d497455fcc9ad50e5d18c53c9401f3bd.ppt
- Количество слайдов: 102
New Jersey Department of Labor Unemployment Insurance Modernization Project Technical Architecture – NJ SUCCESS Revolutionizing Unemployment Insurance services in New Jersey 13 June 2003
Technical architecture for NJ SUCCESS New Jersey’s State Unemployment Compensation Claimant (and) Employer Service System
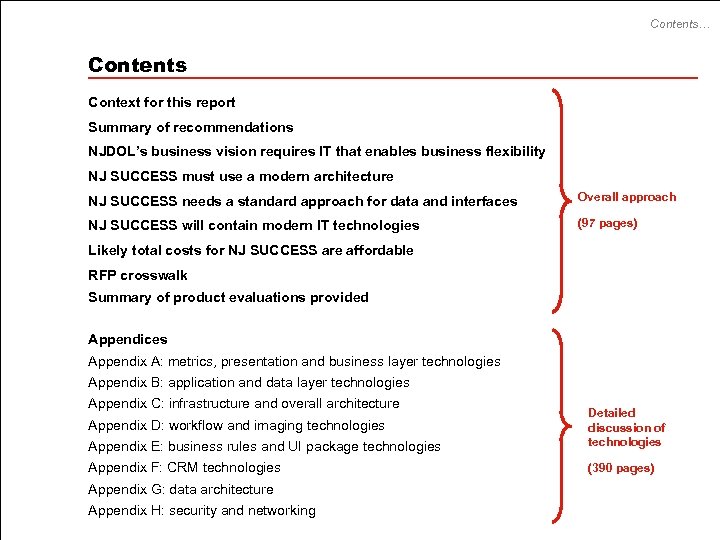
Contents… Contents Context for this report Summary of recommendations NJDOL’s business vision requires IT that enables business flexibility NJ SUCCESS must use a modern architecture NJ SUCCESS needs a standard approach for data and interfaces Overall approach NJ SUCCESS will contain modern IT technologies (97 pages) Likely total costs for NJ SUCCESS are affordable RFP crosswalk Summary of product evaluations provided Appendices Appendix A: metrics, presentation and business layer technologies Appendix B: application and data layer technologies Appendix C: infrastructure and overall architecture Appendix E: business rules and UI package technologies Detailed discussion of technologies Appendix F: CRM technologies (390 pages) Appendix D: workflow and imaging technologies Appendix G: data architecture Appendix H: security and networking
Context… Context of this report in the UI Modernization Program The Technical Architecture defines the future technical environment for NJ SUCCESS, providing capability of delivering UI’s requirements from the Business Process Conceptual Design stage. 1. Baseline Description – ‘as-is’ analysis of current business and technology environment in UI – reviewing parallel initiatives 2. Business Process Conceptual Design – ‘to-be’ analysis of desired final future business environment 3. Technical Architecture – This report ‘to-be’ analysis of desired final future technical environment 4. Strategic Plan – desired implementation and migration approach – including any intermediate stages on the way to the final technical architecture – revisiting parallel initiatives
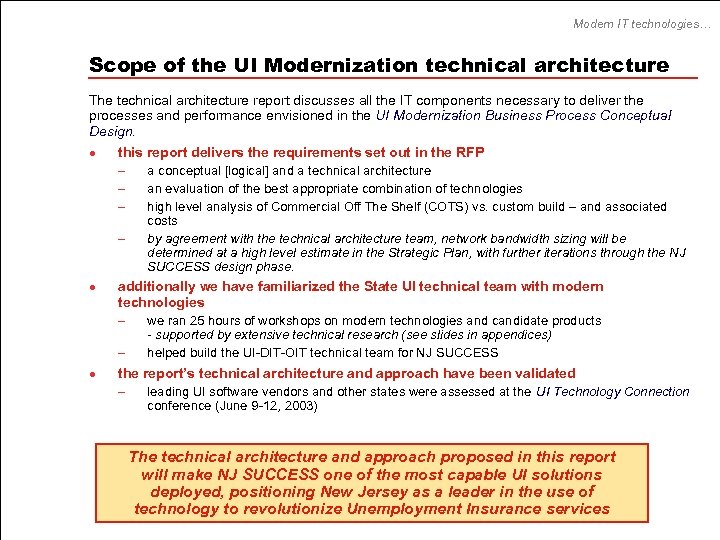
Modern IT technologies… Scope of the UI Modernization technical architecture The technical architecture report discusses all the IT components necessary to deliver the processes and performance envisioned in the UI Modernization Business Process Conceptual Design. l this report delivers the requirements set out in the RFP – a conceptual [logical] and a technical architecture – an evaluation of the best appropriate combination of technologies – high level analysis of Commercial Off The Shelf (COTS) vs. custom build – and associated – l additionally we have familiarized the State UI technical team with modern technologies – we ran 25 hours of workshops on modern technologies and candidate products – l costs by agreement with the technical architecture team, network bandwidth sizing will be determined at a high level estimate in the Strategic Plan, with further iterations through the NJ SUCCESS design phase. - supported by extensive technical research (see slides in appendices) helped build the UI-DIT-OIT technical team for NJ SUCCESS the report’s technical architecture and approach have been validated – leading UI software vendors and other states were assessed at the UI Technology Connection conference (June 9 -12, 2003) The technical architecture and approach proposed in this report will make NJ SUCCESS one of the most capable UI solutions deployed, positioning New Jersey as a leader in the use of technology to revolutionize Unemployment Insurance services
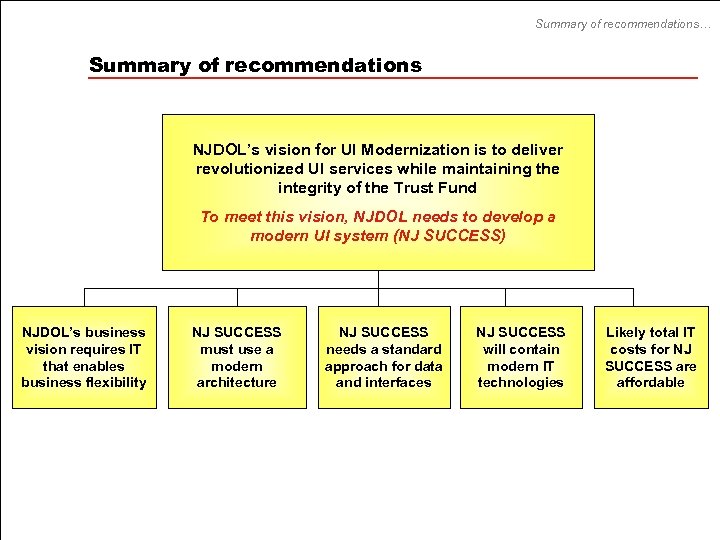
Summary of recommendations… Summary of recommendations NJDOL’s vision for UI Modernization is to deliver revolutionized UI services while maintaining the integrity of the Trust Fund To meet this vision, NJDOL needs to develop a modern UI system (NJ SUCCESS) NJDOL’s business vision requires IT that enables business flexibility NJ SUCCESS must use a modern architecture NJ SUCCESS needs a standard approach for data and interfaces NJ SUCCESS will contain modern IT technologies Likely total IT costs for NJ SUCCESS are affordable
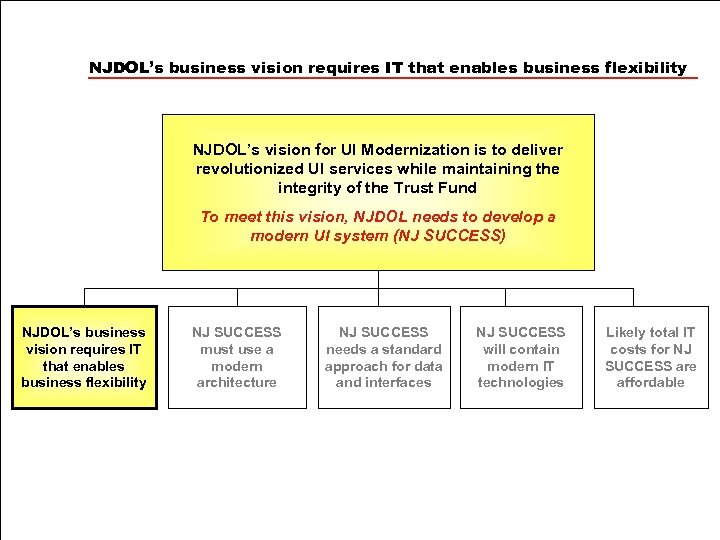
NJDOL’s business vision requires IT that enables business flexibility NJDOL’s vision for UI Modernization is to deliver revolutionized UI services while maintaining the integrity of the Trust Fund To meet this vision, NJDOL needs to develop a modern UI system (NJ SUCCESS) NJDOL’s business vision requires IT that enables business flexibility NJ SUCCESS must use a modern architecture NJ SUCCESS needs a standard approach for data and interfaces NJ SUCCESS will contain modern IT technologies Likely total IT costs for NJ SUCCESS are affordable
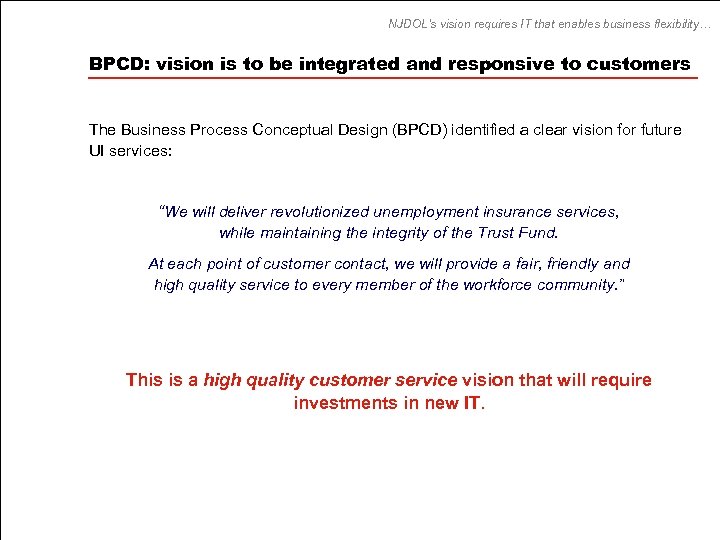
NJDOL’s vision requires IT that enables business flexibility… BPCD: vision is to be integrated and responsive to customers The Business Process Conceptual Design (BPCD) identified a clear vision for future UI services: “We will deliver revolutionized unemployment insurance services, while maintaining the integrity of the Trust Fund. At each point of customer contact, we will provide a fair, friendly and high quality service to every member of the workforce community. ” This is a high quality customer service vision that will require investments in new IT.
Requirements from business process conceptual design phase BPCD: business principles have technical implications The Business Conceptual Design identified business principles that had strong technical implications: l customers will be able to access a holistic UI electronic case file remotely l prevent incorrect payments, before they happen l maintain equally the integrity of systems, processes and finances l there must be ‘one system’ and uniform, easy to access data l get accurate data from the start – and reuse it to avoid redundancy …therefore information needs to be captured and stored electronically l l l optimize staff resources by balancing workload across the state use tools effectively to enable performance management, development and policy improvement use workflow and case management to optimize end-to-end case processing … therefore processes need to be measured and managed l automate the repetitive tasks, thereby freeing up staff to help our customers l encourage remote self-service (via phone, web or email) l streamline communications using modern tools and encourage customers to use the same tools, particularly employers … therefore efficiency improvements need improved automation
Requirements from business conceptual design phase These business design principles translate into functionality typical of modern systems Information needs to be captured electronically implies… l digital imaging and recording l requirement for robust electronic forms l enable e. Communications with all customers and partners l requirement to handle an electronic case file l be easily integrated with workforce partners’ applications and packages l advanced configurable reporting and business intelligence capabilities are needed to support operations management, research, Federal reporting and strategic planning Processes need to be measured and managed implies… l possess multi-level fine granular role based security, with detailed audit trail l should have built in / integrated control and monitoring tools – for processes and systems l requirement for workflow, business rules engine, customer relationship management, content management, imaging and document management functionality Efficiency improvements need improved automation implies… l business logic and workflow must be easily configurable – and not reliant on a technical specialist l be easily expandable – for example, easy to add a new benefit program l should be scalable, robust and flexible to adjust to variations in workload l services should be available to customers and staff, 24 x 7 l a common look and feel for all modules, easy navigation and rich functionality
Requirements from business conceptual design phase BPCD: principles for the implementation phase In addition, the State has defined some fundamental implementation principles that impact the technical architecture and implementation approach selected: l strategic ownership must remain with the State – the new system must not tie NJDOL to a vendor • – l l l i. e. NJ SUCCESS must be an ‘open’ architecture the end-to-end solution must be easily maintainable, in-house implementation must be phased, constituting a series of ‘building block’ projects that individually deliver value to the business modernization must be achieved within reasonable cost throughout the design and delivery of new processes and system tools, we must maintain the integrity of services - benefits, system, data, trust fund
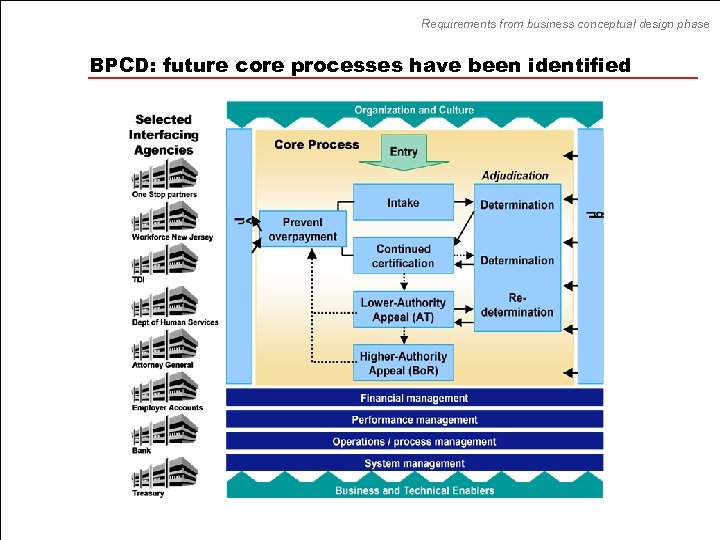
Requirements from business conceptual design phase BPCD: future core processes have been identified
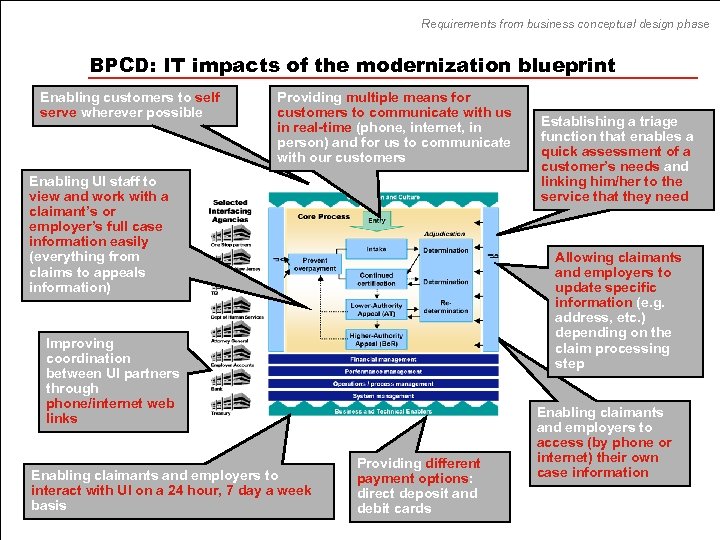
Requirements from business conceptual design phase BPCD: IT impacts of the modernization blueprint Enabling customers to self serve wherever possible Providing multiple means for customers to communicate with us in real-time (phone, internet, in person) and for us to communicate with our customers Enabling UI staff to view and work with a claimant’s or employer’s full case information easily (everything from claims to appeals information) Allowing claimants and employers to update specific information (e. g. address, etc. ) depending on the claim processing step Improving coordination between UI partners through phone/internet web links Enabling claimants and employers to interact with UI on a 24 hour, 7 day a week basis Establishing a triage function that enables a quick assessment of a customer’s needs and linking him/her to the service that they need Providing different payment options: direct deposit and debit cards Enabling claimants and employers to access (by phone or internet) their own case information
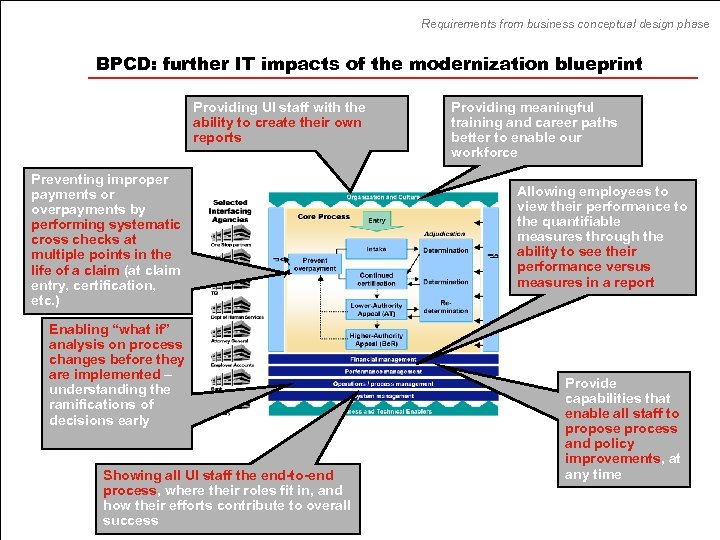
Requirements from business conceptual design phase BPCD: further IT impacts of the modernization blueprint Providing UI staff with the ability to create their own reports Preventing improper payments or overpayments by performing systematic cross checks at multiple points in the life of a claim (at claim entry, certification, etc. ) Enabling “what if” analysis on process changes before they are implemented – understanding the ramifications of decisions early Showing all UI staff the end-to-end process, where their roles fit in, and how their efforts contribute to overall success Providing meaningful training and career paths better to enable our workforce Allowing employees to view their performance to the quantifiable measures through the ability to see their performance versus measures in a report Provide capabilities that enable all staff to propose process and policy improvements, at any time
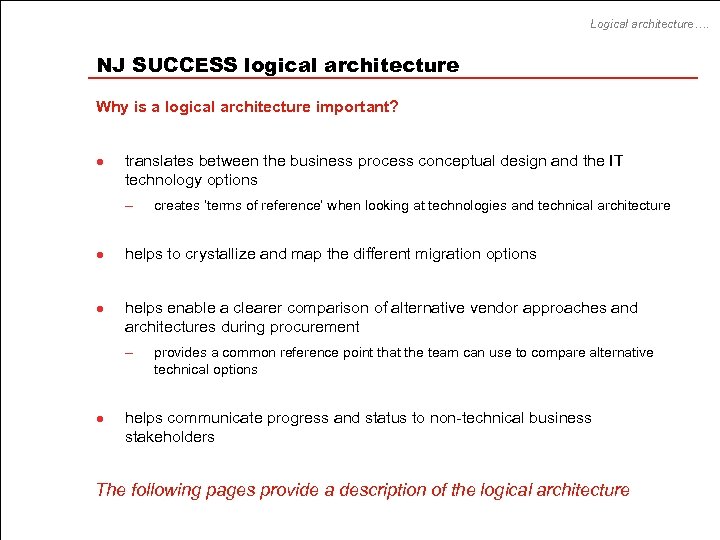
Logical architecture…. NJ SUCCESS logical architecture Why is a logical architecture important? l translates between the business process conceptual design and the IT technology options – l l helps to crystallize and map the different migration options helps enable a clearer comparison of alternative vendor approaches and architectures during procurement – l creates ‘terms of reference’ when looking at technologies and technical architecture provides a common reference point that the team can use to compare alternative technical options helps communicate progress and status to non-technical business stakeholders The following pages provide a description of the logical architecture
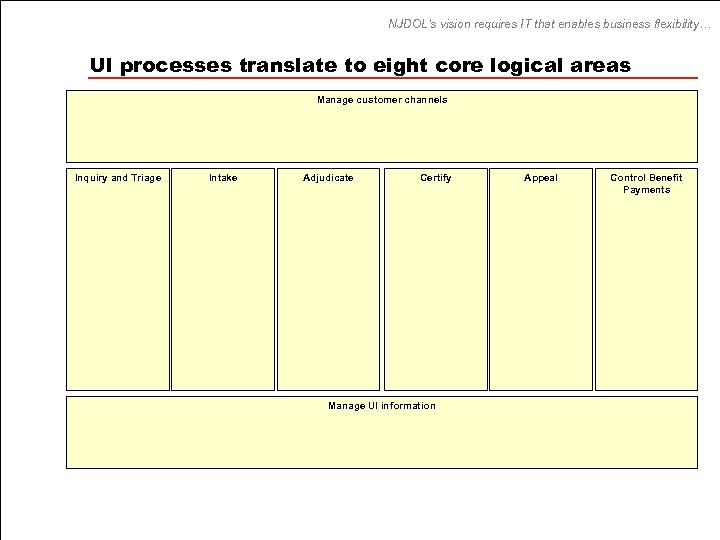
NJDOL’s vision requires IT that enables business flexibility… UI processes translate to eight core logical areas Manage customer channels Inquiry and Triage Intake Adjudicate Certify Manage UI information Appeal Control Benefit Payments
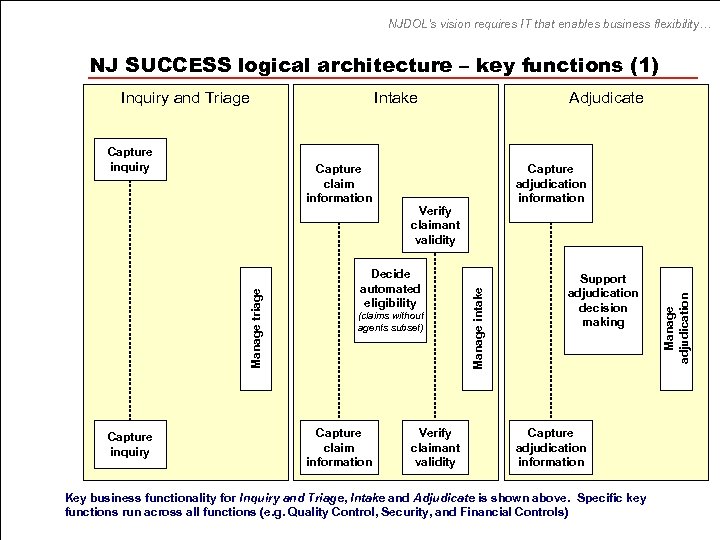
NJDOL’s vision requires IT that enables business flexibility… NJ SUCCESS logical architecture – key functions (1) Manage triage Capture claim information Capture inquiry Capture adjudication information Verify claimant validity Decide automated eligibility (claims without agents subset) Capture claim information Adjudicate Verify claimant validity Support adjudication decision making Capture adjudication information Key business functionality for Inquiry and Triage, Intake and Adjudicate is shown above. Specific key functions run across all functions (e. g. Quality Control, Security, and Financial Controls) Manage adjudication Capture inquiry Intake Manage intake Inquiry and Triage
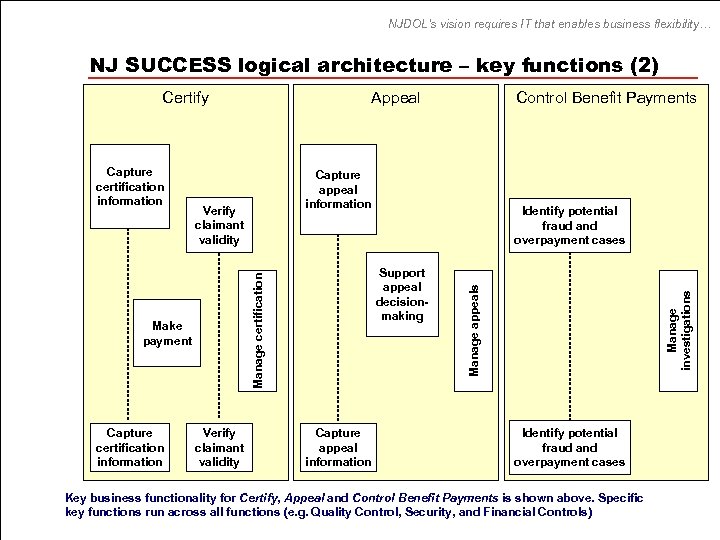
NJDOL’s vision requires IT that enables business flexibility… NJ SUCCESS logical architecture – key functions (2) Capture certification information Verify claimant validity Identify potential fraud and overpayment cases Support appeal decisionmaking Capture appeal information Manage appeals Verify claimant validity Make payment Control Benefit Payments Capture appeal information Manage certification Capture certification information Appeal Manage investigations Certify Identify potential fraud and overpayment cases Key business functionality for Certify, Appeal and Control Benefit Payments is shown above. Specific key functions run across all functions (e. g. Quality Control, Security, and Financial Controls)
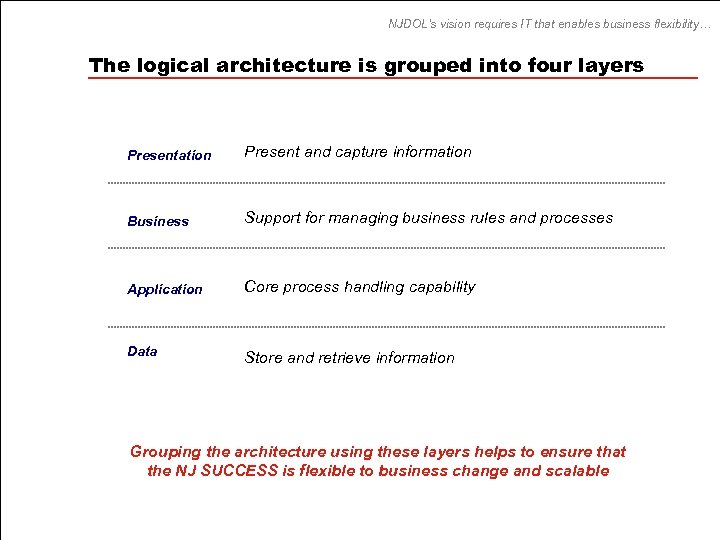
NJDOL’s vision requires IT that enables business flexibility… The logical architecture is grouped into four layers Presentation Present and capture information Business Support for managing business rules and processes Application Core process handling capability Data Store and retrieve information Grouping the architecture using these layers helps to ensure that the NJ SUCCESS is flexible to business change and scalable
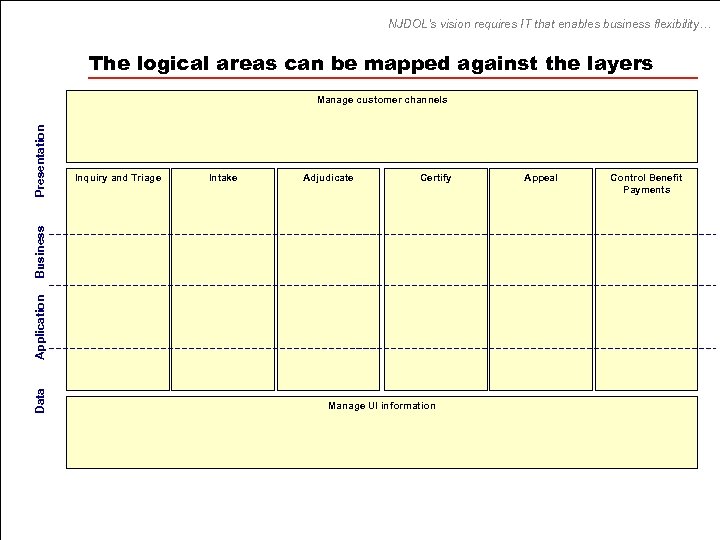
NJDOL’s vision requires IT that enables business flexibility… The logical areas can be mapped against the layers Inquiry and Triage Intake Adjudicate Certify Data Application Business Presentation Manage customer channels Manage UI information Appeal Control Benefit Payments
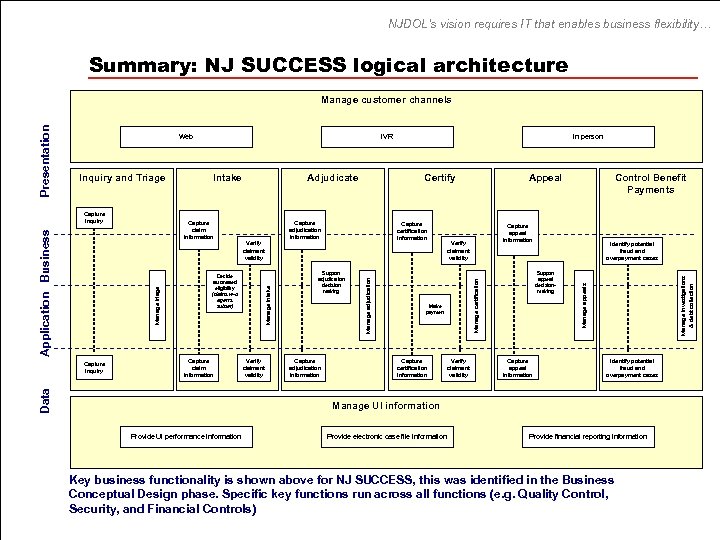
NJDOL’s vision requires IT that enables business flexibility… Summary: NJ SUCCESS logical architecture Capture claim information Verify claimant validity Capture certification information Support adjudication decision making Capture adjudication information Verify claimant validity Control Benefit Payments Capture appeal information Verify claimant validity Make payment Capture certification information Appeal Identify potential fraud and overpayment cases Support appeal decisionmaking Capture appeal information Manage investigations & debt collection Certify Capture adjudication information Verify claimant validity Decide automated eligibility (claims w-o agents subset) Data Capture inquiry Adjudicate In person Manage certification Capture claim information Manage triage Application Business Capture inquiry Intake Manage adjudication Inquiry and Triage IVR Manage appeals Web Manage intake Presentation Manage customer channels Identify potential fraud and overpayment cases Manage UI information Provide UI performance information Provide electronic case file information Provide financial reporting information Key business functionality is shown above for NJ SUCCESS, this was identified in the Business Conceptual Design phase. Specific key functions run across all functions (e. g. Quality Control, Security, and Financial Controls)
NJDOL’s vision requires IT that enables business flexibility… How will NJ SUCCESS support key scenarios? Five sample scenarios have been mapped to NJ SUCCESS’s logical architecture to illustrate how NJ SUCCESS will support the redesigned UI processes: Scenario 1: A straightforward new UI claim Scenario 2: Certification for a continued claim Scenario 3: Employer appeals determination Scenario 4: Potentially fraudulent new claim Scenario 5: Controlling benefit payments
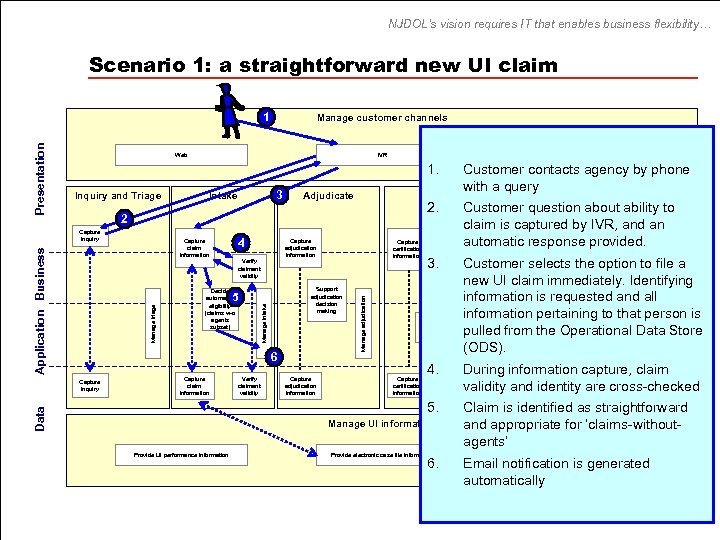
NJDOL’s vision requires IT that enables business flexibility… Scenario 1: a straightforward new UI claim Manage customer channels IVR In person 1. 3 Intake Adjudicate Certify 2. 2 Verify claimant validity Decide automated eligibility (claims w-o agents subset) 5 Manage triage Capture adjudication information Support adjudication decision making 6 Capture claim information Verify claimant validity Capture adjudication information Verify Identify potential 3. claimant. Customer selects the option to file a fraud and validity overpayment cases new UI claim immediately. Identifying Support informationappealrequested and all is decisionmaking information pertaining to that person is Make payment pulled from the Operational Data Store (ODS). Capture certification information 4. 5. Data Capture inquiry Capture certification information Manage UI information Provide UI performance information Control Benefit about Payments ability to Customer question claim is captured by IVR, and an Capture automatic response provided. appeal Manage certification 4 Capture claim information Manage adjudication Application Business Capture inquiry Appeal Provide electronic case file information 6. Manage investigations Inquiry and Triage Customer contacts agency by phone with a query Manage appeals Web Manage intake Presentation 1 During information capture, claim Capture Identify potential appeal fraud and validity and identity are cross-checked information overpayment cases Verify claimant validity Claim is identified as straightforward and appropriate for ‘claims-withoutagents’ Provide financial reporting information Email notification is generated automatically
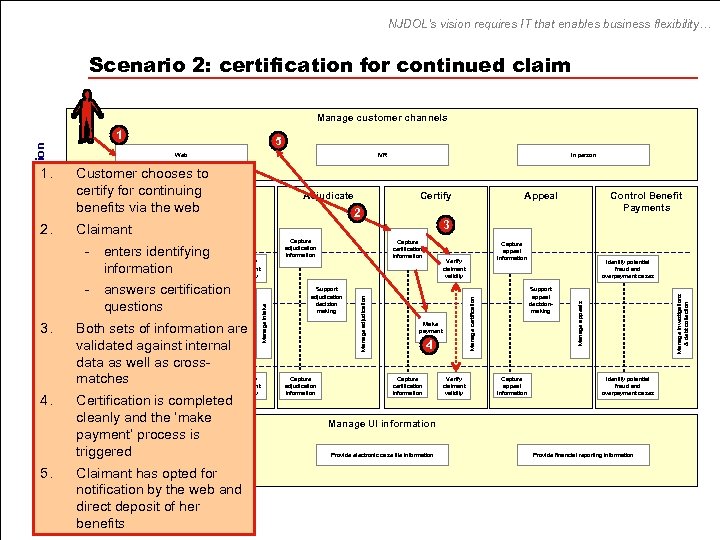
NJDOL’s vision requires IT that enables business flexibility… Scenario 2: certification for continued claim Manage customer channels Data 4. 5. Certify 2 - enters identifying information Verify claimant validity Decide - answers certification automated eligibility questions (claims w-o agents subset) Both sets of information are validated against internal data as well as cross. Capture Verify matches Capture claimant inquiry information Capture adjudication information Certification is completed cleanly and the ‘make payment’ process is triggered Provide UI performance information validity Claimant has opted for notification by the web and direct deposit of her benefits Capture certification information Support adjudication decision making Capture adjudication information Capture appeal information Verify claimant validity Make payment 4 Capture certification information Verify claimant validity Identify potential fraud and overpayment cases Support appeal decisionmaking Capture appeal information Manage investigations & debt collection Capture claim information Control Benefit Payments 3 Claimant Capture inquiry Appeal Manage appeals Adjudicate In person Manage certification 3. Customer chooses to certify for continuing Intake Inquiry and Triage benefits via the web Manage adjudication Application Business 2. IVR Manage intake 1. 5 Web Manage triage Presentation 1 Identify potential fraud and overpayment cases Manage UI information Provide electronic case file information Provide financial reporting information
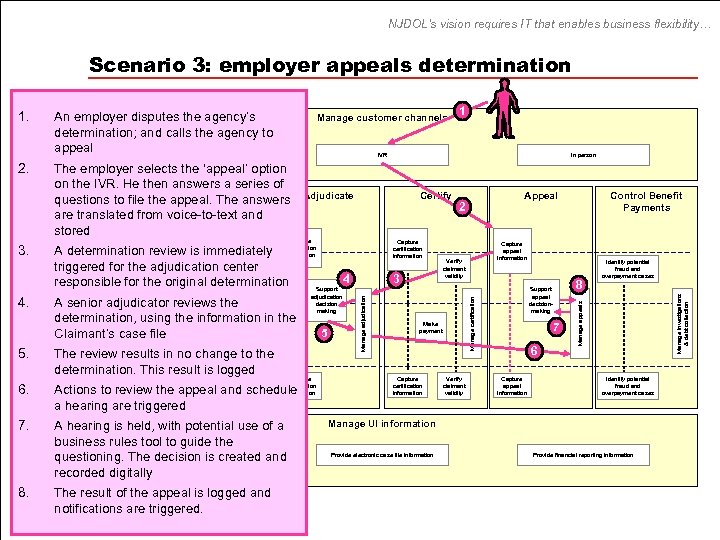
NJDOL’s vision requires IT that enables business flexibility… Scenario 3: employer appeals determination 8. Data 7. The review results in no change to the determination. This result is logged Capture Verify adjudication decision making Capture claimant adjudication inquiry Actions to review the appeal andvalidity schedule information a hearing are triggered A hearing is held, with potential use of a business rules tool to guide the Provide UI performance information questioning. The decision is created and recorded digitally The result of the appeal is logged and notifications are triggered. 5 3 Capture certification information Capture appeal information Verify claimant validity Make payment Verify claimant validity Control Benefit Payments 8 Support appeal decisionmaking 7 6 Capture appeal information Identify potential fraud and overpayment cases Manage investigations & debt collection Capture certification information Appeal 2 Manage appeals Certify Capture A senior adjudicator reviews the determination, using the information in the Claimant’s case file Capture 6. Adjudicate A determination review claim immediately adjudication is information Verify claimant triggered for the adjudication center validity 4 responsible for the original determination Support Decide automated eligibility (claims w-o agents subset) In person Manage certification Capture 1 IVR Manage adjudication 5. Manage customer channels The employer selects the ‘appeal’ option on the IVR. He then answers a series of Inquiry to Triage Intake questions andfile the appeal. The answers are translated from voice-to-text and Capture stored inquiry Manage intake 4. An employer disputes the agency’s determination; and calls the agency to appeal Web Manage triage 3. Application Business 2. Presentation 1. Identify potential fraud and overpayment cases Manage UI information Provide electronic case file information Provide financial reporting information
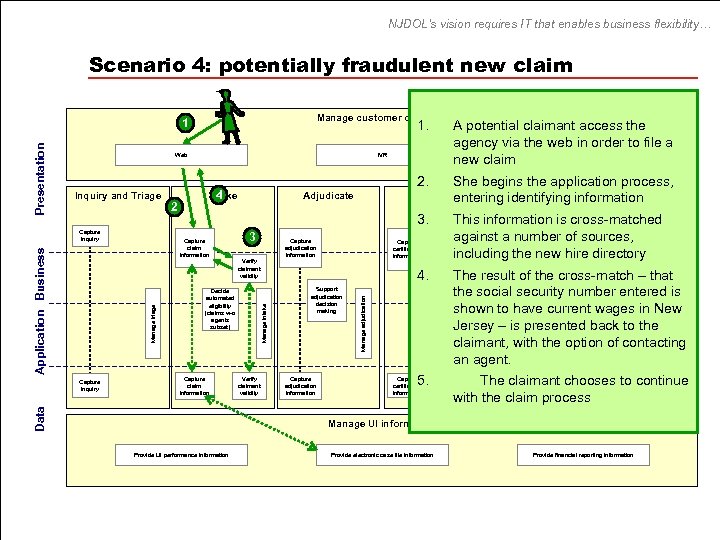
NJDOL’s vision requires IT that enables business flexibility… Scenario 4: potentially fraudulent new claim Manage customer channels 1. Certify entering Verify claimant validity Capture certification information 4. Support adjudication decision making Capture adjudication information Make payment 5. Capture certification information claimant validity fraud and overpayment cases The result of the cross-match – that Support the social security number entered is appeal decisionmaking shown to have current wages in New Jersey – is presented back to the claimant, with the option of contacting an agent. Capture Identify Theappeal claimant choosesfraudpotential toand continue information overpayment cases with the claim process Verify claimant validity Manage UI information Provide UI performance information Provide electronic case file information Manage investigations Verify claimant validity Decide automated eligibility (claims w-o agents subset) Capture claim information Capture adjudication information Manage appeals 3 Payments This information is cross-matched against Capture a number of sources, appeal including the new hire directory information Verify Identify potential Manage certification Adjudicate 3. Data Capture inquiry Intake 4 Capture claim information Manage triage Application Business Capture inquiry 2 She begins the application process, Appeal Control identifying information Benefit IVR Manage adjudication Inquiry and Triage A potential claimant access the agency via the web in order to file a In person new claim 2. Web Manage intake Presentation 1 Provide financial reporting information
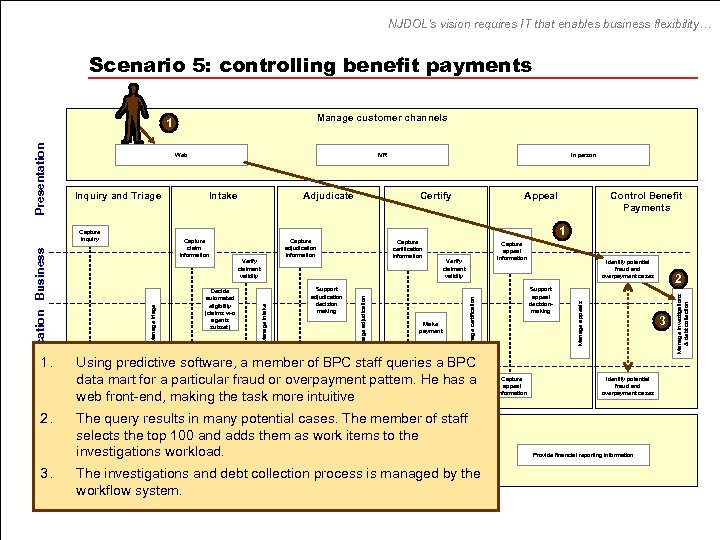
NJDOL’s vision requires IT that enables business flexibility… Scenario 5: controlling benefit payments Manage customer channels Web Data 1. 2. 3. Certify Capture certification information Capture appeal information Verify claimant validity Make payment Using predictive software, a member of BPC staff queries a BPC Capture Verify data mart for a particular fraud or adjudication overpayment pattern. He has a Capture claimant certification claimant inquiry information validity web front-end, making the task more intuitive The query results in many potential cases. The UI information staff Manage member of selects the top 100 and adds them as work items to the investigations performance information Provide UI workload. Provide electronic case file information The investigations and debt collection process is managed by the workflow system. Identify potential fraud and overpayment cases Support appeal decisionmaking Capture appeal information 2 3 Identify potential fraud and overpayment cases Provide financial reporting information Manage investigations & debt collection Support adjudication decision making Control Benefit Payments 1 Capture adjudication information Verify claimant validity Appeal Manage appeals Decide automated eligibility (claims w-o agents subset) Adjudicate In person Manage certification Capture claim information Manage triage Application Business Capture inquiry Intake Manage adjudication Inquiry and Triage IVR Manage intake Presentation 1
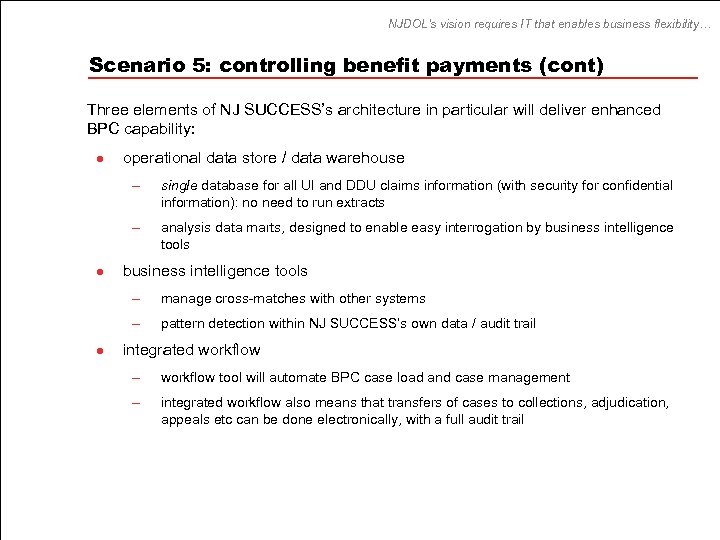
NJDOL’s vision requires IT that enables business flexibility… Scenario 5: controlling benefit payments (cont) Three elements of NJ SUCCESS’s architecture in particular will deliver enhanced BPC capability: l operational data store / data warehouse – – l single database for all UI and DDU claims information (with security for confidential information): no need to run extracts analysis data marts, designed to enable easy interrogation by business intelligence tools – – l manage cross-matches with other systems pattern detection within NJ SUCCESS’s own data / audit trail integrated workflow – workflow tool will automate BPC case load and case management – integrated workflow also means that transfers of cases to collections, adjudication, appeals etc can be done electronically, with a full audit trail
NJDOL’s vision requires IT that enables business flexibility… Increased flexibility for managing the organization Management will derive most immediate benefit from these technologies: l operational data store / data warehouse – – a real-time ‘performance dashboard’ is possible for operational managers – l analysis data marts enable managers to quickly view reports and perform ‘ad-hoc’ analyses on any discrepancies (see slide 51 for details on data marts) storage of a full audit trail (covering accounting, data, system security) will enhance the integrity of UI integrated workflow – – l workflow management tools will enable managers at all levels to monitor operations performance more immediately – and see the impact of adjustments fast end-to-end workflow reporting will provide management with an ability to manage workloads across the process chain integrated customer channel management – this will enable multiple customer channels to be managed in an integrated manner – updates and new services can more easily be communicated across all channels – this enables the future introduction of ‘contact’ centers - providing customer service contacts across all channels from one center
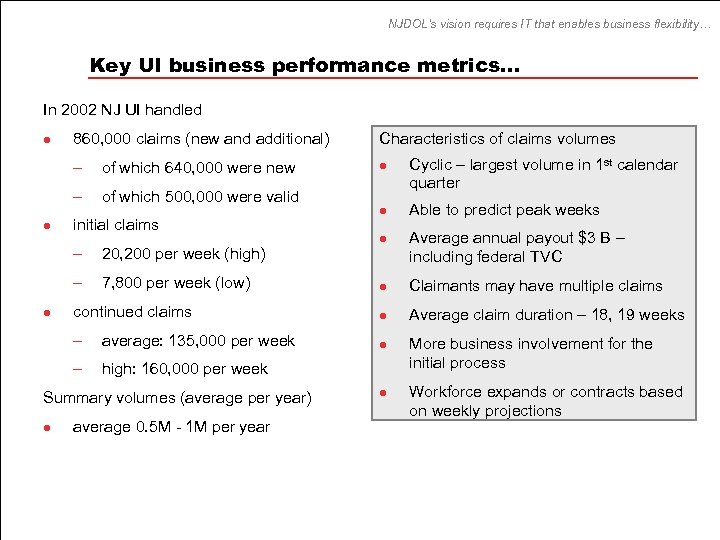
NJDOL’s vision requires IT that enables business flexibility… Key UI business performance metrics… In 2002 NJ UI handled Characteristics of claims volumes of which 640, 000 were new l – l 860, 000 claims (new and additional) – l of which 500, 000 were valid initial claims – 20, 200 per week (high) – 7, 800 per week (low) l l Cyclic – largest volume in 1 st calendar quarter Able to predict peak weeks Average annual payout $3 B – including federal TVC Claimants may have multiple claims continued claims l Average claim duration – 18, 19 weeks – average: 135, 000 per week l – l l high: 160, 000 per week Summary volumes (average per year) l average 0. 5 M - 1 M per year l More business involvement for the initial process Workforce expands or contracts based on weekly projections
NJDOL’s vision requires IT that enables business flexibility… Key UI business performance metrics (continued) In 2002 NJ UI handled l claims have increased over past two years – – l 2002 was 23% more than 2001 was 27% more than 2000 average benefit payout has increased – – l 2001 reached $2. 1 Billion 2002 reached $3 Billion phone calls (claims, pends, and inquiries): – 2002 - 1, 722, 044 calls received – 2002 - – 2003 (1/03 – 4/03) - 753, 087 calls received – 2003 (1/03 – 4/03) - 383, 063 calls answered – 52% 963, 339 calls answered – 58% of total * Note this was information for the three RCCS – the assumption is that there are more calls trying to contact the offices than can be handled
NJDOL’s vision requires IT that enables business flexibility… …NJ SUCCESS performance requirements On the basis of the claims volumes for 2002, the technical architecture team agreed that the following broad assumptions were reasonable to inform this high level technical architecture: l size to handle a 30% increase in claims volume above 2002 figures – l assume peak volumes are 200% of 2002 volumes – l max of 1. 1 M initial claims (both new and additional claims) per year weekly peak of 44 K initial claims, 350 K continued claims assume peak hourly volume of 15, 000 for continued claims and the ability to handle 225 calls at any one time
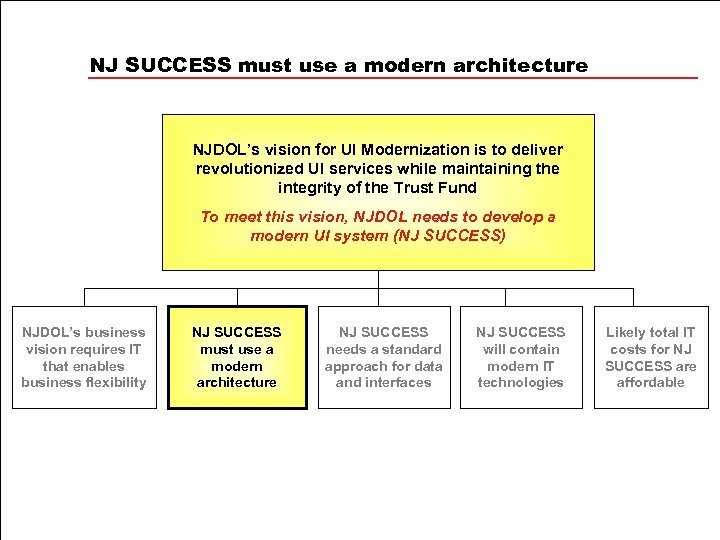
NJ SUCCESS must use a modern architecture NJDOL’s vision for UI Modernization is to deliver revolutionized UI services while maintaining the integrity of the Trust Fund To meet this vision, NJDOL needs to develop a modern UI system (NJ SUCCESS) NJDOL’s business vision requires IT that enables business flexibility NJ SUCCESS must use a modern architecture NJ SUCCESS needs a standard approach for data and interfaces NJ SUCCESS will contain modern IT technologies Likely total IT costs for NJ SUCCESS are affordable
NJ SUCCESS must use a modern architecture… NJ SUCCESS candidate architecture options - general The technical architecture team, including representatives from NJDOL UI, DIT and the State OIT, collectively considered potential suppliers and candidate architecture options. The next three slides summarize these options and the conclusions reached by the team for each option.
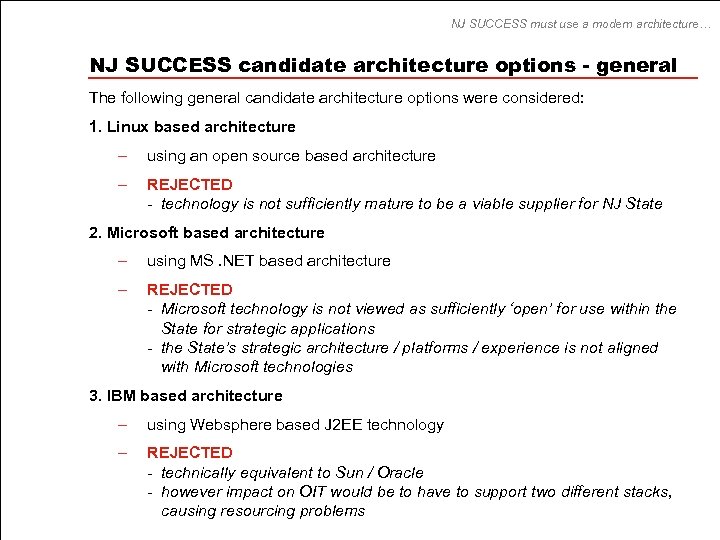
NJ SUCCESS must use a modern architecture… NJ SUCCESS candidate architecture options - general The following general candidate architecture options were considered: 1. Linux based architecture – using an open source based architecture – REJECTED - technology is not sufficiently mature to be a viable supplier for NJ State 2. Microsoft based architecture – using MS. NET based architecture – REJECTED - Microsoft technology is not viewed as sufficiently ‘open’ for use within the State for strategic applications - the State’s strategic architecture / platforms / experience is not aligned with Microsoft technologies 3. IBM based architecture – using Websphere based J 2 EE technology – REJECTED - technically equivalent to Sun / Oracle - however impact on OIT would be to have to support two different stacks, causing resourcing problems
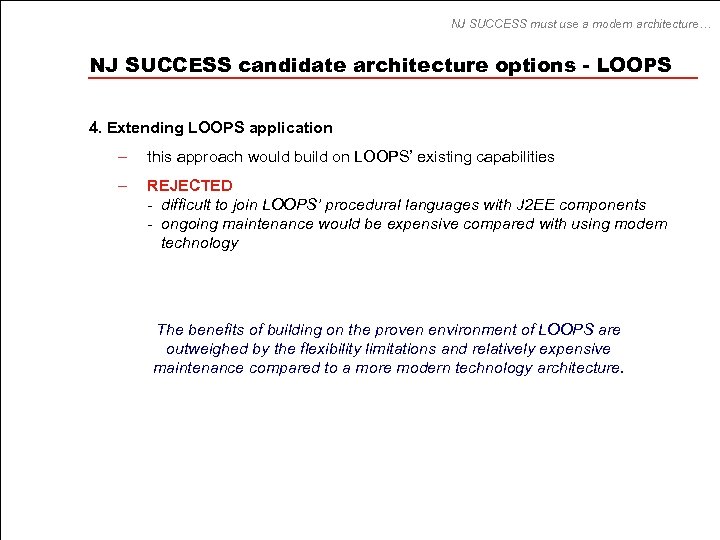
NJ SUCCESS must use a modern architecture… NJ SUCCESS candidate architecture options - LOOPS 4. Extending LOOPS application – this approach would build on LOOPS’ existing capabilities – REJECTED - difficult to join LOOPS’ procedural languages with J 2 EE components - ongoing maintenance would be expensive compared with using modern technology The benefits of building on the proven environment of LOOPS are outweighed by the flexibility limitations and relatively expensive maintenance compared to a more modern technology architecture.
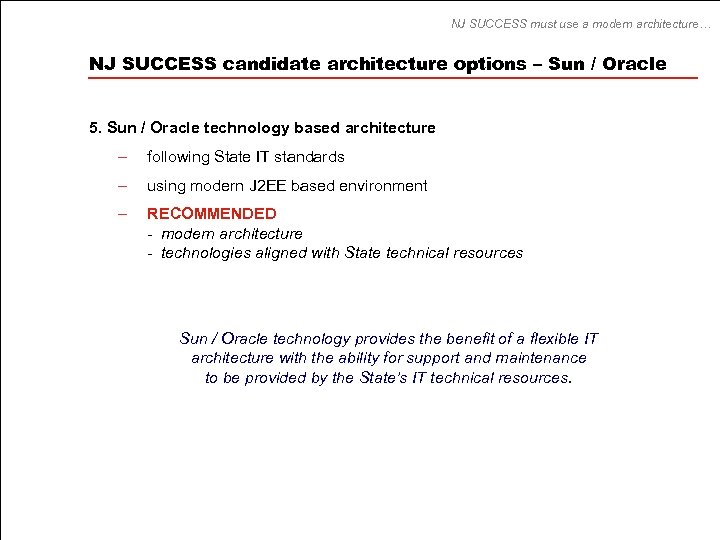
NJ SUCCESS must use a modern architecture… NJ SUCCESS candidate architecture options – Sun / Oracle 5. Sun / Oracle technology based architecture – following State IT standards – using modern J 2 EE based environment – RECOMMENDED - modern architecture - technologies aligned with State technical resources Sun / Oracle technology provides the benefit of a flexible IT architecture with the ability for support and maintenance to be provided by the State’s IT technical resources.
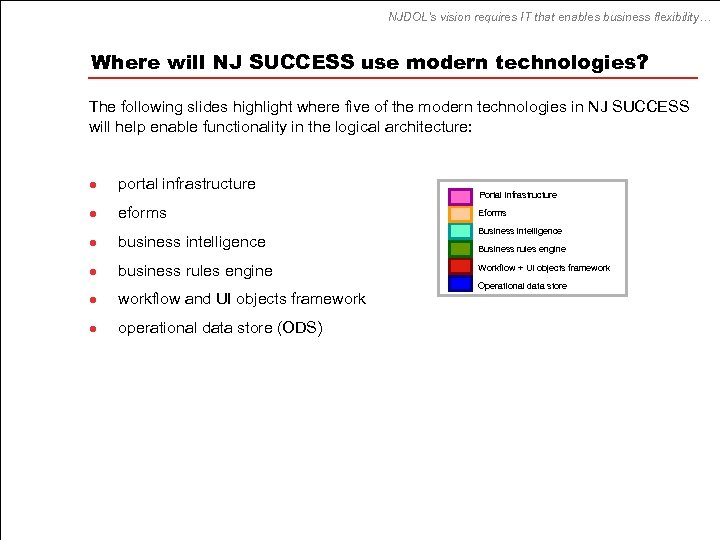
NJDOL’s vision requires IT that enables business flexibility… Where will NJ SUCCESS use modern technologies? The following slides highlight where five of the modern technologies in NJ SUCCESS will help enable functionality in the logical architecture: l portal infrastructure l eforms l business intelligence l business rules engine l workflow and UI objects framework l operational data store (ODS) Portal infrastructure Eforms Business intelligence Business rules engine Workflow + UI objects framework Operational data store
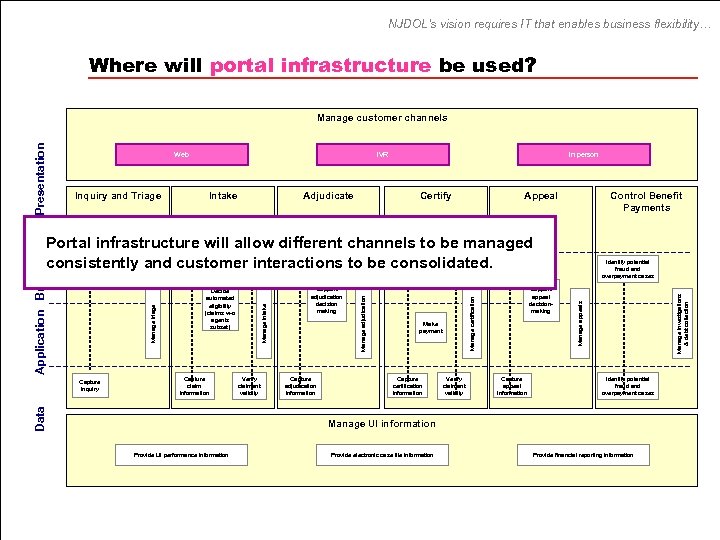
NJDOL’s vision requires IT that enables business flexibility… Where will portal infrastructure be used? Web Inquiry and Triage Capture inquiry IVR Intake Adjudicate In person Certify Appeal Control Benefit Payments Capture claim information Support adjudication decision making Capture adjudication information Verify claimant validity Make payment Capture certification information Capture appeal information Support appeal decisionmaking Verify claimant validity Capture appeal information Identify potential fraud and overpayment cases Manage appeals Manage intake Verify claimant validity Capture certification information Manage certification Verify claimant validity Decide automated eligibility (claims w-o agents subset) Data Capture inquiry Capture adjudication information Manage adjudication Capture claim information Manage triage Application Business Portal infrastructure will allow different channels to be managed consistently and customer interactions to be consolidated. Manage investigations & debt collection Presentation Manage customer channels Identify potential fraud and overpayment cases Manage UI information Provide UI performance information Provide electronic case file information Provide financial reporting information
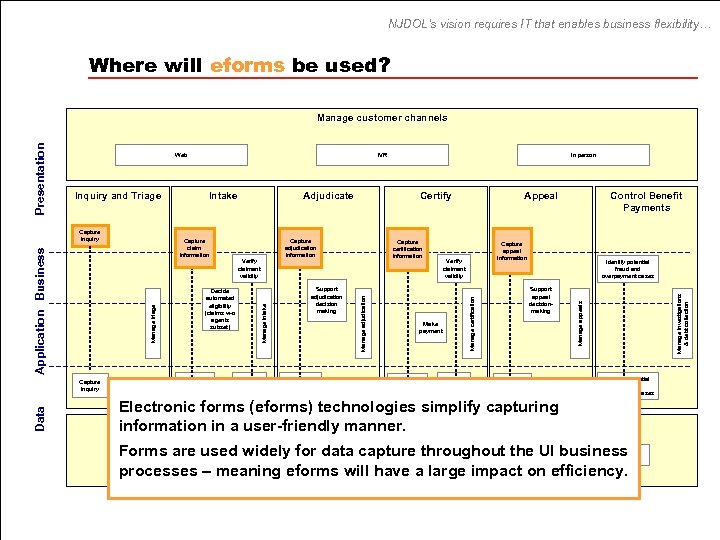
NJDOL’s vision requires IT that enables business flexibility… Where will eforms be used? Capture inquiry Data Capture claim information Capture adjudication information Verify claimant validity Decide automated eligibility (claims w-o agents subset) Verify claimant validity Certify Capture certification information Support adjudication decision making Capture adjudication information Verify claimant validity Control Benefit Payments Capture appeal information Verify claimant validity Make payment Capture certification information Appeal Identify potential fraud and overpayment cases Support appeal decisionmaking Capture appeal information Manage investigations & debt collection Adjudicate In person Manage certification Capture claim information Manage triage Application Business Capture inquiry Intake Manage adjudication Inquiry and Triage IVR Manage appeals Web Manage intake Presentation Manage customer channels Identify potential fraud and overpayment cases Electronic forms (eforms) technologies simplify capturing Manage UI information in a user-friendly manner. Forms are used widely for data capture throughout the UI business processes – meaning eforms will have a large impact on efficiency. Provide UI performance information Provide electronic case file information Provide financial reporting information
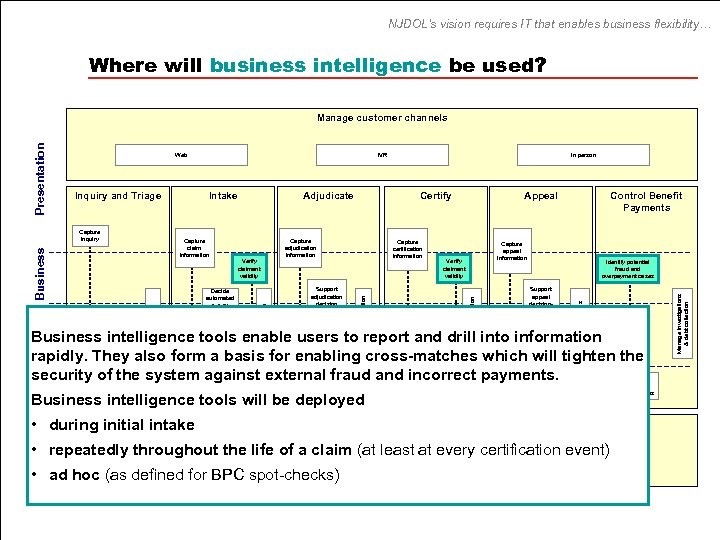
NJDOL’s vision requires IT that enables business flexibility… Where will business intelligence be used? Capture adjudication information Verify claimant validity Decide automated eligibility (claims w-o agents subset) Certify Capture certification information Support adjudication decision making Appeal Capture appeal information Verify claimant validity Make payment Control Benefit Payments Identify potential fraud and overpayment cases Support appeal decisionmaking Business intelligence tools enable users to report and drill into information rapidly. They also form a basis for enabling cross-matches which will tighten the security of the system against external fraud and incorrect payments. Capture inquiry Capture claim information Verify claimant validity Capture adjudication information Data Business intelligence tools will be deployed • during initial intake Capture certification information Verify claimant validity Capture appeal information Identify potential fraud and overpayment cases Manage UI information • repeatedly throughout the life of a claim (at least at every certification event) Provide UI performance information Provide electronic case file information • ad hoc (as defined for BPC spot-checks) Provide financial reporting information Manage investigations & debt collection Adjudicate In person Manage certification Capture claim information Manage triage Application Business Capture inquiry Intake Manage adjudication Inquiry and Triage IVR Manage appeals Web Manage intake Presentation Manage customer channels
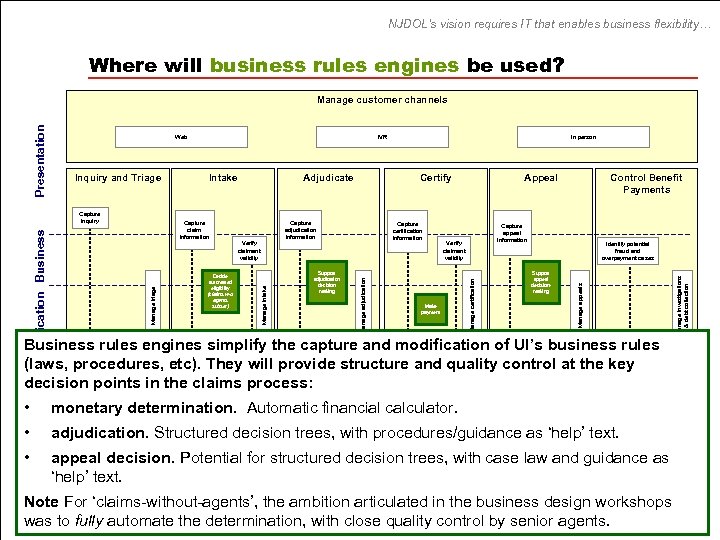
NJDOL’s vision requires IT that enables business flexibility… Where will business rules engines be used? Capture adjudication information Verify claimant validity Decide automated eligibility (claims w-o agents subset) Certify Support adjudication decision making Capture certification information Appeal Capture appeal information Verify claimant validity Make payment Control Benefit Payments Identify potential fraud and overpayment cases Support appeal decisionmaking Business rules engines simplify the capture and modification of UI’s business rules (laws, procedures, etc). They will provide structure and quality control at the key decision points in the claims process: • Data Capture inquiry Capture claim information Verify claimant validity Capture adjudication information Capture certification information Verify claimant validity Capture appeal information Identify potential fraud and overpayment cases Manage UI calculator. monetary determination. Automatic financialinformation • adjudication. Structured decision trees, with procedures/guidance as ‘help’ text. Provide electronic case file information • appeal decision. Potential for structured decision trees, with case law and guidance as ‘help’ text. Provide UI performance information Provide financial reporting information Key ‘claims-without-agents’, the ambition articulated in the business design workshops Note For business functionality is shown above for NJ SUCCESS, this was identified in the Business Conceptual Design phase. was to fully automate the determination, with close quality control by senior agents. Manage investigations & debt collection Adjudicate In person Manage certification Capture claim information Manage triage Application Business Capture inquiry Intake Manage adjudication Inquiry and Triage IVR Manage appeals Web Manage intake Presentation Manage customer channels
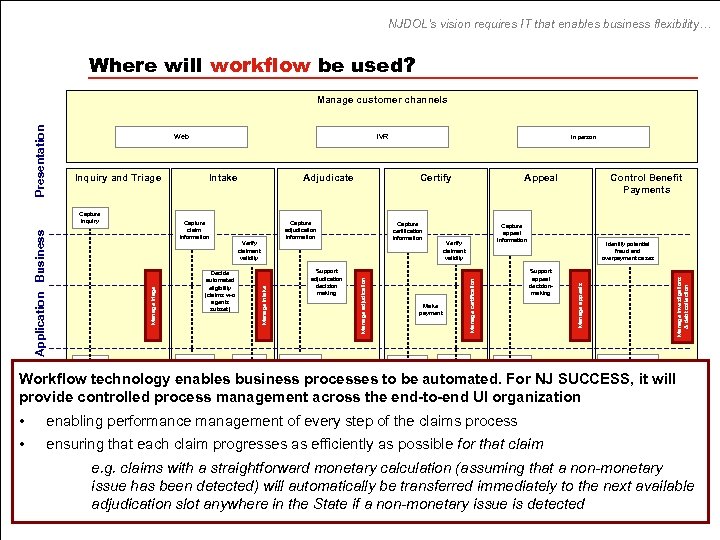
NJDOL’s vision requires IT that enables business flexibility… Where will workflow be used? Capture inquiry Capture claim information Capture adjudication information Verify claimant validity Decide automated eligibility (claims w-o agents subset) Verify claimant validity Certify Capture certification information Support adjudication decision making Capture adjudication information Verify claimant validity Control Benefit Payments Capture appeal information Verify claimant validity Make payment Capture certification information Appeal Identify potential fraud and overpayment cases Support appeal decisionmaking Capture appeal information Manage investigations & debt collection Adjudicate In person Manage certification Capture claim information Manage triage Application Business Capture inquiry Intake Manage adjudication Inquiry and Triage IVR Manage appeals Web Manage intake Presentation Manage customer channels Identify potential fraud and overpayment cases • • Data Workflow technology enables business processes to be automated. For NJ SUCCESS, it will provide controlled process management across the end-to-end UI organization Manage UI information enabling performance management of every step of the claims process Provide UI performance information Provide electronic case file information Provide financial reporting information ensuring that each claim progresses as efficiently as possible for that claim e. g. claims with a straightforward monetary calculation (assuming that a non-monetary issue has been detected) will automatically be transferred immediately to the next available adjudication slot anywhere in the State if a non-monetary issue is detected
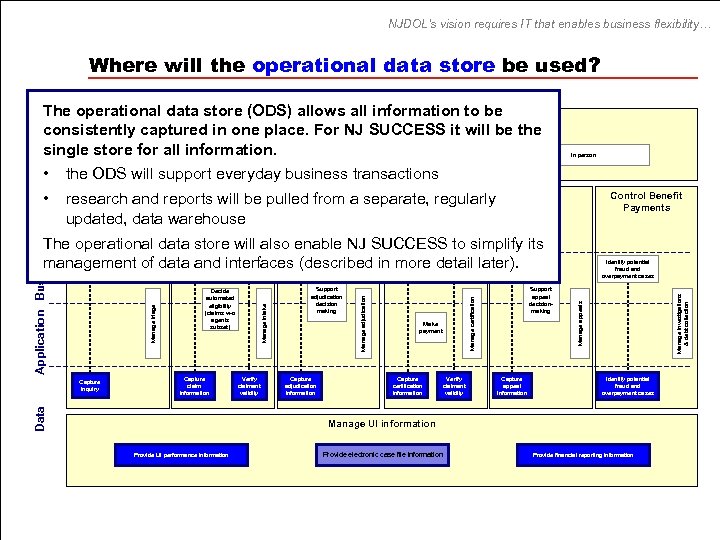
NJDOL’s vision requires IT that enables business flexibility… Where will the operational data store be used? Presentation The operational data store (ODS) allows all information to be Manage customer channels consistently captured in one place. For NJ SUCCESS it will be the single store for all information. Web IVR the ODS will support everyday business transactions • Inquiry and Intake Adjudicate Certify research Triage reports will be pulled from a separate, regularly and updated, data warehouse Capture inquiry Appeal Control Benefit Payments Capture claim information Support adjudication decision making Capture adjudication information Verify claimant validity Make payment Capture certification information Capture appeal information Support appeal decisionmaking Verify claimant validity Capture appeal information Identify potential fraud and overpayment cases Manage appeals Manage intake Verify claimant validity Capture certification information Manage certification Verify claimant validity Decide automated eligibility (claims w-o agents subset) Data Capture inquiry Capture adjudication information Manage adjudication Capture claim information Manage triage Application Business The operational data store will also enable NJ SUCCESS to simplify its management of data and interfaces (described in more detail later). Manage investigations & debt collection • In person Identify potential fraud and overpayment cases Manage UI information Provide UI performance information Provide electronic case file information Provide financial reporting information
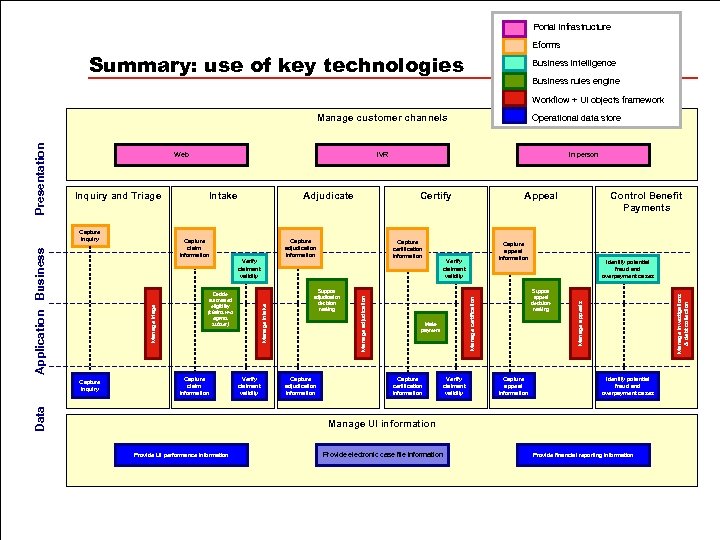
Portal infrastructure Eforms Summary: use of key technologies Business intelligence Business rules engine Workflow + UI objects framework Capture claim information Verify claimant validity Capture certification information Support adjudication decision making Capture adjudication information Verify claimant validity Control Benefit Payments Capture appeal information Verify claimant validity Make payment Capture certification information Appeal Identify potential fraud and overpayment cases Support appeal decisionmaking Capture appeal information Manage investigations & debt collection Certify Capture adjudication information Verify claimant validity In person Manage certification Adjudicate Decide automated eligibility (claims w-o agents subset) Data Capture inquiry Intake Capture claim information Manage triage Application Business Capture inquiry IVR Manage adjudication Inquiry and Triage Operational data store Manage appeals Web Manage intake Presentation Manage customer channels Identify potential fraud and overpayment cases Manage UI information Provide UI performance information Provide electronic case file information Provide financial reporting information
NJ SUCCESS needs a standard approach for data and interfaces NJDOL’s vision for UI Modernization is to deliver revolutionized UI services while maintaining the integrity of the Trust Fund To meet this vision, NJDOL needs to develop a modern UI system (NJ SUCCESS) NJDOL’s business vision requires IT that enables business flexibility NJ SUCCESS must use a modern architecture NJ SUCCESS needs a standard approach for data and interfaces NJ SUCCESS will contain modern IT technologies Likely total IT costs for NJ SUCCESS are affordable
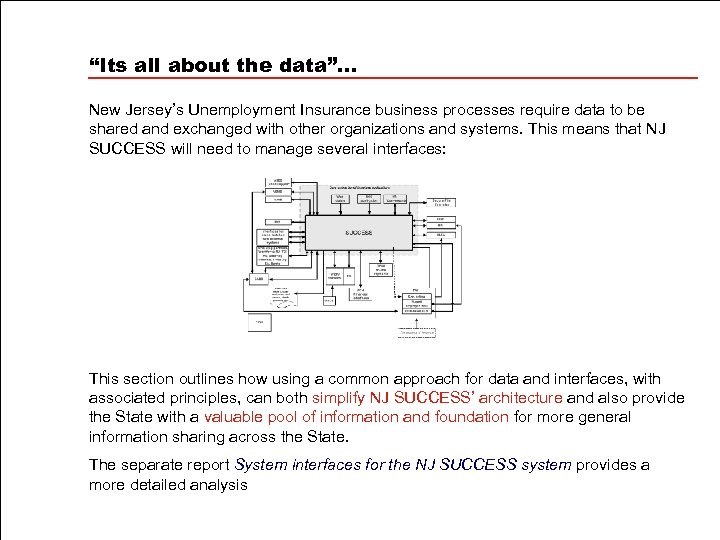
“Its all about the data”… New Jersey’s Unemployment Insurance business processes require data to be shared and exchanged with other organizations and systems. This means that NJ SUCCESS will need to manage several interfaces: This section outlines how using a common approach for data and interfaces, with associated principles, can both simplify NJ SUCCESS’ architecture and also provide the State with a valuable pool of information and foundation for more general information sharing across the State. The separate report System interfaces for the NJ SUCCESS system provides a more detailed analysis
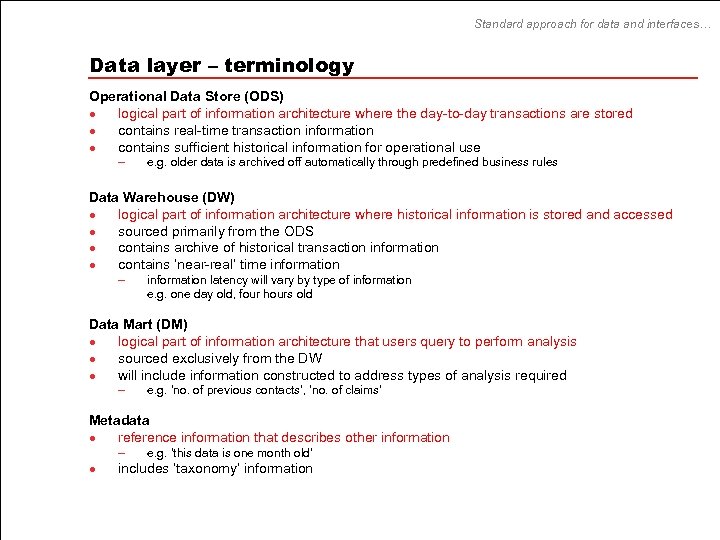
Standard approach for data and interfaces… Data layer – terminology Operational Data Store (ODS) l logical part of information architecture where the day-to-day transactions are stored l contains real-time transaction information l contains sufficient historical information for operational use – e. g. older data is archived off automatically through predefined business rules Data Warehouse (DW) l logical part of information architecture where historical information is stored and accessed l sourced primarily from the ODS l contains archive of historical transaction information l contains ‘near-real’ time information – information latency will vary by type of information e. g. one day old, four hours old Data Mart (DM) l logical part of information architecture that users query to perform analysis l sourced exclusively from the DW l will include information constructed to address types of analysis required – e. g. ‘no. of previous contacts’, ‘no. of claims’ Metadata l reference information that describes other information – l e. g. ‘this data is one month old’ includes ‘taxonomy’ information
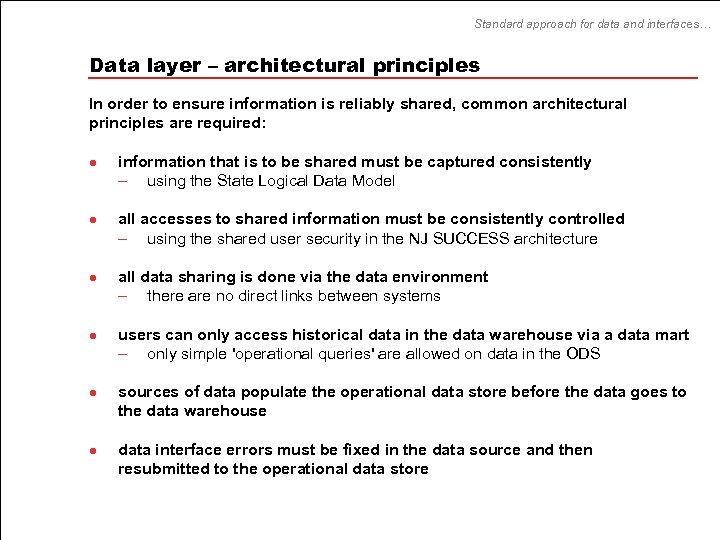
Standard approach for data and interfaces… Data layer – architectural principles In order to ensure information is reliably shared, common architectural principles are required: l l l information that is to be shared must be captured consistently – using the State Logical Data Model all accesses to shared information must be consistently controlled – using the shared user security in the NJ SUCCESS architecture all data sharing is done via the data environment – there are no direct links between systems users can only access historical data in the data warehouse via a data mart – only simple 'operational queries' are allowed on data in the ODS sources of data populate the operational data store before the data goes to the data warehouse data interface errors must be fixed in the data source and then resubmitted to the operational data store
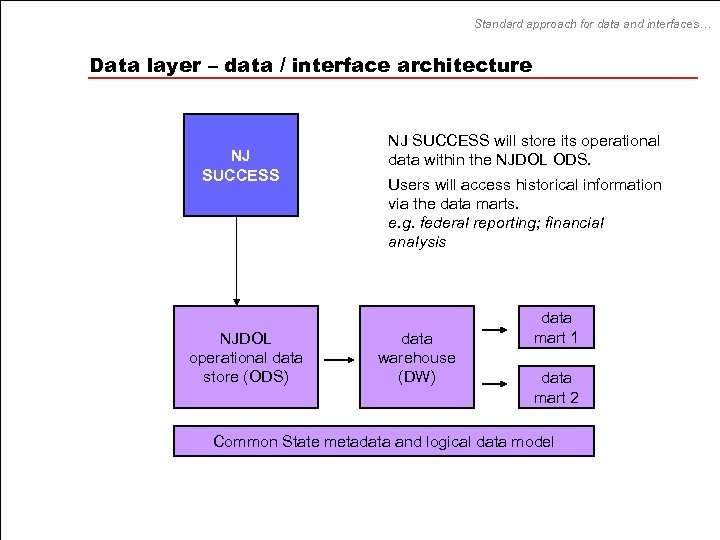
Standard approach for data and interfaces… Data layer – data / interface architecture NJ SUCCESS NJDOL Operational data operational Data store (ODS) NJ SUCCESS will store its operational data within the NJDOL ODS. Users will access historical information via the data marts. e. g. federal reporting; financial analysis Data data Warehouse warehouse (DW) Data data mart Mart 1 Data data mart Mart 2 Common State metadata and Logical data model Common State metadata and logical Data Model
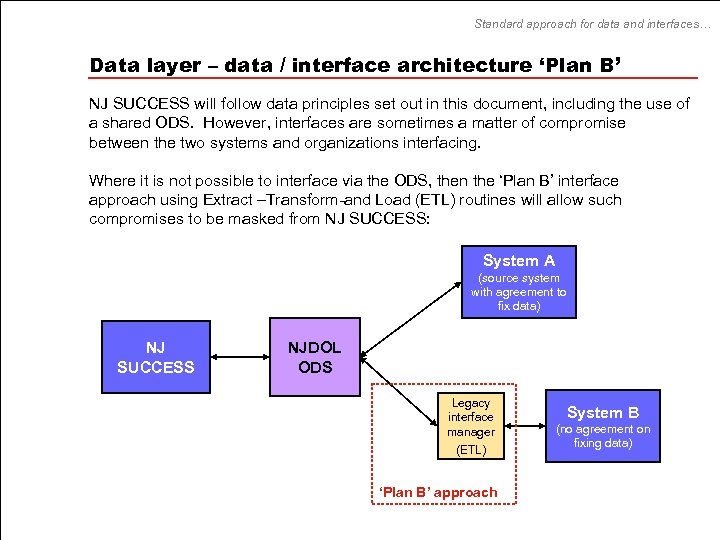
Standard approach for data and interfaces… Data layer – data / interface architecture ‘Plan B’ NJ SUCCESS will follow data principles set out in this document, including the use of a shared ODS. However, interfaces are sometimes a matter of compromise between the two systems and organizations interfacing. Where it is not possible to interface via the ODS, then the ‘Plan B’ interface approach using Extract –Transform-and Load (ETL) routines will allow such compromises to be masked from NJ SUCCESS: System A (source system with agreement to fix data) NJ SUCCESS NJDOL ODS Legacy interface manager (ETL) ‘Plan B’ approach System B (no agreement on fixing data)
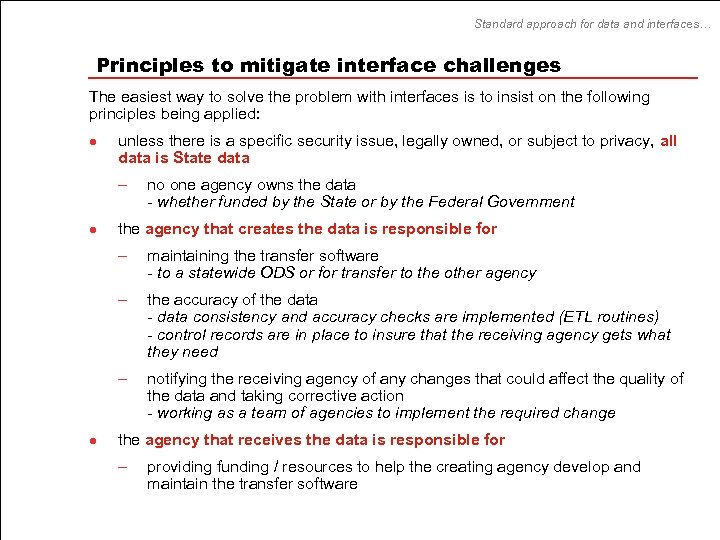
Standard approach for data and interfaces… Principles to mitigate interface challenges The easiest way to solve the problem with interfaces is to insist on the following principles being applied: l unless there is a specific security issue, legally owned, or subject to privacy, all data is State data – l no one agency owns the data - whether funded by the State or by the Federal Government the agency that creates the data is responsible for – – the accuracy of the data - data consistency and accuracy checks are implemented (ETL routines) - control records are in place to insure that the receiving agency gets what they need – l maintaining the transfer software - to a statewide ODS or for transfer to the other agency notifying the receiving agency of any changes that could affect the quality of the data and taking corrective action - working as a team of agencies to implement the required change the agency that receives the data is responsible for – providing funding / resources to help the creating agency develop and maintain the transfer software
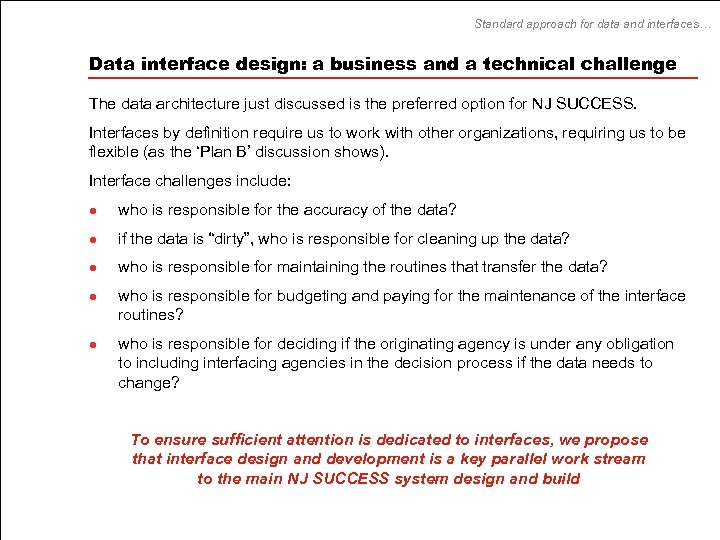
Standard approach for data and interfaces… Data interface design: a business and a technical challenge The data architecture just discussed is the preferred option for NJ SUCCESS. Interfaces by definition require us to work with other organizations, requiring us to be flexible (as the ‘Plan B’ discussion shows). Interface challenges include: l who is responsible for the accuracy of the data? l if the data is “dirty”, who is responsible for cleaning up the data? l who is responsible for maintaining the routines that transfer the data? l l who is responsible for budgeting and paying for the maintenance of the interface routines? who is responsible for deciding if the originating agency is under any obligation to including interfacing agencies in the decision process if the data needs to change? To ensure sufficient attention is dedicated to interfaces, we propose that interface design and development is a key parallel work stream to the main NJ SUCCESS system design and build
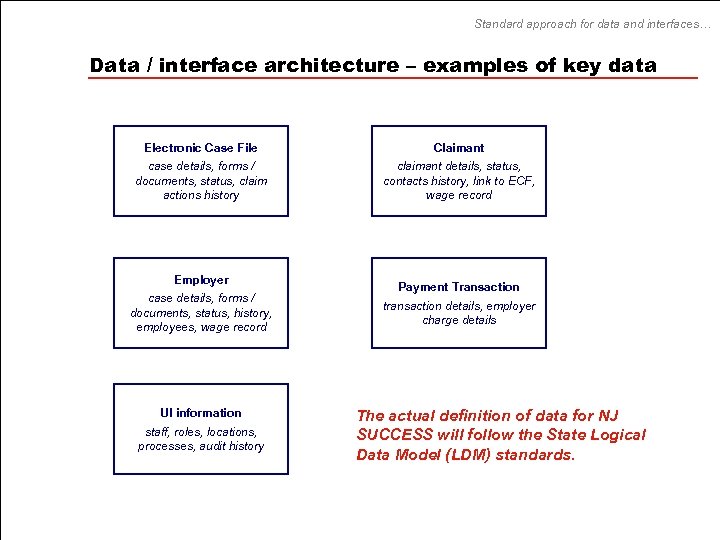
Standard approach for data and interfaces… Data / interface architecture – examples of key data Electronic Case File Claimant case details, forms / documents, status, claim actions history claimant details, status, contacts history, link to ECF, wage record Employer case details, forms / documents, status, history, employees, wage record UI information staff, roles, locations, processes, audit history Payment Transaction transaction details, employer charge details The actual definition of data for NJ SUCCESS will follow the State Logical Data Model (LDM) standards.
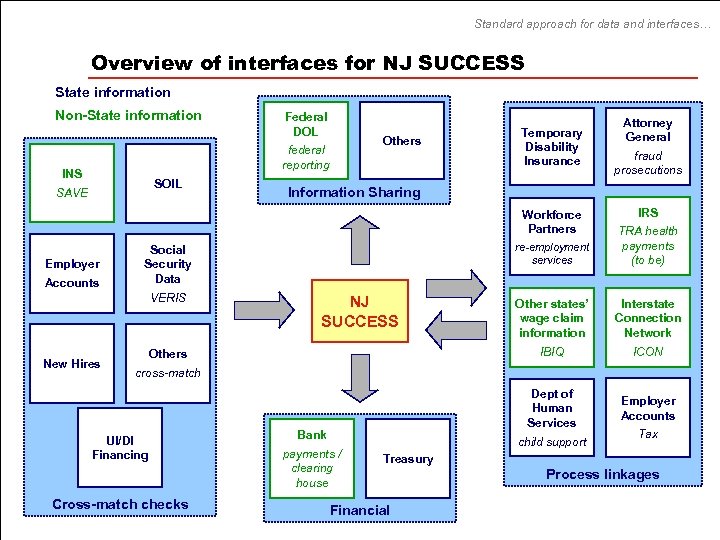
Standard approach for data and interfaces… Overview of interfaces for NJ SUCCESS State information Non-State information Federal DOL federal reporting INS SOIL SAVE Others Temporary Disability Insurance Accounts New Hires IRS re-employment services Other states’ wage claim information Interstate Connection Network ICON Dept of Human Services NJ SUCCESS TRA health payments (to be) IBIQ Social Security Data VERIS fraud prosecutions Information Sharing Workforce Partners Employer Attorney General Employer Accounts cross-match UI/DI Financing Cross-match checks Bank payments / clearing house child support Tax Treasury Financial Process linkages
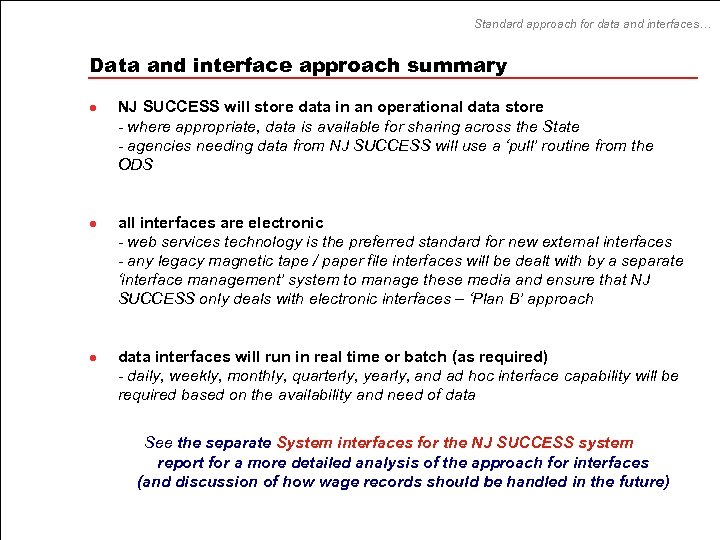
Standard approach for data and interfaces… Data and interface approach summary l l l NJ SUCCESS will store data in an operational data store - where appropriate, data is available for sharing across the State - agencies needing data from NJ SUCCESS will use a ‘pull’ routine from the ODS all interfaces are electronic - web services technology is the preferred standard for new external interfaces - any legacy magnetic tape / paper file interfaces will be dealt with by a separate ‘interface management’ system to manage these media and ensure that NJ SUCCESS only deals with electronic interfaces – ‘Plan B’ approach data interfaces will run in real time or batch (as required) - daily, weekly, monthly, quarterly, yearly, and ad hoc interface capability will be required based on the availability and need of data See the separate System interfaces for the NJ SUCCESS system report for a more detailed analysis of the approach for interfaces (and discussion of how wage records should be handled in the future)
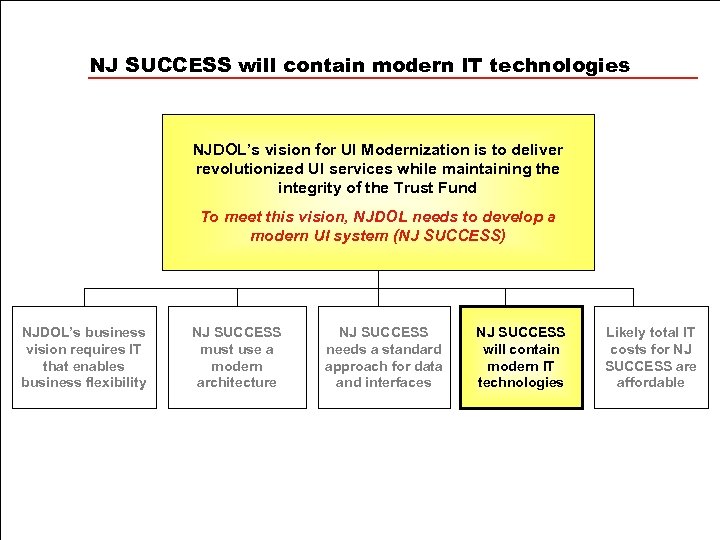
NJ SUCCESS will contain modern IT technologies NJDOL’s vision for UI Modernization is to deliver revolutionized UI services while maintaining the integrity of the Trust Fund To meet this vision, NJDOL needs to develop a modern UI system (NJ SUCCESS) NJDOL’s business vision requires IT that enables business flexibility NJ SUCCESS must use a modern architecture NJ SUCCESS needs a standard approach for data and interfaces NJ SUCCESS will contain modern IT technologies Likely total IT costs for NJ SUCCESS are affordable
Modern IT technologies… Technical architecture background This section summarizes the types of modern IT technologies that are required to deliver NJ SUCCESS – the technical architecture for NJ SUCCESS. The technologies in the technical architecture are grouped in the same manner as the logical architecture, except for the addition of a fifth grouping to cover technologies used to provide ‘infrastructure’ services The five groupings used for the technology architecture cover all technology categories required for NJ SUCCESS.
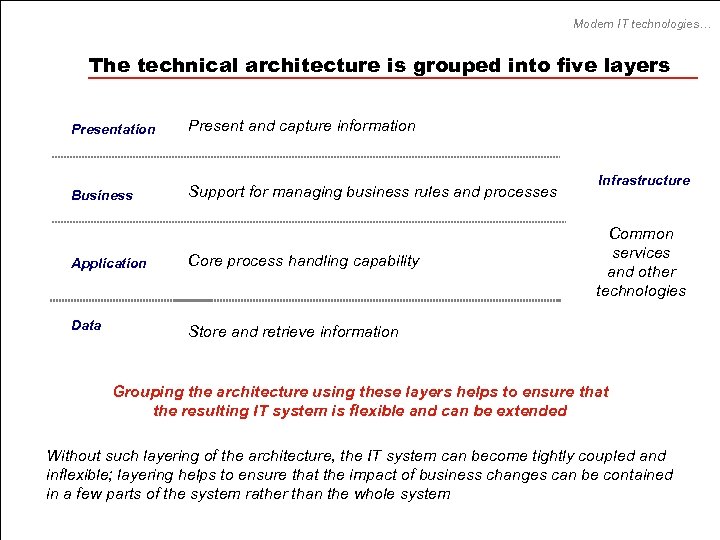
Modern IT technologies… The technical architecture is grouped into five layers Presentation Present and capture information Business Support for managing business rules and processes Application Core process handling capability Data Infrastructure Common services and other technologies Store and retrieve information Grouping the architecture using these layers helps to ensure that the resulting IT system is flexible and can be extended Without such layering of the architecture, the IT system can become tightly coupled and inflexible; layering helps to ensure that the impact of business changes can be contained in a few parts of the system rather than the whole system
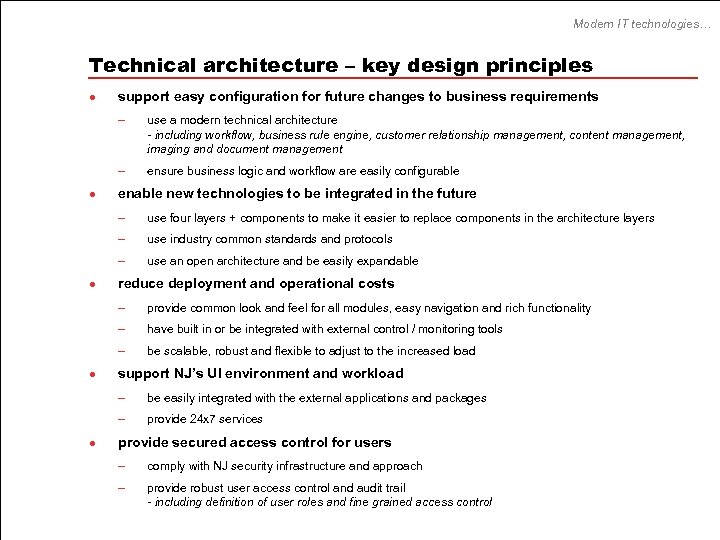
Modern IT technologies… Technical architecture – key design principles l support easy configuration for future changes to business requirements – – l use a modern technical architecture - including workflow, business rule engine, customer relationship management, content management, imaging and document management ensure business logic and workflow are easily configurable enable new technologies to be integrated in the future – – use industry common standards and protocols – l use four layers + components to make it easier to replace components in the architecture layers use an open architecture and be easily expandable reduce deployment and operational costs – – have built in or be integrated with external control / monitoring tools – l provide common look and feel for all modules, easy navigation and rich functionality be scalable, robust and flexible to adjust to the increased load support NJ’s UI environment and workload – – l be easily integrated with the external applications and packages provide 24 x 7 services provide secured access control for users – comply with NJ security infrastructure and approach – provide robust user access control and audit trail - including definition of user roles and fine grained access control
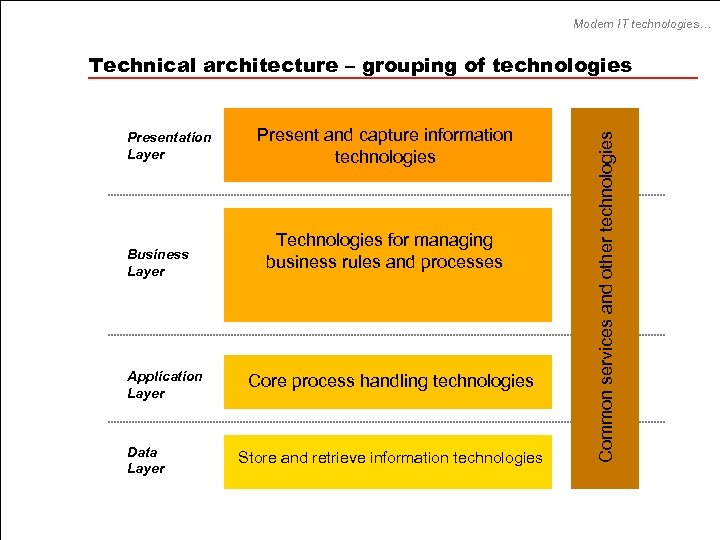
Modern IT technologies… Presentation Layer Business Layer Application Layer Data Layer Present and capture information technologies Technologies for managing business rules and processes Core process handling technologies Store and retrieve information technologies Common services and other technologies Technical architecture – grouping of technologies
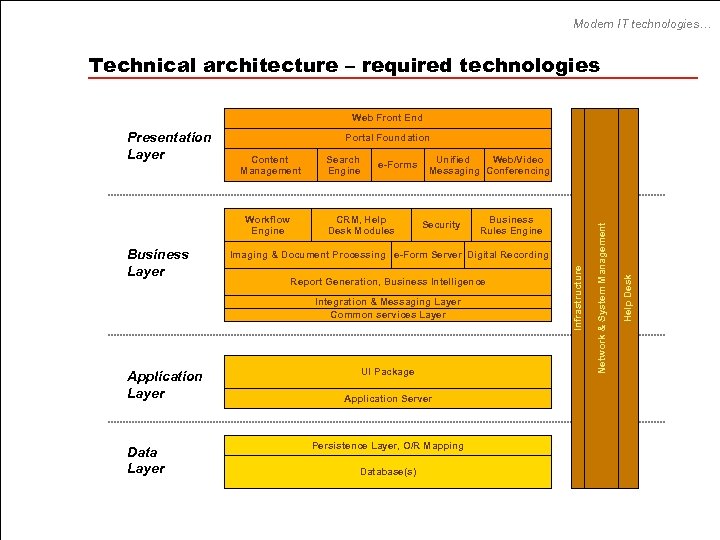
Modern IT technologies… Technical architecture – required technologies Web Front End Portal Foundation Business Layer e-Forms CRM, Help Desk Modules Unified Web/Video Messaging Conferencing Security Imaging & Document Processing e-Form Server Digital Recording Report Generation, Business Intelligence Integration & Messaging Layer Common services Layer Application Layer Data Layer Business Rules Engine UI Package Application Server Persistence Layer, O/R Mapping Database(s) Help Desk Workflow Engine Search Engine Network & System Management Content Management Infrastructure Presentation Layer
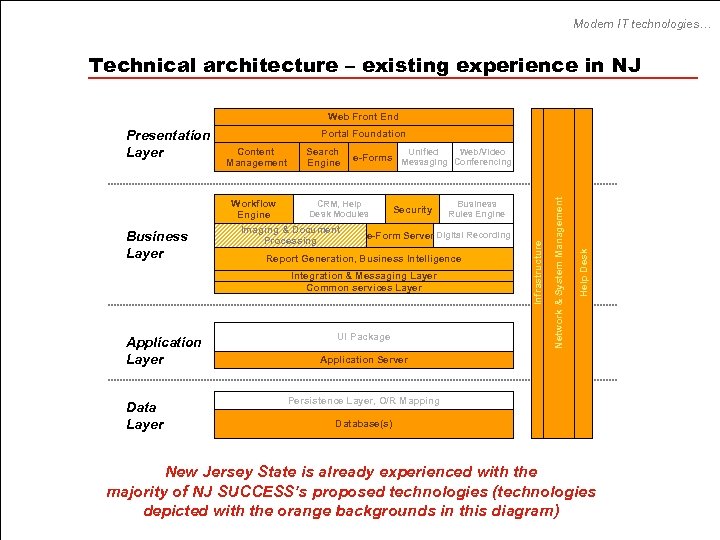
Modern IT technologies… Technical architecture – existing experience in NJ Web Front End Portal Foundation Business Layer Unified CRM, Help Desk Modules Imaging & Document Processing Security Data Layer Business Rules Engine e-Form Server Digital Recording Report Generation, Business Intelligence Integration & Messaging Layer Common services Layer Application Layer Web/Video e-Forms Messaging Conferencing UI Package Help Desk Workflow Engine Search Engine Network & System Management Content Management Infrastructure Presentation Layer Application Server Persistence Layer, O/R Mapping Database(s) New Jersey State is already experienced with the majority of NJ SUCCESS’s proposed technologies (technologies depicted with the orange backgrounds in this diagram)
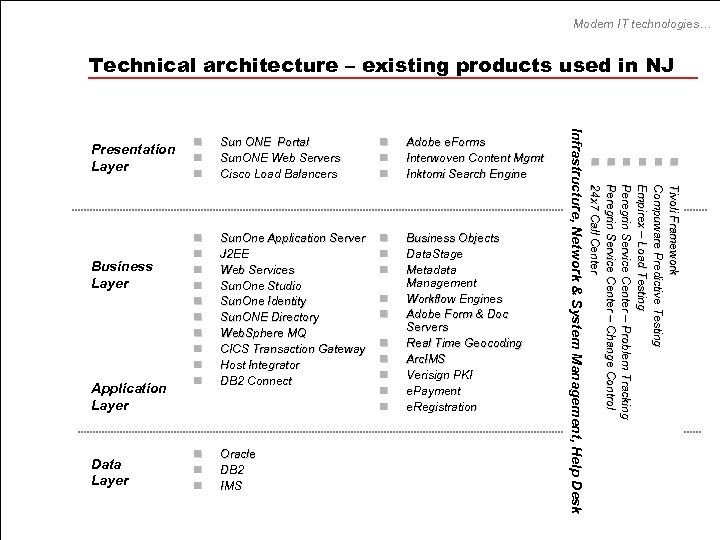
Modern IT technologies… Technical architecture – existing products used in NJ Data Layer n n n Adobe e. Forms Interwoven Content Mgmt Inktomi Search Engine n n n n n Sun. One Application Server J 2 EE Web Services Sun. One Studio Sun. One Identity Sun. ONE Directory Web. Sphere MQ CICS Transaction Gateway Host Integrator DB 2 Connect n n n Business Objects Data. Stage Metadata Management Workflow Engines Adobe Form & Doc Servers Real Time Geocoding Arc. IMS Verisign PKI e. Payment e. Registration n Oracle DB 2 IMS n n n n Tivoli Framework Compuware Predictive Testing Empirex – Load Testing Peregrin Service Center – Problem Tracking Peregrin Service Center – Change Control 24 x 7 Call Center Application Layer Sun ONE Portal Sun. ONE Web Servers Cisco Load Balancers n n n n n Business Layer n n n Infrastructure, Network & System Management, Help Desk Presentation Layer
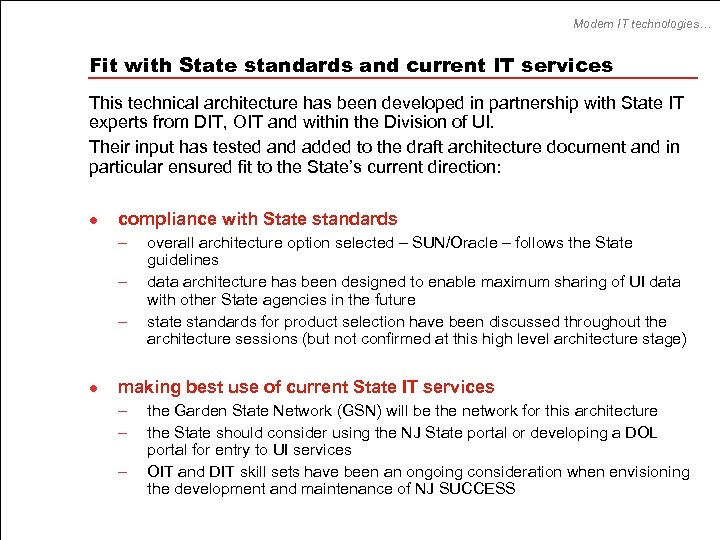
Modern IT technologies… Fit with State standards and current IT services This technical architecture has been developed in partnership with State IT experts from DIT, OIT and within the Division of UI. Their input has tested and added to the draft architecture document and in particular ensured fit to the State’s current direction: l compliance with State standards – – – l overall architecture option selected – SUN/Oracle – follows the State guidelines data architecture has been designed to enable maximum sharing of UI data with other State agencies in the future state standards for product selection have been discussed throughout the architecture sessions (but not confirmed at this high level architecture stage) making best use of current State IT services – – – the Garden State Network (GSN) will be the network for this architecture the State should consider using the NJ State portal or developing a DOL portal for entry to UI services OIT and DIT skill sets have been an ongoing consideration when envisioning the development and maintenance of NJ SUCCESS
Modern IT technologies… Technical architecture candidate products The technologies and approach for NJ SUCCESS architecture represent IT architecture best practice and have been used by other states and comparable organizations. As part of the technical architecture phase, candidate products for each of the technologies for NJ SUCCESS were presented and reviewed during twenty-five hours of workshops. The 390 technology slides from the review workshops are included as appendices to this report – see next page for a mapping of the appendices onto the technical layers
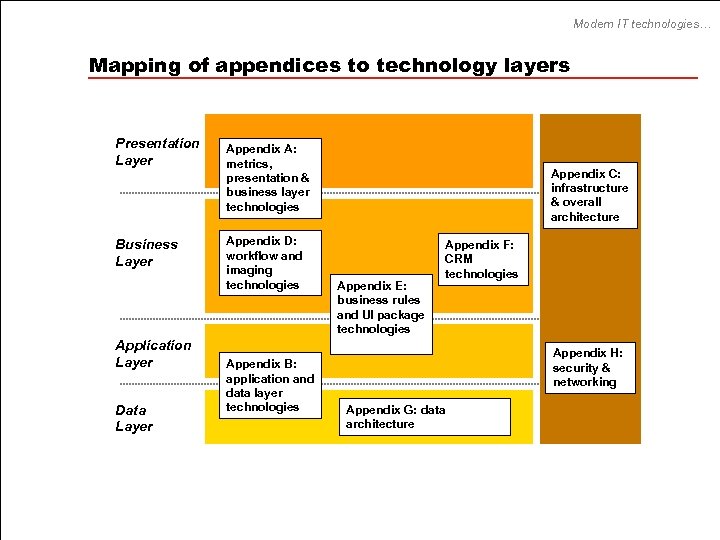
Modern IT technologies… Mapping of appendices to technology layers Presentation Layer Business Layer Application Layer Data Layer Appendix A: metrics, presentation & business layer technologies Appendix D: workflow and imaging technologies Appendix B: application and data layer technologies Appendix C: infrastructure & overall architecture Appendix E: business rules and UI package technologies Appendix F: CRM technologies Appendix H: security & networking Appendix G: data architecture
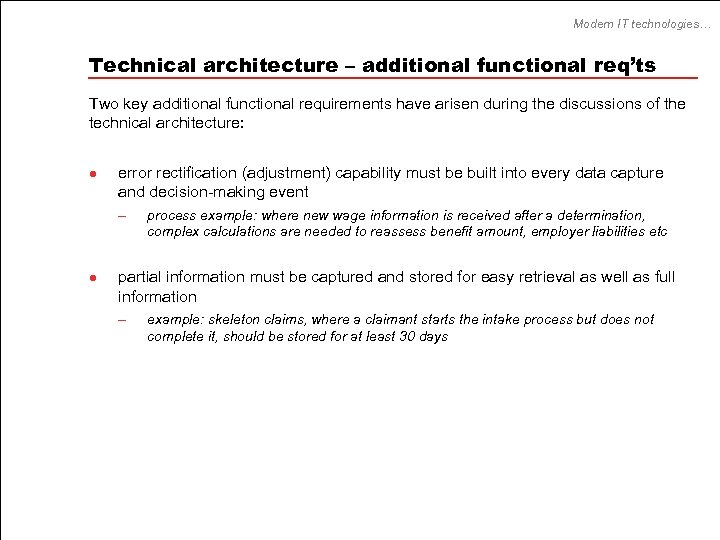
Modern IT technologies… Technical architecture – additional functional req’ts Two key additional functional requirements have arisen during the discussions of the technical architecture: l error rectification (adjustment) capability must be built into every data capture and decision-making event – l process example: where new wage information is received after a determination, complex calculations are needed to reassess benefit amount, employer liabilities etc partial information must be captured and stored for easy retrieval as well as full information – example: skeleton claims, where a claimant starts the intake process but does not complete it, should be stored for at least 30 days
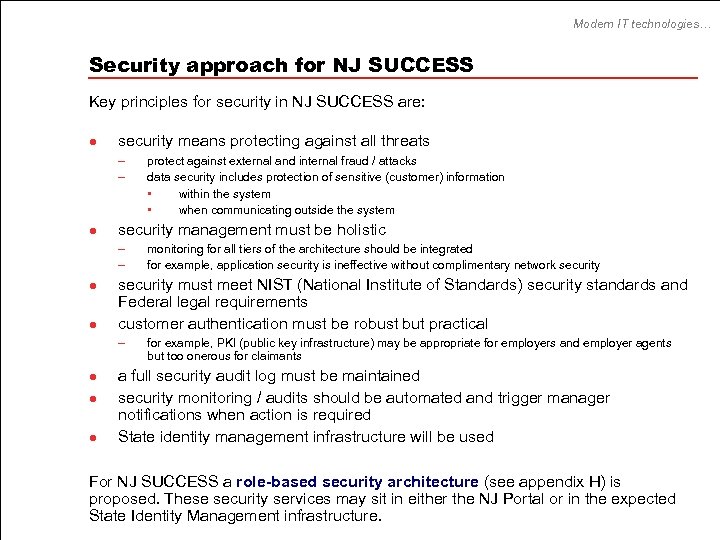
Modern IT technologies… Security approach for NJ SUCCESS Key principles for security in NJ SUCCESS are: l security means protecting against all threats – – l security management must be holistic – – l l monitoring for all tiers of the architecture should be integrated for example, application security is ineffective without complimentary network security must meet NIST (National Institute of Standards) security standards and Federal legal requirements customer authentication must be robust but practical – l protect against external and internal fraud / attacks data security includes protection of sensitive (customer) information • within the system • when communicating outside the system for example, PKI (public key infrastructure) may be appropriate for employers and employer agents but too onerous for claimants a full security audit log must be maintained security monitoring / audits should be automated and trigger manager notifications when action is required State identity management infrastructure will be used For NJ SUCCESS a role-based security architecture (see appendix H) is proposed. These security services may sit in either the NJ Portal or in the expected State Identity Management infrastructure.
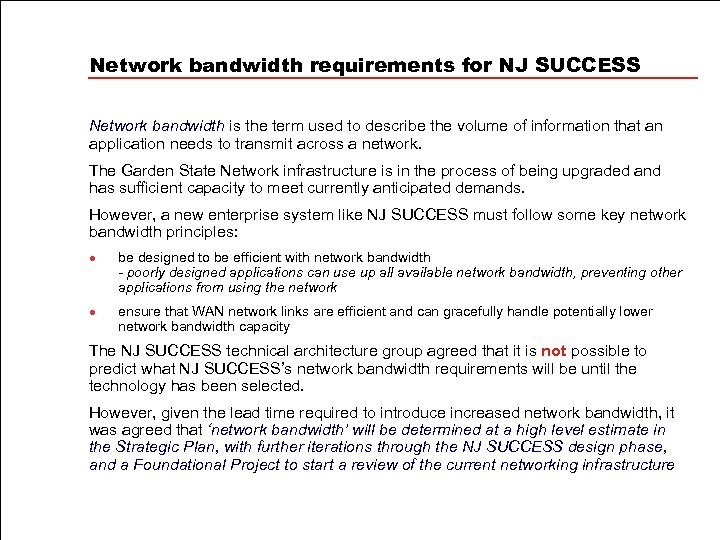
Network bandwidth requirements for NJ SUCCESS Network bandwidth is the term used to describe the volume of information that an application needs to transmit across a network. The Garden State Network infrastructure is in the process of being upgraded and has sufficient capacity to meet currently anticipated demands. However, a new enterprise system like NJ SUCCESS must follow some key network bandwidth principles: l l be designed to be efficient with network bandwidth - poorly designed applications can use up all available network bandwidth, preventing other applications from using the network ensure that WAN network links are efficient and can gracefully handle potentially lower network bandwidth capacity The NJ SUCCESS technical architecture group agreed that it is not possible to predict what NJ SUCCESS’s network bandwidth requirements will be until the technology has been selected. However, given the lead time required to introduce increased network bandwidth, it was agreed that ‘network bandwidth’ will be determined at a high level estimate in the Strategic Plan, with further iterations through the NJ SUCCESS design phase, and a Foundational Project to start a review of the current networking infrastructure
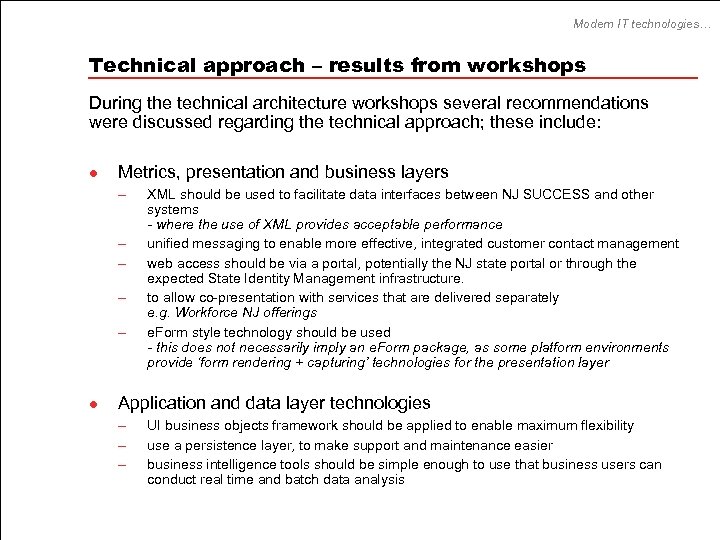
Modern IT technologies… Technical approach – results from workshops During the technical architecture workshops several recommendations were discussed regarding the technical approach; these include: l Metrics, presentation and business layers – – – l XML should be used to facilitate data interfaces between NJ SUCCESS and other systems - where the use of XML provides acceptable performance unified messaging to enable more effective, integrated customer contact management web access should be via a portal, potentially the NJ state portal or through the expected State Identity Management infrastructure. to allow co-presentation with services that are delivered separately e. g. Workforce NJ offerings e. Form style technology should be used - this does not necessarily imply an e. Form package, as some platform environments provide ‘form rendering + capturing’ technologies for the presentation layer Application and data layer technologies – – – UI business objects framework should be applied to enable maximum flexibility use a persistence layer, to make support and maintenance easier business intelligence tools should be simple enough to use that business users can conduct real time and batch data analysis
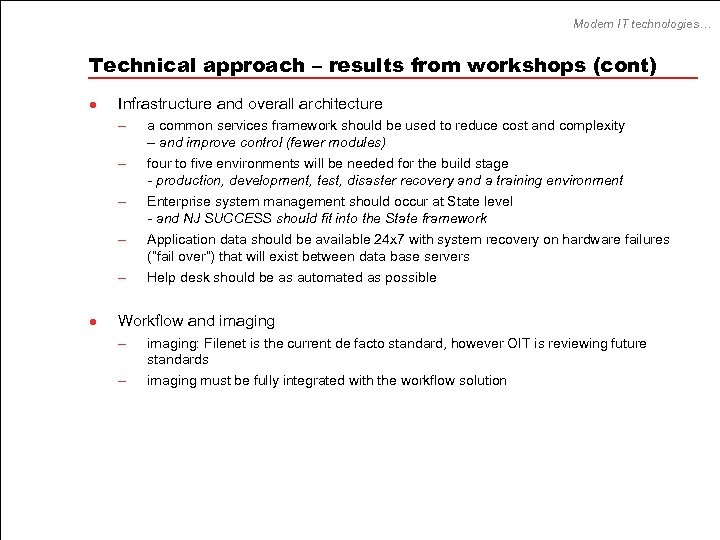
Modern IT technologies… Technical approach – results from workshops (cont) l Infrastructure and overall architecture – – – l a common services framework should be used to reduce cost and complexity – and improve control (fewer modules) four to five environments will be needed for the build stage - production, development, test, disaster recovery and a training environment Enterprise system management should occur at State level - and NJ SUCCESS should fit into the State framework Application data should be available 24 x 7 with system recovery on hardware failures (“fail over”) that will exist between data base servers Help desk should be as automated as possible Workflow and imaging – – imaging: Filenet is the current de facto standard, however OIT is reviewing future standards imaging must be fully integrated with the workflow solution
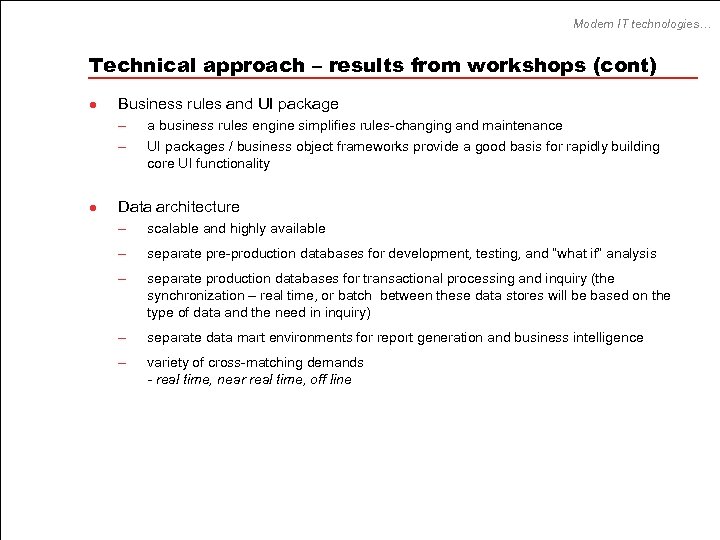
Modern IT technologies… Technical approach – results from workshops (cont) l Business rules and UI package – – l a business rules engine simplifies rules-changing and maintenance UI packages / business object frameworks provide a good basis for rapidly building core UI functionality Data architecture – scalable and highly available – separate pre-production databases for development, testing, and “what if” analysis – separate production databases for transactional processing and inquiry (the synchronization – real time, or batch between these data stores will be based on the type of data and the need in inquiry) – separate data mart environments for report generation and business intelligence – variety of cross-matching demands - real time, near real time, off line
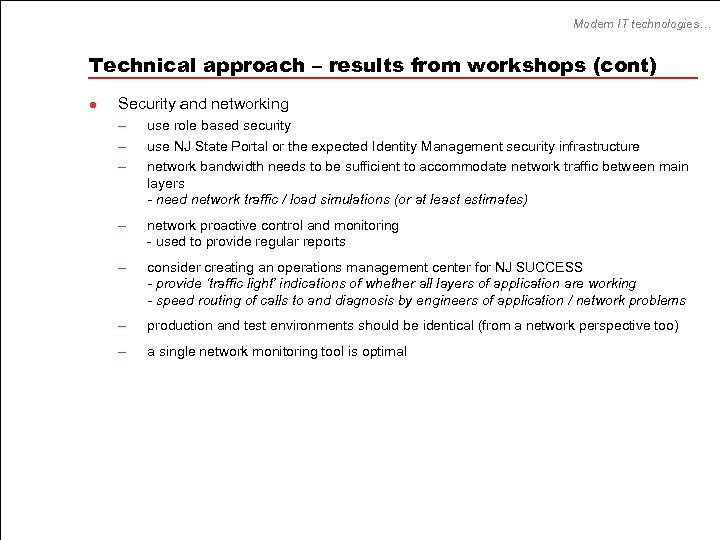
Modern IT technologies… Technical approach – results from workshops (cont) l Security and networking – – – use role based security – network proactive control and monitoring - used to provide regular reports – consider creating an operations management center for NJ SUCCESS - provide ‘traffic light’ indications of whether all layers of application are working - speed routing of calls to and diagnosis by engineers of application / network problems – production and test environments should be identical (from a network perspective too) – a single network monitoring tool is optimal use NJ State Portal or the expected Identity Management security infrastructure network bandwidth needs to be sufficient to accommodate network traffic between main layers - need network traffic / load simulations (or at least estimates)
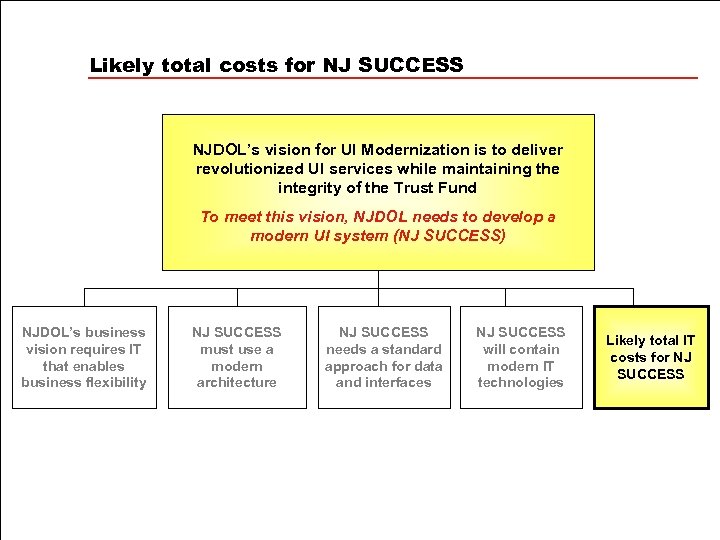
Likely total costs for NJ SUCCESS NJDOL’s vision for UI Modernization is to deliver revolutionized UI services while maintaining the integrity of the Trust Fund To meet this vision, NJDOL needs to develop a modern UI system (NJ SUCCESS) NJDOL’s business vision requires IT that enables business flexibility NJ SUCCESS must use a modern architecture NJ SUCCESS needs a standard approach for data and interfaces NJ SUCCESS will contain modern IT technologies Likely total IT costs for NJ SUCCESS
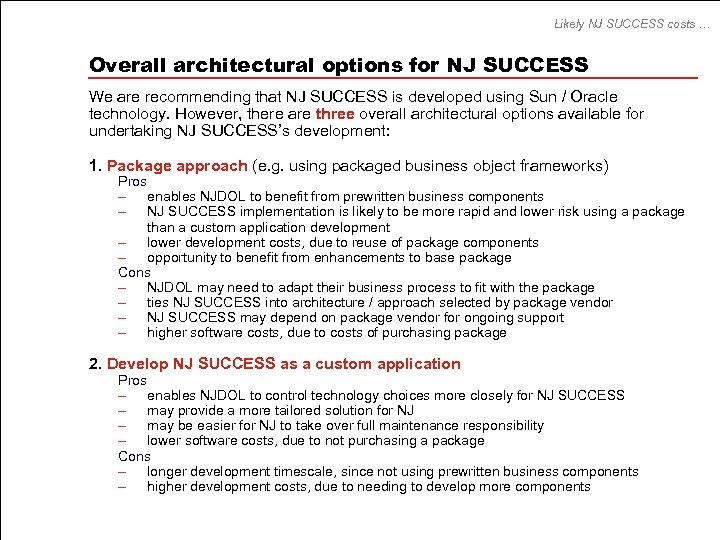
Likely NJ SUCCESS costs … Overall architectural options for NJ SUCCESS We are recommending that NJ SUCCESS is developed using Sun / Oracle technology. However, there are three overall architectural options available for undertaking NJ SUCCESS’s development: 1. Package approach (e. g. using packaged business object frameworks) Pros – enables NJDOL to benefit from prewritten business components – NJ SUCCESS implementation is likely to be more rapid and lower risk using a package than a custom application development – lower development costs, due to reuse of package components – opportunity to benefit from enhancements to base package Cons – NJDOL may need to adapt their business process to fit with the package – ties NJ SUCCESS into architecture / approach selected by package vendor – NJ SUCCESS may depend on package vendor for ongoing support – higher software costs, due to costs of purchasing package 2. Develop NJ SUCCESS as a custom application Pros – enables NJDOL to control technology choices more closely for NJ SUCCESS – may provide a more tailored solution for NJ – may be easier for NJ to take over full maintenance responsibility – lower software costs, due to not purchasing a package Cons – longer development timescale, since not using prewritten business components – higher development costs, due to needing to develop more components
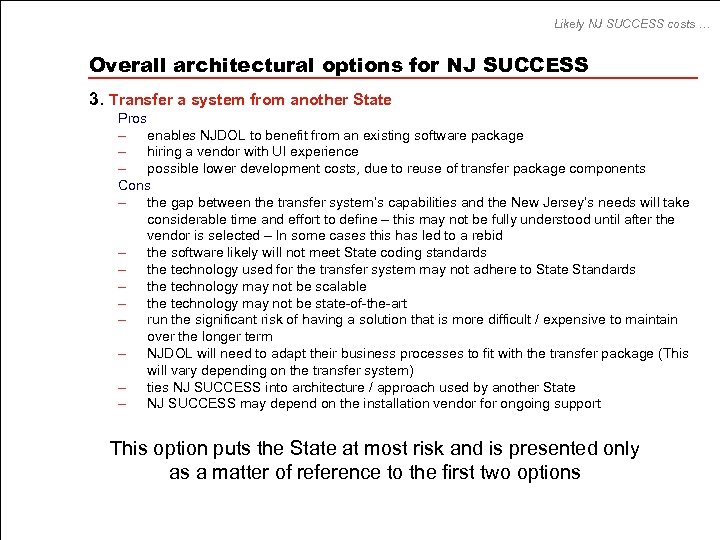
Likely NJ SUCCESS costs … Overall architectural options for NJ SUCCESS 3. Transfer a system from another State Pros – enables NJDOL to benefit from an existing software package – hiring a vendor with UI experience – possible lower development costs, due to reuse of transfer package components Cons – the gap between the transfer system’s capabilities and the New Jersey’s needs will take considerable time and effort to define – this may not be fully understood until after the vendor is selected – In some cases this has led to a rebid – the software likely will not meet State coding standards – the technology used for the transfer system may not adhere to State Standards – the technology may not be scalable – the technology may not be state-of-the-art – run the significant risk of having a solution that is more difficult / expensive to maintain over the longer term – NJDOL will need to adapt their business processes to fit with the transfer package (This will vary depending on the transfer system) – ties NJ SUCCESS into architecture / approach used by another State – NJ SUCCESS may depend on the installation vendor for ongoing support This option puts the State at most risk and is presented only as a matter of reference to the first two options
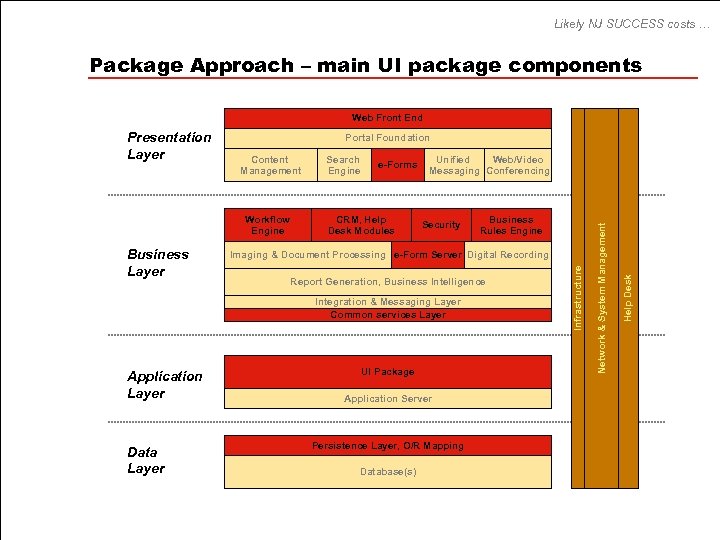
Likely NJ SUCCESS costs … Package Approach – main UI package components Web Front End Portal Foundation Business Layer e-Forms CRM, Help Desk Modules Unified Web/Video Messaging Conferencing Security Imaging & Document Processing e-Form Server Digital Recording Report Generation, Business Intelligence Integration & Messaging Layer Common services Layer Application Layer Data Layer Business Rules Engine UI Package Application Server Persistence Layer, O/R Mapping Database(s) Help Desk Workflow Engine Search Engine Network & System Management Content Management Infrastructure Presentation Layer
Likely NJ SUCCESS costs … Package Approach – example IT build steps Presentation Layer Business Layer Application Layer Data Layer
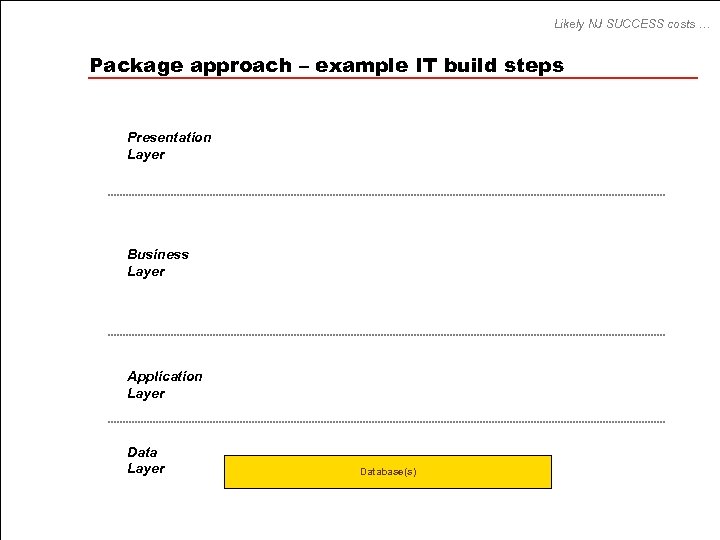
Likely NJ SUCCESS costs … Package approach – example IT build steps Presentation Layer Business Layer Application Layer Database(s)
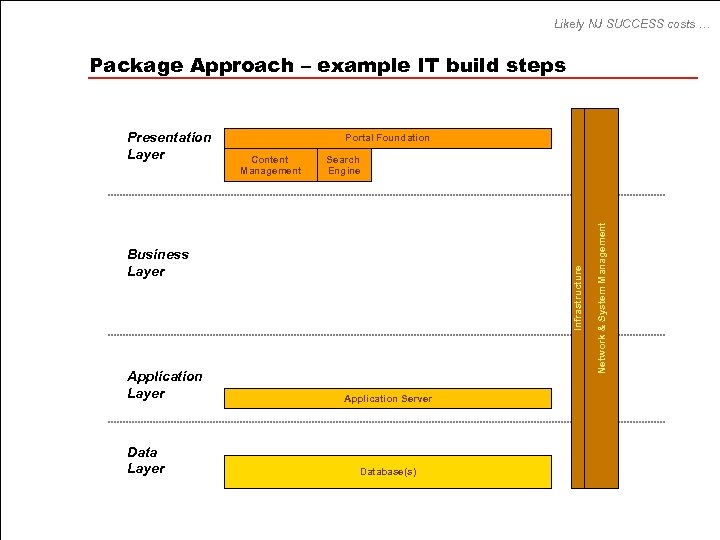
Likely NJ SUCCESS costs … Package Approach – example IT build steps Portal Foundation Content Management Search Engine Application Layer Data Layer Infrastructure Business Layer Application Server Database(s) Network & System Management Presentation Layer
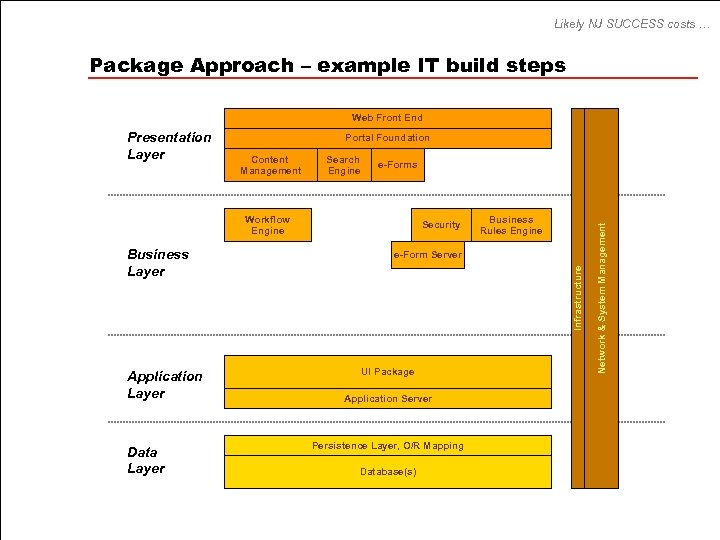
Likely NJ SUCCESS costs … Package Approach – example IT build steps Web Front End Portal Foundation Content Management Search Engine e-Forms Workflow Engine Application Layer Data Layer Business Rules Engine e-Form Server Infrastructure Business Layer Security UI Package Application Server Persistence Layer, O/R Mapping Database(s) Network & System Management Presentation Layer
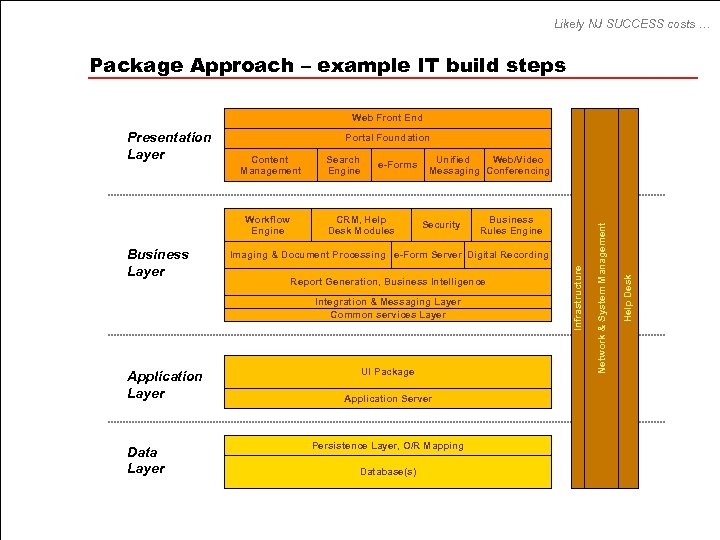
Likely NJ SUCCESS costs … Package Approach – example IT build steps Web Front End Portal Foundation Business Layer e-Forms CRM, Help Desk Modules Unified Web/Video Messaging Conferencing Security Imaging & Document Processing e-Form Server Digital Recording Report Generation, Business Intelligence Integration & Messaging Layer Common services Layer Application Layer Data Layer Business Rules Engine UI Package Application Server Persistence Layer, O/R Mapping Database(s) Help Desk Workflow Engine Search Engine Network & System Management Content Management Infrastructure Presentation Layer
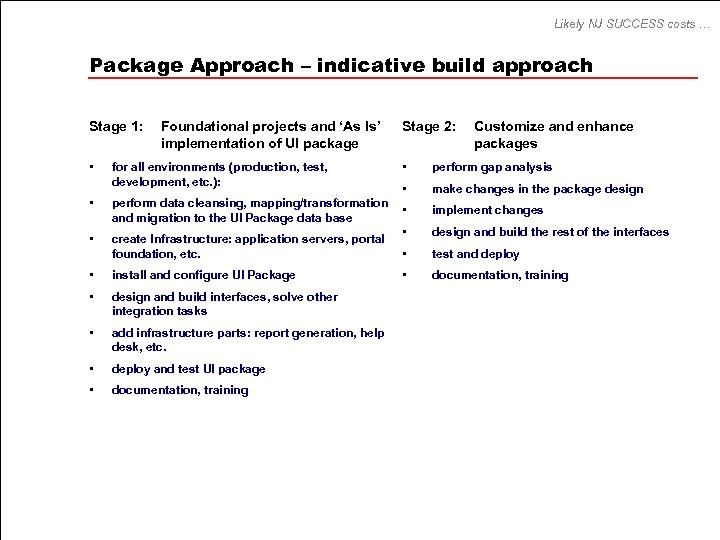
Likely NJ SUCCESS costs … Package Approach – indicative build approach Stage 1: Foundational projects and ‘As Is’ implementation of UI package • for all environments (production, test, development, etc. ): • perform data cleansing, mapping/transformation and migration to the UI Package data base • create Infrastructure: application servers, portal foundation, etc. • install and configure UI Package • design and build interfaces, solve other integration tasks • add infrastructure parts: report generation, help desk, etc. • deploy and test UI package • documentation, training Stage 2: Customize and enhance packages • perform gap analysis • make changes in the package design • implement changes • design and build the rest of the interfaces • test and deploy • documentation, training
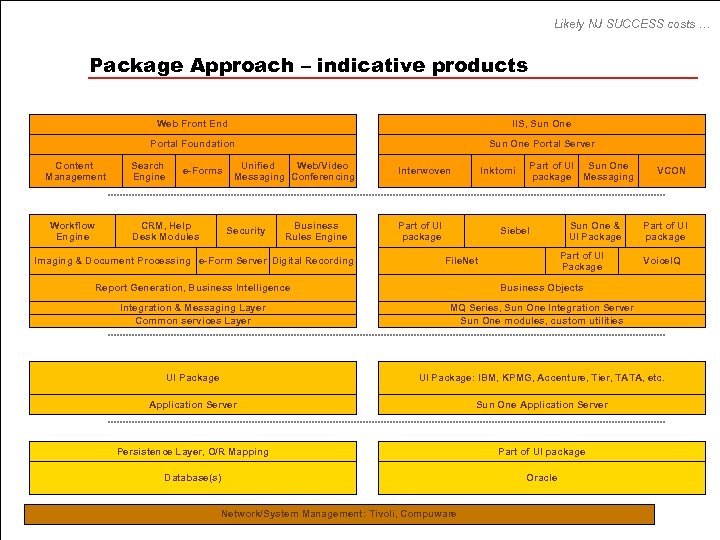
Likely NJ SUCCESS costs … Package Approach – indicative products Web Front End Portal Foundation Content Management Workflow Engine IIS, Sun One Portal Server Search Engine e-Forms CRM, Help Desk Modules Unified Web/Video Messaging Conferencing Security Business Rules Engine Imaging & Document Processing e-Form Server Digital Recording Interwoven Inktomi Part of UI package Part of UI Sun One package Messaging Siebel Sun One & UI Package Part of UI Package File. Net VCON Part of UI package Voice. IQ Report Generation, Business Intelligence Business Objects Integration & Messaging Layer Common services Layer MQ Series, Sun One Integration Server Sun One modules, custom utilities UI Package: IBM, KPMG, Accenture, Tier, TATA, etc. Application Server Sun One Application Server Persistence Layer, O/R Mapping Part of UI package Database(s) Oracle Network/System Management: Tivoli, Compuware
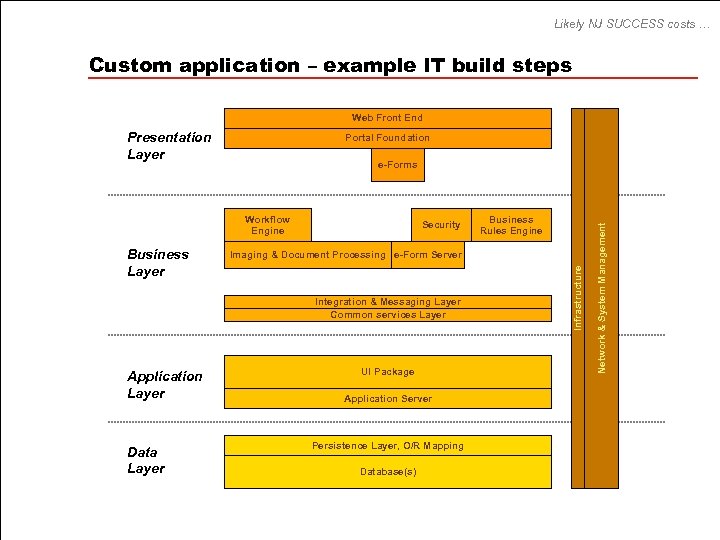
Likely NJ SUCCESS costs … Custom application – example IT build steps Presentation Layer Business Layer Application Layer Database(s)
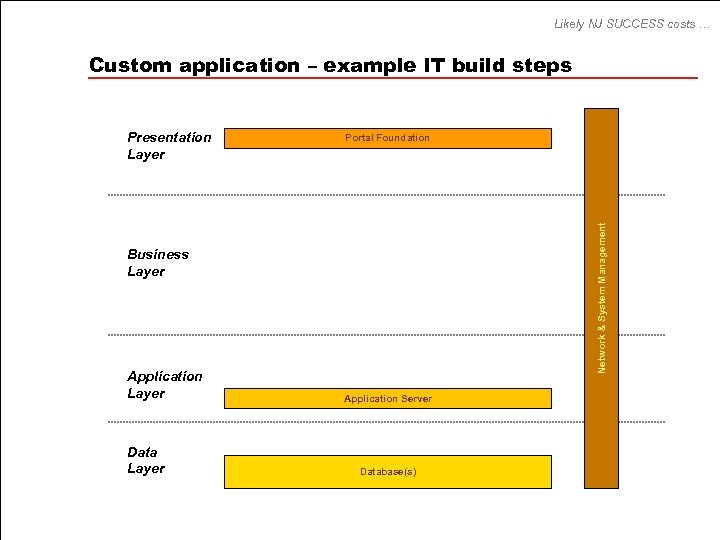
Likely NJ SUCCESS costs … Custom application – example IT build steps Portal Foundation Network & System Management Presentation Layer Business Layer Application Layer Data Layer Application Server Database(s)
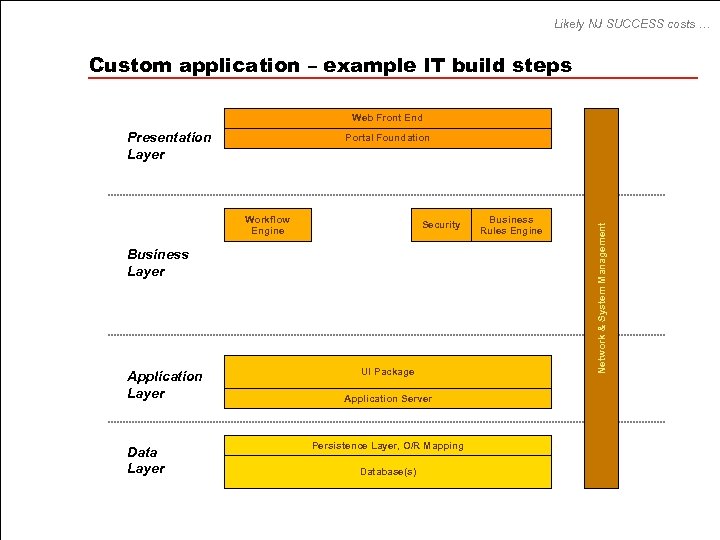
Likely NJ SUCCESS costs … Custom application – example IT build steps Web Front End Presentation Layer Workflow Engine Security Business Layer Application Layer Data Layer UI Package Application Server Persistence Layer, O/R Mapping Database(s) Business Rules Engine Network & System Management Portal Foundation
Likely NJ SUCCESS costs … Custom application – example IT build steps Web Front End Presentation Layer Portal Foundation Workflow Engine Imaging & Document Processing e-Form Server Integration & Messaging Layer Common services Layer Application Layer Data Layer Business Rules Engine UI Package Application Server Persistence Layer, O/R Mapping Database(s) Infrastructure Business Layer Security Network & System Management e-Forms
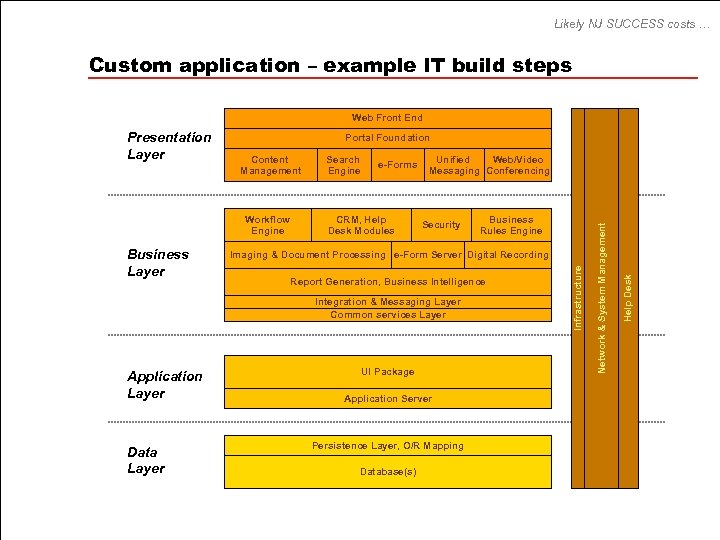
Likely NJ SUCCESS costs … Custom application – example IT build steps Web Front End Portal Foundation Business Layer e-Forms CRM, Help Desk Modules Unified Web/Video Messaging Conferencing Security Imaging & Document Processing e-Form Server Digital Recording Report Generation, Business Intelligence Integration & Messaging Layer Common services Layer Application Layer Data Layer Business Rules Engine UI Package Application Server Persistence Layer, O/R Mapping Database(s) Help Desk Workflow Engine Search Engine Network & System Management Content Management Infrastructure Presentation Layer
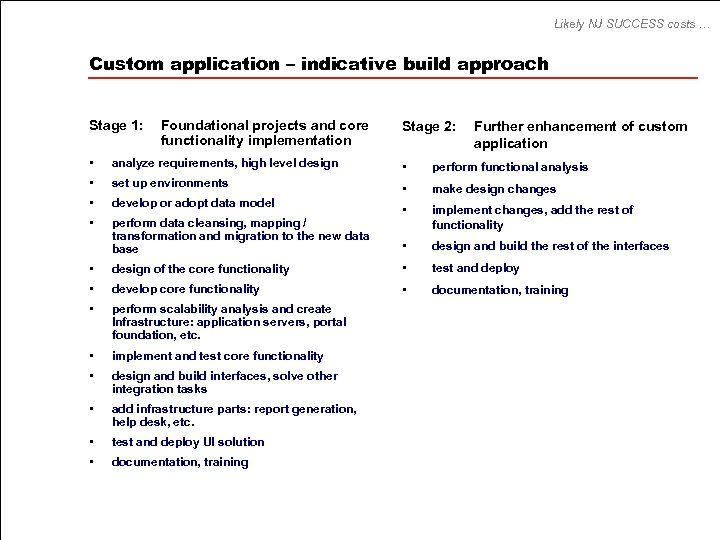
Likely NJ SUCCESS costs … Custom application – indicative build approach Stage 1: Foundational projects and core functionality implementation Stage 2: Further enhancement of custom application • analyze requirements, high level design • perform functional analysis • set up environments • make design changes • develop or adopt data model • perform data cleansing, mapping / transformation and migration to the new data base • implement changes, add the rest of functionality • design and build the rest of the interfaces • design of the core functionality • test and deploy • develop core functionality • documentation, training • perform scalability analysis and create Infrastructure: application servers, portal foundation, etc. • implement and test core functionality • design and build interfaces, solve other integration tasks • add infrastructure parts: report generation, help desk, etc. • test and deploy UI solution • documentation, training
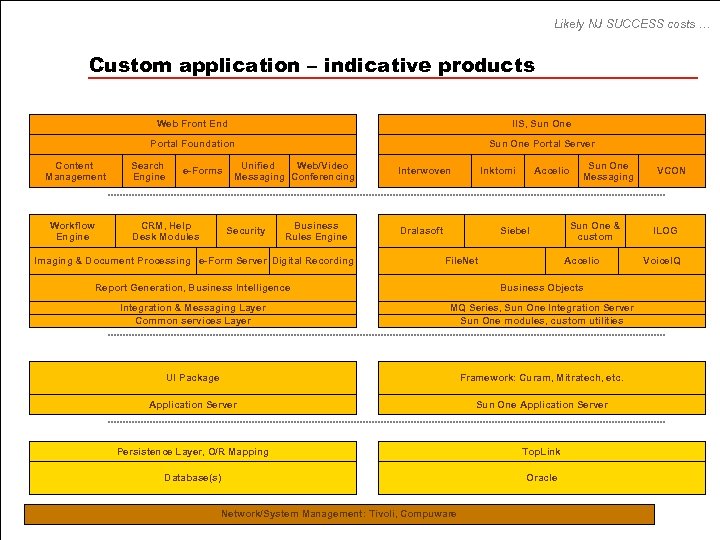
Likely NJ SUCCESS costs … Custom application – indicative products Web Front End Portal Foundation Content Management Workflow Engine IIS, Sun One Portal Server Search Engine e-Forms CRM, Help Desk Modules Unified Web/Video Messaging Conferencing Security Business Rules Engine Imaging & Document Processing e-Form Server Digital Recording Interwoven Inktomi Dralasoft Accelio Siebel File. Net Sun One Messaging Sun One & custom Accelio Report Generation, Business Intelligence Business Objects Integration & Messaging Layer Common services Layer MQ Series, Sun One Integration Server Sun One modules, custom utilities UI Package Framework: Curam, Mitratech, etc. Application Server Sun One Application Server Persistence Layer, O/R Mapping Top. Link Database(s) Oracle Network/System Management: Tivoli, Compuware VCON ILOG Voice. IQ
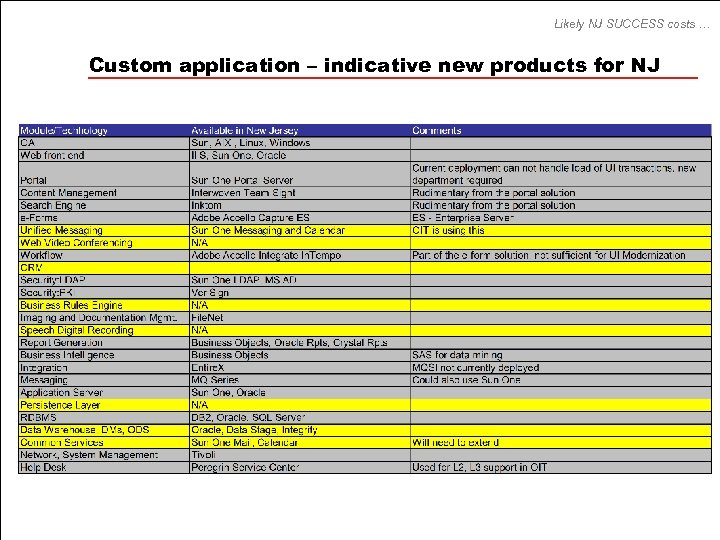
Likely NJ SUCCESS costs … Custom application – indicative new products for NJ
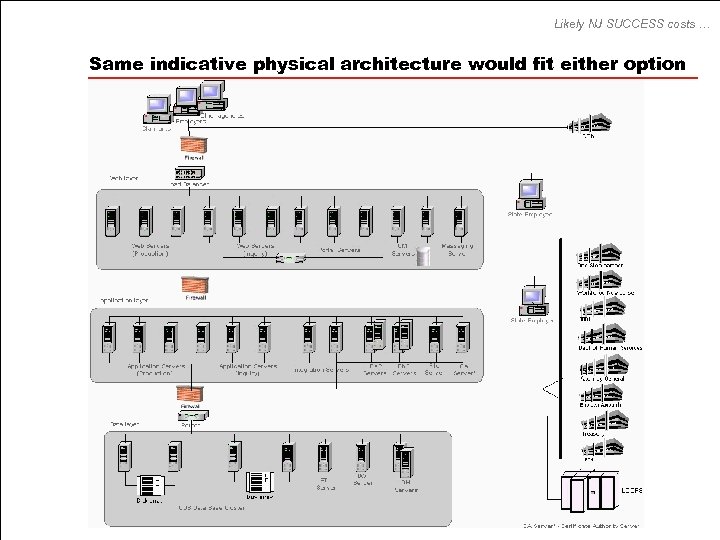
Likely NJ SUCCESS costs … Same indicative physical architecture would fit either option
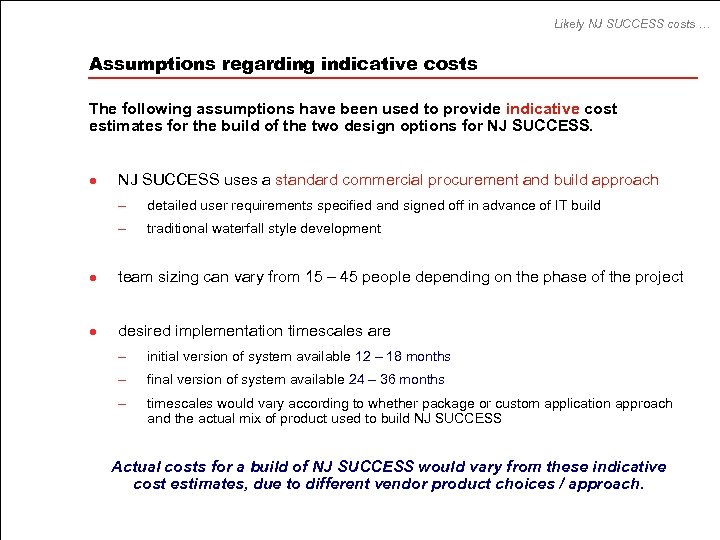
Likely NJ SUCCESS costs … Assumptions regarding indicative costs The following assumptions have been used to provide indicative cost estimates for the build of the two design options for NJ SUCCESS. l NJ SUCCESS uses a standard commercial procurement and build approach – detailed user requirements specified and signed off in advance of IT build – traditional waterfall style development l team sizing can vary from 15 – 45 people depending on the phase of the project l desired implementation timescales are – initial version of system available 12 – 18 months – final version of system available 24 – 36 months – timescales would vary according to whether package or custom application approach and the actual mix of product used to build NJ SUCCESS Actual costs for a build of NJ SUCCESS would vary from these indicative cost estimates, due to different vendor product choices / approach.
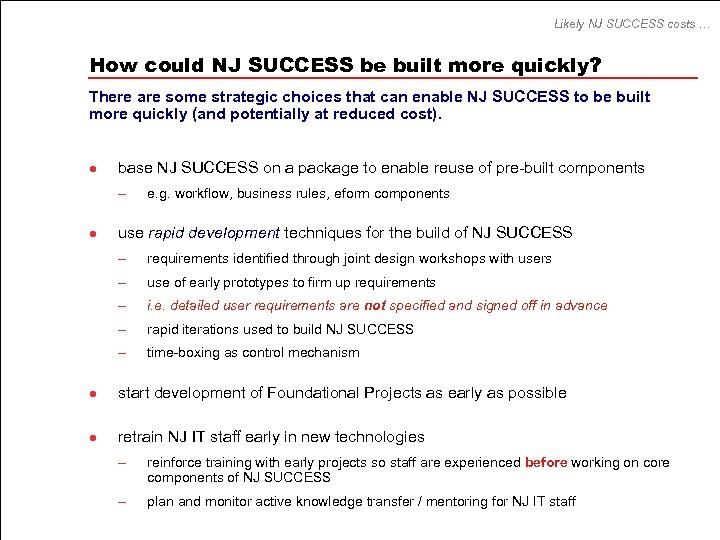
Likely NJ SUCCESS costs … How could NJ SUCCESS be built more quickly? There are some strategic choices that can enable NJ SUCCESS to be built more quickly (and potentially at reduced cost). l base NJ SUCCESS on a package to enable reuse of pre-built components – l e. g. workflow, business rules, eform components use rapid development techniques for the build of NJ SUCCESS – requirements identified through joint design workshops with users – use of early prototypes to firm up requirements – i. e. detailed user requirements are not specified and signed off in advance – rapid iterations used to build NJ SUCCESS – time-boxing as control mechanism l start development of Foundational Projects as early as possible l retrain NJ IT staff early in new technologies – reinforce training with early projects so staff are experienced before working on core components of NJ SUCCESS – plan and monitor active knowledge transfer / mentoring for NJ IT staff
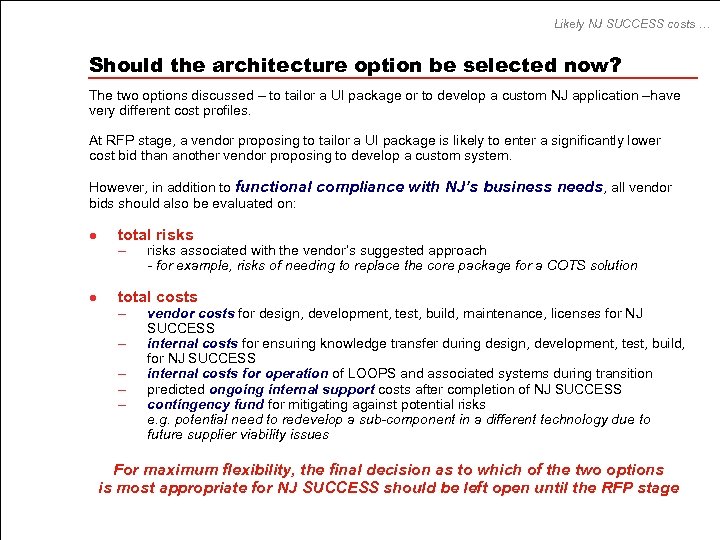
Likely NJ SUCCESS costs … Should the architecture option be selected now? The two options discussed – to tailor a UI package or to develop a custom NJ application –have very different cost profiles. At RFP stage, a vendor proposing to tailor a UI package is likely to enter a significantly lower cost bid than another vendor proposing to develop a custom system. However, in addition to functional compliance with NJ’s business needs, all vendor bids should also be evaluated on: l total risks – l risks associated with the vendor’s suggested approach - for example, risks of needing to replace the core package for a COTS solution total costs – – – vendor costs for design, development, test, build, maintenance, licenses for NJ SUCCESS internal costs for ensuring knowledge transfer during design, development, test, build, for NJ SUCCESS internal costs for operation of LOOPS and associated systems during transition predicted ongoing internal support costs after completion of NJ SUCCESS contingency fund for mitigating against potential risks e. g. potential need to redevelop a sub-component in a different technology due to future supplier viability issues For maximum flexibility, the final decision as to which of the two options is most appropriate for NJ SUCCESS should be left open until the RFP stage
![RFP crosswalk… RFP crosswalk Page(s) Provide a conceptual [logical] architecture 18 - 34 Provide RFP crosswalk… RFP crosswalk Page(s) Provide a conceptual [logical] architecture 18 - 34 Provide](https://present5.com/presentation/d497455fcc9ad50e5d18c53c9401f3bd/image-98.jpg)
RFP crosswalk… RFP crosswalk Page(s) Provide a conceptual [logical] architecture 18 - 34 Provide a technical architecture (‘components of the environment’) Recommend hardware and software options 48 -76 35 – 39, 77 – 86, Appendices Analyze COTS vs custom development 77 - 92 Demonstrate compliance with State standards 65 - 67 Demonstrate preferential use of State IT services already available 72 Demonstrate involvement of State UI IT experts 65, 67, 71, Appendices Demonstrate options analysis, where appropriate 35 - 39, 77 - 87 Demonstrate research on technologies and costs 88 – 92, Appendices
The RFP requirements for this deliverable UI Modernization RFP Requirements “ 3. 2. 3. 4 Technical Architecture Document (Price Line #5) The Contractor must develop a Technical Architecture Document, containing both narrative and diagrammatic elements, detailing the preferred technical configuration. The Technical Architecture Document must include a conceptual description of the principal components of the envisioned environment; including data stores, data integration methods, servers, applications, networking (including capacity impact on database and network infrastructure, i. e. bandwidth), user access control provisions, and data integrity measures. The Technical Architecture Document must also include recommendations for generic hardware and software at the platform level. Software recommendations should include COTS consideration as well as custom development. The technical architecture must be fully compliant with the State of New Jersey's established IT standards and policies (see Appendix H OIT Technical Guidelines and Appendix I Statewide and Labor IT Standards). It must make preferential use of the technical infrastructure and facilities already available to New Jersey State agencies, unless there is compelling justification for doing otherwise, as approved. It is essential that the technical architecture reflect the knowledge and judgment of State technical experts familiar with the Division of UI's current systems, including those in both NJDOL and OIT, as well as the Contractor's own technical expertise and familiarity with industry best practices. Where alternative technical approaches are feasible, the Contractor must provide a thorough justification for the recommended configuration or component, such as a criteria-based comparative evaluation of the alternatives. The evaluation must also include supporting third party ratings, references to technical literature, brochures and references. This evaluation must include an assessment of the business and technical risks associated with each alternative considered as well as the financial impact”.
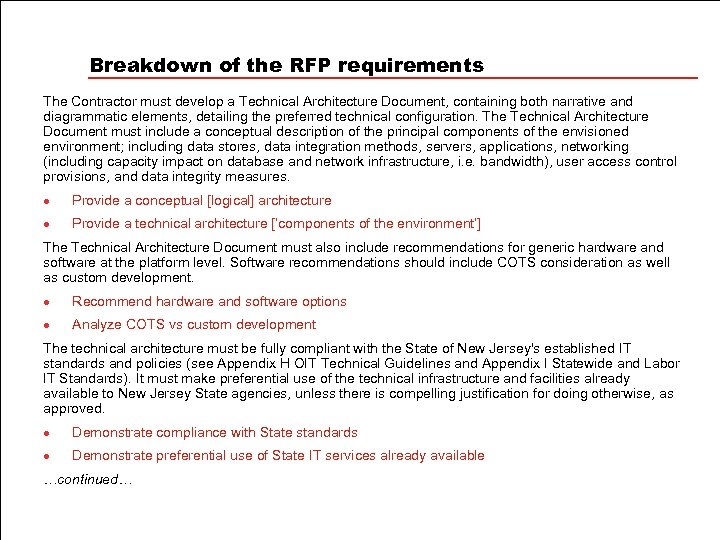
Breakdown of the RFP requirements The Contractor must develop a Technical Architecture Document, containing both narrative and diagrammatic elements, detailing the preferred technical configuration. The Technical Architecture Document must include a conceptual description of the principal components of the envisioned environment; including data stores, data integration methods, servers, applications, networking (including capacity impact on database and network infrastructure, i. e. bandwidth), user access control provisions, and data integrity measures. l Provide a conceptual [logical] architecture l Provide a technical architecture [‘components of the environment’] The Technical Architecture Document must also include recommendations for generic hardware and software at the platform level. Software recommendations should include COTS consideration as well as custom development. l Recommend hardware and software options l Analyze COTS vs custom development The technical architecture must be fully compliant with the State of New Jersey's established IT standards and policies (see Appendix H OIT Technical Guidelines and Appendix I Statewide and Labor IT Standards). It must make preferential use of the technical infrastructure and facilities already available to New Jersey State agencies, unless there is compelling justification for doing otherwise, as approved. l Demonstrate compliance with State standards l Demonstrate preferential use of State IT services already available …continued…
Breakdown of the RFP requirements (cont) It is essential that the technical architecture reflect the knowledge and judgment of State technical experts familiar with the Division of UI's current systems, including those in both NJDOL and OIT, as well as the Contractor's own technical expertise and familiarity with industry best practices. l Demonstrate involvement of State UI IT experts Where alternative technical approaches are feasible, the Contractor must provide a thorough justification for the recommended configuration or component, such as a criteria-based comparative evaluation of the alternatives. l Demonstrate options analysis, where appropriate The evaluation must also include supporting third party ratings, references to technical literature, brochures and references. This evaluation must include an assessment of the business and technical risks associated with each alternative considered as well as the financial impact”. l Demonstrate research on technologies and costs
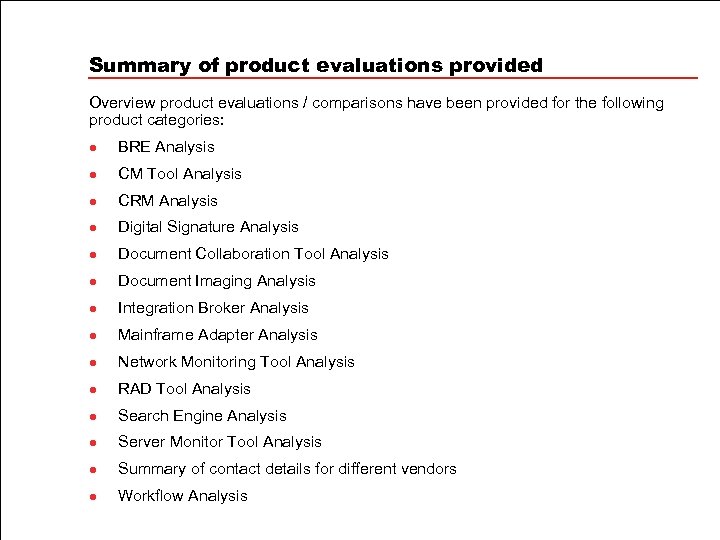
Summary of product evaluations provided Overview product evaluations / comparisons have been provided for the following product categories: l BRE Analysis l CM Tool Analysis l CRM Analysis l Digital Signature Analysis l Document Collaboration Tool Analysis l Document Imaging Analysis l Integration Broker Analysis l Mainframe Adapter Analysis l Network Monitoring Tool Analysis l RAD Tool Analysis l Search Engine Analysis l Server Monitor Tool Analysis l Summary of contact details for different vendors l Workflow Analysis
d497455fcc9ad50e5d18c53c9401f3bd.ppt