36f311a84a57dd542001059a7254b014.ppt
- Количество слайдов: 39
PKI: Public Key Infrastructure – tell me in plain English AND THEN deep technical how PKI works Mostly borrowed & updated from Steve Lamb in Microsoft Land…. Scott Rea, PKI Architect, Dartmouth College + HEBCA
Objectives • • Demystify commonly used terminology Explain how PKI works Get you playing with PKI in the lab Make some simple recommendations 2
Agenda • • Foundational Concept PKI and Signatures Recommendations Reference material – Common Algorithms 3
What can PKI enable? Secure Email – sign and/or encrypt messages Secure browsing – SSL – authentication and encryption Secure code – authenticode Secure wireless – PEAP & EAP-TLS Secure documents – Rights Management Secure networks – segmentation via IPsec Secure files – Encrypted File System(EFS) 4

Foundational Concepts 5
Encryption vs. Authentication • Encrypted information cannot be automatically trusted • You still need authentication – Which we can implement using encryption, of course 6
Assets • What we are securing? – Data – Services (i. e. business etc. applications or their individually accessible parts) • This session is not about securing: – People (sorry), cables, carpets, typewriters and computers (!? ) • Some assets are key assets – Passwords, private keys etc… 7
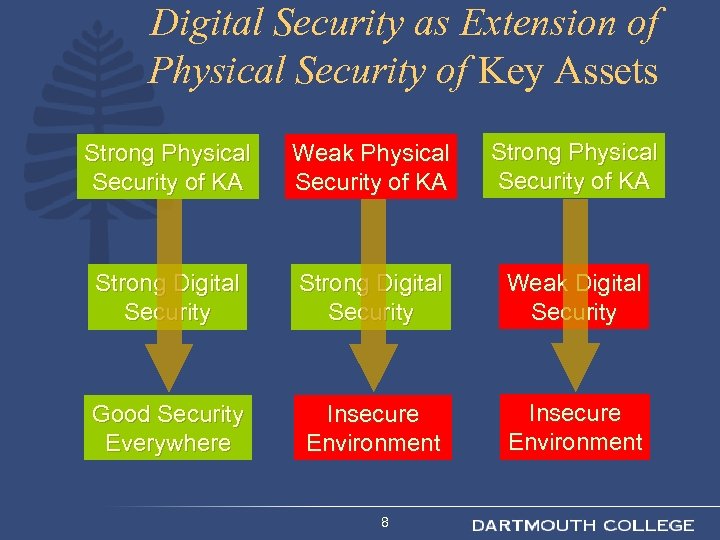
Digital Security as Extension of Physical Security of Key Assets Strong Physical Security of KA Weak Physical Security of KA Strong Digital Security Weak Digital Security Good Security Everywhere Insecure Environment 8
Remember CP and CPS! • “The Certification Practice & Certification Practice Statement (CP/CPS) is a formal statement that describes who may have certificates, how certificates are generated and what they may be used for. ” • http: //www. ietf. org/rfc 3647. txt 9
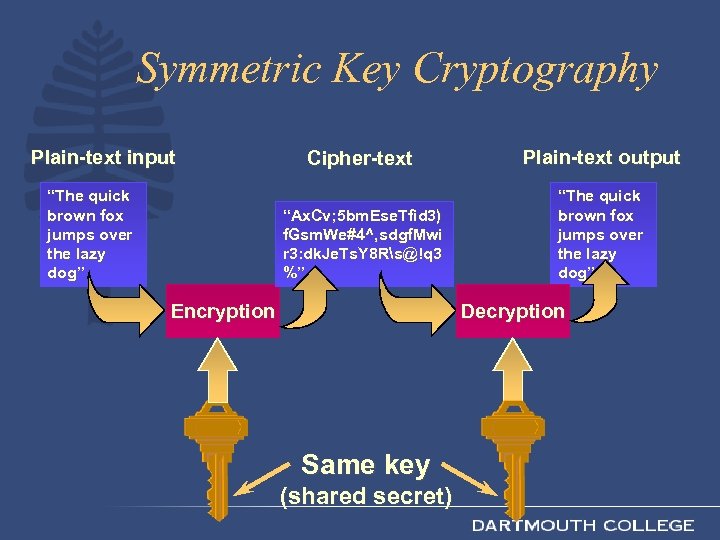
Symmetric Key Cryptography Plain-text input Plain-text output “Ax. Cv; 5 bm. Ese. Tfid 3) f. Gsm. We#4^, sdgf. Mwi r 3: dk. Je. Ts. Y 8 Rs@!q 3 %” “The quick brown fox jumps over the lazy dog” Cipher-text “The quick brown fox jumps over the lazy dog” Encryption Decryption Same key (shared secret)
Symmetric Pros and Cons • Strength: – Simple and really very fast (order of 1000 to 10000 faster than asymmetric mechanisms) • Super-fast (and somewhat more secure) if done in hardware (DES, Rijndael) • Weakness: – Must agree the key beforehand – Securely pass the key to the other party 11
Public Key Cryptography • Knowledge of the encryption key doesn’t give you knowledge of the decryption key • Receiver of information generates a pair of keys – Publish the public key in a directory • Then anyone can send him messages that only she can read 12
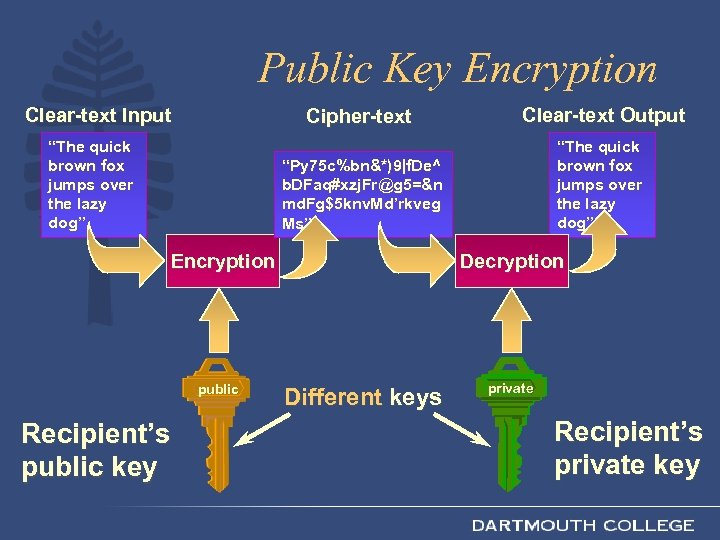
Public Key Encryption Clear-text Input Cipher-text “Py 75 c%bn&*)9|f. De^ b. DFaq#xzj. Fr@g 5=&n md. Fg$5 knv. Md’rkveg Ms” “The quick brown fox jumps over the lazy dog” Clear-text Output “The quick brown fox jumps over the lazy dog” Encryption public Recipient’s public key Decryption Different keys private Recipient’s private key
Public Key Pros and Cons • Weakness: – Extremely slow – Susceptible to “known ciphertext” attack – Problem of trusting public key (see later on PKI) • Strength – Solves problem of passing the key – Allows establishment of trust context between parties 14
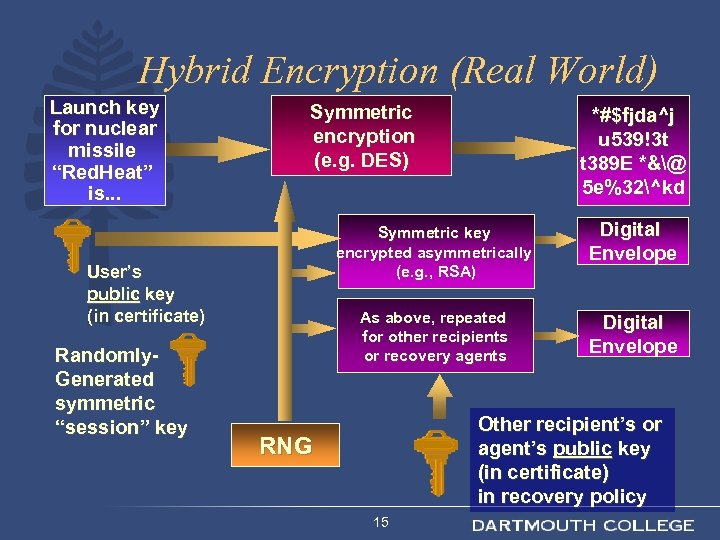
Hybrid Encryption (Real World) Launch key for nuclear missile “Red. Heat” is. . . Symmetric encryption (e. g. DES) Symmetric key encrypted asymmetrically (e. g. , RSA) Digital Envelope As above, repeated for other recipients or recovery agents User’s public key (in certificate) Randomly. Generated symmetric “session” key *#$fjda^j u 539!3 t t 389 E *&@ 5 e%32^kd Digital Envelope Other recipient’s or agent’s public key (in certificate) in recovery policy RNG 15
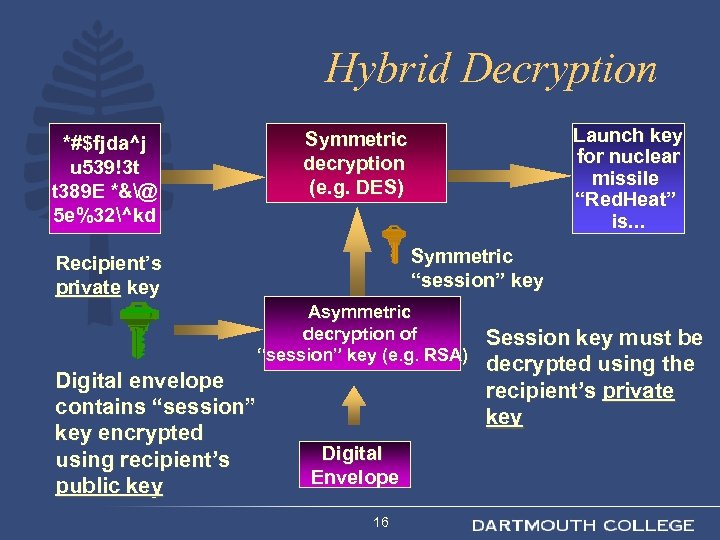
Hybrid Decryption *#$fjda^j u 539!3 t t 389 E *&@ 5 e%32^kd Launch key for nuclear missile “Red. Heat” is. . . Symmetric decryption (e. g. DES) Symmetric “session” key Recipient’s private key Asymmetric decryption of “session” key (e. g. RSA) Digital envelope contains “session” key encrypted using recipient’s public key Digital Envelope 16 Session key must be decrypted using the recipient’s private key
PKI and Signatures 17
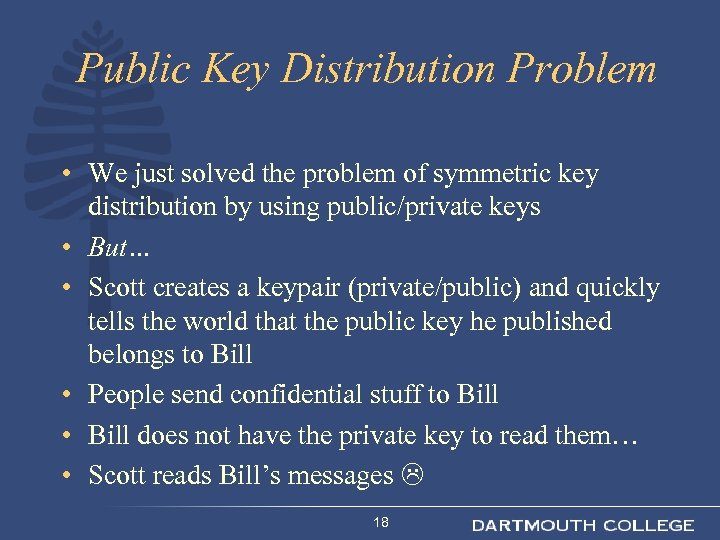
Public Key Distribution Problem • We just solved the problem of symmetric key distribution by using public/private keys • But… • Scott creates a keypair (private/public) and quickly tells the world that the public key he published belongs to Bill • People send confidential stuff to Bill • Bill does not have the private key to read them… • Scott reads Bill’s messages 18

Eureka! • We need PKI to solve that problem • And a few others… 19
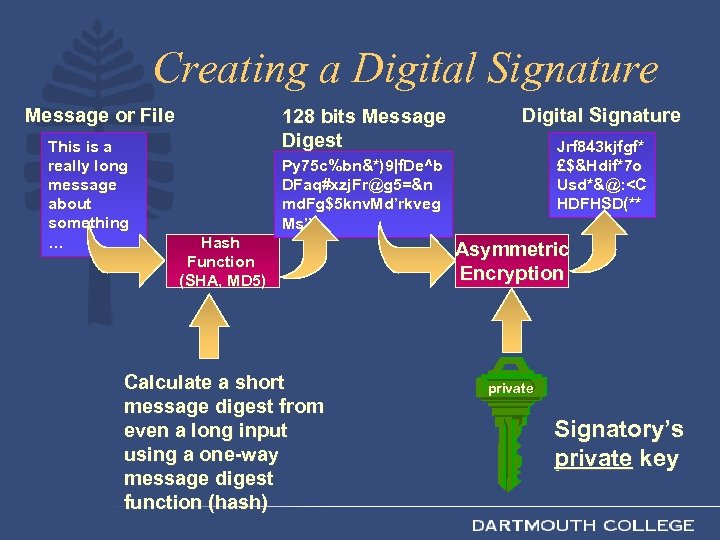
Creating a Digital Signature Message or File This is a really long message about something … 128 bits Message Digest Digital Signature Jrf 843 kjfgf* £$&Hdif*7 o Usd*&@: <C HDFHSD(** Py 75 c%bn&*)9|f. De^b DFaq#xzj. Fr@g 5=&n md. Fg$5 knv. Md’rkveg Ms” Hash Function (SHA, MD 5) Calculate a short message digest from even a long input using a one-way message digest function (hash) Asymmetric Encryption private Signatory’s private key
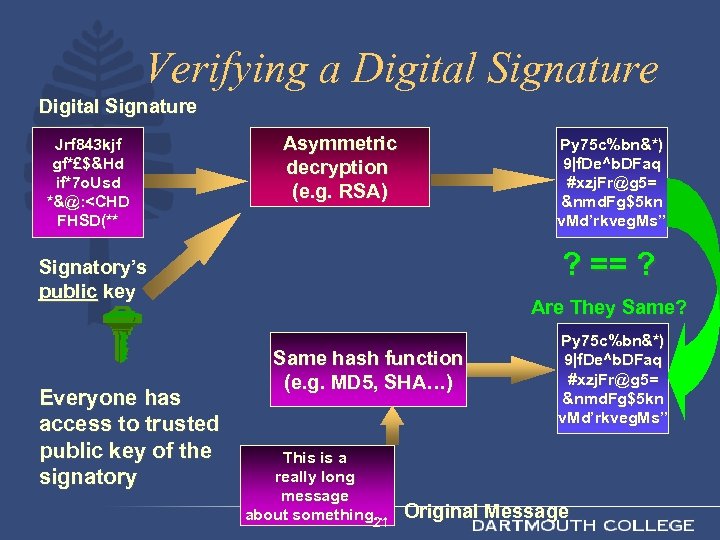
Verifying a Digital Signature Jrf 843 kjf gf*£$&Hd if*7 o. Usd *&@: <CHD FHSD(** Asymmetric decryption (e. g. RSA) Py 75 c%bn&*) 9|f. De^b. DFaq #xzj. Fr@g 5= &nmd. Fg$5 kn v. Md’rkveg. Ms” ? == ? Signatory’s public key Everyone has access to trusted public key of the signatory Are They Same? Same hash function (e. g. MD 5, SHA…) This is a really long message about something… 21 Py 75 c%bn&*) 9|f. De^b. DFaq #xzj. Fr@g 5= &nmd. Fg$5 kn v. Md’rkveg. Ms” Original Message
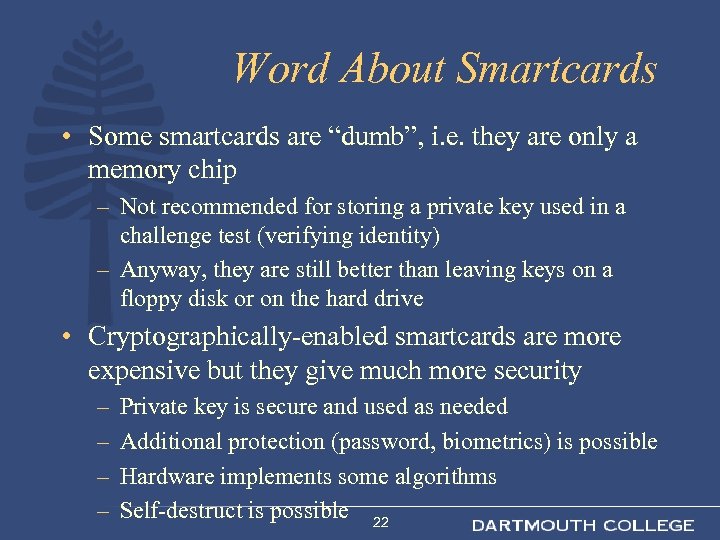
Word About Smartcards • Some smartcards are “dumb”, i. e. they are only a memory chip – Not recommended for storing a private key used in a challenge test (verifying identity) – Anyway, they are still better than leaving keys on a floppy disk or on the hard drive • Cryptographically-enabled smartcards are more expensive but they give much more security – – Private key is secure and used as needed Additional protection (password, biometrics) is possible Hardware implements some algorithms Self-destruct is possible 22
Recommendations • Don’t be scared of PKI! • Set up a test environment to enable you to “play” • Minimise the scope of your first implementation • Read up on CP & CPS • Document the purpose and operating procedures of your PKI 23
Summary • Cryptography is a rich and amazingly mature field • We all rely on it, everyday, with our lives • Know the basics and make good choices avoiding common pitfalls • Plan your PKI early • Avoid very new and unknown solutions • Certificate Policy • Certification Practises statement 24
References • Visit http: //www. pki-page. org/ • Read sci. crypt (incl. archives) • For more detail, read: – – – – Cryptography: An Introduction, N. Smart, Mc. Graw-Hill, ISBN 0 -07 -709987 -7 Practical Cryptography, N. Ferguson & B. Schneier, Wiley, ISBN 0 -471 -22357 -3 Contemporary Cryptography, R. Oppliger, Artech House, ISBN 1 -58053 -642 -5 (to be published May 2005, see http: //www. esecurity. ch/Books/cryptography. html) Applied Cryptography, B. Schneier, John Wiley & Sons, ISBN 0 -471 -11709 -9 Handbook of Applied Cryptography, A. J. Menezes, CRC Press, ISBN 0 -84938523 -7, www. cacr. math. uwaterloo. ca/hac (free PDF) PKI, A. Nash et al. , RSA Press, ISBN 0 -07 -213123 -3 Foundations of Cryptography, O. Goldereich, www. eccc. uni-trier. de/eccc-local/ECCC-Books/oded_book_readme. html Cryptography in C and C++, M. Welschenbach, Apress, ISBN 1 -893115 -95 -X (includes code samples CD) 25
Thanks to Rafal Lukawiecki and Steve Lamb for providing some of the content for this presentation deck – their contact details are as follows… rafal@projectbotticelli. co. uk stephlam@microsoft. com 26

Common Algorithms 27
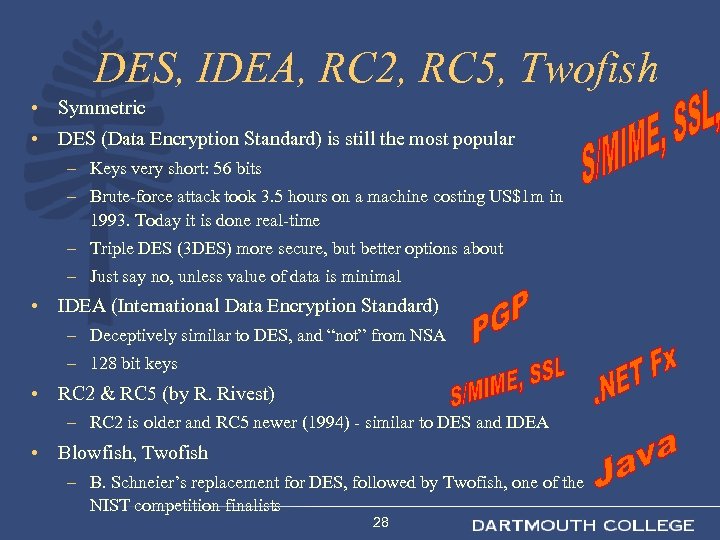
DES, IDEA, RC 2, RC 5, Twofish • Symmetric • DES (Data Encryption Standard) is still the most popular – Keys very short: 56 bits – Brute-force attack took 3. 5 hours on a machine costing US$1 m in 1993. Today it is done real-time – Triple DES (3 DES) more secure, but better options about – Just say no, unless value of data is minimal • IDEA (International Data Encryption Standard) – Deceptively similar to DES, and “not” from NSA – 128 bit keys • RC 2 & RC 5 (by R. Rivest) – RC 2 is older and RC 5 newer (1994) - similar to DES and IDEA • Blowfish, Twofish – B. Schneier’s replacement for DES, followed by Twofish, one of the NIST competition finalists 28
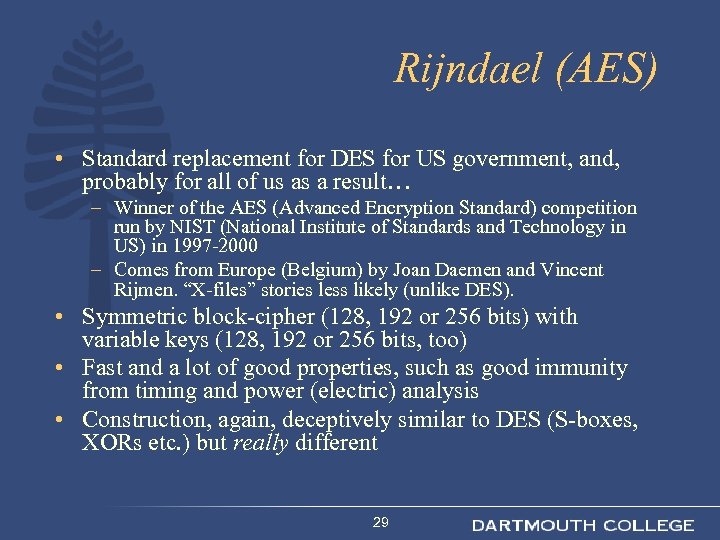
Rijndael (AES) • Standard replacement for DES for US government, and, probably for all of us as a result… – Winner of the AES (Advanced Encryption Standard) competition run by NIST (National Institute of Standards and Technology in US) in 1997 -2000 – Comes from Europe (Belgium) by Joan Daemen and Vincent Rijmen. “X-files” stories less likely (unlike DES). • Symmetric block-cipher (128, 192 or 256 bits) with variable keys (128, 192 or 256 bits, too) • Fast and a lot of good properties, such as good immunity from timing and power (electric) analysis • Construction, again, deceptively similar to DES (S-boxes, XORs etc. ) but really different 29
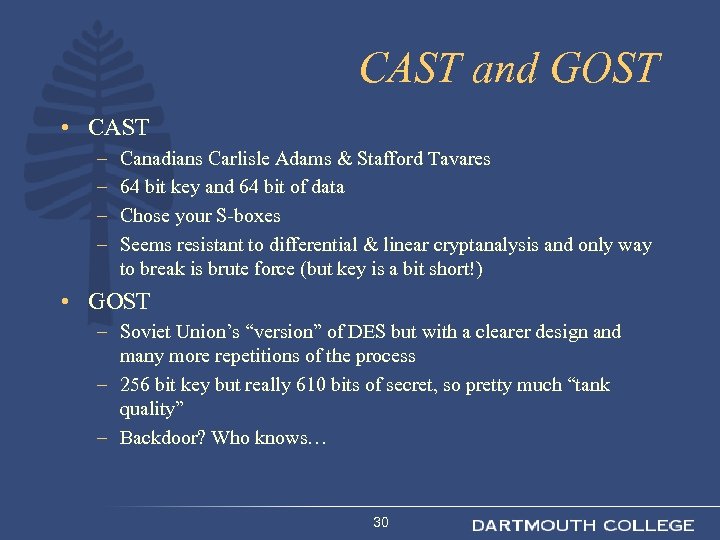
CAST and GOST • CAST – – Canadians Carlisle Adams & Stafford Tavares 64 bit key and 64 bit of data Chose your S-boxes Seems resistant to differential & linear cryptanalysis and only way to break is brute force (but key is a bit short!) • GOST – Soviet Union’s “version” of DES but with a clearer design and many more repetitions of the process – 256 bit key but really 610 bits of secret, so pretty much “tank quality” – Backdoor? Who knows… 30
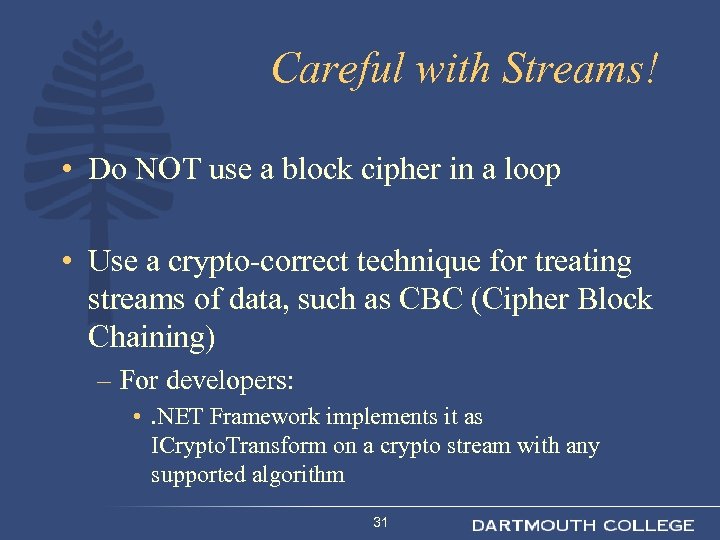
Careful with Streams! • Do NOT use a block cipher in a loop • Use a crypto-correct technique for treating streams of data, such as CBC (Cipher Block Chaining) – For developers: • . NET Framework implements it as ICrypto. Transform on a crypto stream with any supported algorithm 31
RC 4 • Symmetric – Fast, streaming encryption • R. Rivest in 1994 – Originally secret, but “published” on sci. crypt • Related to “one-time pad”, theoretically most secure • But! • It relies on a really good random number generator – And that is the problem • Nowadays, we tend to use block ciphers in modes of operation that work for streams 32
RSA, DSA, El. Gamal, ECC • Asymmetric – Very slow and computationally expensive – need a computer – Very secure • Rivest, Shamir, Adleman – 1978 – Popular and well researched – Strength in today’s inefficiency to factorise into prime numbers – Some worries about key generation process in some implementations • DSA (Digital Signature Algorithm) – NSA/NIST thing – Only for digital signing, not for encryption – Variant of Schnorr and El. Gamal sig algorithm • El. Gamal – Relies on complexity of discrete logarithms • ECC (Elliptic Curve Cryptography) – Really hard maths and topology – Improves RSA (and others) 33
Quantum Cryptography • Method for generating and passing a secret key or a random stream – Not for passing the actual data, but that’s irrelevant • Polarisation of light (photons) can be detected only in a way that destroys the “direction” (basis) – So if someone other than you observes it, you receive nothing useful and you know you were bugged • Perfectly doable over up-to-120 km dedicated long fibreoptic link – Seems pretty perfect, if a bit tedious and slow – Practical implementations still use AES/DES etc. for actual encryption • Don’t confuse it with quantum computing, which won’t be with us for at least another 50 years or so, or maybe longer… 34
MD 5, SHA • Hash functions – not encryption at all! • Goals: – Not reversible: can’t obtain the message from its hash – Hash much shorter than original – Two messages won’t have the same hash • MD 5 (R. Rivest) – 512 bits hashed into 128 – Mathematical model still unknown – But it resisted major attacks • SHA (Secure Hash Algorithm) 35 – US standard based on MD 5
Diffie-Hellman, “SSL”, Certs • Methods for key generation and exchange • DH is very clever since you always generate a new “key-pair” for each asymmetric session – STS, MTI, and certs make it even safer • Certs (certificates) are the most common way to exchange public keys – Foundation of Public Key Infrastructure (PKI) • SSL uses a protocol to exchange keys safely – See later 36
Cryptanalysis • Brute force – Good for guessing passwords, and some 40 -bit symmetric keys (in some cases needed only 27 attempts) • Frequency analysis – For very simple methods only (US mobiles) • Linear cryptanalysis – For stronger DES-like, needs 243 plain-cipher pairs • Differential cryptanalysis – Weaker DES-like, needs from 214 pairs • Power and timing analysis – Fluctuations in response times or power usage by CPU 37
Strong Systems • It is always a mixture! Changes all the time… • Symmetric: – AES, min. 128 bits for RC 2 & RC 5, 3 DES, IDEA, carefully analysed RC 4, 256 bit better • Asymmetric: – RSA, El. Gamal, Diffie-Hellman (for keys) with minimum 1024 bits (go for the maximum, typically 4096, if you can afford it) • Hash: – Either MD 5 or SHA but with at least 128 bit results, 256 better 38
Weak Systems • Anything with 40 -bits (including 128 and 56 bit versions with the remainder “fixed”) – Most consider DES as fairly weak algorithm • CLIPPER • A 5 (GSM mobile phones outside US) • Vigenère (US mobile phones) – Dates from 1585! • Unverified certs with no trust • Weak certs (as in many “class 1” personal certs) 39
36f311a84a57dd542001059a7254b014.ppt