b518990f8c3a9da94b623d7e55f3841a.ppt
- Количество слайдов: 16
PKI Solutions: Buy vs. Build David Wasley, U. California (ret. ) Jim Jokl, U. Virginia Nick Davis, U. Wisconsin
Agenda n Why are we here? n Why do you want a PKI? n Implementation Models n And a word or 2 about trust model(s) n Functional Requirements n Some options for Higher Ed. n Case study: University of Wisconsin n Case study: University of Virginia n Q&A
Why are we here? n Asymmetric cryptography is a tool n n n Information integrity and/or security PKI adds identity context & trust model Deployment has been slow but there are new drivers n n n e-business and accountability Scalable secure and/or trusted email High assurance digital credentials
Why do you want a PKI? n n First step in implementation planning Typical application areas: n n Identity credentials Scalable secure email (s/mime) digital document signing Other apps include: n n Document integrity (web sites, digital archive) Infrastructure protection (IPSEC)
Implementation Models n Many different ways to get PKI services n No one perfect way for all campuses n n Cost models may vary greatly depending on size of campus Biggest differences are n n functional capabilities & flexibility a priori “trusted certificates”
Implementation Models (cont. ) n n n Stand-alone PKI for local use PKI as part of a larger community Commercial PKI services n n n Partial outsource Full outsource Bridged PKI
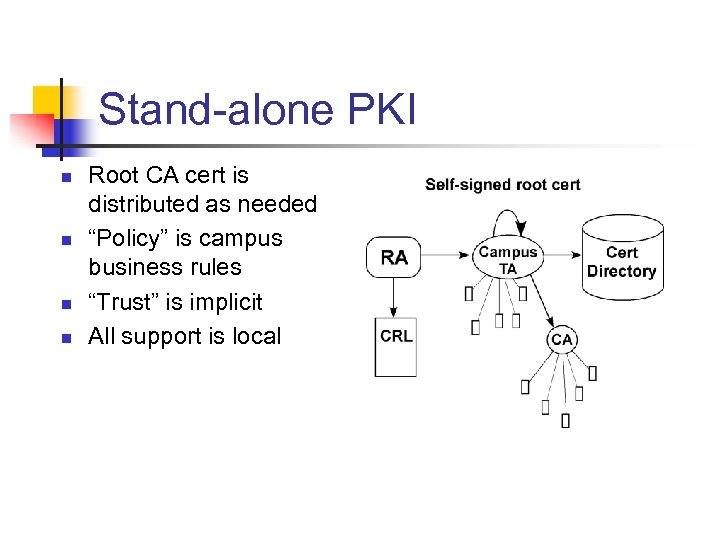
Stand-alone PKI n n Root CA cert is distributed as needed “Policy” is campus business rules “Trust” is implicit All support is local
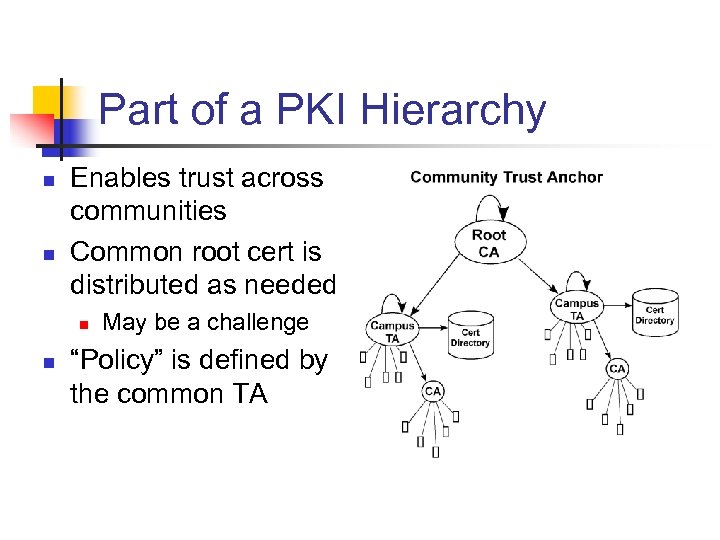
Part of a PKI Hierarchy n n Enables trust across communities Common root cert is distributed as needed n n May be a challenge “Policy” is defined by the common TA
PKI Trust Model(s) n n n Important if certificates are to be used with external parties “Trust Anchor” defines certificate policy for a homogeneous PKI Relying Parties must n n n Understand TA CP Identify which policy(s) it will accept Hold a copy of the TA (root CA) certificate
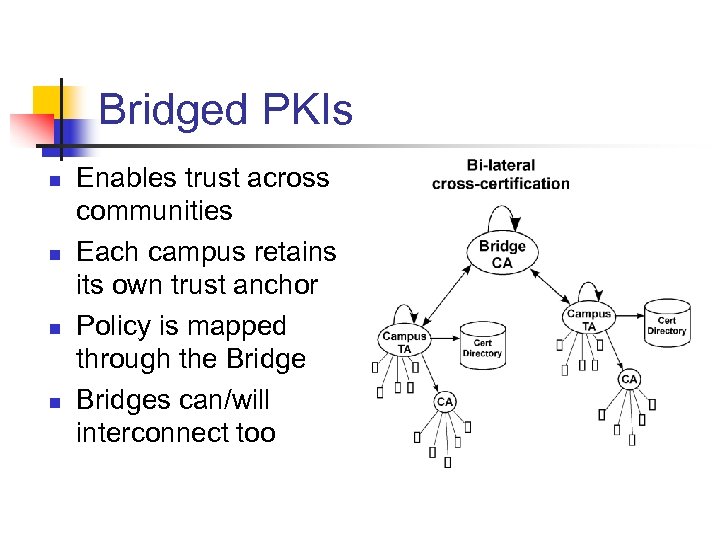
Bridged PKIs n n Enables trust across communities Each campus retains its own trust anchor Policy is mapped through the Bridges can/will interconnect too
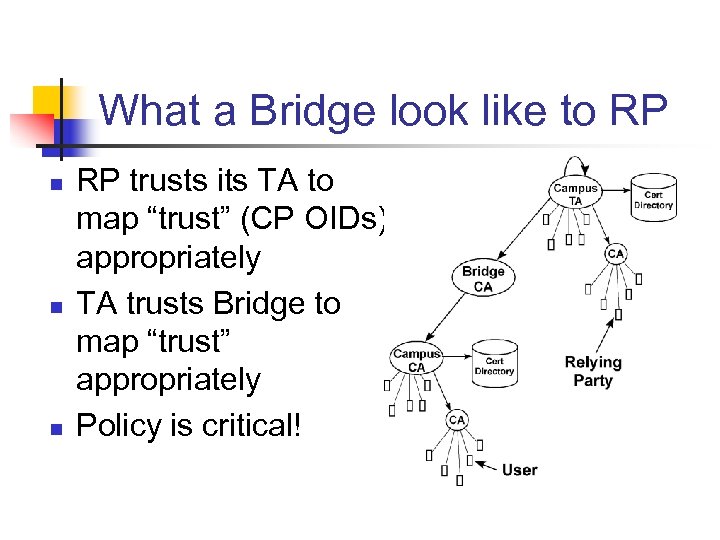
What a Bridge look like to RP n n n RP trusts its TA to map “trust” (CP OIDs) appropriately TA trusts Bridge to map “trust” appropriately Policy is critical!
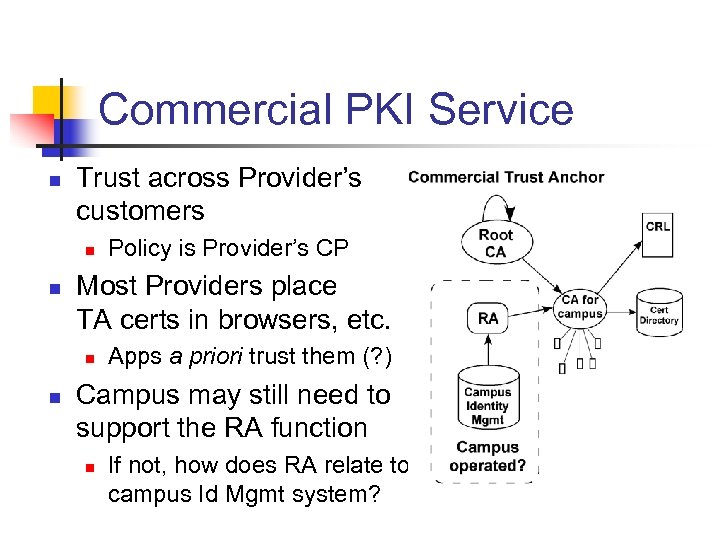
Commercial PKI Service n Trust across Provider’s customers n n Most Providers place TA certs in browsers, etc. n n Policy is Provider’s CP Apps a priori trust them (? ) Campus may still need to support the RA function n If not, how does RA relate to campus Id Mgmt system?
Functional Requirements n Multiple certs per individual n Different cert types n Dual certs and key escrow n Normal versus high assurance certs n Certificate extensions and/or SIA n Real-time certificate status n Subordinate CAs n Infrastructure certs n Transient certs
Some options for Higher Ed. n U. S. Higher Ed. Root (USHER) n Higher Ed. Bridge CA (HEBCA) n Commercial PKI services n n Widely varying features & per user costs EDUCAUSE Identity Management Services Program (IMSP)
Case Studies n University of Wisconsin Nick Davis, PKI Program Manager UW, Madison n University of Virginia Jim Jokl, Director Communications and Systems
Q&A n dlwasley@earthlink. net n ndavis 1@wisc. edu n jaj@virginia. edu
b518990f8c3a9da94b623d7e55f3841a.ppt