2de384c6cf2d0f30ab688a39c79ee987.ppt
- Количество слайдов: 24
 Open. VPN hardening Motto: When you want to protect something, you need to learn how to break it before … This is not about all possible options, but mainly about proper encryption settings. Jan Dusatko
Open. VPN hardening Motto: When you want to protect something, you need to learn how to break it before … This is not about all possible options, but mainly about proper encryption settings. Jan Dusatko
 Let’s start …
Let’s start …
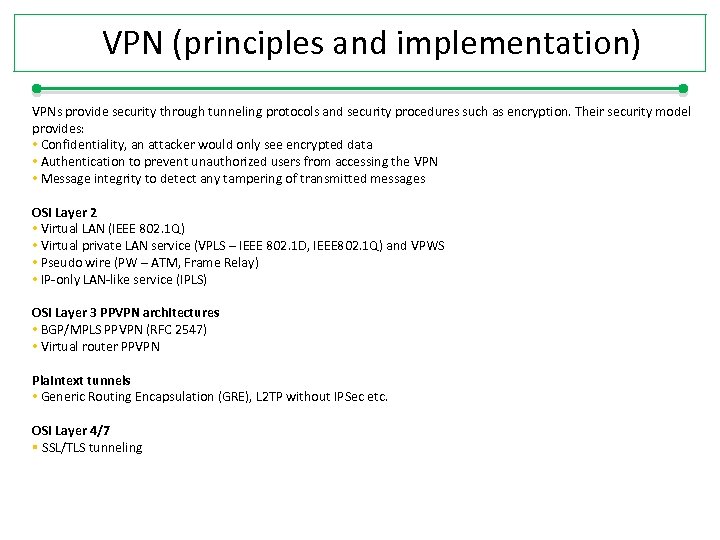 VPN (principles and implementation) VPNs provide security through tunneling protocols and security procedures such as encryption. Their security model provides: • Confidentiality, an attacker would only see encrypted data • Authentication to prevent unauthorized users from accessing the VPN • Message integrity to detect any tampering of transmitted messages OSI Layer 2 • Virtual LAN (IEEE 802. 1 Q) • Virtual private LAN service (VPLS – IEEE 802. 1 D, IEEE 802. 1 Q) and VPWS • Pseudo wire (PW – ATM, Frame Relay) • IP-only LAN-like service (IPLS) OSI Layer 3 PPVPN architectures • BGP/MPLS PPVPN (RFC 2547) • Virtual router PPVPN Plaintext tunnels • Generic Routing Encapsulation (GRE), L 2 TP without IPSec etc. OSI Layer 4/7 § SSL/TLS tunneling
VPN (principles and implementation) VPNs provide security through tunneling protocols and security procedures such as encryption. Their security model provides: • Confidentiality, an attacker would only see encrypted data • Authentication to prevent unauthorized users from accessing the VPN • Message integrity to detect any tampering of transmitted messages OSI Layer 2 • Virtual LAN (IEEE 802. 1 Q) • Virtual private LAN service (VPLS – IEEE 802. 1 D, IEEE 802. 1 Q) and VPWS • Pseudo wire (PW – ATM, Frame Relay) • IP-only LAN-like service (IPLS) OSI Layer 3 PPVPN architectures • BGP/MPLS PPVPN (RFC 2547) • Virtual router PPVPN Plaintext tunnels • Generic Routing Encapsulation (GRE), L 2 TP without IPSec etc. OSI Layer 4/7 § SSL/TLS tunneling
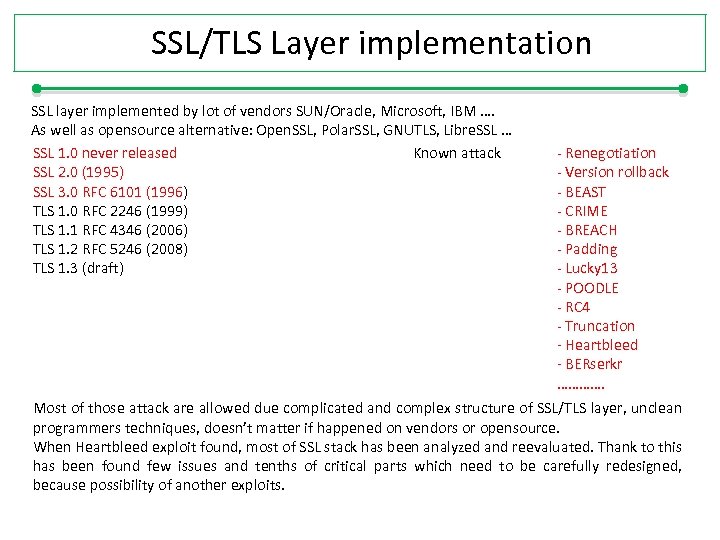 SSL/TLS Layer implementation SSL layer implemented by lot of vendors SUN/Oracle, Microsoft, IBM …. As well as opensource alternative: Open. SSL, Polar. SSL, GNUTLS, Libre. SSL … SSL 1. 0 never released Known attack SSL 2. 0 (1995) SSL 3. 0 RFC 6101 (1996) TLS 1. 0 RFC 2246 (1999) TLS 1. 1 RFC 4346 (2006) TLS 1. 2 RFC 5246 (2008) TLS 1. 3 (draft) - Renegotiation - Version rollback - BEAST - CRIME - BREACH - Padding - Lucky 13 - POODLE - RC 4 - Truncation - Heartbleed - BERserkr …………. Most of those attack are allowed due complicated and complex structure of SSL/TLS layer, unclean programmers techniques, doesn’t matter if happened on vendors or opensource. When Heartbleed exploit found, most of SSL stack has been analyzed and reevaluated. Thank to this has been found few issues and tenths of critical parts which need to be carefully redesigned, because possibility of another exploits.
SSL/TLS Layer implementation SSL layer implemented by lot of vendors SUN/Oracle, Microsoft, IBM …. As well as opensource alternative: Open. SSL, Polar. SSL, GNUTLS, Libre. SSL … SSL 1. 0 never released Known attack SSL 2. 0 (1995) SSL 3. 0 RFC 6101 (1996) TLS 1. 0 RFC 2246 (1999) TLS 1. 1 RFC 4346 (2006) TLS 1. 2 RFC 5246 (2008) TLS 1. 3 (draft) - Renegotiation - Version rollback - BEAST - CRIME - BREACH - Padding - Lucky 13 - POODLE - RC 4 - Truncation - Heartbleed - BERserkr …………. Most of those attack are allowed due complicated and complex structure of SSL/TLS layer, unclean programmers techniques, doesn’t matter if happened on vendors or opensource. When Heartbleed exploit found, most of SSL stack has been analyzed and reevaluated. Thank to this has been found few issues and tenths of critical parts which need to be carefully redesigned, because possibility of another exploits.
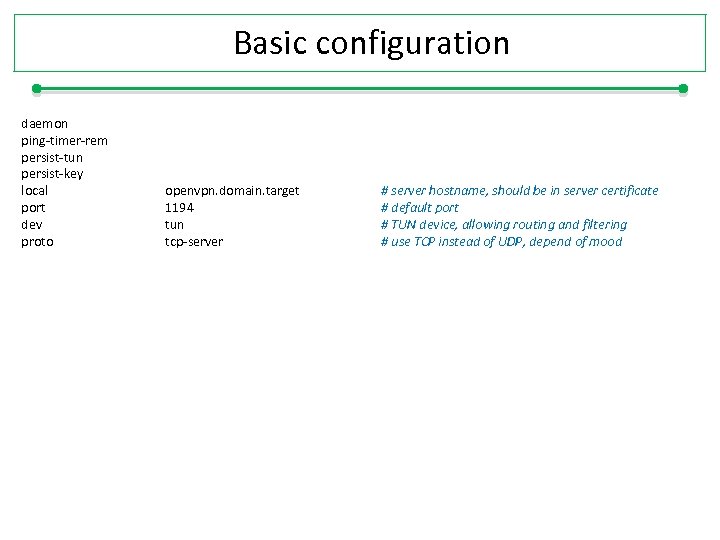 Basic configuration daemon ping-timer-rem persist-tun persist-key local port dev proto openvpn. domain. target 1194 tun tcp-server # server hostname, should be in server certificate # default port # TUN device, allowing routing and filtering # use TCP instead of UDP, depend of mood
Basic configuration daemon ping-timer-rem persist-tun persist-key local port dev proto openvpn. domain. target 1194 tun tcp-server # server hostname, should be in server certificate # default port # TUN device, allowing routing and filtering # use TCP instead of UDP, depend of mood
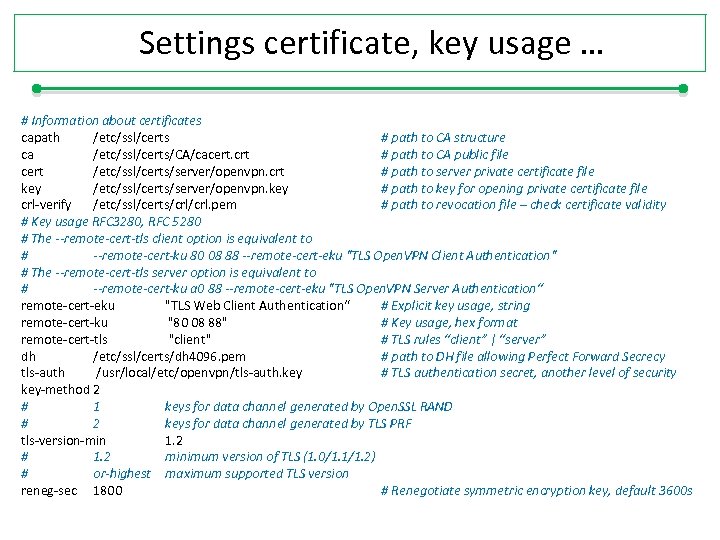 Settings certificate, key usage … # Information about certificates capath /etc/ssl/certs # path to CA structure ca /etc/ssl/certs/CA/cacert. crt # path to CA public file cert /etc/ssl/certs/server/openvpn. crt # path to server private certificate file key /etc/ssl/certs/server/openvpn. key # path to key for opening private certificate file crl-verify /etc/ssl/certs/crl. pem # path to revocation file – check certificate validity # Key usage RFC 3280, RFC 5280 # The --remote-cert-tls client option is equivalent to # --remote-cert-ku 80 08 88 --remote-cert-eku "TLS Open. VPN Client Authentication" # The --remote-cert-tls server option is equivalent to # --remote-cert-ku a 0 88 --remote-cert-eku "TLS Open. VPN Server Authentication“ remote-cert-eku "TLS Web Client Authentication“ # Explicit key usage, string remote-cert-ku "80 08 88" # Key usage, hex format remote-cert-tls "client" # TLS rules “client” | “server” dh /etc/ssl/certs/dh 4096. pem # path to DH file allowing Perfect Forward Secrecy tls-auth /usr/local/etc/openvpn/tls-auth. key # TLS authentication secret, another level of security key-method 2 # 1 keys for data channel generated by Open. SSL RAND # 2 keys for data channel generated by TLS PRF tls-version-min 1. 2 # 1. 2 minimum version of TLS (1. 0/1. 1/1. 2) # or-highest maximum supported TLS version reneg-sec 1800 # Renegotiate symmetric encryption key, default 3600 s
Settings certificate, key usage … # Information about certificates capath /etc/ssl/certs # path to CA structure ca /etc/ssl/certs/CA/cacert. crt # path to CA public file cert /etc/ssl/certs/server/openvpn. crt # path to server private certificate file key /etc/ssl/certs/server/openvpn. key # path to key for opening private certificate file crl-verify /etc/ssl/certs/crl. pem # path to revocation file – check certificate validity # Key usage RFC 3280, RFC 5280 # The --remote-cert-tls client option is equivalent to # --remote-cert-ku 80 08 88 --remote-cert-eku "TLS Open. VPN Client Authentication" # The --remote-cert-tls server option is equivalent to # --remote-cert-ku a 0 88 --remote-cert-eku "TLS Open. VPN Server Authentication“ remote-cert-eku "TLS Web Client Authentication“ # Explicit key usage, string remote-cert-ku "80 08 88" # Key usage, hex format remote-cert-tls "client" # TLS rules “client” | “server” dh /etc/ssl/certs/dh 4096. pem # path to DH file allowing Perfect Forward Secrecy tls-auth /usr/local/etc/openvpn/tls-auth. key # TLS authentication secret, another level of security key-method 2 # 1 keys for data channel generated by Open. SSL RAND # 2 keys for data channel generated by TLS PRF tls-version-min 1. 2 # 1. 2 minimum version of TLS (1. 0/1. 1/1. 2) # or-highest maximum supported TLS version reneg-sec 1800 # Renegotiate symmetric encryption key, default 3600 s
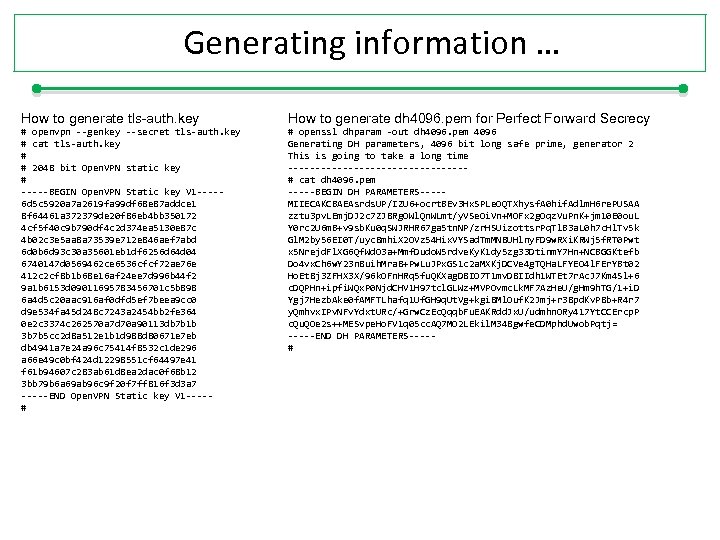 Generating information … How to generate tls-auth. key How to generate dh 4096. pem for Perfect Forward Secrecy # openvpn --genkey --secret tls-auth. key # cat tls-auth. key # # 2048 bit Open. VPN static key # -----BEGIN Open. VPN Static key V 1 ----6 d 5 c 5920 a 7 a 2619 fa 99 df 68 e 87 addce 1 8 f 64461 a 372379 de 20 f 86 eb 4 bb 350172 4 cf 5 f 40 c 9 b 790 df 4 c 2 d 374 ea 5130 e 87 c 4 b 02 c 3 e 5 aa 8 a 73539 e 712 e 846 aef 7 abd 6 d 0 b 6 d 93 c 30 a 35601 eb 1 df 6256 d 64 d 04 6740147 d 0569462 ce 6536 cfcf 72 ae 76 e 412 c 2 cf 8 b 1 b 68 e 16 af 24 ee 7 d 996 b 44 f 2 9 a 1 b 6153 d 09011695783456701 c 5 b 898 6 a 4 d 5 c 20 aac 916 af 0 dfd 5 ef 7 beea 9 cc 0 d 9 e 534 fa 45 d 248 c 7243 a 2454 bb 2 fe 364 0 e 2 c 3374 c 262570 a 7 d 70 a 90113 db 7 b 1 b 3 b 7 b 5 cc 2 d 8 a 512 e 1 b 1 d 988 d 80671 e 7 eb db 4941 a 7 e 24 a 96 c 75414 f 8532 c 1 de 296 a 66 e 49 c 0 bf 424 d 12298551 cf 64497 e 41 f 61 b 94607 c 283 ab 61 d 8 ea 2 dac 0 f 68 b 12 3 bb 79 b 6 a 69 ab 96 c 9 f 20 f 7 ff 816 f 3 d 3 a 7 -----END Open. VPN Static key V 1 ----# # openssl dhparam -out dh 4096. pem 4096 Generating DH parameters, 4096 bit long safe prime, generator 2 This is going to take a long time ----------------# cat dh 4096. pem -----BEGIN DH PARAMETERS----MIIECAKCBAEAsrds. UP/IZU 6+ocrt. BEv 3 Hx. SPLe. OQTXhysf. A 0 hif. Adlm. H 6 re. PUSAA zztu 3 pv. LEmj. DJ 2 c 7 ZJ 8 Rg. OWl. Qn. WLmt/y. VSe. Oi. Vn+MOFx 2 g. Oqz. Vu. Pn. K+jm 10 E 0 ou. L Y 0 rc 2 U 6 m. B+v 9 sb. Ku 0 q. SWJRHR 67 ga 5 tn. NP/zr. HSUizottsr. Pq. Tl. B 3 a. L 0 h 7 c. Hl. Tv 5 k Gl. M 2 by 56 EI 0 T/uyc 8 mhi. X 2 OVz 54 Hix. VYSad. Tm. MN 8 UHlny. FD 9 w. RXi. KRWj 5 f. RT 0 Pwt x 5 Nrejd. Fl. XG 6 Qf. Wd. O 3 a+Mmf. Dudo. W 5 rdve. Ky. K 1 dy 5 zg 33 Dtinm. Y 7 Hn+NCBGGKtefb Do 4 vx. Ch 6 w. Y 23 n 8 uih. Mra 8+Pw. Lu. JPx. GS 1 c 2 a. MXKj. DCVe 4 g. TQHa. LFYEO 4 l. FEr. YBt 02 Ho. Et 8 j 3 ZFHX 3 X/96 k. OFn. HRq 5 fu. QKXag. D 8 IO 7 T 1 mv. D 8 IIdh 1 WTEt 7 r. Ac. J 7 Km 4 Sl+6 c. DQPHn+ipfi. WQx. P 0 Njd. CHV 1 H 97 tcl. GLWz+MVPOvmc. Lk. MF 7 Az. He. U/g. Hm 9 h. TG/1+i. D Ygj 7 Hezb. Ake 0 f. AMFTLhafq 1 Uf. GH 9 q. Ut. Vg+kgi 8 Ml. Ouf. K 2 Jmj+r 38 pd. Kv. P 8 b+R 4 r 7 y. Qmhvx. IPv. NFv. Ydxt. URc/+Grw. Cz. Ec. Qqqb. Fu. EAKRdd. Jx. U/udmhn. ORy 417 Yt. CCErcp. P c. Qu. QOe 2 s++MESvpe. Ho. FV 1 q 05 cc. AQ 7 MO 2 LEkil. M 348 gwfe. CDMphd. Uwob. Pqtj= -----END DH PARAMETERS----#
Generating information … How to generate tls-auth. key How to generate dh 4096. pem for Perfect Forward Secrecy # openvpn --genkey --secret tls-auth. key # cat tls-auth. key # # 2048 bit Open. VPN static key # -----BEGIN Open. VPN Static key V 1 ----6 d 5 c 5920 a 7 a 2619 fa 99 df 68 e 87 addce 1 8 f 64461 a 372379 de 20 f 86 eb 4 bb 350172 4 cf 5 f 40 c 9 b 790 df 4 c 2 d 374 ea 5130 e 87 c 4 b 02 c 3 e 5 aa 8 a 73539 e 712 e 846 aef 7 abd 6 d 0 b 6 d 93 c 30 a 35601 eb 1 df 6256 d 64 d 04 6740147 d 0569462 ce 6536 cfcf 72 ae 76 e 412 c 2 cf 8 b 1 b 68 e 16 af 24 ee 7 d 996 b 44 f 2 9 a 1 b 6153 d 09011695783456701 c 5 b 898 6 a 4 d 5 c 20 aac 916 af 0 dfd 5 ef 7 beea 9 cc 0 d 9 e 534 fa 45 d 248 c 7243 a 2454 bb 2 fe 364 0 e 2 c 3374 c 262570 a 7 d 70 a 90113 db 7 b 1 b 3 b 7 b 5 cc 2 d 8 a 512 e 1 b 1 d 988 d 80671 e 7 eb db 4941 a 7 e 24 a 96 c 75414 f 8532 c 1 de 296 a 66 e 49 c 0 bf 424 d 12298551 cf 64497 e 41 f 61 b 94607 c 283 ab 61 d 8 ea 2 dac 0 f 68 b 12 3 bb 79 b 6 a 69 ab 96 c 9 f 20 f 7 ff 816 f 3 d 3 a 7 -----END Open. VPN Static key V 1 ----# # openssl dhparam -out dh 4096. pem 4096 Generating DH parameters, 4096 bit long safe prime, generator 2 This is going to take a long time ----------------# cat dh 4096. pem -----BEGIN DH PARAMETERS----MIIECAKCBAEAsrds. UP/IZU 6+ocrt. BEv 3 Hx. SPLe. OQTXhysf. A 0 hif. Adlm. H 6 re. PUSAA zztu 3 pv. LEmj. DJ 2 c 7 ZJ 8 Rg. OWl. Qn. WLmt/y. VSe. Oi. Vn+MOFx 2 g. Oqz. Vu. Pn. K+jm 10 E 0 ou. L Y 0 rc 2 U 6 m. B+v 9 sb. Ku 0 q. SWJRHR 67 ga 5 tn. NP/zr. HSUizottsr. Pq. Tl. B 3 a. L 0 h 7 c. Hl. Tv 5 k Gl. M 2 by 56 EI 0 T/uyc 8 mhi. X 2 OVz 54 Hix. VYSad. Tm. MN 8 UHlny. FD 9 w. RXi. KRWj 5 f. RT 0 Pwt x 5 Nrejd. Fl. XG 6 Qf. Wd. O 3 a+Mmf. Dudo. W 5 rdve. Ky. K 1 dy 5 zg 33 Dtinm. Y 7 Hn+NCBGGKtefb Do 4 vx. Ch 6 w. Y 23 n 8 uih. Mra 8+Pw. Lu. JPx. GS 1 c 2 a. MXKj. DCVe 4 g. TQHa. LFYEO 4 l. FEr. YBt 02 Ho. Et 8 j 3 ZFHX 3 X/96 k. OFn. HRq 5 fu. QKXag. D 8 IO 7 T 1 mv. D 8 IIdh 1 WTEt 7 r. Ac. J 7 Km 4 Sl+6 c. DQPHn+ipfi. WQx. P 0 Njd. CHV 1 H 97 tcl. GLWz+MVPOvmc. Lk. MF 7 Az. He. U/g. Hm 9 h. TG/1+i. D Ygj 7 Hezb. Ake 0 f. AMFTLhafq 1 Uf. GH 9 q. Ut. Vg+kgi 8 Ml. Ouf. K 2 Jmj+r 38 pd. Kv. P 8 b+R 4 r 7 y. Qmhvx. IPv. NFv. Ydxt. URc/+Grw. Cz. Ec. Qqqb. Fu. EAKRdd. Jx. U/udmhn. ORy 417 Yt. CCErcp. P c. Qu. QOe 2 s++MESvpe. Ho. FV 1 q 05 cc. AQ 7 MO 2 LEkil. M 348 gwfe. CDMphd. Uwob. Pqtj= -----END DH PARAMETERS----#
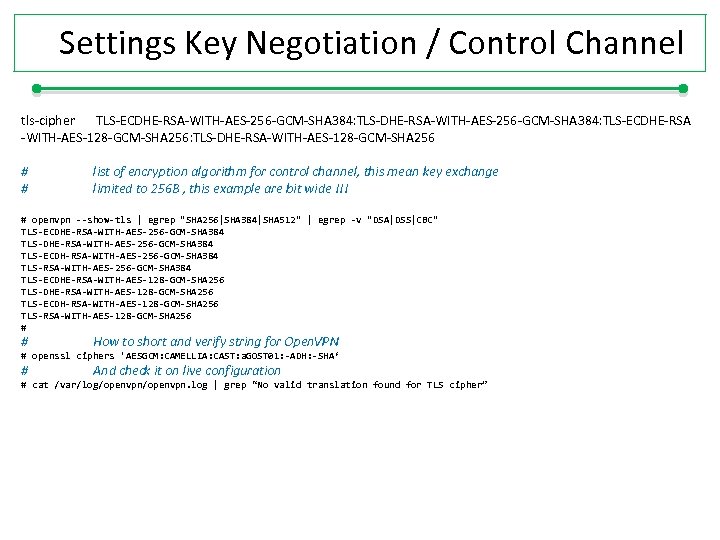 Settings Key Negotiation / Control Channel tls-cipher TLS-ECDHE-RSA-WITH-AES-256 -GCM-SHA 384: TLS-ECDHE-RSA -WITH-AES-128 -GCM-SHA 256: TLS-DHE-RSA-WITH-AES-128 -GCM-SHA 256 # # list of encryption algorithm for control channel, this mean key exchange limited to 256 B , this example are bit wide !!! # openvpn --show-tls | egrep "SHA 256|SHA 384|SHA 512" | egrep -v "DSA|DSS|CBC" TLS-ECDHE-RSA-WITH-AES-256 -GCM-SHA 384 TLS-ECDH-RSA-WITH-AES-256 -GCM-SHA 384 TLS-ECDHE-RSA-WITH-AES-128 -GCM-SHA 256 TLS-ECDH-RSA-WITH-AES-128 -GCM-SHA 256 TLS-RSA-WITH-AES-128 -GCM-SHA 256 # # How to short and verify string for Open. VPN # openssl ciphers 'AESGCM: CAMELLIA: CAST: a. GOST 01: -ADH: -SHA‘ # And check it on live configuration # cat /var/log/openvpn. log | grep “No valid translation found for TLS cipher”
Settings Key Negotiation / Control Channel tls-cipher TLS-ECDHE-RSA-WITH-AES-256 -GCM-SHA 384: TLS-ECDHE-RSA -WITH-AES-128 -GCM-SHA 256: TLS-DHE-RSA-WITH-AES-128 -GCM-SHA 256 # # list of encryption algorithm for control channel, this mean key exchange limited to 256 B , this example are bit wide !!! # openvpn --show-tls | egrep "SHA 256|SHA 384|SHA 512" | egrep -v "DSA|DSS|CBC" TLS-ECDHE-RSA-WITH-AES-256 -GCM-SHA 384 TLS-ECDH-RSA-WITH-AES-256 -GCM-SHA 384 TLS-ECDHE-RSA-WITH-AES-128 -GCM-SHA 256 TLS-ECDH-RSA-WITH-AES-128 -GCM-SHA 256 TLS-RSA-WITH-AES-128 -GCM-SHA 256 # # How to short and verify string for Open. VPN # openssl ciphers 'AESGCM: CAMELLIA: CAST: a. GOST 01: -ADH: -SHA‘ # And check it on live configuration # cat /var/log/openvpn. log | grep “No valid translation found for TLS cipher”
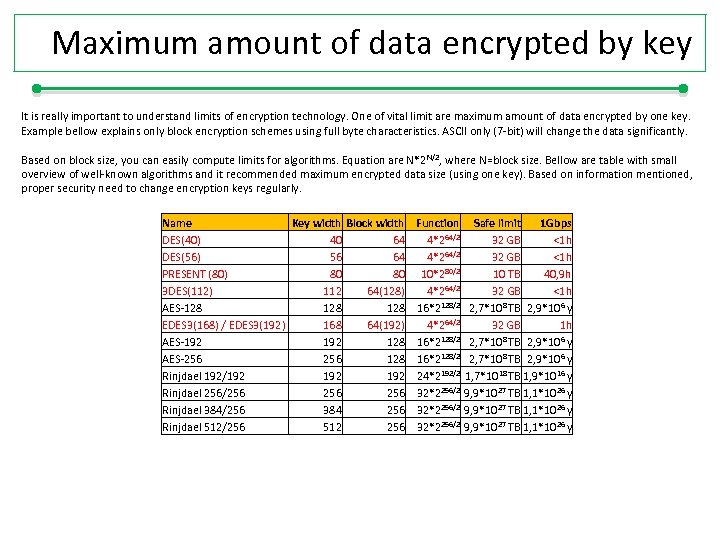 Maximum amount of data encrypted by key It is really important to understand limits of encryption technology. One of vital limit are maximum amount of data encrypted by one key. Example bellow explains only block encryption schemes using full byte characteristics. ASCII only (7 -bit) will change the data significantly. Based on block size, you can easily compute limits for algorithms. Equation are N*2 N/2, where N=block size. Bellow are table with small overview of well-known algorithms and it recommended maximum encrypted data size (using one key). Based on information mentioned, proper security need to change encryption keys regularly. Name Key width Block width DES(40) 40 64 DES(56) 56 64 PRESENT (80) 80 80 3 DES(112) 112 64(128) AES-128 128 EDES 3(168) / EDES 3(192) 168 64(192) AES-192 128 AES-256 128 Rinjdael 192/192 192 Rinjdael 256/256 256 Rinjdael 384/256 384 256 Rinjdael 512/256 512 256 Function 4*264/2 10*280/2 4*264/2 16*2128/2 24*2192/2 32*2256/2 Safe limit 1 Gbps 32 GB <1 h 10 TB 40, 9 h 32 GB <1 h 2, 7*108 TB 2, 9*106 y 32 GB 1 h 8 TB 2, 9*10 6 y 2, 7*108 TB 2, 9*106 y 1, 7*1018 TB 1, 9*1016 y 9, 9*1027 TB 1, 1*1026 y
Maximum amount of data encrypted by key It is really important to understand limits of encryption technology. One of vital limit are maximum amount of data encrypted by one key. Example bellow explains only block encryption schemes using full byte characteristics. ASCII only (7 -bit) will change the data significantly. Based on block size, you can easily compute limits for algorithms. Equation are N*2 N/2, where N=block size. Bellow are table with small overview of well-known algorithms and it recommended maximum encrypted data size (using one key). Based on information mentioned, proper security need to change encryption keys regularly. Name Key width Block width DES(40) 40 64 DES(56) 56 64 PRESENT (80) 80 80 3 DES(112) 112 64(128) AES-128 128 EDES 3(168) / EDES 3(192) 168 64(192) AES-192 128 AES-256 128 Rinjdael 192/192 192 Rinjdael 256/256 256 Rinjdael 384/256 384 256 Rinjdael 512/256 512 256 Function 4*264/2 10*280/2 4*264/2 16*2128/2 24*2192/2 32*2256/2 Safe limit 1 Gbps 32 GB <1 h 10 TB 40, 9 h 32 GB <1 h 2, 7*108 TB 2, 9*106 y 32 GB 1 h 8 TB 2, 9*10 6 y 2, 7*108 TB 2, 9*106 y 1, 7*1018 TB 1, 9*1016 y 9, 9*1027 TB 1, 1*1026 y
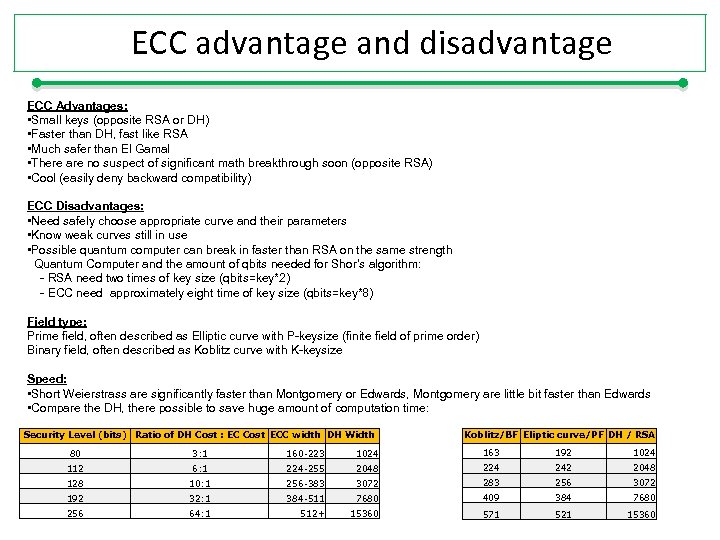 ECC advantage and disadvantage ECC Advantages: • Small keys (opposite RSA or DH) • Faster than DH, fast like RSA • Much safer than El Gamal • There are no suspect of significant math breakthrough soon (opposite RSA) • Cool (easily deny backward compatibility) ECC Disadvantages: • Need safely choose appropriate curve and their parameters • Know weak curves still in use • Possible quantum computer can break in faster than RSA on the same strength Quantum Computer and the amount of qbits needed for Shor’s algorithm: - RSA need two times of key size (qbits=key*2) - ECC need approximately eight time of key size (qbits=key*8) Field type: Prime field, often described as Elliptic curve with P-keysize (finite field of prime order) Binary field, often described as Koblitz curve with K-keysize Speed: • Short Weierstrass are significantly faster than Montgomery or Edwards, Montgomery are little bit faster than Edwards • Compare the DH, there possible to save huge amount of computation time: Security Level (bits) Ratio of DH Cost : EC Cost ECC width DH Width Koblitz/BF Eliptic curve/PF DH / RSA 80 3: 1 160 -223 1024 163 192 1024 112 6: 1 224 -255 2048 224 242 2048 128 10: 1 256 -383 3072 283 256 3072 192 32: 1 384 -511 7680 409 384 7680 256 64: 1 512+ 15360 571 521 15360
ECC advantage and disadvantage ECC Advantages: • Small keys (opposite RSA or DH) • Faster than DH, fast like RSA • Much safer than El Gamal • There are no suspect of significant math breakthrough soon (opposite RSA) • Cool (easily deny backward compatibility) ECC Disadvantages: • Need safely choose appropriate curve and their parameters • Know weak curves still in use • Possible quantum computer can break in faster than RSA on the same strength Quantum Computer and the amount of qbits needed for Shor’s algorithm: - RSA need two times of key size (qbits=key*2) - ECC need approximately eight time of key size (qbits=key*8) Field type: Prime field, often described as Elliptic curve with P-keysize (finite field of prime order) Binary field, often described as Koblitz curve with K-keysize Speed: • Short Weierstrass are significantly faster than Montgomery or Edwards, Montgomery are little bit faster than Edwards • Compare the DH, there possible to save huge amount of computation time: Security Level (bits) Ratio of DH Cost : EC Cost ECC width DH Width Koblitz/BF Eliptic curve/PF DH / RSA 80 3: 1 160 -223 1024 163 192 1024 112 6: 1 224 -255 2048 224 242 2048 128 10: 1 256 -383 3072 283 256 3072 192 32: 1 384 -511 7680 409 384 7680 256 64: 1 512+ 15360 571 521 15360
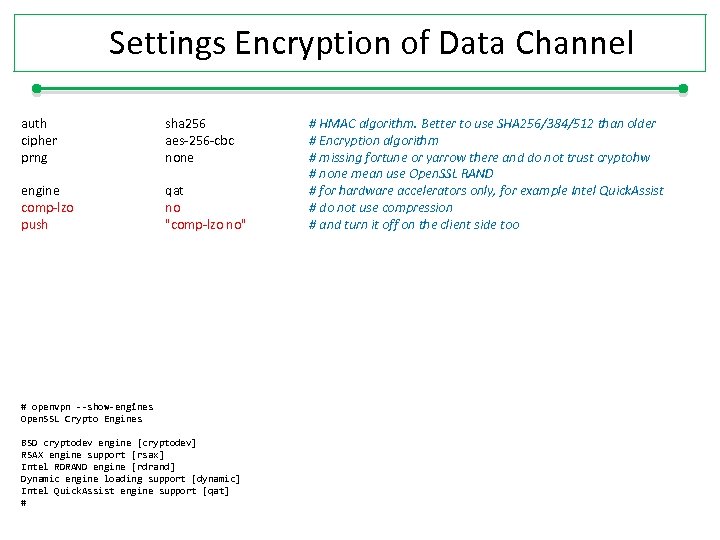 Settings Encryption of Data Channel auth cipher prng sha 256 aes-256 -cbc none engine comp-lzo push qat no "comp-lzo no" # openvpn --show-engines Open. SSL Crypto Engines BSD cryptodev engine [cryptodev] RSAX engine support [rsax] Intel RDRAND engine [rdrand] Dynamic engine loading support [dynamic] Intel Quick. Assist engine support [qat] # # HMAC algorithm. Better to use SHA 256/384/512 than older # Encryption algorithm # missing fortune or yarrow there and do not trust cryptohw # none mean use Open. SSL RAND # for hardware accelerators only, for example Intel Quick. Assist # do not use compression # and turn it off on the client side too
Settings Encryption of Data Channel auth cipher prng sha 256 aes-256 -cbc none engine comp-lzo push qat no "comp-lzo no" # openvpn --show-engines Open. SSL Crypto Engines BSD cryptodev engine [cryptodev] RSAX engine support [rsax] Intel RDRAND engine [rdrand] Dynamic engine loading support [dynamic] Intel Quick. Assist engine support [qat] # # HMAC algorithm. Better to use SHA 256/384/512 than older # Encryption algorithm # missing fortune or yarrow there and do not trust cryptohw # none mean use Open. SSL RAND # for hardware accelerators only, for example Intel Quick. Assist # do not use compression # and turn it off on the client side too
 Is your hardware sufficient ?
Is your hardware sufficient ?
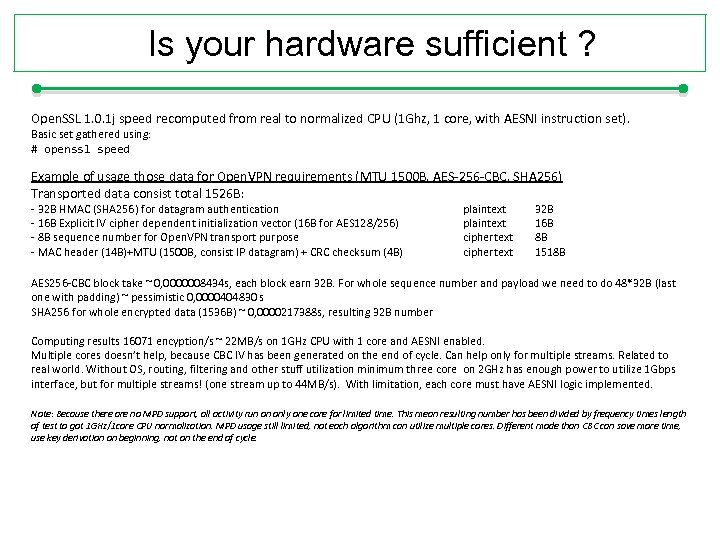 Is your hardware sufficient ? Open. SSL 1. 0. 1 j speed recomputed from real to normalized CPU (1 Ghz, 1 core, with AESNI instruction set). Basic set gathered using: # openssl speed Example of usage those data for Open. VPN requirements (MTU 1500 B, AES-256 -CBC, SHA 256) Transported data consist total 1526 B: - 32 B HMAC (SHA 256) for datagram authentication - 16 B Explicit IV cipher dependent initialization vector (16 B for AES 128/256) - 8 B sequence number for Open. VPN transport purpose - MAC header (14 B)+MTU (1500 B, consist IP datagram) + CRC checksum (4 B) plaintext ciphertext 32 B 16 B 8 B 1518 B AES 256 -CBC block take ~ 0, 0000008434 s, each block earn 32 B. For whole sequence number and payload we need to do 48*32 B (last one with padding) ~ pessimistic 0, 0000404830 s SHA 256 for whole encrypted data (1536 B) ~ 0, 0000217388 s, resulting 32 B number Computing results 16071 encyption/s ~ 22 MB/s on 1 GHz CPU with 1 core and AESNI enabled. Multiple cores doesn’t help, because CBC IV has been generated on the end of cycle. Can help only for multiple streams. Related to real world. Without OS, routing, filtering and other stuff utilization minimum three core on 2 GHz has enough power to utilize 1 Gbps interface, but for multiple streams! (one stream up to 44 MB/s). With limitation, each core must have AESNI logic implemented. Note: Because there are no MPD support, all activity run on only one core for limited time. This mean resulting number has been divided by frequency times length of test to got 1 GHz/1 core CPU normalization. MPD usage still limited, not each algorithm can utilize multiple cores. Different mode than CBC can save more time, use key derivation on beginning, not on the end of cycle.
Is your hardware sufficient ? Open. SSL 1. 0. 1 j speed recomputed from real to normalized CPU (1 Ghz, 1 core, with AESNI instruction set). Basic set gathered using: # openssl speed Example of usage those data for Open. VPN requirements (MTU 1500 B, AES-256 -CBC, SHA 256) Transported data consist total 1526 B: - 32 B HMAC (SHA 256) for datagram authentication - 16 B Explicit IV cipher dependent initialization vector (16 B for AES 128/256) - 8 B sequence number for Open. VPN transport purpose - MAC header (14 B)+MTU (1500 B, consist IP datagram) + CRC checksum (4 B) plaintext ciphertext 32 B 16 B 8 B 1518 B AES 256 -CBC block take ~ 0, 0000008434 s, each block earn 32 B. For whole sequence number and payload we need to do 48*32 B (last one with padding) ~ pessimistic 0, 0000404830 s SHA 256 for whole encrypted data (1536 B) ~ 0, 0000217388 s, resulting 32 B number Computing results 16071 encyption/s ~ 22 MB/s on 1 GHz CPU with 1 core and AESNI enabled. Multiple cores doesn’t help, because CBC IV has been generated on the end of cycle. Can help only for multiple streams. Related to real world. Without OS, routing, filtering and other stuff utilization minimum three core on 2 GHz has enough power to utilize 1 Gbps interface, but for multiple streams! (one stream up to 44 MB/s). With limitation, each core must have AESNI logic implemented. Note: Because there are no MPD support, all activity run on only one core for limited time. This mean resulting number has been divided by frequency times length of test to got 1 GHz/1 core CPU normalization. MPD usage still limited, not each algorithm can utilize multiple cores. Different mode than CBC can save more time, use key derivation on beginning, not on the end of cycle.
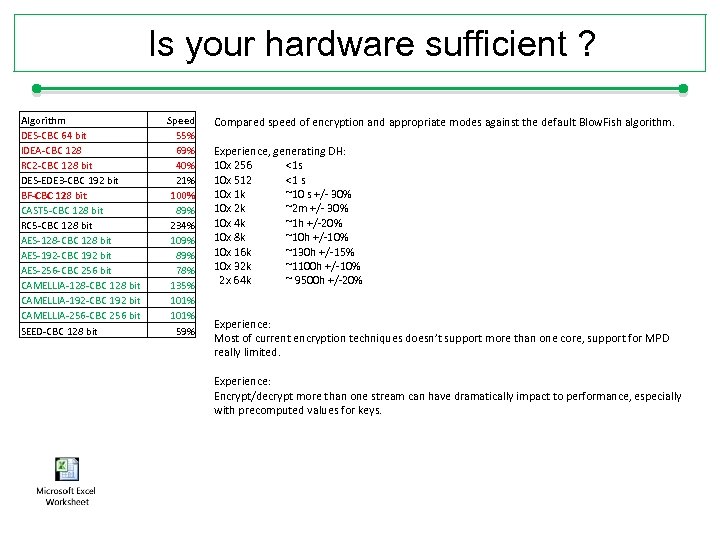 Is your hardware sufficient ? Algorithm DES-CBC 64 bit IDEA-CBC 128 RC 2 -CBC 128 bit DES-EDE 3 -CBC 192 bit BF-CBC 128 bit CAST 5 -CBC 128 bit RC 5 -CBC 128 bit AES-128 -CBC 128 bit AES-192 -CBC 192 bit AES-256 -CBC 256 bit CAMELLIA-128 -CBC 128 bit CAMELLIA-192 -CBC 192 bit CAMELLIA-256 -CBC 256 bit SEED-CBC 128 bit Speed 55% 69% 40% 21% 100% 89% 234% 109% 89% 78% 135% 101% 59% Compared speed of encryption and appropriate modes against the default Blow. Fish algorithm. Experience, generating DH: 10 x 256 <1 s 10 x 512 <1 s 10 x 1 k ~10 s +/- 30% 10 x 2 k ~2 m +/- 30% 10 x 4 k ~1 h +/-20% 10 x 8 k ~10 h +/-10% 10 x 16 k ~130 h +/-15% 10 x 32 k ~1100 h +/-10% 2 x 64 k ~ 9500 h +/-20% Experience: Most of current encryption techniques doesn’t support more than one core, support for MPD really limited. Experience: Encrypt/decrypt more than one stream can have dramatically impact to performance, especially with precomputed values for keys.
Is your hardware sufficient ? Algorithm DES-CBC 64 bit IDEA-CBC 128 RC 2 -CBC 128 bit DES-EDE 3 -CBC 192 bit BF-CBC 128 bit CAST 5 -CBC 128 bit RC 5 -CBC 128 bit AES-128 -CBC 128 bit AES-192 -CBC 192 bit AES-256 -CBC 256 bit CAMELLIA-128 -CBC 128 bit CAMELLIA-192 -CBC 192 bit CAMELLIA-256 -CBC 256 bit SEED-CBC 128 bit Speed 55% 69% 40% 21% 100% 89% 234% 109% 89% 78% 135% 101% 59% Compared speed of encryption and appropriate modes against the default Blow. Fish algorithm. Experience, generating DH: 10 x 256 <1 s 10 x 512 <1 s 10 x 1 k ~10 s +/- 30% 10 x 2 k ~2 m +/- 30% 10 x 4 k ~1 h +/-20% 10 x 8 k ~10 h +/-10% 10 x 16 k ~130 h +/-15% 10 x 32 k ~1100 h +/-10% 2 x 64 k ~ 9500 h +/-20% Experience: Most of current encryption techniques doesn’t support more than one core, support for MPD really limited. Experience: Encrypt/decrypt more than one stream can have dramatically impact to performance, especially with precomputed values for keys.
 Random generators Where randomnes needs: - Key generation - Nonces - One. Time Pads - Salts … RND PRNG CSPRNG Random Number Generator Pseudo. Random Number Generator Cryptographically Secure Pseudo. Random number generator CSPRNG algorithm: Yarrow http: //www. schneier. com/yarrow. html Fortuna https: //www. schneier. com/fortuna. html Intel’s Rd. Rand Via Technology’s Padlock on-chip random number generators reported in 2014 year that the National Security Agency had allegedly weakening cryptographic standards built in conjunction with the National Institute for Standards and Technology so that the NSA could circumvent them in order to perform its surveillance operations. Similar design with kleptography characteristics has been the Dual_EC_DRBG (Dual Elliptic Curve Deterministic Random Bit Generator, 2001), has been removed from NIST standards in 2013 year.
Random generators Where randomnes needs: - Key generation - Nonces - One. Time Pads - Salts … RND PRNG CSPRNG Random Number Generator Pseudo. Random Number Generator Cryptographically Secure Pseudo. Random number generator CSPRNG algorithm: Yarrow http: //www. schneier. com/yarrow. html Fortuna https: //www. schneier. com/fortuna. html Intel’s Rd. Rand Via Technology’s Padlock on-chip random number generators reported in 2014 year that the National Security Agency had allegedly weakening cryptographic standards built in conjunction with the National Institute for Standards and Technology so that the NSA could circumvent them in order to perform its surveillance operations. Similar design with kleptography characteristics has been the Dual_EC_DRBG (Dual Elliptic Curve Deterministic Random Bit Generator, 2001), has been removed from NIST standards in 2013 year.
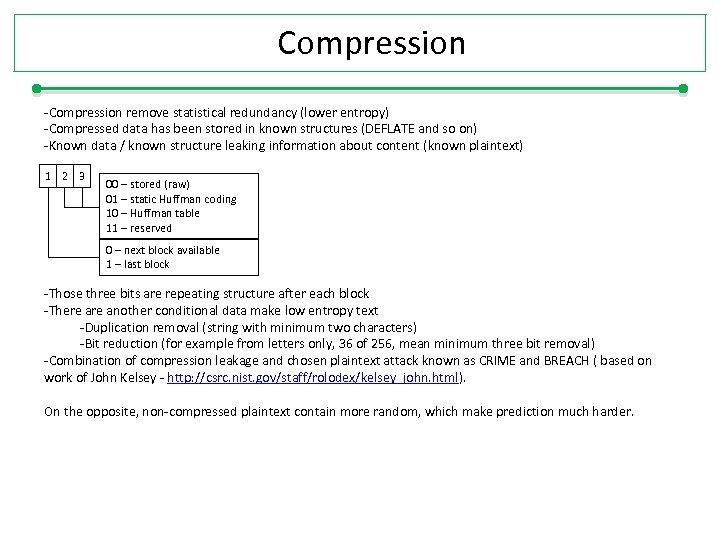 Compression -Compression remove statistical redundancy (lower entropy) -Compressed data has been stored in known structures (DEFLATE and so on) -Known data / known structure leaking information about content (known plaintext) 1 2 3 00 – stored (raw) 01 – static Huffman coding 10 – Huffman table 11 – reserved 0 – next block available 1 – last block -Those three bits are repeating structure after each block -There another conditional data make low entropy text -Duplication removal (string with minimum two characters) -Bit reduction (for example from letters only, 36 of 256, mean minimum three bit removal) -Combination of compression leakage and chosen plaintext attack known as CRIME and BREACH ( based on work of John Kelsey - http: //csrc. nist. gov/staff/rolodex/kelsey_john. html). On the opposite, non-compressed plaintext contain more random, which make prediction much harder.
Compression -Compression remove statistical redundancy (lower entropy) -Compressed data has been stored in known structures (DEFLATE and so on) -Known data / known structure leaking information about content (known plaintext) 1 2 3 00 – stored (raw) 01 – static Huffman coding 10 – Huffman table 11 – reserved 0 – next block available 1 – last block -Those three bits are repeating structure after each block -There another conditional data make low entropy text -Duplication removal (string with minimum two characters) -Bit reduction (for example from letters only, 36 of 256, mean minimum three bit removal) -Combination of compression leakage and chosen plaintext attack known as CRIME and BREACH ( based on work of John Kelsey - http: //csrc. nist. gov/staff/rolodex/kelsey_john. html). On the opposite, non-compressed plaintext contain more random, which make prediction much harder.
 Logging verb status log-append mute 2 /var/log/openvpn/status. log /var/log/openvpn/openvpn. log 64 # verbosity level # status message of connection # openvpn logging # append openvpn logs # mute the repeating messages Note: Log files should be regularly reviewed by engines like OSSEC, NAGIOS … or by custom script. In other case this is a waste of disk space and time spend on hardening.
Logging verb status log-append mute 2 /var/log/openvpn/status. log /var/log/openvpn/openvpn. log 64 # verbosity level # status message of connection # openvpn logging # append openvpn logs # mute the repeating messages Note: Log files should be regularly reviewed by engines like OSSEC, NAGIOS … or by custom script. In other case this is a waste of disk space and time spend on hardening.
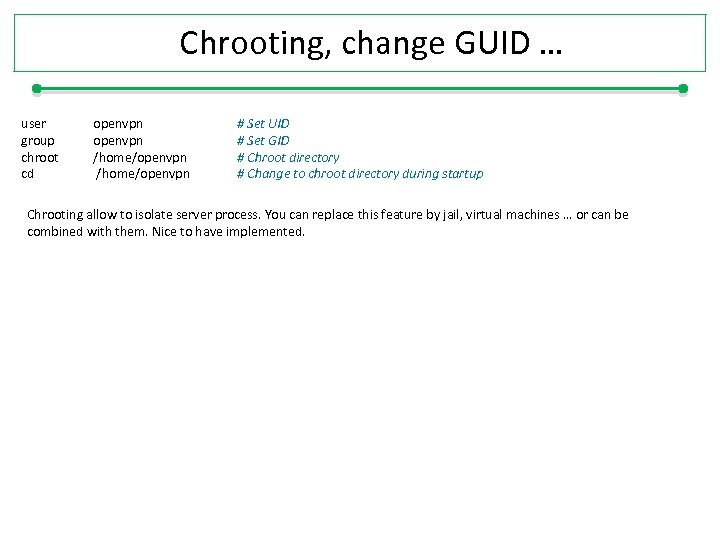 Chrooting, change GUID … user group chroot cd openvpn /home/openvpn # Set UID # Set GID # Chroot directory # Change to chroot directory during startup Chrooting allow to isolate server process. You can replace this feature by jail, virtual machines … or can be combined with them. Nice to have implemented.
Chrooting, change GUID … user group chroot cd openvpn /home/openvpn # Set UID # Set GID # Chroot directory # Change to chroot directory during startup Chrooting allow to isolate server process. You can replace this feature by jail, virtual machines … or can be combined with them. Nice to have implemented.
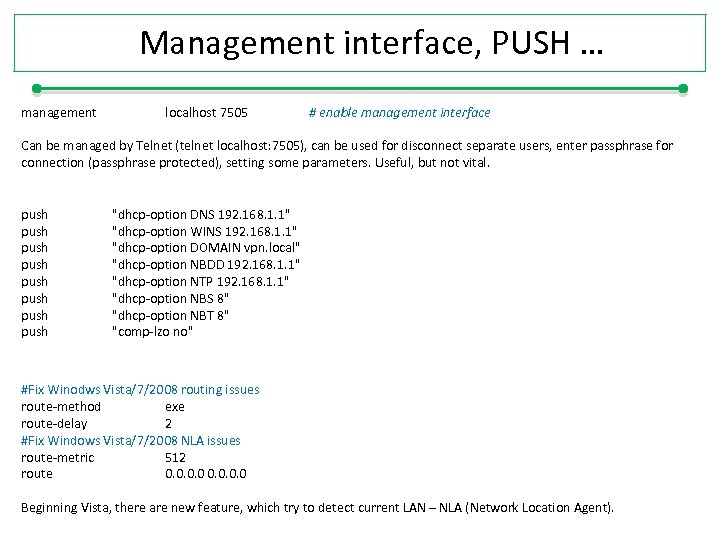 Management interface, PUSH … management localhost 7505 # enable management interface Can be managed by Telnet (telnet localhost: 7505), can be used for disconnect separate users, enter passphrase for connection (passphrase protected), setting some parameters. Useful, but not vital. push push "dhcp-option DNS 192. 168. 1. 1" "dhcp-option WINS 192. 168. 1. 1" "dhcp-option DOMAIN vpn. local" "dhcp-option NBDD 192. 168. 1. 1" "dhcp-option NTP 192. 168. 1. 1" "dhcp-option NBS 8" "dhcp-option NBT 8" "comp-lzo no" #Fix Winodws Vista/7/2008 routing issues route-method exe route-delay 2 #Fix Windows Vista/7/2008 NLA issues route-metric 512 route 0. 0 Beginning Vista, there are new feature, which try to detect current LAN – NLA (Network Location Agent).
Management interface, PUSH … management localhost 7505 # enable management interface Can be managed by Telnet (telnet localhost: 7505), can be used for disconnect separate users, enter passphrase for connection (passphrase protected), setting some parameters. Useful, but not vital. push push "dhcp-option DNS 192. 168. 1. 1" "dhcp-option WINS 192. 168. 1. 1" "dhcp-option DOMAIN vpn. local" "dhcp-option NBDD 192. 168. 1. 1" "dhcp-option NTP 192. 168. 1. 1" "dhcp-option NBS 8" "dhcp-option NBT 8" "comp-lzo no" #Fix Winodws Vista/7/2008 routing issues route-method exe route-delay 2 #Fix Windows Vista/7/2008 NLA issues route-metric 512 route 0. 0 Beginning Vista, there are new feature, which try to detect current LAN – NLA (Network Location Agent).
 Hardening – example … 2. Hardening secure comunnication, but limits backward compatibility. Why? 1. Cryptography standards and implementation are years above real progress in science. Technical standard has been developed by people which sometimes hesitate to ask the scientist.
Hardening – example … 2. Hardening secure comunnication, but limits backward compatibility. Why? 1. Cryptography standards and implementation are years above real progress in science. Technical standard has been developed by people which sometimes hesitate to ask the scientist.
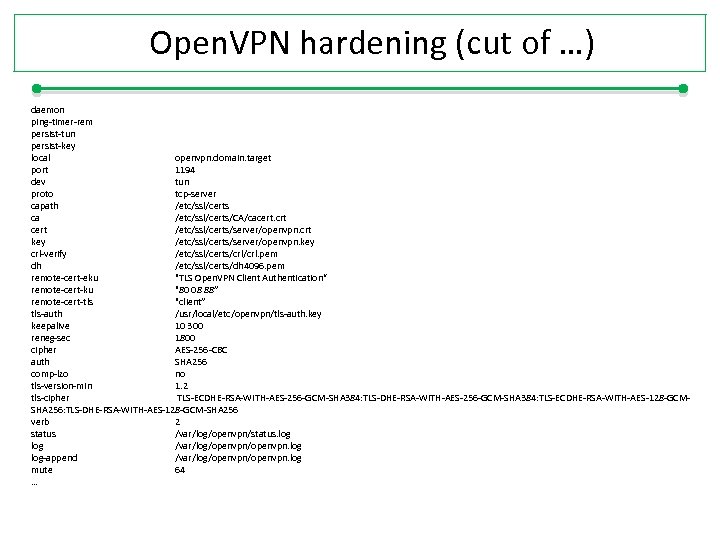 Open. VPN hardening (cut of …) daemon ping-timer-rem persist-tun persist-key local openvpn. domain. target port 1194 dev tun proto tcp-server capath /etc/ssl/certs ca /etc/ssl/certs/CA/cacert. crt cert /etc/ssl/certs/server/openvpn. crt key /etc/ssl/certs/server/openvpn. key crl-verify /etc/ssl/certs/crl. pem dh /etc/ssl/certs/dh 4096. pem remote-cert-eku "TLS Open. VPN Client Authentication“ remote-cert-ku "80 08 88” remote-cert-tls "client” tls-auth /usr/local/etc/openvpn/tls-auth. key keepalive 10 300 reneg-sec 1800 cipher AES-256 -CBC auth SHA 256 comp-lzo no tls-version-min 1. 2 tls-cipher TLS-ECDHE-RSA-WITH-AES-256 -GCM-SHA 384: TLS-ECDHE-RSA-WITH-AES-128 -GCMSHA 256: TLS-DHE-RSA-WITH-AES-128 -GCM-SHA 256 verb 2 status /var/log/openvpn/status. log /var/log/openvpn. log-append /var/log/openvpn. log mute 64 …
Open. VPN hardening (cut of …) daemon ping-timer-rem persist-tun persist-key local openvpn. domain. target port 1194 dev tun proto tcp-server capath /etc/ssl/certs ca /etc/ssl/certs/CA/cacert. crt cert /etc/ssl/certs/server/openvpn. crt key /etc/ssl/certs/server/openvpn. key crl-verify /etc/ssl/certs/crl. pem dh /etc/ssl/certs/dh 4096. pem remote-cert-eku "TLS Open. VPN Client Authentication“ remote-cert-ku "80 08 88” remote-cert-tls "client” tls-auth /usr/local/etc/openvpn/tls-auth. key keepalive 10 300 reneg-sec 1800 cipher AES-256 -CBC auth SHA 256 comp-lzo no tls-version-min 1. 2 tls-cipher TLS-ECDHE-RSA-WITH-AES-256 -GCM-SHA 384: TLS-ECDHE-RSA-WITH-AES-128 -GCMSHA 256: TLS-DHE-RSA-WITH-AES-128 -GCM-SHA 256 verb 2 status /var/log/openvpn/status. log /var/log/openvpn. log-append /var/log/openvpn. log mute 64 …
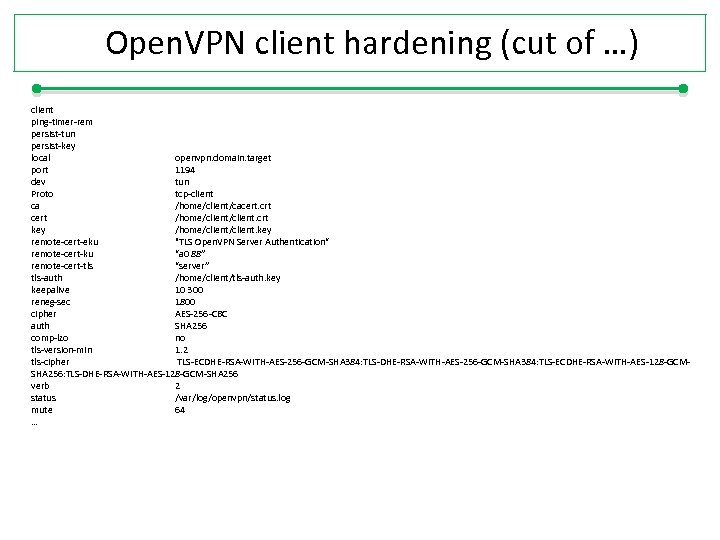 Open. VPN client hardening (cut of …) client ping-timer-rem persist-tun persist-key local openvpn. domain. target port 1194 dev tun Proto tcp-client ca /home/client/cacert. crt cert /home/client. crt key /home/client. key remote-cert-eku "TLS Open. VPN Server Authentication“ remote-cert-ku “a 0 88” remote-cert-tls “server” tls-auth /home/client/tls-auth. key keepalive 10 300 reneg-sec 1800 cipher AES-256 -CBC auth SHA 256 comp-lzo no tls-version-min 1. 2 tls-cipher TLS-ECDHE-RSA-WITH-AES-256 -GCM-SHA 384: TLS-ECDHE-RSA-WITH-AES-128 -GCMSHA 256: TLS-DHE-RSA-WITH-AES-128 -GCM-SHA 256 verb 2 status /var/log/openvpn/status. log mute 64 …
Open. VPN client hardening (cut of …) client ping-timer-rem persist-tun persist-key local openvpn. domain. target port 1194 dev tun Proto tcp-client ca /home/client/cacert. crt cert /home/client. crt key /home/client. key remote-cert-eku "TLS Open. VPN Server Authentication“ remote-cert-ku “a 0 88” remote-cert-tls “server” tls-auth /home/client/tls-auth. key keepalive 10 300 reneg-sec 1800 cipher AES-256 -CBC auth SHA 256 comp-lzo no tls-version-min 1. 2 tls-cipher TLS-ECDHE-RSA-WITH-AES-256 -GCM-SHA 384: TLS-ECDHE-RSA-WITH-AES-128 -GCMSHA 256: TLS-DHE-RSA-WITH-AES-128 -GCM-SHA 256 verb 2 status /var/log/openvpn/status. log mute 64 …
 Motivation Never Say Anything. Only part of government, that actually listen you ?
Motivation Never Say Anything. Only part of government, that actually listen you ?
 Do you want to know more? I would like to invite you 12 th October 2015 on whole day Encryption and Applied encryption training More information will be available 1 st Jun 2015 at http: //cryptosession. cz
Do you want to know more? I would like to invite you 12 th October 2015 on whole day Encryption and Applied encryption training More information will be available 1 st Jun 2015 at http: //cryptosession. cz


