42344d6da74b81f38c8d5bbd8f13de76.ppt
- Количество слайдов: 16
Organizing Nationally for Cybersecurity Southeast Europe Cybersecurity Conference Sofia, Bulgaria 8 -9 September 2003 Howard A. Schmidt Vice President, Chief of Security e. Bay Inc.
Exploiting vulnerabilities is not new… Network Security Incident – c. 1986 n In 1986, the first well-publicized international security incident was identified by Cliff Stoll, then of Lawrence Berkeley National Laboratory in northern California. A simple accounting error in the computer records of systems connected to the ARPANET led Stoll to uncover an international effort, using the network, to connect to computers in the United States and copy information from them. These U. S. computers were not only at universities, but at military and government sites all over the country. When Stoll published his experience in a 1989 book, The Cuckoo's Egg, he raised awareness that the ARPANET could be used for destructive purposes. Source: CERT/CC
Worms are not new either… Malicious Code Attack – c. 1988 n n In 1988, the ARPANET had its first automated network security incident, usually referred to as "the Morris worm“. A student at Cornell University (Ithaca, NY), Robert T. Morris, wrote a program that would connect to another computer, find and use one of several vulnerabilities to copy itself to that second computer, and begin to run the copy of itself at the new location. The worm used so many system resources that the attacked computers could no longer function. As a result, 10% of the U. S. computers connected to the ARPANET effectively stopped at about the same time. By that time, the ARPANET had grown to more than 88, 000 computers and was the primary means of communication among network security experts. With the ARPANET effectively down, it was difficult to coordinate a response to the worm. Many sites removed themselves from the ARPANET altogether, further hampering communication and the transmission of the solution that would stop the worm. Source: CERT/CC
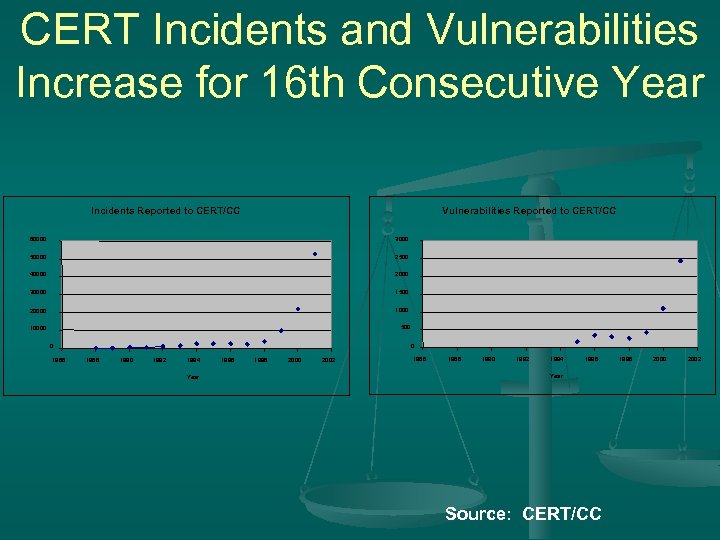
CERT Incidents and Vulnerabilities Increase for 16 th Consecutive Year Incidents Reported to CERT/CC Vulnerabilities Reported to CERT/CC 60000 3000 50000 2500 40000 2000 30000 1500 20000 1000 500 10000 0 1986 0 1988 1990 1992 1994 Year 1996 1998 2000 2002 1986 1988 1990 1992 1994 1996 Year Source: CERT/CC 1998 2000 2002
Steps to Organize Nationally n n Need to look at this as National challenge n Inter-connectivity required to look at this from a “system” approach US President established President’s Commission for Critical Information Protection (1996) “PCCIP” n Members include industry, defense, law enforcement, academia and other government agencies.
Steps to Organize Nationally n n PCCIP report established vast majority of Critical Information Infrastructure owned and operated by private industry. n Approx. 85% Interdependencies existed across 8 major sectors. n Banking & Finance, ICT, Transportation, Gas & Oil, Electricity, Public Safety, Water, Rail Transportation
Steps to Organize Nationally n n n Discovered no one group had a complete over view of interdependencies and cascading effects. May 1998, President signed Presidential Decision Directive 63 (PDD 63) Key Points Need better understanding of interdependencies n Need Information Sharing Analysis Centers (ISACS) n Need better Private-Public partnerships with ALL levels of government n
Steps to Organize Nationally 1 st Information Sharing Analysis Center (Banking & Finance) (1999) n 2 nd ICT (Feb 2001) n Plan for President’s Critical Infrastructure Protection Board n n Proposed April 2001 n Executive Order by President Bush Oct 2001 n Special Advisor for Cyber. Space Security
Steps to Organize Nationally November 2001, President directed the creation of a National Strategy to Defend Cyberspace n Public “Town Hall” meetings n Draft released for public comment September 18 th, 2002 n Final Released Feb 14 th, 2003 n
Steps to Organize Nationally n n n Prevent cyber attacks against our critical infrastructures; Reduce our national vulnerabilities to cyber attack; and Minimize the damage and recovery time from cyber attacks that do occur.
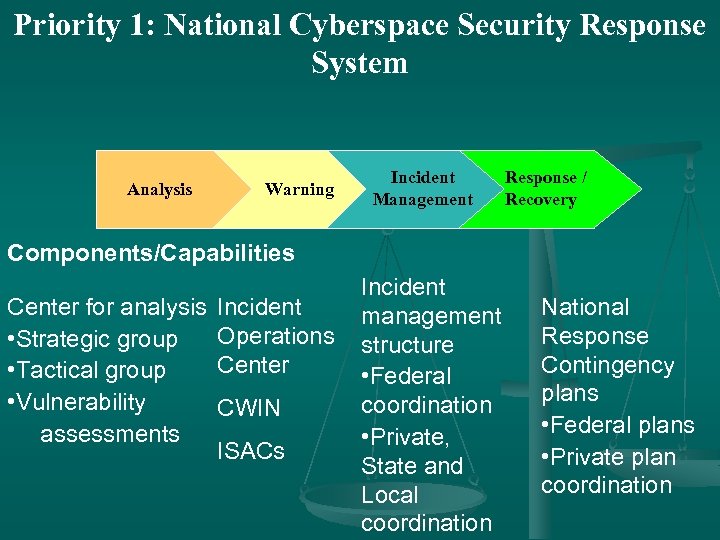
Priority 1: National Cyberspace Security Response System Analysis Warning Incident Management Response / Recovery Components/Capabilities Center for analysis • Strategic group • Tactical group • Vulnerability assessments Incident Operations Center CWIN ISACs Incident management structure • Federal coordination • Private, State and Local coordination National Response Contingency plans • Federal plans • Private plan coordination
Priority 2: Threat and Vulnerability Reduction n Enhance law enforcement’s capabilities; n Pursue national vulnerability assessments; n Secure the mechanisms of the Internet; n Foster trusted DCS/SCADA; n n n Reduce and remediate software vulnerabilities; Understand interdependencies Improve physical security of cyber & telecom; n Prioritize Federal cybersecurity R&D n Assess and secure emerging systems.
Priority 3: Awareness & Training n Promote a national awareness program to empower all users to secure their parts of cyberspace; n Ensure adequate training and education programs exist to support the nation’s cybersecurity needs; n Increase the efficiency of existing Federal cybersecurity training programs; and n Advance private sector support for a well coordinated, widely recognized professional cybersecurity certification.
Priority 4: Securing Government’s Cyberspace n Continuously assess threats and vulnerabilities to Federal cyber systems; n Authenticate and maintain authorization for users of Federal cyber systems; n Secure Federal wireless local area networks; n Improve security in Government outsourcing and procurement; n Establish an Office of Information Security Support Services; and n Encourage State and local governments to consider establishing IT security programs and participating in ISACS with similar governments.
Priority 5: International Cooperation n Strengthen counterintelligence efforts; n Improve attack attribution capabilities; n Improve coordination for responding to cyber attacks; n Work through international organizations and w/ industry to promote a global “culture of security; ” n Foster the establishment of national & international watch-and-warning networks; and n Encourage other nations to accede to the COE Convention on Cybercrime.
Thank You Howard A. Schmidt howard@cyber-security. us 408 -376 -6282
42344d6da74b81f38c8d5bbd8f13de76.ppt