77e1fa76f11a32ffaa5030b5dba5d6fa.ppt
- Количество слайдов: 36
 Moving Security Enforcement into the Heart of the Network Peter Benson CEO Security-Assessment. com October, 2005 Copyright Security-Assessment. com, Qualys Inc, 2005
Moving Security Enforcement into the Heart of the Network Peter Benson CEO Security-Assessment. com October, 2005 Copyright Security-Assessment. com, Qualys Inc, 2005
 Agenda • Evolution of Threats • Why Network Access Control Matters • The Laws of Vulnerabilities • Network Access Control Architectures • Summary and Action Copyright Security-Assessment. com 2005
Agenda • Evolution of Threats • Why Network Access Control Matters • The Laws of Vulnerabilities • Network Access Control Architectures • Summary and Action Copyright Security-Assessment. com 2005
 Security Trend Indicators • • Malicious Code (↑) Vulnerabilities (↑) Spam and Spyware (↑) Phishing and Identity Theft (↑) …. and • Time to Exploitation (↓) Copyright Security-Assessment. com 2005
Security Trend Indicators • • Malicious Code (↑) Vulnerabilities (↑) Spam and Spyware (↑) Phishing and Identity Theft (↑) …. and • Time to Exploitation (↓) Copyright Security-Assessment. com 2005
 Where are the issues ? • A Multitude of insecure Protocols and Services – telnet, ftp, snmp • Known default settings – Passwords, SNMP community strings • System Design Errors – Setup and Access control errors • Software Implementation Flaws – Input validation, lack of sanity checks • User Triggered Issues – Email and Browser related Copyright Security-Assessment. com 2005
Where are the issues ? • A Multitude of insecure Protocols and Services – telnet, ftp, snmp • Known default settings – Passwords, SNMP community strings • System Design Errors – Setup and Access control errors • Software Implementation Flaws – Input validation, lack of sanity checks • User Triggered Issues – Email and Browser related Copyright Security-Assessment. com 2005
 First Generation Threats • • Spreading mostly via email, file-sharing Human Action Required Virus-type spreading / No vulnerabilities Examples: Melissa Macro Virus, Love. Letter VBScript Worm • Replicates to other recipients • Discovery/Removal: Antivirus Copyright Security-Assessment. com 2005
First Generation Threats • • Spreading mostly via email, file-sharing Human Action Required Virus-type spreading / No vulnerabilities Examples: Melissa Macro Virus, Love. Letter VBScript Worm • Replicates to other recipients • Discovery/Removal: Antivirus Copyright Security-Assessment. com 2005
 Second Generation Threats • Active worms • Leveraging known vulnerabilities • Low level of sophistication in spreading strategy (i. e. randomly) • Non Destructive Payloads • Remedy: Identify and Fix Vulnerabilities Copyright Security-Assessment. com 2005
Second Generation Threats • Active worms • Leveraging known vulnerabilities • Low level of sophistication in spreading strategy (i. e. randomly) • Non Destructive Payloads • Remedy: Identify and Fix Vulnerabilities Copyright Security-Assessment. com 2005
 Third Generation Threats • Automated Attacks Leveraging Known and Unknown Vulnerabilities • Collaboration of Social Engineering and Automated Attacks • Multiple Attack Vectors – Email, Web, IM, Vulnerabilities, … • Active Payloads • Remedy: Security Enforcement / Network Access Control Copyright Security-Assessment. com 2005
Third Generation Threats • Automated Attacks Leveraging Known and Unknown Vulnerabilities • Collaboration of Social Engineering and Automated Attacks • Multiple Attack Vectors – Email, Web, IM, Vulnerabilities, … • Active Payloads • Remedy: Security Enforcement / Network Access Control Copyright Security-Assessment. com 2005
 Evolution of Network Access Control • Today: – Static network access – Every device is permitted – Infected or unhealthy devices are frequently the root of an outbreak • Tomorrow: – Dynamic network access based on policies – Screening devices before granting access – Infected or unhealthy devices should be treated separately Copyright Security-Assessment. com 2005
Evolution of Network Access Control • Today: – Static network access – Every device is permitted – Infected or unhealthy devices are frequently the root of an outbreak • Tomorrow: – Dynamic network access based on policies – Screening devices before granting access – Infected or unhealthy devices should be treated separately Copyright Security-Assessment. com 2005
 “Anyone can build a stop sign – or even a traffic light – but it takes a different mind-set entirely to conceive of a city-wide traffic control system. ” Bruce Schneier – Beyond Fear Copyright Security-Assessment. com 2005
“Anyone can build a stop sign – or even a traffic light – but it takes a different mind-set entirely to conceive of a city-wide traffic control system. ” Bruce Schneier – Beyond Fear Copyright Security-Assessment. com 2005
 Building Blocks of Network Access Control • • Assessment of Endpoint Security Decision making based on policy compliance Admission Enforcement at Network infrastructure Quarantining/Remediation of unhealthy devices Copyright Security-Assessment. com 2005
Building Blocks of Network Access Control • • Assessment of Endpoint Security Decision making based on policy compliance Admission Enforcement at Network infrastructure Quarantining/Remediation of unhealthy devices Copyright Security-Assessment. com 2005
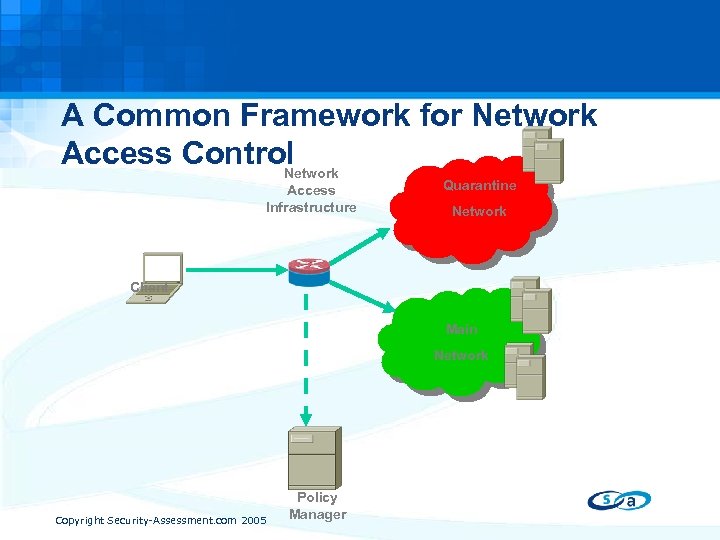 A Common Framework for Network Access Control Network Access Infrastructure Quarantine Network Client Main Network Copyright Security-Assessment. com 2005 Policy Manager
A Common Framework for Network Access Control Network Access Infrastructure Quarantine Network Client Main Network Copyright Security-Assessment. com 2005 Policy Manager
 Why Network Access Control Matters • Objective: Understanding prevalence of critical vulnerabilities over time in real world • Timeframe: January 2002 - Ongoing • Data Source: – 70% Global Enterprise networks – 30 % Random trials • Methodology: Automatic Data collection with statistical data only – no possible correlation to individual user or systems Copyright Security-Assessment. com 2005
Why Network Access Control Matters • Objective: Understanding prevalence of critical vulnerabilities over time in real world • Timeframe: January 2002 - Ongoing • Data Source: – 70% Global Enterprise networks – 30 % Random trials • Methodology: Automatic Data collection with statistical data only – no possible correlation to individual user or systems Copyright Security-Assessment. com 2005
 Raw Results • Largest collection of global real-world vulnerability data: – – 14, 818, 000 IP-Scans since begin 2002 2, 275 out of 3, 374 unique vulnerabilities detected in the real world – – 3, 834, 000 total critical* vulnerabilities found 1, 031 out of 1, 504 unique critical vulnerabilities detected in the real world • Analysis Performed: – – – Identifying Window of Exposure Lifespan of Critical Vulnerabilities Resolution Response Trend over Time Vulnerability Prevalence Providing an attacker the ability to gain full control of the system, and/or leakage of highly sensitive information. For example, vulnerabilities may enable full read and/or write access to files, remote execution of commands, and the presence of backdoors. * Copyright Security-Assessment. com 2005
Raw Results • Largest collection of global real-world vulnerability data: – – 14, 818, 000 IP-Scans since begin 2002 2, 275 out of 3, 374 unique vulnerabilities detected in the real world – – 3, 834, 000 total critical* vulnerabilities found 1, 031 out of 1, 504 unique critical vulnerabilities detected in the real world • Analysis Performed: – – – Identifying Window of Exposure Lifespan of Critical Vulnerabilities Resolution Response Trend over Time Vulnerability Prevalence Providing an attacker the ability to gain full control of the system, and/or leakage of highly sensitive information. For example, vulnerabilities may enable full read and/or write access to files, remote execution of commands, and the presence of backdoors. * Copyright Security-Assessment. com 2005
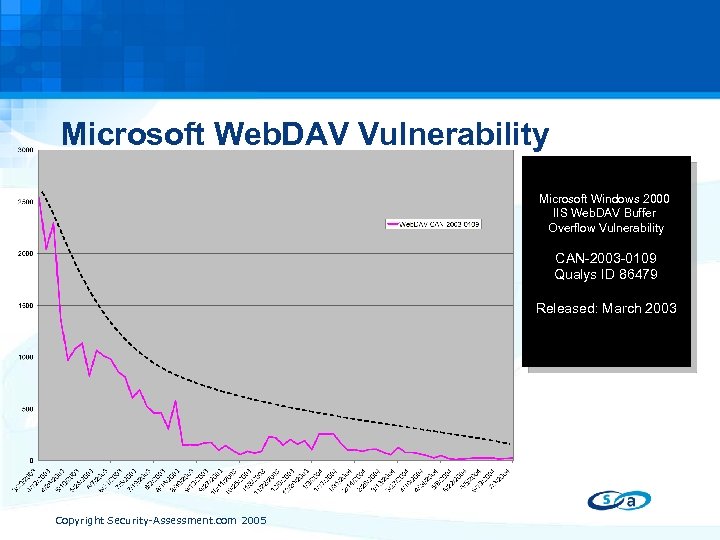 Microsoft Web. DAV Vulnerability Microsoft Windows 2000 IIS Web. DAV Buffer Overflow Vulnerability CAN-2003 -0109 Qualys ID 86479 Released: March 2003 Copyright Security-Assessment. com 2005
Microsoft Web. DAV Vulnerability Microsoft Windows 2000 IIS Web. DAV Buffer Overflow Vulnerability CAN-2003 -0109 Qualys ID 86479 Released: March 2003 Copyright Security-Assessment. com 2005
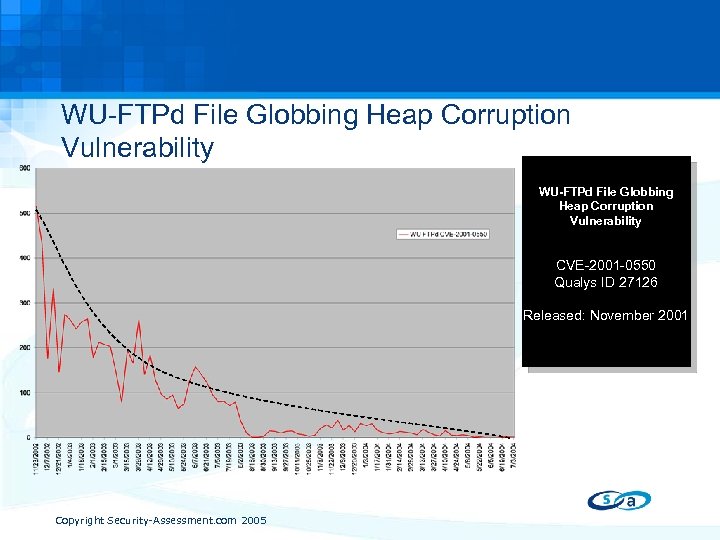 WU-FTPd File Globbing Heap Corruption Vulnerability CVE-2001 -0550 Qualys ID 27126 Released: November 2001 Copyright Security-Assessment. com 2005
WU-FTPd File Globbing Heap Corruption Vulnerability CVE-2001 -0550 Qualys ID 27126 Released: November 2001 Copyright Security-Assessment. com 2005
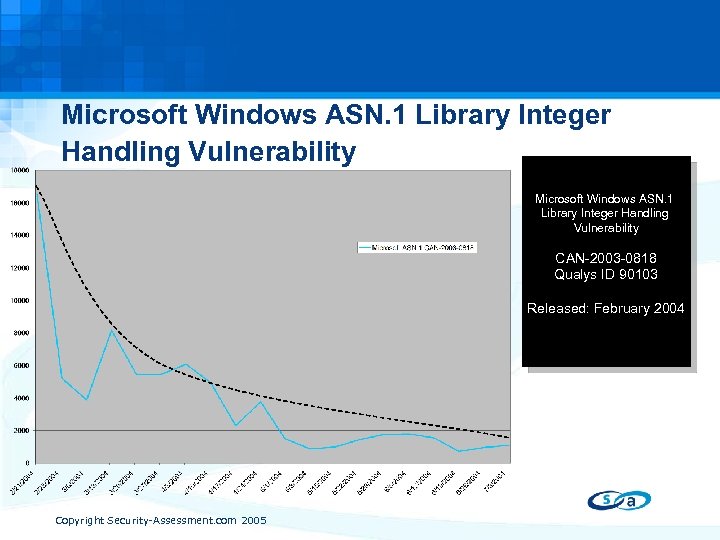 Microsoft Windows ASN. 1 Library Integer Handling Vulnerability CAN-2003 -0818 Qualys ID 90103 Released: February 2004 Copyright Security-Assessment. com 2005
Microsoft Windows ASN. 1 Library Integer Handling Vulnerability CAN-2003 -0818 Qualys ID 90103 Released: February 2004 Copyright Security-Assessment. com 2005
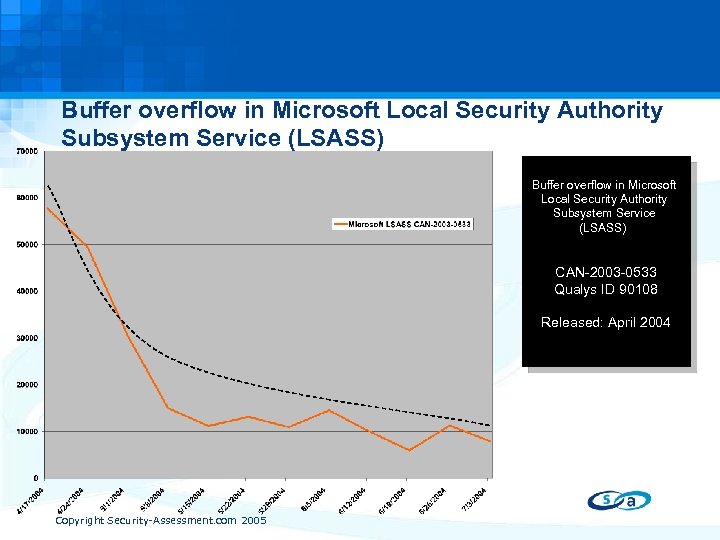 Buffer overflow in Microsoft Local Security Authority Subsystem Service (LSASS) CAN-2003 -0533 Qualys ID 90108 Released: April 2004 Copyright Security-Assessment. com 2005
Buffer overflow in Microsoft Local Security Authority Subsystem Service (LSASS) CAN-2003 -0533 Qualys ID 90108 Released: April 2004 Copyright Security-Assessment. com 2005
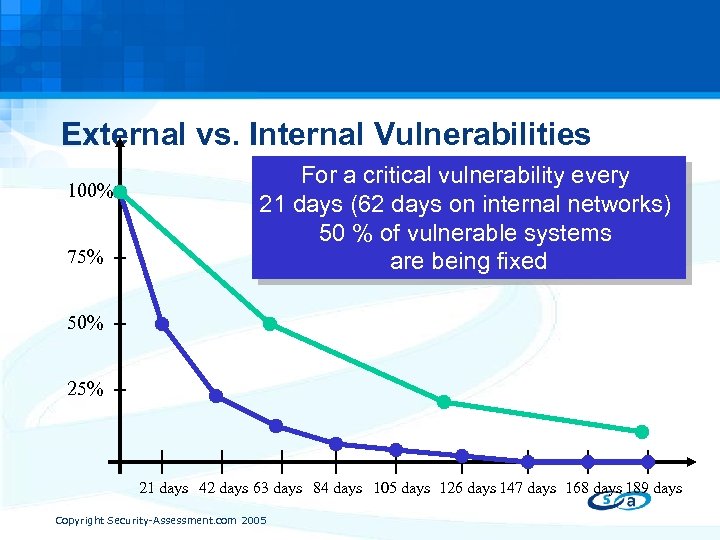 External vs. Internal Vulnerabilities 100% 75% For a critical vulnerability every 21 days (62 days on internal networks) 50 % of vulnerable systems are being fixed 50% 25% 21 days 42 days 63 days 84 days 105 days 126 days 147 days 168 days 189 days Copyright Security-Assessment. com 2005
External vs. Internal Vulnerabilities 100% 75% For a critical vulnerability every 21 days (62 days on internal networks) 50 % of vulnerable systems are being fixed 50% 25% 21 days 42 days 63 days 84 days 105 days 126 days 147 days 168 days 189 days Copyright Security-Assessment. com 2005
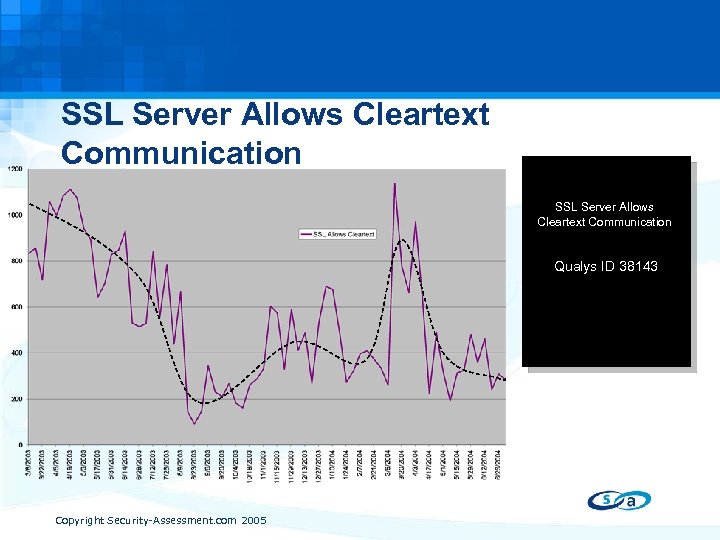 SSL Server Allows Cleartext Communication Qualys ID 38143 Copyright Security-Assessment. com 2005
SSL Server Allows Cleartext Communication Qualys ID 38143 Copyright Security-Assessment. com 2005
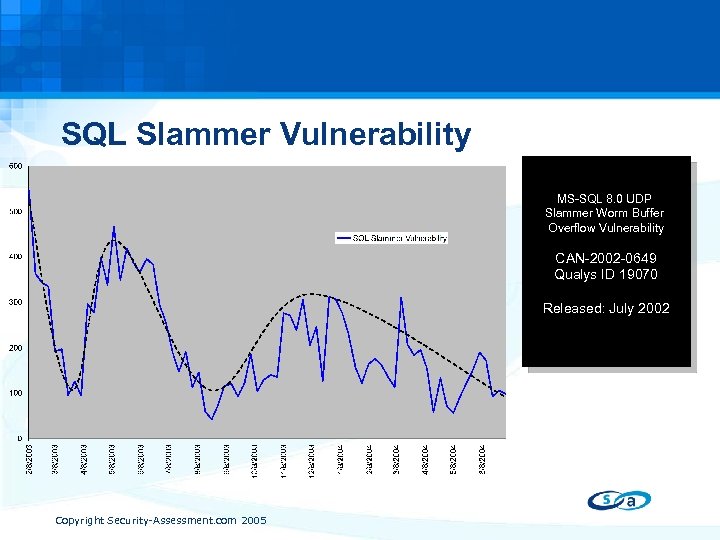 SQL Slammer Vulnerability MS-SQL 8. 0 UDP Slammer Worm Buffer Overflow Vulnerability CAN-2002 -0649 Qualys ID 19070 Released: July 2002 Copyright Security-Assessment. com 2005
SQL Slammer Vulnerability MS-SQL 8. 0 UDP Slammer Worm Buffer Overflow Vulnerability CAN-2002 -0649 Qualys ID 19070 Released: July 2002 Copyright Security-Assessment. com 2005
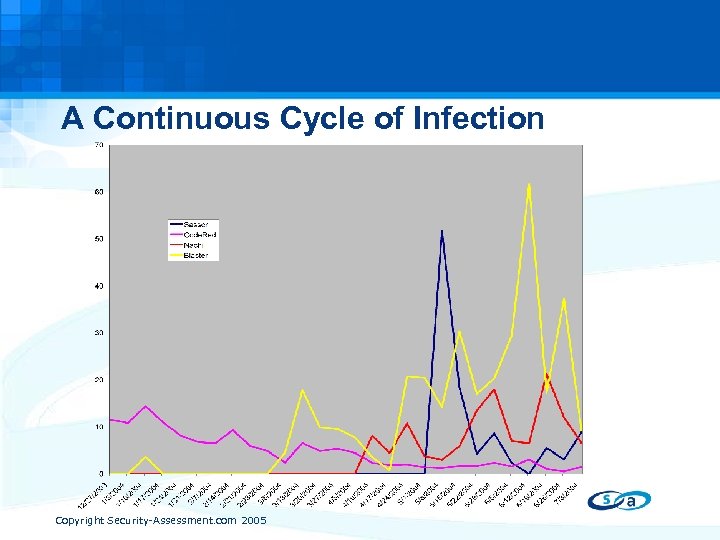 A Continuous Cycle of Infection Copyright Security-Assessment. com 2005
A Continuous Cycle of Infection Copyright Security-Assessment. com 2005
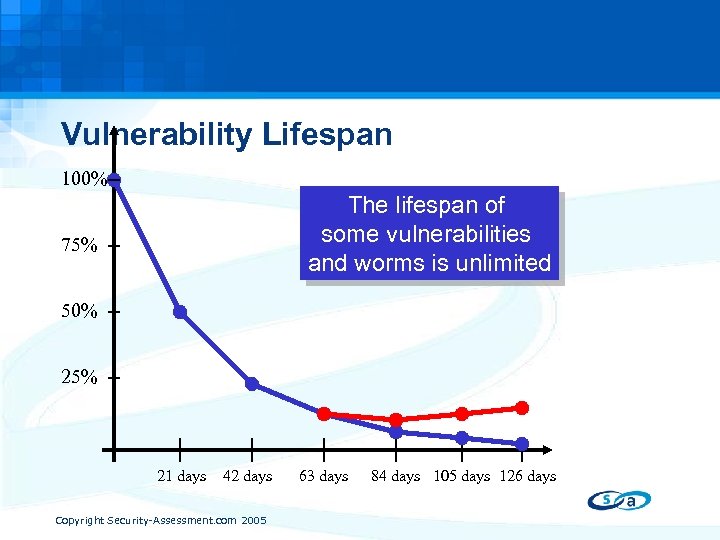 Vulnerability Lifespan 100% The lifespan of some vulnerabilities and worms is unlimited 75% 50% 25% 21 days 42 days Copyright Security-Assessment. com 2005 63 days 84 days 105 days 126 days
Vulnerability Lifespan 100% The lifespan of some vulnerabilities and worms is unlimited 75% 50% 25% 21 days 42 days Copyright Security-Assessment. com 2005 63 days 84 days 105 days 126 days
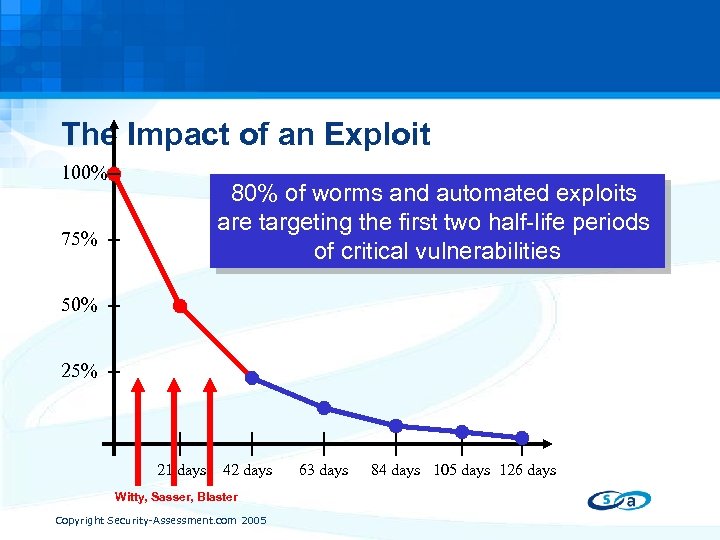 The Impact of an Exploit 100% 80% of worms and automated exploits are targeting the first two half-life periods of critical vulnerabilities 75% 50% 25% 21 days 42 days Witty, Sasser, Blaster Copyright Security-Assessment. com 2005 63 days 84 days 105 days 126 days
The Impact of an Exploit 100% 80% of worms and automated exploits are targeting the first two half-life periods of critical vulnerabilities 75% 50% 25% 21 days 42 days Witty, Sasser, Blaster Copyright Security-Assessment. com 2005 63 days 84 days 105 days 126 days
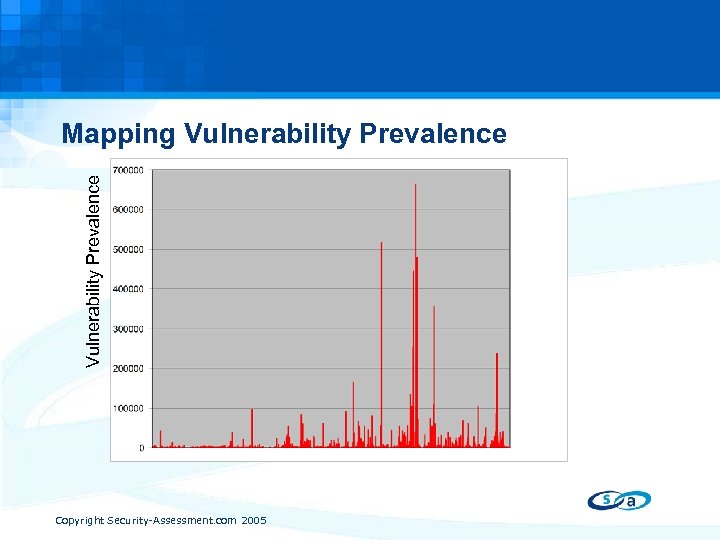 Vulnerability Prevalence Mapping Vulnerability Prevalence Individual Vulnerabilities Copyright Security-Assessment. com 2005
Vulnerability Prevalence Mapping Vulnerability Prevalence Individual Vulnerabilities Copyright Security-Assessment. com 2005
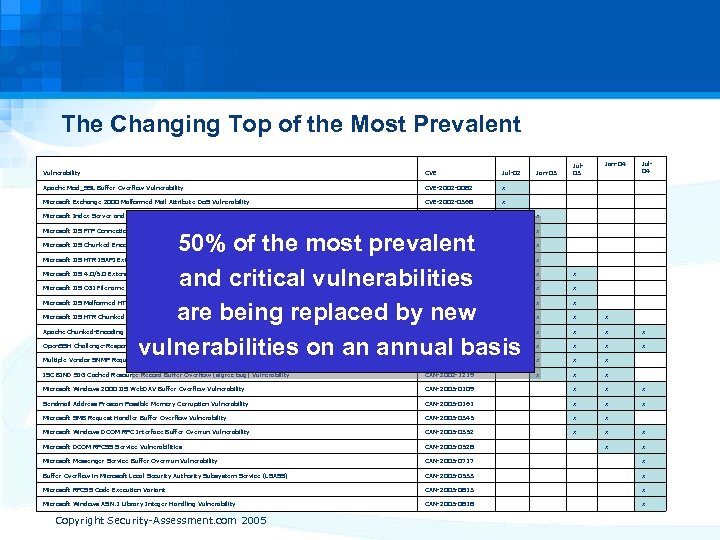 The Changing Top of the Most Prevalent Jan-04 Jul 04 Vulnerability CVE Jul-02 Jan-03 Jul 03 Apache Mod_SSL Buffer Overflow Vulnerability CVE-2002 -0082 x Microsoft Exchange 2000 Malformed Mail Attribute Do. S Vulnerability CVE-2002 -0368 x Microsoft Index Server and Indexing Service ISAPI Extension Buffer Overflow Vulnerability CVE-2001 -0500 x x Microsoft IIS FTP Connection Status Request Denial of Service Vulnerability CVE-2002 -0073 x x Microsoft IIS Chunked Encoding Transfer Heap Overflow Vulnerability CVE-2002 -0079 x x Microsoft IIS HTR ISAPI Extension Heap Overflow Vulnerability CVE-2002 -0364 x x Microsoft IIS 4. 0/5. 0 Extended UNICODE Remote Execution Vulnerability CVE-2000 -0884 x x x Microsoft IIS CGI Filename Decode Error Vulnerability CVE-2001 -0333 x x x Microsoft IIS Malformed HTR Request Buffer Overflow Vulnerability CVE-2002 -0071 x x x Microsoft IIS HTR Chunked Encoding Transfer Heap Overflow Vulnerability CVE-2002 -0364 x x Apache Chunked-Encoding Memory Corruption Vulnerability CVE-2002 -0392 x x x Open. SSH Challenge-Response Authentication Integer Overflow Vulnerability CVE-2002 -0639 x x x Multiple Vendor SNMP Request And Trap Handling Vulnerabilities CAN-2002 -0012 x x x ISC BIND SIG Cached Resource Record Buffer Overflow (sigrec bug) Vulnerability CAN-2002 -1219 x x x Microsoft Windows 2000 IIS Web. DAV Buffer Overflow Vulnerability CAN-2003 -0109 x x x Sendmail Address Prescan Possible Memory Corruption Vulnerability CAN-2003 -0161 x x x Microsoft SMB Request Handler Buffer Overflow Vulnerability CAN-2003 -0345 x x Microsoft Windows DCOM RPC Interface Buffer Overrun Vulnerability CAN-2003 -0352 x x x Microsoft DCOM RPCSS Service Vulnerabilities CAN-2003 -0528 x x Microsoft Messenger Service Buffer Overrrun Vulnerability CAN-2003 -0717 x Buffer Overflow in Microsoft Local Security Authority Subsystem Service (LSASS) CAN-2003 -0533 x Microsoft RPCSS Code Execution Variant CAN-2003 -0813 x Microsoft Windows ASN. 1 Library Integer Handling Vulnerability CAN-2003 -0818 x 50% of the most prevalent and critical vulnerabilities are being replaced by new vulnerabilities on an annual basis Copyright Security-Assessment. com 2005
The Changing Top of the Most Prevalent Jan-04 Jul 04 Vulnerability CVE Jul-02 Jan-03 Jul 03 Apache Mod_SSL Buffer Overflow Vulnerability CVE-2002 -0082 x Microsoft Exchange 2000 Malformed Mail Attribute Do. S Vulnerability CVE-2002 -0368 x Microsoft Index Server and Indexing Service ISAPI Extension Buffer Overflow Vulnerability CVE-2001 -0500 x x Microsoft IIS FTP Connection Status Request Denial of Service Vulnerability CVE-2002 -0073 x x Microsoft IIS Chunked Encoding Transfer Heap Overflow Vulnerability CVE-2002 -0079 x x Microsoft IIS HTR ISAPI Extension Heap Overflow Vulnerability CVE-2002 -0364 x x Microsoft IIS 4. 0/5. 0 Extended UNICODE Remote Execution Vulnerability CVE-2000 -0884 x x x Microsoft IIS CGI Filename Decode Error Vulnerability CVE-2001 -0333 x x x Microsoft IIS Malformed HTR Request Buffer Overflow Vulnerability CVE-2002 -0071 x x x Microsoft IIS HTR Chunked Encoding Transfer Heap Overflow Vulnerability CVE-2002 -0364 x x Apache Chunked-Encoding Memory Corruption Vulnerability CVE-2002 -0392 x x x Open. SSH Challenge-Response Authentication Integer Overflow Vulnerability CVE-2002 -0639 x x x Multiple Vendor SNMP Request And Trap Handling Vulnerabilities CAN-2002 -0012 x x x ISC BIND SIG Cached Resource Record Buffer Overflow (sigrec bug) Vulnerability CAN-2002 -1219 x x x Microsoft Windows 2000 IIS Web. DAV Buffer Overflow Vulnerability CAN-2003 -0109 x x x Sendmail Address Prescan Possible Memory Corruption Vulnerability CAN-2003 -0161 x x x Microsoft SMB Request Handler Buffer Overflow Vulnerability CAN-2003 -0345 x x Microsoft Windows DCOM RPC Interface Buffer Overrun Vulnerability CAN-2003 -0352 x x x Microsoft DCOM RPCSS Service Vulnerabilities CAN-2003 -0528 x x Microsoft Messenger Service Buffer Overrrun Vulnerability CAN-2003 -0717 x Buffer Overflow in Microsoft Local Security Authority Subsystem Service (LSASS) CAN-2003 -0533 x Microsoft RPCSS Code Execution Variant CAN-2003 -0813 x Microsoft Windows ASN. 1 Library Integer Handling Vulnerability CAN-2003 -0818 x 50% of the most prevalent and critical vulnerabilities are being replaced by new vulnerabilities on an annual basis Copyright Security-Assessment. com 2005
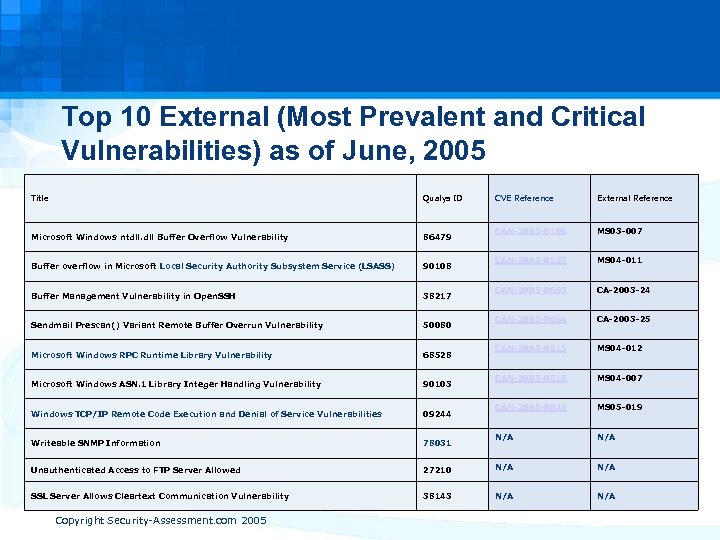 Top 10 External (Most Prevalent and Critical Vulnerabilities) as of June, 2005 Title Qualys ID Microsoft Windows ntdll. dll Buffer Overflow Vulnerability 86479 Buffer overflow in Microsoft Local Security Authority Subsystem Service (LSASS) 90108 Buffer Management Vulnerability in Open. SSH 38217 Sendmail Prescan() Variant Remote Buffer Overrun Vulnerability 50080 Microsoft Windows RPC Runtime Library Vulnerability 68528 Microsoft Windows ASN. 1 Library Integer Handling Vulnerability 90103 Windows TCP/IP Remote Code Execution and Denial of Service Vulnerabilities 09244 Writeable SNMP Information 78031 Unauthenticated Access to FTP Server Allowed SSL Server Allows Cleartext Communication Vulnerability Copyright Security-Assessment. com 2005 CVE Reference External Reference CAN-2003 -0109 MS 03 -007 CAN-2003 -0533 MS 04 -011 CAN-2003 -0693 CA-2003 -24 CAN-2003 -0694 CA-2003 -25 CAN-2003 -0813 MS 04 -012 CAN-2003 -0818 MS 04 -007 CAN-2005 -0048 MS 05 -019 N/A 27210 N/A 38143 N/A
Top 10 External (Most Prevalent and Critical Vulnerabilities) as of June, 2005 Title Qualys ID Microsoft Windows ntdll. dll Buffer Overflow Vulnerability 86479 Buffer overflow in Microsoft Local Security Authority Subsystem Service (LSASS) 90108 Buffer Management Vulnerability in Open. SSH 38217 Sendmail Prescan() Variant Remote Buffer Overrun Vulnerability 50080 Microsoft Windows RPC Runtime Library Vulnerability 68528 Microsoft Windows ASN. 1 Library Integer Handling Vulnerability 90103 Windows TCP/IP Remote Code Execution and Denial of Service Vulnerabilities 09244 Writeable SNMP Information 78031 Unauthenticated Access to FTP Server Allowed SSL Server Allows Cleartext Communication Vulnerability Copyright Security-Assessment. com 2005 CVE Reference External Reference CAN-2003 -0109 MS 03 -007 CAN-2003 -0533 MS 04 -011 CAN-2003 -0693 CA-2003 -24 CAN-2003 -0694 CA-2003 -25 CAN-2003 -0813 MS 04 -012 CAN-2003 -0818 MS 04 -007 CAN-2005 -0048 MS 05 -019 N/A 27210 N/A 38143 N/A
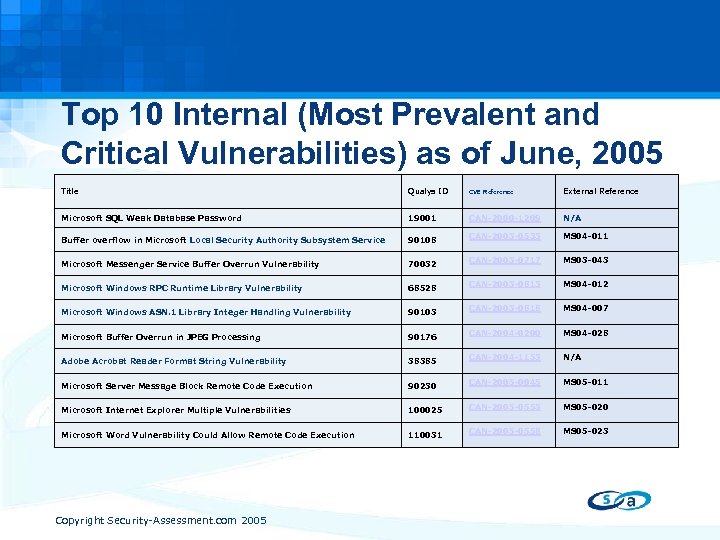 Top 10 Internal (Most Prevalent and Critical Vulnerabilities) as of June, 2005 Title Qualys ID CVE Reference External Reference Microsoft SQL Weak Database Password 19001 CAN-2000 -1209 N/A Buffer overflow in Microsoft Local Security Authority Subsystem Service 90108 CAN-2003 -0533 MS 04 -011 Microsoft Messenger Service Buffer Overrun Vulnerability 70032 CAN-2003 -0717 MS 03 -043 Microsoft Windows RPC Runtime Library Vulnerability 68528 CAN-2003 -0813 MS 04 -012 Microsoft Windows ASN. 1 Library Integer Handling Vulnerability 90103 CAN-2003 -0818 MS 04 -007 Microsoft Buffer Overrun in JPEG Processing 90176 CAN-2004 -0200 MS 04 -028 Adobe Acrobat Reader Format String Vulnerability 38385 CAN-2004 -1153 N/A Microsoft Server Message Block Remote Code Execution 90230 CAN-2005 -0045 MS 05 -011 Microsoft Internet Explorer Multiple Vulnerabilities 100025 CAN-2005 -0553 MS 05 -020 Microsoft Word Vulnerability Could Allow Remote Code Execution 110031 CAN-2005 -0558 MS 05 -023 Copyright Security-Assessment. com 2005
Top 10 Internal (Most Prevalent and Critical Vulnerabilities) as of June, 2005 Title Qualys ID CVE Reference External Reference Microsoft SQL Weak Database Password 19001 CAN-2000 -1209 N/A Buffer overflow in Microsoft Local Security Authority Subsystem Service 90108 CAN-2003 -0533 MS 04 -011 Microsoft Messenger Service Buffer Overrun Vulnerability 70032 CAN-2003 -0717 MS 03 -043 Microsoft Windows RPC Runtime Library Vulnerability 68528 CAN-2003 -0813 MS 04 -012 Microsoft Windows ASN. 1 Library Integer Handling Vulnerability 90103 CAN-2003 -0818 MS 04 -007 Microsoft Buffer Overrun in JPEG Processing 90176 CAN-2004 -0200 MS 04 -028 Adobe Acrobat Reader Format String Vulnerability 38385 CAN-2004 -1153 N/A Microsoft Server Message Block Remote Code Execution 90230 CAN-2005 -0045 MS 05 -011 Microsoft Internet Explorer Multiple Vulnerabilities 100025 CAN-2005 -0553 MS 05 -020 Microsoft Word Vulnerability Could Allow Remote Code Execution 110031 CAN-2005 -0558 MS 05 -023 Copyright Security-Assessment. com 2005
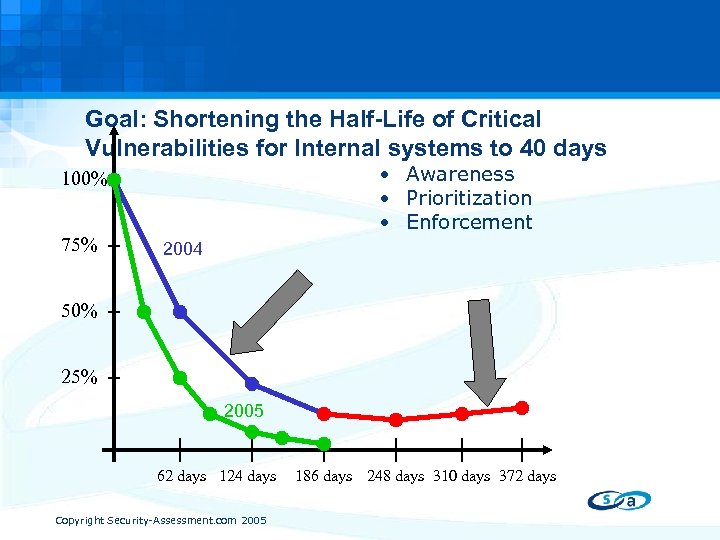 Goal: Shortening the Half-Life of Critical Vulnerabilities for Internal systems to 40 days • Awareness • Prioritization • Enforcement 100% 75% 2004 50% 25% 2005 62 days 124 days Copyright Security-Assessment. com 2005 186 days 248 days 310 days 372 days
Goal: Shortening the Half-Life of Critical Vulnerabilities for Internal systems to 40 days • Awareness • Prioritization • Enforcement 100% 75% 2004 50% 25% 2005 62 days 124 days Copyright Security-Assessment. com 2005 186 days 248 days 310 days 372 days
 Network Access Control Industry Initiatives • Cisco Network Admission Control (NAC) – Leveraging Cisco Networking devices to control access – Evaluation of devices via agent (CTA) or agentless • Microsoft Network Access Protection (NAP) – Client side system health agent – Server side system health validator • TCG Trusted Network Connect (TNC) – Open software architecture for policy based access – Cross vendor architecture Copyright Security-Assessment. com 2005
Network Access Control Industry Initiatives • Cisco Network Admission Control (NAC) – Leveraging Cisco Networking devices to control access – Evaluation of devices via agent (CTA) or agentless • Microsoft Network Access Protection (NAP) – Client side system health agent – Server side system health validator • TCG Trusted Network Connect (TNC) – Open software architecture for policy based access – Cross vendor architecture Copyright Security-Assessment. com 2005
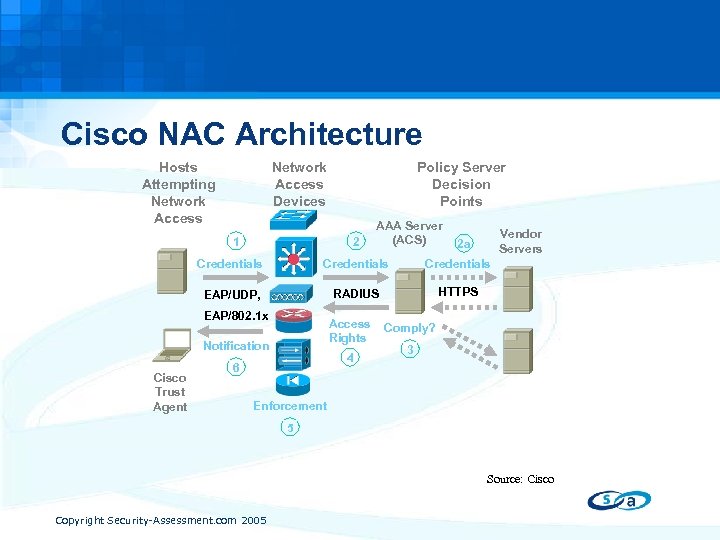 Cisco NAC Architecture Network Access Devices Hosts Attempting Network Access 1 Policy Server Decision Points 2 AAA Server (ACS) Vendor Servers 2 a Credentials EAP/UDP, RADIUS HTTPS EAP/802. 1 x Access Rights Notification Cisco Trust Agent 4 6 Comply? 3 Enforcement 5 Source: Cisco Copyright Security-Assessment. com 2005
Cisco NAC Architecture Network Access Devices Hosts Attempting Network Access 1 Policy Server Decision Points 2 AAA Server (ACS) Vendor Servers 2 a Credentials EAP/UDP, RADIUS HTTPS EAP/802. 1 x Access Rights Notification Cisco Trust Agent 4 6 Comply? 3 Enforcement 5 Source: Cisco Copyright Security-Assessment. com 2005
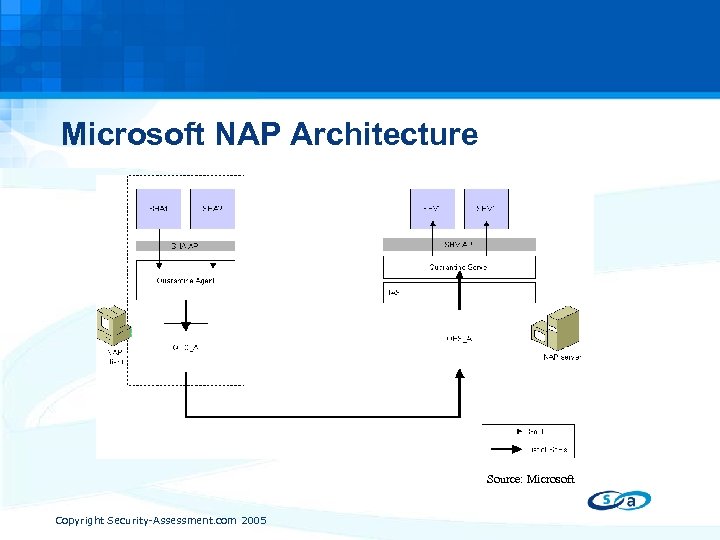 Microsoft NAP Architecture Source: Microsoft Copyright Security-Assessment. com 2005
Microsoft NAP Architecture Source: Microsoft Copyright Security-Assessment. com 2005
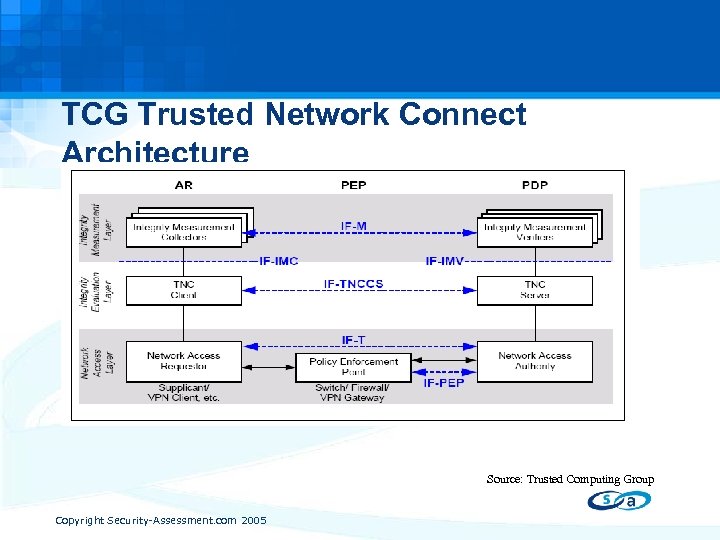 TCG Trusted Network Connect Architecture Source: Trusted Computing Group Copyright Security-Assessment. com 2005
TCG Trusted Network Connect Architecture Source: Trusted Computing Group Copyright Security-Assessment. com 2005
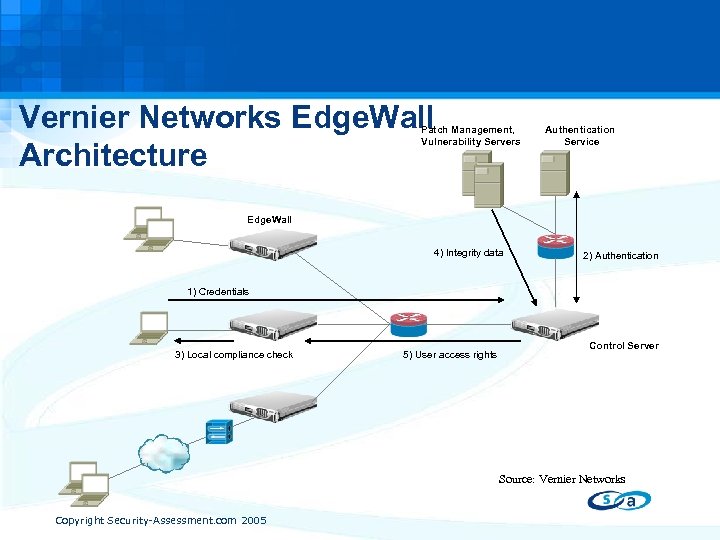 Vernier Networks Edge. Wall Architecture Patch Management, Vulnerability Servers Authentication Service Edge. Wall 4) Integrity data 2) Authentication 1) Credentials 3) Local compliance check 5) User access rights Control Server Source: Vernier Networks Copyright Security-Assessment. com 2005
Vernier Networks Edge. Wall Architecture Patch Management, Vulnerability Servers Authentication Service Edge. Wall 4) Integrity data 2) Authentication 1) Credentials 3) Local compliance check 5) User access rights Control Server Source: Vernier Networks Copyright Security-Assessment. com 2005
 Network Access Control Challenges • Impact/Interoperability with existing infrastructure • Agent-based vs. agent-less approaches • Continuous vs. Initial device evaluation • Interoperability between different architectures Copyright Security-Assessment. com 2005
Network Access Control Challenges • Impact/Interoperability with existing infrastructure • Agent-based vs. agent-less approaches • Continuous vs. Initial device evaluation • Interoperability between different architectures Copyright Security-Assessment. com 2005
 Why Network Access Control is important • Reduced risk of outbreak due to infected endpoints • Safe access to networks through VPN access • Controlled remediation and patching of unhealthy endpoints • Increased security of corporate resources • Increased compliance with regulatory requirements Copyright Security-Assessment. com 2005
Why Network Access Control is important • Reduced risk of outbreak due to infected endpoints • Safe access to networks through VPN access • Controlled remediation and patching of unhealthy endpoints • Increased security of corporate resources • Increased compliance with regulatory requirements Copyright Security-Assessment. com 2005
 Thank You Q&A Peter. benson@security-assessment. com Copyright Security-Assessment. com 2005
Thank You Q&A Peter. benson@security-assessment. com Copyright Security-Assessment. com 2005


