a474fc56045d6c0216e4d6127aea5e53.ppt
- Количество слайдов: 20
 Privacy Issues in Vehicular Ad Hoc Networks. Florian Dötzer BMW Group Research and Technology
Privacy Issues in Vehicular Ad Hoc Networks. Florian Dötzer BMW Group Research and Technology
 Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
 Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
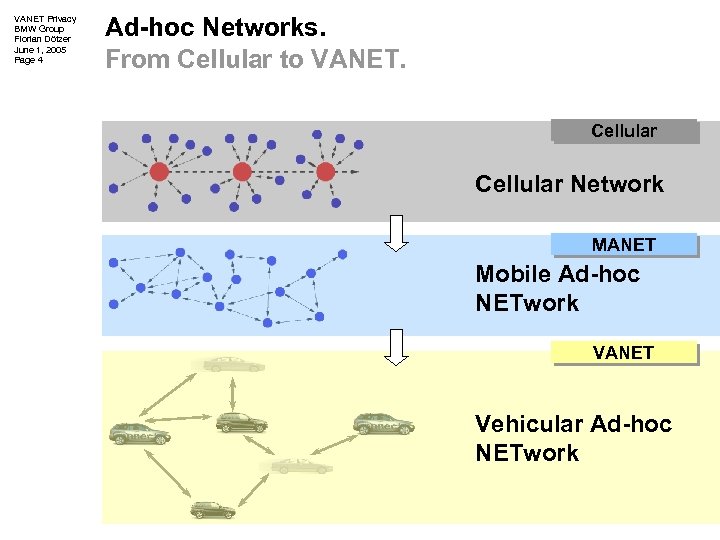 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 4 Ad-hoc Networks. From Cellular to VANET. Cellular Network MANET Mobile Ad-hoc NETwork VANET Vehicular Ad-hoc NETwork
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 4 Ad-hoc Networks. From Cellular to VANET. Cellular Network MANET Mobile Ad-hoc NETwork VANET Vehicular Ad-hoc NETwork
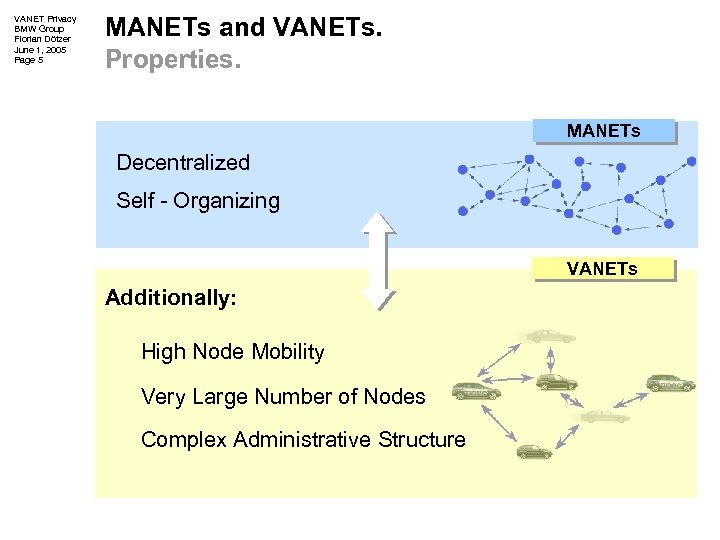 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 5 MANETs and VANETs. Properties. MANETs Decentralized Self - Organizing VANETs Additionally: High Node Mobility Very Large Number of Nodes Complex Administrative Structure
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 5 MANETs and VANETs. Properties. MANETs Decentralized Self - Organizing VANETs Additionally: High Node Mobility Very Large Number of Nodes Complex Administrative Structure
 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 6 VANET. Application Local Danger Warning. VSC – Vehicle Safety Communications
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 6 VANET. Application Local Danger Warning. VSC – Vehicle Safety Communications
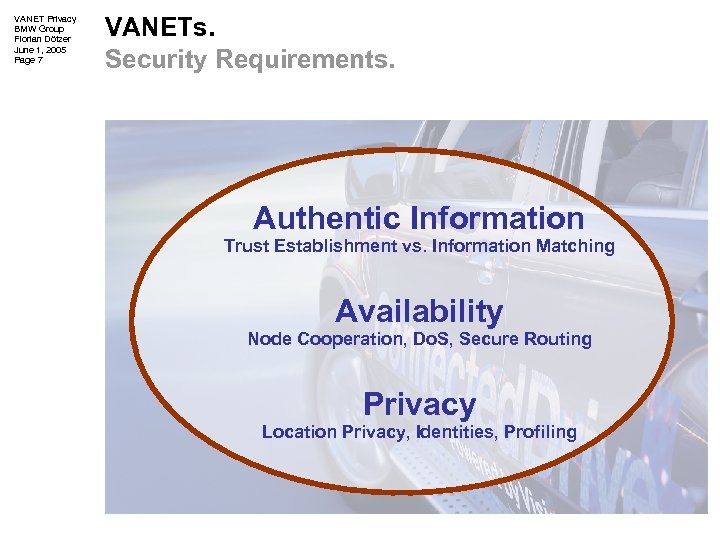 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 7 VANETs. Security Requirements. Authentic Information Trust Establishment vs. Information Matching Availability Node Cooperation, Do. S, Secure Routing Privacy Location Privacy, Identities, Profiling
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 7 VANETs. Security Requirements. Authentic Information Trust Establishment vs. Information Matching Availability Node Cooperation, Do. S, Secure Routing Privacy Location Privacy, Identities, Profiling
 Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 9 Privacy. Importance for VANETs. Cars = Personal Devices Position is known Cars get connected Attacks on Privacy become relevant + Privacy is essential for VANETs BUT: Privacy cannot be “added” afterwards!
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 9 Privacy. Importance for VANETs. Cars = Personal Devices Position is known Cars get connected Attacks on Privacy become relevant + Privacy is essential for VANETs BUT: Privacy cannot be “added” afterwards!
 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 10 VANET Privacy. Example Threats and Attacks. “Automated” Law Enforcement Identity Tracking Configuration Fingerprinting RF-Fingerprinting Location Recording Movement Profiles Communication Relations
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 10 VANET Privacy. Example Threats and Attacks. “Automated” Law Enforcement Identity Tracking Configuration Fingerprinting RF-Fingerprinting Location Recording Movement Profiles Communication Relations
 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 11 VANET Privacy. Requirements. Use of pseudonyms (no real-world identities) Multiple pseudonyms may be used Pseudonym change application requirements Pseudonyms real-world ID mapping Properties / privileges cryptographically bound
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 11 VANET Privacy. Requirements. Use of pseudonyms (no real-world identities) Multiple pseudonyms may be used Pseudonym change application requirements Pseudonyms real-world ID mapping Properties / privileges cryptographically bound
 Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
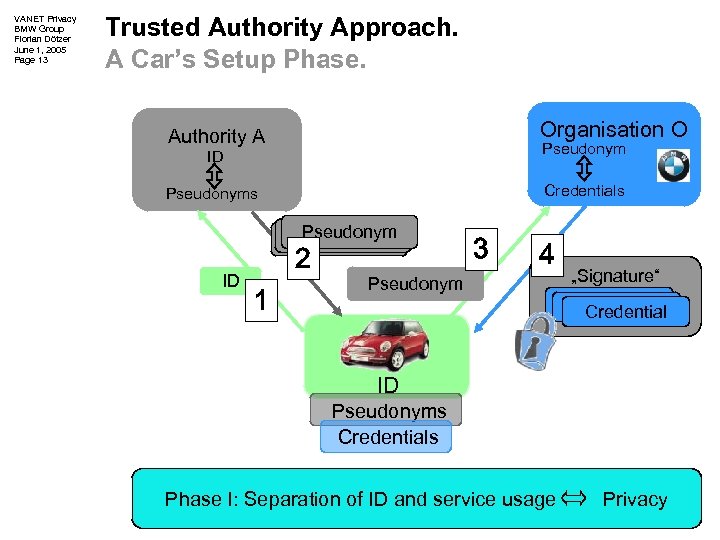 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 13 Trusted Authority Approach. A Car’s Setup Phase. Organisation O Authority A ID Pseudonyms Credentials Pseudonym ID 2 1 3 4 Pseudonym „Signature“ Credential ID Pseudonyms Credentials Phase I: Separation of ID and service usage Privacy
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 13 Trusted Authority Approach. A Car’s Setup Phase. Organisation O Authority A ID Pseudonyms Credentials Pseudonym ID 2 1 3 4 Pseudonym „Signature“ Credential ID Pseudonyms Credentials Phase I: Separation of ID and service usage Privacy
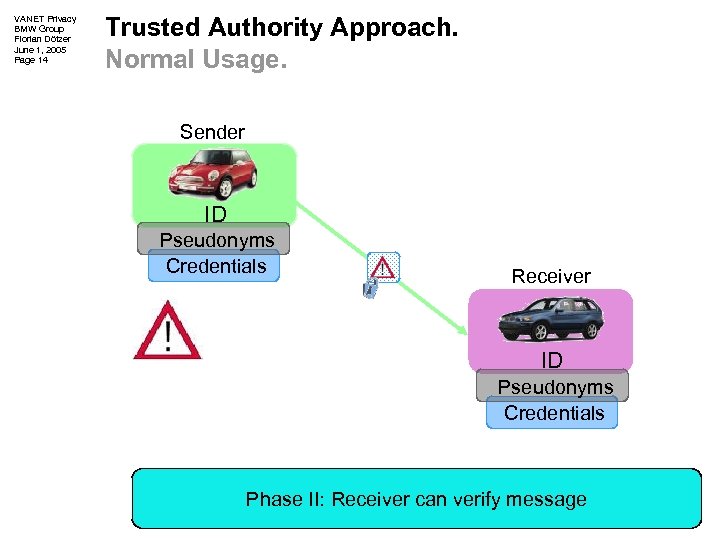 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 14 Trusted Authority Approach. Normal Usage. Sender ID Pseudonyms Credentials Receiver ID Pseudonyms Credentials Phase II: Receiver can verify message
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 14 Trusted Authority Approach. Normal Usage. Sender ID Pseudonyms Credentials Receiver ID Pseudonyms Credentials Phase II: Receiver can verify message
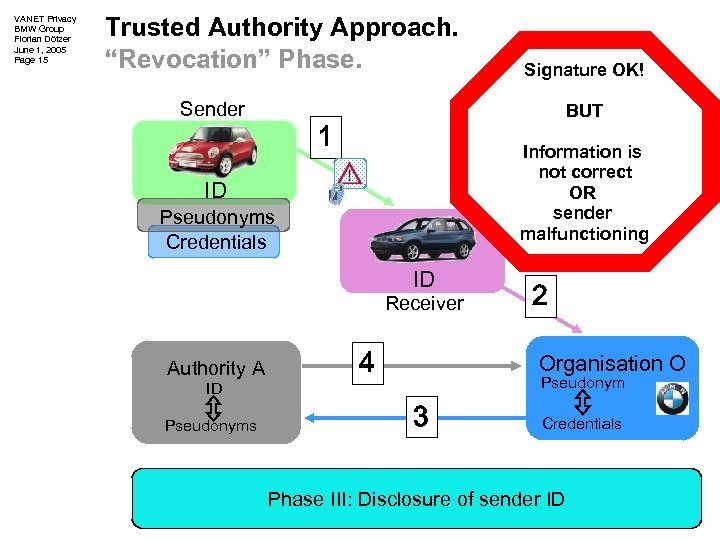 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 15 Trusted Authority Approach. “Revocation” Phase. Sender BUT 1 Information is not correct OR sender malfunctioning ID Pseudonyms Credentials ID Receiver Authority A ID Pseudonyms Signature OK! 4 2 Organisation O Pseudonym 3 Credentials Phase III: Disclosure of sender ID
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 15 Trusted Authority Approach. “Revocation” Phase. Sender BUT 1 Information is not correct OR sender malfunctioning ID Pseudonyms Credentials ID Receiver Authority A ID Pseudonyms Signature OK! 4 2 Organisation O Pseudonym 3 Credentials Phase III: Disclosure of sender ID
 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 16 Trusted Authority Approach. Evaluation. Pro’s + Fulfills given requirements + Provides strong privacy Con’s - Requires independent, trusted authority - Problem of detecting wrong messages
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 16 Trusted Authority Approach. Evaluation. Pro’s + Fulfills given requirements + Provides strong privacy Con’s - Requires independent, trusted authority - Problem of detecting wrong messages
 Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
Agenda. Introduction Privacy in VANETs Exemplary Approach Future Work / Conclusion
 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 18 Future Work. And Open Questions… How to change pseudonyms? Feasibility of Organizational Solution Feasibility of Smart Card Approach Location Related Pseudonyms System without IDs?
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 18 Future Work. And Open Questions… How to change pseudonyms? Feasibility of Organizational Solution Feasibility of Smart Card Approach Location Related Pseudonyms System without IDs?
 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 19 Conclusion. Privacy is essential for VANETs Privacy must be considered at system design Trusted authority approach is far from perfect Additional research is necessary
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 19 Conclusion. Privacy is essential for VANETs Privacy must be considered at system design Trusted authority approach is far from perfect Additional research is necessary
 VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 20 Thanks for Listening. Questions?
VANET Privacy BMW Group Florian Dötzer June 1, 2005 Page 20 Thanks for Listening. Questions?


