9f8e9798a2db214d542258ee2d5c8bbd.ppt
- Количество слайдов: 109
Network Security Refik MOLVA Institut Eurécom B. P. 193 06904 Sophia Antipolis Cedex - France Refik. Molva@eurecom. fr ÓInstitut Eurecom 2002

Outline THEORY 1. Symmetric Cryptography 2. Asymmetric Cryptography 3. Hash Functions and Integrity 4. Authentication 5. Key Management APPLICATIONS 6. Internet Security Using Firewalls 7. Internet Security with Cryptographic Mechanisms 9. Multicast Security Network Security - R. Molva - ÓInstitut Eurecom 2002
Security Services 7498 -2 ISO standard defines : security services and mechanisms in the context of OSI r function placement in OSI layers r does not cover the security of standalone systems. r authentication r access control r confidentiality r integrity r non-repudiation Network Security - R. Molva - ÓInstitut Eurecom 2002

Services vs. Layers 1. Application Layer Security finest granularity (user and program verification) r end-to-end security r non-transparent to applications r 2. Transport Layer medium level granularity (end-users are not visible) r end-to-end security r transparent to applications r 3. Network Layer low granularity r no end-to-end security (hop-by-hop security relies on intermediate systems) r transparent to applications r 4. Physical Layer like network layer security, plus r ease of integration r limited functionality (hardware only) r Network Security - R. Molva - ÓInstitut Eurecom 2002
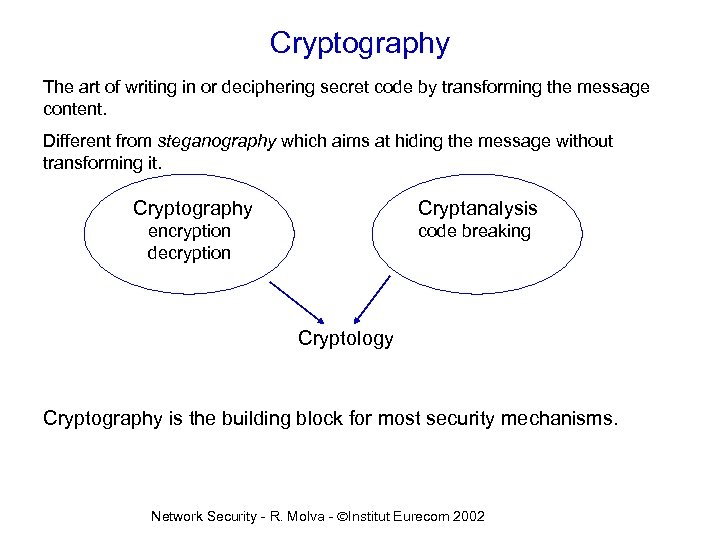
Cryptography The art of writing in or deciphering secret code by transforming the message content. Different from steganography which aims at hiding the message without transforming it. Cryptography Cryptanalysis encryption decryption code breaking Cryptology Cryptography is the building block for most security mechanisms. Network Security - R. Molva - ÓInstitut Eurecom 2002
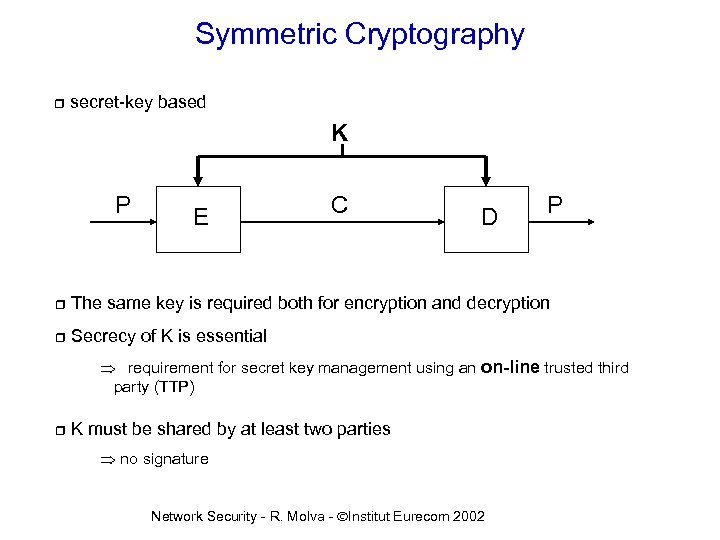
Symmetric Cryptography r secret-key based K P E C D P r The same key is required both for encryption and decryption r Secrecy of K is essential requirement for secret key management using an on-line trusted third party (TTP) r K must be shared by at least two parties no signature Network Security - R. Molva - ÓInstitut Eurecom 2002

DES E (encryption) k 1 R 1 Input 64 -bit k 2 k 15 R 2 k 16 R 15 R 16 IP-1 IP R 16 R 15 k 16 R 2 k 15 R 1 k 1 D (decryption) IP : initial permutation, IP-1(IP(x)) = x Ri : key-dependent functions ki : 16 sub-keys(48 bits) (key schedule) result of shift and select operations on 56 -bit K Network Security - R. Molva - ÓInstitut Eurecom 2002 Output 64 -bit
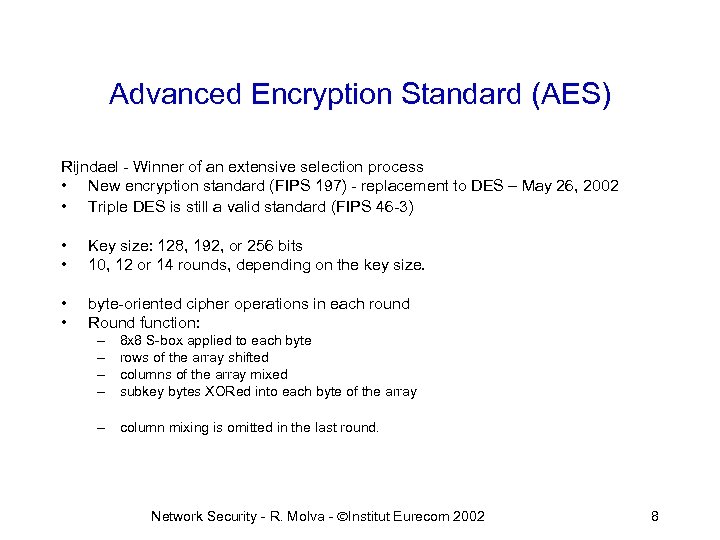
Advanced Encryption Standard (AES) Rijndael - Winner of an extensive selection process • New encryption standard (FIPS 197) - replacement to DES – May 26, 2002 • Triple DES is still a valid standard (FIPS 46 -3) • • Key size: 128, 192, or 256 bits 10, 12 or 14 rounds, depending on the key size. • • byte-oriented cipher operations in each round Round function: – – 8 x 8 S-box applied to each byte rows of the array shifted columns of the array mixed subkey bytes XORed into each byte of the array – column mixing is omitted in the last round. Network Security - R. Molva - ÓInstitut Eurecom 2002 8

AES-Rijndael Performance • “…a machine that could recover a DES key in a second then it would take that machine approximately 149 thousand-billion (149 trillion) years to crack a 128 -bit AES key. To put that into perspective, the universe is believed to be less than 20 billion years old. ” • Key setup time – 200 keys /msec in 32 bit C / Apple G 4 Power. PC • Encryption speed – 52 Mbits/s in 32 bit C / Apple Power. PC – 4. 8 Mbits/s in Java / Intel Pentium Pro 200 Network Security - R. Molva - ÓInstitut Eurecom 2002 9

Asymmetric Cryptography r public-key cryptography K’ P E K C D r Different keys for encryption and decryption r Each user has a secret key (K) and a public key (K’) r P No shared secret between the origin and the recipient þno need to manage secret keys but integrity of K’ must be assured with an offline trusted third party (TTP) þdigital signature is possible Network Security - R. Molva - ÓInstitut Eurecom 2002

Asymmetric Cryptography r each user U has a secret key KSU r everybody can access KPU (public database) r only U knows KSU Name : A, Key : KPa Name : B, Key : KPb and a public key KPU A, KPa Name : C, Key : KPc EKPa (message) A, KPa EKPa (message) A KSa r DKSu (EKPu(X)) = x et EKPu (DKSu(X)) = x Network Security - R. Molva - ÓInstitut Eurecom 2002
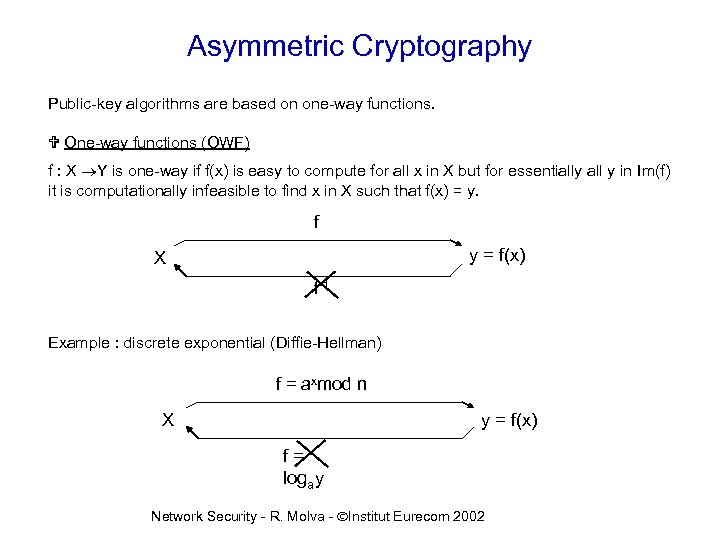
Asymmetric Cryptography Public-key algorithms are based on one-way functions. V One-way functions (OWF) f : X Y is one-way if f(x) is easy to compute for all x in X but for essentially all y in Im(f) it is computationally infeasible to find x in X such that f(x) = y. f y = f(x) X f-1 Example : discrete exponential (Diffie-Hellman) f = axmod n X y = f(x) f= logay Network Security - R. Molva - ÓInstitut Eurecom 2002
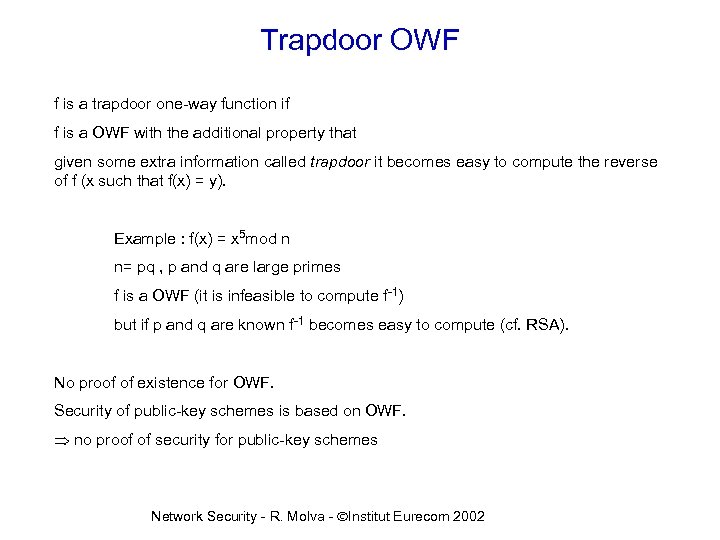
Trapdoor OWF f is a trapdoor one-way function if f is a OWF with the additional property that given some extra information called trapdoor it becomes easy to compute the reverse of f (x such that f(x) = y). Example : f(x) = x 5 mod n n= pq , p and q are large primes f is a OWF (it is infeasible to compute f-1) but if p and q are known f-1 becomes easy to compute (cf. RSA). No proof of existence for OWF. Security of public-key schemes is based on OWF. no proof of security for public-key schemes Network Security - R. Molva - ÓInstitut Eurecom 2002

The DIFFIE-HELLMAN Algorithm r pioneer of public key algorithms A and B set a shared secret (axy mod p ) without exchanging secret information. r axy mod p can be used as a secret key with a symmetrical algorithm to encrypt data. r relies on the difficulty of computing discrete log. r Network Security - R. Molva - ÓInstitut Eurecom 2002 14

RSA r message structured in n bit blocks r for each block P of cleartext : V encryption: V decryption: r C = P e mod r P = C d mod r main property (non-trivial): (xe)d º (xd)e º x (mod r) þsecurity relies on the choice of r, e and d Network Security - R. Molva - ÓInstitut Eurecom 2002
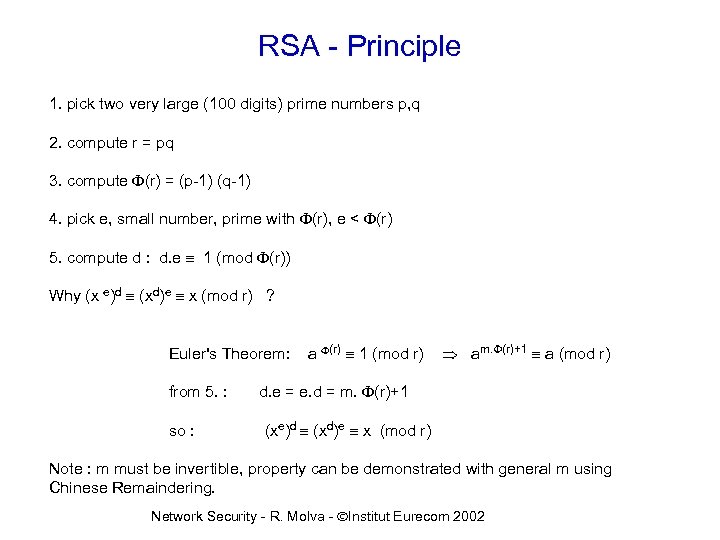
RSA - Principle 1. pick two very large (100 digits) prime numbers p, q 2. compute r = pq 3. compute F(r) = (p-1) (q-1) 4. pick e, small number, prime with F(r), e < F(r) 5. compute d : d. e º 1 (mod F(r)) Why (x e)d º (xd)e º x (mod r) ? Euler's Theorem: from 5. : so : a F(r) º 1 (mod r) am. F(r)+1 º a (mod r) d. e = e. d = m. F(r)+1 (xe)d º (xd)e º x (mod r) Note : m must be invertible, property can be demonstrated with general m using Chinese Remaindering. Network Security - R. Molva - ÓInstitut Eurecom 2002

RSA - Example 1. p =17, q =13 2. r = 221 3. F(r) = (p-1) (q-1) = 192 4. e = 11 5. d = 35 , d. e ( 1 (mod 192) e = 11 P = 123 E d = 35 C = 12311(mod 221) C = 115 D Network Security - R. Molva - ÓInstitut Eurecom 2002 C = 11535(mod 221) P = 123
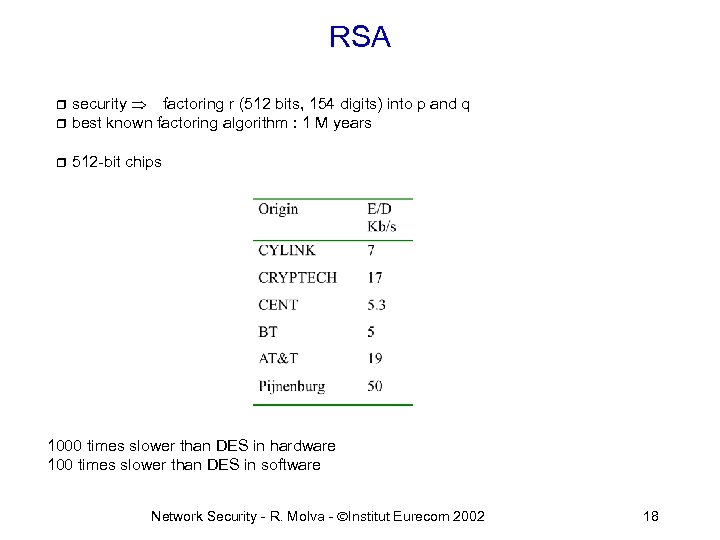
RSA security factoring r (512 bits, 154 digits) into p and q r best known factoring algorithm : 1 M years r r 512 -bit chips 1000 times slower than DES in hardware 100 times slower than DES in software Network Security - R. Molva - ÓInstitut Eurecom 2002 18

El Gamal Public Key Encryption r DH key agreement in encryption p is prime, x and y in Zp-1 a is a generator in Zp. b=ay mod p KPB = ( p, a, b) is the public key. KSB = y is the secret key. Known by A x (random) Known by B y Public Key (p, a, ay mod p) ay mod p axy mod p Encryption: m 1 = ax mod p m 2 = m. axy mod p m 1=DH key agreement + m 2=encrypted message Decryption: m 1 axy mod p m = m 2. (m 1 y)-1 mod p = m. axy. ((ax)y)-1 mod p Network Security - R. Molva - ÓInstitut Eurecom 2002 19
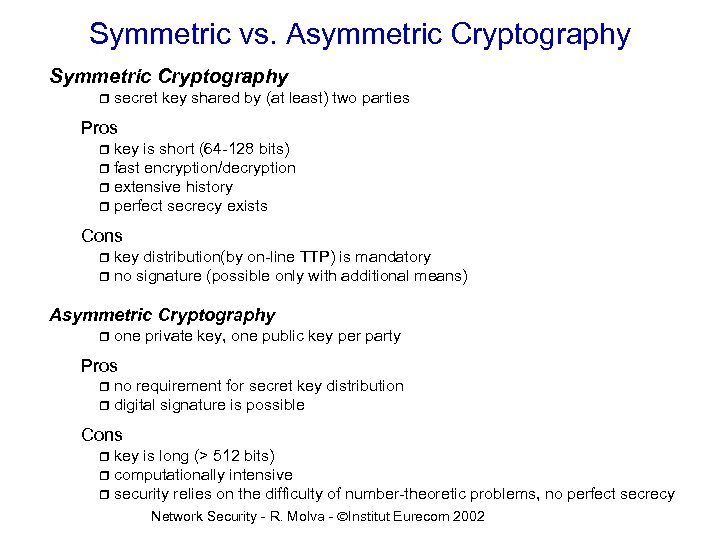
Symmetric vs. Asymmetric Cryptography Symmetric Cryptography r secret key shared by (at least) two parties Pros key is short (64 -128 bits) r fast encryption/decryption r extensive history r perfect secrecy exists r Cons key distribution(by on-line TTP) is mandatory r no signature (possible only with additional means) r Asymmetric Cryptography r one private key, one public key per party Pros no requirement for secret key distribution r digital signature is possible r Cons key is long (> 512 bits) r computationally intensive r security relies on the difficulty of number-theoretic problems, no perfect secrecy r Network Security - R. Molva - ÓInstitut Eurecom 2002

Symmetric vs. Asymmetric Cryptography Summary Use Asymmetric Cryptography for key distribution (for symmetric keys) r digital signature r Use Symmetric Cryptography for bulk data encryption r data integrity r Network Security - R. Molva - ÓInstitut Eurecom 2002
Plaintext Network Security - R. Molva - ÓInstitut Eurecom 2002

DES-ECB Encryption Network Security - R. Molva - ÓInstitut Eurecom 2002 23

DES-CBC Encryption Network Security - R. Molva - ÓInstitut Eurecom 2002
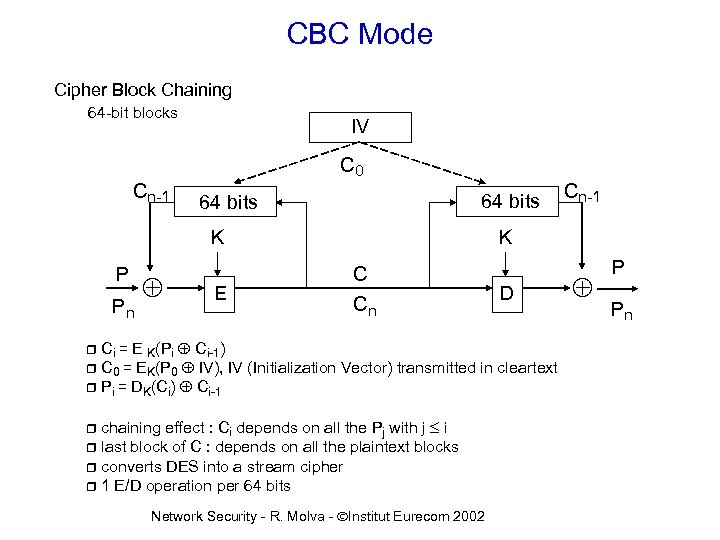
CBC Mode Cipher Block Chaining 64 -bit blocks IV C 0 Cn-1 64 bits K P Pn E Cn-1 K C Cn D Ci = E K(Pi Ci-1) r C 0 = EK(P 0 IV), IV (Initialization Vector) transmitted in cleartext r Pi = DK(Ci) Ci-1 r chaining effect : Ci depends on all the Pj with j £ i r last block of C : depends on all the plaintext blocks r converts DES into a stream cipher r 1 E/D operation per 64 bits r Network Security - R. Molva - ÓInstitut Eurecom 2002 P Pn
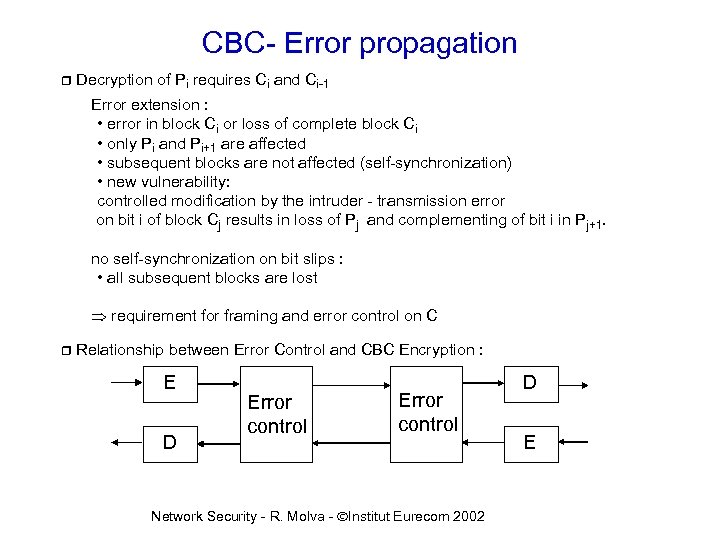
CBC- Error propagation r Decryption of Pi requires Ci and Ci-1 Error extension : • error in block Ci or loss of complete block Ci • only Pi and Pi+1 are affected • subsequent blocks are not affected (self-synchronization) • new vulnerability: controlled modification by the intruder - transmission error on bit i of block Cj results in loss of Pj and complementing of bit i in Pj+1. no self-synchronization on bit slips : • all subsequent blocks are lost requirement for framing and error control on C r Relationship between Error Control and CBC Encryption : E D Error control Network Security - R. Molva - ÓInstitut Eurecom 2002 D E

CFB Mode Cipher Feedback n = variable block size for C and P, n £ 64 shift register IV shift register 64 bits 64 K 64 n E 64 K 64 Select n left bits n P n n C n 1 E/D operation / n bits s 0 : initial value of the register, transmitted in cleartext Network Security - R. Molva - ÓInstitut Eurecom 2002 P n
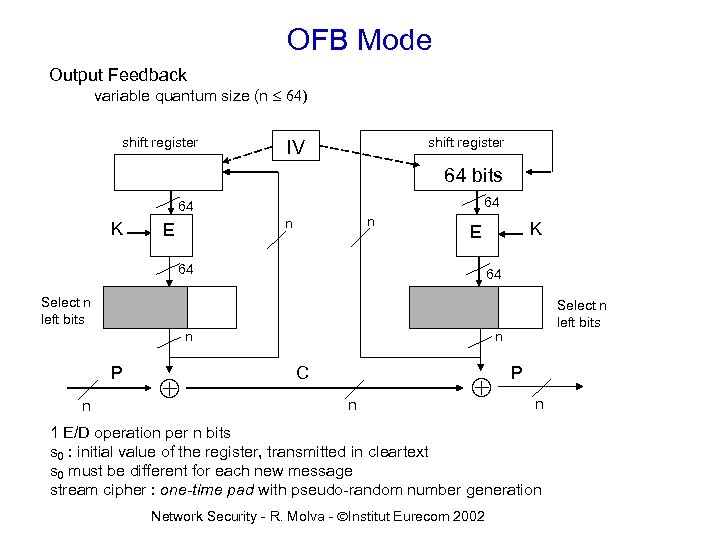
OFB Mode Output Feedback variable quantum size (n £ 64) shift register IV 64 bits 64 64 K n n E K E 64 64 Select n left bits n P n Select n left bits n C n P n 1 E/D operation per n bits s 0 : initial value of the register, transmitted in cleartext s 0 must be different for each new message stream cipher : one-time pad with pseudo-random number generation Network Security - R. Molva - ÓInstitut Eurecom 2002
Outline THEORY 1. Symmetric Cryptography 2. Asymmetric Cryptography 3. Hash Functions and Integrity 4. Authentication 5. Key Management APPLICATIONS 6. Internet Security Using Firewalls 7. Internet Security with Cryptographic Mechanisms 8. Multicast Security Network Security - R. Molva - ÓInstitut Eurecom 2002 29

Hash Functions message Arbitrary length h message digest fixed length (n ³ 128 bits) Main purpose : Modification Detection Codes (MDC), Manipulation Detection Codes or Message Integrity Check (MIC) Objective : data integrity with additional security means h(m) serves as a representative of message m if m changes, h(m) changes with high probability Security properties : • one-way: given y, finding x | h(x) = y is difficult. • collision resistence : it is difficult to find x ¹ x' | h(x) = h(x'). Network Security - R. Molva - ÓInstitut Eurecom 2002
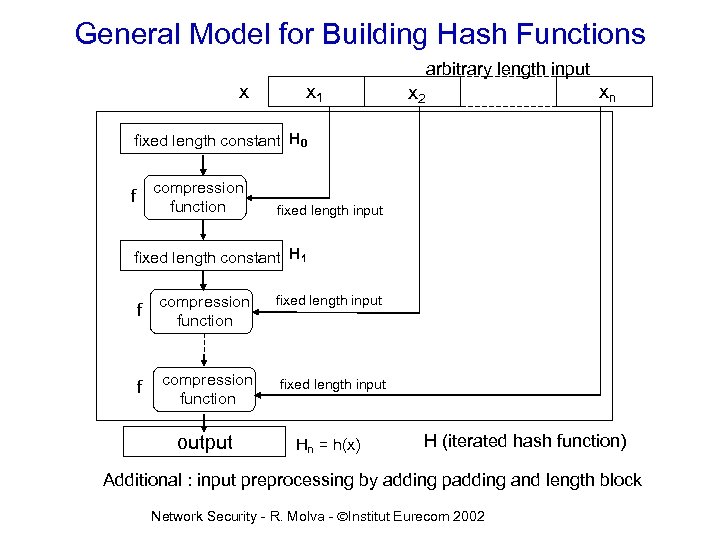
General Model for Building Hash Functions arbitrary length input x x 1 x 2 xn fixed length constant H 0 compression function f fixed length input fixed length constant H 1 f compression function output fixed length input Hn = h(x) H (iterated hash function) Additional : input preprocessing by adding padding and length block Network Security - R. Molva - ÓInstitut Eurecom 2002
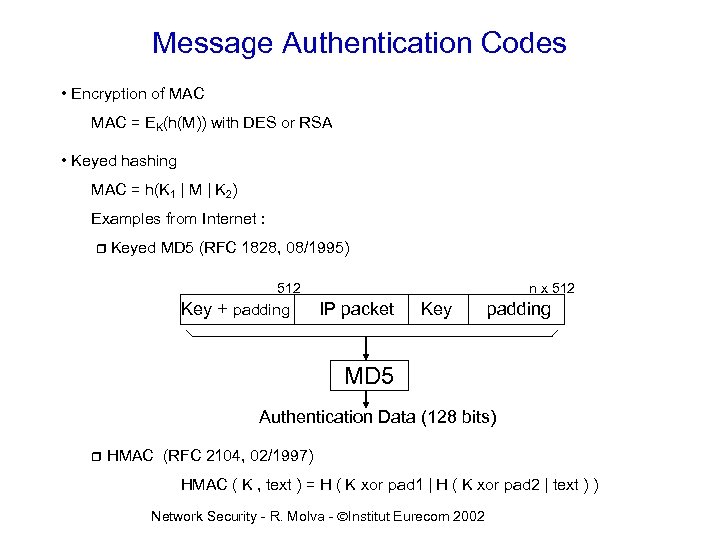
Message Authentication Codes • Encryption of MAC = EK(h(M)) with DES or RSA • Keyed hashing MAC = h(K 1 | M | K 2) Examples from Internet : r Keyed MD 5 (RFC 1828, 08/1995) 512 Key + padding n x 512 IP packet Key padding MD 5 Authentication Data (128 bits) r HMAC (RFC 2104, 02/1997) HMAC ( K , text ) = H ( K xor pad 1 | H ( K xor pad 2 | text ) ) Network Security - R. Molva - ÓInstitut Eurecom 2002
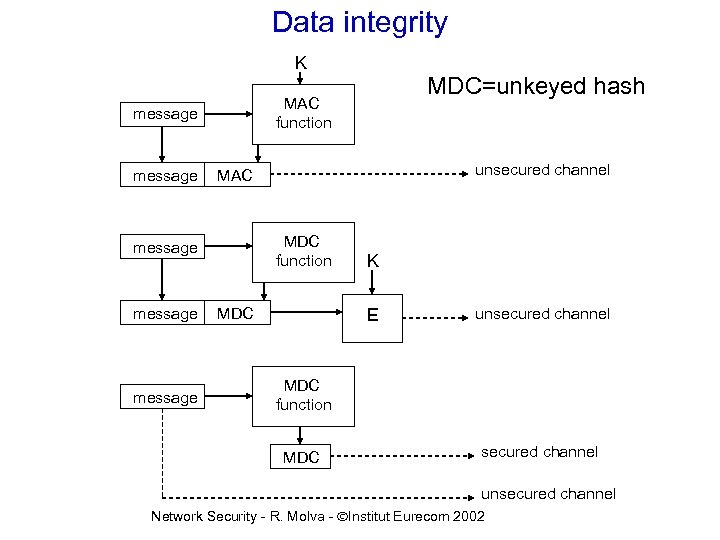
Data integrity K MAC function message unsecured channel MAC MDC function message MDC=unkeyed hash MDC K E unsecured channel MDC function MDC secured channel unsecured channel Network Security - R. Molva - ÓInstitut Eurecom 2002
Outline THEORY 1. Symmetric Cryptography 2. Asymmetric Cryptography 3. Hash Functions and Integrity 4. Authentication 5. Key Management APPLICATIONS 6. Internet Security Using Firewalls 7. Internet Security with Cryptographic Mechanisms 8. Multicast Security Network Security - R. Molva - ÓInstitut Eurecom 2002 34

Authentication Protocols (1/2) • Secret function of a predictable item A h. K(time stamp or counter) B • Synchronization requirement • synchronized clocks very difficult with distributed systems how to secure a global time service ? • counters losses how to secure re-synchronization? • Protocol requires only 1 message Network Security - R. Molva - ÓInstitut Eurecom 2002

Authentication Protocols (2/2) • Secret function of an unpredictable item (nonce : random number used only once) A N B h. K(N) • No need for synchronization • 2 messages • Mutual authentication A Na h. K(Na), Nb h. K(Nb) B Network Security - R. Molva - ÓInstitut Eurecom 2002
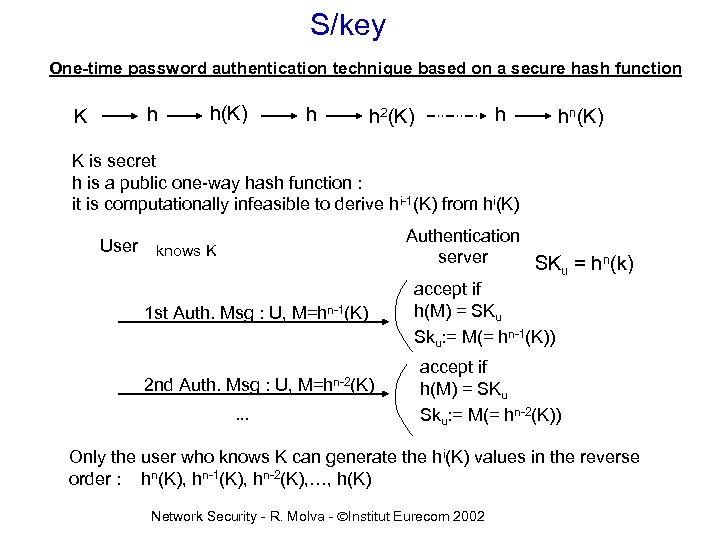
S/key One-time password authentication technique based on a secure hash function K h h(K) h h h 2(K) hn(K) K is secret h is a public one-way hash function : it is computationally infeasible to derive hi-1(K) from hi(K) User knows K 1 st Auth. Msg : U, M=hn-1(K) 2 nd Auth. Msg : U, . . . M=hn-2(K) Authentication server SKu = hn(k) accept if h(M) = SKu Sku: = M(= hn-1(K)) accept if h(M) = SKu Sku: = M(= hn-2(K)) Only the user who knows K can generate the hi(K) values in the reverse order : hn(K), hn-1(K), hn-2(K), …, h(K) Network Security - R. Molva - ÓInstitut Eurecom 2002
Passive Devices storage of non-secret verification value W in the device W=OWF(S), S is a secret kept by the user r r verification by a reader r authentication: - user enters secret value S - reader computes V=OWF(S) - reader compares V with W stored in the device r magnetic stripe cards r cards with a memory chip Network Security - R. Molva - ÓInstitut Eurecom 2002
Active Devices r r Able to run cryptographic algorithms and strong authentication protocols Eliminate the risk of exhaustive attacks and replay on the PIN 1. Personal computers 2. Tokens 3. Smart cards Principle : r PIN-based verification of the user by the personal device. PIN is not disclosed outside the protected area. r Personal device runs the authentication protocol on behalf of the user through untrusted environments. Strong authentication protocols resist to attacks from hostile public environment. Network Security - R. Molva - ÓInstitut Eurecom 2002
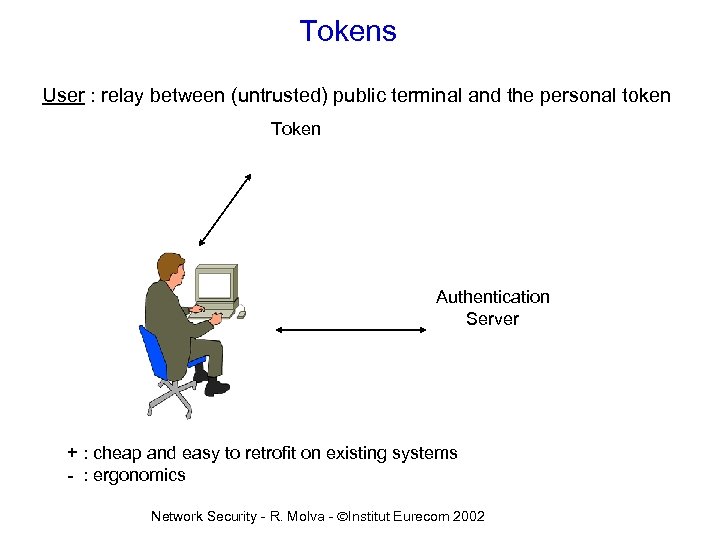
Tokens User : relay between (untrusted) public terminal and the personal token Token Authentication Server + : cheap and easy to retrofit on existing systems - : ergonomics Network Security - R. Molva - ÓInstitut Eurecom 2002

Smart Cards Communication between smart card and authentication server is transparent for the user After the user verification, the smart card runs the strong authenticationprotocol : • symmetrical (DES) or asymmetrical (RSA) algorithm • nonce-, time stamp-, or counter-based The card can perform other services : • data encryption • digital signature • message integrity Advanced smart cards include : • an operating system • a file system with access control • a Java virtual machine + : the most secure and user-friendly - : cost of deployment, retrofitting : a reader is required on each terminal Network Security - R. Molva - ÓInstitut Eurecom 2002
Digital Signature Generation of A’s signature on message M: S= EKSa(h(M)) r h is an unkeyed hash function (MD 5, SHA-1, . . . ) r KSa is A’s private RSA key Verification of A’s signature by any other party: compute h(M) r using A’s public key KPa, check if r DKPa(S) = h(M) Network Security - R. Molva - ÓInstitut Eurecom 2002 42
Outline THEORY 1. Symmetric Cryptography 2. Asymmetric Cryptography 3. Hash Functions and Integrity 4. Authentication 5. Key Management APPLICATIONS 6. Internet Security Using Firewalls 7. Internet Security with Cryptographic Mechanisms 8. Multicast Security Network Security - R. Molva - ÓInstitut Eurecom 2002 43
Key Management Most security mechanisms are based on cryptography. Cryptography requires: generation distribution storage archival deletion. . . of (secret and public) keys Network Security - R. Molva - ÓInstitut Eurecom 2002
Key Generation random number generation problem ·a random bit generator can be used to generate random numbers ·a random bit generator outputs a sequence of statistically independent and unbiased bits. Solutions : ·physical sources biased, de-skewing is necessary impractical ·pseudorandom bit generators Based on a truly random binary sequence of length k, generate a sequence of length l >> k using a deterministic algorithm. The output sequence appears to be random. Among all possible outputs (if it were truly random) only a fraction 2 k/2 l can be generated. The goal is to expand the truly random "seed" to a longer pseudorandom sequence. Network Security - R. Molva - ÓInstitut Eurecom 2002
Pseudorandom Bit Generators (PRBG) Security properties: • resistance to statistical tests : the output of a pseudorandom bit generator should not be distinguishable from a truly random sequence of the same length by a polynomial-time algorithm. • resistance to next-bit test : the next bit of the output sequence cannot be predicted based on the bit sequence that is already generated using a polynomial-time algorithm. • the two conditions are equivalent • a PRBG that fulfills one of these properties is said cryptographically secure. • in addition the k-bit seed must be large enough so that an exhaustive search over possible seeds is infeasible. Ex : linear congruence xn = axn-1 + b mod p is not secure because given a partial output sequence, the remainder of the output bits can be predicted. Network Security - R. Molva - ÓInstitut Eurecom 2002
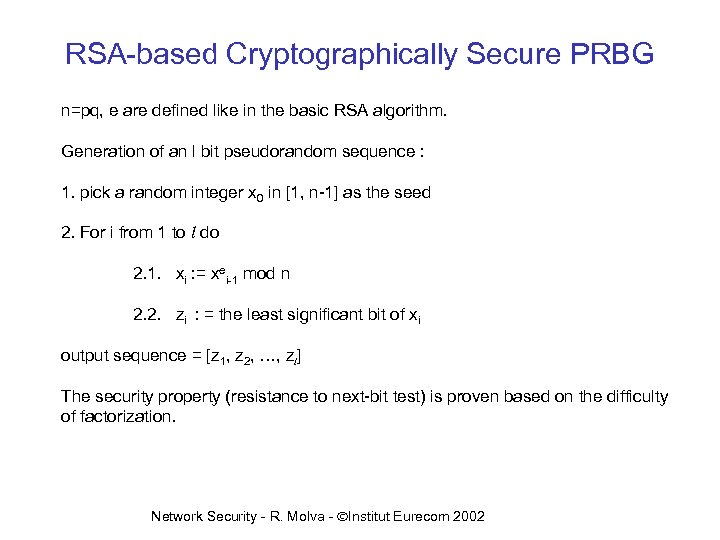
RSA-based Cryptographically Secure PRBG n=pq, e are defined like in the basic RSA algorithm. Generation of an l bit pseudorandom sequence : 1. pick a random integer x 0 in [1, n-1] as the seed 2. For i from 1 to l do 2. 1. xi : = xei-1 mod n 2. 2. zi : = the least significant bit of xi output sequence = [z 1, z 2, …, zl] The security property (resistance to next-bit test) is proven based on the difficulty of factorization. Network Security - R. Molva - ÓInstitut Eurecom 2002
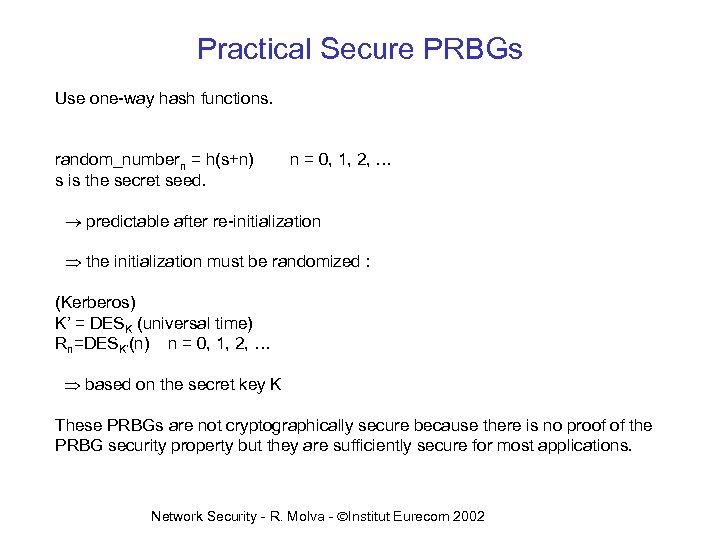
Practical Secure PRBGs Use one-way hash functions. random_numbern = h(s+n) s is the secret seed. n = 0, 1, 2, … predictable after re-initialization the initialization must be randomized : (Kerberos) K’ = DESK (universal time) Rn=DESK’(n) n = 0, 1, 2, … based on the secret key K These PRBGs are not cryptographically secure because there is no proof of the PRBG security property but they are sufficiently secure for most applications. Network Security - R. Molva - ÓInstitut Eurecom 2002
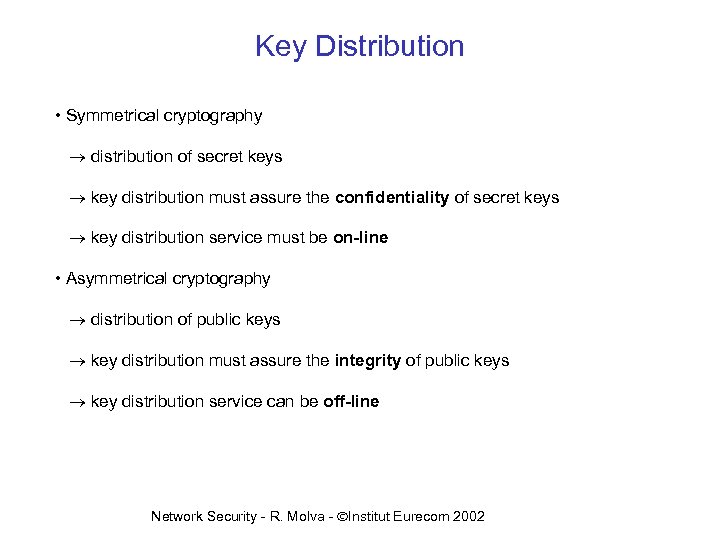
Key Distribution • Symmetrical cryptography distribution of secret keys key distribution must assure the confidentiality of secret keys key distribution service must be on-line • Asymmetrical cryptography distribution of public keys key distribution must assure the integrity of public keys key distribution service can be off-line Network Security - R. Molva - ÓInstitut Eurecom 2002
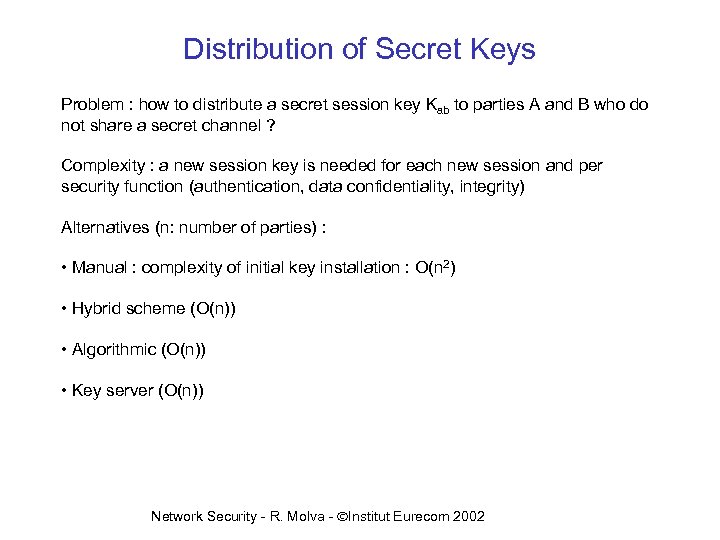
Distribution of Secret Keys Problem : how to distribute a secret session key Kab to parties A and B who do not share a secret channel ? Complexity : a new session key is needed for each new session and per security function (authentication, data confidentiality, integrity) Alternatives (n: number of parties) : • Manual : complexity of initial key installation : O(n 2) • Hybrid scheme (O(n)) • Algorithmic (O(n)) • Key server (O(n)) Network Security - R. Molva - ÓInstitut Eurecom 2002

Hybrid scheme Use public-key cryptography to distribute secret session keys. Use secret key (symmetrical) cryptography for bulk data encryption. A B KSa KSb Network Security - R. Molva - ÓInstitut Eurecom 2002
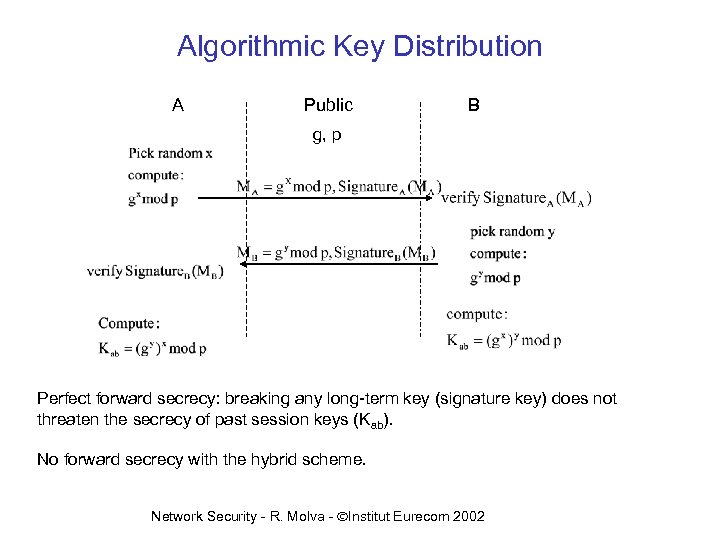
Algorithmic Key Distribution A Public B g, p Perfect forward secrecy: breaking any long-term key (signature key) does not threaten the secrecy of past session keys (Kab). No forward secrecy with the hybrid scheme. Network Security - R. Molva - ÓInstitut Eurecom 2002

Key distribution with a key server Key Server 2. Here are the envelopes for A and B Ka Kb 1. I am A, I want a key to communicate with B 3. Here is the shared key prove that you are B A 4. Here is my proof, prove that you are A Ka 5. Here is my proof A and B share the same key Trust in key server: • security of session keys • entity authentication Network Security - R. Molva - ÓInstitut Eurecom 2002 B Kb
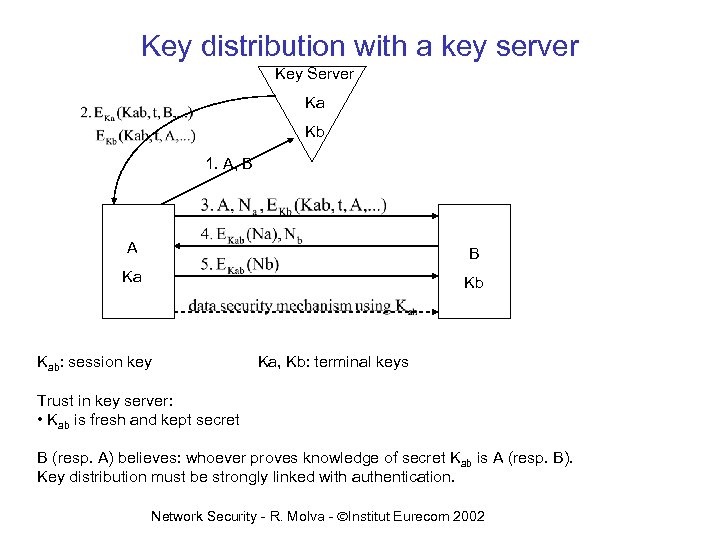
Key distribution with a key server Key Server Ka Kb 1. A, B A B Ka Kb Kab: session key Ka, Kb: terminal keys Trust in key server: • Kab is fresh and kept secret B (resp. A) believes: whoever proves knowledge of secret Kab is A (resp. B). Key distribution must be strongly linked with authentication. Network Security - R. Molva - ÓInstitut Eurecom 2002
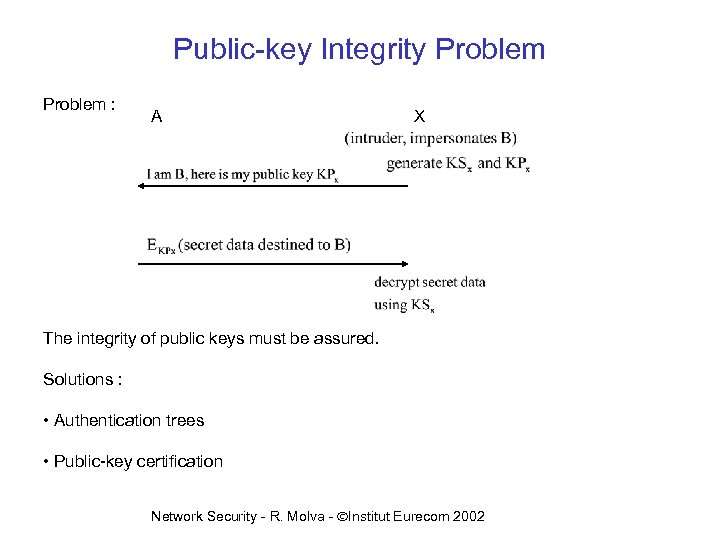
Public-key Integrity Problem : A X The integrity of public keys must be assured. Solutions : • Authentication trees • Public-key certification Network Security - R. Molva - ÓInstitut Eurecom 2002

Identity Certificate Public Key certificate of entity A (key=KPa) created by X: • signed by trusted party X using secret key KSx • can be checked by using public key KPX Prerequisite for verifying a certificate: KPX must be known and trusted. • identity certificates are required for all services implemented using public-key encryption (entity authentication, data origin authentication, data integrity, nonrepudiation of origin, key distribution) • the security of these services entirely relies on the validity (integrity) of the certificate that includes the public key. • On the contrary of a common belief, a certificate alone does not prove anything, it must be used together with a mechanism like an authentication protocol through which the owner of the public-key demonstrates his knowledge of the corresponding private key. Network Security - R. Molva - ÓInstitut Eurecom 2002
TTP Functions • Certification Authority (CA) • Registration Authority (RA) • Name Service • Certificate Directory • Key Generator Network Security - R. Molva - ÓInstitut Eurecom 2002
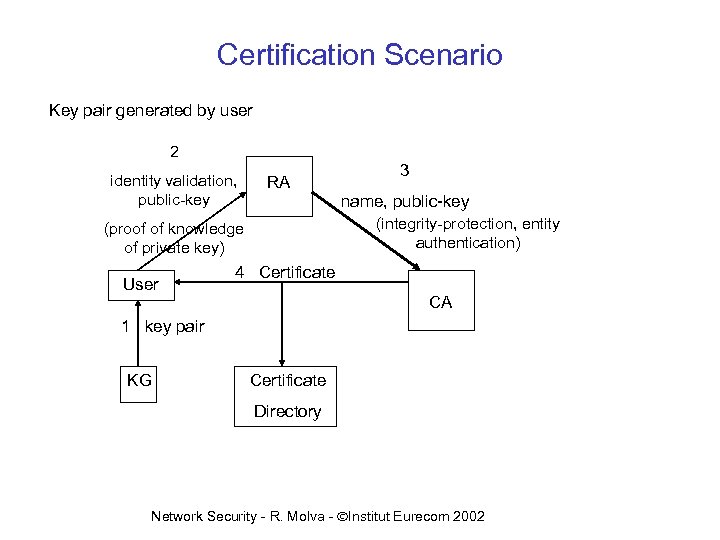
Certification Scenario Key pair generated by user 2 identity validation, public-key RA name, public-key (integrity-protection, entity authentication) (proof of knowledge of private key) User 3 4 Certificate CA 1 key pair KG Certificate Directory Network Security - R. Molva - ÓInstitut Eurecom 2002
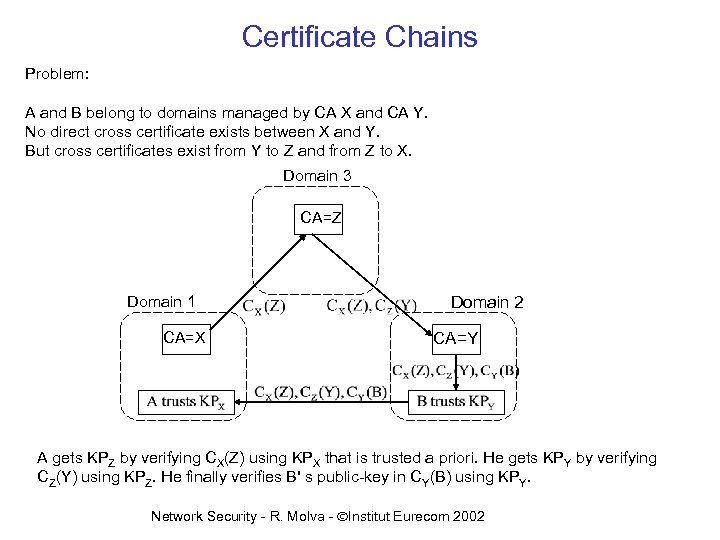
Certificate Chains Problem: A and B belong to domains managed by CA X and CA Y. No direct cross certificate exists between X and Y. But cross certificates exist from Y to Z and from Z to X. Domain 3 CA=Z Domain 1 CA=X Domain 2 CA=Y A gets KPZ by verifying CX(Z) using KPX that is trusted a priori. He gets KPY by verifying CZ(Y) using KPZ. He finally verifies B' s public-key in CY(B) using KPY. Network Security - R. Molva - ÓInstitut Eurecom 2002
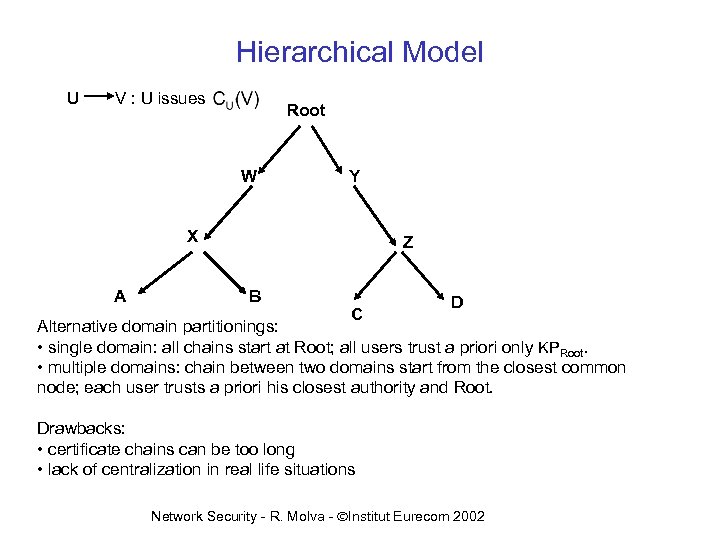
Hierarchical Model U V : U issues Root W Y X A Z B C D Alternative domain partitionings: • single domain: all chains start at Root; all users trust a priori only KPRoot. • multiple domains: chain between two domains start from the closest common node; each user trusts a priori his closest authority and Root. Drawbacks: • certificate chains can be too long • lack of centralization in real life situations Network Security - R. Molva - ÓInstitut Eurecom 2002
Outline THEORY 1. Symmetric Cryptography 2. Asymmetric Cryptography 3. Hash Functions and Integrity 4. Authentication 5. Key Management APPLICATIONS 6. Internet Security Using Firewalls Mechanisms 7. Internet Security with Cryptographic 8. Multicast Security Network Security - R. Molva - ÓInstitut Eurecom 2002 61

Internet Security Directions Cryptographic security protect only sensitive resources using logical means e-commerce HTTP SMTP FTP TELNET DNS RIP Secure virtual channel using cryptography SNMP BGP TCP/UDP OSPF IP Data Link Internet Pros • flexible (service type and security level) • end-to-end (application and user security) • no impact on global network Cons • deployment (retrofitting in end-systems) • cost of migration (protocol impact) Network Security - R. Molva - ÓInstitut Eurecom 2002

Internet Security Directions Domain Control Isolate trusted network from untrusted Internet by filtering traffic across the border Filter Intranet (trusted) Internet (untrusted) Pros • no impact on the intranet components • no impact on application software and users • ease of deployment for company intranets Cons • impediment to the global network concept • no end-to-end security • insufficient for e-commerce applications Network Security - R. Molva - ÓInstitut Eurecom 2002
Filtering Components Traffic filtering based on (combination of) : • packet filters • application gateways • circuit gateways Network Security - R. Molva - ÓInstitut Eurecom 2002
Packet Filters • Function integrated with packet forwarding • Principle: • for each IP packet received from a local interface • check the packet against the set of access rules • forward, discard and/or log the packet according to the result of the rulebased verification • Access rules are based on (a selection of): • information of the TCP/IP header: - source and destination IP addresses - source and destination port numbers - protocol type (TCP/UDP) - flags (ACK, SYN) • the identity of the incoming interface • direction of the packet (in/out) • implemented by • router (CISCO) • IP forwarding algorithm in a host (Linux) • dedicated device (Firewall-1 Checkpoint, Screend, etc. ) Network Security - R. Molva - ÓInstitut Eurecom 2002

Application Gateways Opposite approach to packet filtering: Instead of a general purpose mechanism for all kind of traffic, a special purpose access control mechanism is used for each application. • Idea: Application gateway is a proxy server. Each proxy server acts as an intermediate between the client and the actual server. Proxy server performs varoous verifications on the application protocol between the client and server. Generic operation of an application gateway: • the client first connects to proxy server • proxy server performs authentication and access control verification • if the client is authorized, proxy server connects to the actual destination • further communication between the client and the actual server is relayed through the proxy server and some optional filtering can be applied on the data exchange. An application gateway is a process, not a host. There is an application gateway for each application protocol that is authorized. Application gateways can be combined with a packet filter. Network Security - R. Molva - ÓInstitut Eurecom 2002
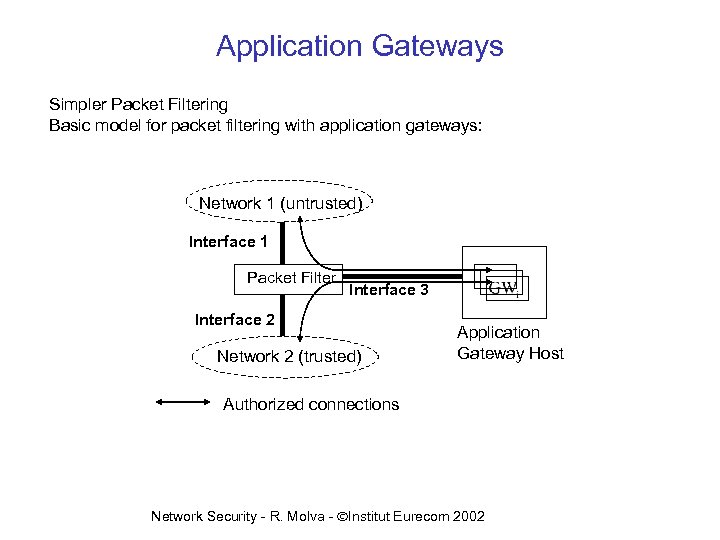
Application Gateways Simpler Packet Filtering Basic model for packet filtering with application gateways: Network 1 (untrusted) Interface 1 Packet Filter Interface 3 Interface 2 Network 2 (trusted) Application Gateway Host Authorized connections Network Security - R. Molva - ÓInstitut Eurecom 2002
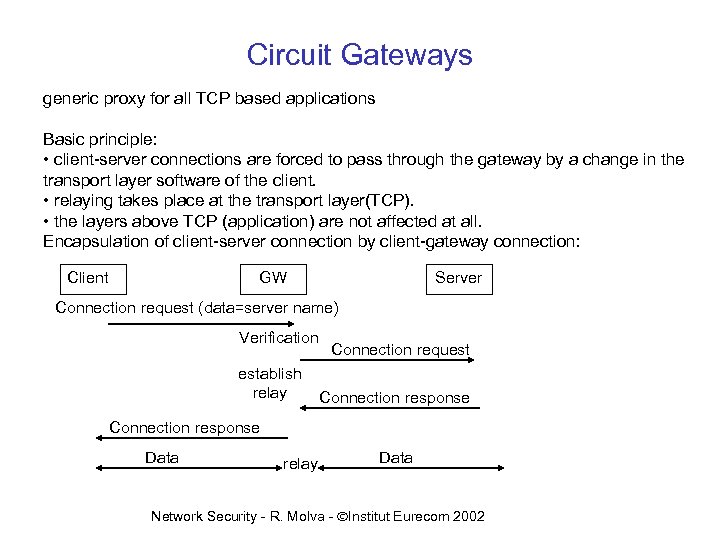
Circuit Gateways generic proxy for all TCP based applications Basic principle: • client-server connections are forced to pass through the gateway by a change in the transport layer software of the client. • relaying takes place at the transport layer(TCP). • the layers above TCP (application) are not affected at all. Encapsulation of client-server connection by client-gateway connection: Client GW Server Connection request (data=server name) Verification establish relay Connection request Connection response Data relay Data Network Security - R. Molva - ÓInstitut Eurecom 2002

Packet filtering Firewall Local Network Packet Filter Internet Router • Router blocks all or most access to internal network. • Router can allow selective access to services. • Usually inherently danagerous services as NIS, NFS, X 11 are blocked Network Security - R. Molva - ÓInstitut Eurecom 2002
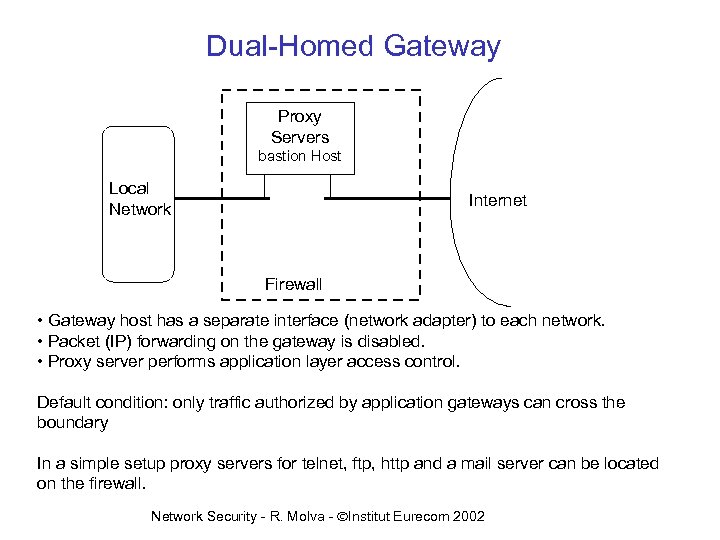
Dual-Homed Gateway Proxy Servers bastion Host Local Network Internet Firewall • Gateway host has a separate interface (network adapter) to each network. • Packet (IP) forwarding on the gateway is disabled. • Proxy server performs application layer access control. Default condition: only traffic authorized by application gateways can cross the boundary In a simple setup proxy servers for telnet, ftp, http and a mail server can be located on the firewall. Network Security - R. Molva - ÓInstitut Eurecom 2002

Screened Host Firewall Proxy Servers Bastion Host Packet Filter Local Network Open Services Internet Router Firewall • packet filter "forces" all inbound packets to connect to the gateway or "bastion host". • packet filter lets out only packets from the gateway. • Proxy servers performs application layer access control. Main difference from Dual-homed Gateway: no true network isolation Network Security - R. Molva - ÓInstitut Eurecom 2002
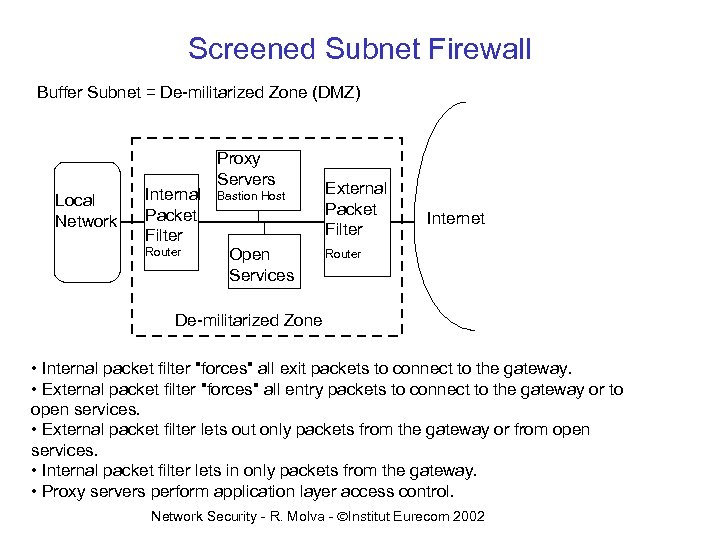
Screened Subnet Firewall Buffer Subnet = De-militarized Zone (DMZ) Local Network Internal Packet Filter Router Proxy Servers Bastion Host Open Services External Packet Filter Internet Router De-militarized Zone • Internal packet filter "forces" all exit packets to connect to the gateway. • External packet filter "forces" all entry packets to connect to the gateway or to open services. • External packet filter lets out only packets from the gateway or from open services. • Internal packet filter lets in only packets from the gateway. • Proxy servers perform application layer access control. Network Security - R. Molva - ÓInstitut Eurecom 2002

Other Useful Tools • TCP_WRAPPER • host-based access control and logging for TCP-based services • located at each host • integrated with inetd • Tripwire • host-based integrity verification • detects modification of essential files • based on hashing • SATAN, ISS • vulnerability testing on UNIX networks • based on well-known security flaws • COPS • vulnerability testing on UNIX systems • ISS Real Secure, Netranger, etc. • network intrusion detection • based on traffic analysis and recognition of well-known attack sequences Network Security - R. Molva - ÓInstitut Eurecom 2002

Outline THEORY 1. Symmetric Cryptography 2. Asymmetric Cryptography 3. Hash Functions and Integrity 4. Authentication 5. Key Management APPLICATIONS 6. Internet Security Using Firewalls 7. Internet Security with Cryptographic Mechanisms 8. Multicast Security Network Security - R. Molva - ÓInstitut Eurecom 2002 74
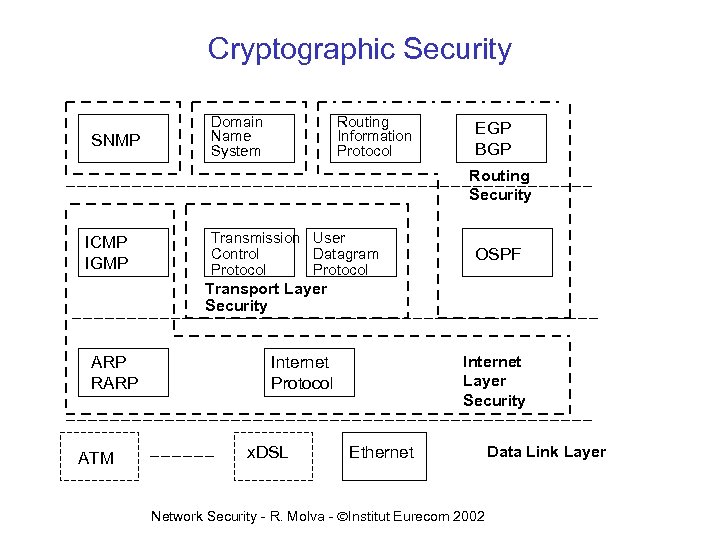
Cryptographic Security SNMP Domain Name System Routing Information Protocol EGP BGP Routing Security ICMP IGMP Transmission User Control Datagram Protocol OSPF Transport Layer Security ARP RARP ATM Internet Layer Security Internet Protocol x. DSL Ethernet Network Security - R. Molva - ÓInstitut Eurecom 2002 Data Link Layer

Internet Layer Security Architecture IPsec RFC 2401 - Architecture Document • IP Authentication Header (IP AH) • IP Encapsulating Security Payload (ESP) • Keyed Hash Functions • Key management and Security Associations • No protection for ARP in IPv 4 • Secure equivalent in IPv 6 using ICMP Network Security - R. Molva - ÓInstitut Eurecom 2002
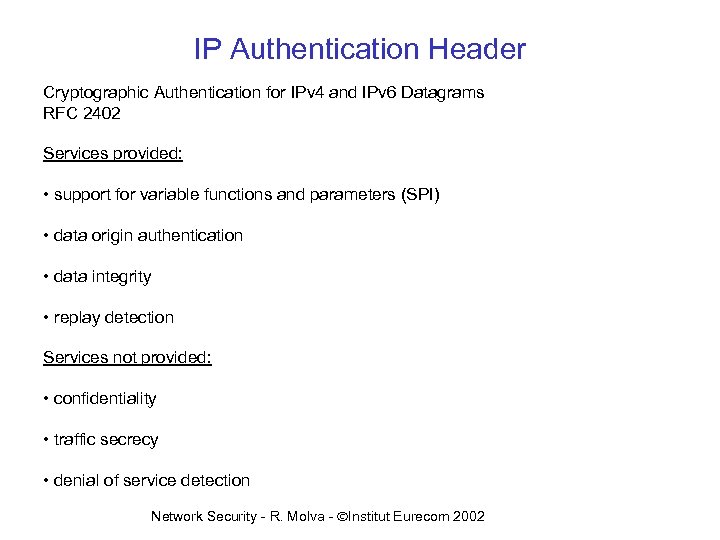
IP Authentication Header Cryptographic Authentication for IPv 4 and IPv 6 Datagrams RFC 2402 Services provided: • support for variable functions and parameters (SPI) • data origin authentication • data integrity • replay detection Services not provided: • confidentiality • traffic secrecy • denial of service detection Network Security - R. Molva - ÓInstitut Eurecom 2002
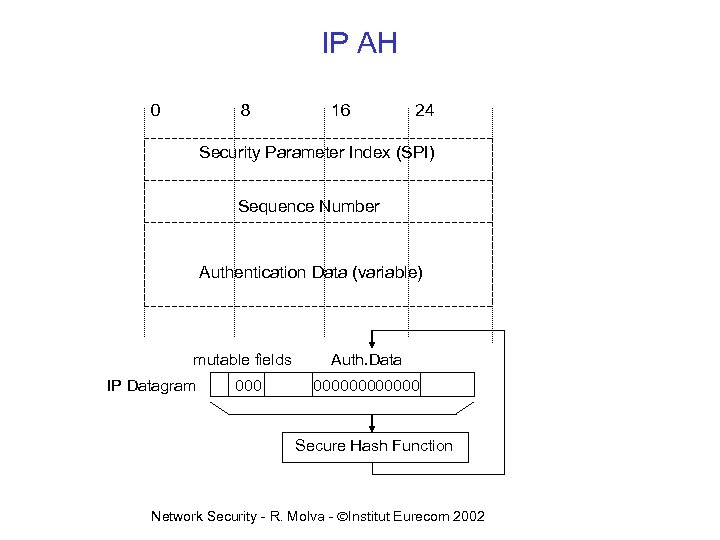
IP AH 0 8 16 24 Security Parameter Index (SPI) Sequence Number Authentication Data (variable) mutable fields IP Datagram 000 Auth. Data 000000 Secure Hash Function Network Security - R. Molva - ÓInstitut Eurecom 2002
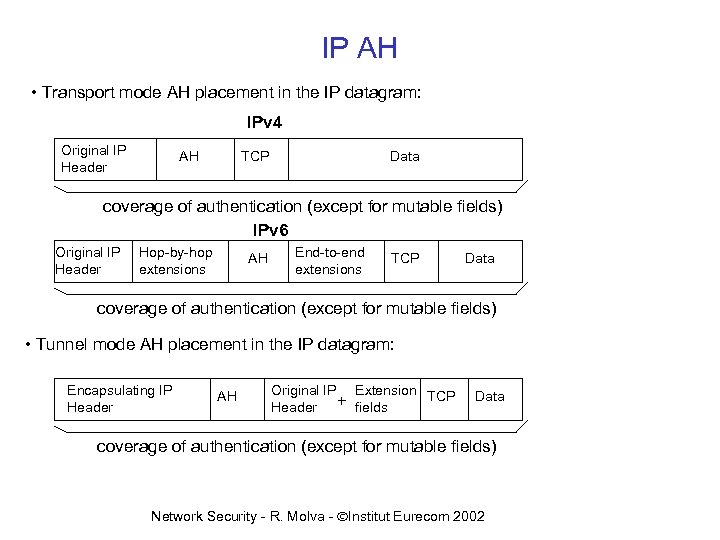
IP AH • Transport mode AH placement in the IP datagram: IPv 4 Original IP Header AH TCP Data coverage of authentication (except for mutable fields) IPv 6 Original IP Header Hop-by-hop extensions AH End-to-end extensions TCP Data coverage of authentication (except for mutable fields) • Tunnel mode AH placement in the IP datagram: Encapsulating IP Header AH Original IP Extension TCP Header + fields Data coverage of authentication (except for mutable fields) Network Security - R. Molva - ÓInstitut Eurecom 2002

IP AH Secure Hash Function alternatives: • Keyed MD 5 (RFC 1828) 512 Key + padding IP packet n x 512 Key padding MD 5 Authentication Data (128 bits) • HMAC (RFC 2104) • Asymmetric or Symmetric Encryption of MD 5 output Network Security - R. Molva - ÓInstitut Eurecom 2002

IP Encapsulating Security Payload RFC 2406 Services provided: • data confidentiality • data integrity with replay detection • traffic confidentiality (optional) 16 24 Security Parameter Index (SPI) Sequence Number Payload Padding Authentication Data (variable) Network Security - R. Molva - ÓInstitut Eurecom 2002 Coverage of Authentication 8 Coverage of Confidentiality 0
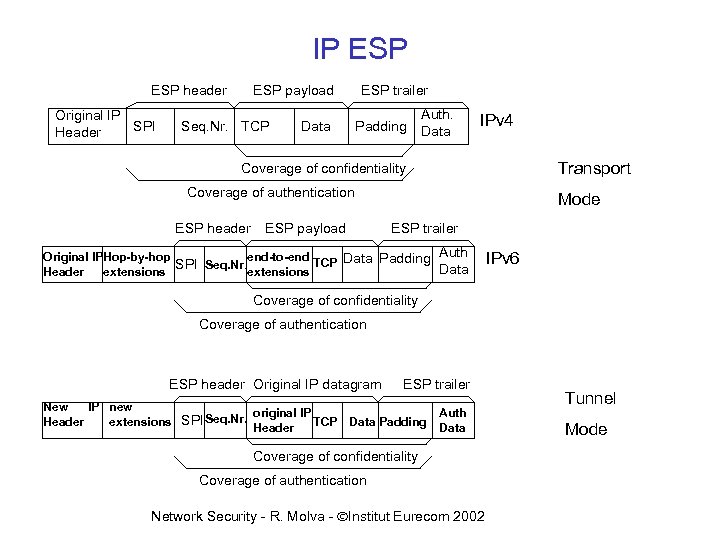
IP ESP header Original IP SPI Header ESP payload Seq. Nr. TCP ESP trailer Data Padding Auth. Data IPv 4 Transport Coverage of confidentiality Coverage of authentication ESP header ESP payload Mode ESP trailer Auth Original IPHop-by-hop end-to-end SPI Seq. Nr. extensions TCP Data Padding Data Header extensions IPv 6 Coverage of confidentiality Coverage of authentication ESP header Original IP datagram New IP new original IP TCP Header extensions SPI Seq. Nr. Header ESP trailer Data Padding Auth Data Coverage of confidentiality Coverage of authentication Network Security - R. Molva - ÓInstitut Eurecom 2002 Tunnel Mode

End-to-end security with IPsec Internet or Intranet Transport Mode Tunnel Mode IP 1 AH ULH IP 2 AH IP 1 ULH IP 1 ESP ULH IP 2 ESP IP 1 ULH IP 1 AH ESP ULH : One or more SA’s applied to the same traffic stream IP 1 : original IP header IP 2 : encapsulating IP header ULH : Upper Layer Header Network Security - R. Molva - ÓInstitut Eurecom 2002

Simple virtual private network with IPsec Intranet Internet Intranet Tunnel Mode IP 2 AH IP 1 ULH IP 2 ESP IP 1 ULH Network Security - R. Molva - ÓInstitut Eurecom 2002

Remote access with IPsec Internet Intranet SG Network Security - R. Molva - ÓInstitut Eurecom 2002
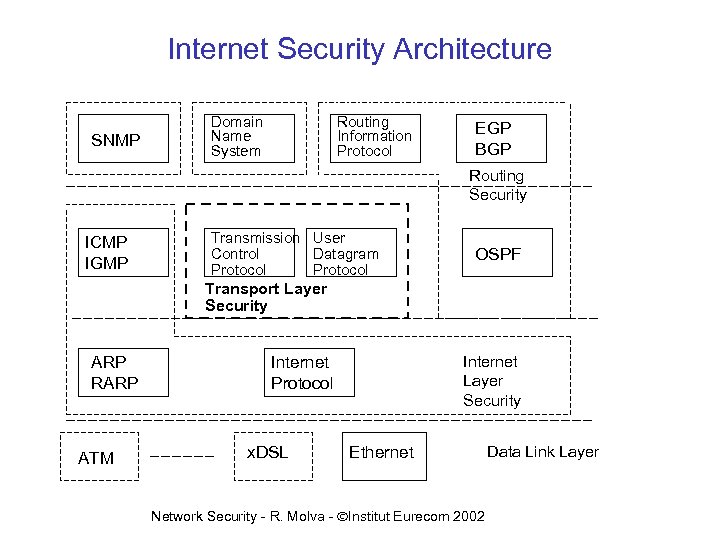
Internet Security Architecture SNMP Domain Name System Routing Information Protocol EGP BGP Routing Security ICMP IGMP Transmission User Control Datagram Protocol OSPF Transport Layer Security ARP RARP ATM Internet Layer Security Internet Protocol x. DSL Ethernet Network Security - R. Molva - ÓInstitut Eurecom 2002 Data Link Layer

Transport Layer Security (TLS) Protocol RFC 2246 Based on Secure Sockets Layer (SSL) from Netscape Communications Services provided : • peer entity authentication • data confidentiality • data integrity (replay detection) • generation/distribution of session keys • security parameter negotiation Two sub-layers: • TLS Record Protocol • TLS Handshake Protocol • Record sub-layer encapsulates Application Data and Handshake Protocol Network Security - R. Molva - ÓInstitut Eurecom 2002
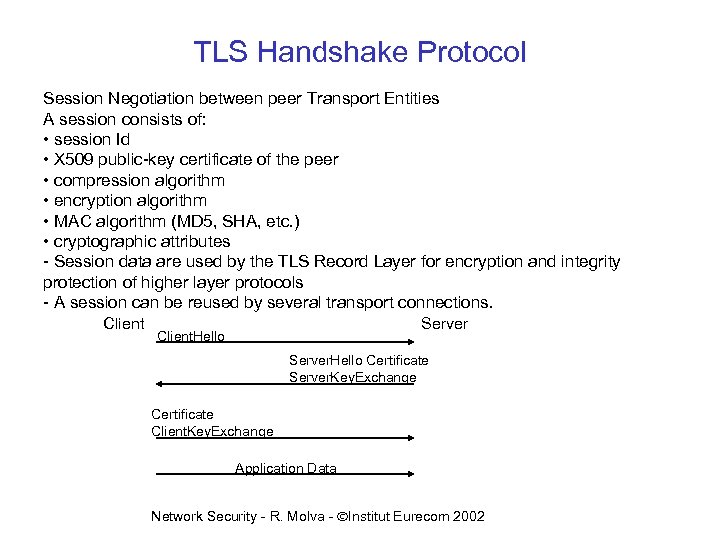
TLS Handshake Protocol Session Negotiation between peer Transport Entities A session consists of: • session Id • X 509 public-key certificate of the peer • compression algorithm • encryption algorithm • MAC algorithm (MD 5, SHA, etc. ) • cryptographic attributes - Session data are used by the TLS Record Layer for encryption and integrity protection of higher layer protocols - A session can be reused by several transport connections. Client Server Client. Hello Server. Hello Certificate Server. Key. Exchange Certificate Client. Key. Exchange Application Data Network Security - R. Molva - ÓInstitut Eurecom 2002
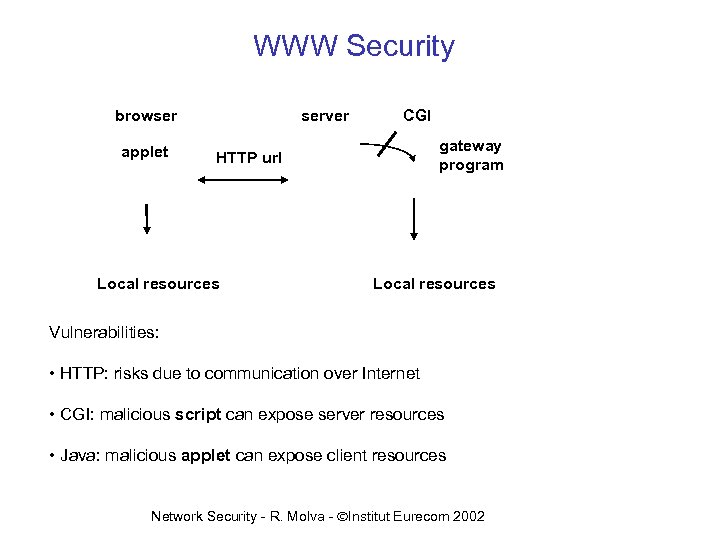
WWW Security browser applet server CGI gateway program HTTP url Local resources Vulnerabilities: • HTTP: risks due to communication over Internet • CGI: malicious script can expose server resources • Java: malicious applet can expose client resources Network Security - R. Molva - ÓInstitut Eurecom 2002
HTTP and CGI Security Client-server communication: • Standard: authentication by the server • uuencoded cleartext passwords • domain-based access control • per subtree of the html document directory • application layer: Secure HTTP • transport layer: SSL Netscape (see Transport Layer Security) • proxy server to filter traffic at domain boundary CGI: • restricted access to cgi-bin directory • user-provided parameter verification in the cgi scripts • limited use of setuid bit with cgi scripts • limited use of process creation in cgi scripts • hide source of cgi scripts from the net Network Security - R. Molva - ÓInstitut Eurecom 2002
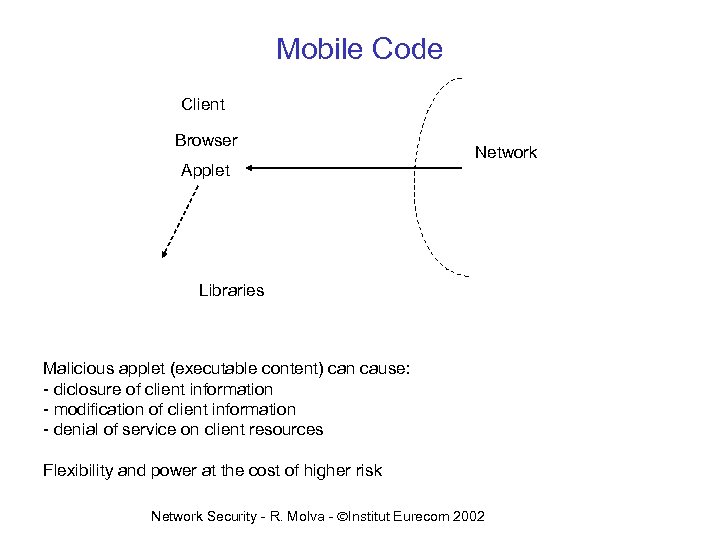
Mobile Code Client Browser Applet Network Libraries Malicious applet (executable content) can cause: - diclosure of client information - modification of client information - denial of service on client resources Flexibility and power at the cost of higher risk Network Security - R. Molva - ÓInstitut Eurecom 2002
Java Security Language features • object-oriented data encapsulation • type-safety • final attribute • absence of pointers • garbage collection • namespace encapsulation Protection against malicious Applets: Sandbox Approach Bytecode Verifier converts bytecode from the network into local class, checking: • stack overflows • pointers • access restrictions • object and method access Class Loader • protects integrity of local classes • forces class import from origin node • signature verification by subtyped Signed. Class. Loader Security Manager • access control by the runtime environment (browser) • used by the other objects Network Security - R. Molva - ÓInstitut Eurecom 2002

Outline THEORY 1. Symmetric Cryptography 2. Asymmetric Cryptography 3. Hash Functions and Integrity 4. Authentication 5. Key Management APPLICATIONS 6. Internet Security Using Firewalls 7. Internet Security with Cryptographic Mechanisms 8. Multicast Security Network Security - R. Molva - ÓInstitut Eurecom 2002 93

Multicast Security • Key Management • Data Origin Authentication • Data Confidentiality Network Security - R. Molva - ÓInstitut Eurecom 2002 94

Key Management • Security requirements – membership (JOIN/LEAVE) security; – Containment. • Scalability – Processing cost – Membership dynamics • No group-wide re-key message – Treat the group as single entity • Existing algorithms : – one key for the whole group – the group is a set of subgroups : different keys in each subgroup Network Security - R. Molva - ÓInstitut Eurecom 2002 95
![Multicast Key management • Keygraphs [Wong et al. 98] K 0 = Group Key Multicast Key management • Keygraphs [Wong et al. 98] K 0 = Group Key](https://present5.com/presentation/9f8e9798a2db214d542258ee2d5c8bbd/image-96.jpg)
Multicast Key management • Keygraphs [Wong et al. 98] K 0 = Group Key u 4’s keys = {K 3, K 34, K 1234, K 0} K 1234 u 4 JOINS : trivial K 5678 u 4 LEAVES : {K 34’, K 1234’, K 0’}K 3 u 3 K 12 K 34 K 56 K 78 {K 1234’, K 0’}K 12 u 1, u 2 {K 0’}K 5678 u 5, u 6, u 7, u 8 K 1 K 2 K 3 K 4 K 5 K 6 K 7 K 8 u 1 u 2 u 3 u 4 u 5 u 6 u 7 u 8 advantage : number of re-key messages are in the logarithmic order there is no containment. Network Security - R. Molva - ÓInstitut Eurecom 2002 96
![Multicast Key Management Sub-group approach • Iolus [Mittra, 97] • intermediate nodes involved in Multicast Key Management Sub-group approach • Iolus [Mittra, 97] • intermediate nodes involved in](https://present5.com/presentation/9f8e9798a2db214d542258ee2d5c8bbd/image-97.jpg)
Multicast Key Management Sub-group approach • Iolus [Mittra, 97] • intermediate nodes involved in key distribution GSC (Group Security Controller) defines the groups and the GSI K 1 GSC GSI K 3 K 2 GSI K 5 GSI K 6 GSI K 4 GSI (Group Security Intermediary): 1 - decrypt M with the key of the group; 2 - recrypt M with the key of the other group he’s involved in. advantage : containment + scalability disadvantage : we have to trust GSIs Network Security - R. Molva - ÓInstitut Eurecom 2002 97
![Multicast Key Management Sub-group Approach • [Molva et al. 99] • Based on asymmetric Multicast Key Management Sub-group Approach • [Molva et al. 99] • Based on asymmetric](https://present5.com/presentation/9f8e9798a2db214d542258ee2d5c8bbd/image-98.jpg)
Multicast Key Management Sub-group Approach • [Molva et al. 99] • Based on asymmetric algorithms a 1 Source sends: a 2 a 3 a 6 a 4 a 7 a 5 Recipients in subgroup: S 4 Network Security - R. Molva - ÓInstitut Eurecom 2002 98
![Multicast Key Management (4/4) • MARKS [Briscoe 99] access to segments between s 4 Multicast Key Management (4/4) • MARKS [Briscoe 99] access to segments between s 4](https://present5.com/presentation/9f8e9798a2db214d542258ee2d5c8bbd/image-99.jpg)
Multicast Key Management (4/4) • MARKS [Briscoe 99] access to segments between s 4 and s 8 using t 2 and t 10 t 0 L t 1 L L t 3 R R R t 2 L t 4 k 4 t 5 L R L t 11 t 7 t 8 t 9 t 10 k 1 k 2 k 3 k 4 k 5 R L t 12 k 6 L and R are one-way functions. R t 6 t 13 = t 10 ; k 5 = L(L(t 2)); etc. R t 14 k 7 k 8 Network Security - R. Molva - ÓInstitut Eurecom 2002 99
![Broadcast Encryption(2/3) • k-resilient scheme [Fiat et al. 1994] Every user ui is assigned Broadcast Encryption(2/3) • k-resilient scheme [Fiat et al. 1994] Every user ui is assigned](https://present5.com/presentation/9f8e9798a2db214d542258ee2d5c8bbd/image-100.jpg)
Broadcast Encryption(2/3) • k-resilient scheme [Fiat et al. 1994] Every user ui is assigned a set of keys Ki S S sends {M}K and a key envelope to a user set T u 1 u 2 u 3 …. . un Each users in T retrieves K from the key envelope using Ki mathematically proven k-resilient. Network Security - R. Molva - ÓInstitut Eurecom 2002 100
![Broadcast encryption(3/3) • f-redundant key cover schemes [Abdalla et al. 2000] k(ui) = {Kj} Broadcast encryption(3/3) • f-redundant key cover schemes [Abdalla et al. 2000] k(ui) = {Kj}](https://present5.com/presentation/9f8e9798a2db214d542258ee2d5c8bbd/image-101.jpg)
Broadcast encryption(3/3) • f-redundant key cover schemes [Abdalla et al. 2000] k(ui) = {Kj} ui Kj u 8 K u 5 1 u 2 u 9 u 10 u 3 u 4 K 2 K 5 u 6 u 11 K 3 u 13 u 7 u 12 K 4 U U = universe of users ui Ki = sets of users (one key per set) S {u 2, u 6, u 10, u 12} : M S computes Cmin(K) and sends the same message encrypted with the keys in Cmin(K) (minimal key cover). => f-redundancy: some of users outside the intended destination group will be able to access M Network Security - R. Molva - ÓInstitut Eurecom 2002 101
![Data Encryption (1/3) • [Pannetrat et al. 2002] Based on same idea as the Data Encryption (1/3) • [Pannetrat et al. 2002] Based on same idea as the](https://present5.com/presentation/9f8e9798a2db214d542258ee2d5c8bbd/image-102.jpg)
Data Encryption (1/3) • [Pannetrat et al. 2002] Based on same idea as the key distribution algorithm using intermediate nodes • Symmetric encryption in XOR-Counter mode. – Apply several layers of encryption at the source and recipients. – Only two operations in the intermediate elements • One decryption • One encryption Network Security - R. Molva - ÓInstitut Eurecom 2002 102
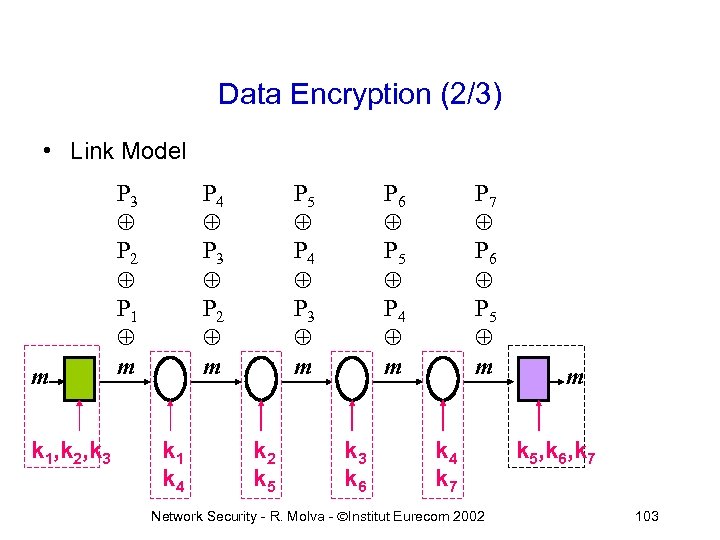
Data Encryption (2/3) • Link Model m k 1, k 2, k 3 P 3 P 2 P 1 m P 4 P 3 P 2 m k 1 k 4 P 5 P 4 P 3 m k 2 k 5 P 6 P 5 P 4 m k 3 k 6 P 7 P 6 P 5 m k 4 k 7 Network Security - R. Molva - ÓInstitut Eurecom 2002 m k 5, k 6, k 7 103

Data Encryption(3/3) • Group Model k 2 k 10 k 3, k 4, k 10 k 2 k 5 Network Security - R. Molva - ÓInstitut Eurecom 2002 k 5, k 6, k 7 k 5, k 6, k 8 104
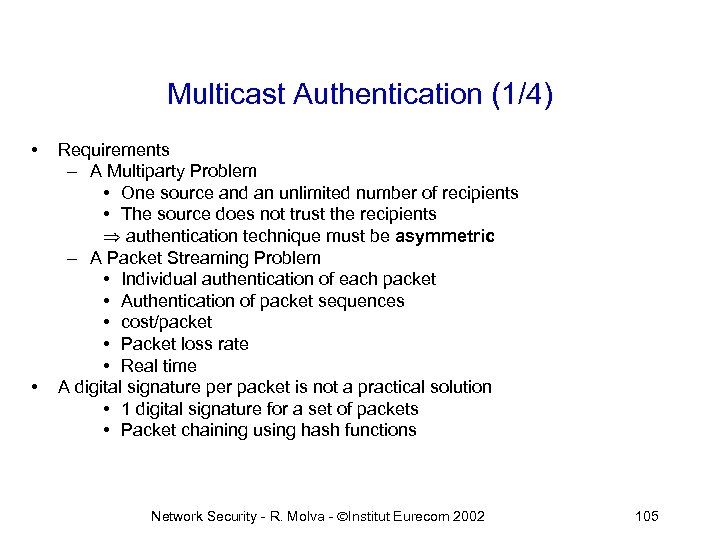
Multicast Authentication (1/4) • • Requirements – A Multiparty Problem • One source and an unlimited number of recipients • The source does not trust the recipients authentication technique must be asymmetric – A Packet Streaming Problem • Individual authentication of each packet • Authentication of packet sequences • cost/packet • Packet loss rate • Real time A digital signature per packet is not a practical solution • 1 digital signature for a set of packets • Packet chaining using hash functions Network Security - R. Molva - ÓInstitut Eurecom 2002 105
![Multicast Authentication (2/4) • TESLA [Perrig et al. 2000] • Lamport’s hash chaining like Multicast Authentication (2/4) • TESLA [Perrig et al. 2000] • Lamport’s hash chaining like](https://present5.com/presentation/9f8e9798a2db214d542258ee2d5c8bbd/image-106.jpg)
Multicast Authentication (2/4) • TESLA [Perrig et al. 2000] • Lamport’s hash chaining like in S/Key: K 0, K 1, K 2, . . . Kn Ki = h(Ki+1) • Authenticated multicast message sent at time interval i: Mi, MAC(Ki, Mi), Ki-1 • • • Mi authenticated using a further message in the stream Synchronization required to detect re-plays: Kj only valid in interval Ij The first message asymmetrically authenticated using a digital signature. Network Security - R. Molva - ÓInstitut Eurecom 2002 106
![Multicast Authentication (3/4) • [Pannetrat et al. 2002] hash ha ha sh sh P Multicast Authentication (3/4) • [Pannetrat et al. 2002] hash ha ha sh sh P](https://present5.com/presentation/9f8e9798a2db214d542258ee2d5c8bbd/image-107.jpg)
Multicast Authentication (3/4) • [Pannetrat et al. 2002] hash ha ha sh sh P P P sh ha Advantages : • Spread the cost of a signature over several packets. • Erasure code to tolerate losses. • No need to send duplicate hash values E. C. 1 Sign E. C. 2 Network Security - R. Molva - ÓInstitut Eurecom 2002 107

Multicast Authentication (4/4) • Alternative feedback schemes PPPP PPPP Network Security - R. Molva - ÓInstitut Eurecom 2002 108
Thank You Network Security - R. Molva - ÓInstitut Eurecom 2002 109
9f8e9798a2db214d542258ee2d5c8bbd.ppt