98b78fa1d62c88cb7e21ffe149306fab.ppt
- Количество слайдов: 25

Project 2
Introduction Network Vulnerability Assessment “A review of a system of systems to identify weaknesses or errors in design, implementation, or operation. ”
Security Space Security Audit l Security scanning service. l It requires little or no knowledge or skill to set up and run. l Platforms – – – Windows Linux Unix Macintosh Web servers Database products. (Almost anything that can be remotely tested).
Advantages (claimed) l An external view of your network. Getting an external view of your network usually involves getting access to a machine on the outside of your network for the purpose of running your scan. The cost of setting up and maintaining this type of access can often be more than the cost of this service alone. l Reproducible. As an audit mechanism, Security Audits are a low cost, reproducible audit that can be run whenever you need. l Low effort Setting up and configuring a vulnerability scanner for properation can be time-consuming. l Always up to date By using a service, you automatically receive the latest vulnerability tests without having to install them into your own scanner
Different Services They offer four different types of service. – – Standard Service. Advanced Service. Dedicated Service. Recurring Service.
Standard Service l The service scans more than 1500 ports (0 -1024 and other service ports). l The test can be set to start at time of convenience for the user. l For monthly or annual subscription unlimited IP allocated for the user can be scanned unlimited times. l The user can also purchase additional channels. Usually one channel is allocated to each user which mean a bandwidth of 50 kbps. If the user wants to get more bandwidth it can be bought.
Advanced Service l The service scans more than 65535 ports. l The test can be set to start at time of convenience for the user. l For monthly or annual subscription unlimited IP allocated for the user can be scanned unlimited times. l It scan 256 IPs with one request for category or any test the user desires in the same network and the results will be shown in the same report. l The user can also purchase additional channels. If the user wants to get more bandwidth it can be bought.
Dedicated Service l Designed for large scale networks, can run 50 audits simultaneously (50 channels) per dedicated server. l Servers can be leased weekly or monthly, without long term commitments. l The user can audit unlimited IPs (providing the IP is yours, or allocated for your own use). Can run unlimited number of audits. l The reports include detailed and comprehensive information on vulnerabilities and remedies. The reports can also be able merges into a single report, for comparison or summary
Recurring Service l Performs a port scan of all 65, 535 port of an IP for open ports and possible trojans. l Can schedule audits to be launched automatically at selected times. l The report provides detailed and comprehensive information on vulnerabilities and remedies. l May use up your quota of audits as quickly or as slowly as you choose. May carry over unused audits (if any) from one year to the next
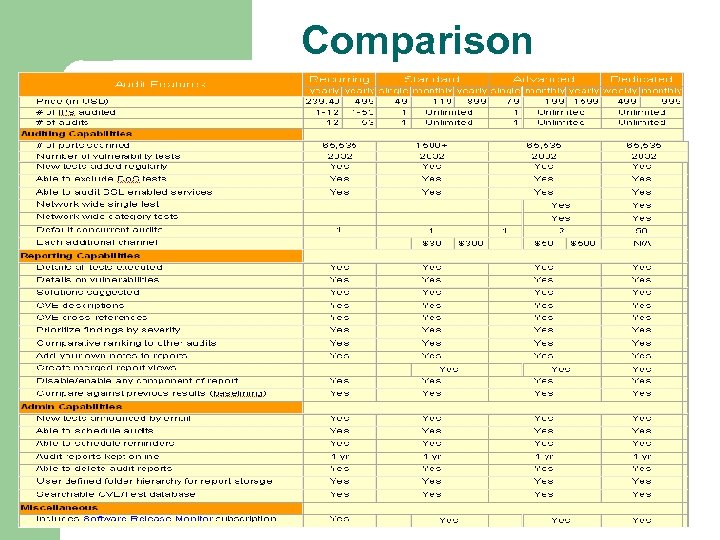
Comparison
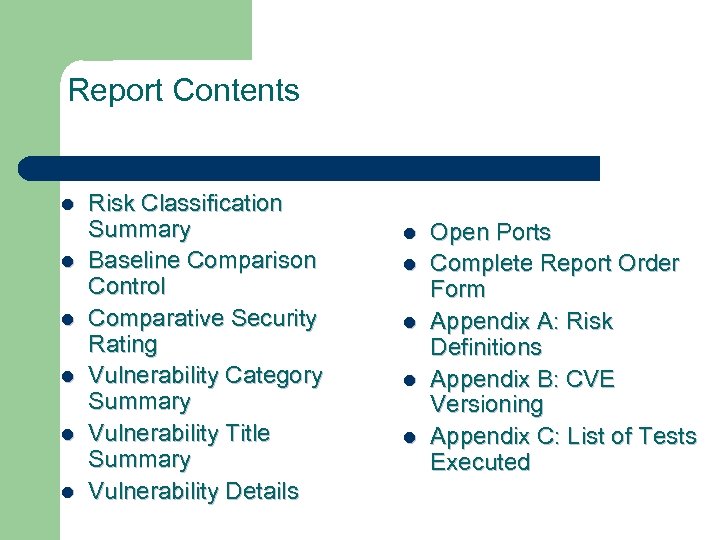
Report Contents l l l Risk Classification Summary Baseline Comparison Control Comparative Security Rating Vulnerability Category Summary Vulnerability Title Summary Vulnerability Details l l l Open Ports Complete Report Order Form Appendix A: Risk Definitions Appendix B: CVE Versioning Appendix C: List of Tests Executed
Conclusion to Security. Space Security Audit l For smaller organizations, Security scan is a means of convenience and no capital expenditure. l Security scans of some kind should be part of any welldesigned security maintenance plan. Disadvantages – Too many false positives (according to comments of various security experts). Since it is paid for the user would like the reports to be efficient. – If the system contains confidential information then it is not a very good idea to store the reports of vulnerability in someone else’s server.
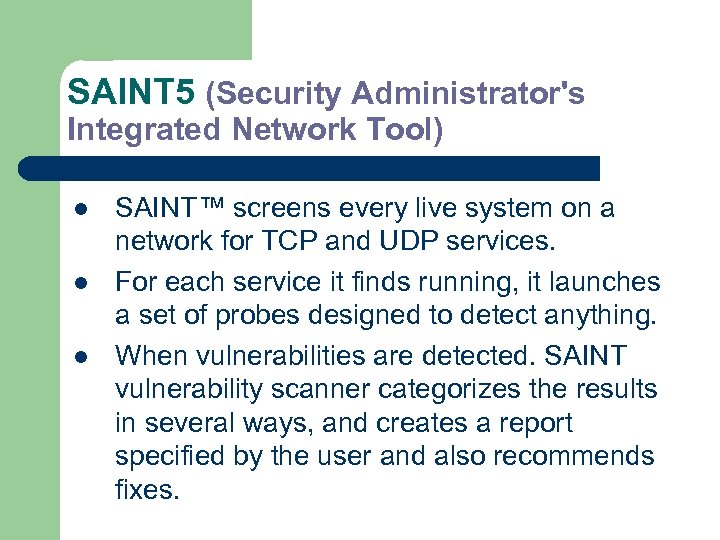
SAINT 5 (Security Administrator's Integrated Network Tool) l l l SAINT™ screens every live system on a network for TCP and UDP services. For each service it finds running, it launches a set of probes designed to detect anything. When vulnerabilities are detected. SAINT vulnerability scanner categorizes the results in several ways, and creates a report specified by the user and also recommends fixes.
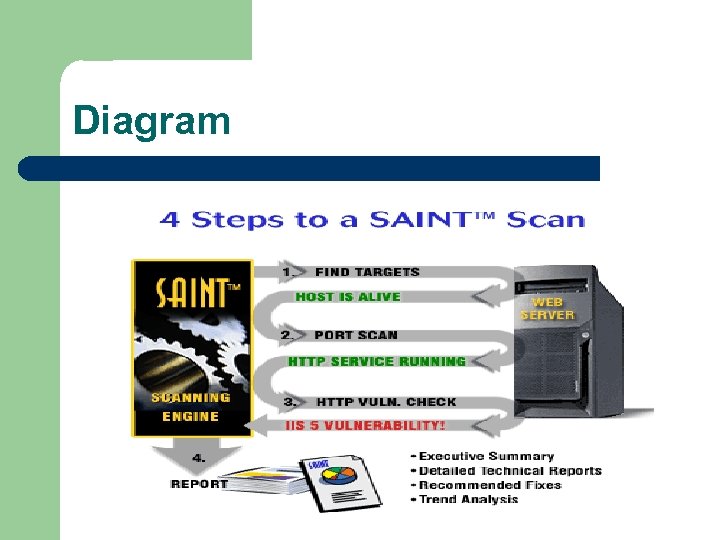
Diagram
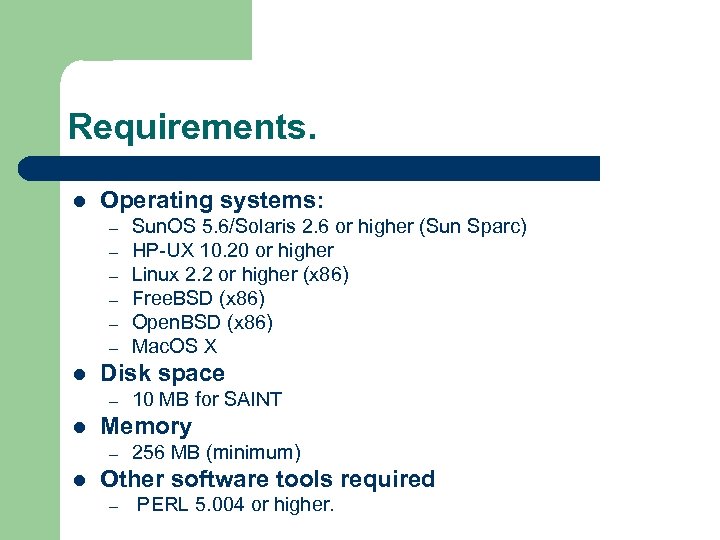
Requirements. l Operating systems: – – – l Disk space – l 10 MB for SAINT Memory – l Sun. OS 5. 6/Solaris 2. 6 or higher (Sun Sparc) HP-UX 10. 20 or higher Linux 2. 2 or higher (x 86) Free. BSD (x 86) Open. BSD (x 86) Mac. OS X 256 MB (minimum) Other software tools required – PERL 5. 004 or higher.
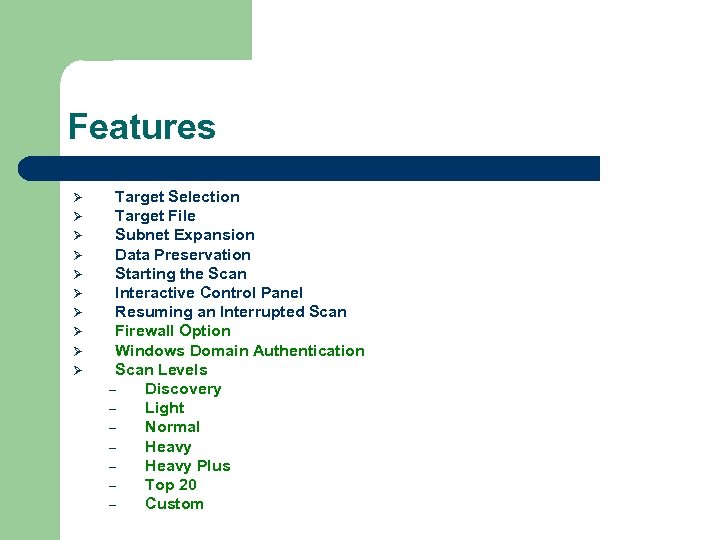
Features Ø Ø Ø Ø Ø Target Selection Target File Subnet Expansion Data Preservation Starting the Scan Interactive Control Panel Resuming an Interrupted Scan Firewall Option Windows Domain Authentication Scan Levels – Discovery – Light – Normal – Heavy Plus – Top 20 – Custom
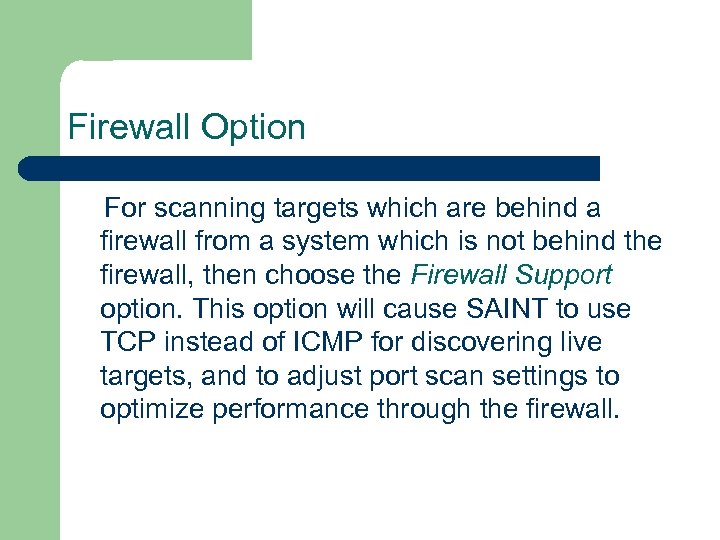
Firewall Option For scanning targets which are behind a firewall from a system which is not behind the firewall, then choose the Firewall Support option. This option will cause SAINT to use TCP instead of ICMP for discovering live targets, and to adjust port scan settings to optimize performance through the firewall.
Windows Domain Authentication While some vulnerabilities on Microsoft Windows systems can be detected by an unprivileged scan, others, such as missing hot fixes and service packs, require administrative privileges on the target. In order to conduct a thorough scan of Windows targets, SAINT gives you the option of authenticating to the domain in order to detect these types of vulnerabilities.
Scan Levels Scan level can be of different intensity. – Discovery l – Light l – Hosts which are alive and reports their IP addresses. SAINT collects information from the DNS (Domain Name System), tries to identify the operating system, and tries to establish what RPC (Remote Procedure Call) services the host offers and what file systems it shares via the network. Normal l This level includes all of the Light scan probes, and also includes probes for the presence of common network services
Scan Levels (cont. ) – Heavy l – Heavy Plus l – This scanning level is the same as heavy except that it does not attempt to avoid ports which are known to cause certain software to crash Top 20 l – At this level, SAINT will check for services listening on any TCP and UDP port. (with the exception of ports which are known to cause certain software to crash when scanned) Any services detected will then be scanned for any known vulnerabilities. This is a special scanning level designed specifically to detect vulnerabilities which are among the SANS Top 20 Most Critical Internet Security Vulnerabilities Custom l This scanning level allows the user to run any combination of SAINT probes. Which of the user-defined scan levels to use is selected from the pull-down menu.
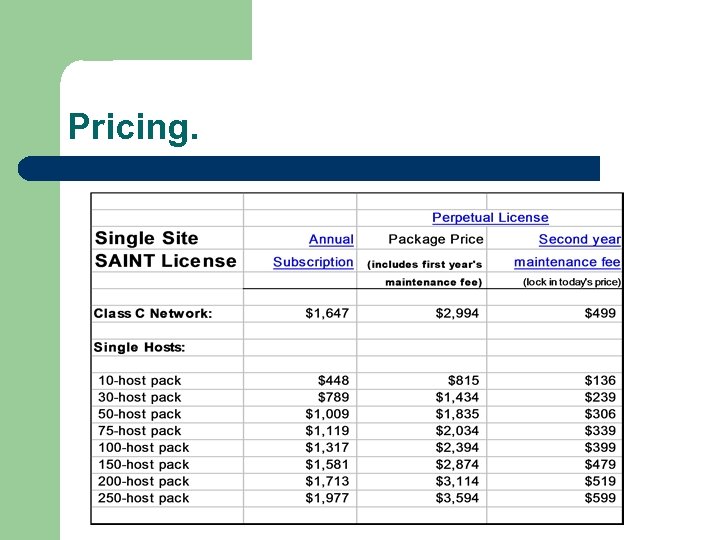
Pricing.
Conclusion to SAINT 5 l You can configure this tool extensively, tailoring scans to your network’s characteristics and determining the depth of the scans you run. l SAINT has a very efficient way of presenting the report. The installation procedure is very easy. l Conveniently, SAINT 5 can be configured to log on to Microsoft Windows domains— simply by using an administrative user name and password—to perform tests that require domain authentication. Disadvantages – – Within reports there’s no query feature or grouping function that would help the user zero in on certain problems. Quickly become overwhelming, especially if scanning larger networks.
Security Audit V. S SAINT. l l l l l Price is definitely a factor. Secuirty Audit is available at just below $1000 (dedicated server) while SAINT while cost a shade below $3000. SAINT is runs specific scans as introduced by the user. While Security Audit is more general. SAINT provides more privacy than Security Audit since the reports are with the user. Security Audit is hassle free. And more convenient for small businesses and home user. While SAINT is built with the picture to maintain of large network in mind. Security Audit makes the maintenance easier and cheap, since no need to hire a in-house security expert (if situation permits it). SAINT offers technical support for a fee. SAINT provides a SAINTwriter to edit and present reports in different forms (e. g. executive form etc). Security Audit provides an external view of the system. While to get external view by using SAINT might prove expensive (setting up and maintaining the external machine). SAINT cannot be set up in a windows machine. While Security Audit does not need to be set up.
SOURCES http: //www. saintcorporation. com http: //www. securityspace. com www. pcmag. com http: //specials. cramsession. com/s/promos/Security_Watch_LP_2_2. htm http: //www. esecurityplanet. com/trends/print. php/10751_1475291 http: //www. nwc. com/1201 f 1 b 1. html Security space (E-Soft Inc) 2025 Guelph Line Burlington, ON L 7 P 4 X 4 Phone: (905) 331 -2260 Fax: (905) 331 -2504 Toll-free: (800) 799 4831 Email: general@securityspace. com SAINT Corporation 4720 Montgomery Lane Suite 800 Bethesda, MD 20814 Phone: (301) 656 -0521 or 1 -(800) 596 -2006 Fax: (301) 656 -4806
Questions KAZI NASIM FAISAL 100659146 PICTURE TAKEN FROM: http: //www. haverhillpl. org/images/question 001. jpg
98b78fa1d62c88cb7e21ffe149306fab.ppt