49e5202260696d74bd4269b460c9b66d.ppt
- Количество слайдов: 48
 Network Security Netzwerksicherheit Lecture ID: ET-IDA-082 (2416082) Lecture-21 Network Defense Strong Password Protocols Firewalls 17. 07. 2008 , v 2 Prof. W. Adi Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 1
Network Security Netzwerksicherheit Lecture ID: ET-IDA-082 (2416082) Lecture-21 Network Defense Strong Password Protocols Firewalls 17. 07. 2008 , v 2 Prof. W. Adi Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 1
 Outlines - Strong Password Protocols - Lamport‘s Hash - Strong Protocols - Firewalls - Types and applications Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 2
Outlines - Strong Password Protocols - Lamport‘s Hash - Strong Protocols - Firewalls - Types and applications Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 2
 Password Schemes Strong Password Protocols Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 3
Password Schemes Strong Password Protocols Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 3
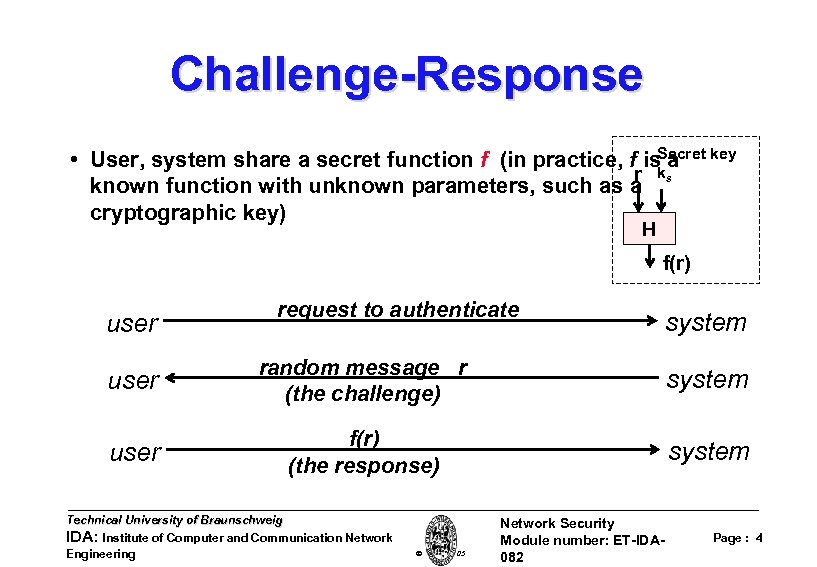 Challenge-Response • User, system share a secret function f (in practice, f is. Secret key a ks r known function with unknown parameters, such as a cryptographic key) H f(r) user request to authenticate system user random message r (the challenge) system user f(r) (the response) system Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 4
Challenge-Response • User, system share a secret function f (in practice, f is. Secret key a ks r known function with unknown parameters, such as a cryptographic key) H f(r) user request to authenticate system user random message r (the challenge) system user f(r) (the response) system Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 4
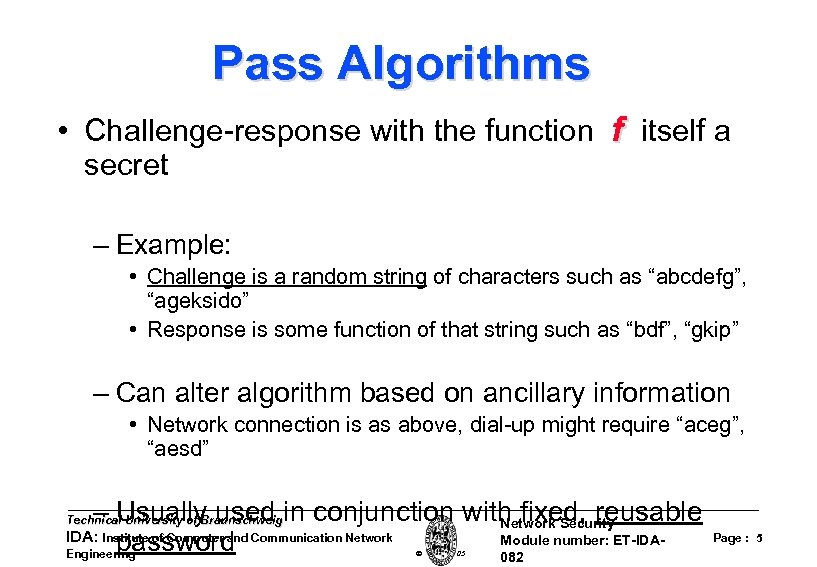 Pass Algorithms • Challenge-response with the function f itself a secret – Example: • Challenge is a random string of characters such as “abcdefg”, “ageksido” • Response is some function of that string such as “bdf”, “gkip” – Can alter algorithm based on ancillary information • Network connection is as above, dial-up might require “aceg”, “aesd” – Usually used in conjunction with fixed, reusable Network Security Module number: ET-IDApassword 082 Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Page : 5
Pass Algorithms • Challenge-response with the function f itself a secret – Example: • Challenge is a random string of characters such as “abcdefg”, “ageksido” • Response is some function of that string such as “bdf”, “gkip” – Can alter algorithm based on ancillary information • Network connection is as above, dial-up might require “aceg”, “aesd” – Usually used in conjunction with fixed, reusable Network Security Module number: ET-IDApassword 082 Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Page : 5
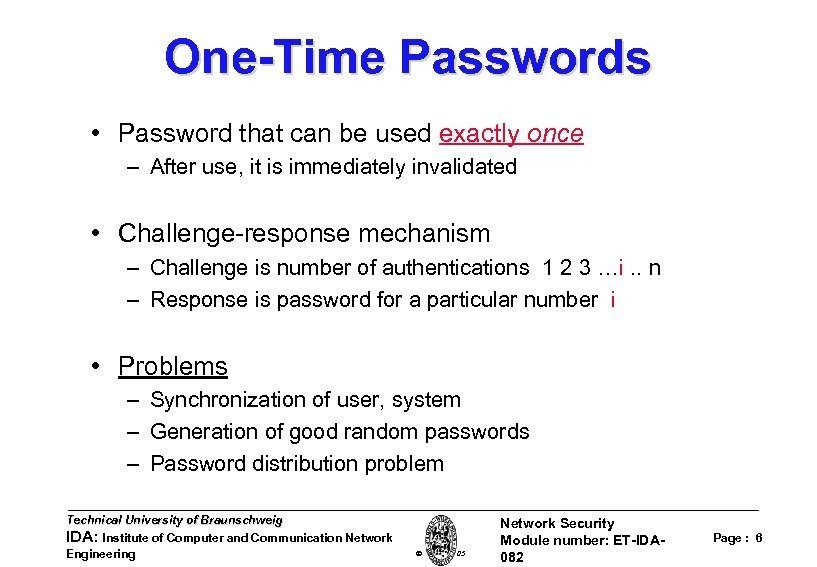 One-Time Passwords • Password that can be used exactly once – After use, it is immediately invalidated • Challenge-response mechanism – Challenge is number of authentications 1 2 3 …i. . n – Response is password for a particular number i • Problems – Synchronization of user, system – Generation of good random passwords – Password distribution problem Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 6
One-Time Passwords • Password that can be used exactly once – After use, it is immediately invalidated • Challenge-response mechanism – Challenge is number of authentications 1 2 3 …i. . n – Response is password for a particular number i • Problems – Synchronization of user, system – Generation of good random passwords – Password distribution problem Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 6
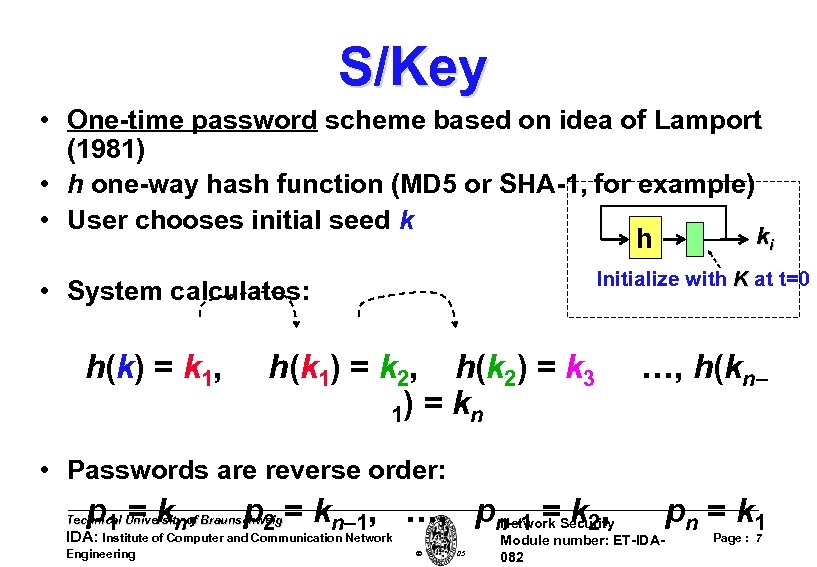 S/Key • One-time password scheme based on idea of Lamport (1981) • h one-way hash function (MD 5 or SHA-1, for example) • User chooses initial seed k ki h Initialize with K at t=0 • System calculates: h(k) = k 1, h(k 1) = k 2, h(k 2) = k 3 1) = k n …, h(kn– • Passwords are reverse order: p 1 = kn , p 2 = kn– 1, …, pn– 1 =Security Network k 2, Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Module number: ET-IDA 082 p n = k 1 Page : 7
S/Key • One-time password scheme based on idea of Lamport (1981) • h one-way hash function (MD 5 or SHA-1, for example) • User chooses initial seed k ki h Initialize with K at t=0 • System calculates: h(k) = k 1, h(k 1) = k 2, h(k 2) = k 3 1) = k n …, h(kn– • Passwords are reverse order: p 1 = kn , p 2 = kn– 1, …, pn– 1 =Security Network k 2, Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Module number: ET-IDA 082 p n = k 1 Page : 7
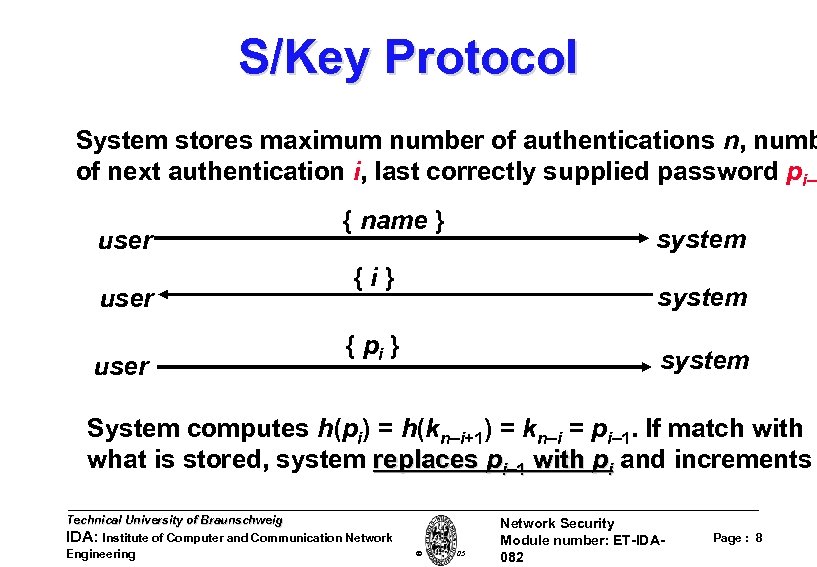 S/Key Protocol System stores maximum number of authentications n, numb of next authentication i, last correctly supplied password pi– user { name } {i} system { pi } system System computes h(pi) = h(kn–i+1) = kn–i = pi– 1. If match with what is stored, system replaces pi– 1 with pi and increments Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 8
S/Key Protocol System stores maximum number of authentications n, numb of next authentication i, last correctly supplied password pi– user { name } {i} system { pi } system System computes h(pi) = h(kn–i+1) = kn–i = pi– 1. If match with what is stored, system replaces pi– 1 with pi and increments Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 8
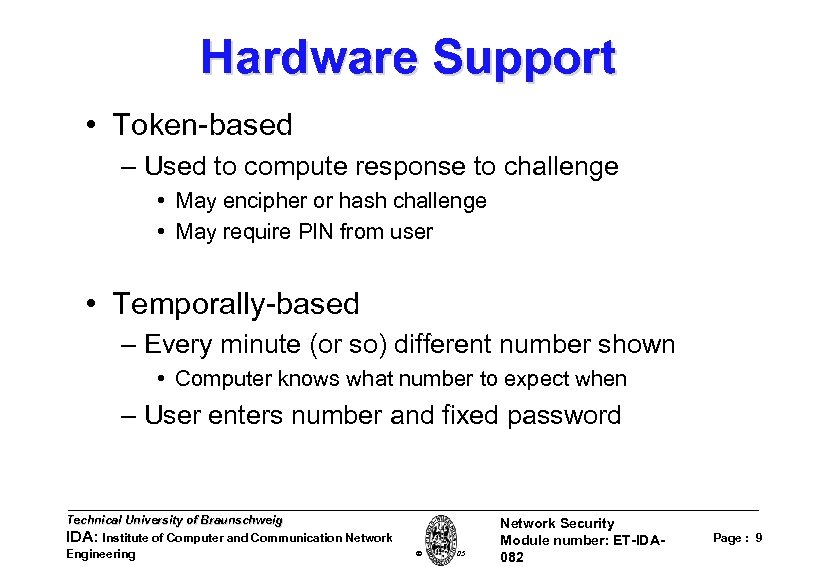 Hardware Support • Token-based – Used to compute response to challenge • May encipher or hash challenge • May require PIN from user • Temporally-based – Every minute (or so) different number shown • Computer knows what number to expect when – User enters number and fixed password Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 9
Hardware Support • Token-based – Used to compute response to challenge • May encipher or hash challenge • May require PIN from user • Temporally-based – Every minute (or so) different number shown • Computer knows what number to expect when – User enters number and fixed password Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 9
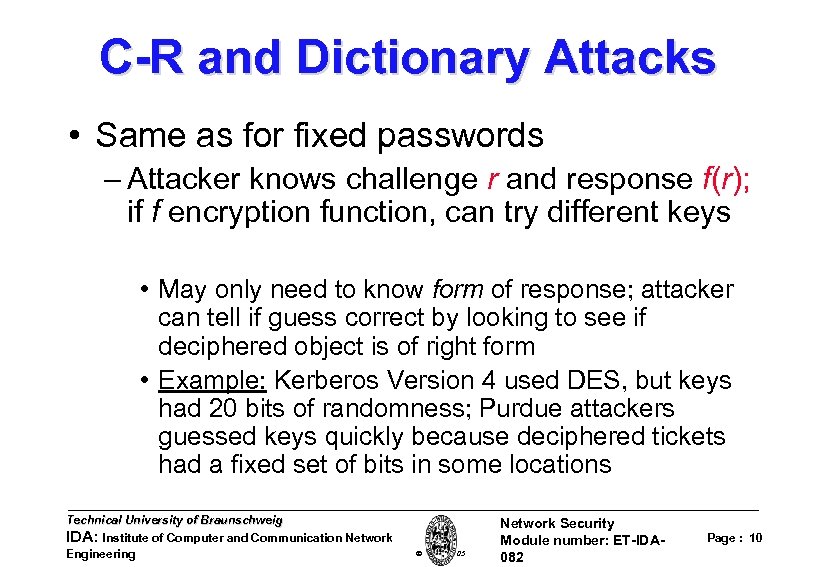 C-R and Dictionary Attacks • Same as for fixed passwords – Attacker knows challenge r and response f(r); if f encryption function, can try different keys • May only need to know form of response; attacker can tell if guess correct by looking to see if deciphered object is of right form • Example: Kerberos Version 4 used DES, but keys had 20 bits of randomness; Purdue attackers guessed keys quickly because deciphered tickets had a fixed set of bits in some locations Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 10
C-R and Dictionary Attacks • Same as for fixed passwords – Attacker knows challenge r and response f(r); if f encryption function, can try different keys • May only need to know form of response; attacker can tell if guess correct by looking to see if deciphered object is of right form • Example: Kerberos Version 4 used DES, but keys had 20 bits of randomness; Purdue attackers guessed keys quickly because deciphered tickets had a fixed set of bits in some locations Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 10
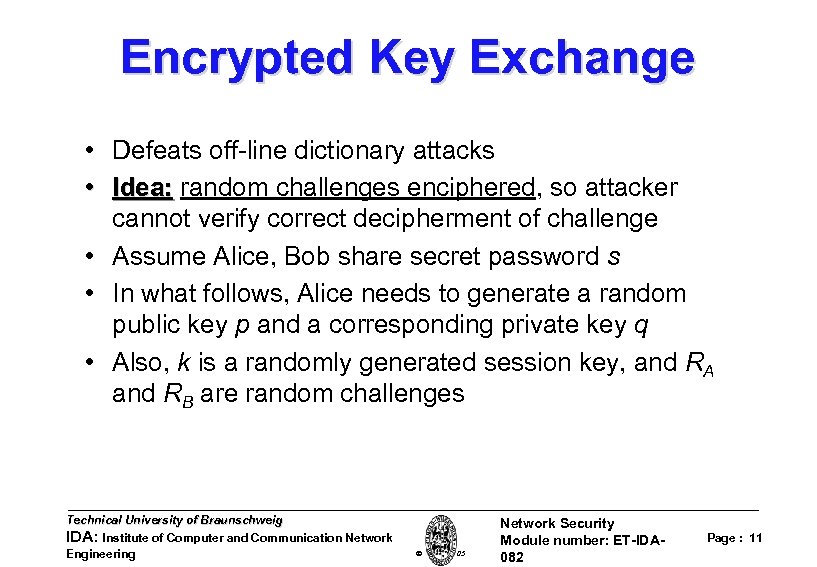 Encrypted Key Exchange • Defeats off-line dictionary attacks • Idea: random challenges enciphered, so attacker cannot verify correct decipherment of challenge • Assume Alice, Bob share secret password s • In what follows, Alice needs to generate a random public key p and a corresponding private key q • Also, k is a randomly generated session key, and RA and RB are random challenges Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 11
Encrypted Key Exchange • Defeats off-line dictionary attacks • Idea: random challenges enciphered, so attacker cannot verify correct decipherment of challenge • Assume Alice, Bob share secret password s • In what follows, Alice needs to generate a random public key p and a corresponding private key q • Also, k is a randomly generated session key, and RA and RB are random challenges Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 11
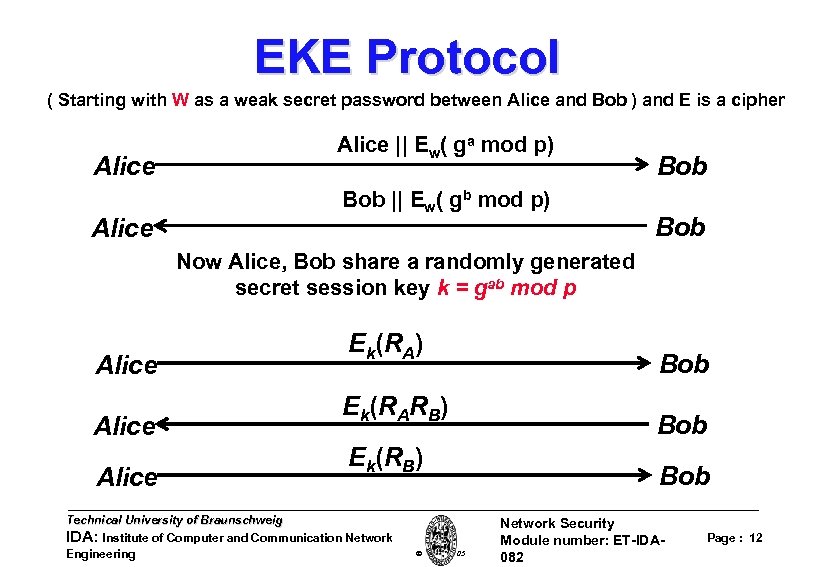 EKE Protocol ( Starting with W as a weak secret password between Alice and Bob ) and E is a cipher Alice || Ew( ga mod p) Bob || Ew( gb mod p) Bob Now Alice, Bob share a randomly generated secret session key k = gab mod p Alice Ek(RA) Ek(RARB) Ek(RB) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Bob Bob Network Security Module number: ET-IDA 082 Page : 12
EKE Protocol ( Starting with W as a weak secret password between Alice and Bob ) and E is a cipher Alice || Ew( ga mod p) Bob || Ew( gb mod p) Bob Now Alice, Bob share a randomly generated secret session key k = gab mod p Alice Ek(RA) Ek(RARB) Ek(RB) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Bob Bob Network Security Module number: ET-IDA 082 Page : 12
 Biometrics • Automated measurement of biological, behavioral features that identify a person – Fingerprints: optical or electrical techniques • Maps fingerprint into a graph, then compares with database • Measurements not exact, so approximate matching algorithms used – Voices: speaker verification or recognition • Verification: uses statistical techniques to test hypothesis that speaker is who is claimed (speaker dependent) • Recognition: checks content of answers (speaker independent) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 13
Biometrics • Automated measurement of biological, behavioral features that identify a person – Fingerprints: optical or electrical techniques • Maps fingerprint into a graph, then compares with database • Measurements not exact, so approximate matching algorithms used – Voices: speaker verification or recognition • Verification: uses statistical techniques to test hypothesis that speaker is who is claimed (speaker dependent) • Recognition: checks content of answers (speaker independent) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 13
 Other Characteristics • Can use several other characteristics – Eyes: patterns in irises unique • Measure patterns, determine if differences are random; or correlate images using statistical tests – Faces: image, or specific characteristics like distance from nose to chin • Lighting, view of face, other noise can hinder this – Keystroke dynamics: believed to be unique • Keystroke intervals, pressure, duration of stroke, where key is struck • Statistical tests used Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 14
Other Characteristics • Can use several other characteristics – Eyes: patterns in irises unique • Measure patterns, determine if differences are random; or correlate images using statistical tests – Faces: image, or specific characteristics like distance from nose to chin • Lighting, view of face, other noise can hinder this – Keystroke dynamics: believed to be unique • Keystroke intervals, pressure, duration of stroke, where key is struck • Statistical tests used Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 14
 Cautions • These can be fooled! – Assumes biometric device accurate in the environment it is being used in! – Transmission of data to validator is tamperproof, correct Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 15
Cautions • These can be fooled! – Assumes biometric device accurate in the environment it is being used in! – Transmission of data to validator is tamperproof, correct Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 15
 Location • If you know where user is, validate identity by seeing if person is where the user is Requires special-purpose hardware to locate user • GPS (global positioning system) device gives location signature of entity • Host uses LSS (location signature sensor) to get signature for entity Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 16
Location • If you know where user is, validate identity by seeing if person is where the user is Requires special-purpose hardware to locate user • GPS (global positioning system) device gives location signature of entity • Host uses LSS (location signature sensor) to get signature for entity Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 16
 Multiple Methods • Example: “where you are” also requires entity to have LSS (Location Signature Sensor) and/or GPS, so also “which means you have? ” have? • Can assign different methods to different tasks As users perform more and more sensitive tasks, must authenticate in a variety of ways • includes controls on access (time of day, etc. ), resources, and requests to change passwords • Pluggable Authentication Modules (Physical Security) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 17
Multiple Methods • Example: “where you are” also requires entity to have LSS (Location Signature Sensor) and/or GPS, so also “which means you have? ” have? • Can assign different methods to different tasks As users perform more and more sensitive tasks, must authenticate in a variety of ways • includes controls on access (time of day, etc. ), resources, and requests to change passwords • Pluggable Authentication Modules (Physical Security) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 17
 Key Points • Authentication is not cryptography – You have to consider system components • Passwords are here to stay – They provide a basis for most forms of authentication • Protocols are important – They can make attacks harder Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 18
Key Points • Authentication is not cryptography – You have to consider system components • Passwords are here to stay – They provide a basis for most forms of authentication • Protocols are important – They can make attacks harder Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 18
 Internal Defenses Firewalls etc. Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 19
Internal Defenses Firewalls etc. Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 19
 Perimeter and Internal Defenses • Commonly deployed defenses – Perimeter defenses – Firewall, IDS • Protect local area network and hosts • Keep external threats from internal network – Internal defenses – Virus scanning • Protect hosts from threats that get through the perimeter defenses – Extend the “perimeter” – VPN • Common practices, but could be improved – Internal threats are significant • Unhappy employees • Compromised hosts Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 20
Perimeter and Internal Defenses • Commonly deployed defenses – Perimeter defenses – Firewall, IDS • Protect local area network and hosts • Keep external threats from internal network – Internal defenses – Virus scanning • Protect hosts from threats that get through the perimeter defenses – Extend the “perimeter” – VPN • Common practices, but could be improved – Internal threats are significant • Unhappy employees • Compromised hosts Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 20
 • Standard perimeter defense mechanisms – Firewall • Packet filter (stateless, stateful) • Application layer proxies – Traffic shaping – Intrusion detection • Anomaly and misuse detection • Methods applicable to network or host Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 21
• Standard perimeter defense mechanisms – Firewall • Packet filter (stateless, stateful) • Application layer proxies – Traffic shaping – Intrusion detection • Anomaly and misuse detection • Methods applicable to network or host Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 21
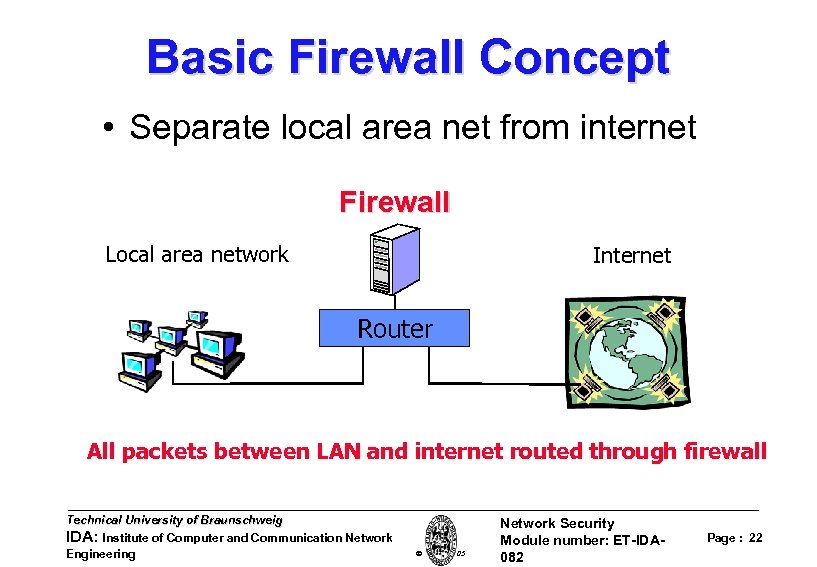 Basic Firewall Concept • Separate local area net from internet Firewall Local area network Internet Router All packets between LAN and internet routed through firewall Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 22
Basic Firewall Concept • Separate local area net from internet Firewall Local area network Internet Router All packets between LAN and internet routed through firewall Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 22
 Firewall goals • Prevent malicious attacks on hosts – Port sweeps, ICMP echo to broadcast addr, syn flooding, … – Worm propagation • Exploit buffer overflow in program listening on network • Prevent general disruption of internal network – External SMNP packets • Provide defense in depth – Programs contain bugs and are vulnerable to attack – Network protocols may contain; • Design weaknesses (SSH CRC) • Implementation flaws (SSL, NTP, FTP, SMTP. . . ) • Control traffic between “zones of trusts” Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 23
Firewall goals • Prevent malicious attacks on hosts – Port sweeps, ICMP echo to broadcast addr, syn flooding, … – Worm propagation • Exploit buffer overflow in program listening on network • Prevent general disruption of internal network – External SMNP packets • Provide defense in depth – Programs contain bugs and are vulnerable to attack – Network protocols may contain; • Design weaknesses (SSH CRC) • Implementation flaws (SSL, NTP, FTP, SMTP. . . ) • Control traffic between “zones of trusts” Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 23
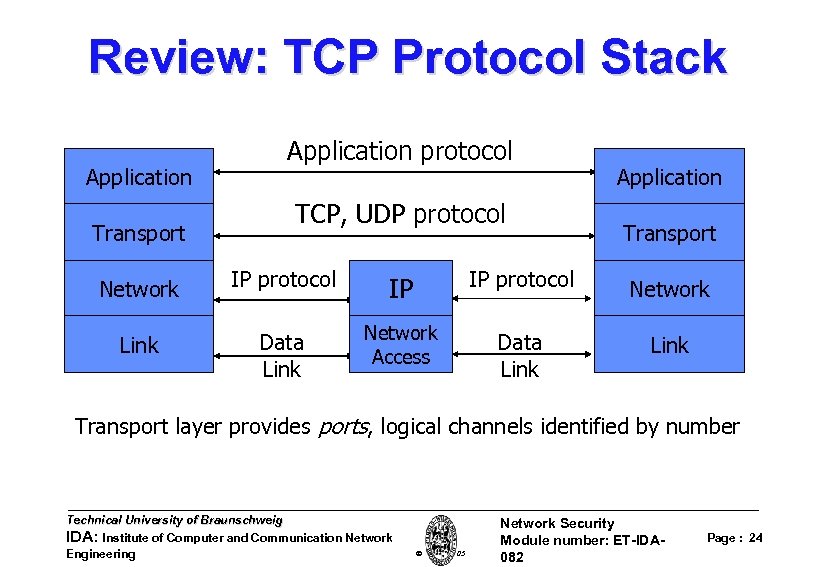 Review: TCP Protocol Stack Application Transport Application protocol TCP, UDP protocol Application Transport Network IP protocol IP IP protocol Network Link Data Link Network Access Data Link Transport layer provides ports, logical channels identified by number Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 24
Review: TCP Protocol Stack Application Transport Application protocol TCP, UDP protocol Application Transport Network IP protocol IP IP protocol Network Link Data Link Network Access Data Link Transport layer provides ports, logical channels identified by number Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 24
 Types of Firewalls • Three common types of Firewalls: – Packet-filtering routers – Application-level gateways – Circuit-level gateways Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 25
Types of Firewalls • Three common types of Firewalls: – Packet-filtering routers – Application-level gateways – Circuit-level gateways Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 25
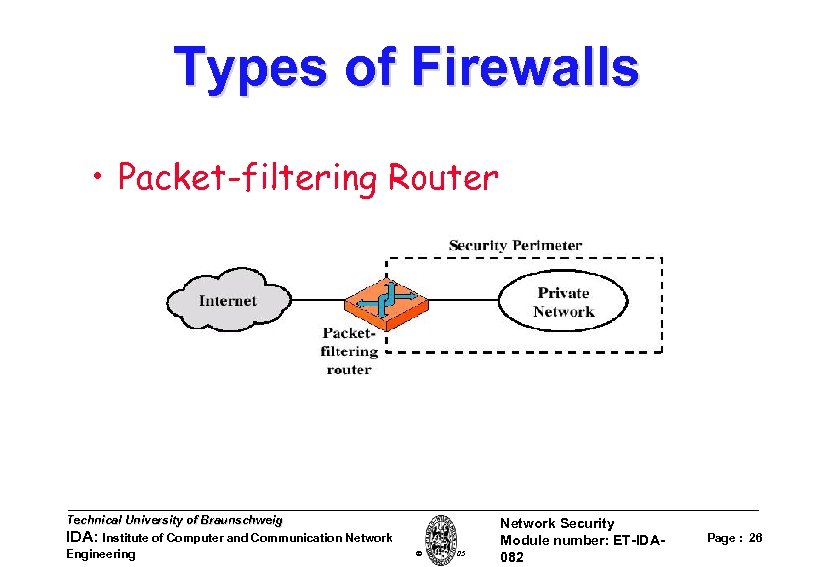 Types of Firewalls • Packet-filtering Router Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 26
Types of Firewalls • Packet-filtering Router Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 26
 Types of Firewalls • Packet-filtering Router – Applies a set of rules to each incoming IP packet and then forwards or discards the packet – Filter packets going in both directions – The packet filter is typically set up as a list of rules based on matches to fields in the IP or TCP header – Two default policies (discard or forward) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 27
Types of Firewalls • Packet-filtering Router – Applies a set of rules to each incoming IP packet and then forwards or discards the packet – Filter packets going in both directions – The packet filter is typically set up as a list of rules based on matches to fields in the IP or TCP header – Two default policies (discard or forward) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 27
 Packet-filtering Router • Advantages: – Simplicity – Transparency to users – High speed • Disadvantages: – Difficulty of setting up packet filter rules – Lack of Authentication Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 28
Packet-filtering Router • Advantages: – Simplicity – Transparency to users – High speed • Disadvantages: – Difficulty of setting up packet filter rules – Lack of Authentication Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 28
 Packet-filtering Router • Possible attacks and appropriate countermeasures – IP address spoofing – Source routing attacks – Tiny fragment attacks Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 29
Packet-filtering Router • Possible attacks and appropriate countermeasures – IP address spoofing – Source routing attacks – Tiny fragment attacks Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 29
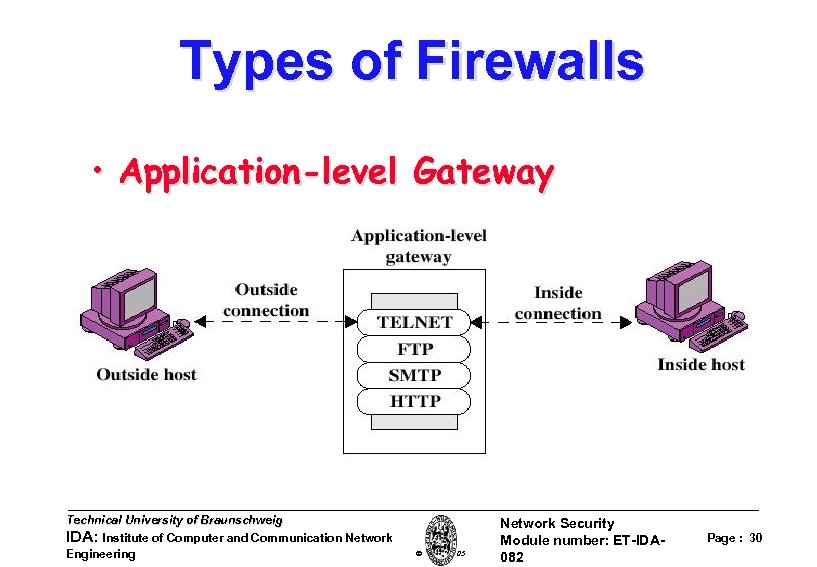 Types of Firewalls • Application-level Gateway Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 30
Types of Firewalls • Application-level Gateway Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 30
 Types of Firewalls • Application-level Gateway – Also called proxy server – Acts as a relay of application-level traffic Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 31
Types of Firewalls • Application-level Gateway – Also called proxy server – Acts as a relay of application-level traffic Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 31
 Application-level Gateway • Advantages: – Higher security than packet filters – Only need to scrutinize a few allowable applications – Easy to log and audit all incoming traffic • Disadvantages: – Additional processing overhead on each connection (gateway as splice point) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 32
Application-level Gateway • Advantages: – Higher security than packet filters – Only need to scrutinize a few allowable applications – Easy to log and audit all incoming traffic • Disadvantages: – Additional processing overhead on each connection (gateway as splice point) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 32
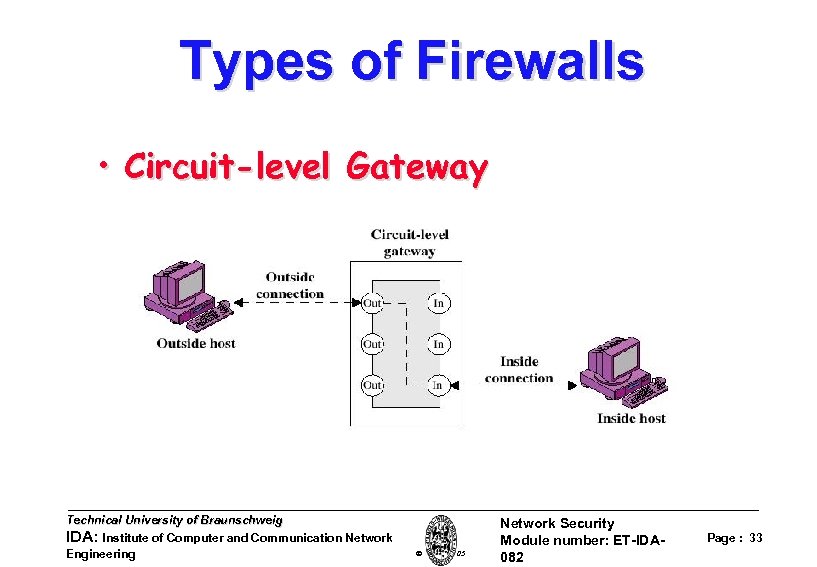 Types of Firewalls • Circuit-level Gateway Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 33
Types of Firewalls • Circuit-level Gateway Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 33
 Circuit-level Gateway • Circuit-level Gateway – Stand-alone system or – Specialized function performed by an Application-level Gateway – Sets up two TCP connections – The gateway typically relays TCP segments from one connection to the other without examining the contents Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 34
Circuit-level Gateway • Circuit-level Gateway – Stand-alone system or – Specialized function performed by an Application-level Gateway – Sets up two TCP connections – The gateway typically relays TCP segments from one connection to the other without examining the contents Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 34
 Circuit-level Gateway • Circuit-level Gateway – The security function consists of determining which connections will be allowed – Typically use is a situation in which the system administrator trusts the internal users – An example is the SOCKS package Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 35
Circuit-level Gateway • Circuit-level Gateway – The security function consists of determining which connections will be allowed – Typically use is a situation in which the system administrator trusts the internal users – An example is the SOCKS package Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 35
 Firewall Configurations • In addition to the use of simple configuration of a single system (single packet filtering router or single gateway), more complex configurations are possible • Three common configurations Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 36
Firewall Configurations • In addition to the use of simple configuration of a single system (single packet filtering router or single gateway), more complex configurations are possible • Three common configurations Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 36
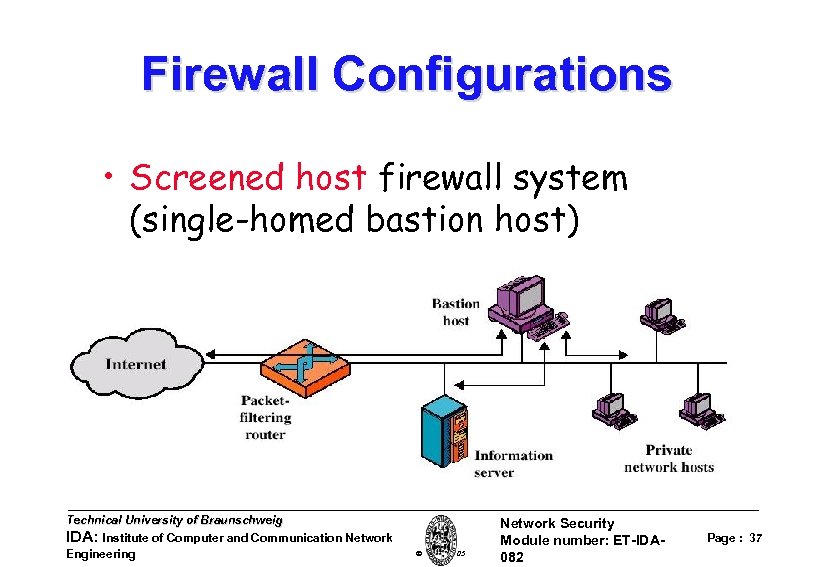 Firewall Configurations • Screened host firewall system (single-homed bastion host) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 37
Firewall Configurations • Screened host firewall system (single-homed bastion host) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 37
 Firewall Configurations • Screened host firewall, single-homed bastion configuration • Firewall consists of two systems: – A packet-filtering router – A bastion host Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 38
Firewall Configurations • Screened host firewall, single-homed bastion configuration • Firewall consists of two systems: – A packet-filtering router – A bastion host Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 38
 Firewall Configurations • Configuration for the packetfiltering router: – Only packets from and to the bastion host are allowed to pass through the router • The bastion host performs authentication and proxy functions Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 39
Firewall Configurations • Configuration for the packetfiltering router: – Only packets from and to the bastion host are allowed to pass through the router • The bastion host performs authentication and proxy functions Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 39
 Firewall Configurations • Greater security than single configurations because of two reasons: – This configuration implements both packet-level and application-level filtering (allowing for flexibility in defining security policy) – An intruder must generally penetrate two separate systems Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 40
Firewall Configurations • Greater security than single configurations because of two reasons: – This configuration implements both packet-level and application-level filtering (allowing for flexibility in defining security policy) – An intruder must generally penetrate two separate systems Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 40
 Firewall Configurations • This configuration also affords flexibility in providing direct Internet access (public information server, e. g. Web server) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 41
Firewall Configurations • This configuration also affords flexibility in providing direct Internet access (public information server, e. g. Web server) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 41
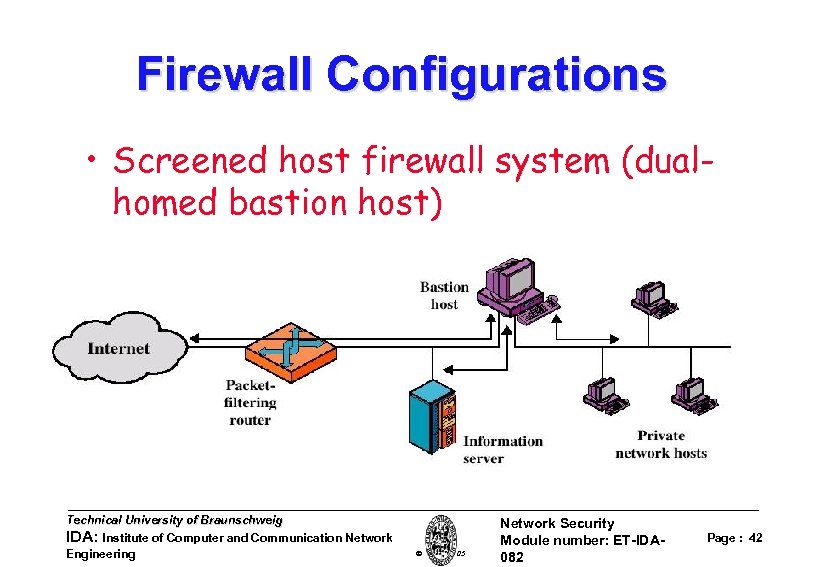 Firewall Configurations • Screened host firewall system (dualhomed bastion host) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 42
Firewall Configurations • Screened host firewall system (dualhomed bastion host) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 42
 Firewall Configurations • Screened host firewall, dual-homed bastion configuration – The packet-filtering router is not completely compromised – Traffic between the Internet and other hosts on the private network has to flow through the bastion host Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 43
Firewall Configurations • Screened host firewall, dual-homed bastion configuration – The packet-filtering router is not completely compromised – Traffic between the Internet and other hosts on the private network has to flow through the bastion host Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 43
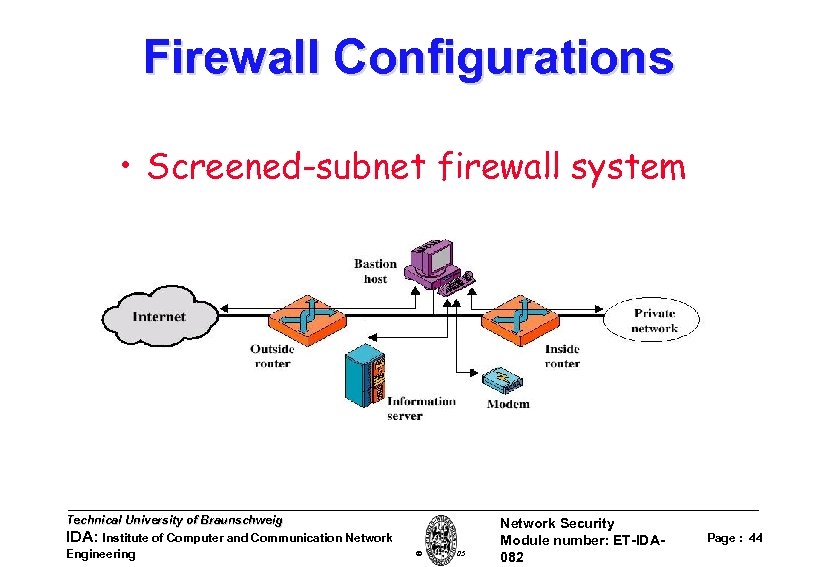 Firewall Configurations • Screened-subnet firewall system Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 44
Firewall Configurations • Screened-subnet firewall system Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 44
 Firewall Configurations • Screened subnet firewall configuration – Most secure configuration of the three – Two packet-filtering routers are used – Creation of an isolated sub-network Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 45
Firewall Configurations • Screened subnet firewall configuration – Most secure configuration of the three – Two packet-filtering routers are used – Creation of an isolated sub-network Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 45
 Firewall Configurations • Advantages: – Three levels of defense to thwart intruders – The outside router advertises only the existence of the screened subnet to the Internet (internal network is invisible to the Internet) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 46
Firewall Configurations • Advantages: – Three levels of defense to thwart intruders – The outside router advertises only the existence of the screened subnet to the Internet (internal network is invisible to the Internet) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 46
 Firewall Configurations • Advantages: – The inside router advertises only the existence of the screened subnet to the internal network (the systems on the inside network cannot construct direct routes to the Internet) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 47
Firewall Configurations • Advantages: – The inside router advertises only the existence of the screened subnet to the internal network (the systems on the inside network cannot construct direct routes to the Internet) Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 47
 Trusted System Technology Trusted Computing • One way to enhance the ability of a system to defend against intruders and malicious programs is to implement trusted system technology Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 48
Trusted System Technology Trusted Computing • One way to enhance the ability of a system to defend against intruders and malicious programs is to implement trusted system technology Technical University of Braunschweig IDA: Institute of Computer and Communication Network Engineering W. Adi 2005 Network Security Module number: ET-IDA 082 Page : 48


