ed8805c5cb145e04d5ae7069fc4e2666.ppt
- Количество слайдов: 26
PHREAKING
Content • Phreaking history • Bluetooth vulnerabilities • Smart phone vulnerabilities • Scandal in Greece • US State investigation and Report about Chinese vendors
Let’s try! • Can I have some phone numbers?
Term and reasons • What is “phreaking”? • Phone and freak • Why it developed? • Long distance calls • One and only operator in U. S. • Signaling vs. traffic, control plane vs. data plane
Simplest methods • Switch hook • vs. DTMF (Dual-tone multi-frequency signaling)
2600 Hz • AT&T automatic switches • Tone dialing • In-band signaling • Different SF (single-frequency) tones had different control meaning • Originally planned to be used internally between remote switches • 2600 Hz meant to remote (long distance) switch that call is over (off- hook), but transparently go through in local switch • Means long distance carrier remained seized • Joe Engressia, blind, perfect-pitch 7 -year old boy (1957) found the signal • John "Captain Crunch“ Draper found a free whistle to make the same sound • After resetting the line, short 2600 Hz whistles can route you to another long distance number
Cap’n’Crunch Whistle
MF (Multi-frequency) Tones • Most common signaling used MF • 1964 Bell System Technical Journal • Published an article about technical details of long distance signaling frequencies used • Medium level knowledge in electronics was enough to recreate circuits • Blue boxes • Esquire Magazine published a story “Secrets of the Little Blue Box” • Provided a popular description of using “blue box” technology including enough technical details that others satrted being interested • Steve Wozniak • More details one year later: "How to Build a 'Phone Phreaks' box" in Ramparts Magazine
Blue Box • Generates the same tones were used communication (control calls) between telecom switches
Rainbow Boxes • Black box • Provided a free call to the caller, but device was connected to receiver (called) party • “The F relay was used to detect a ring trip, and when activated, switched the called telephone from the ringing supply to the audio path. The D relay was used to start and stop the metering of the telephone call. The trick was to activate the F relay but not the D relay. ” • http: //en. wikipedia. org/wiki/Bl ack_box_%28 phreaking%29 • Red box • Indicates to the network that coin is dropped to the payphone so call can be initiated • In US: Automated Coin Toll Service
BBS-s and Information Sharing • Bulletin Board System, accessed by personal computers and modems • During these times hard discussion was ongoing to split AT&T into small pieces • 1984 AT&T breakup
Toll Fraud • Small companies emerged to handle long distance market calls • Complex process: • dial a local access number, • enter calling card number (6 -7 digits) • enter area code and phone number • To find a valid card number was almost possible by hand (call to a BBS for example) • It was impossible or terribly expensive to trace these hacks by the small companies
Diverters • Call forwarding features was not part of business exchanges (until 1993) • Small businesses switched on their call answering diverters to use telecom operators service (it is a call to another equipment) • Some diverters gave you a dial tone after recording was stopped • Phreakers needed to find these problematic services • Cost was covered by small businesses • These voice mail boxes and bridges could be used as a communication channel for several phreaks until they were discovered
As a Summary • “Many of today’s hacks work because the traditional phone system was built on the premise that only large, monopolistic phone companies would be using it, and they would all play by the same rules. But the network isn't the telcos' private sandbox anymore; it can be manipulated and controlled by anybody who understands basic computer networking. ” • http: //www. wired. com/wired/archive/12. 12/phreakers_pr. ht ml
Greece Scandal • Vodafone Greece use Ericsson equipment • Seemed around 100 mobile phone numbers of politicians (also the prime minister) were tapped • Started before the 2004 Olympics, until March 2005 • The phone calls in question were "conference called" to 14 other lines with prepaid cards • (Prepaid cards were located in the area of Ilissia (coincidentally around the American embassy). • Calls seem to have been recorded. • Vodafone informed the government right away, scandal (partly political) issued on 2006.
Greece Scandal • Rouge software was detected after another (SMS sending issue) was investigated by Ericsson employees • http: //www. schneier. com/blog/archives/2006/06/greek_wir etappi_1. html
Bluetooth Vulnerabilities • Bluetooth worm • Sends a marketing message or a program seems useful • Reverse SMS • “Bluesnarfing” • Get access to a mobile using bluetooth connection • Get information, any kind of data, address books, sms-s, chats, etc. • Also able to crash a phone • “Bluebugging” • Able to send commands and control the whole phone behavior • Change mobile to “listener” or spy device • Pairing is needed • A possible option to sniff the data traffic when it's pairing with another device
Lucky and social hacking • Defcon story about Lucky 225 • Vonage as a telecom provider: • "We give people a temporary phone number before we verify it with the phone company, and verification takes a couple of weeks. Somebody could pick the White House number and pretend to be the president. “
Yet the problem is inbound signaling • Today telecom networks do not use inbound signaling • Control plane and data plane separation is a must • Yet possible to hack control plane but far more expensive device is needed • Application level signaling can be done inbound • Citibank card registration process
Smart Phones Vulnerabilities • Installed applications can take over controlling your phone • Too many software version, different bugs in different software levels • No firewall on devices • Forced install/uninstall
Security Issue • Investigative Report on the U. S. National Security Issues Posed by Chinese Telecommunications Companies Huawei and ZTE
Security Reports of H & ZTE • U. S. National Security Report about Chinese Telecommunications Companies Huawei and ZTE • “In particular, to the extent these companies are influenced by the state, or provide Chinese intelligence services access to telecommunication networks, the opportunity exists for further economic and foreign espionage by a foreign nation-state already known to be a major perpetrator of cyber espionage. ”
Executive Summary • “Neither company was willing to provide sufficient evidence to • • • ameliorate the Committee’s concerns. Neither company was forthcoming with detailed information about its formal relationships or regulatory interaction with Chinese authorities. Neither company provided specific details about the precise role of each company’s Chinese Communist Party Committee. Furthermore, neither company provided detailed information about its operations in the United States. Huawei, in particular, failed to provide thorough information about its corporate structure, history, ownership, operations, financial arrangements, or management. Most importantly, neither company provided sufficient internal documentation or other evidence to support the limited answers they did provide to Committee investigators. ”
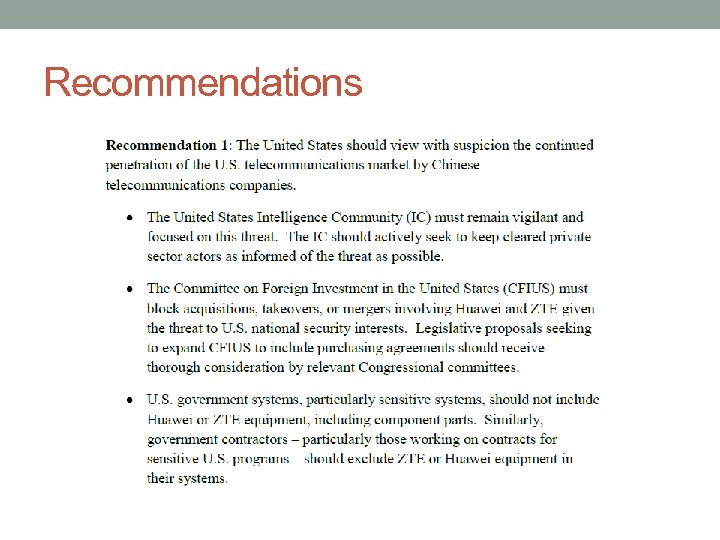
Recommendations
Recommendations

Asterisk – (asterisk. org)
ed8805c5cb145e04d5ae7069fc4e2666.ppt