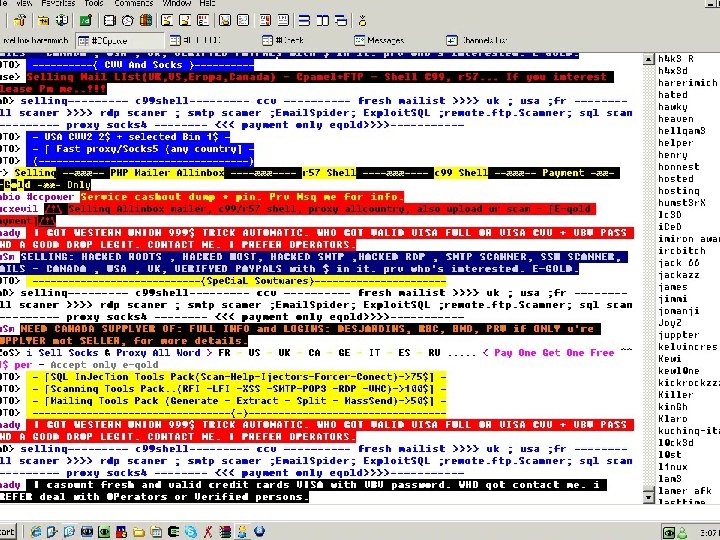 Criminal Chat Room Activity 6 • Proprietary and Confidential
Criminal Chat Room Activity 6 • Proprietary and Confidential
 Identity Theft Overview
Identity Theft Overview
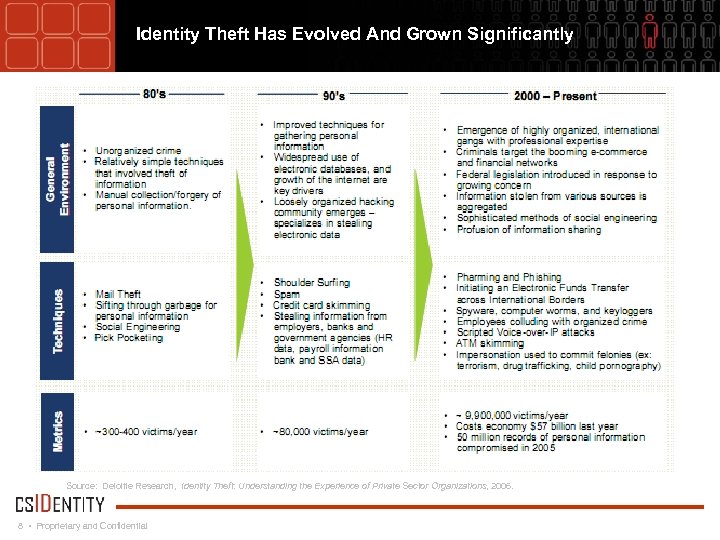 Identity Theft Has Evolved And Grown Significantly Source: Deloitte Research, Identity Theft: Understanding the Experience of Private Sector Organizations, 2006. 8 • Proprietary and Confidential
Identity Theft Has Evolved And Grown Significantly Source: Deloitte Research, Identity Theft: Understanding the Experience of Private Sector Organizations, 2006. 8 • Proprietary and Confidential
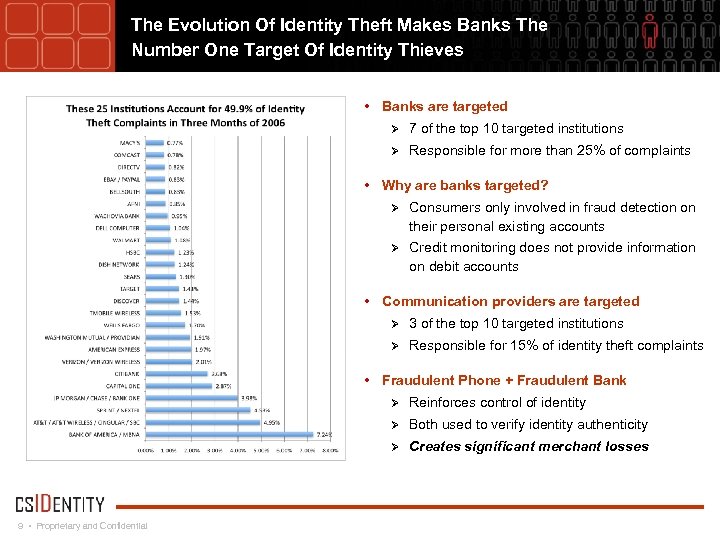 The Evolution Of Identity Theft Makes Banks The Number One Target Of Identity Thieves • Banks are targeted Ø 7 of the top 10 targeted institutions Ø Responsible for more than 25% of complaints • Why are banks targeted? Ø Consumers only involved in fraud detection on their personal existing accounts Ø Credit monitoring does not provide information on debit accounts • Communication providers are targeted Ø 3 of the top 10 targeted institutions Ø Responsible for 15% of identity theft complaints • Fraudulent Phone + Fraudulent Bank Ø Ø Both used to verify identity authenticity Ø 9 • Proprietary and Confidential Reinforces control of identity Creates significant merchant losses
The Evolution Of Identity Theft Makes Banks The Number One Target Of Identity Thieves • Banks are targeted Ø 7 of the top 10 targeted institutions Ø Responsible for more than 25% of complaints • Why are banks targeted? Ø Consumers only involved in fraud detection on their personal existing accounts Ø Credit monitoring does not provide information on debit accounts • Communication providers are targeted Ø 3 of the top 10 targeted institutions Ø Responsible for 15% of identity theft complaints • Fraudulent Phone + Fraudulent Bank Ø Ø Both used to verify identity authenticity Ø 9 • Proprietary and Confidential Reinforces control of identity Creates significant merchant losses
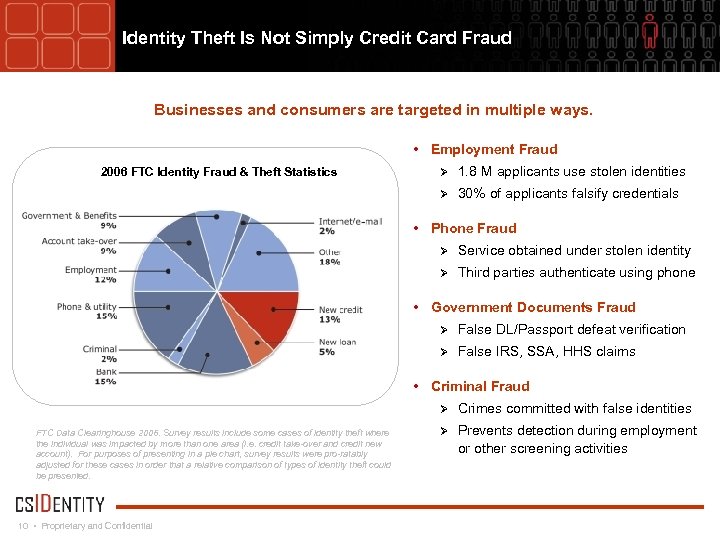 Identity Theft Is Not Simply Credit Card Fraud Businesses and consumers are targeted in multiple ways. • Employment Fraud Ø 1. 8 M applicants use stolen identities Ø 2006 FTC Identity Fraud & Theft Statistics 30% of applicants falsify credentials • Phone Fraud Ø Service obtained under stolen identity Ø Third parties authenticate using phone • Government Documents Fraud Ø False DL/Passport defeat verification Ø False IRS, SSA, HHS claims • Criminal Fraud Ø FTC Data Clearinghouse 2006. Survey results include some cases of identity theft where the individual was impacted by more than one area (i. e. credit take-over and credit new account). For purposes of presenting in a pie chart, survey results were pro-ratably adjusted for these cases in order that a relative comparison of types of identity theft could be presented. 10 • Proprietary and Confidential Crimes committed with false identities Ø Prevents detection during employment or other screening activities
Identity Theft Is Not Simply Credit Card Fraud Businesses and consumers are targeted in multiple ways. • Employment Fraud Ø 1. 8 M applicants use stolen identities Ø 2006 FTC Identity Fraud & Theft Statistics 30% of applicants falsify credentials • Phone Fraud Ø Service obtained under stolen identity Ø Third parties authenticate using phone • Government Documents Fraud Ø False DL/Passport defeat verification Ø False IRS, SSA, HHS claims • Criminal Fraud Ø FTC Data Clearinghouse 2006. Survey results include some cases of identity theft where the individual was impacted by more than one area (i. e. credit take-over and credit new account). For purposes of presenting in a pie chart, survey results were pro-ratably adjusted for these cases in order that a relative comparison of types of identity theft could be presented. 10 • Proprietary and Confidential Crimes committed with false identities Ø Prevents detection during employment or other screening activities
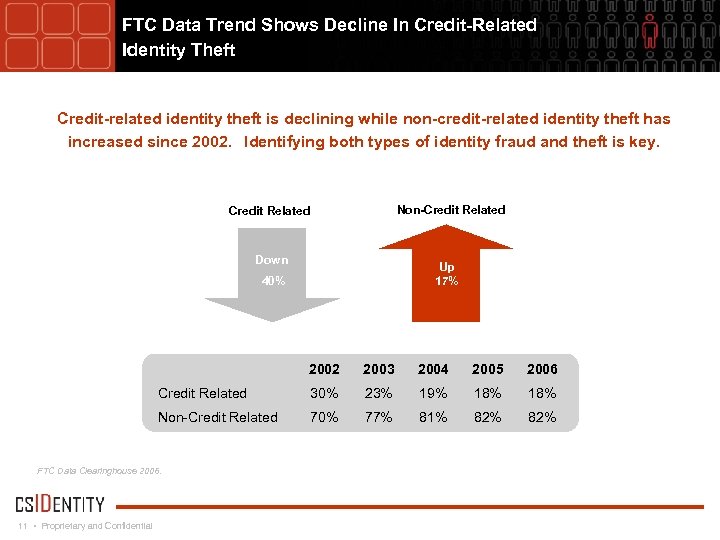 FTC Data Trend Shows Decline In Credit-Related Identity Theft Credit-related identity theft is declining while non-credit-related identity theft has increased since 2002. Identifying both types of identity fraud and theft is key. Non-Credit Related Down Up 17% 40% 2002 2003 2004 2005 2006 Credit Related 30% 23% 19% 18% Non-Credit Related 70% 77% 81% 82% FTC Data Clearinghouse 2006. 11 • Proprietary and Confidential
FTC Data Trend Shows Decline In Credit-Related Identity Theft Credit-related identity theft is declining while non-credit-related identity theft has increased since 2002. Identifying both types of identity fraud and theft is key. Non-Credit Related Down Up 17% 40% 2002 2003 2004 2005 2006 Credit Related 30% 23% 19% 18% Non-Credit Related 70% 77% 81% 82% FTC Data Clearinghouse 2006. 11 • Proprietary and Confidential
 Identity Theft Crimes Impact Individuals In Countless Ways • Unable to secure a job • Damage to professional reputation • Wrongly arrested • Unable to open new bank accounts • Tax liabilities • Existing bank accounts shut down • IRS audits • Existing bank accounts drained • Fraudulent tax refunds • Unable to open new credit accounts • IRS notice of undeclared income • Existing credit terminated • Unable to buy a home • Existing credit used fraudulently • Unable to buy a car • Unable to take out loans • Unable to pay for college • Fraudulent loans • Theft/loss of government benefits • Health insurance used fraudulently • Fraudulent payday loans issued • Erroneous health records due to fraud • Property deeds compromised – property sold fraudulently • Loss of security clearances 12 • Proprietary and Confidential
Identity Theft Crimes Impact Individuals In Countless Ways • Unable to secure a job • Damage to professional reputation • Wrongly arrested • Unable to open new bank accounts • Tax liabilities • Existing bank accounts shut down • IRS audits • Existing bank accounts drained • Fraudulent tax refunds • Unable to open new credit accounts • IRS notice of undeclared income • Existing credit terminated • Unable to buy a home • Existing credit used fraudulently • Unable to buy a car • Unable to take out loans • Unable to pay for college • Fraudulent loans • Theft/loss of government benefits • Health insurance used fraudulently • Fraudulent payday loans issued • Erroneous health records due to fraud • Property deeds compromised – property sold fraudulently • Loss of security clearances 12 • Proprietary and Confidential
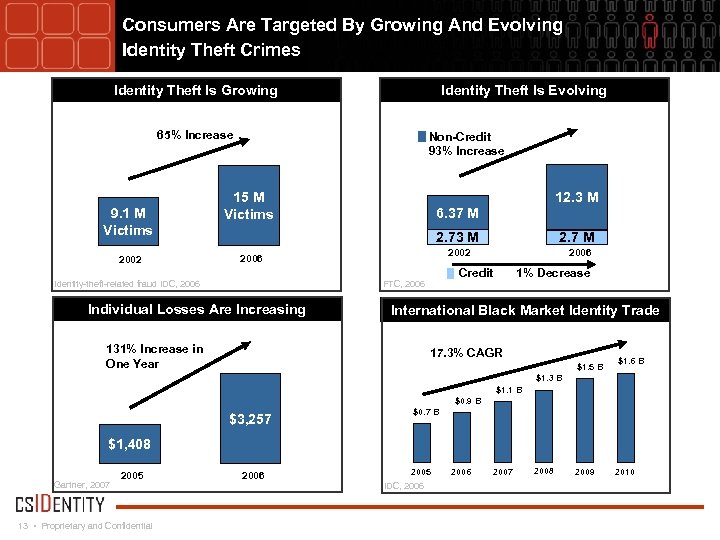 Consumers Are Targeted By Growing And Evolving Identity Theft Crimes Identity Theft Is Growing Identity Theft Is Evolving 65% Increase 9. 1 M Victims 2002 Non-Credit 93% Increase Victims 15 M Victims 12. 3 M 6. 37 M 2. 73 M 2006 Identity-theft-related fraud IDC, 2006 Credit FTC, 2006 Individual Losses Are Increasing 2. 7 M 2002 1% Decrease International Black Market Identity Trade 131% Increase in One Year 17. 3% CAGR $1. 5 B $1. 6 B $1. 3 B $1. 1 B $0. 9 B $3, 257 $0. 7 B $1, 408 Gartner, 2007 2005 13 • Proprietary and Confidential 2006 2005 IDC, 2006 2007 2008 2009 2010
Consumers Are Targeted By Growing And Evolving Identity Theft Crimes Identity Theft Is Growing Identity Theft Is Evolving 65% Increase 9. 1 M Victims 2002 Non-Credit 93% Increase Victims 15 M Victims 12. 3 M 6. 37 M 2. 73 M 2006 Identity-theft-related fraud IDC, 2006 Credit FTC, 2006 Individual Losses Are Increasing 2. 7 M 2002 1% Decrease International Black Market Identity Trade 131% Increase in One Year 17. 3% CAGR $1. 5 B $1. 6 B $1. 3 B $1. 1 B $0. 9 B $3, 257 $0. 7 B $1, 408 Gartner, 2007 2005 13 • Proprietary and Confidential 2006 2005 IDC, 2006 2007 2008 2009 2010
 Businesses Are Targeted Both To Commit Fraud And To Steal Identities Cost per Record Exposed in Data Breach $149 2006 $197 2007 Source: Ponemon Institute Aggregate Business Identity Losses (not due to breaches) ($ in billions) $57 $53$53 2003 $57 2006 Source: Javelin Strategy and Research Survey 2006. 14 • Proprietary and Confidential
Businesses Are Targeted Both To Commit Fraud And To Steal Identities Cost per Record Exposed in Data Breach $149 2006 $197 2007 Source: Ponemon Institute Aggregate Business Identity Losses (not due to breaches) ($ in billions) $57 $53$53 2003 $57 2006 Source: Javelin Strategy and Research Survey 2006. 14 • Proprietary and Confidential
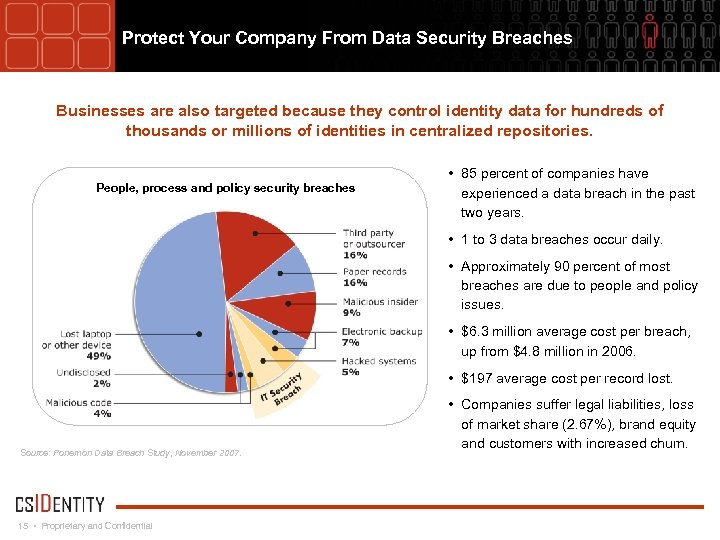 Protect Your Company From Data Security Breaches Businesses are also targeted because they control identity data for hundreds of thousands or millions of identities in centralized repositories. People, process and policy security breaches • 85 percent of companies have experienced a data breach in the past two years. • 1 to 3 data breaches occur daily. • Approximately 90 percent of most breaches are due to people and policy issues. • $6. 3 million average cost per breach, up from $4. 8 million in 2006. • $197 average cost per record lost. Source: Ponemon Data Breach Study, November 2007. 15 • Proprietary and Confidential • Companies suffer legal liabilities, loss of market share (2. 67%), brand equity and customers with increased churn.
Protect Your Company From Data Security Breaches Businesses are also targeted because they control identity data for hundreds of thousands or millions of identities in centralized repositories. People, process and policy security breaches • 85 percent of companies have experienced a data breach in the past two years. • 1 to 3 data breaches occur daily. • Approximately 90 percent of most breaches are due to people and policy issues. • $6. 3 million average cost per breach, up from $4. 8 million in 2006. • $197 average cost per record lost. Source: Ponemon Data Breach Study, November 2007. 15 • Proprietary and Confidential • Companies suffer legal liabilities, loss of market share (2. 67%), brand equity and customers with increased churn.
 Identity Theft Protection and Data Security
Identity Theft Protection and Data Security
 Regulatory Landscape • Agencies, financial institutions and businesses face a myriad of federal and state regulatory requirements, for example: Ø Patriot Act Ø Sarbanes-Oxley Ø Fair Credit Reporting Act Ø Fair and Accurate Transactions Act Ø Gramm-Leach-Bliley Act Ø State data privacy and security laws 17 • Proprietary and Confidential
Regulatory Landscape • Agencies, financial institutions and businesses face a myriad of federal and state regulatory requirements, for example: Ø Patriot Act Ø Sarbanes-Oxley Ø Fair Credit Reporting Act Ø Fair and Accurate Transactions Act Ø Gramm-Leach-Bliley Act Ø State data privacy and security laws 17 • Proprietary and Confidential
 Identity Theft Defense Framework • Understand environment, criminals, and motives Ø Ø Ø Why would the data you control be desired? How would a criminal conduct transactions with your organization using a stolen identity? Are you vulnerable to internal risks from employees, contractors, and vendors? • Understand risk areas Ø Ø What types of transactions are high risk and where would they occur? Are their gaps between systems or organization silos that can be exploited? • Install controls to identify and prevent theft and fraud Ø Ø Who do you hire? Who has access? Who conducts transactions – who authorizes, who overrides, and who is responsible? Who monitors and audits? • Plan for post-fraud response Ø Ø Ø What constitutes a breach and what defines the severity of breach? Who is notified and how is information conveyed to exposed victims? What victim protection solutions will be extended based on data exposed and severity of breach? 18 • Proprietary and Confidential
Identity Theft Defense Framework • Understand environment, criminals, and motives Ø Ø Ø Why would the data you control be desired? How would a criminal conduct transactions with your organization using a stolen identity? Are you vulnerable to internal risks from employees, contractors, and vendors? • Understand risk areas Ø Ø What types of transactions are high risk and where would they occur? Are their gaps between systems or organization silos that can be exploited? • Install controls to identify and prevent theft and fraud Ø Ø Who do you hire? Who has access? Who conducts transactions – who authorizes, who overrides, and who is responsible? Who monitors and audits? • Plan for post-fraud response Ø Ø Ø What constitutes a breach and what defines the severity of breach? Who is notified and how is information conveyed to exposed victims? What victim protection solutions will be extended based on data exposed and severity of breach? 18 • Proprietary and Confidential
 Identity Data Security Requirements • Thirty-nine states (including Texas) have data security and privacy legislation. Ø Federal legislation mimicking California data security and privacy legislation is pending • Define data requiring compliance – Personal Confidential Information (PCI). Ø Name associated with Social Security number, driver’s license, account data (debit or credit), usernames and passwords, and other sensitive data • Protect PCI data from exposure. Ø Storage – database, desktop, laptop, paper Ø Transfer – e-mail, other network, backup tape (other medium), physical Ø Destruction – data storage timelines, physical storage and destruction policies • Define a policy for responding to data security breaches. Ø Proactively develop data breach response plan as part of overall disaster recovery efforts Ø Promptly implement breach plan upon breach identification Ø Notify consumer victims and extend victim protection services in response to a breach 19 • Proprietary and Confidential
Identity Data Security Requirements • Thirty-nine states (including Texas) have data security and privacy legislation. Ø Federal legislation mimicking California data security and privacy legislation is pending • Define data requiring compliance – Personal Confidential Information (PCI). Ø Name associated with Social Security number, driver’s license, account data (debit or credit), usernames and passwords, and other sensitive data • Protect PCI data from exposure. Ø Storage – database, desktop, laptop, paper Ø Transfer – e-mail, other network, backup tape (other medium), physical Ø Destruction – data storage timelines, physical storage and destruction policies • Define a policy for responding to data security breaches. Ø Proactively develop data breach response plan as part of overall disaster recovery efforts Ø Promptly implement breach plan upon breach identification Ø Notify consumer victims and extend victim protection services in response to a breach 19 • Proprietary and Confidential
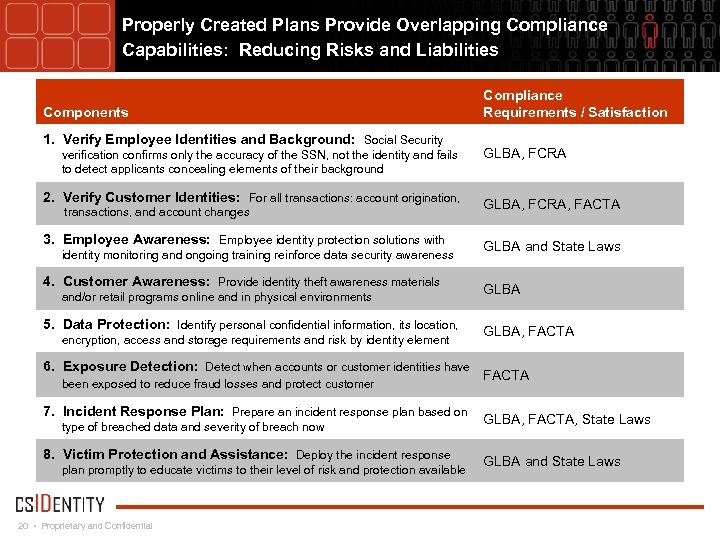 Properly Created Plans Provide Overlapping Compliance Capabilities: Reducing Risks and Liabilities Components 1. Verify Employee Identities and Background: Social Security verification confirms only the accuracy of the SSN, not the identity and fails to detect applicants concealing elements of their background 2. Verify Customer Identities: For all transactions: account origination, transactions, and account changes 3. Employee Awareness: Employee identity protection solutions with identity monitoring and ongoing training reinforce data security awareness 4. Customer Awareness: Provide identity theft awareness materials and/or retail programs online and in physical environments 5. Data Protection: Identify personal confidential information, its location, encryption, access and storage requirements and risk by identity element 6. Exposure Detection: Detect when accounts or customer identities have been exposed to reduce fraud losses and protect customer 7. Incident Response Plan: Prepare an incident response plan based on type of breached data and severity of breach now 8. Victim Protection and Assistance: Deploy the incident response plan promptly to educate victims to their level of risk and protection available 20 • Proprietary and Confidential Compliance Requirements / Satisfaction GLBA, FCRA, FACTA GLBA and State Laws GLBA, FACTA, State Laws GLBA and State Laws
Properly Created Plans Provide Overlapping Compliance Capabilities: Reducing Risks and Liabilities Components 1. Verify Employee Identities and Background: Social Security verification confirms only the accuracy of the SSN, not the identity and fails to detect applicants concealing elements of their background 2. Verify Customer Identities: For all transactions: account origination, transactions, and account changes 3. Employee Awareness: Employee identity protection solutions with identity monitoring and ongoing training reinforce data security awareness 4. Customer Awareness: Provide identity theft awareness materials and/or retail programs online and in physical environments 5. Data Protection: Identify personal confidential information, its location, encryption, access and storage requirements and risk by identity element 6. Exposure Detection: Detect when accounts or customer identities have been exposed to reduce fraud losses and protect customer 7. Incident Response Plan: Prepare an incident response plan based on type of breached data and severity of breach now 8. Victim Protection and Assistance: Deploy the incident response plan promptly to educate victims to their level of risk and protection available 20 • Proprietary and Confidential Compliance Requirements / Satisfaction GLBA, FCRA, FACTA GLBA and State Laws GLBA, FACTA, State Laws GLBA and State Laws
 About CSIdentity 21 • Proprietary and Confidential
About CSIdentity 21 • Proprietary and Confidential
 CSIdentity Targets Identity Fraud Across Industries And Markets Consumer: Comprehensive identity theft protection and personal security solutions. Government: Detection of altered, fabricated and stolen identities used by individuals crossing borders and utilizing the United States’ transportation systems. 22 • Proprietary and Confidential Business: Identity theft and fraud detection, HR Benefits, breach management solutions, data solutions and security tools.
CSIdentity Targets Identity Fraud Across Industries And Markets Consumer: Comprehensive identity theft protection and personal security solutions. Government: Detection of altered, fabricated and stolen identities used by individuals crossing borders and utilizing the United States’ transportation systems. 22 • Proprietary and Confidential Business: Identity theft and fraud detection, HR Benefits, breach management solutions, data solutions and security tools.
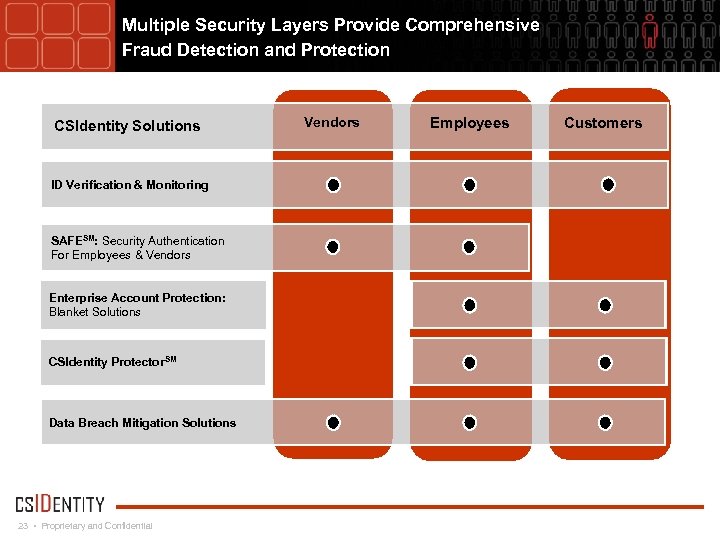 Multiple Security Layers Provide Comprehensive Fraud Detection and Protection CSIdentity Solutions ID Verification & Monitoring SAFESM: Security Authentication For Employees & Vendors Enterprise Account Protection: Blanket Solutions CSIdentity Protector. SM Data Breach Mitigation Solutions 23 • Proprietary and Confidential Vendors Employees Customers
Multiple Security Layers Provide Comprehensive Fraud Detection and Protection CSIdentity Solutions ID Verification & Monitoring SAFESM: Security Authentication For Employees & Vendors Enterprise Account Protection: Blanket Solutions CSIdentity Protector. SM Data Breach Mitigation Solutions 23 • Proprietary and Confidential Vendors Employees Customers
 Questions & Answers 24 • Proprietary and Confidential
Questions & Answers 24 • Proprietary and Confidential


