df877a46cce3e098685e52e4b95bf1f9.ppt
- Количество слайдов: 39
 NATO VM 3 D Conference at Defense Research Establishment Valcartier Presented By: Chet Maciag DIW In-house Program Manager 8 June 00 Defensive Information Warfare Branch Air Force Research Lab, Rome Research Site (AFRL/IFGB)
NATO VM 3 D Conference at Defense Research Establishment Valcartier Presented By: Chet Maciag DIW In-house Program Manager 8 June 00 Defensive Information Warfare Branch Air Force Research Lab, Rome Research Site (AFRL/IFGB)
 Application Domain: Information Warfare “…information operations conducted to defend one’s own information and information systems or attacking and affecting an adversary’s information and information systems. ” (AFDD 2 -5) “. . . information warfare is about the way humans think and, more importantly, the way humans make decisions. The target of information warfare, then, is the human. . . ” – Prof George Stein, Air War College
Application Domain: Information Warfare “…information operations conducted to defend one’s own information and information systems or attacking and affecting an adversary’s information and information systems. ” (AFDD 2 -5) “. . . information warfare is about the way humans think and, more importantly, the way humans make decisions. The target of information warfare, then, is the human. . . ” – Prof George Stein, Air War College
 Definition - U. S. (Information Warfare and Information Assurance) • Information Assurance – Information operations that protect and defend information and information systems by ensuring their availability, integrity, authentication, confidentiality, and non-repudiation. Information assurance includes providing for restoration of information systems by incorporating protection, detection, and reaction capabilities. (DODD S-3600. 1)
Definition - U. S. (Information Warfare and Information Assurance) • Information Assurance – Information operations that protect and defend information and information systems by ensuring their availability, integrity, authentication, confidentiality, and non-repudiation. Information assurance includes providing for restoration of information systems by incorporating protection, detection, and reaction capabilities. (DODD S-3600. 1)
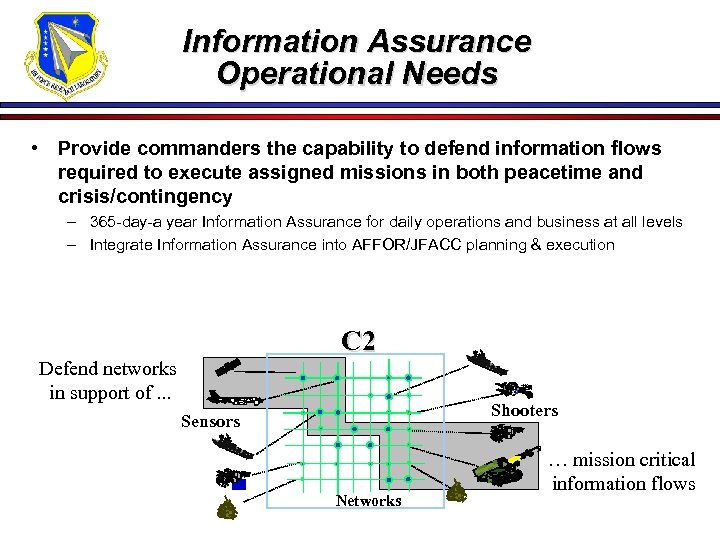 Information Assurance Operational Needs • Provide commanders the capability to defend information flows required to execute assigned missions in both peacetime and crisis/contingency – 365 -day-a year Information Assurance for daily operations and business at all levels – Integrate Information Assurance into AFFOR/JFACC planning & execution C 2 Defend networks in support of. . . Shooters Sensors Networks … mission critical information flows
Information Assurance Operational Needs • Provide commanders the capability to defend information flows required to execute assigned missions in both peacetime and crisis/contingency – 365 -day-a year Information Assurance for daily operations and business at all levels – Integrate Information Assurance into AFFOR/JFACC planning & execution C 2 Defend networks in support of. . . Shooters Sensors Networks … mission critical information flows
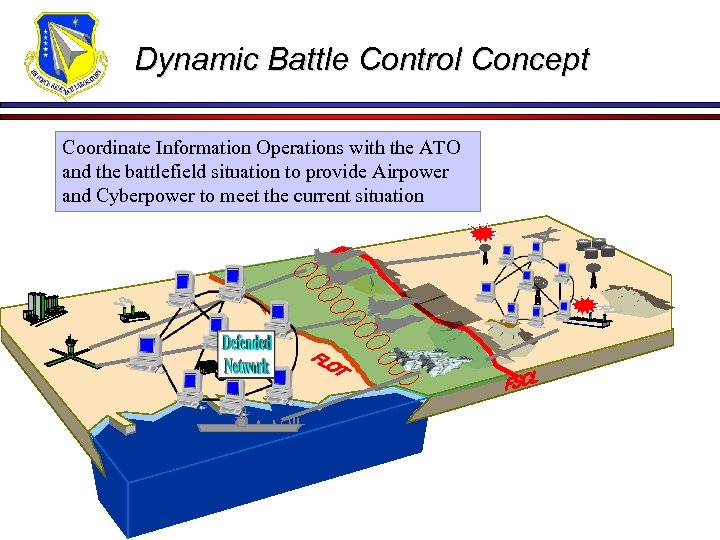 Dynamic Battle Control Concept Coordinate Information Operations with the ATO and the battlefield situation to provide Airpower and Cyberpower to meet the current situation
Dynamic Battle Control Concept Coordinate Information Operations with the ATO and the battlefield situation to provide Airpower and Cyberpower to meet the current situation
 Analogous State of Art in IA
Analogous State of Art in IA
 Moonlight Maze “Russian Hackers Steal US Weapons Secrets” “American officials believe Russia may have stolen some of the nation's most sensitive military secrets, including weapons guidance systems and naval intelligence codes, in a concerted espionage offensive that investigators have called operation Moonlight Maze. This was so sophisticated and well coordinated that security experts trying to build ramparts against further incursions believe America may be losing the world's first ‘cyber war’. ” 25 July 1999 London Sunday Times (Interview with Mr. John Hamre, Deputy Secretary of Defense)
Moonlight Maze “Russian Hackers Steal US Weapons Secrets” “American officials believe Russia may have stolen some of the nation's most sensitive military secrets, including weapons guidance systems and naval intelligence codes, in a concerted espionage offensive that investigators have called operation Moonlight Maze. This was so sophisticated and well coordinated that security experts trying to build ramparts against further incursions believe America may be losing the world's first ‘cyber war’. ” 25 July 1999 London Sunday Times (Interview with Mr. John Hamre, Deputy Secretary of Defense)
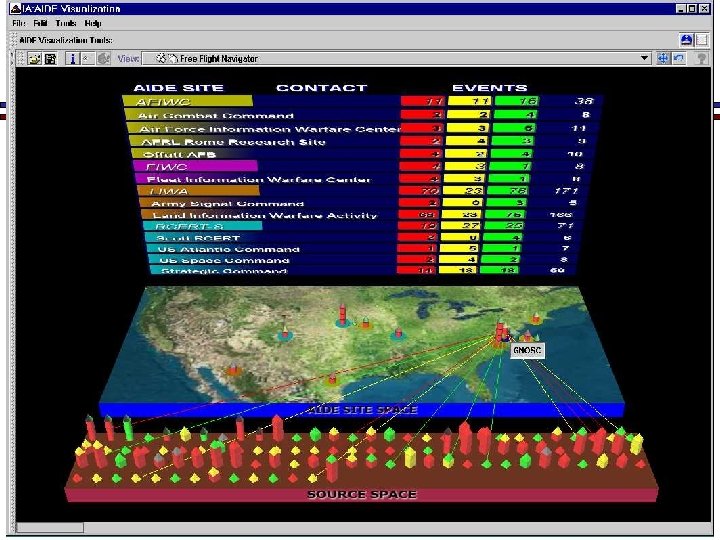
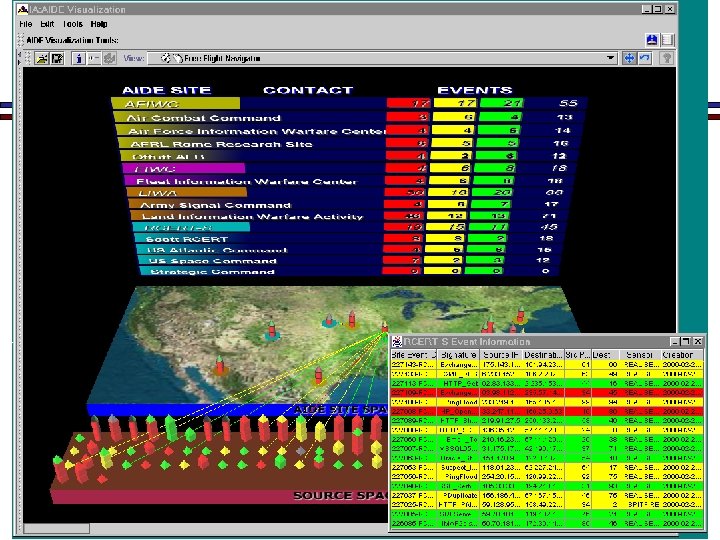
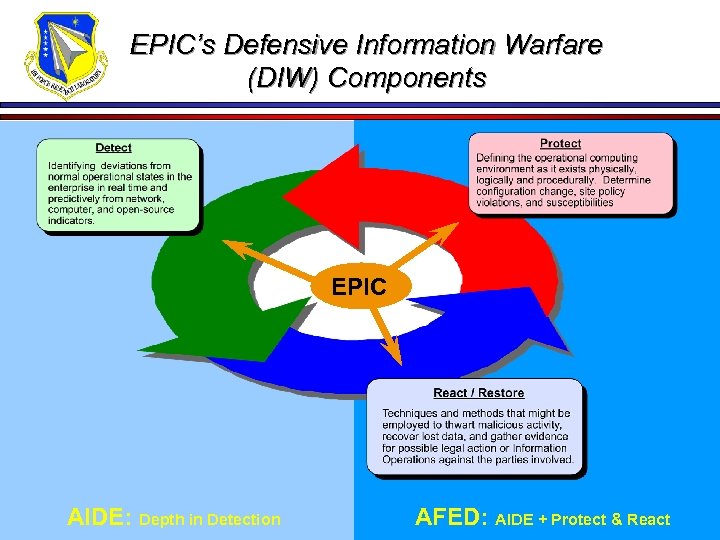 EPIC’s Defensive Information Warfare (DIW) Components EPIC AIDE: Depth in Detection AFED: AIDE + Protect & React
EPIC’s Defensive Information Warfare (DIW) Components EPIC AIDE: Depth in Detection AFED: AIDE + Protect & React
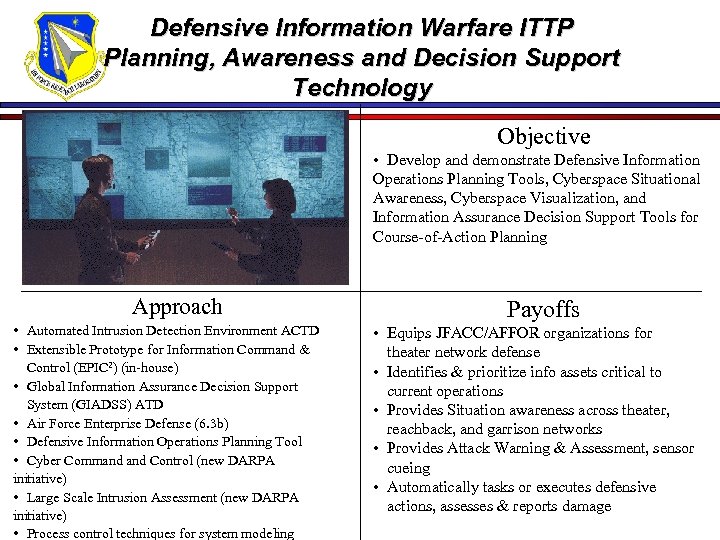 Defensive Information Warfare ITTP Planning, Awareness and Decision Support Technology Objective • Develop and demonstrate Defensive Information Operations Planning Tools, Cyberspace Situational Awareness, Cyberspace Visualization, and Information Assurance Decision Support Tools for Course-of-Action Planning Approach • Automated Intrusion Detection Environment ACTD • Extensible Prototype for Information Command & Control (EPIC 2) (in-house) • Global Information Assurance Decision Support System (GIADSS) ATD • Air Force Enterprise Defense (6. 3 b) • Defensive Information Operations Planning Tool • Cyber Command Control (new DARPA initiative) • Large Scale Intrusion Assessment (new DARPA initiative) • Process control techniques for system modeling Payoffs • Equips JFACC/AFFOR organizations for theater network defense • Identifies & prioritize info assets critical to current operations • Provides Situation awareness across theater, reachback, and garrison networks • Provides Attack Warning & Assessment, sensor cueing • Automatically tasks or executes defensive actions, assesses & reports damage
Defensive Information Warfare ITTP Planning, Awareness and Decision Support Technology Objective • Develop and demonstrate Defensive Information Operations Planning Tools, Cyberspace Situational Awareness, Cyberspace Visualization, and Information Assurance Decision Support Tools for Course-of-Action Planning Approach • Automated Intrusion Detection Environment ACTD • Extensible Prototype for Information Command & Control (EPIC 2) (in-house) • Global Information Assurance Decision Support System (GIADSS) ATD • Air Force Enterprise Defense (6. 3 b) • Defensive Information Operations Planning Tool • Cyber Command Control (new DARPA initiative) • Large Scale Intrusion Assessment (new DARPA initiative) • Process control techniques for system modeling Payoffs • Equips JFACC/AFFOR organizations for theater network defense • Identifies & prioritize info assets critical to current operations • Provides Situation awareness across theater, reachback, and garrison networks • Provides Attack Warning & Assessment, sensor cueing • Automatically tasks or executes defensive actions, assesses & reports damage
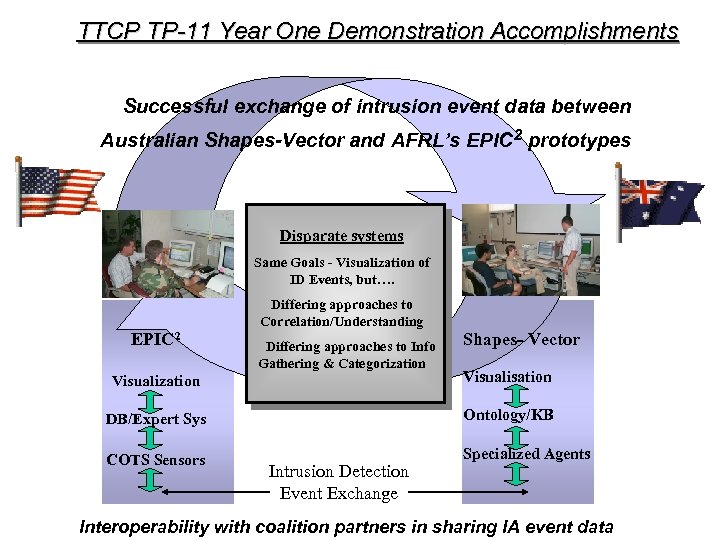 TTCP TP-11 Year One Demonstration Accomplishments Successful exchange of intrusion event data between Australian Shapes-Vector and AFRL’s EPIC 2 prototypes Disparate systems Same Goals - Visualization of ID Events, but…. Differing approaches to Correlation/Understanding EPIC 2 Differing approaches to Info Gathering & Categorization Shapes- Vector Visualization Visualisation DB/Expert Sys Ontology/KB COTS Sensors Specialized Agents Intrusion Detection Event Exchange Interoperability with coalition partners in sharing IA event data
TTCP TP-11 Year One Demonstration Accomplishments Successful exchange of intrusion event data between Australian Shapes-Vector and AFRL’s EPIC 2 prototypes Disparate systems Same Goals - Visualization of ID Events, but…. Differing approaches to Correlation/Understanding EPIC 2 Differing approaches to Info Gathering & Categorization Shapes- Vector Visualization Visualisation DB/Expert Sys Ontology/KB COTS Sensors Specialized Agents Intrusion Detection Event Exchange Interoperability with coalition partners in sharing IA event data
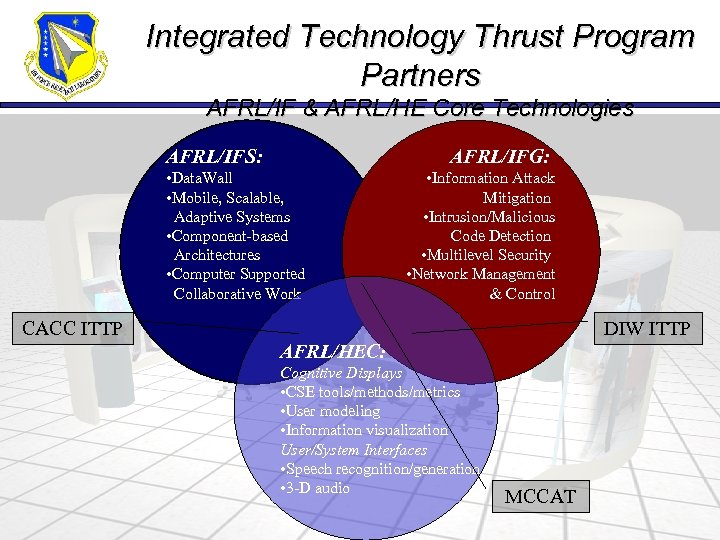 Integrated Technology Thrust Program Partners AFRL/IF & AFRL/HE Core Technologies AFRL/IFS: AFRL/IFG: • Data. Wall • Mobile, Scalable, Adaptive Systems • Component-based Architectures • Computer Supported Collaborative Work • Information Attack Mitigation • Intrusion/Malicious Code Detection • Multilevel Security • Network Management & Control CACC ITTP DIW ITTP AFRL/HEC: Cognitive Displays • CSE tools/methods/metrics • User modeling • Information visualization User/System Interfaces • Speech recognition/generation • 3 -D audio MCCAT
Integrated Technology Thrust Program Partners AFRL/IF & AFRL/HE Core Technologies AFRL/IFS: AFRL/IFG: • Data. Wall • Mobile, Scalable, Adaptive Systems • Component-based Architectures • Computer Supported Collaborative Work • Information Attack Mitigation • Intrusion/Malicious Code Detection • Multilevel Security • Network Management & Control CACC ITTP DIW ITTP AFRL/HEC: Cognitive Displays • CSE tools/methods/metrics • User modeling • Information visualization User/System Interfaces • Speech recognition/generation • 3 -D audio MCCAT
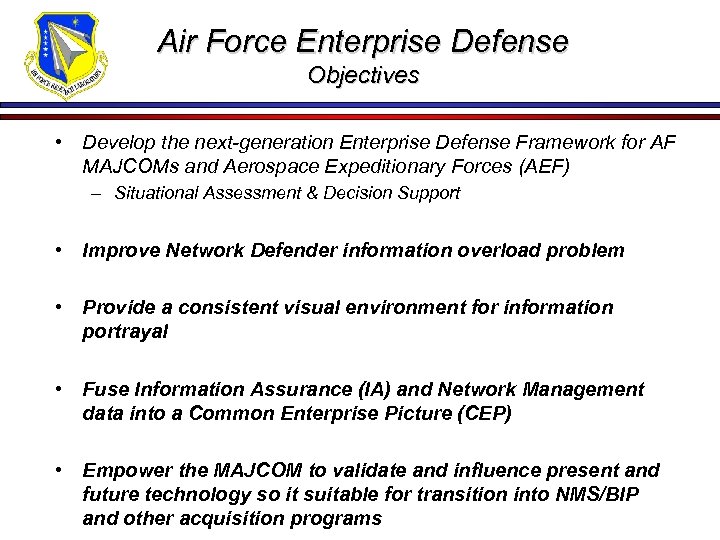 Air Force Enterprise Defense Objectives • Develop the next-generation Enterprise Defense Framework for AF MAJCOMs and Aerospace Expeditionary Forces (AEF) – Situational Assessment & Decision Support • Improve Network Defender information overload problem • Provide a consistent visual environment for information portrayal • Fuse Information Assurance (IA) and Network Management data into a Common Enterprise Picture (CEP) • Empower the MAJCOM to validate and influence present and future technology so it suitable for transition into NMS/BIP and other acquisition programs
Air Force Enterprise Defense Objectives • Develop the next-generation Enterprise Defense Framework for AF MAJCOMs and Aerospace Expeditionary Forces (AEF) – Situational Assessment & Decision Support • Improve Network Defender information overload problem • Provide a consistent visual environment for information portrayal • Fuse Information Assurance (IA) and Network Management data into a Common Enterprise Picture (CEP) • Empower the MAJCOM to validate and influence present and future technology so it suitable for transition into NMS/BIP and other acquisition programs
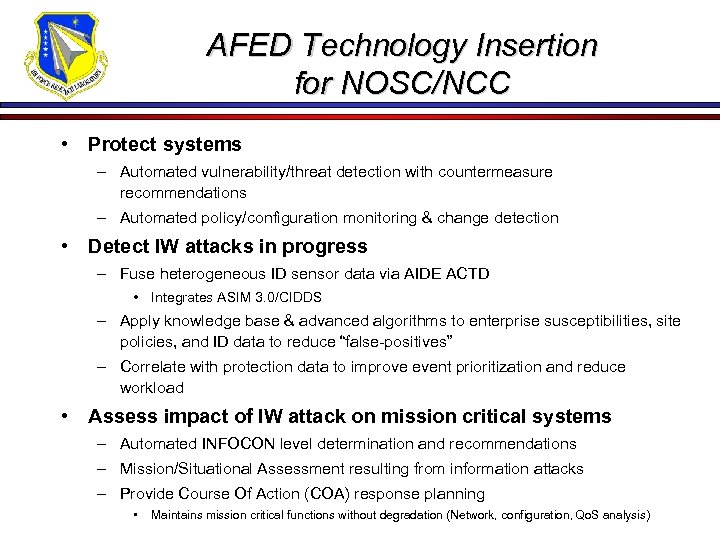 AFED Technology Insertion for NOSC/NCC • Protect systems – Automated vulnerability/threat detection with countermeasure recommendations – Automated policy/configuration monitoring & change detection • Detect IW attacks in progress – Fuse heterogeneous ID sensor data via AIDE ACTD • Integrates ASIM 3. 0/CIDDS – Apply knowledge base & advanced algorithms to enterprise susceptibilities, site policies, and ID data to reduce “false-positives” – Correlate with protection data to improve event prioritization and reduce workload • Assess impact of IW attack on mission critical systems – Automated INFOCON level determination and recommendations – Mission/Situational Assessment resulting from information attacks – Provide Course Of Action (COA) response planning • Maintains mission critical functions without degradation (Network, configuration, Qo. S analysis)
AFED Technology Insertion for NOSC/NCC • Protect systems – Automated vulnerability/threat detection with countermeasure recommendations – Automated policy/configuration monitoring & change detection • Detect IW attacks in progress – Fuse heterogeneous ID sensor data via AIDE ACTD • Integrates ASIM 3. 0/CIDDS – Apply knowledge base & advanced algorithms to enterprise susceptibilities, site policies, and ID data to reduce “false-positives” – Correlate with protection data to improve event prioritization and reduce workload • Assess impact of IW attack on mission critical systems – Automated INFOCON level determination and recommendations – Mission/Situational Assessment resulting from information attacks – Provide Course Of Action (COA) response planning • Maintains mission critical functions without degradation (Network, configuration, Qo. S analysis)
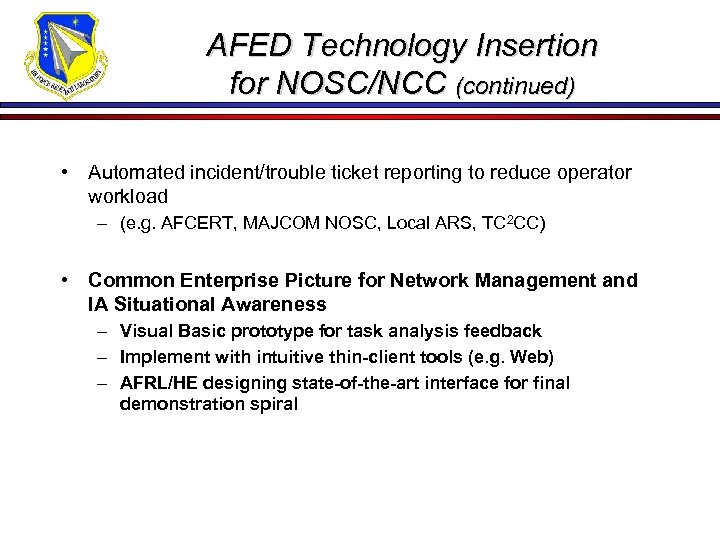 AFED Technology Insertion for NOSC/NCC (continued) • Automated incident/trouble ticket reporting to reduce operator workload – (e. g. AFCERT, MAJCOM NOSC, Local ARS, TC 2 CC) • Common Enterprise Picture for Network Management and IA Situational Awareness – Visual Basic prototype for task analysis feedback – Implement with intuitive thin-client tools (e. g. Web) – AFRL/HE designing state-of-the-art interface for final demonstration spiral
AFED Technology Insertion for NOSC/NCC (continued) • Automated incident/trouble ticket reporting to reduce operator workload – (e. g. AFCERT, MAJCOM NOSC, Local ARS, TC 2 CC) • Common Enterprise Picture for Network Management and IA Situational Awareness – Visual Basic prototype for task analysis feedback – Implement with intuitive thin-client tools (e. g. Web) – AFRL/HE designing state-of-the-art interface for final demonstration spiral
 Funding Issues
Funding Issues
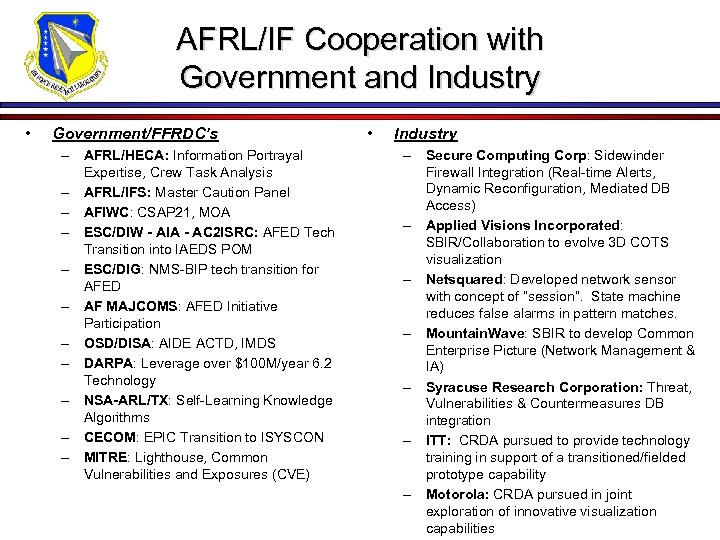 AFRL/IF Cooperation with Government and Industry • Government/FFRDC’s – AFRL/HECA: Information Portrayal Expertise, Crew Task Analysis – AFRL/IFS: Master Caution Panel – AFIWC: CSAP 21, MOA – ESC/DIW - AIA - AC 2 ISRC: AFED Tech Transition into IAEDS POM – ESC/DIG: NMS-BIP tech transition for AFED – AF MAJCOMS: AFED Initiative Participation – OSD/DISA: AIDE ACTD, IMDS – DARPA: Leverage over $100 M/year 6. 2 Technology – NSA-ARL/TX: Self-Learning Knowledge Algorithms – CECOM: EPIC Transition to ISYSCON – MITRE: Lighthouse, Common Vulnerabilities and Exposures (CVE) • Industry – Secure Computing Corp: Sidewinder Firewall Integration (Real-time Alerts, Dynamic Reconfiguration, Mediated DB Access) – Applied Visions Incorporated: SBIR/Collaboration to evolve 3 D COTS visualization – Netsquared: Developed network sensor with concept of “session”. State machine reduces false alarms in pattern matches. – Mountain. Wave: SBIR to develop Common Enterprise Picture (Network Management & IA) – Syracuse Research Corporation: Threat, Vulnerabilities & Countermeasures DB integration – ITT: CRDA pursued to provide technology training in support of a transitioned/fielded prototype capability – Motorola: CRDA pursued in joint exploration of innovative visualization capabilities
AFRL/IF Cooperation with Government and Industry • Government/FFRDC’s – AFRL/HECA: Information Portrayal Expertise, Crew Task Analysis – AFRL/IFS: Master Caution Panel – AFIWC: CSAP 21, MOA – ESC/DIW - AIA - AC 2 ISRC: AFED Tech Transition into IAEDS POM – ESC/DIG: NMS-BIP tech transition for AFED – AF MAJCOMS: AFED Initiative Participation – OSD/DISA: AIDE ACTD, IMDS – DARPA: Leverage over $100 M/year 6. 2 Technology – NSA-ARL/TX: Self-Learning Knowledge Algorithms – CECOM: EPIC Transition to ISYSCON – MITRE: Lighthouse, Common Vulnerabilities and Exposures (CVE) • Industry – Secure Computing Corp: Sidewinder Firewall Integration (Real-time Alerts, Dynamic Reconfiguration, Mediated DB Access) – Applied Visions Incorporated: SBIR/Collaboration to evolve 3 D COTS visualization – Netsquared: Developed network sensor with concept of “session”. State machine reduces false alarms in pattern matches. – Mountain. Wave: SBIR to develop Common Enterprise Picture (Network Management & IA) – Syracuse Research Corporation: Threat, Vulnerabilities & Countermeasures DB integration – ITT: CRDA pursued to provide technology training in support of a transitioned/fielded prototype capability – Motorola: CRDA pursued in joint exploration of innovative visualization capabilities
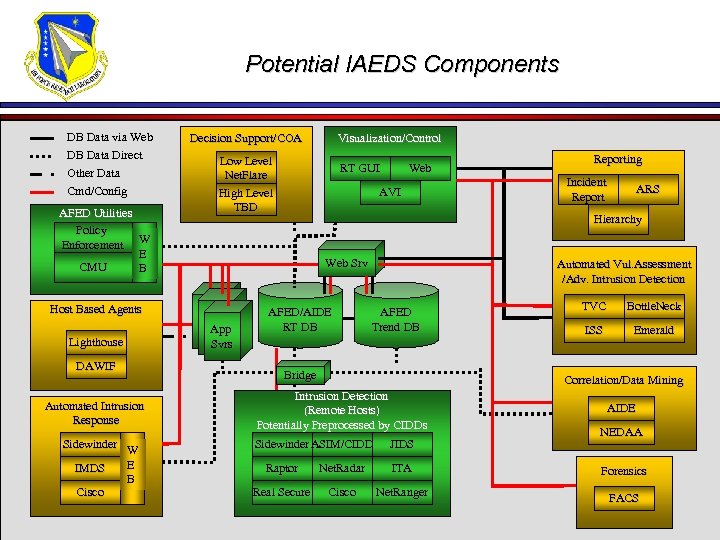 Potential IAEDS Components DB Data via Web DB Data Direct Other Data Cmd/Config AFED Utilities Policy Enforcement W E CMU B Host Based Agents Lighthouse DAWIF Automated Intrusion Response Sidewinder W E IMDS B Cisco Decision Support/COA Visualization/Control Low Level Net. Flare High Level TBD RT GUI Web AVI Incident Report ARS Hierarchy Web Srv App Svrs Reporting AFED/AIDE RT DB Automated Vul. Assessment /Adv. Intrusion Detection Adv. AFED Trend DB Bridge TVC Bottle. Neck ISS Emerald Correlation/Data Mining Intrusion Detection (Remote Hosts) Potentially Preprocessed by CIDDs Sidewinder ASIM/CIDD JIDS AIDE NEDAA Raptor Net. Radar ITA Forensics Real Secure Cisco Net. Ranger FACS
Potential IAEDS Components DB Data via Web DB Data Direct Other Data Cmd/Config AFED Utilities Policy Enforcement W E CMU B Host Based Agents Lighthouse DAWIF Automated Intrusion Response Sidewinder W E IMDS B Cisco Decision Support/COA Visualization/Control Low Level Net. Flare High Level TBD RT GUI Web AVI Incident Report ARS Hierarchy Web Srv App Svrs Reporting AFED/AIDE RT DB Automated Vul. Assessment /Adv. Intrusion Detection Adv. AFED Trend DB Bridge TVC Bottle. Neck ISS Emerald Correlation/Data Mining Intrusion Detection (Remote Hosts) Potentially Preprocessed by CIDDs Sidewinder ASIM/CIDD JIDS AIDE NEDAA Raptor Net. Radar ITA Forensics Real Secure Cisco Net. Ranger FACS
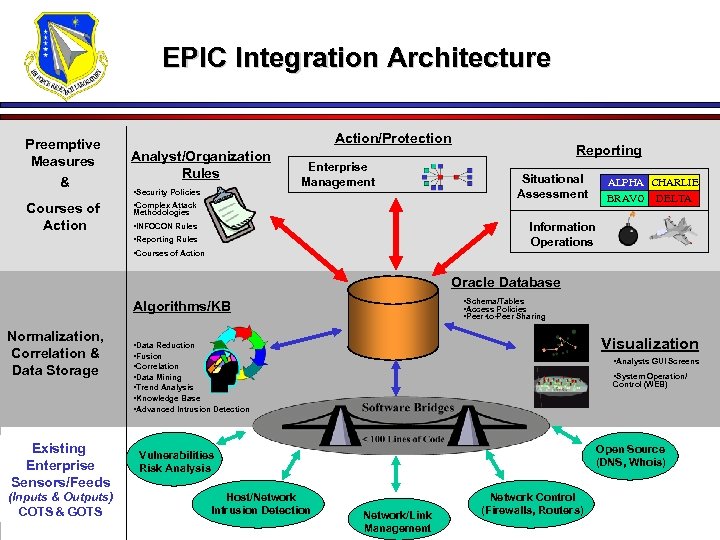 EPIC Integration Architecture Preemptive Measures & Courses of Action/Protection Analyst/Organization Rules • Security Policies Enterprise Management Reporting Situational Assessment • Complex Attack ALPHA CHARLIE BRAVO DELTA Methodologies Information Operations • INFOCON Rules • Reporting Rules • Courses of Action Oracle Database • Schema/Tables • Access Policies • Peer-to-Peer Sharing Algorithms/KB Normalization, Correlation & Data Storage Existing Enterprise Sensors/Feeds (Inputs & Outputs) COTS & GOTS Visualization • Data Reduction • Fusion • Correlation • Data Mining • Trend Analysis • Knowledge Base • Advanced Intrusion Detection • Analysts GUI Screens • System Operation/ Control (WEB) Open Source (DNS, Whois) Vulnerabilities Risk Analysis Host/Network Intrusion Detection Network/Link Management Network Control (Firewalls, Routers)
EPIC Integration Architecture Preemptive Measures & Courses of Action/Protection Analyst/Organization Rules • Security Policies Enterprise Management Reporting Situational Assessment • Complex Attack ALPHA CHARLIE BRAVO DELTA Methodologies Information Operations • INFOCON Rules • Reporting Rules • Courses of Action Oracle Database • Schema/Tables • Access Policies • Peer-to-Peer Sharing Algorithms/KB Normalization, Correlation & Data Storage Existing Enterprise Sensors/Feeds (Inputs & Outputs) COTS & GOTS Visualization • Data Reduction • Fusion • Correlation • Data Mining • Trend Analysis • Knowledge Base • Advanced Intrusion Detection • Analysts GUI Screens • System Operation/ Control (WEB) Open Source (DNS, Whois) Vulnerabilities Risk Analysis Host/Network Intrusion Detection Network/Link Management Network Control (Firewalls, Routers)
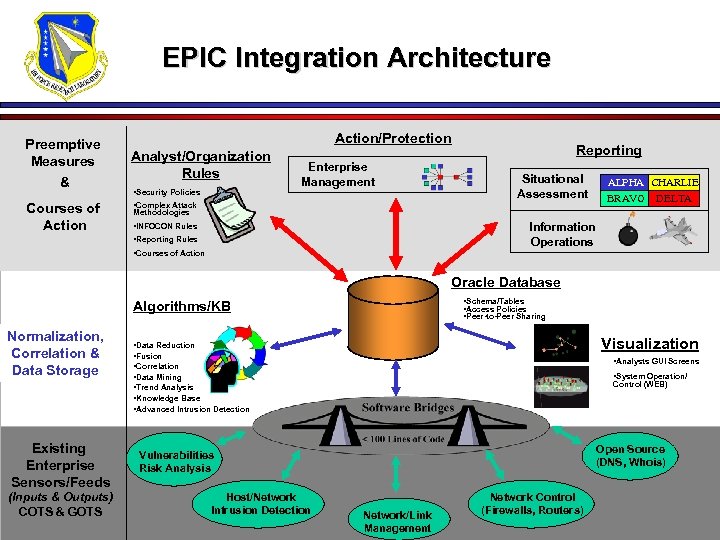 EPIC Integration Architecture Preemptive Measures & Courses of Action/Protection Analyst/Organization Rules • Security Policies Enterprise Management Reporting Situational Assessment • Complex Attack ALPHA CHARLIE BRAVO DELTA Methodologies Information Operations • INFOCON Rules • Reporting Rules • Courses of Action Oracle Database • Schema/Tables • Access Policies • Peer-to-Peer Sharing Algorithms/KB Normalization, Correlation & Data Storage Existing Enterprise Sensors/Feeds (Inputs & Outputs) COTS & GOTS Visualization • Data Reduction • Fusion • Correlation • Data Mining • Trend Analysis • Knowledge Base • Advanced Intrusion Detection • Analysts GUI Screens • System Operation/ Control (WEB) Open Source (DNS, Whois) Vulnerabilities Risk Analysis Host/Network Intrusion Detection Network/Link Management Network Control (Firewalls, Routers)
EPIC Integration Architecture Preemptive Measures & Courses of Action/Protection Analyst/Organization Rules • Security Policies Enterprise Management Reporting Situational Assessment • Complex Attack ALPHA CHARLIE BRAVO DELTA Methodologies Information Operations • INFOCON Rules • Reporting Rules • Courses of Action Oracle Database • Schema/Tables • Access Policies • Peer-to-Peer Sharing Algorithms/KB Normalization, Correlation & Data Storage Existing Enterprise Sensors/Feeds (Inputs & Outputs) COTS & GOTS Visualization • Data Reduction • Fusion • Correlation • Data Mining • Trend Analysis • Knowledge Base • Advanced Intrusion Detection • Analysts GUI Screens • System Operation/ Control (WEB) Open Source (DNS, Whois) Vulnerabilities Risk Analysis Host/Network Intrusion Detection Network/Link Management Network Control (Firewalls, Routers)
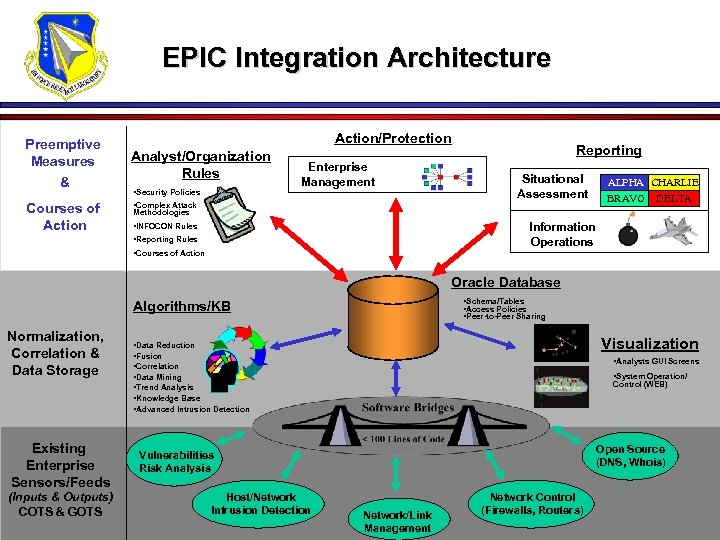 EPIC Integration Architecture Preemptive Measures & Courses of Action/Protection Analyst/Organization Rules • Security Policies Enterprise Management Reporting Situational Assessment • Complex Attack ALPHA CHARLIE BRAVO DELTA Methodologies Information Operations • INFOCON Rules • Reporting Rules • Courses of Action Oracle Database • Schema/Tables • Access Policies • Peer-to-Peer Sharing Algorithms/KB Normalization, Correlation & Data Storage Existing Enterprise Sensors/Feeds (Inputs & Outputs) COTS & GOTS Visualization • Data Reduction • Fusion • Correlation • Data Mining • Trend Analysis • Knowledge Base • Advanced Intrusion Detection • Analysts GUI Screens • System Operation/ Control (WEB) Open Source (DNS, Whois) Vulnerabilities Risk Analysis Host/Network Intrusion Detection Network/Link Management Network Control (Firewalls, Routers)
EPIC Integration Architecture Preemptive Measures & Courses of Action/Protection Analyst/Organization Rules • Security Policies Enterprise Management Reporting Situational Assessment • Complex Attack ALPHA CHARLIE BRAVO DELTA Methodologies Information Operations • INFOCON Rules • Reporting Rules • Courses of Action Oracle Database • Schema/Tables • Access Policies • Peer-to-Peer Sharing Algorithms/KB Normalization, Correlation & Data Storage Existing Enterprise Sensors/Feeds (Inputs & Outputs) COTS & GOTS Visualization • Data Reduction • Fusion • Correlation • Data Mining • Trend Analysis • Knowledge Base • Advanced Intrusion Detection • Analysts GUI Screens • System Operation/ Control (WEB) Open Source (DNS, Whois) Vulnerabilities Risk Analysis Host/Network Intrusion Detection Network/Link Management Network Control (Firewalls, Routers)
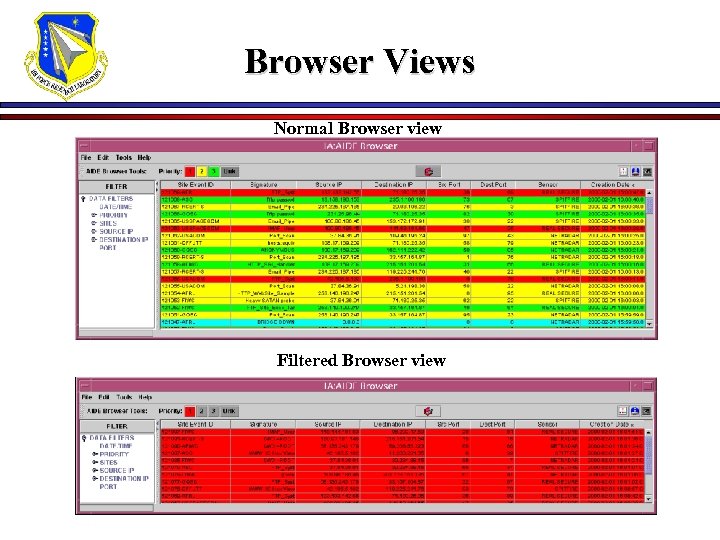 Browser Views Normal Browser view Filtered Browser view
Browser Views Normal Browser view Filtered Browser view
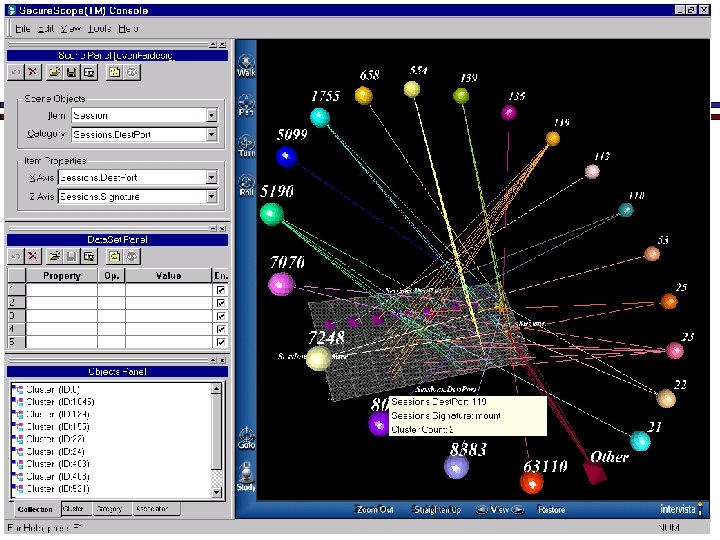
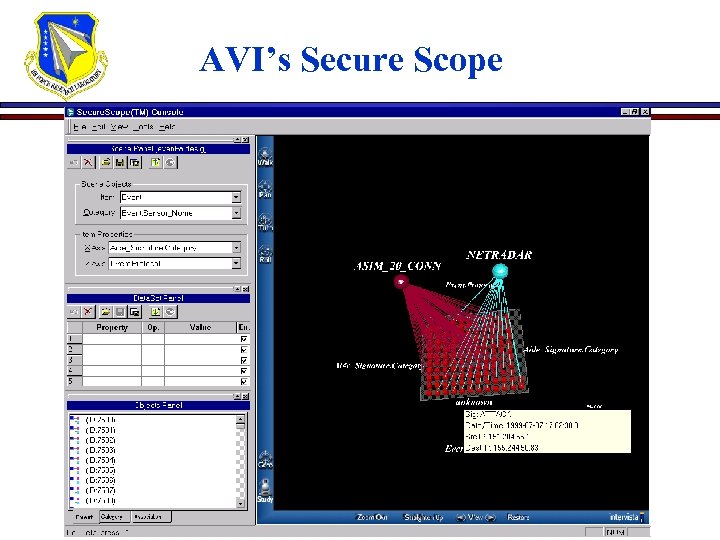 AVI’s Secure Scope
AVI’s Secure Scope
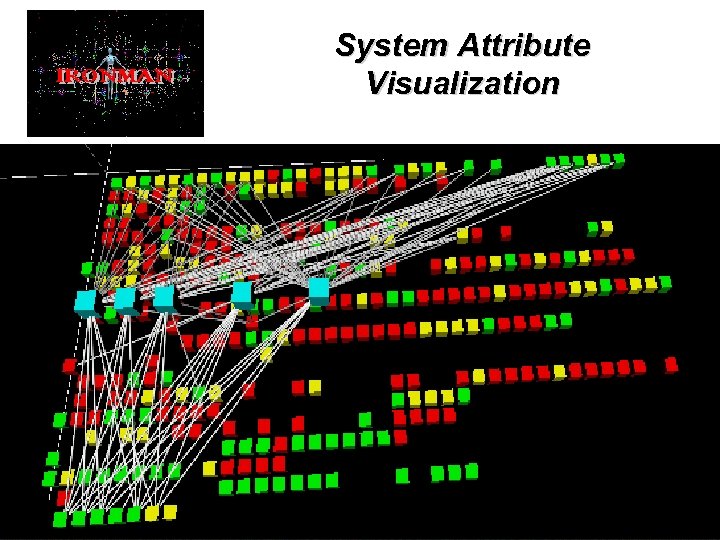 System Attribute Visualization • e. g. Mapping Network Components to Vulnerabilities
System Attribute Visualization • e. g. Mapping Network Components to Vulnerabilities
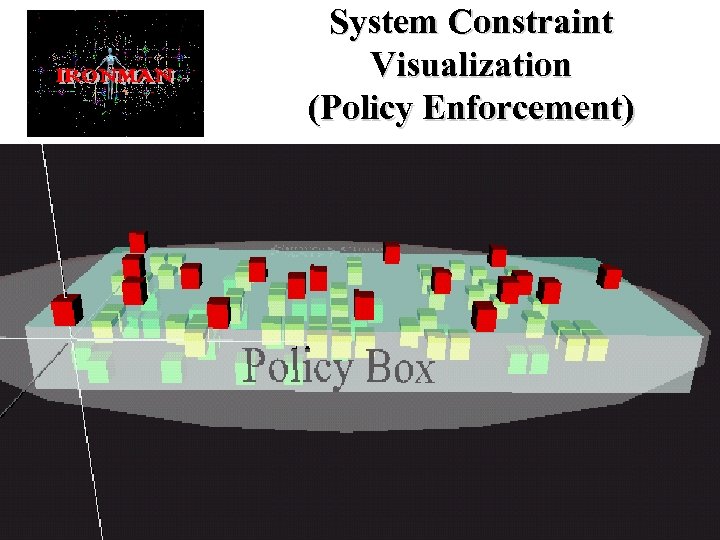 System Constraint Visualization (Policy Enforcement) • e. g. Policy Violations by Multiple Components • VRML 2. 0 with behaviours and external interfaces
System Constraint Visualization (Policy Enforcement) • e. g. Policy Violations by Multiple Components • VRML 2. 0 with behaviours and external interfaces
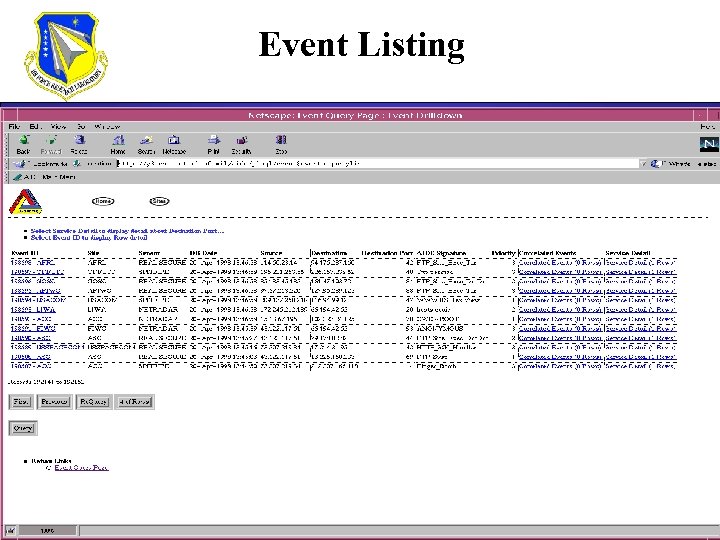 Event Listing
Event Listing
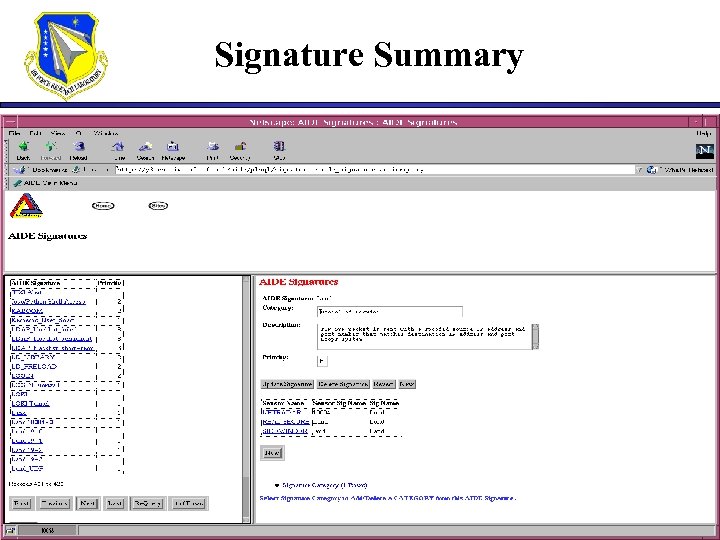 Signature Summary
Signature Summary
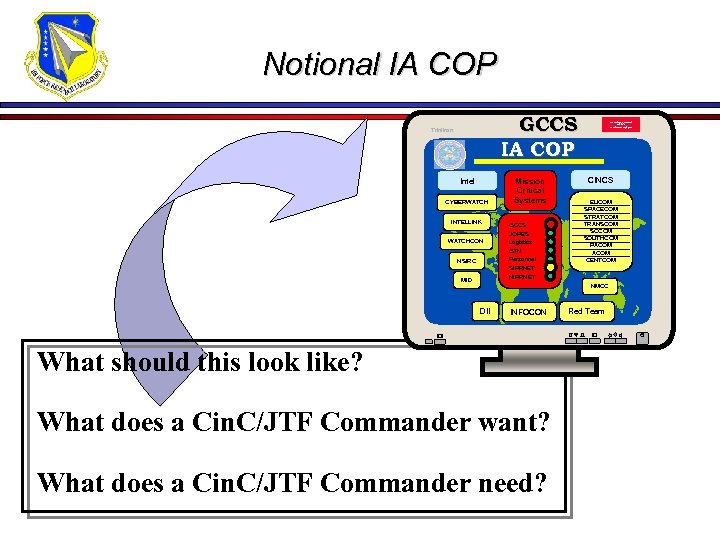 Notional IA COP GCCS IA COP Trinitron Intel CYBERWATCH INTELLINK WATCHCON NSIRC MID Mission Critical Systems GCCS JOPES Logistics GTN Personnel SIPRNET NIPRNET This medium is classified SECRET US Government property CINCS EUCOM SPACECOM STRATCOM TRANSCOM SOUTHCOM PACOM CENTCOM NMCC DII INFOCON What should this look like? What does a Cin. C/JTF Commander want? What does a Cin. C/JTF Commander need? Red Team
Notional IA COP GCCS IA COP Trinitron Intel CYBERWATCH INTELLINK WATCHCON NSIRC MID Mission Critical Systems GCCS JOPES Logistics GTN Personnel SIPRNET NIPRNET This medium is classified SECRET US Government property CINCS EUCOM SPACECOM STRATCOM TRANSCOM SOUTHCOM PACOM CENTCOM NMCC DII INFOCON What should this look like? What does a Cin. C/JTF Commander want? What does a Cin. C/JTF Commander need? Red Team
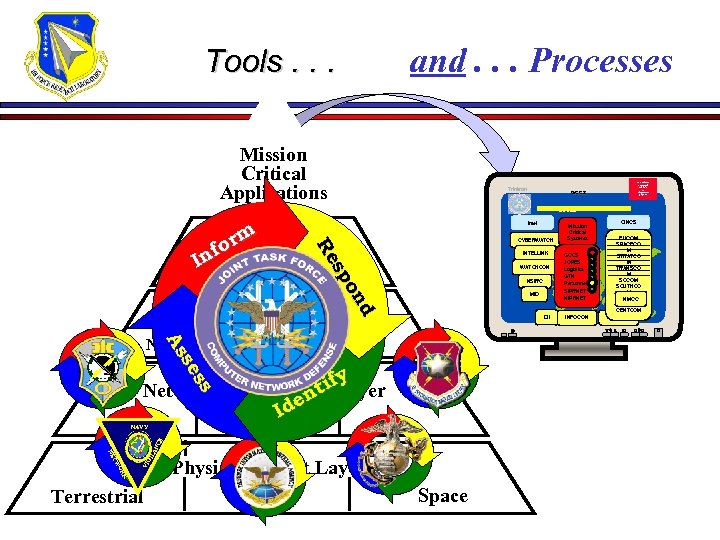 Tools. . . and. . . Processes Mission Critical Applications Trinitron This medium is classified SECRET US Government property GCCS IA COP Intel m or f Net Services Layer In CYBERWATCH d d on on sp sp Re Re INTELLINK WATCHCON NSIRC MID Sensor Grid Layer ss ss se se As As Non-Intrusive DII Intrusive y tif Network (IP Routing) Layer n de I SIPRNET Other NIPRNET TW NE K OR VI GI LA NC E NAVY Terrestrial Physical/Circuit Layer RF Space Mission Critical Systems GCCS JOPES Logistics GTN Personnel SIPRNET NIPRNET INFOCON CINCS EUCOM SPACECO M STRATCO M TRANSCO M SOCOM SOUTHCO M PACOM NMCC ACOM CENTCOM Red Team
Tools. . . and. . . Processes Mission Critical Applications Trinitron This medium is classified SECRET US Government property GCCS IA COP Intel m or f Net Services Layer In CYBERWATCH d d on on sp sp Re Re INTELLINK WATCHCON NSIRC MID Sensor Grid Layer ss ss se se As As Non-Intrusive DII Intrusive y tif Network (IP Routing) Layer n de I SIPRNET Other NIPRNET TW NE K OR VI GI LA NC E NAVY Terrestrial Physical/Circuit Layer RF Space Mission Critical Systems GCCS JOPES Logistics GTN Personnel SIPRNET NIPRNET INFOCON CINCS EUCOM SPACECO M STRATCO M TRANSCO M SOCOM SOUTHCO M PACOM NMCC ACOM CENTCOM Red Team
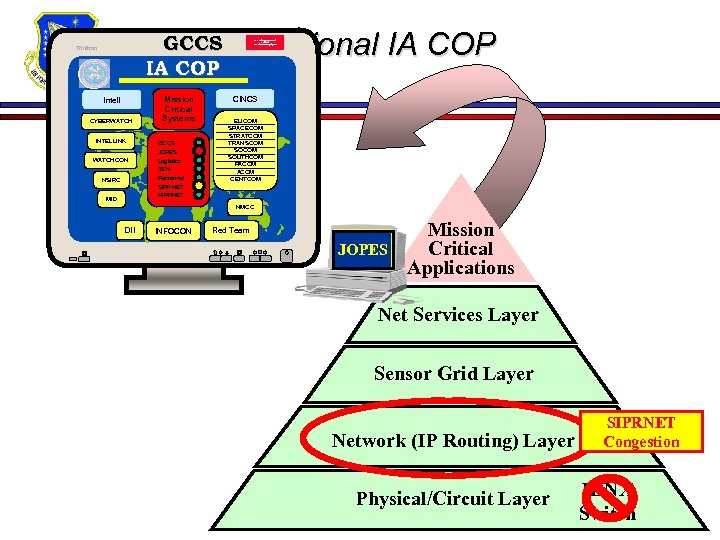 Notional IA COP GCCS IA COP Trinitron Intell CYBERWATCH INTELLINK WATCHCON NSIRC MID Mission Critical Systems GCCS JOPES Logistics GTN Personnel SIPRNET NIPRNET This medium is classified SECRET US Government property CINCS EUCOM SPACECOM STRATCOM TRANSCOM SOUTHCOM PACOM CENTCOM NMCC DII INFOCON Red Team JOPES Mission Critical Applications Net Services Layer Sensor Grid Layer Network (IP Routing) Layer Physical/Circuit Layer SIPRNET Congestion IDNX Switch
Notional IA COP GCCS IA COP Trinitron Intell CYBERWATCH INTELLINK WATCHCON NSIRC MID Mission Critical Systems GCCS JOPES Logistics GTN Personnel SIPRNET NIPRNET This medium is classified SECRET US Government property CINCS EUCOM SPACECOM STRATCOM TRANSCOM SOUTHCOM PACOM CENTCOM NMCC DII INFOCON Red Team JOPES Mission Critical Applications Net Services Layer Sensor Grid Layer Network (IP Routing) Layer Physical/Circuit Layer SIPRNET Congestion IDNX Switch
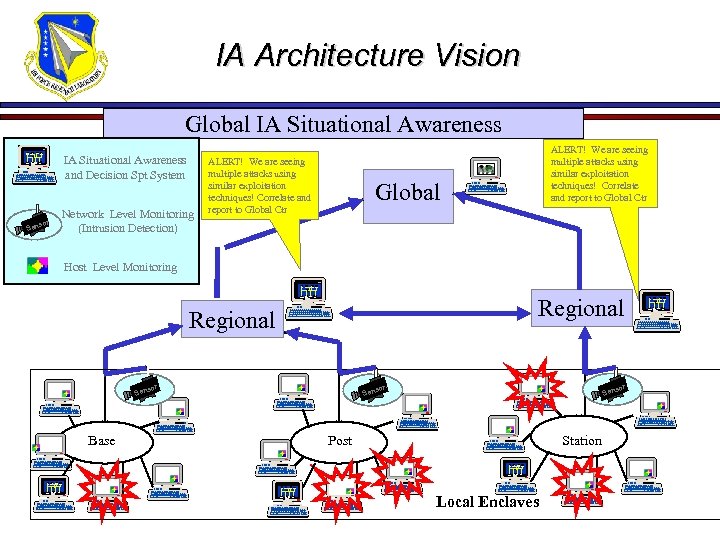 IA Architecture Vision Ensures consistent technology and reporting Global IA Situational Awareness Consistent Thresholds IA Situational Awareness and Decision Spt System sor Sen Network Level Monitoring (Intrusion Detection) ALERT! We are seeing multiple attacks using similar exploitation techniques! Correlate and report to Global Ctr Global Host Level Monitoring Regional sor Sen Base Sen Post Station Local Enclaves sor
IA Architecture Vision Ensures consistent technology and reporting Global IA Situational Awareness Consistent Thresholds IA Situational Awareness and Decision Spt System sor Sen Network Level Monitoring (Intrusion Detection) ALERT! We are seeing multiple attacks using similar exploitation techniques! Correlate and report to Global Ctr Global Host Level Monitoring Regional sor Sen Base Sen Post Station Local Enclaves sor
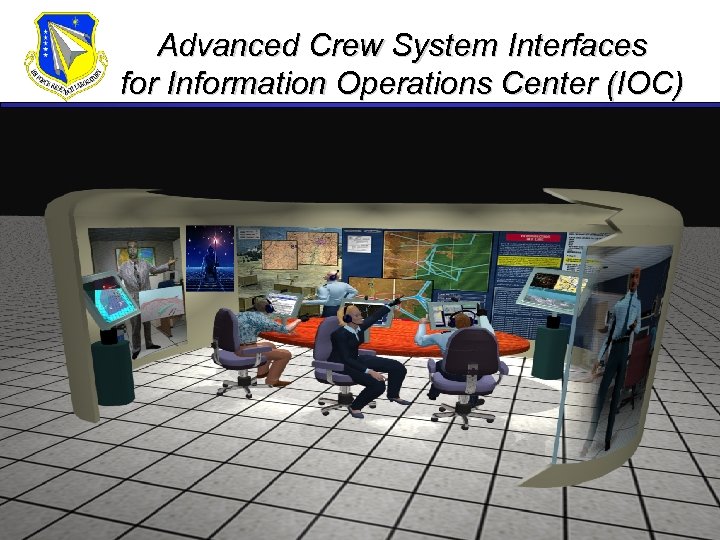 Advanced Crew System Interfaces for Information Operations Center (IOC)
Advanced Crew System Interfaces for Information Operations Center (IOC)
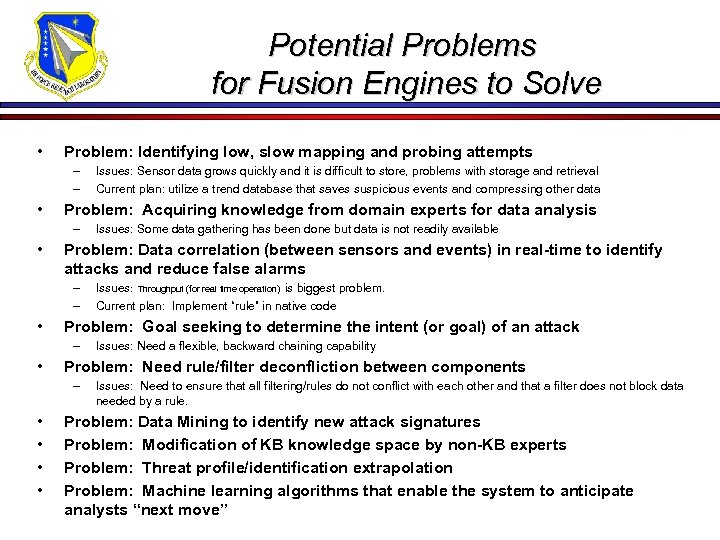 Potential Problems for Fusion Engines to Solve • Problem: Identifying low, slow mapping and probing attempts – – • Problem: Acquiring knowledge from domain experts for data analysis – • Issues: Need a flexible, backward chaining capability Problem: Need rule/filter deconfliction between components – • • Issues: Throughput (for real time operation) is biggest problem. Current plan: Implement “rule” in native code Problem: Goal seeking to determine the intent (or goal) of an attack – • Issues: Some data gathering has been done but data is not readily available Problem: Data correlation (between sensors and events) in real-time to identify attacks and reduce false alarms – – • Issues: Sensor data grows quickly and it is difficult to store, problems with storage and retrieval Current plan: utilize a trend database that saves suspicious events and compressing other data Issues: Need to ensure that all filtering/rules do not conflict with each other and that a filter does not block data needed by a rule. Problem: Data Mining to identify new attack signatures Problem: Modification of KB knowledge space by non-KB experts Problem: Threat profile/identification extrapolation Problem: Machine learning algorithms that enable the system to anticipate analysts “next move”
Potential Problems for Fusion Engines to Solve • Problem: Identifying low, slow mapping and probing attempts – – • Problem: Acquiring knowledge from domain experts for data analysis – • Issues: Need a flexible, backward chaining capability Problem: Need rule/filter deconfliction between components – • • Issues: Throughput (for real time operation) is biggest problem. Current plan: Implement “rule” in native code Problem: Goal seeking to determine the intent (or goal) of an attack – • Issues: Some data gathering has been done but data is not readily available Problem: Data correlation (between sensors and events) in real-time to identify attacks and reduce false alarms – – • Issues: Sensor data grows quickly and it is difficult to store, problems with storage and retrieval Current plan: utilize a trend database that saves suspicious events and compressing other data Issues: Need to ensure that all filtering/rules do not conflict with each other and that a filter does not block data needed by a rule. Problem: Data Mining to identify new attack signatures Problem: Modification of KB knowledge space by non-KB experts Problem: Threat profile/identification extrapolation Problem: Machine learning algorithms that enable the system to anticipate analysts “next move”
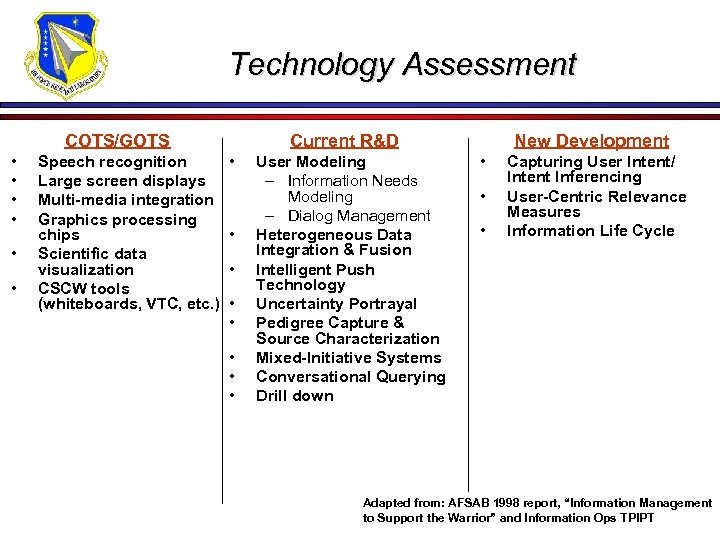 Technology Assessment COTS/GOTS • • • Speech recognition Large screen displays Multi-media integration Graphics processing chips Scientific data visualization CSCW tools (whiteboards, VTC, etc. ) Current R&D • • User Modeling – Information Needs Modeling – Dialog Management Heterogeneous Data Integration & Fusion Intelligent Push Technology Uncertainty Portrayal Pedigree Capture & Source Characterization Mixed-Initiative Systems Conversational Querying Drill down New Development • • • Capturing User Intent/ Intent Inferencing User-Centric Relevance Measures Information Life Cycle Adapted from: AFSAB 1998 report, “Information Management to Support the Warrior” and Information Ops TPIPT
Technology Assessment COTS/GOTS • • • Speech recognition Large screen displays Multi-media integration Graphics processing chips Scientific data visualization CSCW tools (whiteboards, VTC, etc. ) Current R&D • • User Modeling – Information Needs Modeling – Dialog Management Heterogeneous Data Integration & Fusion Intelligent Push Technology Uncertainty Portrayal Pedigree Capture & Source Characterization Mixed-Initiative Systems Conversational Querying Drill down New Development • • • Capturing User Intent/ Intent Inferencing User-Centric Relevance Measures Information Life Cycle Adapted from: AFSAB 1998 report, “Information Management to Support the Warrior” and Information Ops TPIPT
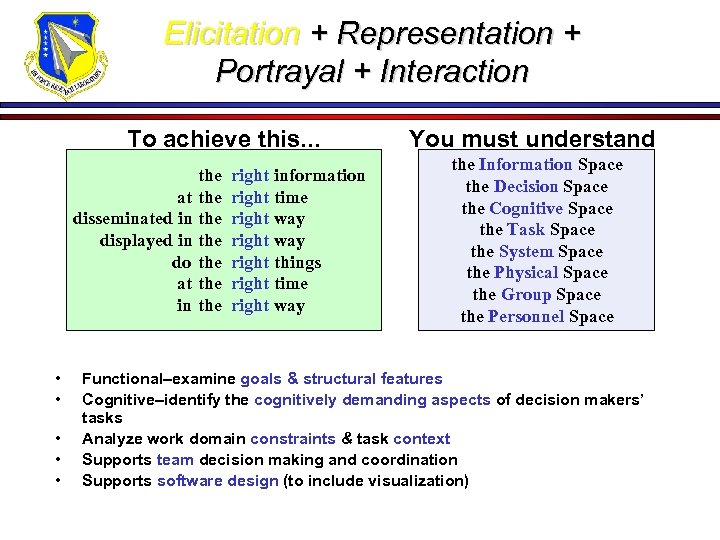 Elicitation + Representation + Portrayal + Interaction To achieve this. . . at disseminated in displayed in do at in • • • the the right information right time right way right things right time right way You must understand the Information Space the Decision Space the Cognitive Space the Task Space the System Space the Physical Space the Group Space the Personnel Space Functional–examine goals & structural features Cognitive–identify the cognitively demanding aspects of decision makers’ tasks Analyze work domain constraints & task context Supports team decision making and coordination Supports software design (to include visualization)
Elicitation + Representation + Portrayal + Interaction To achieve this. . . at disseminated in displayed in do at in • • • the the right information right time right way right things right time right way You must understand the Information Space the Decision Space the Cognitive Space the Task Space the System Space the Physical Space the Group Space the Personnel Space Functional–examine goals & structural features Cognitive–identify the cognitively demanding aspects of decision makers’ tasks Analyze work domain constraints & task context Supports team decision making and coordination Supports software design (to include visualization)
 Machine Learning Algorithms for Auto-Refining Visualisations • Dynamic IO Field – ROE, CONOPS • Rapidly Evolving Technology – Standards, Processing Power • Knowledge elicitation can fail to improve visualization – Users tend to think only in terms of current process/technology – Cannot specify what they want until they see it • Balance expeditious acquisition with due diligence in knowledge elicitation • The “My Yahoo”(. com) concept – Custom visualizations – Customizable visualizations • Self-arranging menus & drill-downs based on analyst use
Machine Learning Algorithms for Auto-Refining Visualisations • Dynamic IO Field – ROE, CONOPS • Rapidly Evolving Technology – Standards, Processing Power • Knowledge elicitation can fail to improve visualization – Users tend to think only in terms of current process/technology – Cannot specify what they want until they see it • Balance expeditious acquisition with due diligence in knowledge elicitation • The “My Yahoo”(. com) concept – Custom visualizations – Customizable visualizations • Self-arranging menus & drill-downs based on analyst use


