e7d2cfb731e9d134f40de923f2ba1896.ppt
- Количество слайдов: 21
 Online AAI José A. Montenegro GISUM Group Security Information Section University of Malaga (Spain) Email: monte@lcc. uma. es Web: www. lcc. uma. es/~monte
Online AAI José A. Montenegro GISUM Group Security Information Section University of Malaga (Spain) Email: monte@lcc. uma. es Web: www. lcc. uma. es/~monte
 AAI? o Authentication & Authorization Infrastructure n n o Several possibilities We focused on PKI + PMI Development Background n PKI o o n Cert’e. M - Online PKI and more … X 509 ITU-T PMI o o Extending Cert’e. M – Online PMI X 509 ITU-T 2
AAI? o Authentication & Authorization Infrastructure n n o Several possibilities We focused on PKI + PMI Development Background n PKI o o n Cert’e. M - Online PKI and more … X 509 ITU-T PMI o o Extending Cert’e. M – Online PMI X 509 ITU-T 2
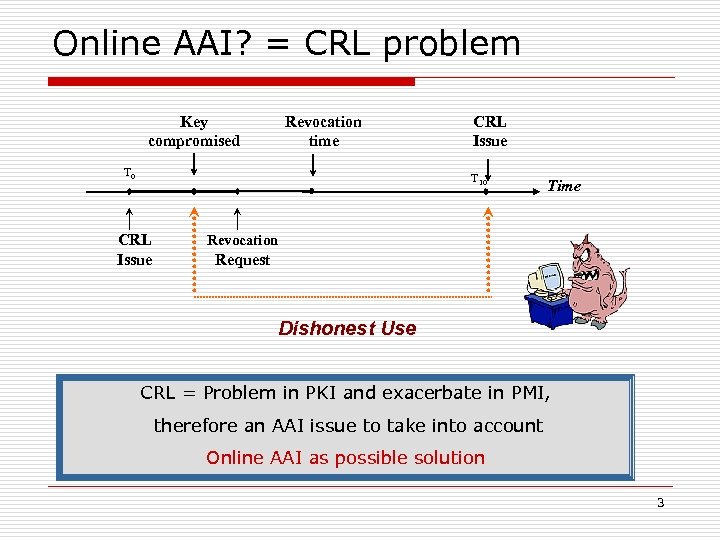 Online AAI? = CRL problem Key compromised Revocation time T 0 CRL Issue T 10 CRL Issue Time Revocation Request Dishonest Use CRL = Problem in PKI and exacerbate in PMI, therefore an AAI issue to take into account Online AAI as possible solution 3
Online AAI? = CRL problem Key compromised Revocation time T 0 CRL Issue T 10 CRL Issue Time Revocation Request Dishonest Use CRL = Problem in PKI and exacerbate in PMI, therefore an AAI issue to take into account Online AAI as possible solution 3
 What is Cert’e. M? o PKI online n n Designed & Implemented in ’ 98. Try to solve CRLs problems o o Email based on n n o OCSP service did not develop yet. X 509 usually linked to X 500 name X 509 proposal lets links to Email address (Rfc 822) Use an architecture of CAs that satisfy the needs of near-certification; 4
What is Cert’e. M? o PKI online n n Designed & Implemented in ’ 98. Try to solve CRLs problems o o Email based on n n o OCSP service did not develop yet. X 509 usually linked to X 500 name X 509 proposal lets links to Email address (Rfc 822) Use an architecture of CAs that satisfy the needs of near-certification; 4
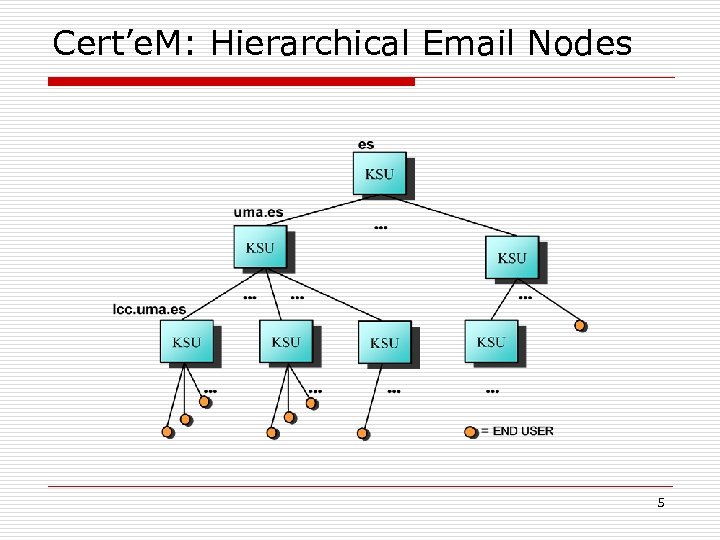 Cert’e. M: Hierarchical Email Nodes 5
Cert’e. M: Hierarchical Email Nodes 5
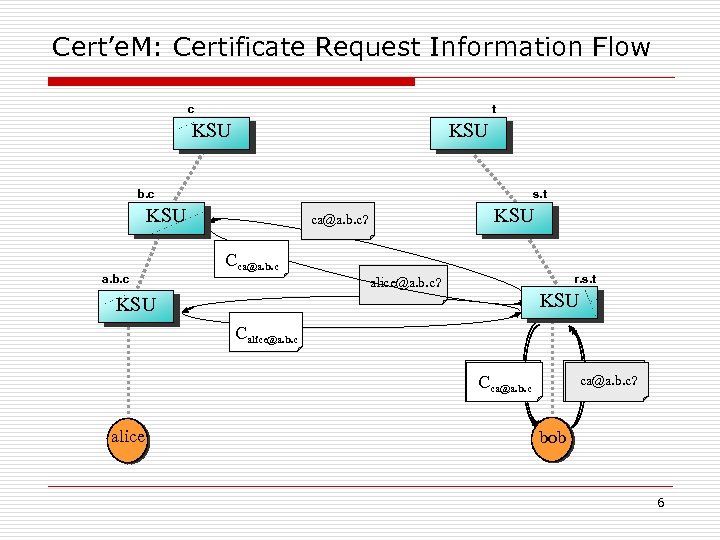 Cert’e. M: Certificate Request Information Flow c t KSU b. c s. t KSU a. b. c KSU ca@a. b. c? Cca@a. b. c r. s. t alice@a. b. c? KSU Calice@a. b. c? ca@a. b. c? Calice@a. b. c Cca@a. b. c alice bob 6
Cert’e. M: Certificate Request Information Flow c t KSU b. c s. t KSU a. b. c KSU ca@a. b. c? Cca@a. b. c r. s. t alice@a. b. c? KSU Calice@a. b. c? ca@a. b. c? Calice@a. b. c Cca@a. b. c alice bob 6
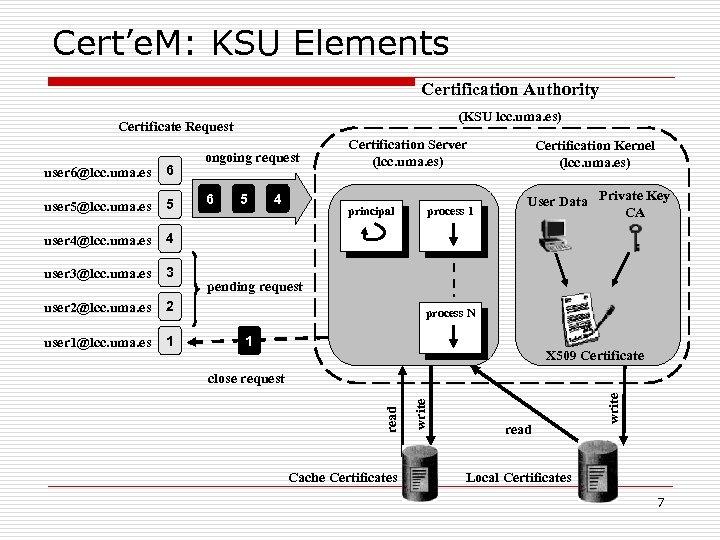 Cert’e. M: KSU Elements Certification Authority (KSU lcc. uma. es) Certificate Request 5 user 4@lcc. uma. es 4 user 3@lcc. uma. es 3 user 2@lcc. uma. es 2 user 1@lcc. uma. es 1 Certification Kernel (lcc. uma. es) 6 5 4 principal process 1 User Data Private Key CA pending request process N 1 X 509 Certificate close request Cache Certificates read write user 5@lcc. uma. es write 6 Certification Server (lcc. uma. es) read user 6@lcc. uma. es ongoing request Local Certificates 7
Cert’e. M: KSU Elements Certification Authority (KSU lcc. uma. es) Certificate Request 5 user 4@lcc. uma. es 4 user 3@lcc. uma. es 3 user 2@lcc. uma. es 2 user 1@lcc. uma. es 1 Certification Kernel (lcc. uma. es) 6 5 4 principal process 1 User Data Private Key CA pending request process N 1 X 509 Certificate close request Cache Certificates read write user 5@lcc. uma. es write 6 Certification Server (lcc. uma. es) read user 6@lcc. uma. es ongoing request Local Certificates 7
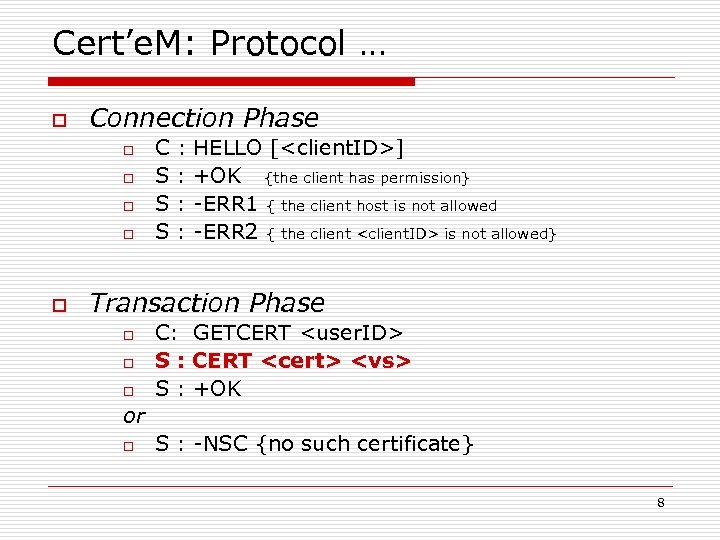 Cert’e. M: Protocol … o Connection Phase o o o C S S S : : HELLO [
Cert’e. M: Protocol … o Connection Phase o o o C S S S : : HELLO [
 … Cert’e. M: Protocol o Transaction Phase n S : CERT
… Cert’e. M: Protocol o Transaction Phase n S : CERT
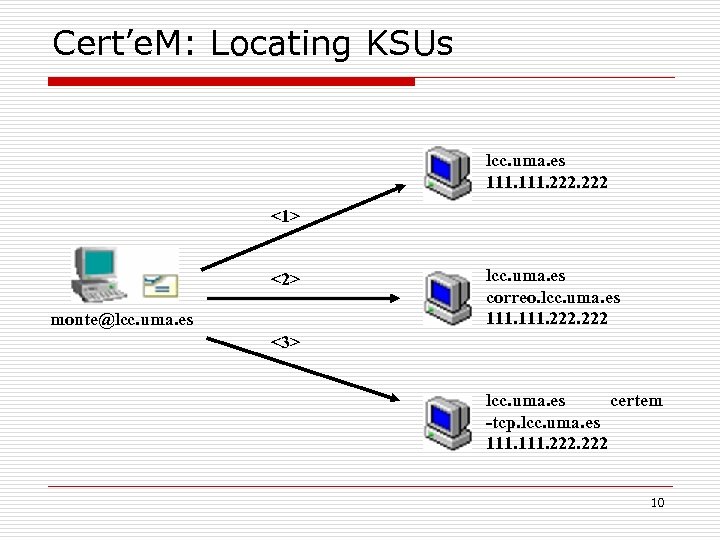 Cert’e. M: Locating KSUs lcc. uma. es 111. 222 <1> <2> monte@lcc. uma. es correo. lcc. uma. es 111. 222 <3> lcc. uma. es certem -tcp. lcc. uma. es 111. 222 10
Cert’e. M: Locating KSUs lcc. uma. es 111. 222 <1> <2> monte@lcc. uma. es correo. lcc. uma. es 111. 222 <3> lcc. uma. es certem -tcp. lcc. uma. es 111. 222 10
 Cert’e. M Conclusion o guarantees that CAs will only certify those users close to them; o provides real-time revocation of keys (without the need of CRLs); o close to S/MIME o Can provide quality service to GRIDs o slight protocol inter-KSU and user-KSU o provided services to several projects we have been implicated n (not only theoretic solution) 11
Cert’e. M Conclusion o guarantees that CAs will only certify those users close to them; o provides real-time revocation of keys (without the need of CRLs); o close to S/MIME o Can provide quality service to GRIDs o slight protocol inter-KSU and user-KSU o provided services to several projects we have been implicated n (not only theoretic solution) 11
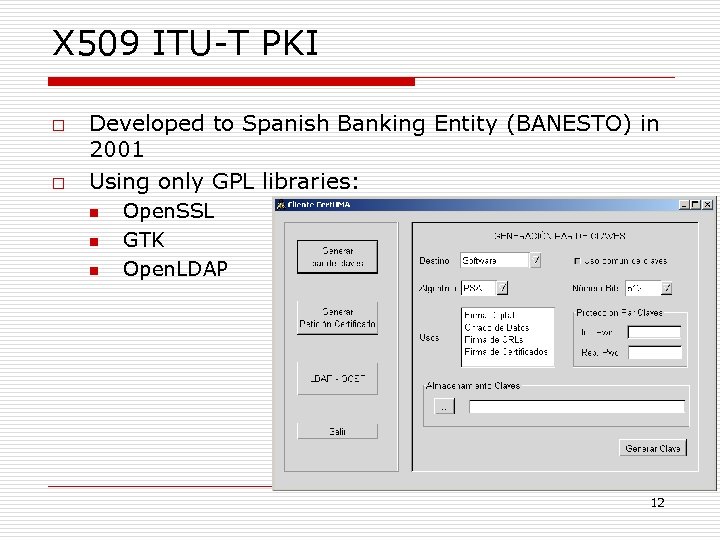 X 509 ITU-T PKI o o Developed to Spanish Banking Entity (BANESTO) in 2001 Using only GPL libraries: n n n Open. SSL GTK Open. LDAP 12
X 509 ITU-T PKI o o Developed to Spanish Banking Entity (BANESTO) in 2001 Using only GPL libraries: n n n Open. SSL GTK Open. LDAP 12
 X 509 ITU-T PMI (I) o ITU-T proposal defines four PMI models: o o o General, Control Role Delegation (PERMIS Project) (Our proposal) We have extended Open. SSL library attribute certificates management authorization capabilities, because: o o with and This library is widely deployed There was no previous experience with the introduction of attribute certificates in Open. SSL We wanted to approach privilege delegation procedures (we are still in the way) and … we had already developed a PKI using Open. SSL 13
X 509 ITU-T PMI (I) o ITU-T proposal defines four PMI models: o o o General, Control Role Delegation (PERMIS Project) (Our proposal) We have extended Open. SSL library attribute certificates management authorization capabilities, because: o o with and This library is widely deployed There was no previous experience with the introduction of attribute certificates in Open. SSL We wanted to approach privilege delegation procedures (we are still in the way) and … we had already developed a PKI using Open. SSL 13
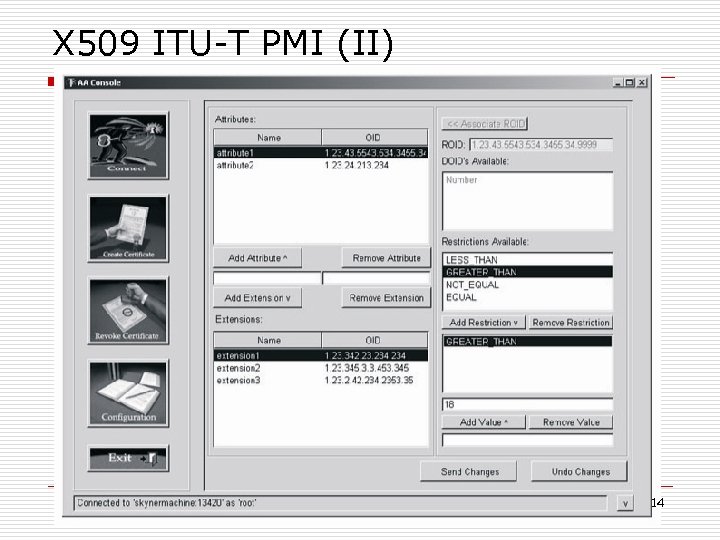 X 509 ITU-T PMI (II) 14
X 509 ITU-T PMI (II) 14
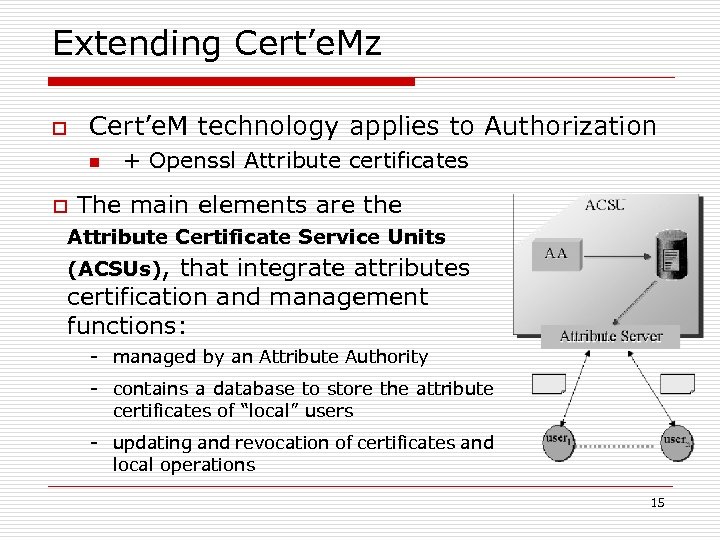 Extending Cert’e. Mz o Cert’e. M technology applies to Authorization n o + Openssl Attribute certificates The main elements are the Attribute Certificate Service Units (ACSUs), that integrate attributes certification and management functions: - managed by an Attribute Authority - contains a database to store the attribute certificates of “local” users - updating and revocation of certificates and local operations 15
Extending Cert’e. Mz o Cert’e. M technology applies to Authorization n o + Openssl Attribute certificates The main elements are the Attribute Certificate Service Units (ACSUs), that integrate attributes certification and management functions: - managed by an Attribute Authority - contains a database to store the attribute certificates of “local” users - updating and revocation of certificates and local operations 15
![AAI scenario (I) [Alice@a. b. c, operation] SAlice t s eque R Bob AC AAI scenario (I) [Alice@a. b. c, operation] SAlice t s eque R Bob AC](https://present5.com/presentation/e7d2cfb731e9d134f40de923f2ba1896/image-16.jpg) AAI scenario (I) [Alice@a. b. c, operation] SAlice t s eque R Bob AC PKC Who is the user ? & What can he do ? 1 A B: Token 2 B AAI: Request AAI 3 AAI B: AC + PKC 16
AAI scenario (I) [Alice@a. b. c, operation] SAlice t s eque R Bob AC PKC Who is the user ? & What can he do ? 1 A B: Token 2 B AAI: Request AAI 3 AAI B: AC + PKC 16
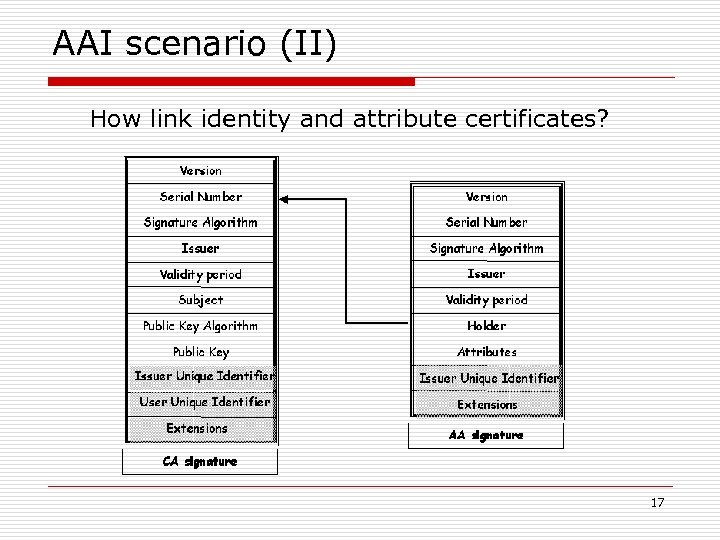 AAI scenario (II) How link identity and attribute certificates? 17
AAI scenario (II) How link identity and attribute certificates? 17
 Future Work o o Actually working in delegation model Delegation statements establish a Directed graphs n o D. G. offer a global vision of delegation system Theoretical model apply to PMI, and it work!!! 18
Future Work o o Actually working in delegation model Delegation statements establish a Directed graphs n o D. G. offer a global vision of delegation system Theoretical model apply to PMI, and it work!!! 18
 Thank you Any ? i on es t Qu José A. Montenegro GISUM Group Security Information Section University of Malaga (Spain) Email: monte@lcc. uma. es Web: www. lcc. uma. es/~monte 19
Thank you Any ? i on es t Qu José A. Montenegro GISUM Group Security Information Section University of Malaga (Spain) Email: monte@lcc. uma. es Web: www. lcc. uma. es/~monte 19
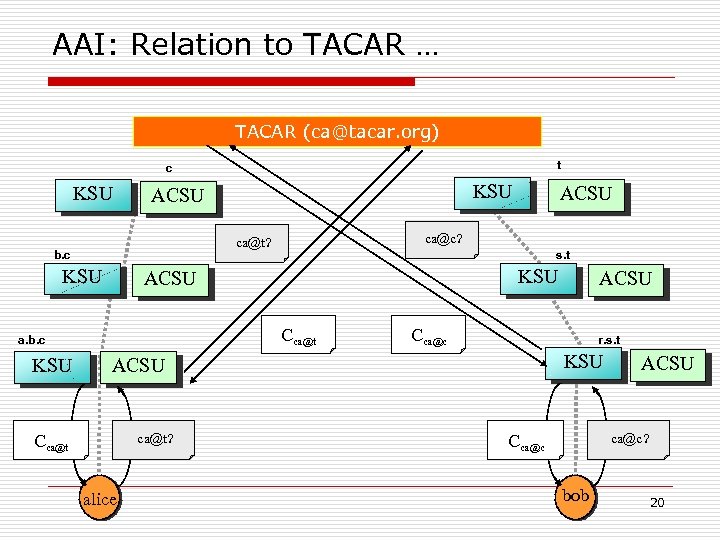 AAI: Relation to TACAR … TACAR (ca@tacar. org) t c KSU s. t KSU ACSU Cca@t a. b. c ACSU ca@c? ca@t? b. c KSU ACSU Cca@c r. s. t KSU ACSU ca@t? Cca@t alice ACSU ca@c? Cca@c bob 20
AAI: Relation to TACAR … TACAR (ca@tacar. org) t c KSU s. t KSU ACSU Cca@t a. b. c ACSU ca@c? ca@t? b. c KSU ACSU Cca@c r. s. t KSU ACSU ca@t? Cca@t alice ACSU ca@c? Cca@c bob 20
 … AAI: Relation to TACAR o Remember CA belongs to upper level. n o o Domain c and t is stored in TACAR is common root to “a. b. c” and “r. s. t” tree How to localize TACAR? n n Same way as whichever KSU/ACSU node. Add ca. c@tacar. org and ca. t@tacar. org certificates to TACAR 21
… AAI: Relation to TACAR o Remember CA belongs to upper level. n o o Domain c and t is stored in TACAR is common root to “a. b. c” and “r. s. t” tree How to localize TACAR? n n Same way as whichever KSU/ACSU node. Add ca. c@tacar. org and ca. t@tacar. org certificates to TACAR 21


