c0b505108d6e7c82045584984e8a49e5.ppt
- Количество слайдов: 22
 Protecting the Exchange of Medical Images in Healthcare Process Integration with Web Services Dickson K. W. CHIU Vivying S. Y. Cheng Senior Member, IEEE Dept. of Computer Science Hong Kong University of Science & Technology Dickson Computer Systems Hong Kong kwchiu@acm. org, dicksonchiu@ieee. org vivying@cs. ust. hk Patrick C. K. HUNG Eleanna Kafeza Faculty of Business and Information Technology, University of Ontario Institute of Technology Department of Marketing and Communications, Athens University of Economics and Business Patrick. Hung@uoit. ca MIEP kafeza@aueb. gr 1
Protecting the Exchange of Medical Images in Healthcare Process Integration with Web Services Dickson K. W. CHIU Vivying S. Y. Cheng Senior Member, IEEE Dept. of Computer Science Hong Kong University of Science & Technology Dickson Computer Systems Hong Kong kwchiu@acm. org, dicksonchiu@ieee. org vivying@cs. ust. hk Patrick C. K. HUNG Eleanna Kafeza Faculty of Business and Information Technology, University of Ontario Institute of Technology Department of Marketing and Communications, Athens University of Economics and Business Patrick. Hung@uoit. ca MIEP kafeza@aueb. gr 1
 Introduction n Medical images exist in electronic format n n Problem: uncontrolled exchange of medical images n n for easy storage and maintenance promote high quality healthcare services for patients a picture is worth a thousand words Human initiated: emails, fax, ad hoc file transfer, … Software initiated or software-to-software Cross-institutional healthcare processes integration Health Insurance Portability and Accountability Act of 1996 (HIPAA) n n MIEP (1) Privacy, (2) Security, (3) Identifiers (4) Transactions and Code Sets rules cover PHI “in any form or medium” 2
Introduction n Medical images exist in electronic format n n Problem: uncontrolled exchange of medical images n n for easy storage and maintenance promote high quality healthcare services for patients a picture is worth a thousand words Human initiated: emails, fax, ad hoc file transfer, … Software initiated or software-to-software Cross-institutional healthcare processes integration Health Insurance Portability and Accountability Act of 1996 (HIPAA) n n MIEP (1) Privacy, (2) Security, (3) Identifiers (4) Transactions and Code Sets rules cover PHI “in any form or medium” 2
 Proposed Approach n n n Medical Image Exchange Platform (MIEP) Layered approach Contemporary information technologies n n Web services for the information transport Role based access control (RBAC) Watermarking for the integrity and privacy protection Single-point border check MIEP 3
Proposed Approach n n n Medical Image Exchange Platform (MIEP) Layered approach Contemporary information technologies n n Web services for the information transport Role based access control (RBAC) Watermarking for the integrity and privacy protection Single-point border check MIEP 3
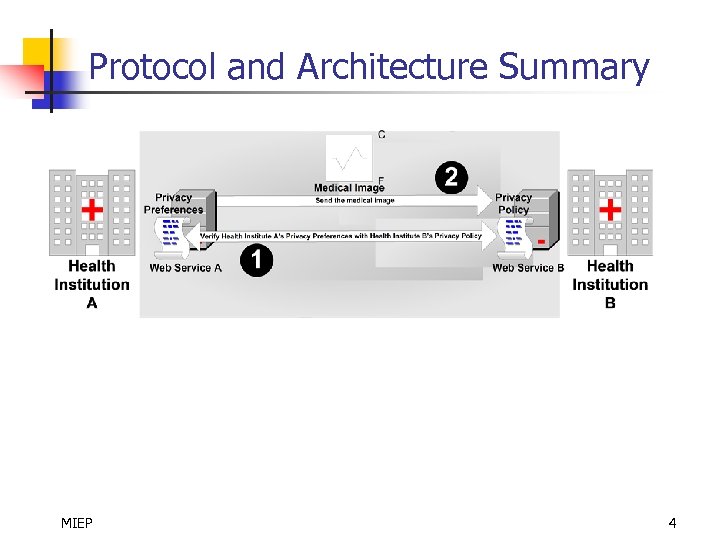 Protocol and Architecture Summary MIEP 4
Protocol and Architecture Summary MIEP 4
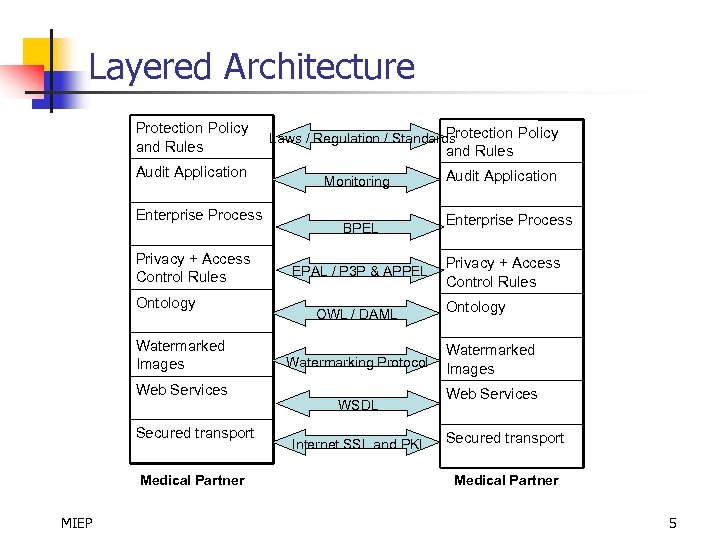 Layered Architecture Protection Policy and Rules Audit Application Enterprise Process Privacy + Access Control Rules Ontology Watermarked Images Web Services Secured transport Medical Partner MIEP Protection Policy Laws / Regulation / Standards and Rules Monitoring BPEL EPAL / P 3 P & APPEL OWL / DAML Watermarking Protocol WSDL Internet SSL and PKI Audit Application Enterprise Process Privacy + Access Control Rules Ontology Watermarked Images Web Services Secured transport Medical Partner 5
Layered Architecture Protection Policy and Rules Audit Application Enterprise Process Privacy + Access Control Rules Ontology Watermarked Images Web Services Secured transport Medical Partner MIEP Protection Policy Laws / Regulation / Standards and Rules Monitoring BPEL EPAL / P 3 P & APPEL OWL / DAML Watermarking Protocol WSDL Internet SSL and PKI Audit Application Enterprise Process Privacy + Access Control Rules Ontology Watermarked Images Web Services Secured transport Medical Partner 5
 Development Methodology - Overview n n Policies Rules Technical Auditing MIEP 6
Development Methodology - Overview n n Policies Rules Technical Auditing MIEP 6
 Development Methodology - Policies n n n Protection policies should comply with requirements in laws, regulations, and code of practices. Healthcare process integration should comply with the protection policies - privacy and access control requirements should be specified explicitly. Existing protection policy guarding internal operations may serve as basic hints for external partners. MIEP 7
Development Methodology - Policies n n n Protection policies should comply with requirements in laws, regulations, and code of practices. Healthcare process integration should comply with the protection policies - privacy and access control requirements should be specified explicitly. Existing protection policy guarding internal operations may serve as basic hints for external partners. MIEP 7
 Development Methodology - Rules n n RBAC for employees of internal and external parties Need-to-know principle - consider: n n the access need of each task of each process for each role sensitivity of the image content contingencies and necessary override mechanisms => avoid ad hoc decisions. Make sure that medical partners understand not only the protection policies but also the ontology based on which these rules are defined MIEP 8
Development Methodology - Rules n n RBAC for employees of internal and external parties Need-to-know principle - consider: n n the access need of each task of each process for each role sensitivity of the image content contingencies and necessary override mechanisms => avoid ad hoc decisions. Make sure that medical partners understand not only the protection policies but also the ontology based on which these rules are defined MIEP 8
 Development Methodology - Technical n n n Express these rules in a high level language such as EPAL, P 3 P, and APPEL. Ensure document images are exchanged via only the pre-defined MIEP Web service calls and from authenticated partners. Firewall and email filters may be implemented to scan for and stop uncontrolled image traffic. Watermark (containing protection information) is inserted into each image sent or received via the MIEP Web services. Validation of document access against the access information embedded in the image watermark. MIEP 9
Development Methodology - Technical n n n Express these rules in a high level language such as EPAL, P 3 P, and APPEL. Ensure document images are exchanged via only the pre-defined MIEP Web service calls and from authenticated partners. Firewall and email filters may be implemented to scan for and stop uncontrolled image traffic. Watermark (containing protection information) is inserted into each image sent or received via the MIEP Web services. Validation of document access against the access information embedded in the image watermark. MIEP 9
 Development Methodology - Auditing n n Auditing application may use existing in-house software as a blue-print, but now stricter. Monitor actively all document image access to ensure n n n MIEP security and privacy constraints are met the integrity of image data otherwise, alerts should be sent to the management. 10
Development Methodology - Auditing n n Auditing application may use existing in-house software as a blue-print, but now stricter. Monitor actively all document image access to ensure n n n MIEP security and privacy constraints are met the integrity of image data otherwise, alerts should be sent to the management. 10
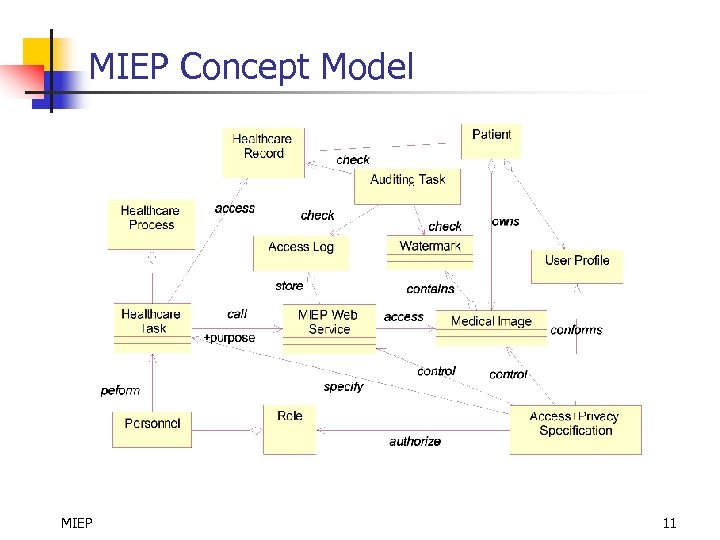 MIEP Concept Model MIEP 11
MIEP Concept Model MIEP 11
 Some Technical Details n n Outgoing Images Incoming Images Image Pickup Service Privacy Policies and Rules MIEP 12
Some Technical Details n n Outgoing Images Incoming Images Image Pickup Service Privacy Policies and Rules MIEP 12
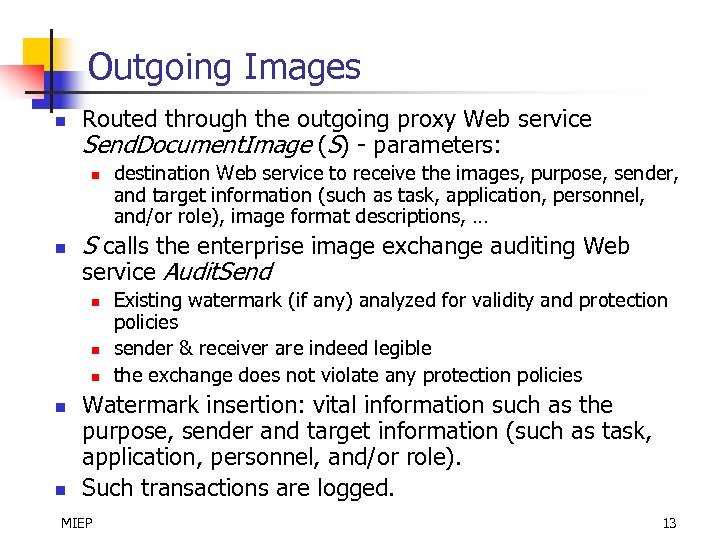 Outgoing Images n Routed through the outgoing proxy Web service Send. Document. Image (S) - parameters: n n S calls the enterprise image exchange auditing Web service Audit. Send n n n destination Web service to receive the images, purpose, sender, and target information (such as task, application, personnel, and/or role), image format descriptions, … Existing watermark (if any) analyzed for validity and protection policies sender & receiver are indeed legible the exchange does not violate any protection policies Watermark insertion: vital information such as the purpose, sender and target information (such as task, application, personnel, and/or role). Such transactions are logged. MIEP 13
Outgoing Images n Routed through the outgoing proxy Web service Send. Document. Image (S) - parameters: n n S calls the enterprise image exchange auditing Web service Audit. Send n n n destination Web service to receive the images, purpose, sender, and target information (such as task, application, personnel, and/or role), image format descriptions, … Existing watermark (if any) analyzed for validity and protection policies sender & receiver are indeed legible the exchange does not violate any protection policies Watermark insertion: vital information such as the purpose, sender and target information (such as task, application, personnel, and/or role). Such transactions are logged. MIEP 13
 Incoming Images n Routed through the incoming proxy Web service Receive. Document. Image (R) - parameters: n n n destination to receive the images (Web service URL, port and operation), the user id, purpose, sender and target information (such as task, application, personnel, and/or role), image format descriptions, … R call the enterprise image exchange auditing Web service Audit. Receive for validation. Compliant watermark from partner’s MIEP (if any) can be extracted for addition validation. Similar watermark insertion for tracking. Such transactions are logged. MIEP 14
Incoming Images n Routed through the incoming proxy Web service Receive. Document. Image (R) - parameters: n n n destination to receive the images (Web service URL, port and operation), the user id, purpose, sender and target information (such as task, application, personnel, and/or role), image format descriptions, … R call the enterprise image exchange auditing Web service Audit. Receive for validation. Compliant watermark from partner’s MIEP (if any) can be extracted for addition validation. Similar watermark insertion for tracking. Such transactions are logged. MIEP 14
 Image Pickup Service n n Not every business partner could immediately switch to a MIEP platform. Initially allow a “pick up” service to cater for manual retrieval of the image in case the partner is not fully automated. Used in a call back mode to further enhance the security for program-to-program interaction. Pre-registration required for auditing and protection. MIEP 15
Image Pickup Service n n Not every business partner could immediately switch to a MIEP platform. Initially allow a “pick up” service to cater for manual retrieval of the image in case the partner is not fully automated. Used in a call back mode to further enhance the security for program-to-program interaction. Pre-registration required for auditing and protection. MIEP 15
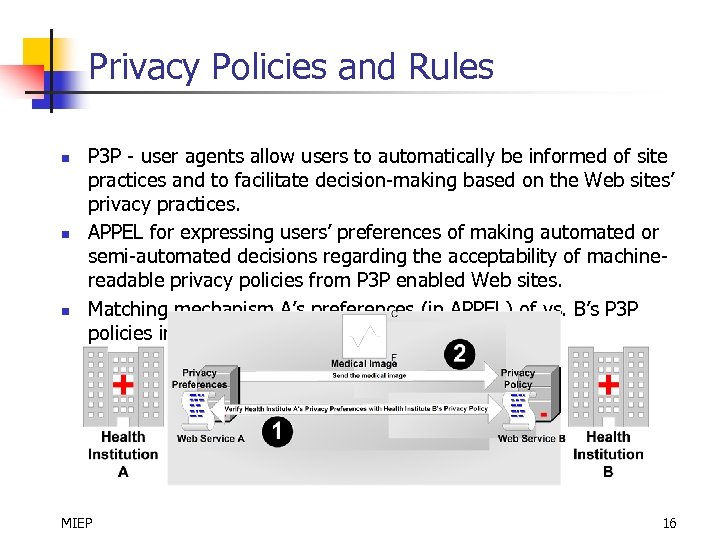 Privacy Policies and Rules n n n P 3 P - user agents allow users to automatically be informed of site practices and to facilitate decision-making based on the Web sites’ privacy practices. APPEL for expressing users’ preferences of making automated or semi-automated decisions regarding the acceptability of machinereadable privacy policies from P 3 P enabled Web sites. Matching mechanism A’s preferences (in APPEL) of vs. B’s P 3 P policies in Step 1. MIEP 16
Privacy Policies and Rules n n n P 3 P - user agents allow users to automatically be informed of site practices and to facilitate decision-making based on the Web sites’ privacy practices. APPEL for expressing users’ preferences of making automated or semi-automated decisions regarding the acceptability of machinereadable privacy policies from P 3 P enabled Web sites. Matching mechanism A’s preferences (in APPEL) of vs. B’s P 3 P policies in Step 1. MIEP 16
 Validation with HIPAA rules n The right to view and make a copy of a patients own medical records, and the right to request PHI to be shared with the patient in a particular way. n n The right to find out where PHI has been shared for purposes other than care, payment, or healthcare operations n n MIEP tracks and logs all cross-institutional exchange of medical image. The right to request special restrictions on the use or disclosure of PHI. n n Patients can readily request their own medical images through the MIEP image pick up services MIEP maintains the patients’ profiles regarding their privacy preferences The right to file complaints. n MIEP can provide exchange records and evidence. 17
Validation with HIPAA rules n The right to view and make a copy of a patients own medical records, and the right to request PHI to be shared with the patient in a particular way. n n The right to find out where PHI has been shared for purposes other than care, payment, or healthcare operations n n MIEP tracks and logs all cross-institutional exchange of medical image. The right to request special restrictions on the use or disclosure of PHI. n n Patients can readily request their own medical images through the MIEP image pick up services MIEP maintains the patients’ profiles regarding their privacy preferences The right to file complaints. n MIEP can provide exchange records and evidence. 17
 Summary n Replace ad hoc and manual image exchange procedures with a unified Medical Image Exchange Platform (MIEP) n n n Embedded watermark ensure integrity, privacy, and access control Advantages of Web service / SOA n n Layered MIEP architecture Design and implementation methodology Image exchange protocol Application of Web services and watermarking technologies Legacy systems and existing practices corrected with MIEP Reusability of MIEP => streamlines the development, deployment, and maintenance of software components for image exchange Single border check for all the protection policies and auditing procedures => adequate control and auditing Expandability For future tracking and auditing purposes MIEP 18
Summary n Replace ad hoc and manual image exchange procedures with a unified Medical Image Exchange Platform (MIEP) n n n Embedded watermark ensure integrity, privacy, and access control Advantages of Web service / SOA n n Layered MIEP architecture Design and implementation methodology Image exchange protocol Application of Web services and watermarking technologies Legacy systems and existing practices corrected with MIEP Reusability of MIEP => streamlines the development, deployment, and maintenance of software components for image exchange Single border check for all the protection policies and auditing procedures => adequate control and auditing Expandability For future tracking and auditing purposes MIEP 18
 Future Work § § Exploration of any potential usability and performance issues. Mechanisms and tools for managing the interactions taking place between different layers in the proposed framework. Further requirements engineering for privacy and security. Application of ontologies § § § role classifications terms used to present a domain of knowledge Representation of the privacy access control policy in EPAL and the compliance of EPAL to the Web services. Adoption issues Application in other professional business domains: financial, legal … MIEP 19
Future Work § § Exploration of any potential usability and performance issues. Mechanisms and tools for managing the interactions taking place between different layers in the proposed framework. Further requirements engineering for privacy and security. Application of ontologies § § § role classifications terms used to present a domain of knowledge Representation of the privacy access control policy in EPAL and the compliance of EPAL to the Web services. Adoption issues Application in other professional business domains: financial, legal … MIEP 19
 Question and Answer Thank you! Contact: dicksonchiu@ieee. org MIEP 20
Question and Answer Thank you! Contact: dicksonchiu@ieee. org MIEP 20
… <-- evidence (abbreviated) -->" src="https://present5.com/presentation/c0b505108d6e7c82045584984e8a49e5/image-21.jpg" alt="An Illustrative APPEL Privacy Preference
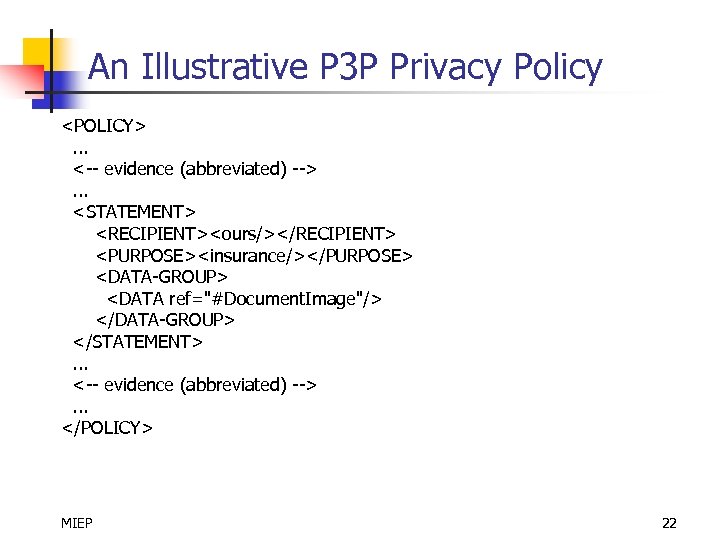 An Illustrative P 3 P Privacy Policy
An Illustrative P 3 P Privacy Policy


