Information_Security.pptx
- Количество слайдов: 16
 Organizational measures for the protection of information. Organization of information security of company.
Organizational measures for the protection of information. Organization of information security of company.
 Information security systems is a set of organizational and technical measures to ensure information security. The main object of protection is the data that is processed in the automated control system (ACS), and are involved in the performance of business processes.
Information security systems is a set of organizational and technical measures to ensure information security. The main object of protection is the data that is processed in the automated control system (ACS), and are involved in the performance of business processes.
 The process of creating information protection system can be divided into three stages: § Formation of the enterprise policy in the field of information security; § Selection and implementation of hardware and software protection; § Development and conducting of a number of organizational measures.
The process of creating information protection system can be divided into three stages: § Formation of the enterprise policy in the field of information security; § Selection and implementation of hardware and software protection; § Development and conducting of a number of organizational measures.
 How to build a security system, what methods and means can be used at the same time? § Identification, authentication and authorization of the subjects; § Control access to system resources; § Registration and analysis of events occurring in the system; § Integrity monitoring of system resources.
How to build a security system, what methods and means can be used at the same time? § Identification, authentication and authorization of the subjects; § Control access to system resources; § Registration and analysis of events occurring in the system; § Integrity monitoring of system resources.
 Basic organizational and administrative and technical measures on creation and maintenance the functioning of complex system of protection § One - time event - once conducted and repeated only if the full review of the decision; § Events held at realization or the occurrence of certain changes in the most protected system or the external environment; § Periodically carried event; § Permanently (continuously or discontinuously at random times) carried event.
Basic organizational and administrative and technical measures on creation and maintenance the functioning of complex system of protection § One - time event - once conducted and repeated only if the full review of the decision; § Events held at realization or the occurrence of certain changes in the most protected system or the external environment; § Periodically carried event; § Permanently (continuously or discontinuously at random times) carried event.
 One – time event § System-wide measures for the establishment of scientific, technical and methodological bases of protection the AU; § Activities implemented in the design, construction and equipment of computer centers § Activities implemented in the design, development and commissioning of hardware and software § The development and approval of functional responsibilities of officers service computer security; § · Measures to establish a system of protection the AS and infrastructure;
One – time event § System-wide measures for the establishment of scientific, technical and methodological bases of protection the AU; § Activities implemented in the design, construction and equipment of computer centers § Activities implemented in the design, development and commissioning of hardware and software § The development and approval of functional responsibilities of officers service computer security; § · Measures to establish a system of protection the AS and infrastructure;
 Periodic events § Distribution of requisites of access control (passwords, encryption keys, etc. ); § Analysis of system logs, the adoption of measures to detect violations of the rules of work; § Measures to revise the structure and construction of the system of protection § Implementation of analysis of state and performance evaluation of measures and applied means of protection.
Periodic events § Distribution of requisites of access control (passwords, encryption keys, etc. ); § Analysis of system logs, the adoption of measures to detect violations of the rules of work; § Measures to revise the structure and construction of the system of protection § Implementation of analysis of state and performance evaluation of measures and applied means of protection.
 Permanent event § Measures to ensure a sufficient level of physical protection (fire protection, protection of premises, access control, ensuring the safety and physical integrity of MCA, media, etc. ) § Measures for continuous supporting the functioning and management of used means of protection; § Explicit and hidden control over the work of the staff; § Constantly and periodically performs analysis and evaluation of state and effectiveness of the measures applied remedies.
Permanent event § Measures to ensure a sufficient level of physical protection (fire protection, protection of premises, access control, ensuring the safety and physical integrity of MCA, media, etc. ) § Measures for continuous supporting the functioning and management of used means of protection; § Explicit and hidden control over the work of the staff; § Constantly and periodically performs analysis and evaluation of state and effectiveness of the measures applied remedies.
 All the security measures of computer systems of the Company are divided on: § § § Legal (legislative); Moral and ethical; Organizational (administrative); Physical; Technical (instrumental and software).
All the security measures of computer systems of the Company are divided on: § § § Legal (legislative); Moral and ethical; Organizational (administrative); Physical; Technical (instrumental and software).
 Internal organization Axiom: A structured management framework directs, monitors and controls the implementation of information security as a whole within
Internal organization Axiom: A structured management framework directs, monitors and controls the implementation of information security as a whole within
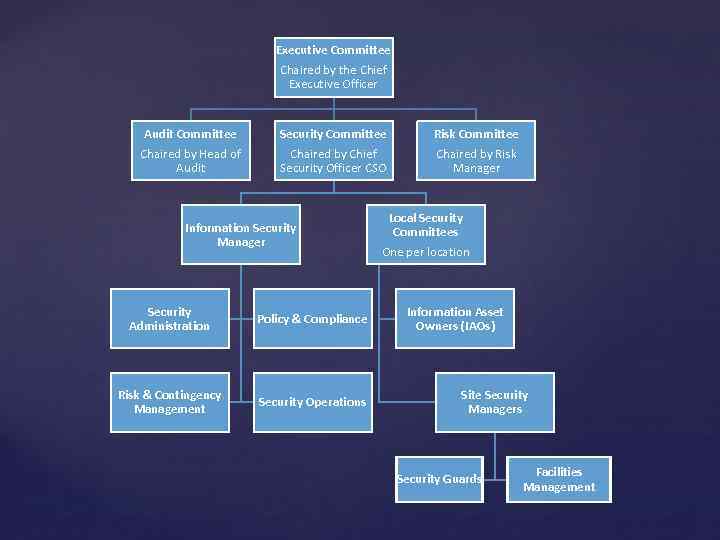 Executive Committee Chaired by the Chief Executive Officer Audit Committee Chaired by Head of Audit Security Committee Chaired by Chief Security Officer CSO Information Security Manager Security Administration Policy & Compliance Risk & Contingency Management Security Operations Risk Committee Chaired by Risk Manager Local Security Committees One per location Information Asset Owners (IAOs) Site Security Managers Security Guards Facilities Management
Executive Committee Chaired by the Chief Executive Officer Audit Committee Chaired by Head of Audit Security Committee Chaired by Chief Security Officer CSO Information Security Manager Security Administration Policy & Compliance Risk & Contingency Management Security Operations Risk Committee Chaired by Risk Manager Local Security Committees One per location Information Asset Owners (IAOs) Site Security Managers Security Guards Facilities Management
 Management commitment to information security § The Board of Directors is ultimately accountable for corporate governance as a whole. The management and control of information security risks is an integral part of corporate governance. In practice, however, the Board explicitly delegates executive responsibilities for most governance matters to the Executive Directors, led by the Chief Executive Officer (CEO). § The Executive Directors give overall strategic direction by approving and mandating the information security principles and axioms but delegate operational responsibilities for physical and information security to the Security Committee (SC) chaired by the Chief Security Officer (CSO).
Management commitment to information security § The Board of Directors is ultimately accountable for corporate governance as a whole. The management and control of information security risks is an integral part of corporate governance. In practice, however, the Board explicitly delegates executive responsibilities for most governance matters to the Executive Directors, led by the Chief Executive Officer (CEO). § The Executive Directors give overall strategic direction by approving and mandating the information security principles and axioms but delegate operational responsibilities for physical and information security to the Security Committee (SC) chaired by the Chief Security Officer (CSO).
 The Executive Directors demonstrate their commitment to information security by: § A statement of support from the Chief Executive Officer (CEO); § Reviewing and re-approving the principles and axioms every year; § Approving the IT budget including a specific element set aside for information security; § Receiving and acting appropriately on management reports concerning information security performance metrics, security incidents, investment requests etc.
The Executive Directors demonstrate their commitment to information security by: § A statement of support from the Chief Executive Officer (CEO); § Reviewing and re-approving the principles and axioms every year; § Approving the IT budget including a specific element set aside for information security; § Receiving and acting appropriately on management reports concerning information security performance metrics, security incidents, investment requests etc.
 The Chief Security Officer (CSO) is responsible for: § Chairing the Security Committee; § Taking the lead on information governance as a whole for example by issuing the policy manual and by providing the overall strategic direction, support and review necessary to ensure that information assets are identified and suitably protected throughout
The Chief Security Officer (CSO) is responsible for: § Chairing the Security Committee; § Taking the lead on information governance as a whole for example by issuing the policy manual and by providing the overall strategic direction, support and review necessary to ensure that information assets are identified and suitably protected throughout
 The ISM and Information Security Management are responsible for: § Defining technical and non-technical information security standards, procedures and guidelines; § Supporting IAOs and managers in the definition and implementation of controls, processes and supporting tools to comply with the policy manual and manage information security risks; § Reviewing and monitoring compliance with the policy statements and contributing to Internal Audit and Control Self Assessment (CSA) processes; § Collecting, analyzing and commenting on information security metrics and incidents; § Supporting IAOs in the investigation and remediation of information security incidents or other policy violations; § Liaising as necessary with related internal functions such as IT Operations, Risk Management, Compliance and Internal Audit, as well as the CSO, LSCs, SC and external functions such as the Police when appropriate; § Organizing a security awareness campaign for personnel to enhance the security culture and develop a broad understanding of the requirements of ISO/IEC 27002.
The ISM and Information Security Management are responsible for: § Defining technical and non-technical information security standards, procedures and guidelines; § Supporting IAOs and managers in the definition and implementation of controls, processes and supporting tools to comply with the policy manual and manage information security risks; § Reviewing and monitoring compliance with the policy statements and contributing to Internal Audit and Control Self Assessment (CSA) processes; § Collecting, analyzing and commenting on information security metrics and incidents; § Supporting IAOs in the investigation and remediation of information security incidents or other policy violations; § Liaising as necessary with related internal functions such as IT Operations, Risk Management, Compliance and Internal Audit, as well as the CSO, LSCs, SC and external functions such as the Police when appropriate; § Organizing a security awareness campaign for personnel to enhance the security culture and develop a broad understanding of the requirements of ISO/IEC 27002.
 Information Asset Owners (IAOs) are managers held accountable for the protection of particular Significant Information Assets by their LSC or the SC. IAOs may delegate information security tasks to managers or other individuals but remain accountable for proper implementation of the tasks. IAOs are responsible for: § Appropriate classification and protection of the information assets; § Specifying and funding suitable protective controls; § Authorizing access to information assets in accordance with the classification and business needs; § Undertaking or commissioning information security risk assessments to ensure that the information security requirements are properly defined and documented during the early stages of development; § Ensuring timely completion of regular system/data access reviews; and § Monitoring compliance with protection requirements affecting their assets.
Information Asset Owners (IAOs) are managers held accountable for the protection of particular Significant Information Assets by their LSC or the SC. IAOs may delegate information security tasks to managers or other individuals but remain accountable for proper implementation of the tasks. IAOs are responsible for: § Appropriate classification and protection of the information assets; § Specifying and funding suitable protective controls; § Authorizing access to information assets in accordance with the classification and business needs; § Undertaking or commissioning information security risk assessments to ensure that the information security requirements are properly defined and documented during the early stages of development; § Ensuring timely completion of regular system/data access reviews; and § Monitoring compliance with protection requirements affecting their assets.


