8b74ca62bc33aabce0492f1f51573d20.ppt
- Количество слайдов: 48
 Nicolas T. Courtois - University College of London
Nicolas T. Courtois - University College of London
 Goals of Attackers
Goals of Attackers
 Comp. Sec COMPGA 01 Stage 1: Get to run some code (even without privileges). Stage 2: Gain admin access, usually by calling other local programs and exploiting their vulnerabilities. 3 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 Stage 1: Get to run some code (even without privileges). Stage 2: Gain admin access, usually by calling other local programs and exploiting their vulnerabilities. 3 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 • • 4 crash software (can be DOS) crash hardware (e. g. hard drive) get some data or side channels inject arbitrary code Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 • • 4 crash software (can be DOS) crash hardware (e. g. hard drive) get some data or side channels inject arbitrary code Nicolas T. Courtois, December 2009
 What’s Wrong?
What’s Wrong?
 Comp. Sec COMPGA 01 6 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 6 Nicolas T. Courtois, December 2009
 Vectors of Attack - Inputs
Vectors of Attack - Inputs
 Comp. Sec COMPGA 01 8 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 8 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 9 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 9 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 10 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 10 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 11 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 11 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 12 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 12 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 13 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 13 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 14 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 14 Nicolas T. Courtois, December 2009
 Buffer Overflow
Buffer Overflow
 Comp. Sec COMPGA 01 16 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 16 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 17 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 17 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 18 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 18 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 • C and C++ particularly dangerous – – Fast, therefore used in servers and all critical code (performance-wise and security-wise) allows arbitrary manipulation of pointers • 19 but not outside the virtual 2 Gbyte space allocated by the OS Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 • C and C++ particularly dangerous – – Fast, therefore used in servers and all critical code (performance-wise and security-wise) allows arbitrary manipulation of pointers • 19 but not outside the virtual 2 Gbyte space allocated by the OS Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 20 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 20 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 21 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 21 Nicolas T. Courtois, December 2009

 Comp. Sec COMPGA 01 23 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 23 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 24 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 24 Nicolas T. Courtois, December 2009
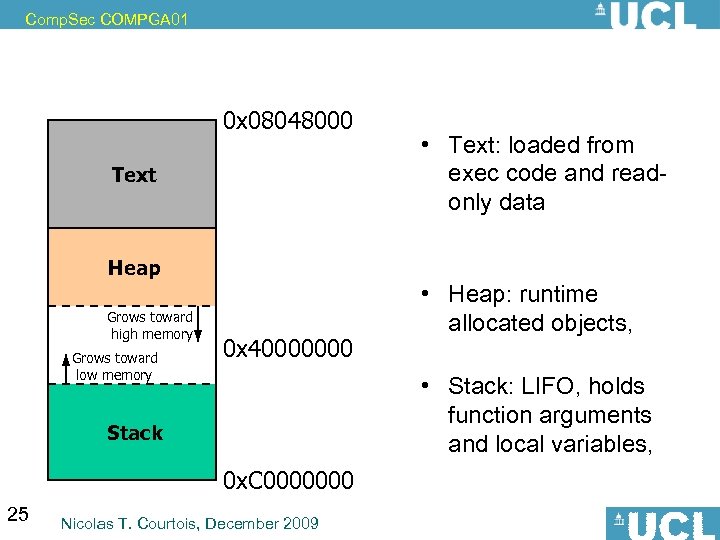 Comp. Sec COMPGA 01 0 x 08048000 Text Heap Grows toward high memory Grows toward low memory 0 x 40000000 Stack 0 x. C 0000000 25 Nicolas T. Courtois, December 2009 • Text: loaded from exec code and readonly data size fixed at compilation • Heap: runtime allocated objects, large (2 Gb) • Stack: LIFO, holds function arguments and local variables, small size (256 K)
Comp. Sec COMPGA 01 0 x 08048000 Text Heap Grows toward high memory Grows toward low memory 0 x 40000000 Stack 0 x. C 0000000 25 Nicolas T. Courtois, December 2009 • Text: loaded from exec code and readonly data size fixed at compilation • Heap: runtime allocated objects, large (2 Gb) • Stack: LIFO, holds function arguments and local variables, small size (256 K)
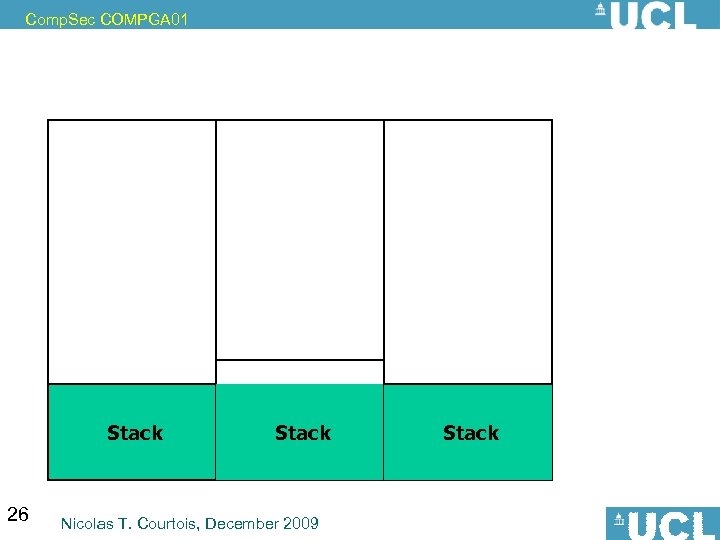 Comp. Sec COMPGA 01 Stack 26 Stack Nicolas T. Courtois, December 2009 Stack
Comp. Sec COMPGA 01 Stack 26 Stack Nicolas T. Courtois, December 2009 Stack
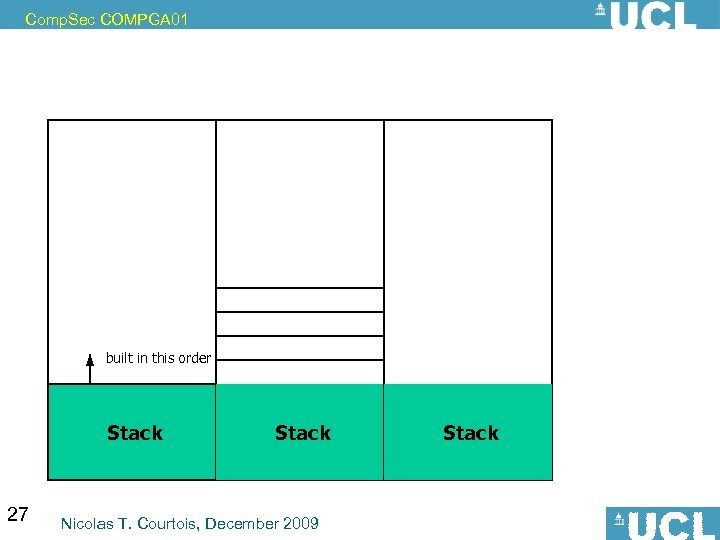 Comp. Sec COMPGA 01 built in this order Stack 27 Stack Nicolas T. Courtois, December 2009 Stack
Comp. Sec COMPGA 01 built in this order Stack 27 Stack Nicolas T. Courtois, December 2009 Stack
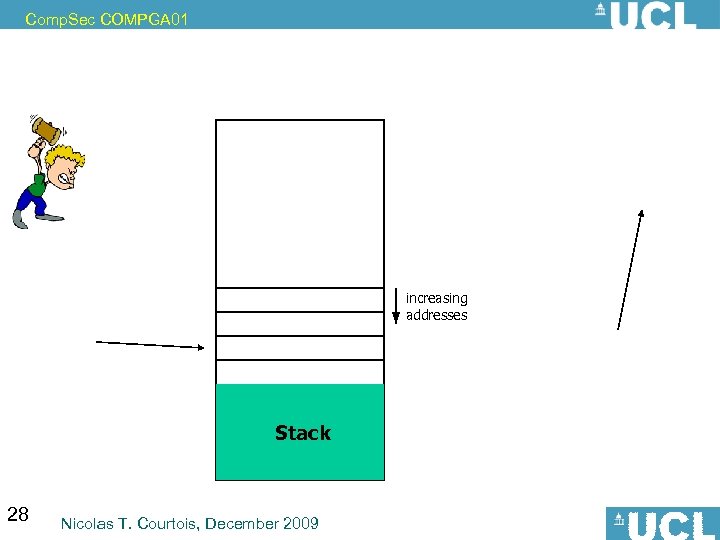 Comp. Sec COMPGA 01 increasing addresses Stack 28 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 increasing addresses Stack 28 Nicolas T. Courtois, December 2009
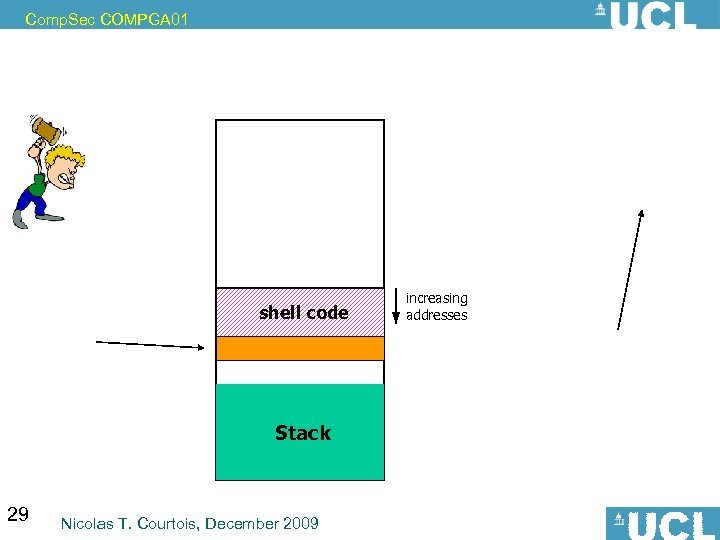 Comp. Sec COMPGA 01 shell code Stack 29 Nicolas T. Courtois, December 2009 increasing addresses
Comp. Sec COMPGA 01 shell code Stack 29 Nicolas T. Courtois, December 2009 increasing addresses
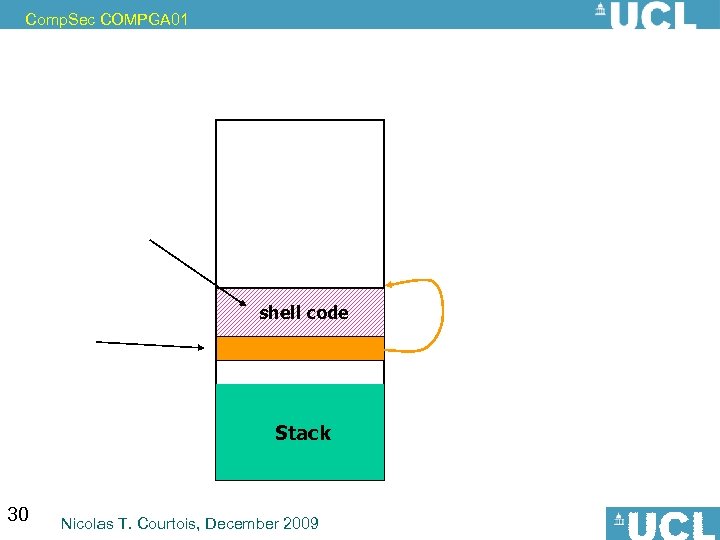 Comp. Sec COMPGA 01 shell code Stack 30 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 shell code Stack 30 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 up to very high, up to 100% (there are stable exploits, never fail and produce consistent results) 31 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 up to very high, up to 100% (there are stable exploits, never fail and produce consistent results) 31 Nicolas T. Courtois, December 2009
 What Hackers Do?
What Hackers Do?
 Can We Fix It?
Can We Fix It?
 Comp. Sec COMPGA 01 34 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 34 Nicolas T. Courtois, December 2009
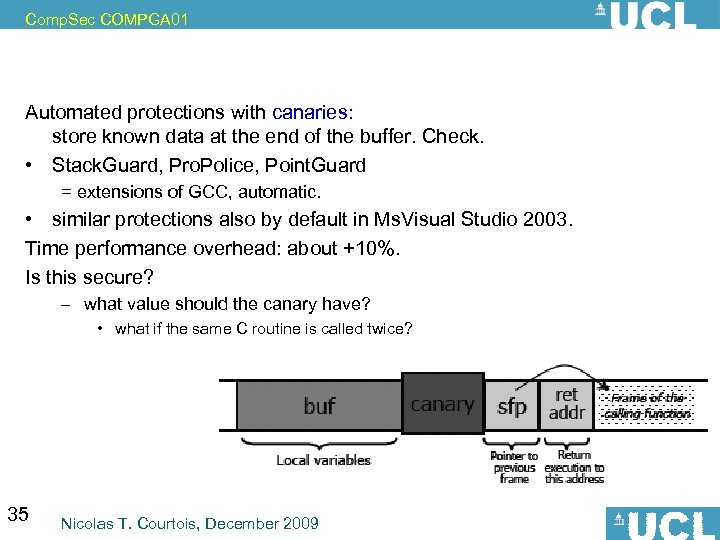 Comp. Sec COMPGA 01 Automated protections with canaries: store known data at the end of the buffer. Check. • Stack. Guard, Pro. Police, Point. Guard = extensions of GCC, automatic. • similar protections also by default in Ms. Visual Studio 2003. Time performance overhead: about +10%. Is this secure? – what value should the canary have? • what if the same C routine is called twice? 35 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 Automated protections with canaries: store known data at the end of the buffer. Check. • Stack. Guard, Pro. Police, Point. Guard = extensions of GCC, automatic. • similar protections also by default in Ms. Visual Studio 2003. Time performance overhead: about +10%. Is this secure? – what value should the canary have? • what if the same C routine is called twice? 35 Nicolas T. Courtois, December 2009
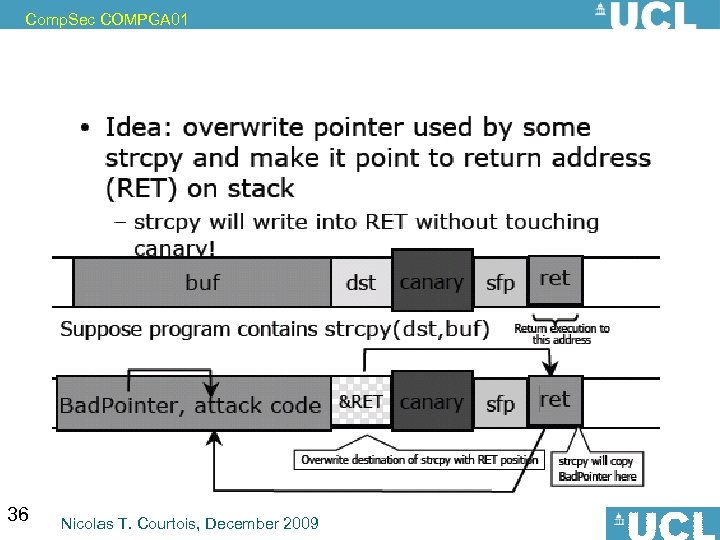 Comp. Sec COMPGA 01 36 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 36 Nicolas T. Courtois, December 2009
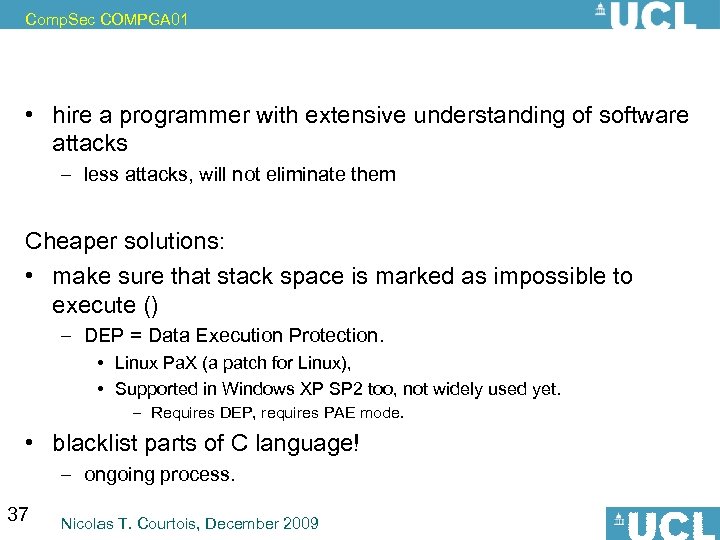 Comp. Sec COMPGA 01 • hire a programmer with extensive understanding of software attacks – less attacks, will not eliminate them Cheaper solutions: • make sure that stack space is marked as impossible to execute () – DEP = Data Execution Protection. • Linux Pa. X (a patch for Linux), • Supported in Windows XP SP 2 too, not widely used yet. – Requires DEP, requires PAE mode. • blacklist parts of C language! – ongoing process. 37 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 • hire a programmer with extensive understanding of software attacks – less attacks, will not eliminate them Cheaper solutions: • make sure that stack space is marked as impossible to execute () – DEP = Data Execution Protection. • Linux Pa. X (a patch for Linux), • Supported in Windows XP SP 2 too, not widely used yet. – Requires DEP, requires PAE mode. • blacklist parts of C language! – ongoing process. 37 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 38 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 38 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 39 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 39 Nicolas T. Courtois, December 2009
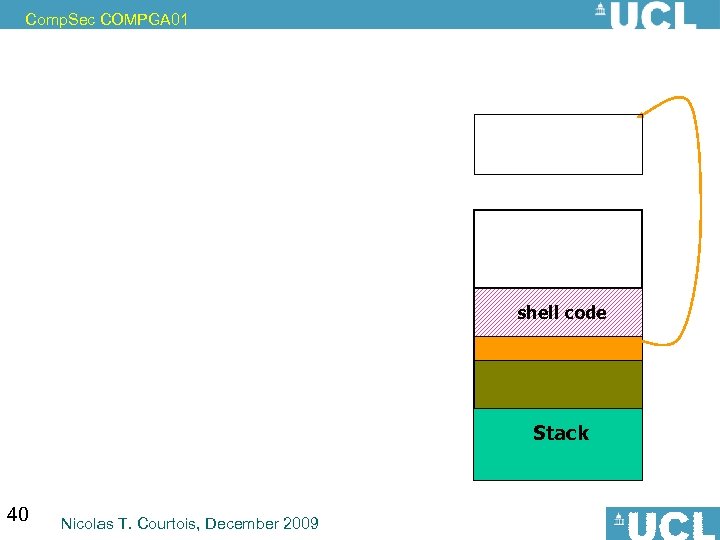 Comp. Sec COMPGA 01 shell code Stack 40 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 shell code Stack 40 Nicolas T. Courtois, December 2009
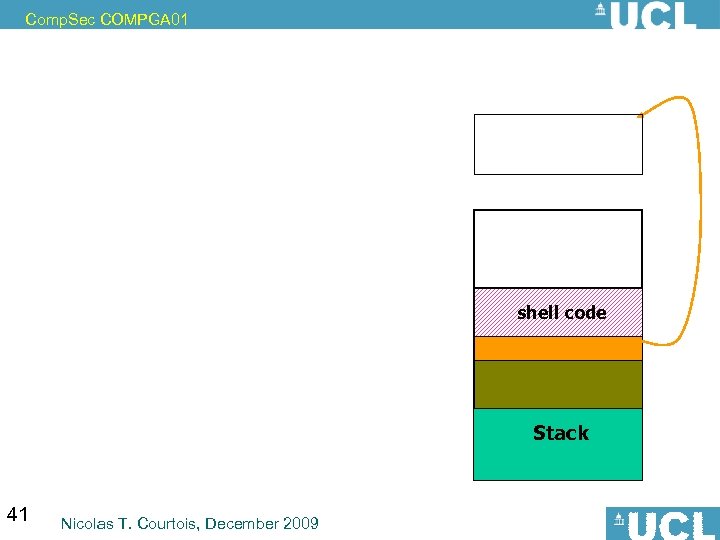 Comp. Sec COMPGA 01 shell code Stack 41 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 shell code Stack 41 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 42 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 42 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 43 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 43 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 44 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 44 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 45 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 45 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 46 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 46 Nicolas T. Courtois, December 2009
 Comp. Sec COMPGA 01 47 Nicolas T. Courtois, December 2009
Comp. Sec COMPGA 01 47 Nicolas T. Courtois, December 2009
 Heap Overflow not on the exam
Heap Overflow not on the exam


