2a3e172d40ed48a7fb5f82dd63bfcc6e.ppt
- Количество слайдов: 40
Overview of Modern Web Architectures, Standards, Security, and Future Directions Oct/26/2009 Zhenhua Guo 1
Outline n n n Web App Case Study Modern Web Characteristics Modern Web Architecture : Open. Social q q q Architecture Components Security n n Background Authorization Out of Scope: Authentication Future Directions 2
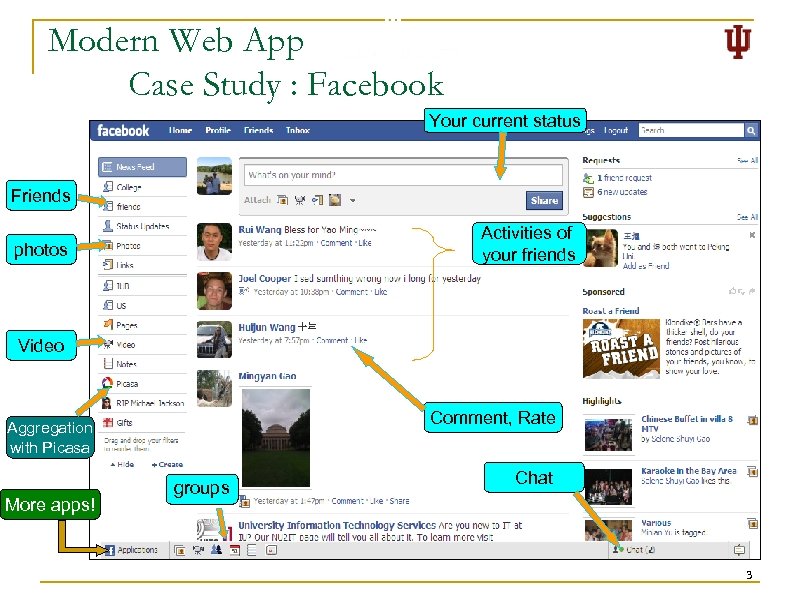
Modern Web App Case Study : Facebook Your current status n Friends photos Facebook q q More than 200 million active users Activities of MS paid $240 million foryour friends 1. 6 percent Video Comment, Rate Aggregation with Picasa More apps! groups Chat 3
Previous Web App Case Study : Yahoo! Directory Provider-defined directory 4
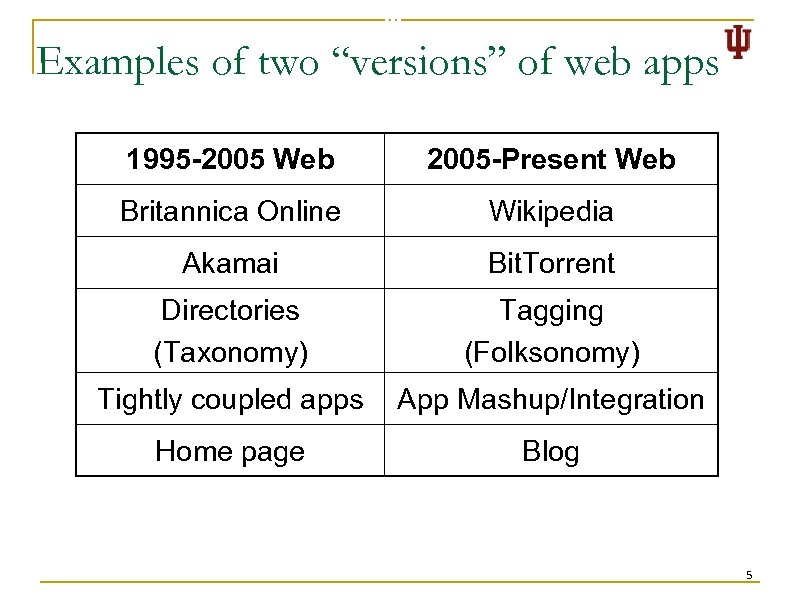
Examples of two “versions” of web apps 1995 -2005 Web 2005 -Present Web Britannica Online Wikipedia Akamai Bit. Torrent Directories (Taxonomy) Tagging (Folksonomy) Tightly coupled apps App Mashup/Integration Home page Blog 5
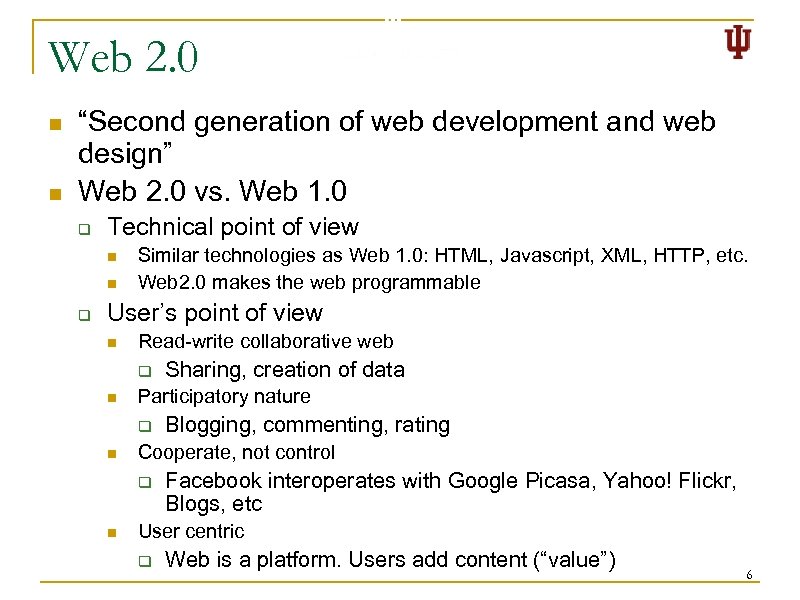
Web 2. 0 n n “Second generation of web development and web design” Web 2. 0 vs. Web 1. 0 q Technical point of view n n q Similar technologies as Web 1. 0: HTML, Javascript, XML, HTTP, etc. Web 2. 0 makes the web programmable User’s point of view n Read-write collaborative web q n Participatory nature q n Blogging, commenting, rating Cooperate, not control q n Sharing, creation of data Facebook interoperates with Google Picasa, Yahoo! Flickr, Blogs, etc User centric q Web is a platform. Users add content (“value”) 6
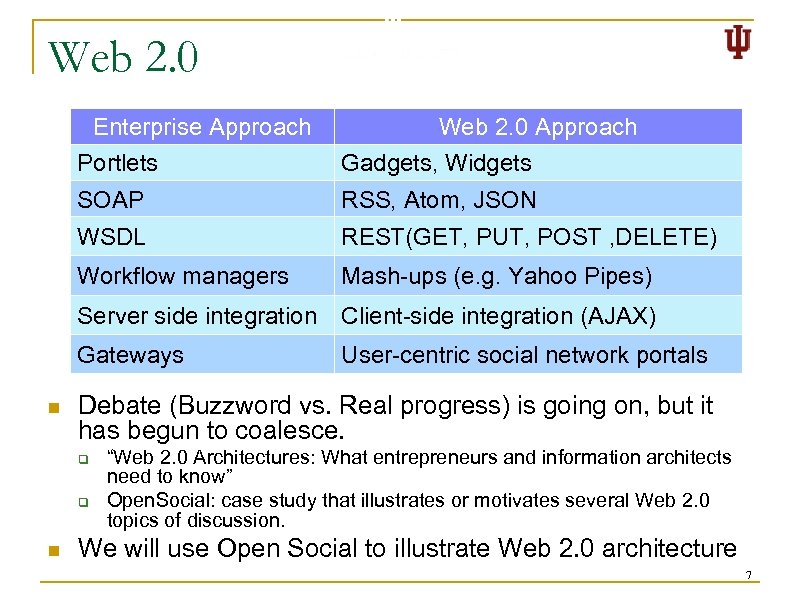
Web 2. 0 Enterprise Approach Web 2. 0 Approach Portlets SOAP RSS, Atom, JSON WSDL REST(GET, PUT, POST , DELETE) Workflow managers Mash-ups (e. g. Yahoo Pipes) Server side integration Client-side integration (AJAX) Gateways n Gadgets, Widgets User-centric social network portals Debate (Buzzword vs. Real progress) is going on, but it has begun to coalesce. q q n “Web 2. 0 Architectures: What entrepreneurs and information architects need to know” Open. Social: case study that illustrates or motivates several Web 2. 0 topics of discussion. We will use Open Social to illustrate Web 2. 0 architecture 7
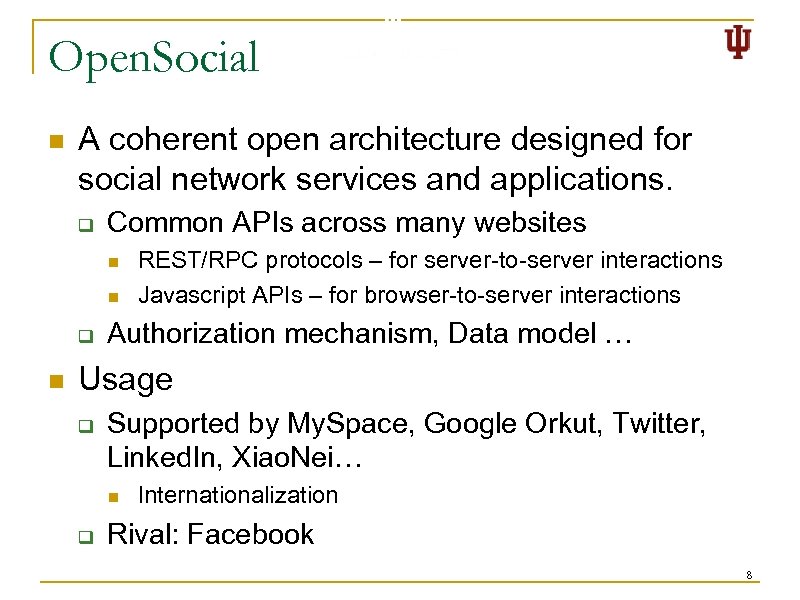
Open. Social n A coherent open architecture designed for social network services and applications. q Common APIs across many websites n n q n REST/RPC protocols – for server-to-server interactions Javascript APIs – for browser-to-server interactions Authorization mechanism, Data model … Usage q Supported by My. Space, Google Orkut, Twitter, Linked. In, Xiao. Nei… n q Internationalization Rival: Facebook 8
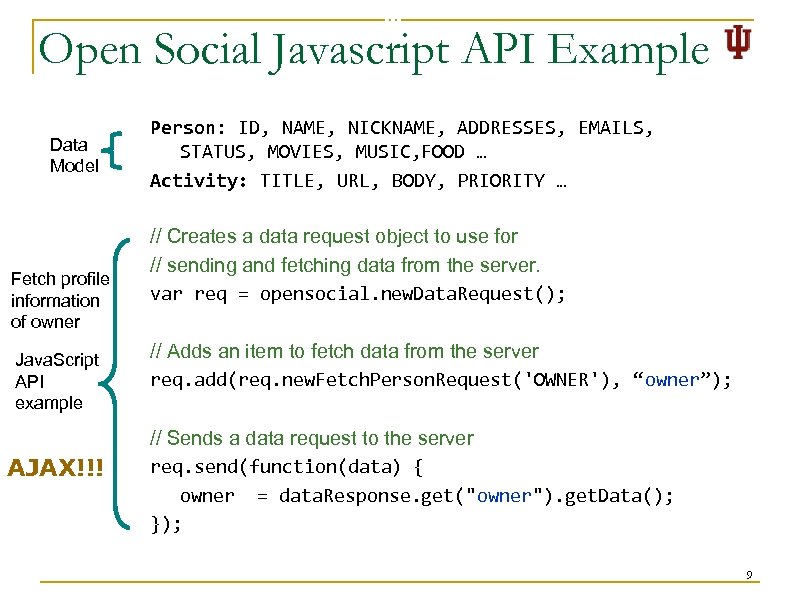
Open Social Javascript API Example Data Model Fetch profile information of owner Java. Script API example AJAX!!! Person: ID, NAME, NICKNAME, ADDRESSES, EMAILS, STATUS, MOVIES, MUSIC, FOOD … Activity: TITLE, URL, BODY, PRIORITY … // Creates a data request object to use for // sending and fetching data from the server. var req = opensocial. new. Data. Request(); // Adds an item to fetch data from the server req. add(req. new. Fetch. Person. Request('OWNER'), “owner”); // Sends a data request to the server req. send(function(data) { owner = data. Response. get("owner"). get. Data(); }); 9
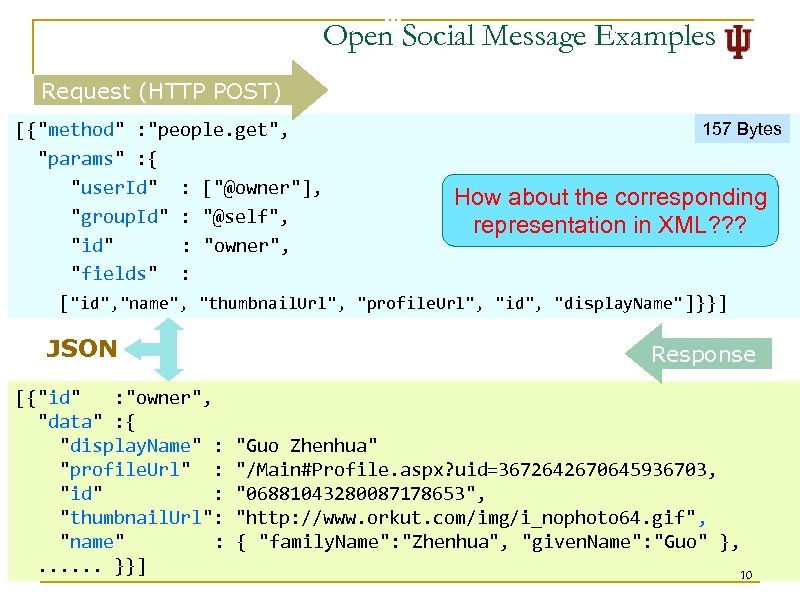
Open Social Message Examples Request (HTTP POST) 157 Bytes [{"method" : "people. get", "params" : { "user. Id" : ["@owner"], How about the corresponding "group. Id" : "@self", representation in XML? ? ? "id" : "owner", "fields" : ["id", "name", "thumbnail. Url", "profile. Url", "id", "display. Name" ]}}] JSON [{"id" : "owner", "data" : { "display. Name" : "profile. Url" : "id" : "thumbnail. Url": "name" : . . . }}] Response "Guo Zhenhua" "/Main#Profile. aspx? uid=3672642670645936703, "06881043280087178653", "http: //www. orkut. com/img/i_nophoto 64. gif", { "family. Name": "Zhenhua", "given. Name": "Guo" }, 10
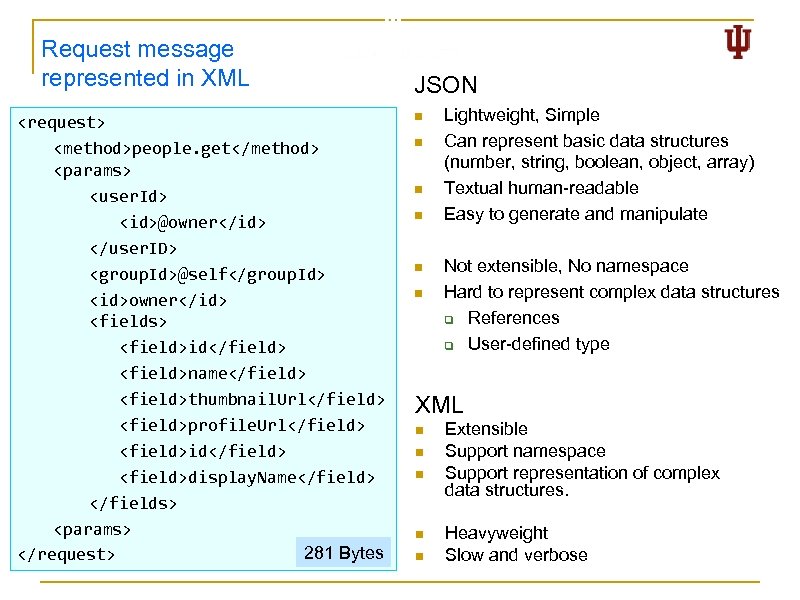
Request message represented in XML <request> <method>people. get</method> <params> <user. Id> <id>@owner</id> </user. ID> <group. Id>@self</group. Id> <id>owner</id> <fields> <field>id</field> <field>name</field> <field>thumbnail. Url</field> <field>profile. Url</field> <field>id</field> <field>display. Name</field> </fields> <params> 281 Bytes </request> JSON n n n Lightweight, Simple Can represent basic data structures (number, string, boolean, object, array) Textual human-readable Easy to generate and manipulate Not extensible, No namespace Hard to represent complex data structures q References q User-defined type XML n n n Extensible Support namespace Support representation of complex data structures. Heavyweight Slow and verbose
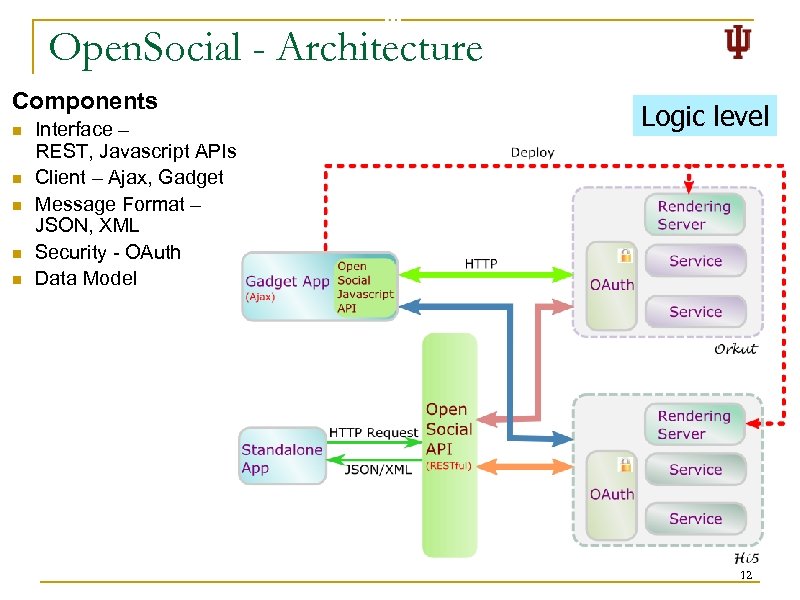
Open. Social - Architecture Components n n n Interface – REST, Javascript APIs Client – Ajax, Gadget Message Format – JSON, XML Security - OAuth Data Model Logic level 12
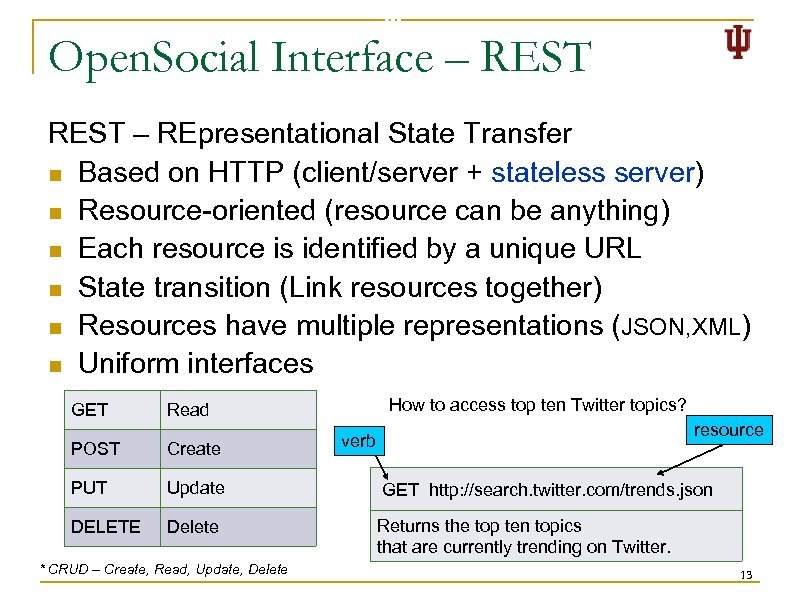
Open. Social Interface – REST – REpresentational State Transfer n Based on HTTP (client/server + stateless server) n Resource-oriented (resource can be anything) n Each resource is identified by a unique URL n State transition (Link resources together) n Resources have multiple representations (JSON, XML) n Uniform interfaces GET How to access top ten Twitter topics? Read resource verb POST Create PUT Update GET http: //search. twitter. com/trends. json DELETE Delete Returns the top ten topics that are currently trending on Twitter. * CRUD – Create, Read, Update, Delete 13
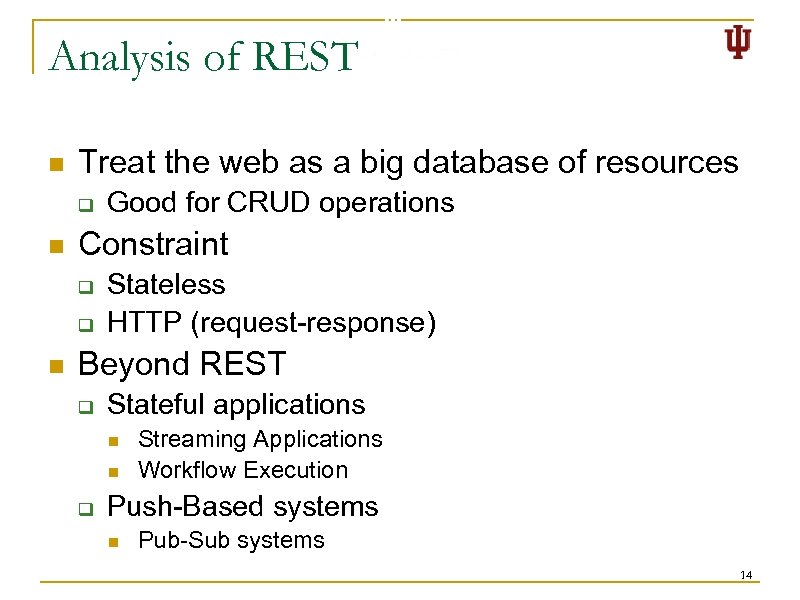
Analysis of REST n Treat the web as a big database of resources q n Constraint q q n Good for CRUD operations Stateless HTTP (request-response) Beyond REST q Stateful applications n n q Streaming Applications Workflow Execution Push-Based systems n Pub-Sub systems 14
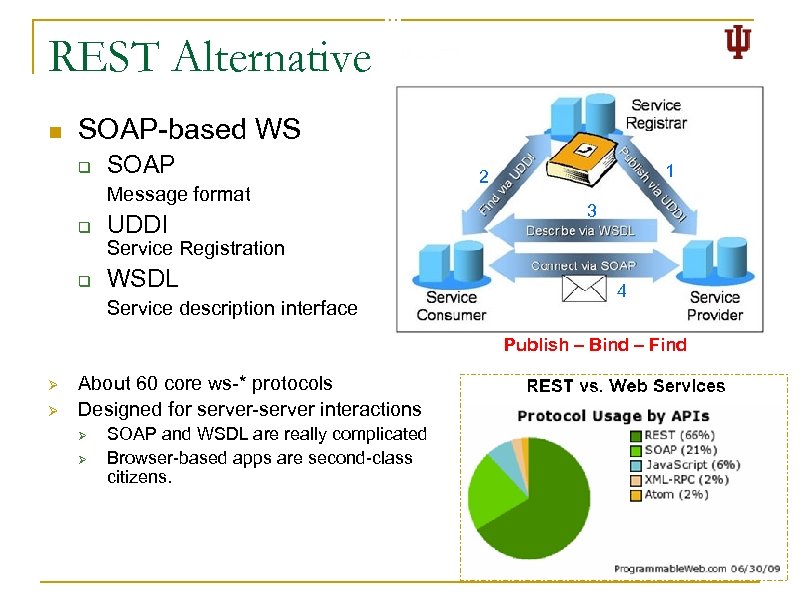
REST Alternative n SOAP-based WS q SOAP Message format q UDDI 1 2 3 Service Registration q WSDL Service description interface 4 Publish – Bind – Find Ø Ø About 60 core ws-* protocols Designed for server-server interactions Ø Ø SOAP and WSDL are really complicated Browser-based apps are second-class citizens. 15
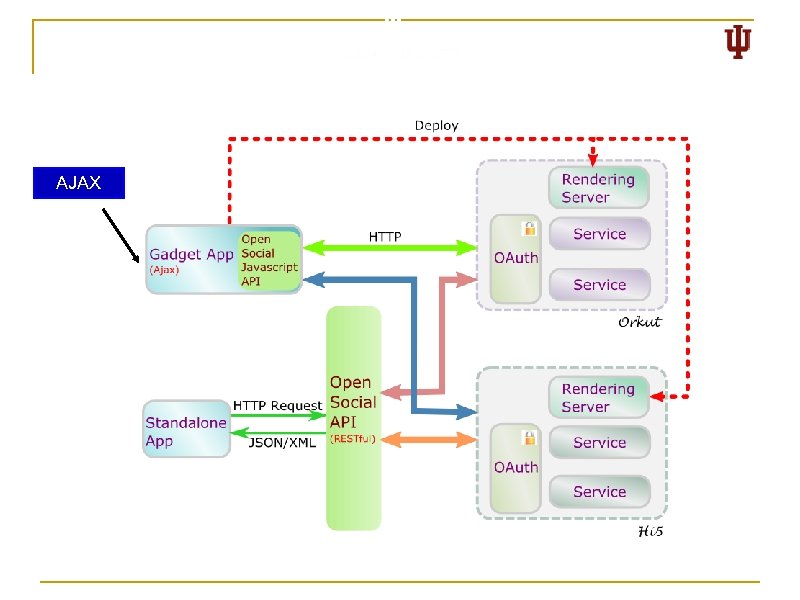
AJAX
Open. Social Client Tech – AJAX n Rationale Update sections without refreshing the whole page q More interactive q More responsive q Requires less bandwidth n Asynchronous Java. Script and XML q q q HTML + CSS Presentation DOM Document model (for dynamic manipulation) XMLHttp. Request Asynchronous Communication JSON/XML Data exchange format Javascript Bring these together 17
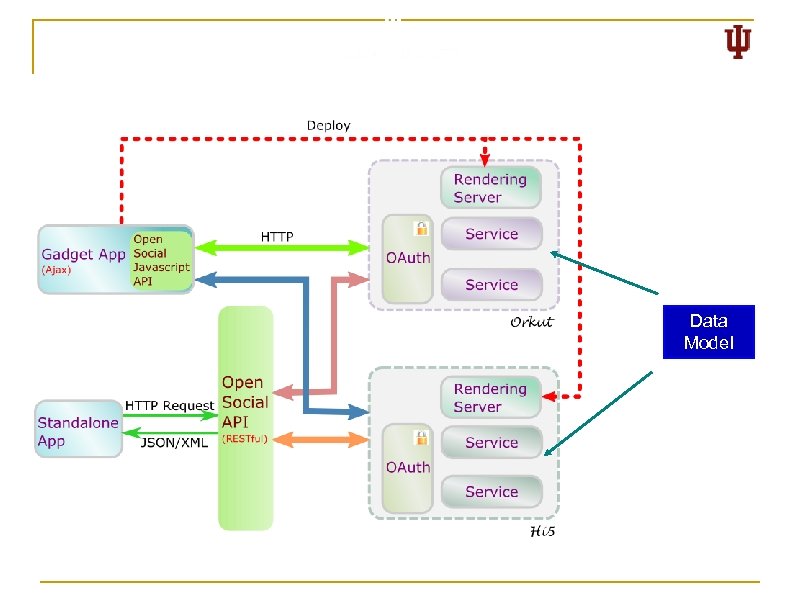
Data Model
Open. Social - Data Model n Define data models for basic objects in social network q q q n Relationships between objects can not be represented. q q n Person Activity App. Data Friend of a Friend (FOAF) – Based on W 3 C RDF XHTML Friends Network (XFN) Other possible issues q q Groups, roles, communities Strength of relationships Relationships in which more than two objects are involved Scalability (in terms of number of friends) 19
Security in Open. Social 20
Beyond Functionalities - Security n Identity q q n “On the internet, nobody knows you're a dog” Claimed Identity ≠ Real Identity Data protection q q Who can access your Facebook data? Increasing risk of identity theft and impersonation. n n Cartoon by Peter Steiner. The New Yorker, July 5, 1993 issue (Vol. 69 (LXIX) no. 20) page 61 Favorite color, mother’s maiden name, … “Friends” and applications have access to this “Predicting Social Security numbers from public data” Communication links Messages are passed by intermediary machines q Intermediaries understand your messages? q Intermediaries alter your messages? q Intermediaries forge your messages? 21
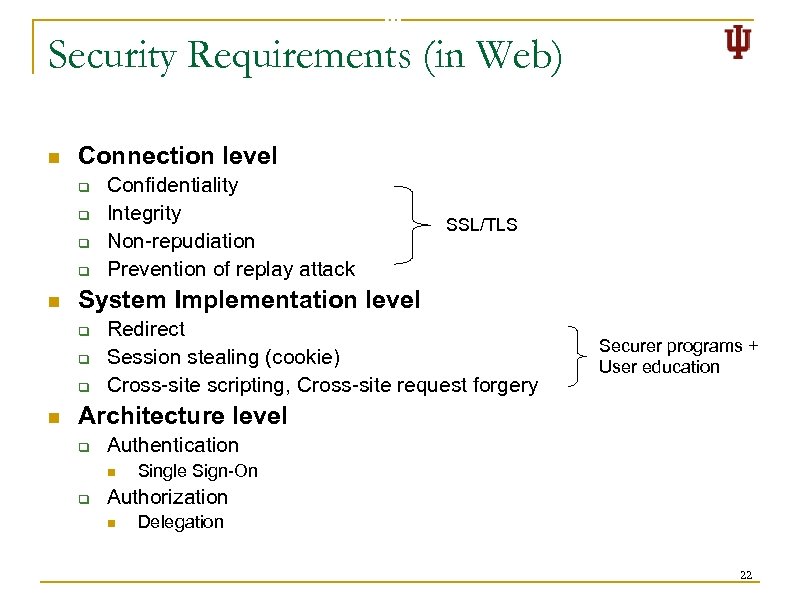
Security Requirements (in Web) n Connection level q q n SSL/TLS System Implementation level q q q n Confidentiality Integrity Non-repudiation Prevention of replay attack Redirect Session stealing (cookie) Cross-site scripting, Cross-site request forgery Securer programs + User education Architecture level q Authentication n q Single Sign-On Authorization n Delegation 22
Challenges n Technical Challenges q q n Loosely coupled components No single, isolated trusted base Domain-specific policies Separation of security policies and security mechanisms. Possible solutions q Authentication n q Central Authentication Service Cosign Open. ID Authorization n n Shibboleth OAuth 23
Open. Social Authorization – OAuth n Motivation q n Solution q q n Delegated authorization protocol Light-weight Explicit user consent Based on REST 3 rd-party App Twitter Drawbacks q q q n To allow third party apps to access users’ data stored at service provider without requiring username and password. Vulnerable to session fixation attack (http: //oauth. net/advisories/2009 -1) Delegation granularity (Service provider-specific) Access token expiration and revocation Resources q http: //oauth. net/ 24
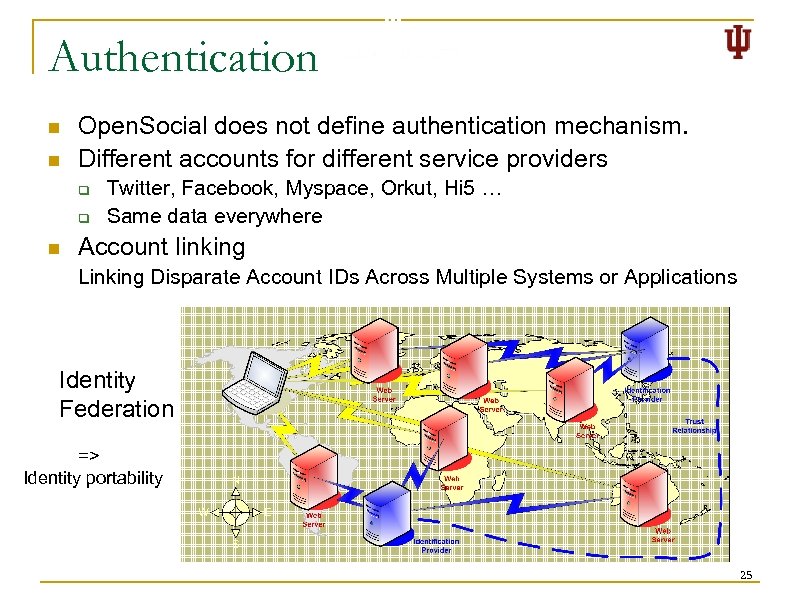
Authentication n n Open. Social does not define authentication mechanism. Different accounts for different service providers q q n Twitter, Facebook, Myspace, Orkut, Hi 5 … Same data everywhere Account linking Linking Disparate Account IDs Across Multiple Systems or Applications Identity Federation => Identity portability 25
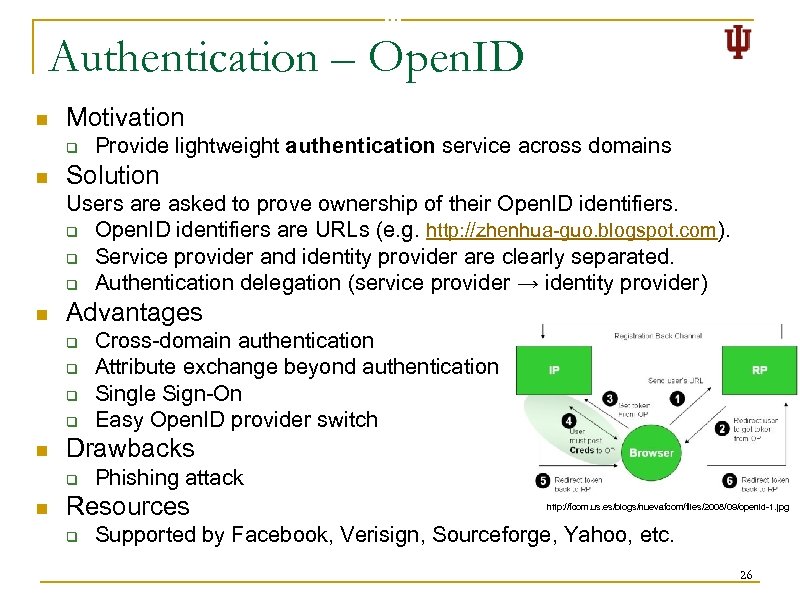
Authentication – Open. ID n Motivation q n Provide lightweight authentication service across domains Solution Users are asked to prove ownership of their Open. ID identifiers. q Open. ID identifiers are URLs (e. g. http: //zhenhua-guo. blogspot. com). q Service provider and identity provider are clearly separated. q Authentication delegation (service provider → identity provider) n Advantages q q n Drawbacks q n Cross-domain authentication Attribute exchange beyond authentication Single Sign-On Easy Open. ID provider switch Phishing attack Resources q http: //fcom. us. es/blogs/nuevafcom/files/2008/09/openid-1. jpg Supported by Facebook, Verisign, Sourceforge, Yahoo, etc. 26
OAuth and Open. ID n n Based on relaxed REST Use SSL/TLS to guarantee confidentiality, integrity and non-repudiation. Scalability Vulnerable to q q q Phishing Cross-site scripting Cross-site request forgery 27
Conclusions n n n Adoption of web 2. 0 Services, not packaged software Open Architecture and Open Standards q q q n n Interoperability Flexibility Integration Security Adoption in scientific communities q Traditional gateways n q LEAD, Earth System Grid Gateways that integrate web 2. 0 technologies n n n my. Experiment, Sci. Vee, Sakai Open Life Science Gateway Polar. Grid Portal
Research Opportunities n Social network in scientific communities q n Data Integration q q q n Manual integration Unified specification Adaptive integration Security model q n Collaboration and Cooperation Open, Flexible, Scalable, … Data Mining q Tag, Comment, Email, Blog, … 29
Future Directions n Semantic Web (Web 3. 0? ) q n Machine-readable representations of resources and relationships Artificial Intelligence, Data Mining q Search Engine n q Recommendation System n q Scaling Question Answering n q Information search Information retrieval Social Network Analysis n n Flow pattern recognition Strength of connections 30
My Research n Gadget Layout Management n OAuth implementation q q n Implement 2 -legged OAuth Integrate 3 -legged OAuth Polar. Grid Portal
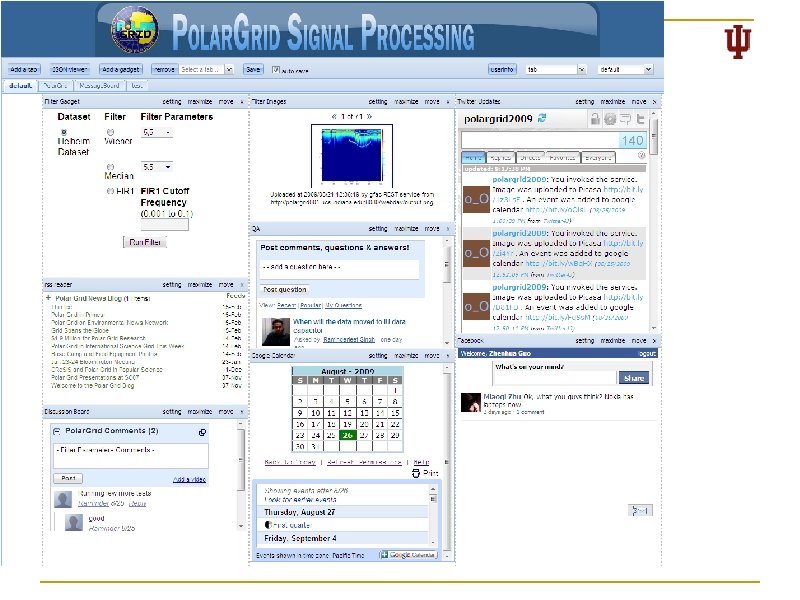
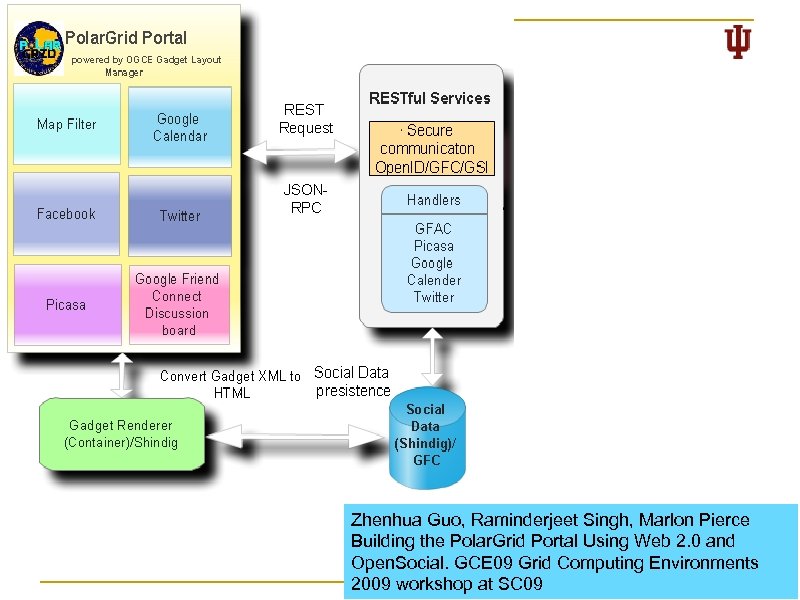
Zhenhua Guo, Raminderjeet Singh, Marlon Pierce Building the Polar. Grid Portal Using Web 2. 0 and Open. Social. GCE 09 Grid Computing Environments 33 2009 workshop at SC 09

Reference Papers n Distributed Systems q Hongbin Liu, Shrideep Pallickara, Geoffrey Fox. Performance of Web Services Security. Proceedings of the 13 th Mardi Gras Conference, 2005 q Satoshi Shirasuna, Aleksander Slominski, Liang Fang, Dennis Gannon. Performance comparison of security mechanisms for grid services. Proceedings of the Fifth IEEE/ACM International Workshop on Grid Computing, 2004 q Shrideep Pallickara, Marlon E. Pierce, Harshawardhan Gadgil, Geoffrey Fox, Yan, Yi Huang. A Framework for Secure End-to-End Delivery of Messages in Publish/Subscribe Systems. The 7 th IEEE/ACM International Conference on Grid Computing, 2006 q Cesare Pautasso, Olaf Zimmermann, and Frank Leymann. Restful web services vs. "big"' web services: making the right architectural decision. Proceeding of the 17 th international Conference on World Wide Web, 2008 q Michael zur Muehlen, Jeffrey V. Nickerson and Keith D. Swenson. Developing web services choreography standards—the case of REST vs. SOAP. http: //www. sciencedirect. com/science? _ob=Article. URL&_udi=B 6 V 8 S-4 CF 5 FWK 1&_user=10&_rdoc=1&_fmt=&_orig=search&_sort=d&_docanchor=&view=c&_search. Str. Id =1058155249&_rerun. Origin=scholar. google&_acct=C 000050221&_version=1&_url. Version =0&_userid=10&md 5=e 9 c 0 b 58 f 44 e 71 de 372 ea 92 e 94 b 34 f 385
Reference (cont. ) n Authentication q Clifford Neuman, Theodore Ts'o. Kerberos: An Authentication Service for Computer Networks. IEEE Communications, 1994 q John Kohl, B. Clifford Neuman, Theodore T'so. The Evolution of the Kerberos Authentication System. In Distributed Open Systems, pages 78 -94. IEEE Computer Society Press, 1994 q David Recordon , Drummond Reed. Open. ID 2. 0: a platform for user-centric identity management. Proceedings of the second ACM workshop on Digital identity management, 2006 q Drummond Reed, Les Chasen, William Tan. Open. ID identity discovery with XRI and XRDS. IDtrust, ACM International Conference Proceeding Series, Vol. 283, pp. 19 -25, ACM, 2008 35

Reference (cont. ) n Authorization q David Chadwick, Alexander Otenko. The PERMIS X. 509 role based privilege management infrastructure. Future Generation Computer Systems, 19(2), pp. 277 -289, 2003 q David Chadwick, Gansen Zhao, Sassa Otenko, Romain Laborde, Linying Su, Tuan-Anh Nguyen. PERMIS: a modular authorization infrastructure. Concurrency and Computation: Practice and Experience, 20(11), pp. 1341 -1357, 2008 q Von Welch, Frank Siebenlist, Ian Foster, John Bresnahan, Karl Czajkowski, Jarek Gawor, Carl Kesselman, Sam Meder, Laura Pearlman, Steven Tuecke. Security for Grid Services. Twelfth International Symposium on High Performance Distributed Computing, IEEE Press, 2003 q Ian Foster, Carl Kesselman, Gene Tsudik, Steven Tuecke. A Security Architecture for Computational Grids. ACM Conference on Computers and Security, pp. 83 -91, ACM Press, 1998 q Mary Thompson, William Johnston, Srilekha Mudumbai, Gary Hoo, Keith Jackson, Abdelilah Essiari. Certificate-based Access Control for Widely Distributed Resources. Proceedings of the 8 th USENIX Security Symposium (SECURITY-99), pp. 215 -228, Usenix Association, 1999 q Anirban Chakrabarti, Anish Damodaran, Subhasis Sengupta. Grid Computing Security: A Taxonomy. IEEE Security & Privacy, 6(1), pp. 44 -51, 2008 q Tom Barton, Jim Basney, Tim Freeman, Tom Scavo, Frank Siebenlist, Von Welch, Rachana Ananthakrishnan, Bill Baker, Monte Goode, Kate Keahey. Identity federation and attribute-based authorization through the globus toolkit, Shibboleth, Grid. Shib, and My. Proxy. 5 th Annual PKI R&D Workshop, 2006
Reference (cont. ) q q q q Ralf Groeper, Christian Grimm, Stefan Piger, Jan Wiebelitz. An Architecture for Authorization in Grids using Shibboleth and VOMS. Euromicro Conference-Software Engineering and Advanced Applications, pp. 367 -374, IEEE Computer Society, 2007 Von Welch, Tom Barton, Kate Keahey, Frank Siebenlist. Attributes, anonymity, and access -shibboleth and globus integration to facilitate grid collaboration. 4 th Annual PKI R&D Workshop, 2005 Laura Pearlman, Von Welch, Ian T. Foster, Carl Kesselman, Steven Tuecke. A Community Authorization Service for Group Collaboration. POLICY, pp. 50 -59, IEEE Computer Society, 2002 Roberto Alfieri, Roberto Cecchini, Vincenzo Ciaschini, Luca dell'Agnello, Ákos Frohner, Alberto Gianoli, Károly Lörentey, Fabio Spataro. VOMS, an Authorization System for Virtual Organizations. European Across Grids Conference, Lecture Notes in Computer Science, Vol. 2970, pp. 33 -40 Springer, 2003 Laura Pearlman, Von Welch, Ian T. Foster, Carl Kesselman, Steven Tuecke. A community authorization service for group collaboration. Proceedings of the 3 rd IEEE International Workshop on Policies, 2002 Laura Pearlman, Von Welch, Ian Foster, Carl Kesselman, Steven Tuecke. The community authorization service: Status and future. Proceedings of Computing in High Energy Physics, 2003
Reference (cont. ) q q q n Justin Binns, Jonathan Di. Carlo, Joseph Insley, Ti Leggett, Cory Lueninghoener, John-Paul Navarro, Michael Papka. Enabling community access to Tera. Grid visualization resources. Concurrency and Computation: Practice and Experience, 19(6), pp. 783 -794, 2007 Jim Basney, Marty Humphrey, Von Welch. The My. Proxy online credential repository. Software: Practice and Experience, 2005 Jason Novotny, Steven Tuecke, Von Welch. An online credential repository for the grid: My. Proxy. High Performance Distributed Computing, 2001. Proceedings. 10 th IEEE International Symposium Andreas Pashalidis, Chris Mitchell. A Taxonomy of Single Sign-On Systems. Information Security and Privacy: Australasian Conference, 2003 Thomas Groß. Security Analysis of the SAML Single Sign-on Browser/Artifact Profile. Annual Computer Security Applications Conference, pp. 298 -307, IEEE Computer Society, 2003 Minor (Artificial Intelligence) Related q Patrick Kelley, Paul Drielsma, Norman Sadeh, Lorrie Faith Cranor. User-controllable learning of security and privacy policies. Proceedings of the 1 st ACM workshop on Workshop on AISec, pp. 11 -18, ACM, 2008 q Guang Xiang, Ge Yu, Xiangli Qu, Xiaomei Dong, Lina Wang. A Hybrid Machine Learning/Statistical Model of Grid Security. Grid and Cooperative Computing, Lecture Notes in Computer Science, Vol. 3251, pp. 348 -355, Springer, 2004
Reference (cont. ) n Specifications q Shibboleth Architecture - Protocols and Profiles q Web Services Security: SOAP Message Security 1. 1 (WS-Security 2004) q Security Assertion Markup Language(SAML) V 2. 0 Technical Overview q Security and Privacy Considerations for the OASIS Security Assertion Markup Language(SAML) V 2. 0 q XML Encryption Syntax and Processing q An Internet Attribute Certificate Profile for Authorization (RFC 3281) q Technical Comparison: Open. ID and SAML - Draft 06 q Open. ID (http: //openid. net/developers/specs/) q OAuth 1. 0(http: //oauth. net/core/1. 0/) q Central Authentication Service (http: //www. jasig. org/cas/protocol)
Questions?
2a3e172d40ed48a7fb5f82dd63bfcc6e.ppt