6964c87d9a65eb1801f0befb680e761d.ppt
- Количество слайдов: 52
Office of Security Education Refresher Briefing
Objectives • Annual requirement • Satisfactory knowledge of processing, handling and safeguarding of Classified National Security Information
Authorities • E. O. 12958, Classified National Security Information, as amended • 32 CFR Part 2001, Implementing Directive • DOO 20 -6, Director of Security; Security Manual, Section III www. osec. doc. gov/osy
Classified National Security Information is Official information that relates to the national defense or foreign relations of the United States, which has been deemed to require protection from unauthorized disclosure
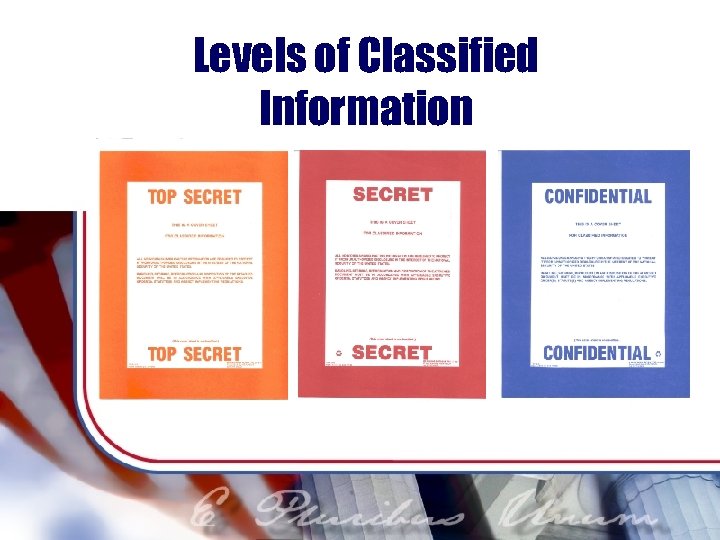
Levels of Classified Information
National Security Classify Reason Categories E. O. 12958 section 1. 4 Classified information must fall under one of the following categories: 1. 4 (a) Military plans, weapons systems, or operations; 1. 4 (b) Foreign government information; 1. 4 (c) Intelligence activities, sources or methods or cryptology; 1. 4 (d) Foreign relations or foreign activities of the United States including confidential sources;
National Security Classify Reason Categories E. O. 12958 section 1. 4 cont’d 1. 4. (e) Scientific, technological or economic matters relating to the national security; 1. 4 (f) United States Government programs for safeguarding nuclear materials or facilities; or 1. 4 (g) Vulnerabilities or capabilities of systems, installations, projects or plan relating to the national security. 1. 4 (h) weapons of mass destruction
Reasons NOT to classify Information may not be classified to: • Conceal violation of law, inefficiency, or administrative error. • Prevent embarrassment to a person, organization, or agency. • Restrain competition. • Prevent or delay the release of information that does not require protection in the interests of national security.
Sensitive Information marked “Sensitive” “For Official Use Only, ” “Sensitive But Unclassified, ” “Company Proprietary, ” etc. , is not classified Protection from unauthorized disclosure is required • Remember sensitive information should not be marked with classified stamps
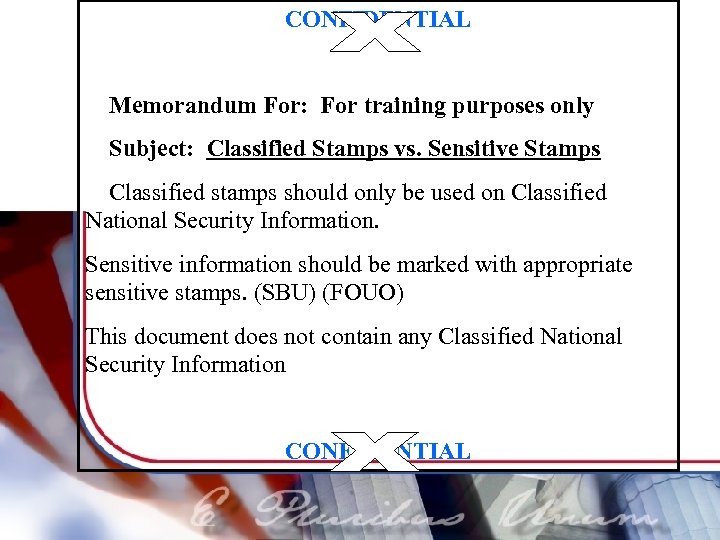
CONFIDENTIAL Memorandum For: For training purposes only Subject: Classified Stamps vs. Sensitive Stamps Classified stamps should only be used on Classified National Security Information. Sensitive information should be marked with appropriate sensitive stamps. (SBU) (FOUO) This document does not contain any Classified National Security Information CONFIDENTIAL
How is information classified? • Original Classification • Derivative Classification
Original Classification • An initial determination that information needs protection in the interests of national security • Must have written authority to originally classify information
Original Classification Authority (OCA) • Secretary of Commerce delegated authority from President, delegates within DOC • Secret is highest level of OCA in DOC
Derivative Classification • Incorporating, paraphrasing, restating, or generating in new form, information that is already classified • Written authority is not needed
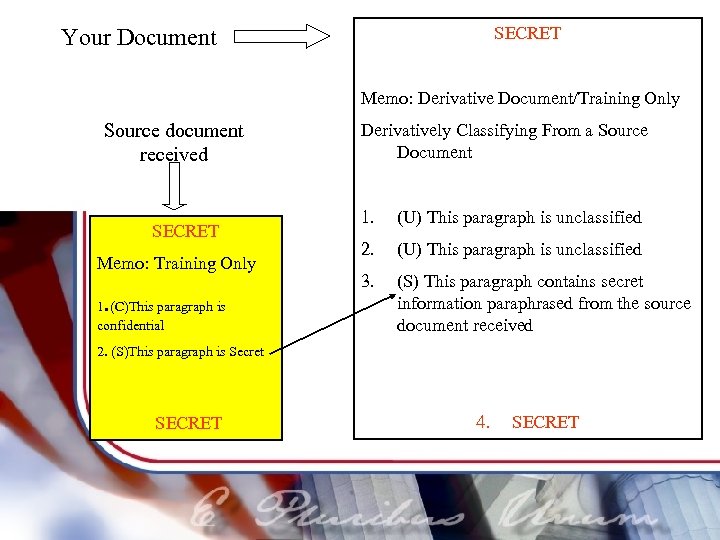
SECRET Your Document Memo: Derivative Document/Training Only Source document received SECRET Memo: Training Only . 1 (C)This paragraph is confidential Derivatively Classifying From a Source Document 1. (U) This paragraph is unclassified 2. (U) This paragraph is unclassified 3. (S) This paragraph contains secret information paraphrased from the source document received 2. (S)This paragraph is Secret SECRET 4. SECRET
Declassification • Only an Original Classification Authority can authorize declassification • Documents are generally marked for declassification within 10 years and can be up to 25 years
Summary • Please do not perform OCA unless you have written authority • Remember you do not need written authority to perform derivative classification • Please do not use classified stamps on sensitive information
Questions? Making Original and Derivative Classification decisions can be complicated. For additional training and/or questions, please contact the Office of Security’s Information Security Team at 202 -482 -8115.
Protecting Classified Information "We have an obligation to protect military, operational security, intelligence sources, and methods, and sensitive law enforcement investigations. " President George W. Bush, Memo to AG, FBI, CIA, State, Treasury, and Defense, October 5, 2001
Proper Security Practices üAccountability üProtecting Classified at work üTransmission üDestruction üReporting Requirements
Accountability of Classified Information • Required for all Classified National Security Information • Classified Document Control Record, form CD-481, for Top Secret and Secret • Record Top Secret and Secret documents in manual or electronic record system with classified control point or classified control officer
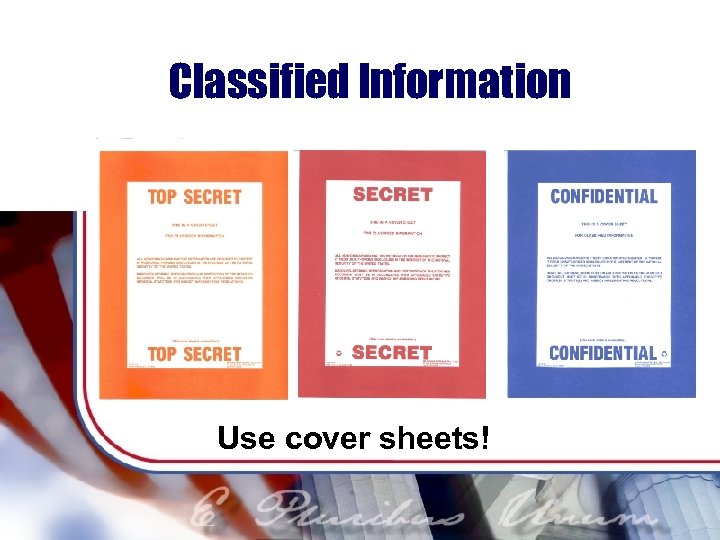
Classified Information Use cover sheets!
Classified Information Properly Marked • Paragraphs marked • Document marked at highest level contained • Cover, front and back, top and bottom • Classified by line • Declassification instructions
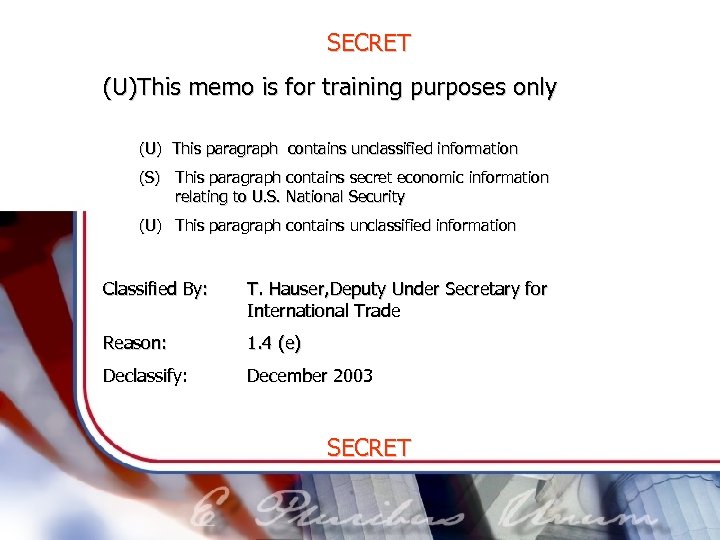
SECRET (U)This memo is for training purposes only (U) This paragraph contains unclassified information (S) This paragraph contains secret economic information relating to U. S. National Security (U) This paragraph contains unclassified information Classified By: T. Hauser, Deputy Under Secretary for International Trade Reason: 1. 4 (e) Declassify: December 2003 SECRET
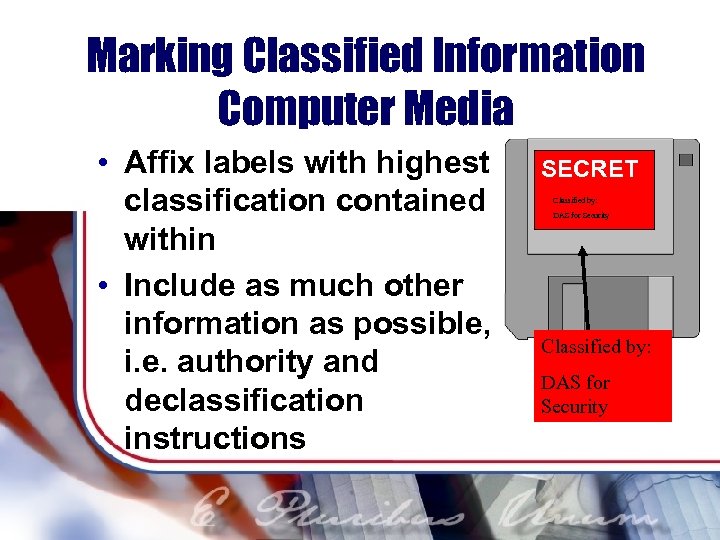
Marking Classified Information Computer Media • Affix labels with highest classification contained within • Include as much other information as possible, i. e. authority and declassification instructions SECRET Classified by: DAS for Security
Protecting Classified at Work • Classified information must be stored in a GSA-approved security container (safe) when not in use DO NOT STORE CLASSIFIED IN THE FOLLOWING: ØFiling Cabinets ØOver head Cabinets ØWindow Sills
Safe Combinations • Security container combinations are classified at the level of information in the safe • Memorize combinations; never write them down • Don’t share with anyone who does not need to know
Safe Combinations cont’d Change combinations when: • Security container is found open • Someone who has the combination leaves • Combination has been compromised • When the security container is taken out of service
Protecting Classified Information You must limit access to authorized persons by verifying: § § Identification Need to know Clearance Ability to protect
Protecting Classified NO unauthorized use of computers! § Systems must be certified and accredited PRIOR to classified use § See your Information Technology Security Officer
Transmitting Classified • Always use a STU-III* or STE** telephone for classified calls • Use compatible facsimile machines cleared for classified use for quick and secure document transmission *Secure Telephone Unit, Third Generation **Secure Telephone Equipment
Transmission: Double Wrapping • Must be done to prepare for hand carry, or US Postal • Affords 2 layers of protection • Protects against damage • Use opaque envelopes • Don’t forget a receipt • ü ü Inner wrapping information includes full address return address classification markings top/bottom and front and back ü return receipt
Transmission: Double Wrapping cont’d • Outer Wrapping ü full address of receiver ü full return address NO CLASSIFICATION MARKINGS!
Transmitting Classified Secret and Confidential only § Hand-carry § Approved courier § US Postal Service To transmit Top Secret in any manner, call your security officer
Reproduction of Classified • • Paper (photocopier) Electronically Use approved equipment only! Remember accountability, account for your copies!
Reproduction of Classified • Approved photocopiers: § Are in controlled environments § Are sanitized after classified copying § Serviced by cleared personnel or monitored service personnel • Contact your security officer if your copier jams while working with classified
Destruction at HCHB • • Shredding (approved cross-cut shredder) Classified waste “burn bags” Must be protected until turned-in! Turn-in: Tuesdays & Thursdays, Room B -509, 1 -3 p. m. • Don’t forget to record destruction! • For additional “burn bag” information contact the Security Service Center at 202 - 482 -8355

Most leaks result from: • • Negligence Carelessness Casual Conversations Open Sources
Reporting Requirements All cleared employees must report contact with a foreign national who: § Requests classified information § Wants more information than they need to know § Acts suspiciously Report incidents to your security officer immediately

Reporting Requirements All employees with Sensitive Compartmented Access must: • • Report Planned Travel Obtain travel briefing After-travel report The Office of Security’s Personnel Security Team at 202 -482 -8115
End of Day Security Checks • Check all areas to include safes, windows, desktops for classified • Complete the SF 701, Activity Security Checklist • Complete SF 702, Security Container Checklist • Turn on alarm if appropriate

Unauthorized Disclosure of Security Information ü SF 312 Non-Disclosure Agreement ü Security Infractions/Violations ü Penalties for Compromise
SF 312 Non-Disclosure Agreement • Binding contract • Lifetime obligation • You get access • Government gets your word to protect classified
Unauthorized Disclosure of Security Information • Security Infraction: occurs when classified information is not safeguarded but does not result in a compromise of material • Security Violation: occurs when classified information is not safeguarded and could result in a probable compromise of material • Compromise: An actual compromise of classified information, whether intentional or unintentional
Penalties for Compromising Classified Information (E. O. 12958) • • • Reprimand Suspension without pay Denial of access Removal Others in accordance with applicable laws and regulations
Title 50, USC, Sec. 783 War & National Defense Unauthorized Disclosure of Classified Information. It is unlawful to give classified information to an agent or representative of any foreign government that would result in harm to the National Security.
Title 18, USC, Sec. 794 Crimes & Criminal Procedures Sec. 794. Gathering or delivering defense information to aid of foreign government Delivery of defense information with intent or reason to believe that it is to be used to the injury of the United States or to the advantage of a foreign nation, shall be punished by death or by imprisonment for any term of years or for life. . . ,
Title 18, USC, Sec. 798 (1) Any person convicted of a violation of this section shall forfeit to the United States irrespective of any provision of State law (A) any property constituting, or derived from, any proceeds the person obtained, directly or indirectly, as the result of such violation; and (B) any of the person's property used, or intended to be used, in any manner or part, to commit, or to facilitate the commission of, such violation.

When You Depart Commerce You must: • Turn all classified material over to your classified control point • Contact your Security Officer for a debriefing • Turn in your ID, keys, and access cards
Your Security Officer • Be PROACTIVE • Request help • Report § Security violations § Suspected loss or compromise § Incidents or problems
Who is responsible for security?

YOU!
6964c87d9a65eb1801f0befb680e761d.ppt