3c7a576972267b71ee9a1038d65164d3.ppt
- Количество слайдов: 37
Navigating the Digital Fishbowl: Forensics and Anti-Forensics J. A. “Drew” Hamilton, Jr. , Ph. D. Professor, Computer Science & Engineering Associate Vice President for Research Office of Research & Economic Development 1
Unrealistic Hacker Fears Office of Research & Economic Development 2
SSL Side Channel Attacks First off, what is SSL? When can an attacker see your traffic? No SSL Wireless Untrusted networks Office of Research & Economic Development 3
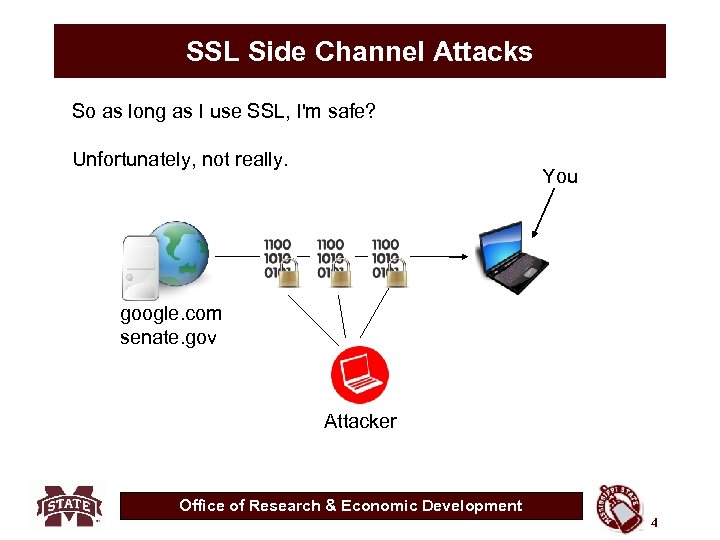
SSL Side Channel Attacks So as long as I use SSL, I'm safe? Unfortunately, not really. You google. com senate. gov Attacker Office of Research & Economic Development 4
SSL Side Channel Attacks In the past year, multiple proof-of-concept demonstrations have shown that this traffic analysis can be used to reliably guess at the content of your traffic. Specifically, an attack on Google Maps has shown that it is possible to determine the GPS coordinates of the location a Google Maps user is looking at. What else could potentially be vulnerable? Google Searches Youtube videos Streaming music Wikipedia Other “Web 2. 0” sites This isn't just limited to SSL, either. VPN and other forms of encryption suffer from some of the same flaws. Office of Research & Economic Development 5
Trend Manipulation • Whatever became of The Orchids? What if you create 5, 000 Virtual Machines, 5, 000 dummy accounts and 5, 000 “likes” for the Orchids? Office of Research & Economic Development 6
Forensic methodologies / capabilities Overriding Philosophy: (NSA-Based) • “All commercial systems & software can be compromised. ” • “The primary purpose of forensic analysis is to determine what has been touched, tampered and/or compromised. ” • My emphasis at Auburn was on detection not prosecution. • Anti-forensic capability developed as result of work for the Missile Defense Agency Office of Research & Economic Development 7
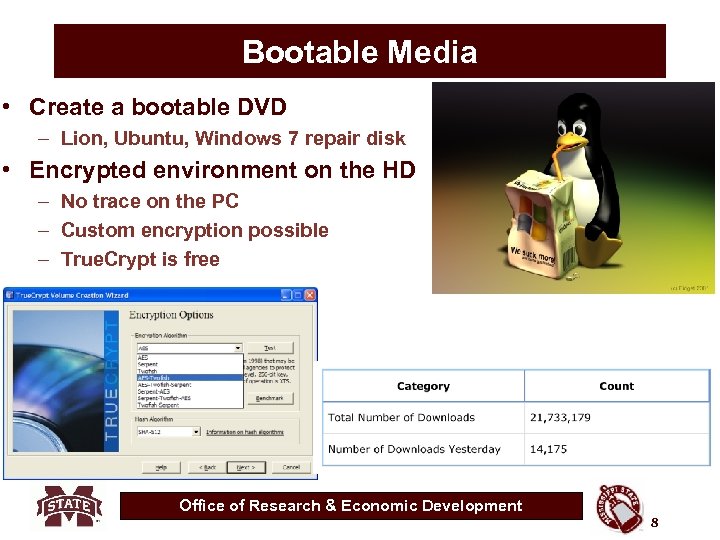
Bootable Media • Create a bootable DVD – Lion, Ubuntu, Windows 7 repair disk • Encrypted environment on the HD – No trace on the PC – Custom encryption possible – True. Crypt is free Office of Research & Economic Development 8
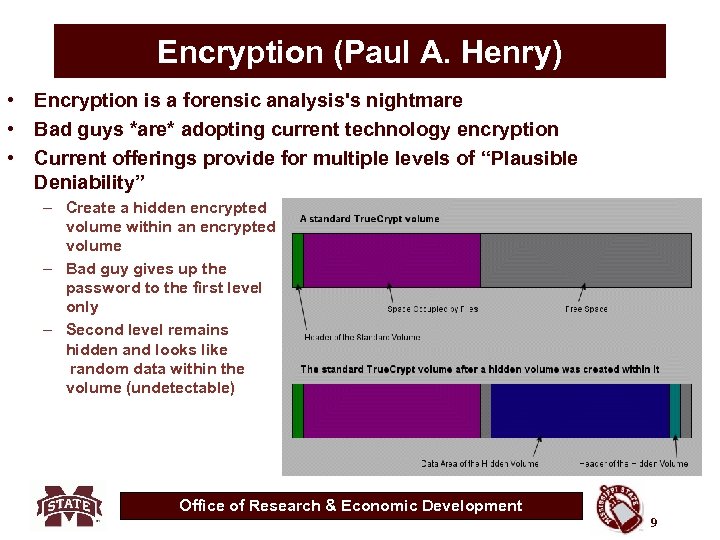
Encryption (Paul A. Henry) • Encryption is a forensic analysis's nightmare • Bad guys *are* adopting current technology encryption • Current offerings provide for multiple levels of “Plausible Deniability” – Create a hidden encrypted volume within an encrypted volume – Bad guy gives up the password to the first level only – Second level remains hidden and looks like random data within the volume (undetectable) Office of Research & Economic Development 9
Encryption and the 5 th Amendment • Is being forced to reveal your decryption password a violation of the constitutional guarantee of freedom from self-incrimination in a criminal trial? • Colorado U. S. District Judge Robert Blackburn ruled, failing to compel the defendant to decrypt her laptop would amount to "a concession to her and potential criminals" in other types of cases that they can evade prosecution or conviction by encrypting all digital evidence that might implicate them in crimes. • http: //gcn. com/articles/2012/01/24/agg-laptop-decryptioncourt-order-ruling. aspx? s=gcndaily_250112 Office of Research & Economic Development 10
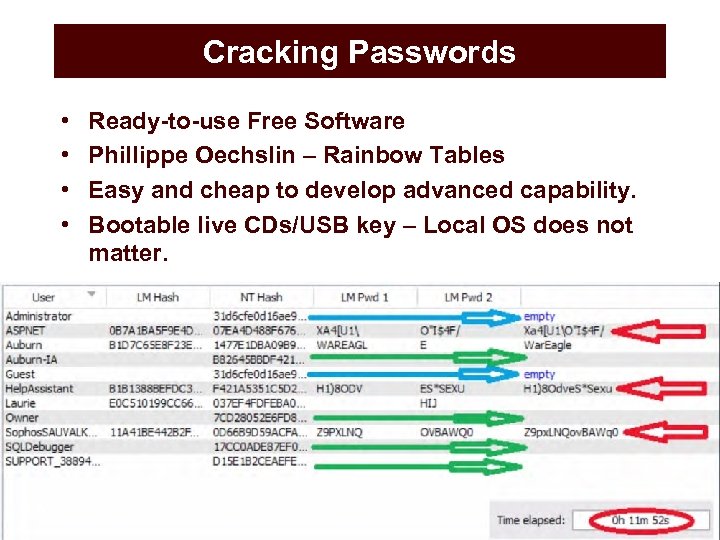
Cracking Passwords • • Ready-to-use Free Software Phillippe Oechslin – Rainbow Tables Easy and cheap to develop advanced capability. Bootable live CDs/USB key – Local OS does not matter. Office of Research & Economic Development 11
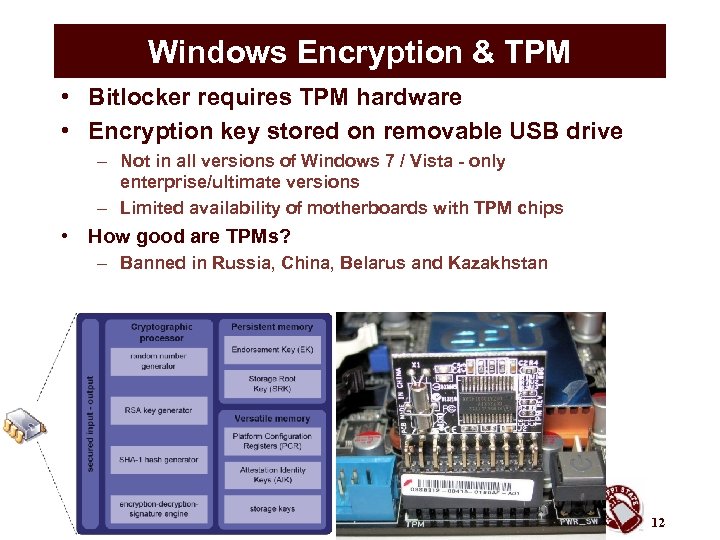
Windows Encryption & TPM • Bitlocker requires TPM hardware • Encryption key stored on removable USB drive – Not in all versions of Windows 7 / Vista - only enterprise/ultimate versions – Limited availability of motherboards with TPM chips • How good are TPMs? – Banned in Russia, China, Belarus and Kazakhstan Office of Research & Economic Development 12
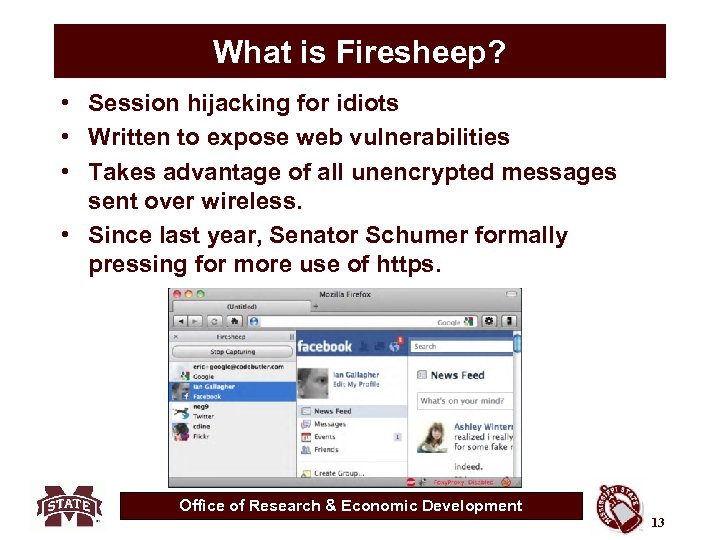
What is Firesheep? • Session hijacking for idiots • Written to expose web vulnerabilities • Takes advantage of all unencrypted messages sent over wireless. • Since last year, Senator Schumer formally pressing for more use of https. Office of Research & Economic Development 13
Have You Got Your Mojo (pac)? • • Mojo. Pac makes your USB Drive or IPOD your PC Leaves no trace on the host Free download www. mojopac. com Office of Research & Economic Development 14
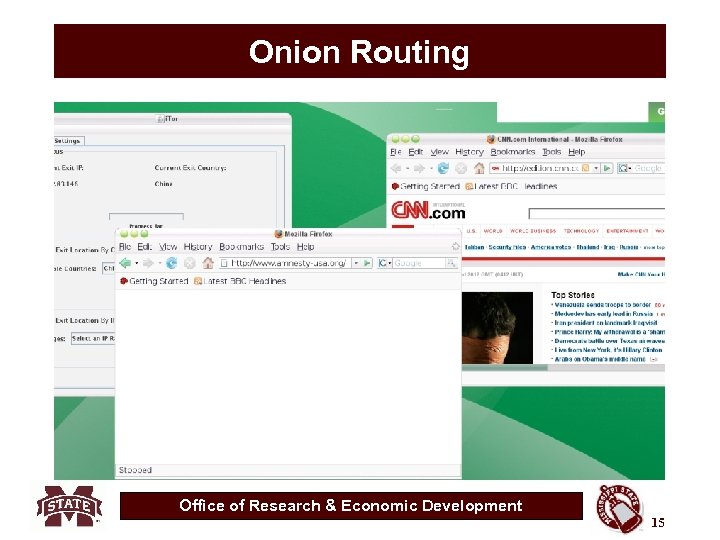
Onion Routing Office of Research & Economic Development 15
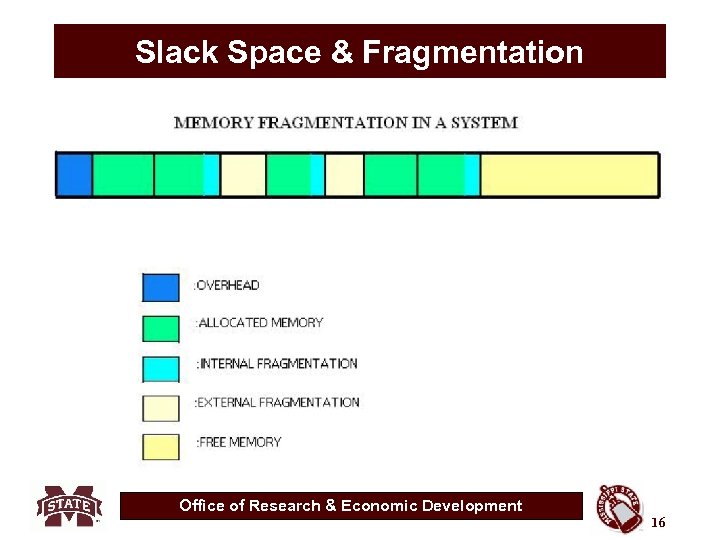
Slack Space & Fragmentation Office of Research & Economic Development 16
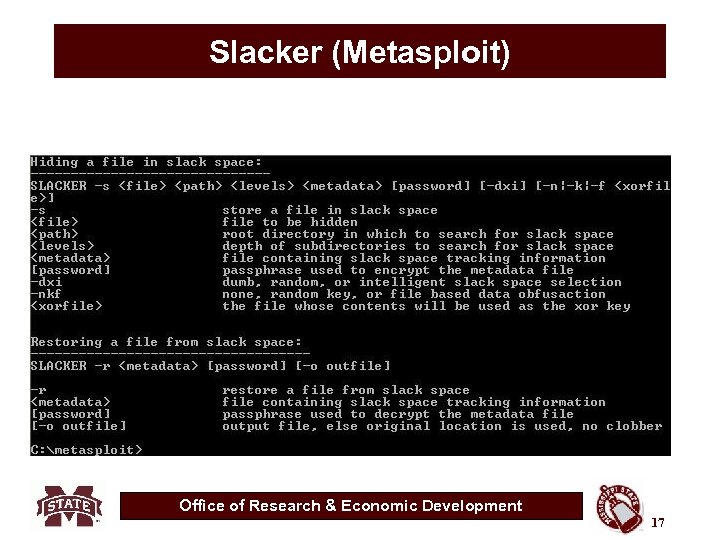
Slacker (Metasploit) Office of Research & Economic Development 17
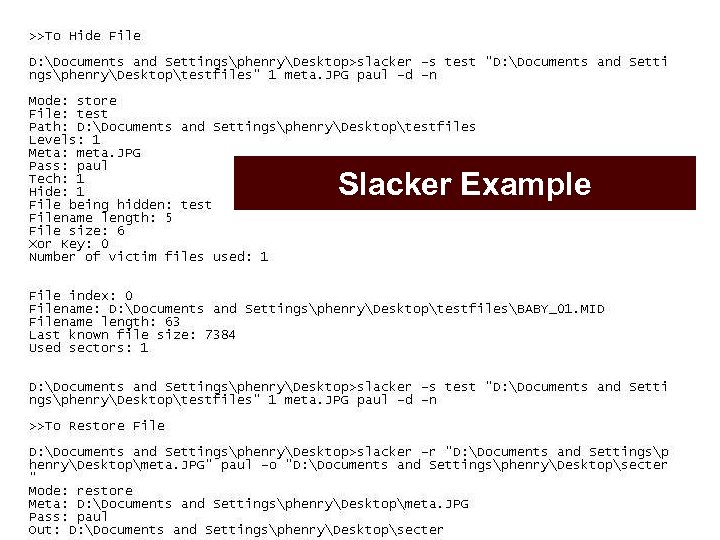
Slacker Example Office of Research & Economic Development 18
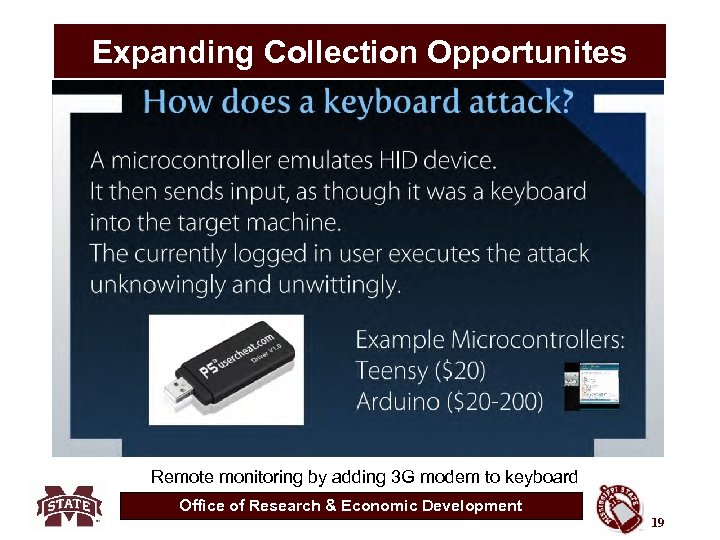
Expanding Collection Opportunites Remote monitoring by adding 3 G modem to keyboard Office of Research & Economic Development 19
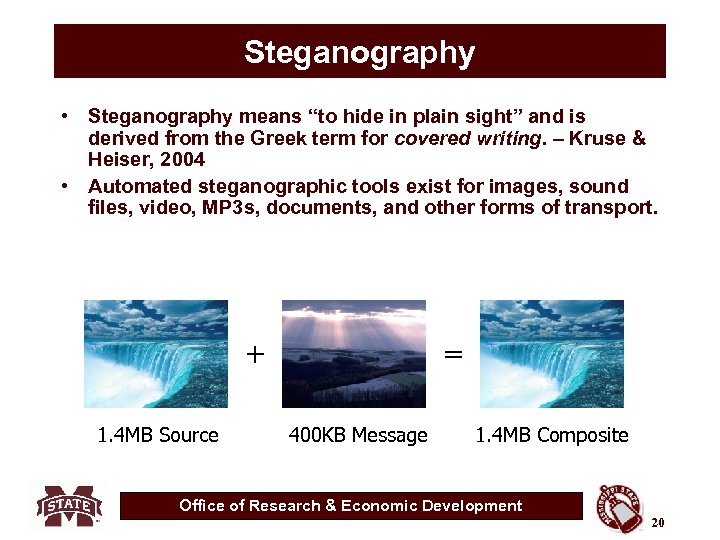
Steganography • Steganography means “to hide in plain sight” and is derived from the Greek term for covered writing. – Kruse & Heiser, 2004 • Automated steganographic tools exist for images, sound files, video, MP 3 s, documents, and other forms of transport. + 1. 4 MB Source = 400 KB Message 1. 4 MB Composite Office of Research & Economic Development 20
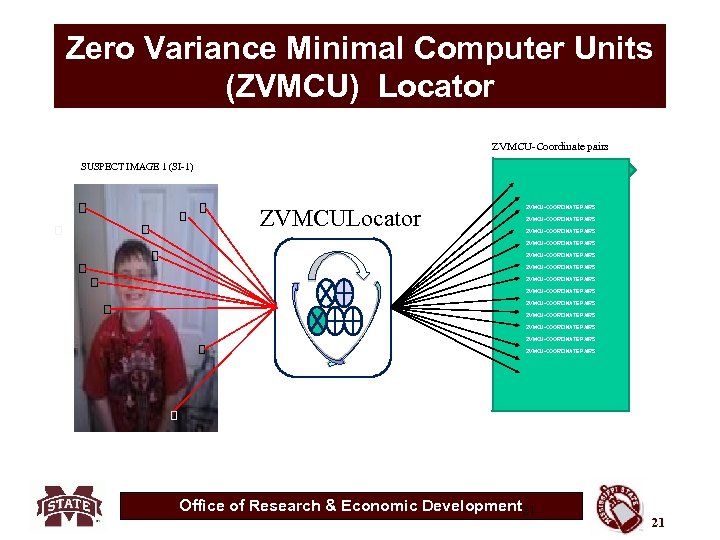
Zero Variance Minimal Computer Units (ZVMCU) Locator ZVMCU-Coordinate pairs SUSPECT IMAGE 1 (SI-1) ZVMCULocator ZVMCU-COORDINATE PAIRS ZVMCU-COORDINATE PAIRS ZVMCU-COORDINATE PAIRS ZVMCU-COORDINATE PAIRS Office of Research & Economic Development 21 21
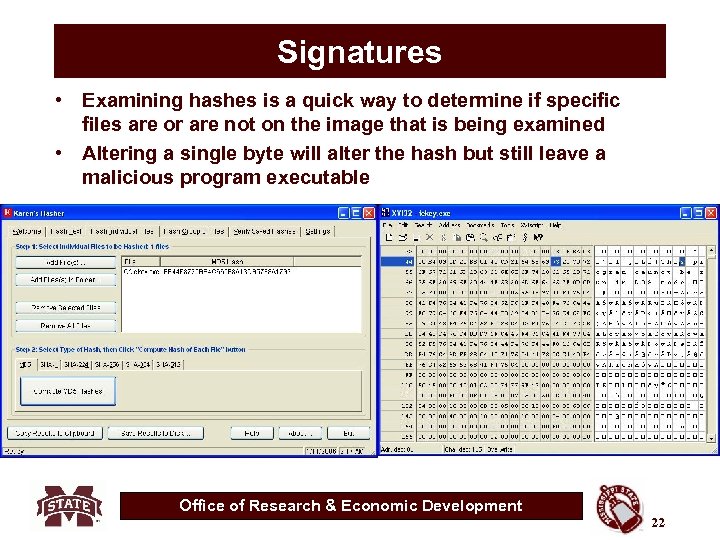
Signatures • Examining hashes is a quick way to determine if specific files are or are not on the image that is being examined • Altering a single byte will alter the hash but still leave a malicious program executable Office of Research & Economic Development 22
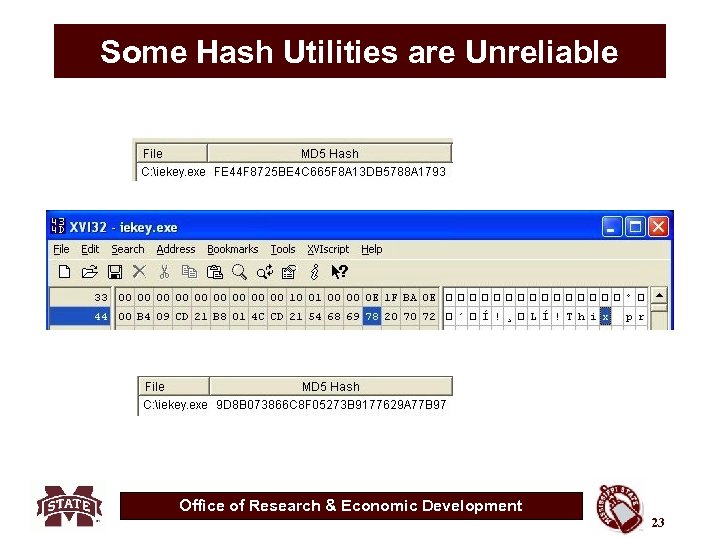
Some Hash Utilities are Unreliable Office of Research & Economic Development 23
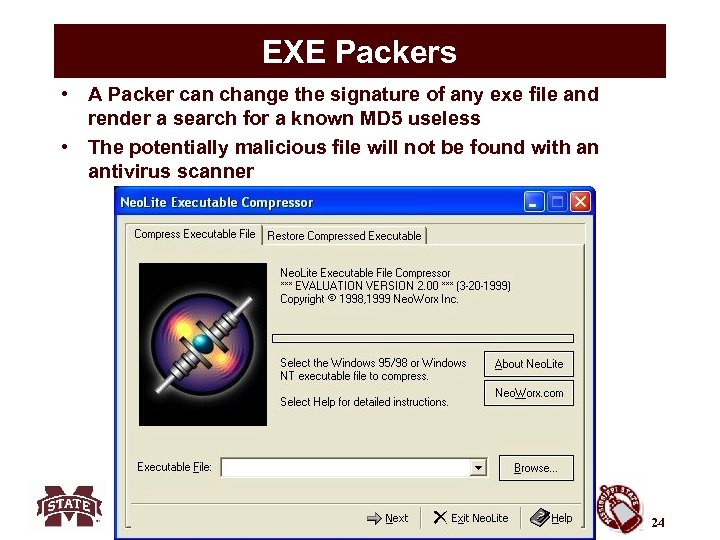
EXE Packers • A Packer can change the signature of any exe file and render a search for a known MD 5 useless • The potentially malicious file will not be found with an antivirus scanner Office of Research & Economic Development 24
Binders • Binders combine two or more executable in to a single executable file • Allows the bad guy to attach a Trojan, Key logger or other malicious program to a common exe file • The resulting MD 5 will not match a known bad database • 37 different free binders are downloadable at http: //www. trojanfrance. com/index. php? dir=Binde rs/ Office of Research & Economic Development 25
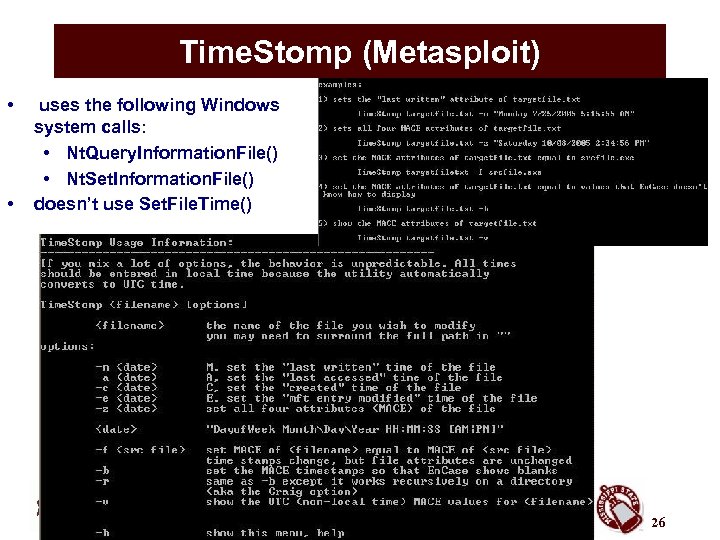
Time. Stomp (Metasploit) • • uses the following Windows system calls: • Nt. Query. Information. File() • Nt. Set. Information. File() doesn’t use Set. File. Time() Metasploit Anti. Forensics Project Office of Research & Economic Development 26
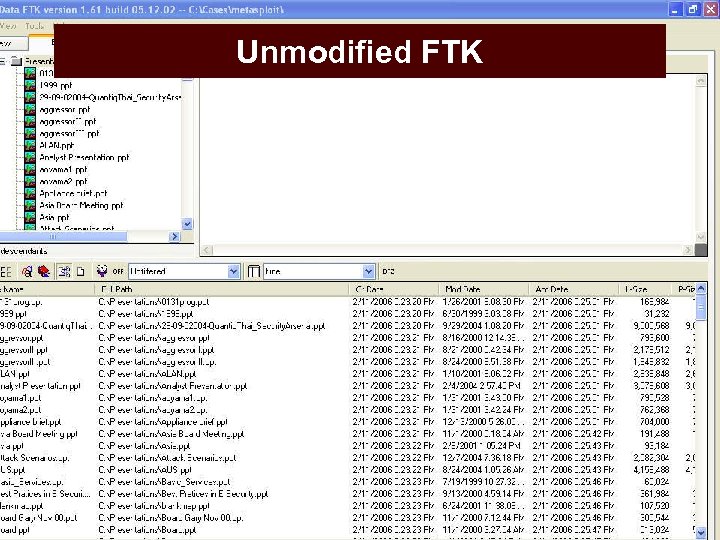
Unmodified FTK Office of Research & Economic Development 27
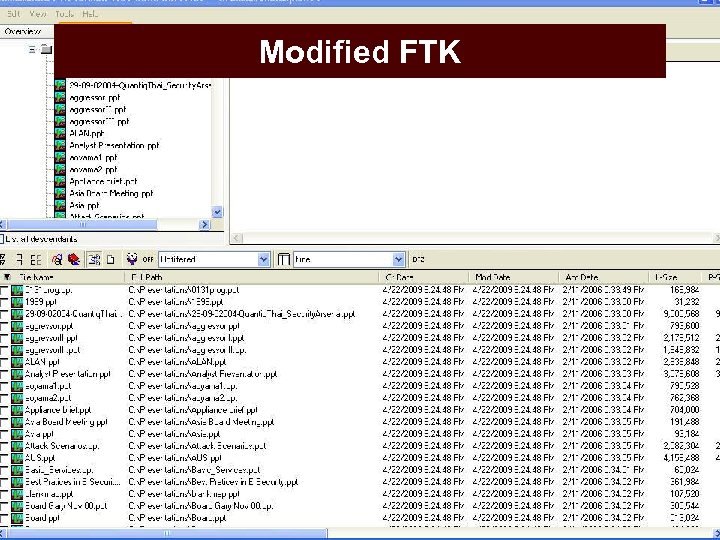
Modified FTK Office of Research & Economic Development 28
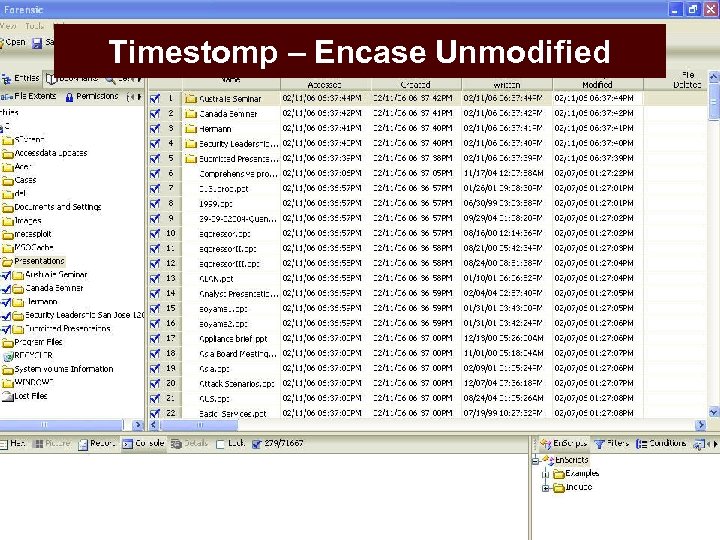
Timestomp – Encase Unmodified Office of Research & Economic Development 29
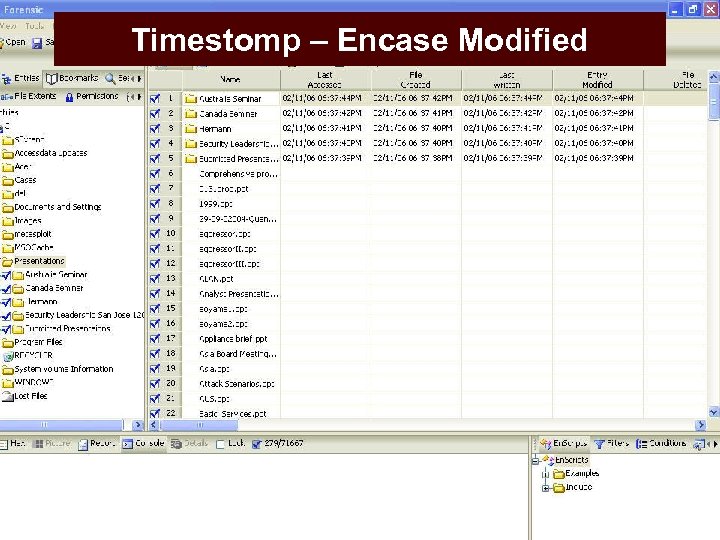
Timestomp – Encase Modified Office of Research & Economic Development 30
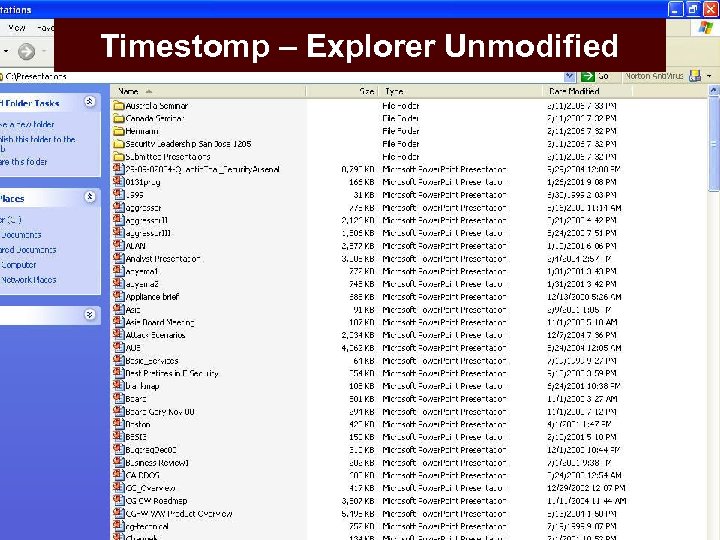
Timestomp – Explorer Unmodified Office of Research & Economic Development 31
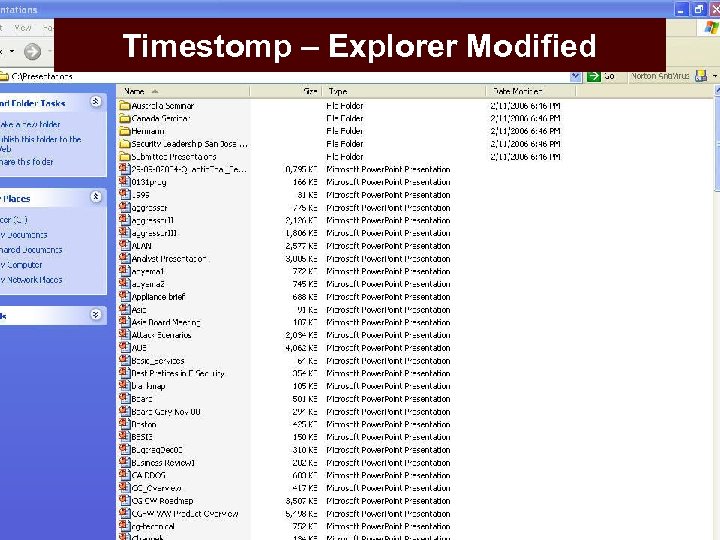
Timestomp – Explorer Modified Office of Research & Economic Development 32
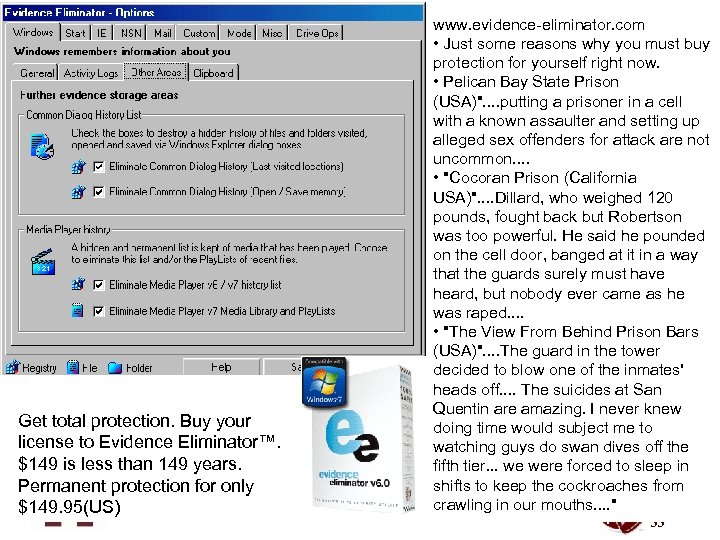
www. evidence-eliminator. com • Just some reasons why you must buy protection for yourself right now. • Pelican Bay State Prison (USA)". . putting a prisoner in a cell with a known assaulter and setting up alleged sex offenders for attack are not uncommon. . • "Cocoran Prison (California USA)". . Dillard, who weighed 120 pounds, fought back but Robertson was too powerful. He said he pounded on the cell door, banged at it in a way that the guards surely must have heard, but nobody ever came as he was raped. . • "The View From Behind Prison Bars (USA)". . The guard in the tower decided to blow one of the inmates' heads off. . The suicides at San Quentin are amazing. I never knew Get total protection. Buy your doing time would subject me to license to Evidence Eliminator™. watching guys do swan dives off the $149 is less than 149 years. fifth tier. . . we were forced to sleep in shifts to keep the cockroaches from Permanent protection for only crawling in our Office of Research & Economic Development mouths. . " $149. 95(US) 33
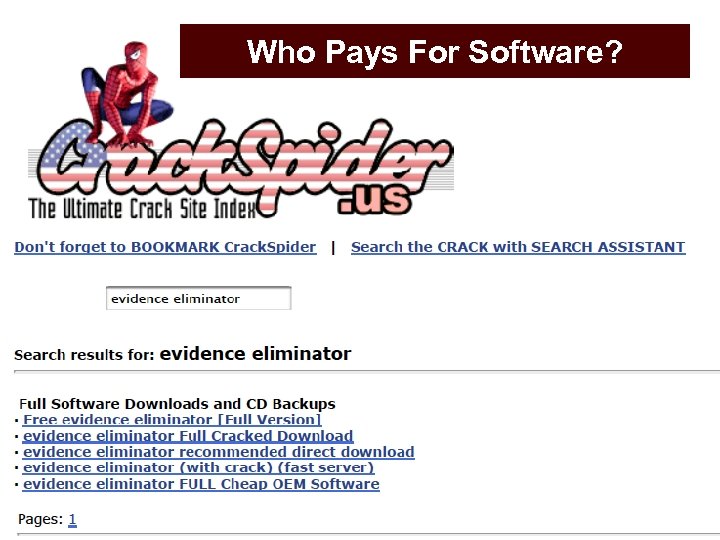
Who Pays For Software? Office of Research & Economic Development 34

Magnetic Remanance Office of Research & Economic Development 35
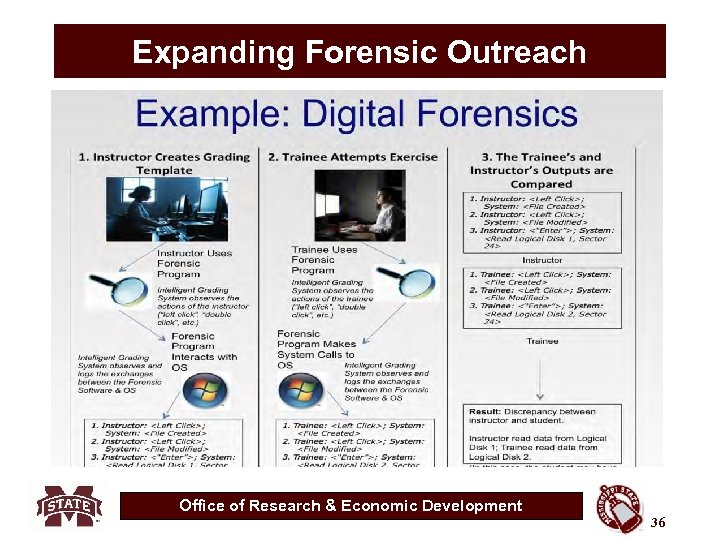
Expanding Forensic Outreach Office of Research & Economic Development 36
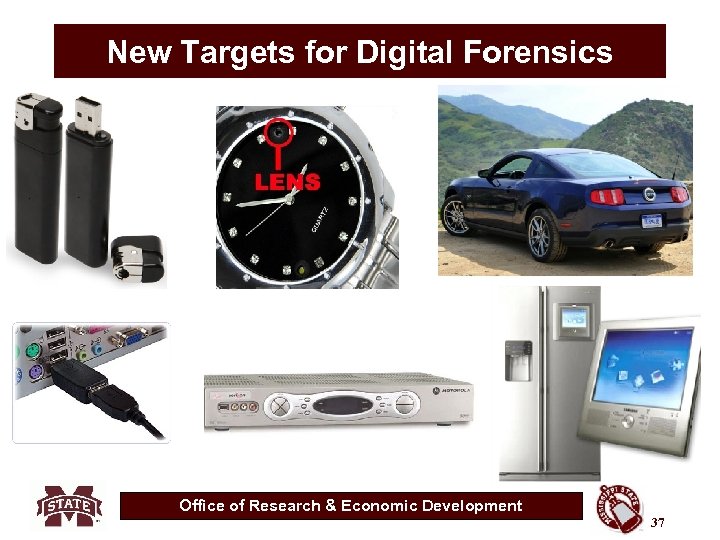
New Targets for Digital Forensics Office of Research & Economic Development 37
3c7a576972267b71ee9a1038d65164d3.ppt