46daa538937220b6d4c1a0d26e373cbf.ppt
- Количество слайдов: 36

OWASP Europe Conference 2008 Graph Analysis for Web. Apps: From Nodes to Edges OWASP Simon Roses Femerling Security Technologist and Researcher Copyright © The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the OWASP License. The OWASP Foundation http: //www. owasp. org
Intro - Who I am < Natural from wonderful Mallorca Island in the Mediterranean Sea < Postgraduate in E-Commerce from Harvard University and a B. S. from Suffolk University at Boston, Massachusetts < Former Pw. C, @Stake among others… < Security Technologist (ACE Team) at Microsoft OWASP

Talk Objectives <Success Cases using graphs in security space <Not a class on graphs <Improve web assessments by 4 Saving time 4 Focus on what matters 4 Surgical Testing OWASP

Agenda <Overview <Process <Data Analysis <Summary <Q&A OWASP

OVERVIEW OWASP
Why? <Apps are more complex daily <Tired of using poor tool set <Move away from raw text <Need identify patterns quickly <Time is precious and usually you don’t have enough OWASP
Security Visualization <Becoming a popular field <Needs a lot of research <Makes easier to analyze data <We perform better with visual images that raw data OWASP
Success Cases Visualization <Reverse Engineering <IDS Log Analysis <Network Analysis <Source Code Review http: //secviz. org/ OWASP

OWASP
OWASP
OWASP

OWASP
PROCESS OWASP
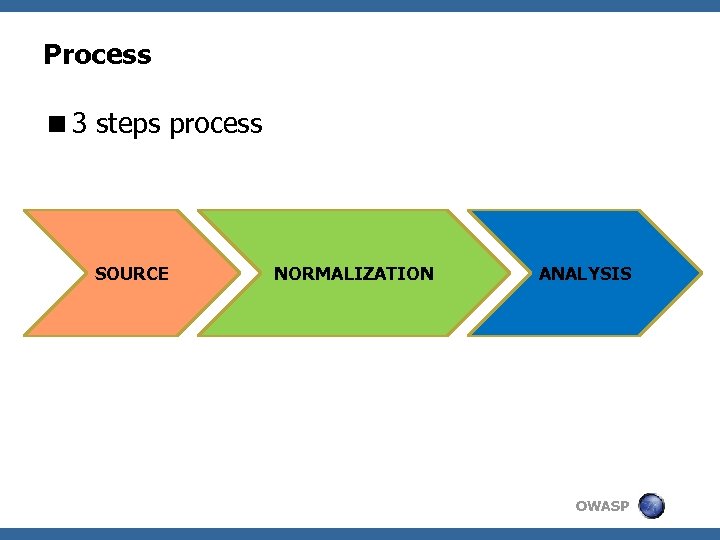
Process <3 steps process SOURCE NORMALIZATION ANALYSIS OWASP
SOURCE <Black box or White box independency <As much data we got the better (everything is important) <Lot of tools that can help us 4 Proxies 4 Crawlers 4 Scanners SOURCE OWASP

NORMALIZATION <Raw data normalized <XML for convenience <Normalize / Analysis Engine is key NORMALIZATION OWASP

ANALYSIS <Start identifying issues easier and faster <Visual approach <Take decisions and focus testing <Data Mining is the key ANALYSIS OWASP
DATA ANALYSIS OWASP
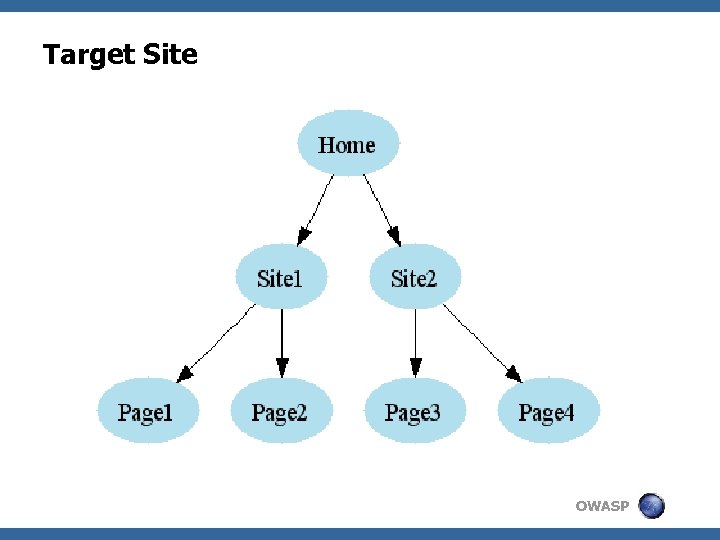
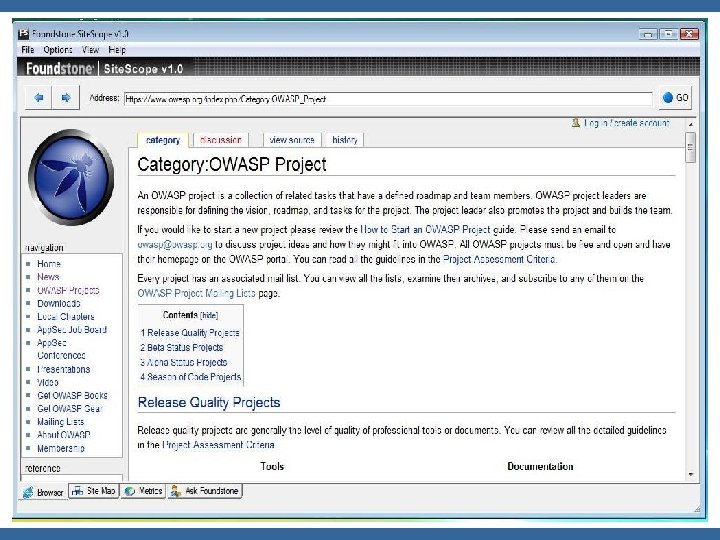
Target Site OWASP

Target Relationship <Query: Pages that link to Home <Objectives: 4 Learning about target 4 Mapping Application OWASP
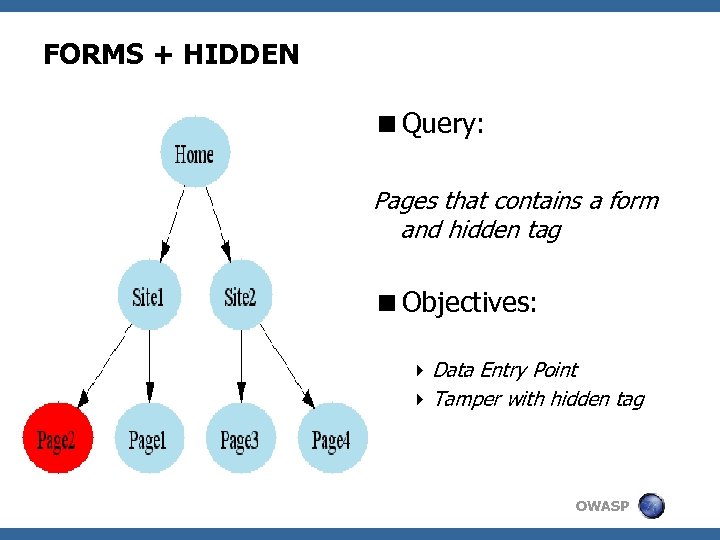
FORMS + HIDDEN <Query: Pages that contains a form and hidden tag <Objectives: 4 Data Entry Point 4 Tamper with hidden tag OWASP
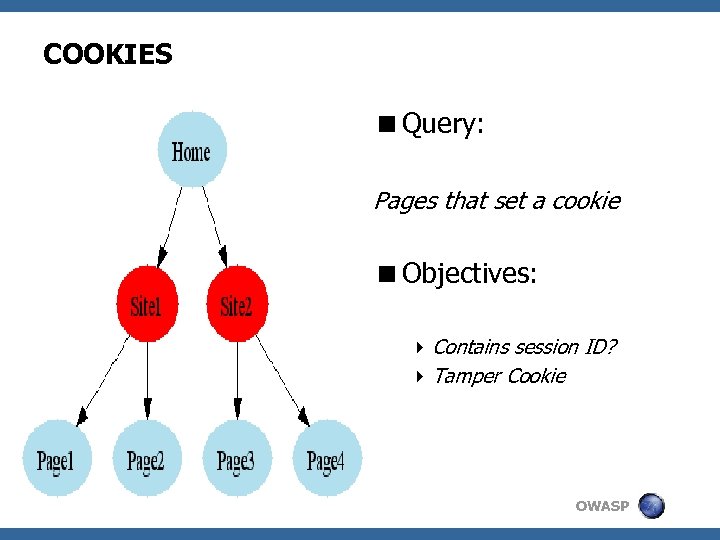
COOKIES <Query: Pages that set a cookie <Objectives: 4 Contains session ID? 4 Tamper Cookie OWASP

SSL <Query: Pages that uses SSL <Objectives: 4 Check SSL Certificate 4 Can I call pages without SSL? OWASP
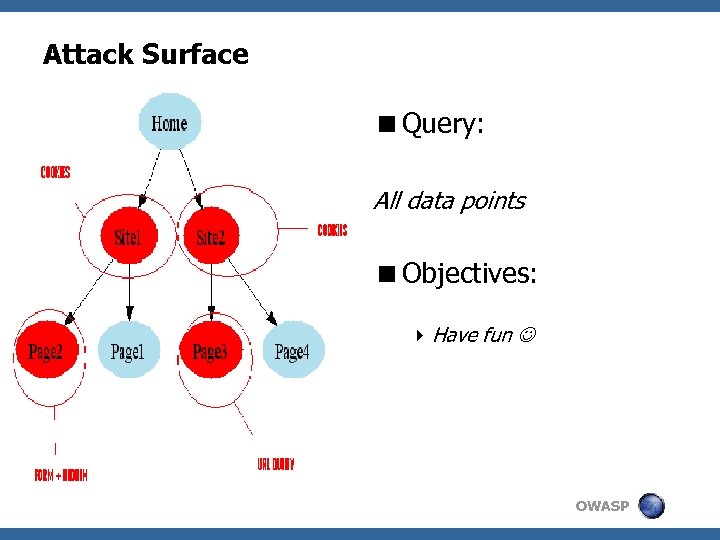
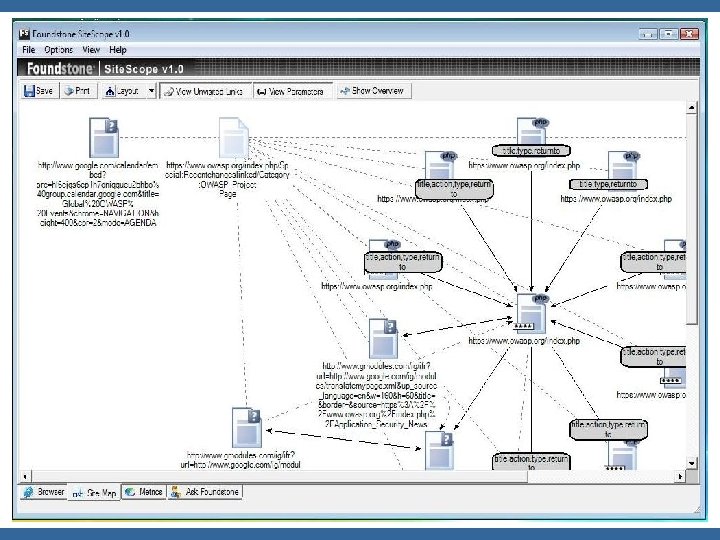
Attack Surface <Query: All data points <Objectives: 4 Have fun OWASP

Analysis tips < Diff between pages < What pages contain more data entries? < What pages contain more issues? < Identify pages with script code, comments, etc… < We are constrained to: 4 What we know from target 4 Our imagination OWASP
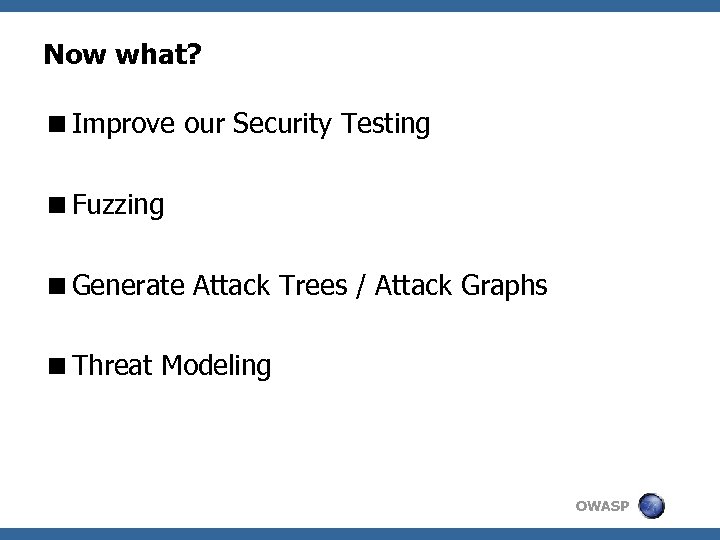
Now what? <Improve our Security Testing <Fuzzing <Generate Attack Trees / Attack Graphs <Threat Modeling OWASP

Web Attack Graphs OWASP
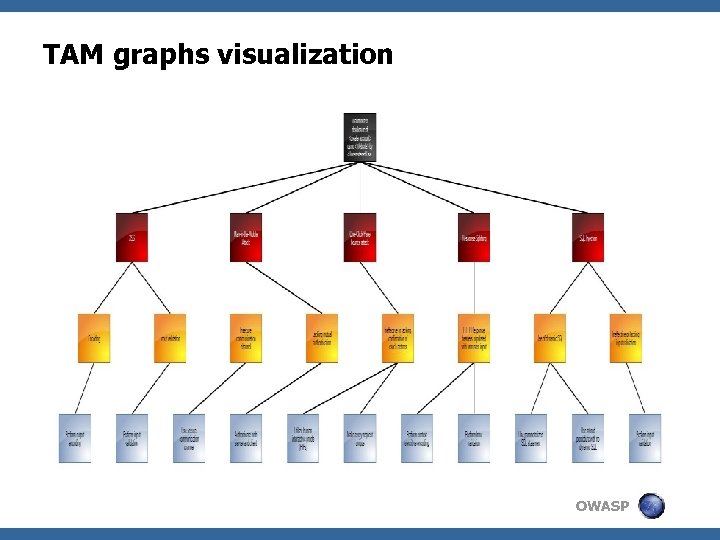
TAM graphs visualization OWASP

Data Analysis Goal Build a focus attack roadmap to test target OWASP
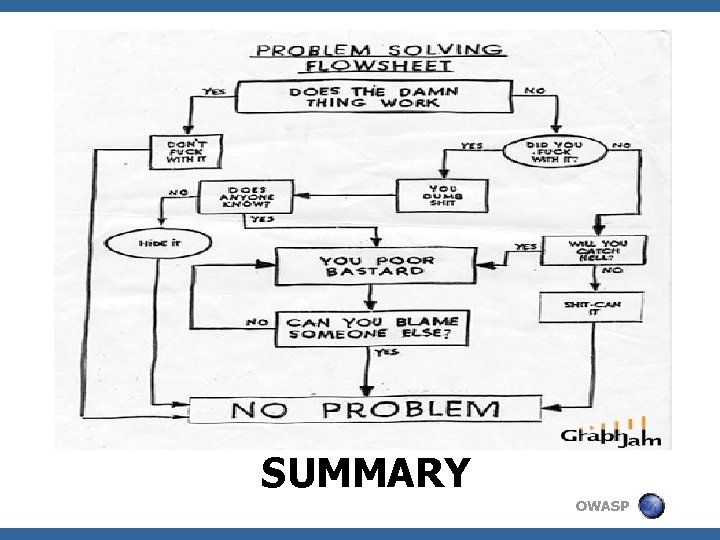
SUMMARY OWASP
Security Visualization Coolness <Makes our lives easier <Allows for easy pattern identification <Cuts down our analysis time <Focus security testing <Add cool visuals to report OWASP
Future <Adding graphs analysis into PANTERA <Some current research into web sec graphs <Build an automated process <Check out OWASP Tiger (http: //www. owasp. org/index. php/OWASP_Tiger) OWASP

Pantera Data Mining I OWASP

Pantera Data Mining II OWASP

Nice toolset to play with… < Python 4 Pydot (http: //code. google. com/p/pydot/) 4 p. GRAPH (included in PAIMEI) < Java 4 JUNG (http: //jung. sourceforge. net/) 4 JGraph. T (http: //www. jgrapht. org/) <. NET 4 Quick. Graph (http: //www. codeproject. com/KB/miscctrl/quickgraph. aspx) 4 MSAGL (http: //research. microsoft. com/research/msagl/) OWASP

The End <Q&A < Important: Beer / hard liquor (Vodka Lemon, Margaritas, Mojitos, you named it…) are always welcome < Simon Roses Femerling www. roseslabs. com OWASP
46daa538937220b6d4c1a0d26e373cbf.ppt