58a870f86701775645fcaefa7a0ed5e3.ppt
- Количество слайдов: 36
Protecting Web services and Web applications against security threats OWASP App. Sec Europe May 2006 Rix Groenboom Support Manager Parasoft UK Ltd rix. groenboom@parasoft. com Copyright © 2006 - The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License. The OWASP Foundation http: //www. owasp. org/
What We Will Explore < What threats we see today < Practices for securing Web Services and SOA < Use of a Policy based Approach: 4 “Inside Out & Outside In” OWASP App. Sec Europe 2006 2
Structure of this presentation <Problems, Threats, and Solutions <“Testing Security Into The Application” <A Four-Step Approach To Securing SOAP <Examples of Threats Prevented OWASP App. Sec Europe 2006 3
Problems: Size and Complexity <3 MLOC of SW <50 lines = 25 cm <100 = 50 cm <200 =1 m <1, 000 =5 m <10 kloc = 50 m <100 kloc = 500 m <1 Mloc = 5 km <3 Mloc = 15 km <8 Mloc = MARATHON OWASP App. Sec Europe 2006 4
Problems: Examples OWASP App. Sec Europe 2006 5
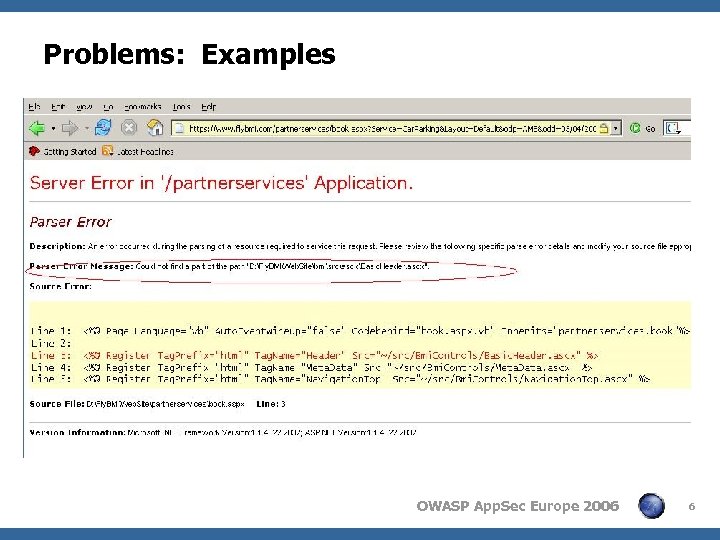
Problems: Examples OWASP App. Sec Europe 2006 6
Problems: XML Bomb bomb. xml OWASP App. Sec Europe 2006 7
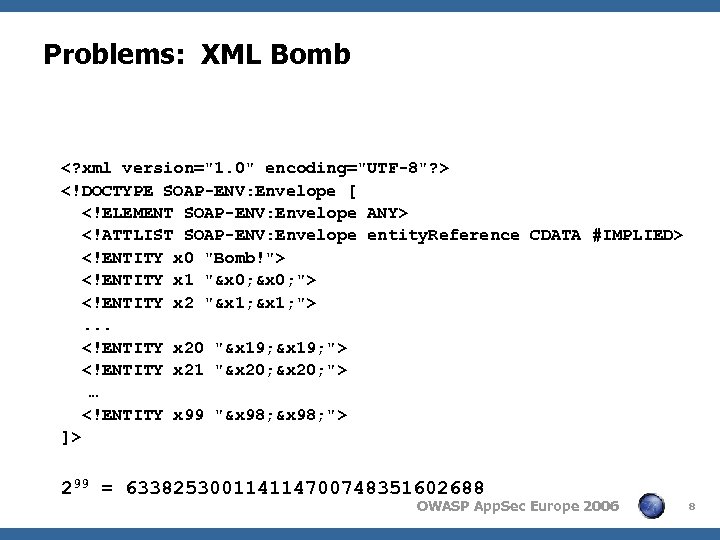
Problems: XML Bomb <? xml version="1. 0" encoding="UTF-8"? > <!DOCTYPE SOAP-ENV: Envelope [ <!ELEMENT SOAP-ENV: Envelope ANY> <!ATTLIST SOAP-ENV: Envelope entity. Reference CDATA #IMPLIED> <!ENTITY x 0 "Bomb!"> <!ENTITY x 1 "&x 0; "> <!ENTITY x 2 "&x 1; ">. . . <!ENTITY x 20 "&x 19; "> <!ENTITY x 21 "&x 20; "> … <!ENTITY x 99 "&x 98; "> ]> 299 = 633825300114114700748351602688 OWASP App. Sec Europe 2006 8
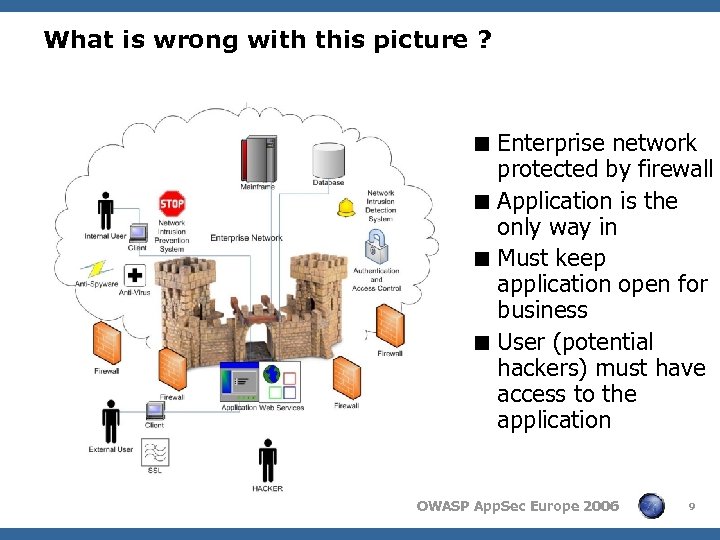
What is wrong with this picture ? < Enterprise network protected by firewall < Application is the only way in < Must keep application open for business < User (potential hackers) must have access to the application OWASP App. Sec Europe 2006 9
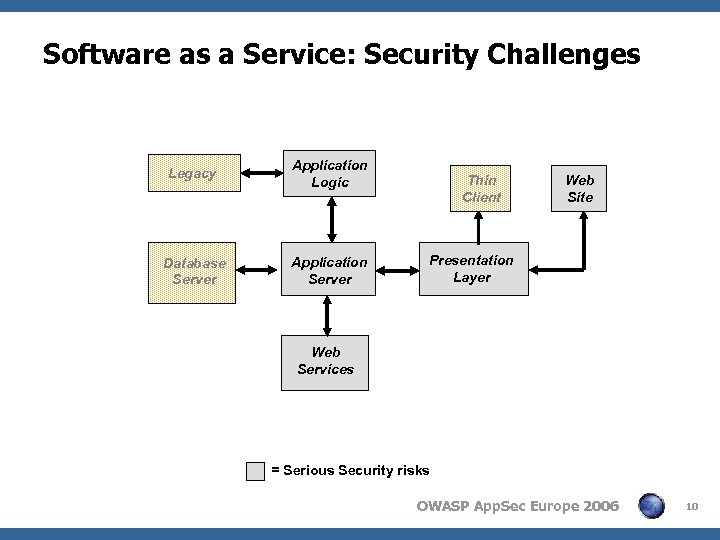
Software as a Service: Security Challenges Legacy Application Logic Database Server Application Server Thin Client Web Site Presentation Layer Web Services = Serious Security risks OWASP App. Sec Europe 2006 10
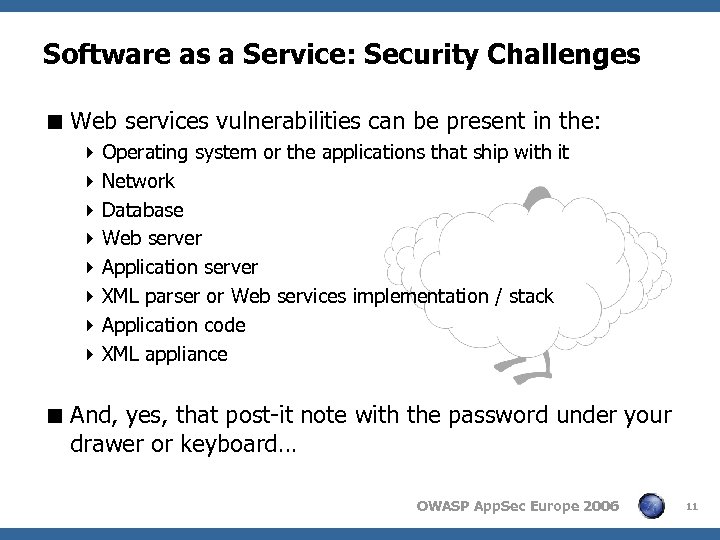
Software as a Service: Security Challenges < Web services vulnerabilities can be present in the: 4 Operating system or the applications that ship with it 4 Network 4 Database 4 Web server 4 Application server 4 XML parser or Web services implementation / stack 4 Application code 4 XML appliance < And, yes, that post-it note with the password under your drawer or keyboard… OWASP App. Sec Europe 2006 11
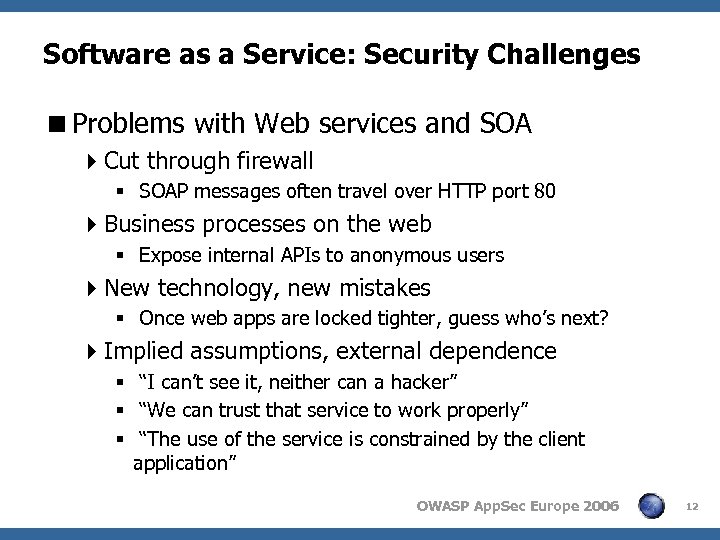
Software as a Service: Security Challenges <Problems with Web services and SOA 4 Cut through firewall § SOAP messages often travel over HTTP port 80 4 Business processes on the web § Expose internal APIs to anonymous users 4 New technology, new mistakes § Once web apps are locked tighter, guess who’s next? 4 Implied assumptions, external dependence § “I can’t see it, neither can a hacker” § “We can trust that service to work properly” § “The use of the service is constrained by the client application” OWASP App. Sec Europe 2006 12
Software as a Service: Security Challenges < The Year 2000 problem revisited ! 4 Gary Mc. Graw (at CMU/SEI meeting) < Y 2 K problem: 4 Applications never designed to work > 30, 40 years 4 Source code contains root cause of the problems 4 One defect (bug) is enough to cause serious problems < And now with security: 4 Applications never designed to be connected to networks / internet 4 Source code contains root cause of the problems 4 One vulnerability is enough to cause serious risk 4 And worse, people hunt for them ! OWASP App. Sec Europe 2006 13
Securing Web Services – Solutions So far < General Practices 4 Define acceptable protocols § Shut down other services § Lock down firewall (change port) 4 Enforce security mechanisms § § Authentication Access Control Auditing … to Z OWASP App. Sec Europe 2006 14
Securing Web Services – Solutions So far < SOA Security Mechanisms 4 WS-Security § § § XML Encryption XML Signature X 509 Username Tokens SAML 4 WS-Trust 4 WS-Secure. Conversation 4 WS-Security. Policy 4 WS-Federation 4 WS-Privacy 4 WS-* OWASP App. Sec Europe 2006 15
General Web Services Threats <Common to all Web applications 4 SQL Injections § Special characters in queries 4 Capture and Replay Attacks § Man in the middle attacks 4 Do. S (resulting from a large load) § Blow up application from inside 4 Improper Error Handling § Dump of stack trace etc 4 Broken Access Control § Take over earlier sessions tokens etc OWASP App. Sec Europe 2006 16
General Web Services Threats <Specific to XML Web services 4 Large Payloads § Send huge XML load, or generate huge responses 4 XPath Injections § Query XML documents for certain nodes 4 External Entity Attacks § Misuse pointed to XML data using URI 4 XML Bombs § Recursive XML entity declaration OWASP App. Sec Europe 2006 17
General Web Services Threats <However, threats also come from within: 4 Since 1999, the percentage of companies reporting a computer-security incident from inside is almost the same as those reporting it from the outside 428. 9% of of security incidents come from employees <Source: 4 The Wall Street Journal Online (Feb 13, 2006) 4 http: //online. wsj. com/article/SB 113926053552466409. html OWASP App. Sec Europe 2006 18
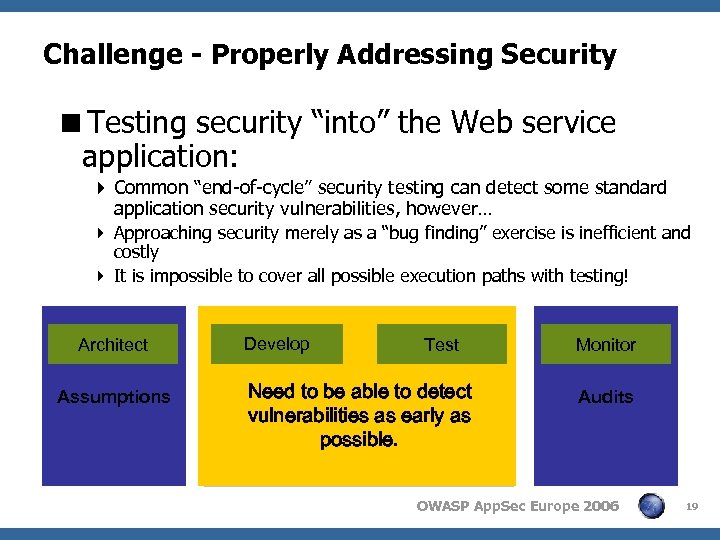
Challenge - Properly Addressing Security <Testing security “into” the Web service application: 4 Common “end-of-cycle” security testing can detect some standard application security vulnerabilities, however… 4 Approaching security merely as a “bug finding” exercise is inefficient and costly 4 It is impossible to cover all possible execution paths with testing! Architect Assumptions Develop Test Need to be able to detect GAP vulnerabilities as early as possible. Monitor Audits OWASP App. Sec Europe 2006 19
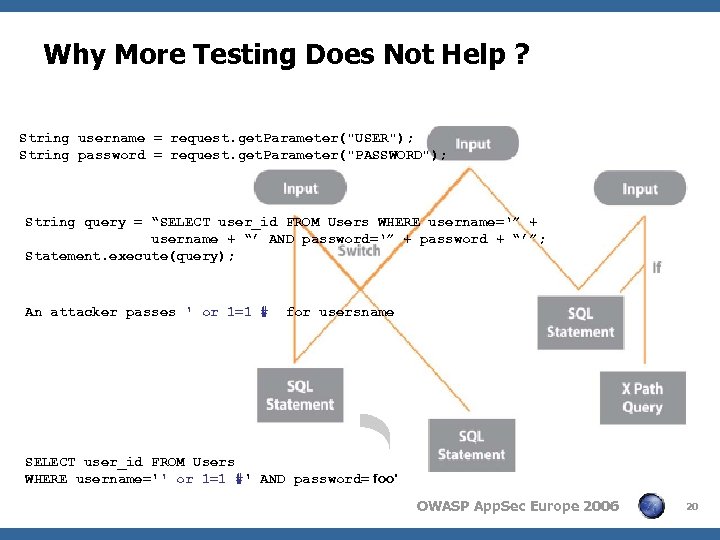
Why More Testing Does Not Help ? String username = request. get. Parameter("USER"); String password = request. get. Parameter("PASSWORD"); String query = “SELECT user_id FROM Users WHERE username=‘” + username + “’ AND password=‘” + password + “’”; Statement. execute(query); An attacker passes ' or 1=1 # for usersname SELECT user_id FROM Users WHERE username='' or 1=1 #' AND password=‘foo’ OWASP App. Sec Europe 2006 20
Securing Web Services <A different approach is needed 4 A preventive, policy-based approach rather than a reactive one 4 Security, like quality, must be built into the application and cannot be tested in 4 Application are large and complex <We propose a combined approach: 4 Outside In 4 Inside Out OWASP App. Sec Europe 2006 21
Securing Web Services: Step 1 <Assessment: Impact & Risk 4 Analyze the business process § Assets, users, entry points § What needs to be protected? How? § Outsource for expertise before implementation 4 Define security threats § CIA: Confidentiality, Availability, Integrity § Risk = Threat x Vulnerability x Expected Loss – Threat = Motivated Attacker with Path to Valuable Asset – Vulnerability = Weakness in system – Expected Loss = Impact of threat realization § Misusage, the general WS threats, etc. OWASP App. Sec Europe 2006 22
Securing Web Services: Step 1 <Assessment: Penetration Testing 4 Find a few general vulnerabilities 4 Many penetration activities can be automated § Generate injection attacks, XSS, scan for broken access control, etc. § Simulate large loads, generate big messages, etc. 4 Penetration testing is not exhaustive 4 But, a vulnerability you find § Is like a real bug: if you see one, there are 1000 you do not see ! § “where smoke is, is fire” & “tip of the iceberg” § Helps you in Step 2 OWASP App. Sec Europe 2006 23
Securing Web Services: Step 2 <Develop a Security Policy: 4 A security policy is a set of guidelines that are an overall strategy for application security <Secure implementation guidelines: 4 Use trusted libraries 4 Adhere to coding and XML standards § Release IO resources in the code § Turn off DTD support in XML parsers § Constrain schema types 4 Review implementation for errors 4 Turn off features by default OWASP App. Sec Europe 2006 24
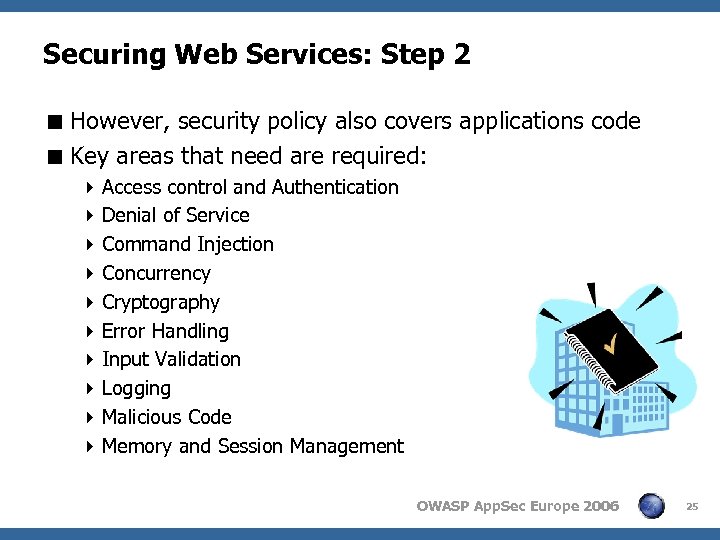
Securing Web Services: Step 2 < However, security policy also covers applications code < Key areas that need are required: 4 Access control and Authentication 4 Denial of Service 4 Command Injection 4 Concurrency 4 Cryptography 4 Error Handling 4 Input Validation 4 Logging 4 Malicious Code 4 Memory and Session Management OWASP App. Sec Europe 2006 25
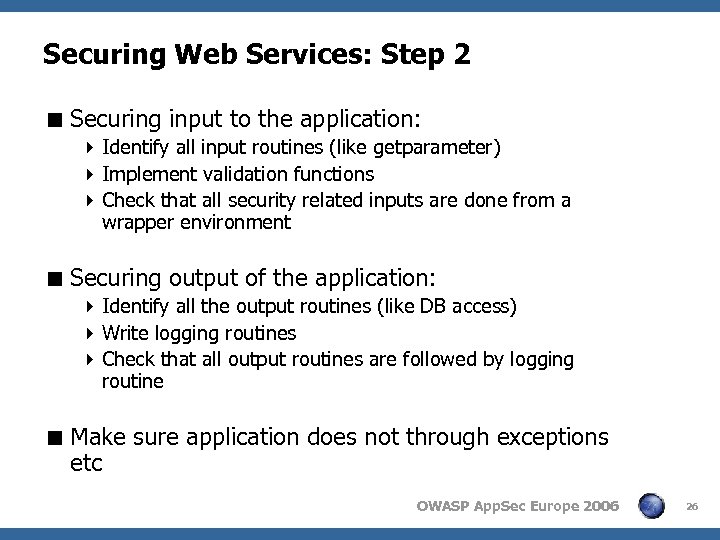
Securing Web Services: Step 2 < Securing input to the application: 4 Identify all input routines (like getparameter) 4 Implement validation functions 4 Check that all security related inputs are done from a wrapper environment < Securing output of the application: 4 Identify all the output routines (like DB access) 4 Write logging routines 4 Check that all output routines are followed by logging routine < Make sure application does not through exceptions etc OWASP App. Sec Europe 2006 26
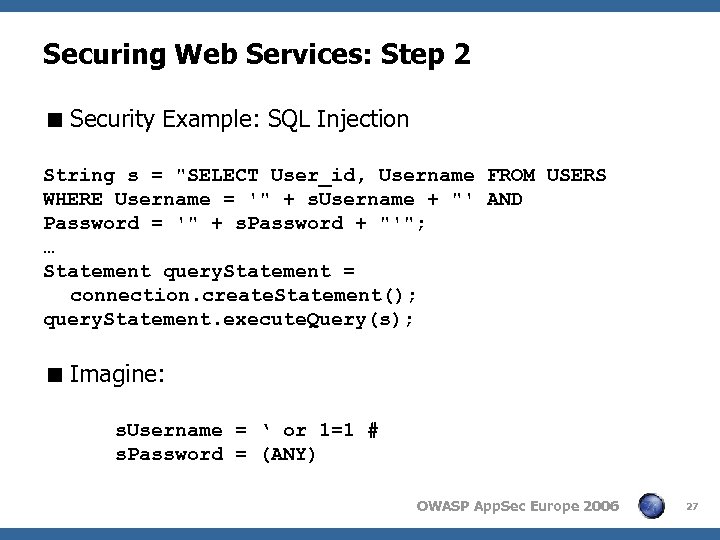
Securing Web Services: Step 2 < Security Example: SQL Injection String s = "SELECT User_id, Username FROM USERS WHERE Username = '" + s. Username + "' AND Password = '" + s. Password + "'"; … Statement query. Statement = connection. create. Statement(); query. Statement. execute. Query(s); < Imagine: s. Username = ‘ or 1=1 # s. Password = (ANY) OWASP App. Sec Europe 2006 27
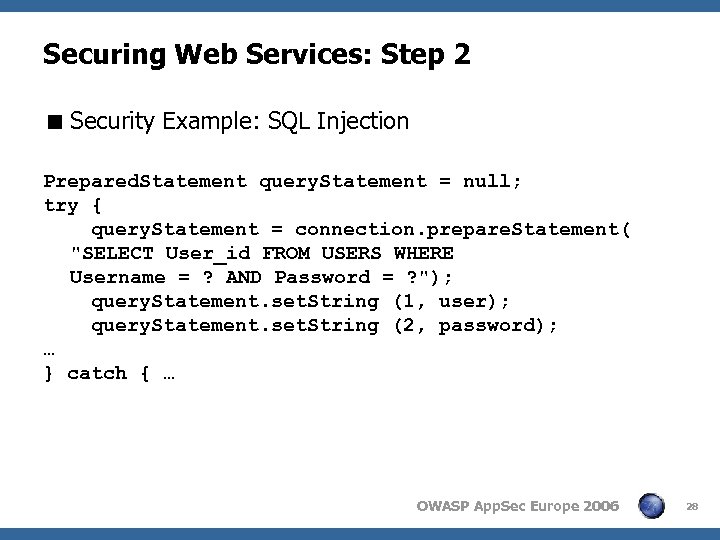
Securing Web Services: Step 2 < Security Example: SQL Injection Prepared. Statement query. Statement = null; try { query. Statement = connection. prepare. Statement( "SELECT User_id FROM USERS WHERE Username = ? AND Password = ? "); query. Statement. set. String (1, user); query. Statement. set. String (2, password); … } catch { … OWASP App. Sec Europe 2006 28
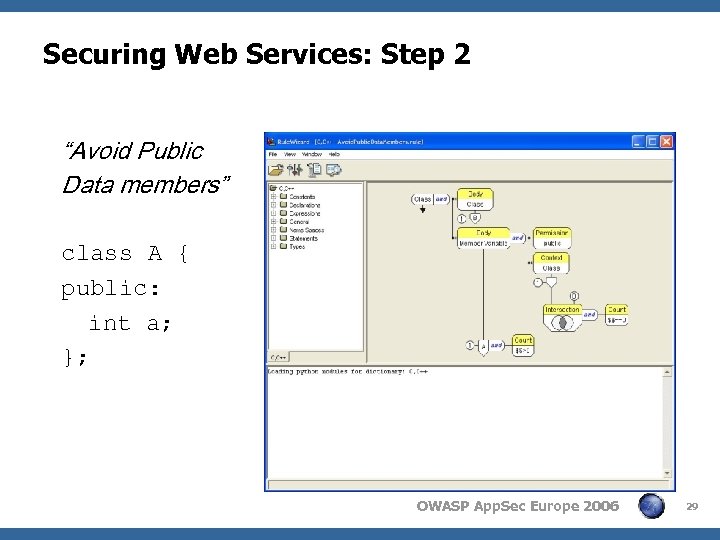
Securing Web Services: Step 2 “Avoid Public Data members” class A { public: int a; }; OWASP App. Sec Europe 2006 29
Securing Web Services: Step 3 < Enforce Security Policy Throughout SDLC 4 A policy without an automated enforcement mechanisms is like law without police < Available techniques: 4 Static / Dynamic Code analysis § Map policies to executable rules § Configure the rules based on the policies and projects at hand 4 Compliance SOA Development Governance in SDLC § Like: SOAP, WSDL, Schema, XML Metadata. 4 Runtime SOA Governance § Management, Registry, Orchestration OWASP App. Sec Europe 2006 30
Securing Web Services: Step 4 <Regression Testing 4 Software development is an iterative process 4 An iterative development process fails without regression testing. The same applies to security 4 Fixing a security vulnerability should be coupled with a policy and an enforcement mechanism to prevent it from reoccurring again 4 Regression testing practices results in a visible quality process that reinforces trust OWASP App. Sec Europe 2006 31
General Web Services Threats Prevented <SQL Injections 4 Policy: Validate user input; strip potentially malicious characters like ‘ and “ as soon as you get them 4 Test: Penetrate, regression test <Capture and Replay Attacks 4 Policy: Use signed random nonce values and Timestamps 4 Test: Penetrate, regression test <Do. S (resulting from a large load) 4 Policy: Secure coding standards 4 Test: Simulate attacks, regression test OWASP App. Sec Europe 2006 32
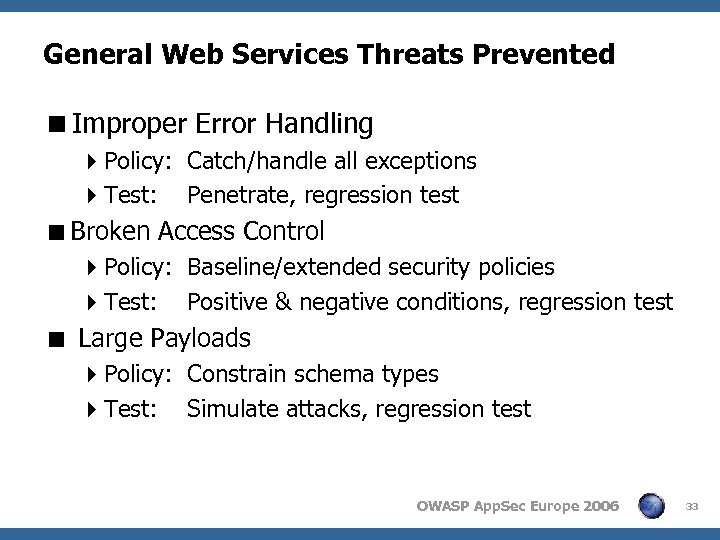
General Web Services Threats Prevented <Improper Error Handling 4 Policy: Catch/handle all exceptions 4 Test: Penetrate, regression test <Broken Access Control 4 Policy: Baseline/extended security policies 4 Test: Positive & negative conditions, regression test < Large Payloads 4 Policy: Constrain schema types 4 Test: Simulate attacks, regression test OWASP App. Sec Europe 2006 33
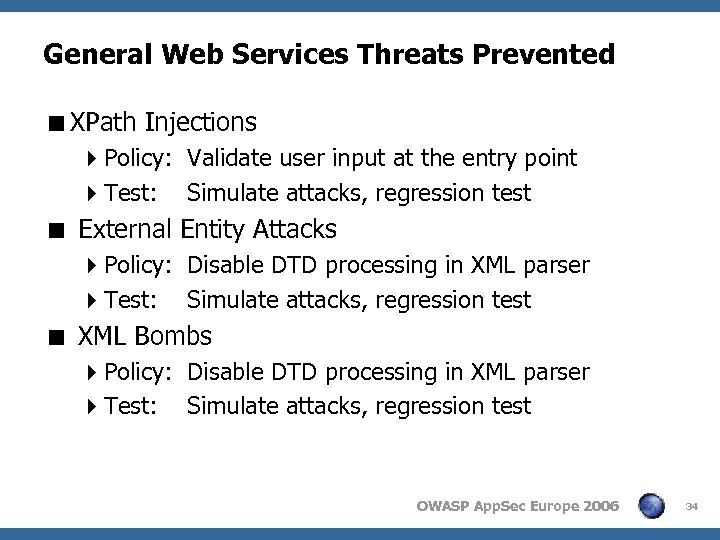
General Web Services Threats Prevented <XPath Injections 4 Policy: Validate user input at the entry point 4 Test: Simulate attacks, regression test < External Entity Attacks 4 Policy: Disable DTD processing in XML parser 4 Test: Simulate attacks, regression test < XML Bombs 4 Policy: Disable DTD processing in XML parser 4 Test: Simulate attacks, regression test OWASP App. Sec Europe 2006 34
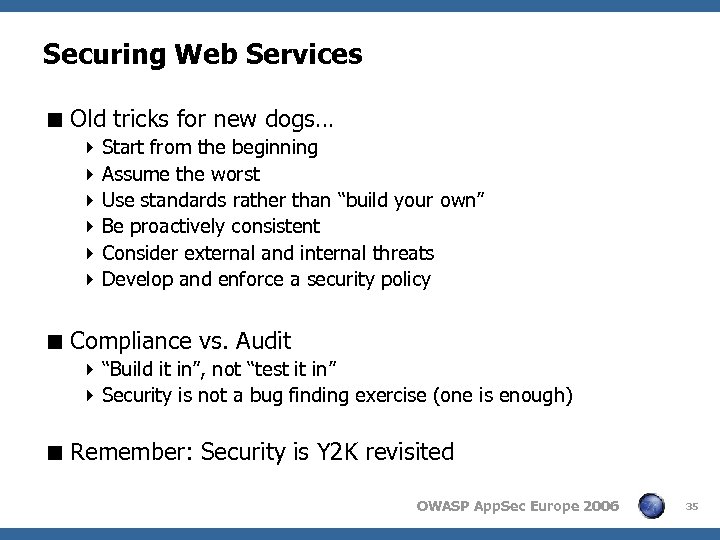
Securing Web Services < Old tricks for new dogs… 4 Start from the beginning 4 Assume the worst 4 Use standards rather than “build your own” 4 Be proactively consistent 4 Consider external and internal threats 4 Develop and enforce a security policy < Compliance vs. Audit 4 “Build it in”, not “test it in” 4 Security is not a bug finding exercise (one is enough) < Remember: Security is Y 2 K revisited OWASP App. Sec Europe 2006 35
Conclusion <Thank you <Resources 4 http: //www. cgisecurity. com/ws/ 4 http: //www. oasisopen. org/committees/tc_cat. php? cat=ws 4 http: //www. soaleaders. org/ <Commercial 4 http: //www. parasoft. com/ OWASP App. Sec Europe 2006 36
58a870f86701775645fcaefa7a0ed5e3.ppt