315816091a1b4548fa7c13563da51095.ppt
- Количество слайдов: 26
 On the Generation of X. 509 v 3 Certificates with Biometric Information Martínez-Silva et al.
On the Generation of X. 509 v 3 Certificates with Biometric Information Martínez-Silva et al.
 Motivation Martínez-Silva et al.
Motivation Martínez-Silva et al.
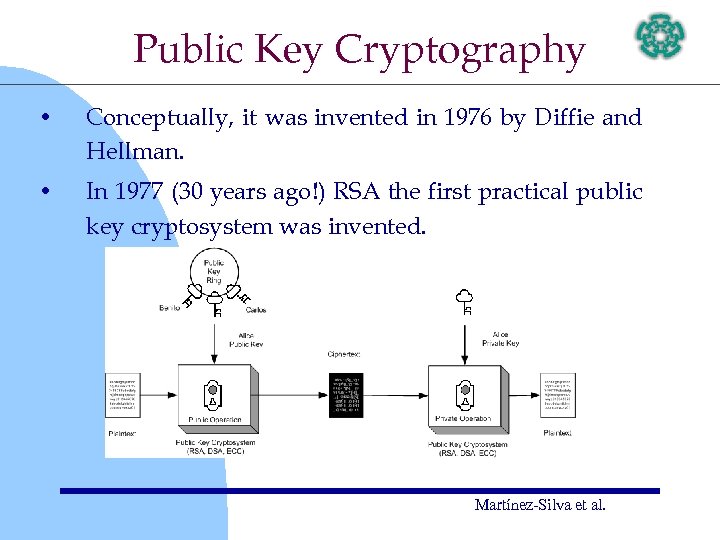 Public Key Cryptography • Conceptually, it was invented in 1976 by Diffie and Hellman. • In 1977 (30 years ago!) RSA the first practical public key cryptosystem was invented. Martínez-Silva et al.
Public Key Cryptography • Conceptually, it was invented in 1976 by Diffie and Hellman. • In 1977 (30 years ago!) RSA the first practical public key cryptosystem was invented. Martínez-Silva et al.
 Public Key Cryptography • Some major examples of public key cryptosystems are: – – DSA – ECC – • RSA NTRU Although public key cryptography allows the definition of digital signatures and their verification in a reliable way, this mechanism is not enough for preventing attacks. Martínez-Silva et al.
Public Key Cryptography • Some major examples of public key cryptosystems are: – – DSA – ECC – • RSA NTRU Although public key cryptography allows the definition of digital signatures and their verification in a reliable way, this mechanism is not enough for preventing attacks. Martínez-Silva et al.
 Digital Certificate Benefits • Secure Key Authentication – • Key Revocation – • A certificate indicates valid periods of operation Non-repudiation – • Avoids attacks such as man-in-the-middle A user cannot deny his/her public key. Policy Applications – It helps to concert security policies among a large community Martínez-Silva et al.
Digital Certificate Benefits • Secure Key Authentication – • Key Revocation – • A certificate indicates valid periods of operation Non-repudiation – • Avoids attacks such as man-in-the-middle A user cannot deny his/her public key. Policy Applications – It helps to concert security policies among a large community Martínez-Silva et al.
 X. 509 v 3 Certificate • X. 509 certificates version 3, were defined as an IETF standard [RFC 2459, 1999]. • It is composed by three main structures: TBS certificate (TBSCertificate), algorithm identifier (signature-Algorithm) and digital signature (signature. Value). • The TBS certificate and algorithm identifier consists of ten common fields, six of them mandatory and four optional. • Additionally, an X. 509 v 3 certificate must be formatted according to the (Abstract Syntax Notation One) ASN. 1 language Martínez-Silva et al.
X. 509 v 3 Certificate • X. 509 certificates version 3, were defined as an IETF standard [RFC 2459, 1999]. • It is composed by three main structures: TBS certificate (TBSCertificate), algorithm identifier (signature-Algorithm) and digital signature (signature. Value). • The TBS certificate and algorithm identifier consists of ten common fields, six of them mandatory and four optional. • Additionally, an X. 509 v 3 certificate must be formatted according to the (Abstract Syntax Notation One) ASN. 1 language Martínez-Silva et al.
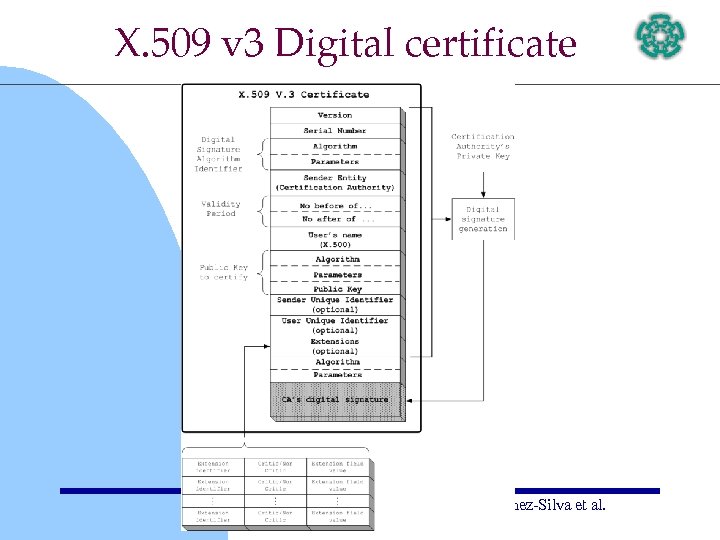 X. 509 v 3 Digital certificate Martínez-Silva et al.
X. 509 v 3 Digital certificate Martínez-Silva et al.
 Biometric Digital Certificate: Why? • By incorporating biometric information, it allows a stronger and more robust authentication. • For certain applications will be important to make sure that the biometric information presented to a system really belongs to a given user and that biometric data has been certificated by an authority. • Similarly, it may help to avoid that a user denies his biometric information Martínez-Silva et al.
Biometric Digital Certificate: Why? • By incorporating biometric information, it allows a stronger and more robust authentication. • For certain applications will be important to make sure that the biometric information presented to a system really belongs to a given user and that biometric data has been certificated by an authority. • Similarly, it may help to avoid that a user denies his biometric information Martínez-Silva et al.
 Technical Contributions we present the kernel implementation of a Mobile Certification Authority (MCA), with the following features: • Our MCA kernel is able to issue digital certificates fully complying with the X. 509 v 3 standard; • it supports either RSA or ECDSA as a public key cryptosystem engine and; • it can incorporate biometric-based user identification information (in the form of fingerprint recognition) to the digital certificate. Martínez-Silva et al.
Technical Contributions we present the kernel implementation of a Mobile Certification Authority (MCA), with the following features: • Our MCA kernel is able to issue digital certificates fully complying with the X. 509 v 3 standard; • it supports either RSA or ECDSA as a public key cryptosystem engine and; • it can incorporate biometric-based user identification information (in the form of fingerprint recognition) to the digital certificate. Martínez-Silva et al.
 Research Contributions • We provide a performance comparison between RSA and elliptic curve cryptosystems as a public key crypto-engines. • Among the NIST-recommended elliptic curves we establish which one is the more suitable for mobile devices such as PDAs. • We assessed the space/bandwidth needed for a X. 509 v 3 certificate with and without biometric information. • We give a concrete example of a biometric ECC/RSA certificate fully complying with the X. 509 v 3 standard. Martínez-Silva et al.
Research Contributions • We provide a performance comparison between RSA and elliptic curve cryptosystems as a public key crypto-engines. • Among the NIST-recommended elliptic curves we establish which one is the more suitable for mobile devices such as PDAs. • We assessed the space/bandwidth needed for a X. 509 v 3 certificate with and without biometric information. • We give a concrete example of a biometric ECC/RSA certificate fully complying with the X. 509 v 3 standard. Martínez-Silva et al.
 Generating/validating X. 509 v 3 Certificates Martínez-Silva et al.
Generating/validating X. 509 v 3 Certificates Martínez-Silva et al.
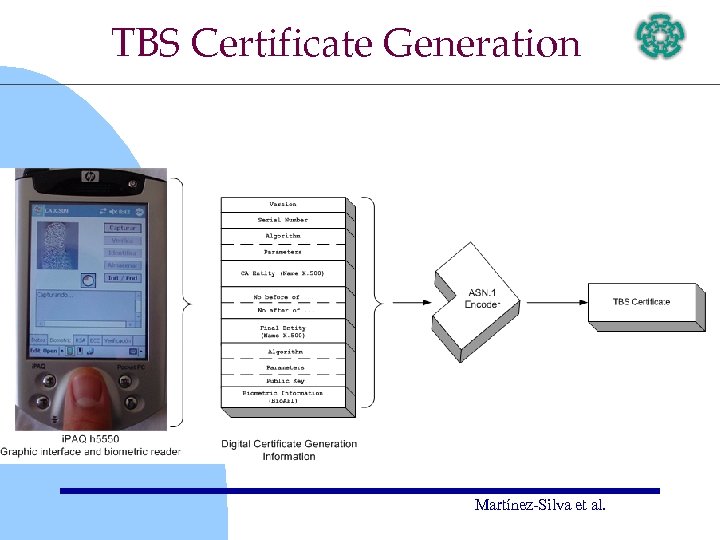 TBS Certificate Generation Martínez-Silva et al.
TBS Certificate Generation Martínez-Silva et al.
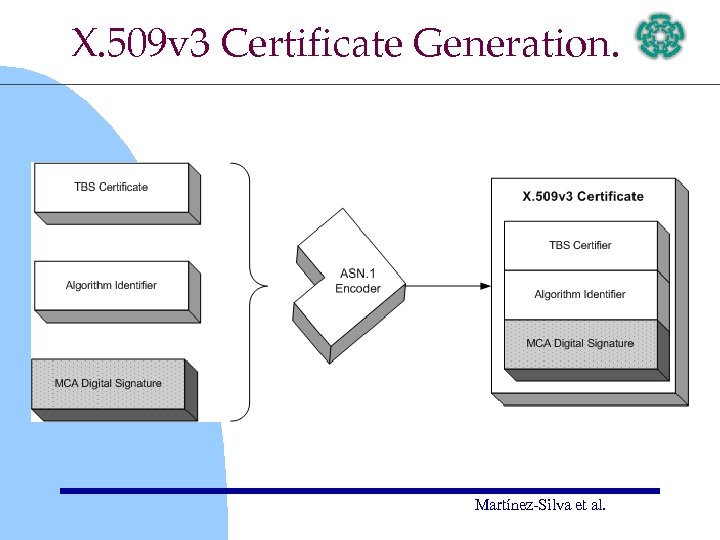 X. 509 v 3 Certificate Generation. Martínez-Silva et al.
X. 509 v 3 Certificate Generation. Martínez-Silva et al.
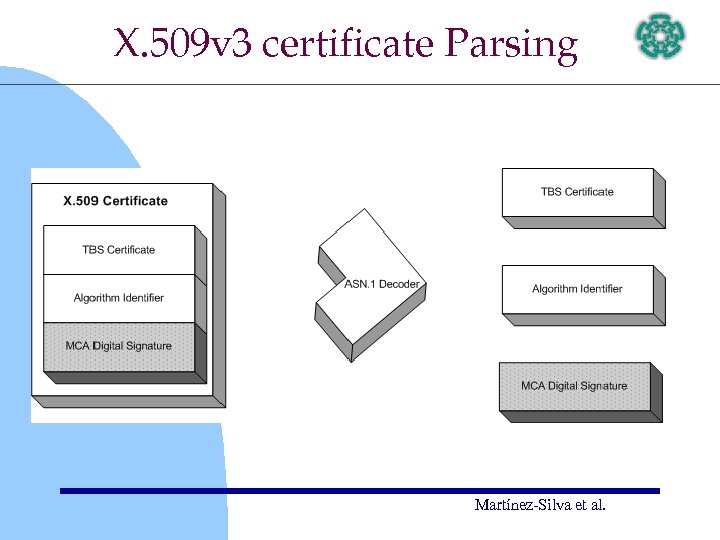 X. 509 v 3 certificate Parsing Martínez-Silva et al.
X. 509 v 3 certificate Parsing Martínez-Silva et al.
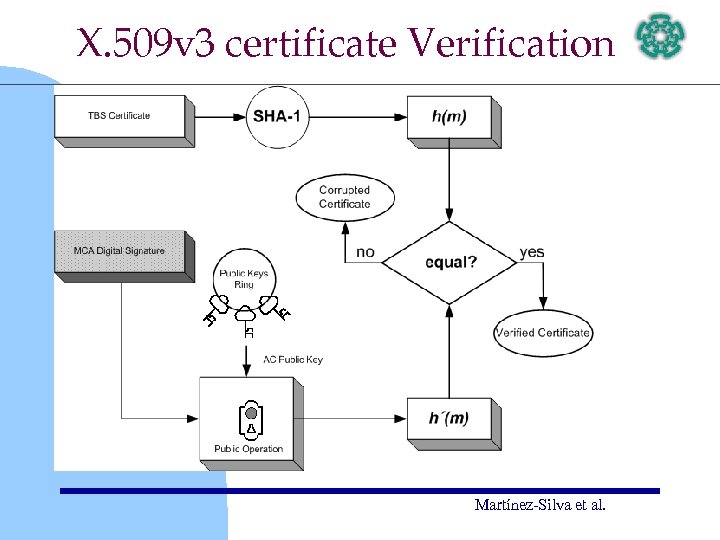 X. 509 v 3 certificate Verification Martínez-Silva et al.
X. 509 v 3 certificate Verification Martínez-Silva et al.
 Mobile Certification Authority Martínez-Silva et al.
Mobile Certification Authority Martínez-Silva et al.
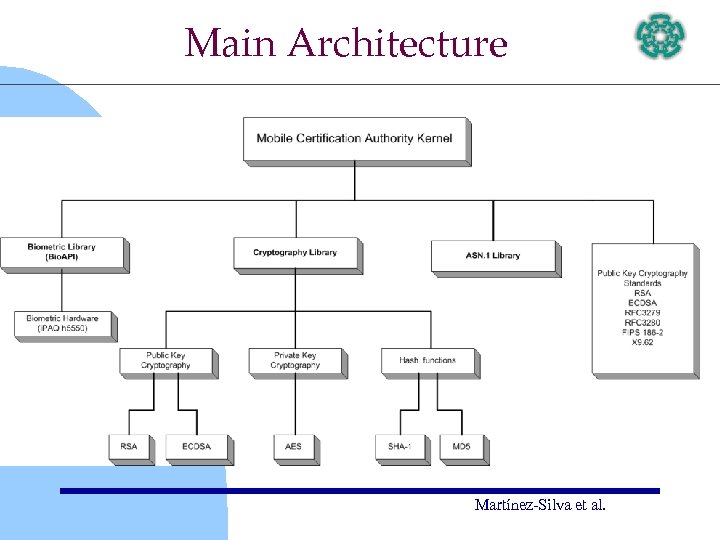 Main Architecture Martínez-Silva et al.
Main Architecture Martínez-Silva et al.
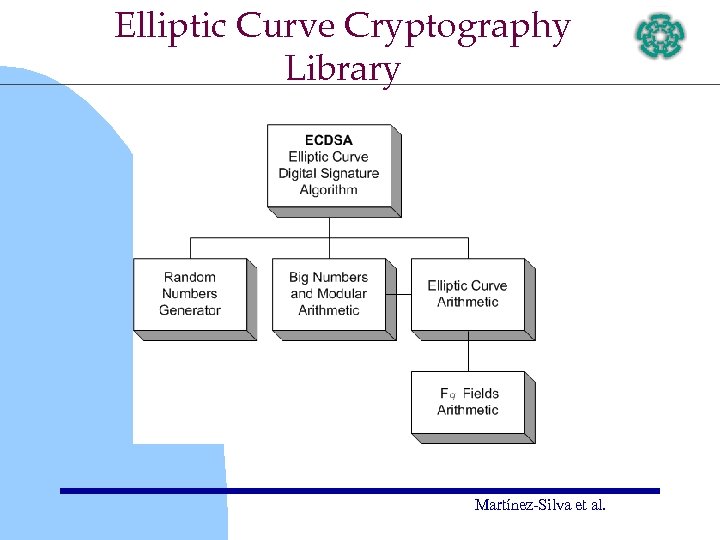 Elliptic Curve Cryptography Library Martínez-Silva et al.
Elliptic Curve Cryptography Library Martínez-Silva et al.
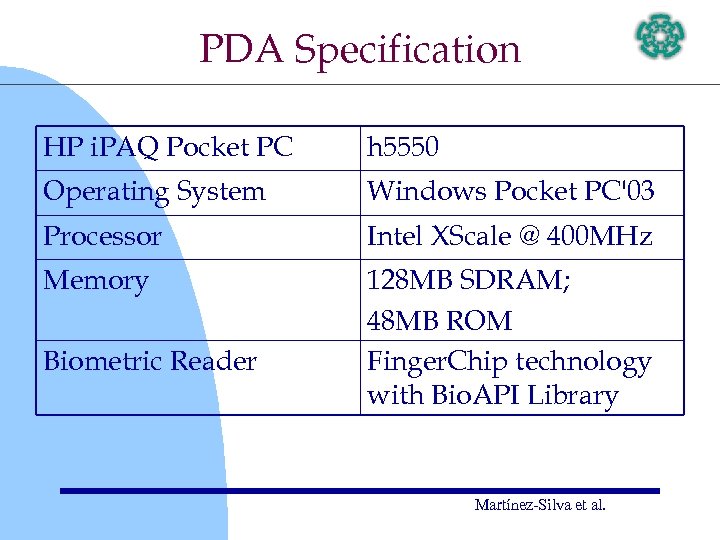 PDA Specification HP i. PAQ Pocket PC h 5550 Operating System Windows Pocket PC'03 Processor Intel XScale @ 400 MHz Memory 128 MB SDRAM; 48 MB ROM Finger. Chip technology with Bio. API Library Biometric Reader Martínez-Silva et al.
PDA Specification HP i. PAQ Pocket PC h 5550 Operating System Windows Pocket PC'03 Processor Intel XScale @ 400 MHz Memory 128 MB SDRAM; 48 MB ROM Finger. Chip technology with Bio. API Library Biometric Reader Martínez-Silva et al.
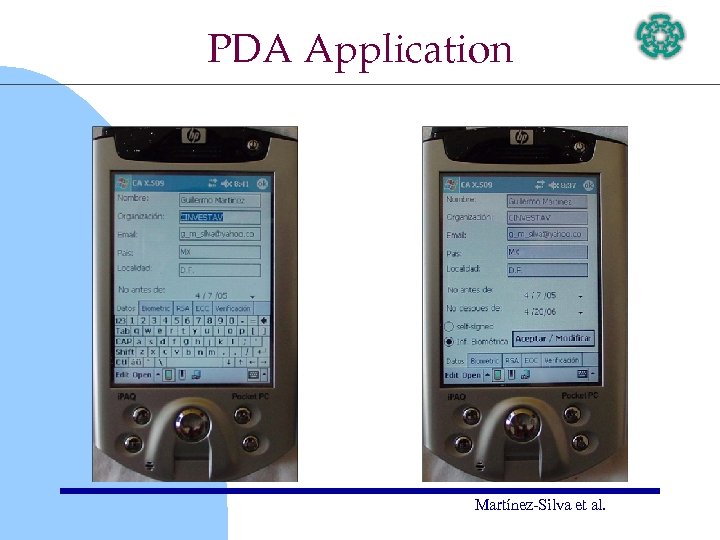 PDA Application Martínez-Silva et al.
PDA Application Martínez-Silva et al.
 Experimental Results Martínez-Silva et al.
Experimental Results Martínez-Silva et al.
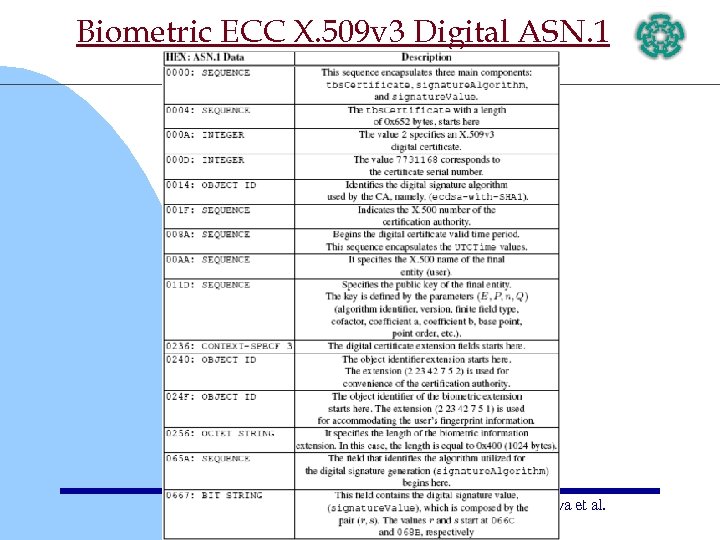 Biometric ECC X. 509 v 3 Digital ASN. 1 Martínez-Silva et al.
Biometric ECC X. 509 v 3 Digital ASN. 1 Martínez-Silva et al.
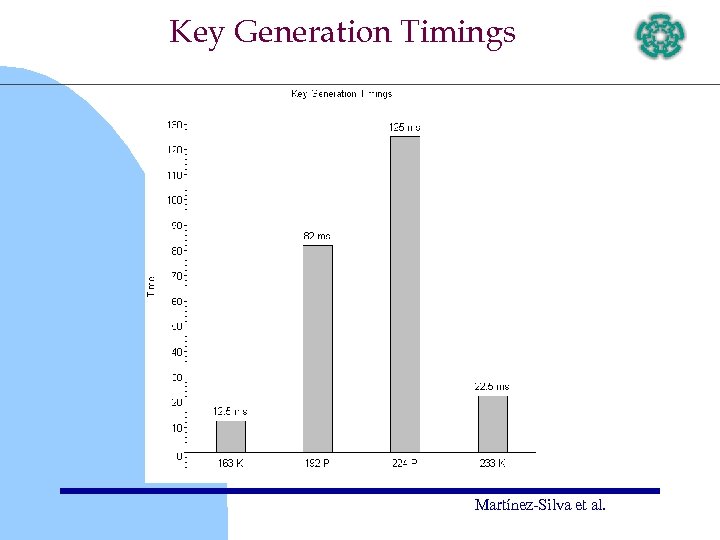 Key Generation Timings Martínez-Silva et al.
Key Generation Timings Martínez-Silva et al.
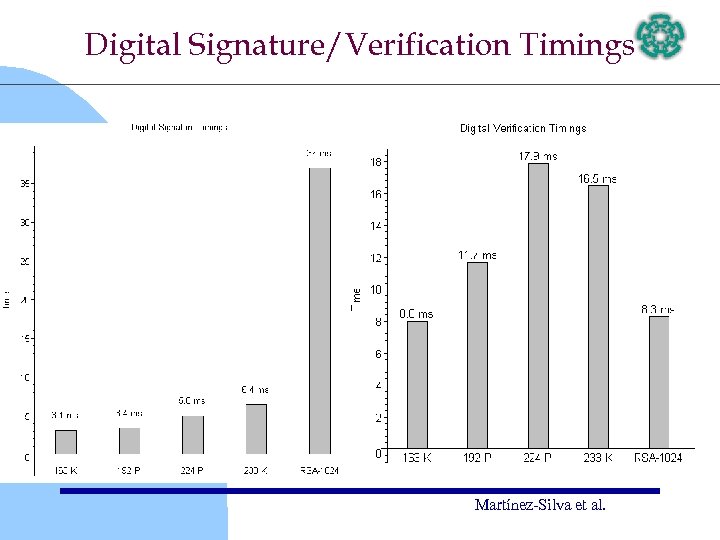 Digital Signature/Verification Timings Martínez-Silva et al.
Digital Signature/Verification Timings Martínez-Silva et al.
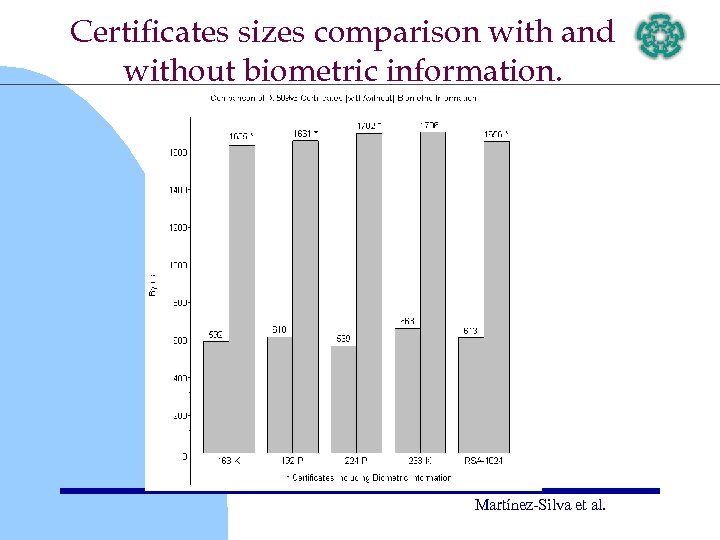 Certificates sizes comparison with and without biometric information. Martínez-Silva et al.
Certificates sizes comparison with and without biometric information. Martínez-Silva et al.
 Conclusions • fingerprint biometric information increases the size of all certificates considered by about 1 K byte, but there is room for improvements. • A rather surprising result was that the size difference between the RSA-based and ECDSAbased digital certificates is fairly small. • We confirmed that ECDSA is more efficient than RSA. Concretely, when working with constrained computational environments and/or wireless applications, the NIST-163 K-ECDSA appears to be the ideal selection. Martínez-Silva et al.
Conclusions • fingerprint biometric information increases the size of all certificates considered by about 1 K byte, but there is room for improvements. • A rather surprising result was that the size difference between the RSA-based and ECDSAbased digital certificates is fairly small. • We confirmed that ECDSA is more efficient than RSA. Concretely, when working with constrained computational environments and/or wireless applications, the NIST-163 K-ECDSA appears to be the ideal selection. Martínez-Silva et al.


