5d50c912b1f2e3c8cff743f1a9af0153.ppt
- Количество слайдов: 15
Permission-Based Sending (PBS) NSLP: Network Traffic Authorization draft-hong-nsis-pbs-nslp-01 Se Gi Hong & Henning Schulzrinne Columbia University July 2008 IETF 72 - NSIS 1

Overview of PBS • Objective – Preventing Denial-of-Service (Do. S) attacks and other forms of unauthorized traffic. • Network traffic authorization – A sender has to receive permission from the intended receiver before it injects any packets into the network. – Permission represents the authority to send data. • Deny-by-default – In the closed network (all end users have PBS NSLP functionalities) • The unauthorized traffic without permission is dropped at the first router by default. – In the open Internet (some end users do not have PBS NSLP functionalities) • The traffic from the end users who do not have PBS NSLP functionalities are rate-limited by default. July 2008 IETF 72 - NSIS 2

Design Overview • Distributed system – The permission is granted by the intended receiver of a data flow. – Signaling installs and revokes the permission state of routers for data flows. • Stateful system – A subset of routers keeps state for a data flow and monitors whether the flow is authorized. • Deployable system – PBS can be applied to current networks. • The PBS does not change IP and TCP/UDP packet header. – Existing security protocol is used. • IPsec • Scalable system – Not all routers need to be aware of PBS. – Reduce computational overhead. • Only the data packets from senders who are affected by the attacks use IPsec. July 2008 IETF 72 - NSIS 3

Design Overview • Do. S defense mechanism – Do. S detection mechanism • PBS Detection Algorithm (PDA) can detect Do. S attacks. • PDA uses signaling messages to monitor the attacks. – Reaction mechanism against Do. S attacks • Limited permission – Limited permission prevents overflow of data packets. • IPsec Authentication Header (AH) – For the authentication and integrity of data packets. • Changing data path – To avoid a compromised router that drops legitimate packets. July 2008 IETF 72 - NSIS 4
Three Components of the PBS NSLP Architecture • Path-coupled (on-path) signaling component – Installs and maintains permission state. – Monitors attacks, and triggers reaction mechanism against the attacks. – Authentication of signaling message is protected by IPsec AH. • Authorization component – Decides whether to grant permission (amount of data volume) for a flow – Detects and identifies the attack by PDA. – Decides the reaction mechanism against the attacks. • e. g. , IPsec AH for data packet, changing data flow path • Traffic management component – Screens the data packets to see whether the data packets are authorized. – Drops the unauthorized packets using IP packet filter. – Calculates the volume of the data to monitor data flow. – Verifies the authentication of packets. July 2008 IETF 72 - NSIS 5

PBS NSLP Signaling Message • Two-way handshake – Query message • Sent by a sender to request permission • Requested application is described • Rate-limited by proof-of-work – Permission message • Sent by a receiver • Sets up (grants), removes (revokes) and modifies permission state • Triggers reaction mechanism against the attacks • Soft-state – The permission state is refreshed periodically by a soft-state mechanism July 2008 IETF 72 - NSIS 6
PBS Detection Algorithm (PDA) • Monitoring Do. S attack – Use existing PBS NSLP messages (Query/Permission messages) – Use soft-state mechanism to periodically monitor the data flow • Basic operation of PDA – Query message sent by a sender contains the number of bytes that the sender has sent since the permission was granted – The receiver compares the number of bytes in the Query message and the number of bytes that the receiver has actually received – If there is a difference, the signaling message (Permission message) triggers the reaction mechanism July 2008 IETF 72 - NSIS 7
Back-up slides July 2008 IETF 72 - NSIS 8
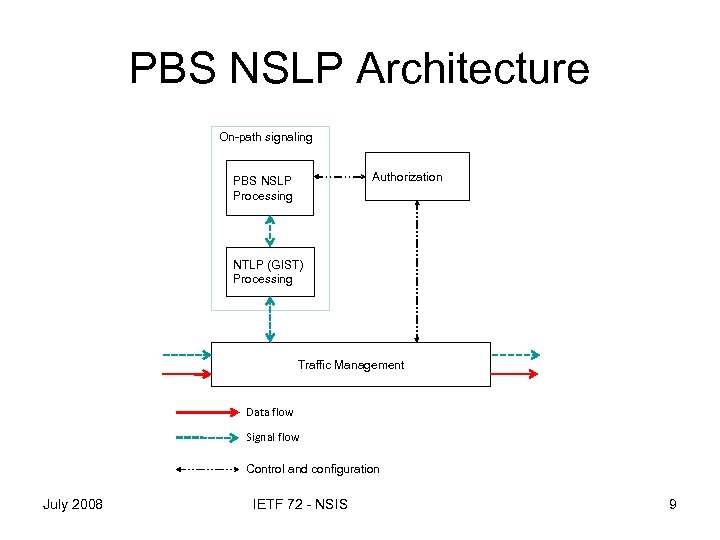
PBS NSLP Architecture On-path signaling Authorization PBS NSLP Processing NTLP (GIST) Processing Traffic Management Data flow Signal flow Control and configuration July 2008 IETF 72 - NSIS 9
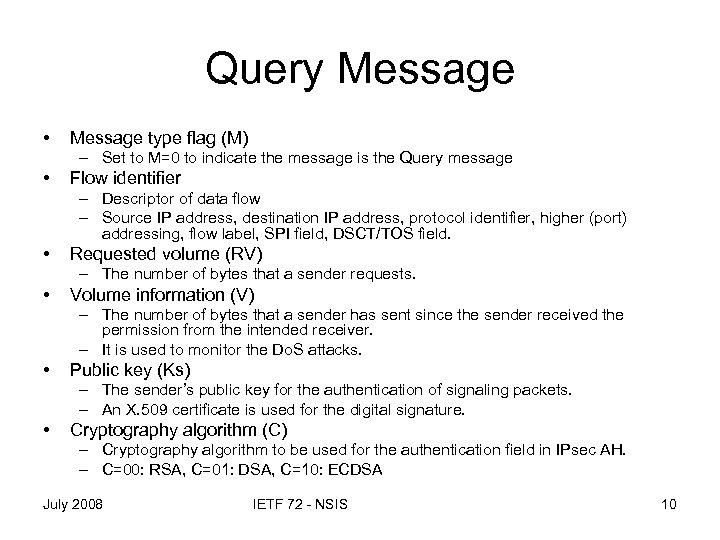
Query Message • Message type flag (M) – Set to M=0 to indicate the message is the Query message • Flow identifier – Descriptor of data flow – Source IP address, destination IP address, protocol identifier, higher (port) addressing, flow label, SPI field, DSCT/TOS field. • Requested volume (RV) – The number of bytes that a sender requests. • Volume information (V) – The number of bytes that a sender has sent since the sender received the permission from the intended receiver. – It is used to monitor the Do. S attacks. • Public key (Ks) – The sender’s public key for the authentication of signaling packets. – An X. 509 certificate is used for the digital signature. • Cryptography algorithm (C) – Cryptography algorithm to be used for the authentication field in IPsec AH. – C=00: RSA, C=01: DSA, C=10: ECDSA July 2008 IETF 72 - NSIS 10

Permission Message • Message type flag (M) – Set to M=1 to indicate the message is the Permission message • • Flow identifier Allowed volume (AV) – The number of bytes that a receiver grants a sender for the request. • Time limit (TTL) – Time limit for the permission of the data flow. • Refresh period (T) – Used for the soft-state of the permission. • Solution flags (S) – S=00: No reaction, S=01: IPsec AH with HMAC, S=10: IPsec AH with public key cryptography for the data flow. S=11: The sender needs to change data path. • Public key (Kr) – The receiver’s public key for the authentication of signaling packets. – An X. 509 certificate is used for the digital signature. • Cryptography algorithm (C) – Cryptography algorithm to be used for the authentication field in IPsec AH. July 2008 IETF 72 - NSIS 11
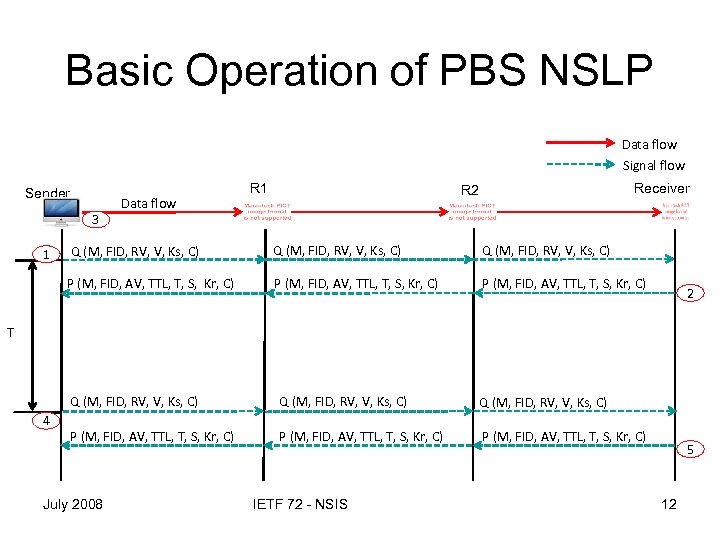
Basic Operation of PBS NSLP Data flow Signal flow Sender 3 Data flow R 1 Receiver R 2 Q (M, FID, RV, V, Ks, C) P (M, FID, AV, TTL, T, S, Kr, C) 1 P (M, FID, AV, TTL, T, S, Kr, C) 2 T Q (M, FID, RV, V, Ks, C) 4 Q (M, FID, RV, V, Ks, C) P (M, FID, AV, TTL, T, S, Kr, C) July 2008 IETF 72 - NSIS 5 12

Basic Operation of PDA Data flow A (Attacker spoofing S’s address) Attack flow (2 MB) R 1 Sender Data flow (1 MB) 3 4 Query 1 Permission (AV=10 MB) R 2 Query Permission (AV=10 MB) Signal flow R 3 Query Permission (AV=10 MB) Receiver Query 2 Permission (AV=10 MB) Detect attack (1 MB Vs 3 MB) T 5 Query (V=1 MB) Permission (S=10) July 2008 Query (V=1 MB) Permission (S=10) IETF 72 - NSIS Query (V=1 MB) Permission (S=10) Query (V=1 MB) 6 Permission (S=10) 13
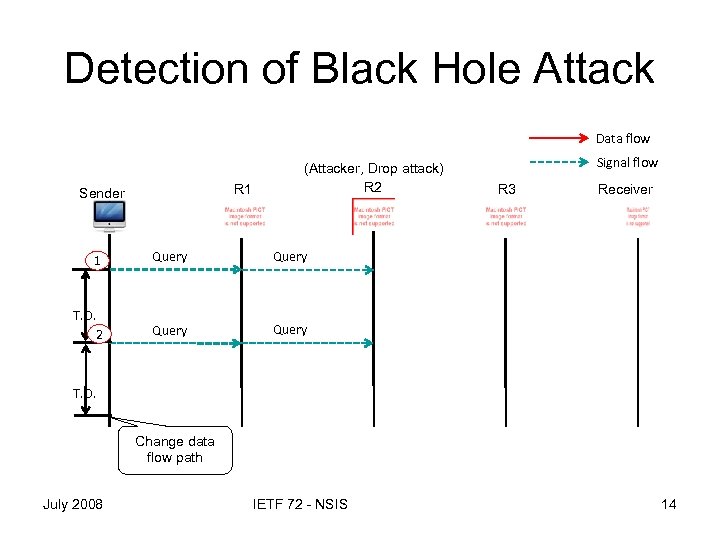
Detection of Black Hole Attack Data flow R 1 Sender (Attacker, Drop attack) R 2 1 Query R 3 Receiver Query T. O. 2 Signal flow Query T. O. Change data flow path July 2008 IETF 72 - NSIS 14

Detection of Dropping Only Data Packets Data flow Signal flow (Attacker, Drop attack) R 1 Sender Data flow (1 MB) 3 Query 1 Permission (AV=10 MB) Data flow (1 MB) R 3 R 2 Query Permission (AV=10 MB) T Receiver Query Permission (AV=10 MB) 2 Detect attack (1 MB Vs 0 MB) 4 Query (V=1 MB) Permission (S=11) July 2008 Query (V=1 MB) Permission (S=11) IETF 72 - NSIS Query (V=1 MB) Permission (S=11) 5 15
5d50c912b1f2e3c8cff743f1a9af0153.ppt