ba3d6c50d70412b5803f0a78e96703cd.ppt
- Количество слайдов: 18
Module 12 Virtual Private Networks ¨MModified by : Ahmad Al Ghoul ¨PPhiladelphia University ¨FFaculty Of Administrative & Financial Sciences ¨BBusiness Networking & System Management Department ¨RRoom Number 32406 ¨EE-mail Address: ahmad 4_2_69@hotmail. com Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 1
Contents ¨ ¨ ¨ Relation to SSL & SSH Virtual Private Network Three Types of VPNs The Concept of Tunneling General IPTunneling Look at the stack GRE & PPTP Generic Routing Encapsulation PPTP Ipsec Encapsulating Security Payload Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 2
Relation to SSL & SSH ¨ Recall SSL is the secure socket layer – It provides an encrypted and authenticated TCP connection between a client and a server. – It does not hide your network because you still use standard IP visible to all. Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 3
Virtual Private Network ¨ Why? – Institutions are distribted – They need to protect themselves – Old Days • Buy your own phone lines and build a physically private network. – VPN • Use the internet as a “carrier” of your private traffic. Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 4
Three Types of VPNs ¨ Remote access – A company uses a dial-up system to allow remote workers to connect and establish secure connections to the company network ¨ Site-to-site – Intranet • Connect two different, but remote LANS to form a single network – Extranet • Two different companies want to establish a private connection Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 5
Reasons and Requirements ¨ Typical Reasons for wanting a VPN – – – – Extend geographic connectivity Improve security Reduce operational costs versus traditional WAN Improve productivity Simplify network topology Provide global networking opportunities Provide telecommuter support ¨ Requirements for a Good VPN – – – Security Reliability Scalability Network management Policy management Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 6
The Concept of Tunneling ¨ tunneling - the process of placing an entire packet within another packet and sending it over a network. ¨ Tunneling requires three different protocols: – Carrier protocol: The protocol used by the network that the information is traveling over – Encapsulating protocol: The protocol (GRE, IPSec, L 2 F, PPTP, L 2 TP) that is wrapped around the original data – Passenger protocol: The original data (IPX, Net. Beui, IP) being carried Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 7
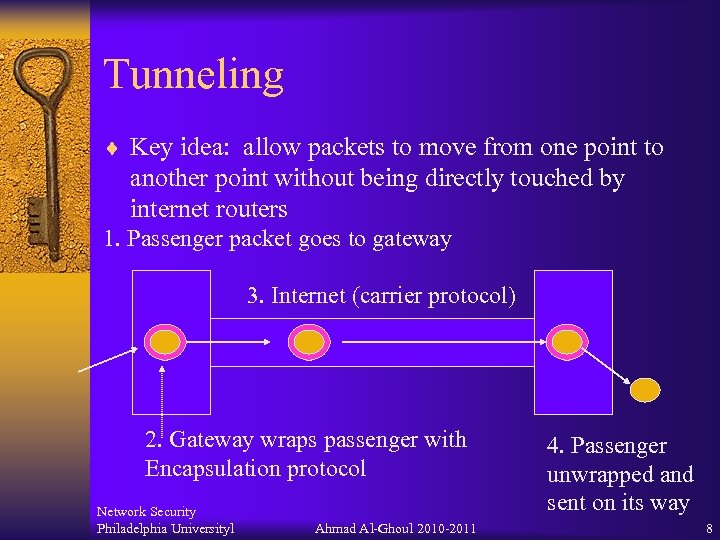
Tunneling ¨ Key idea: allow packets to move from one point to another point without being directly touched by internet routers 1. Passenger packet goes to gateway 3. Internet (carrier protocol) 2. Gateway wraps passenger with Encapsulation protocol Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 4. Passenger unwrapped and sent on its way 8
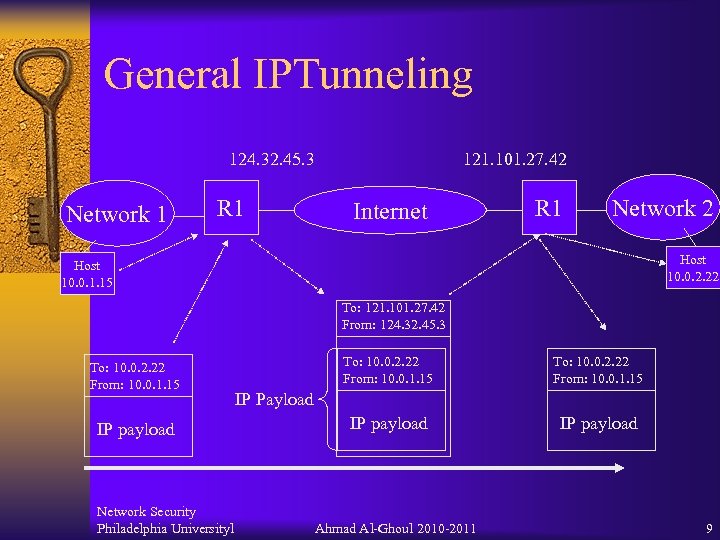
General IPTunneling 124. 32. 45. 3 Network 1 R 1 121. 101. 27. 42 Internet R 1 Network 2 Host 10. 0. 2. 22 Host 10. 0. 1. 15 To: 121. 101. 27. 42 From: 124. 32. 45. 3 To: 10. 0. 2. 22 From: 10. 0. 1. 15 IP payload Network Security Philadelphia Universityl To: 10. 0. 2. 22 From: 10. 0. 1. 15 IP payload IP Payload Ahmad Al-Ghoul 2010 -2011 9
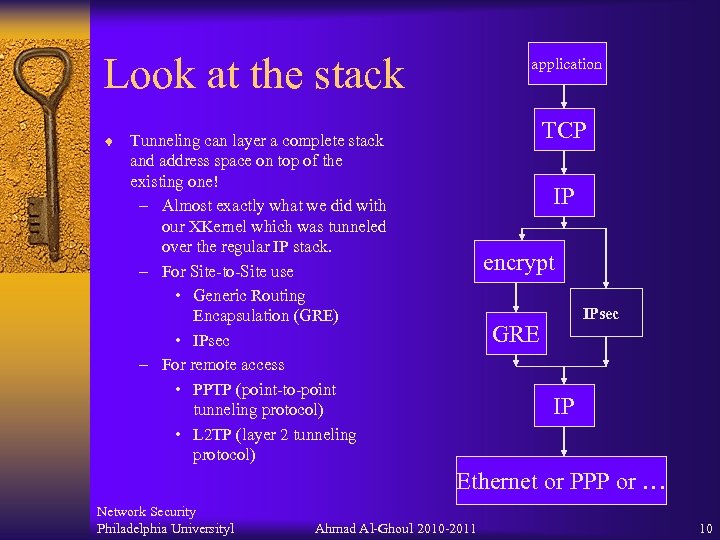
Look at the stack application TCP ¨ Tunneling can layer a complete stack and address space on top of the existing one! – Almost exactly what we did with our XKernel which was tunneled over the regular IP stack. – For Site-to-Site use • Generic Routing Encapsulation (GRE) • IPsec – For remote access • PPTP (point-to-point tunneling protocol) • L 2 TP (layer 2 tunneling protocol) IP encrypt IPsec GRE IP Ethernet or PPP or … Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 10
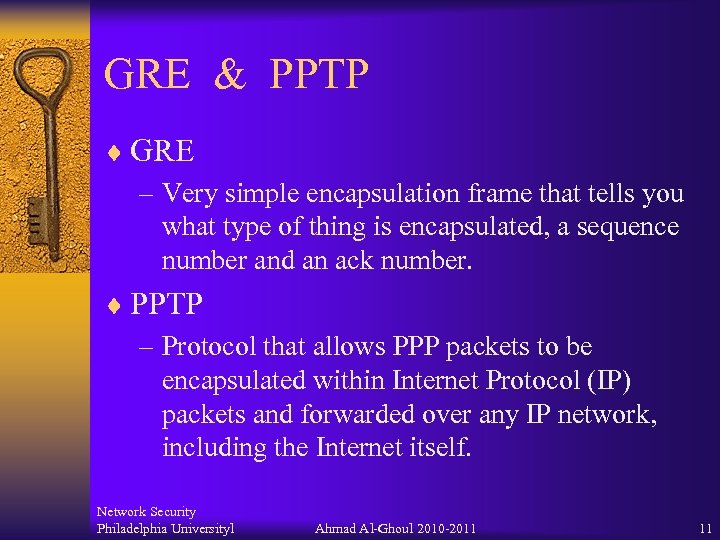
GRE & PPTP ¨ GRE – Very simple encapsulation frame that tells you what type of thing is encapsulated, a sequence number and an ack number. ¨ PPTP – Protocol that allows PPP packets to be encapsulated within Internet Protocol (IP) packets and forwarded over any IP network, including the Internet itself. Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 11
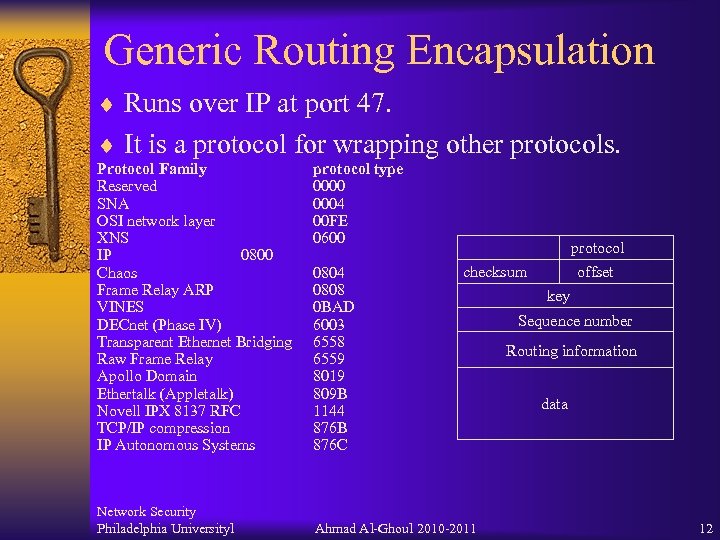
Generic Routing Encapsulation ¨ Runs over IP at port 47. ¨ It is a protocol for wrapping other protocols. Protocol Family Reserved SNA OSI network layer XNS IP 0800 Chaos Frame Relay ARP VINES DECnet (Phase IV) Transparent Ethernet Bridging Raw Frame Relay Apollo Domain Ethertalk (Appletalk) Novell IPX 8137 RFC TCP/IP compression IP Autonomous Systems Network Security Philadelphia Universityl protocol type 0000 0004 00 FE 0600 0804 0808 0 BAD 6003 6558 6559 8019 809 B 1144 876 B 876 C protocol checksum Ahmad Al-Ghoul 2010 -2011 offset key Sequence number Routing information data 12
PPTP ¨ For a dial-up client – First establish a PPP connection to the server – Set up a TCP connection on port 1723 for control messages • Session management command-replies • Handles calls and keep-alive messages – Over the PPP one runs IP and TCP. ¨ In other cases use existing IP level. Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 13
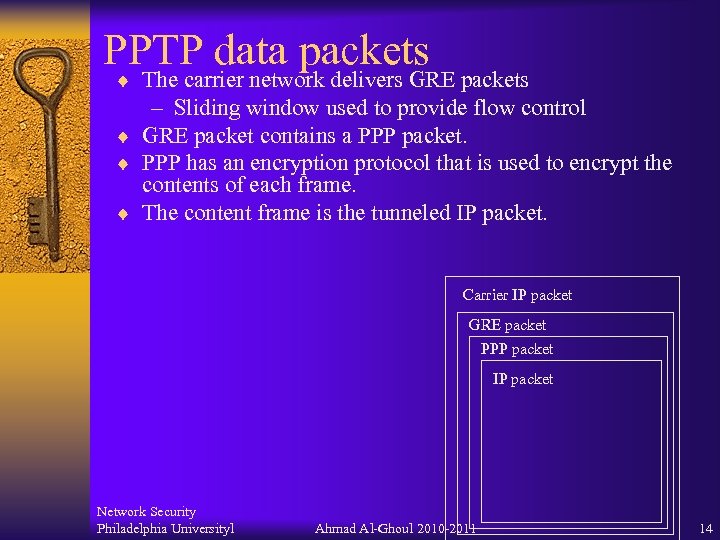
PPTP data packets ¨ The carrier network delivers GRE packets – Sliding window used to provide flow control ¨ GRE packet contains a PPP packet. ¨ PPP has an encryption protocol that is used to encrypt the contents of each frame. ¨ The content frame is the tunneled IP packet. Carrier IP packet GRE packet PPP packet IP packet Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 14
IPsec ¨ A General Framework for IP security – NOTE: SSL is at the TCP level – IPSec is designed to be at the IP level ¨ Two Components – Two protocols for security • A header for authentication (AH) • A header for secure encapsulation (ESP) – Internet Security Assoc. and Key Mgmt Protocl ¨ A Security Association (SA) is a one way connection between two hosts/routers that is based on a choice of AH/ESP and Key protocol. Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 15
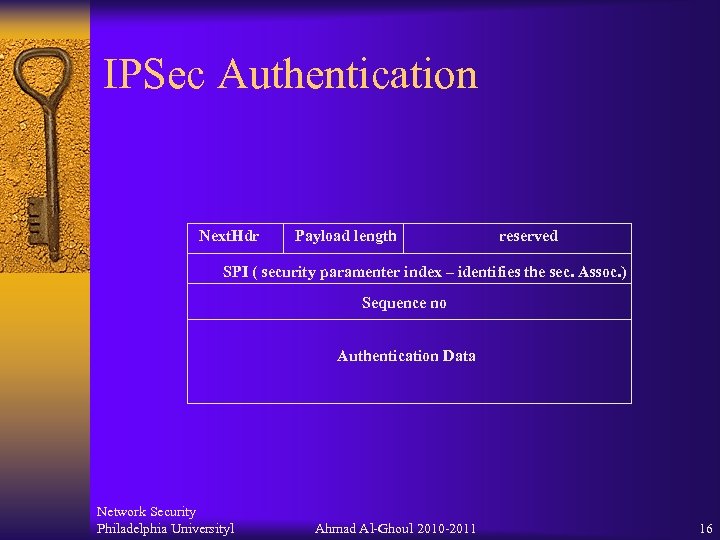
IPSec Authentication Next. Hdr Payload length reserved SPI ( security paramenter index – identifies the sec. Assoc. ) Sequence no Authentication Data Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 16
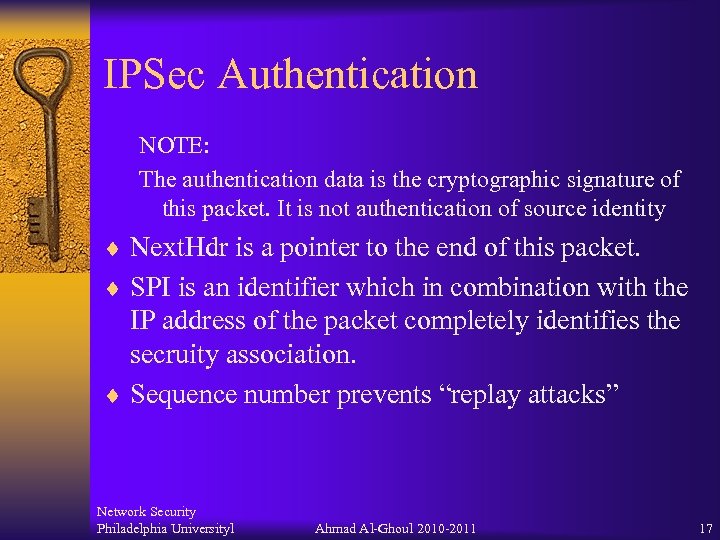
IPSec Authentication NOTE: The authentication data is the cryptographic signature of this packet. It is not authentication of source identity ¨ Next. Hdr is a pointer to the end of this packet. ¨ SPI is an identifier which in combination with the IP address of the packet completely identifies the secruity association. ¨ Sequence number prevents “replay attacks” Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 17
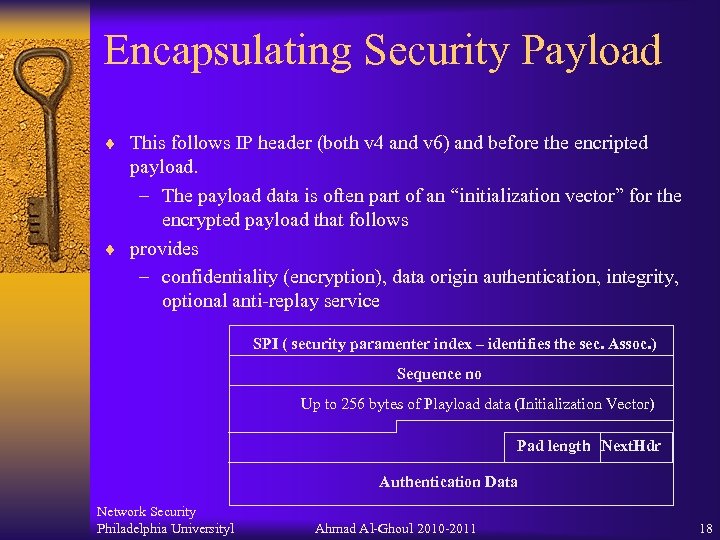
Encapsulating Security Payload ¨ This follows IP header (both v 4 and v 6) and before the encripted payload. – The payload data is often part of an “initialization vector” for the encrypted payload that follows ¨ provides – confidentiality (encryption), data origin authentication, integrity, optional anti-replay service SPI ( security paramenter index – identifies the sec. Assoc. ) Sequence no Up to 256 bytes of Playload data (Initialization Vector) Pad length Next. Hdr Authentication Data Network Security Philadelphia Universityl Ahmad Al-Ghoul 2010 -2011 18
ba3d6c50d70412b5803f0a78e96703cd.ppt