13f2c478c5673253a7b40c532701a7b2.ppt
- Количество слайдов: 26
Modeling the trust boundaries created by securable objects Matt Miller USENIX W 00 T ‘ 08 July 28 th, 2008
Problem statement § Trust boundaries must be understood Ø Ø Ø Required for accurate characterization of threats Required for auditing code exposed to untrusted data Provides insight to both attackers and defenders § Techniques exist to model trust boundaries from a design perspective Ø Threat modeling § Techniques are needed to identify and analyze trust boundaries from an implementation perspective Ø Securable objects are the focus of this presentation
Agenda § A brief explanation of trust boundaries and securable objects § Automatically capturing access rights granted to securable objects § Analyzing captured data to derive permitted data flows, trust boundaries, threats, and potential elevation paths
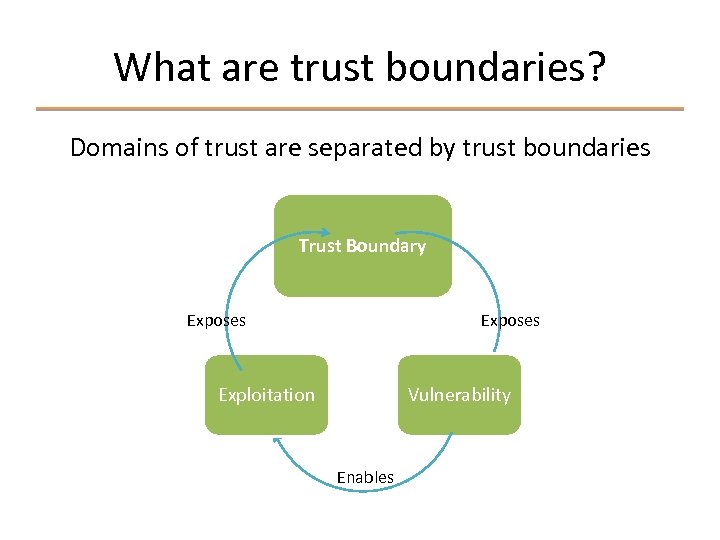
What are trust boundaries? Domains of trust are separated by trust boundaries Trust Boundary Exposes Exploitation Vulnerability Enables
Securable objects § Used by Windows as an abstraction for various types of resources Ø Files, registry keys, sections, events, processes, threads, etc § Objects can be assigned a security descriptor to control access Ø Security identifiers (SIDs) can be granted/denied specific access rights
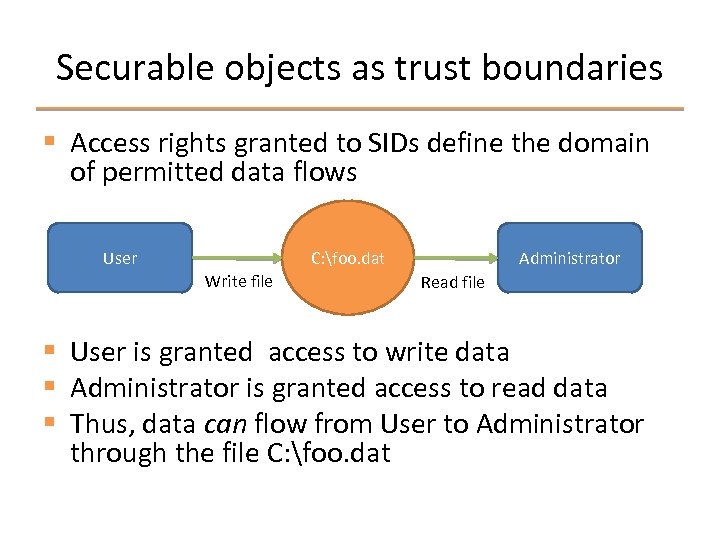
Securable objects as trust boundaries § Access rights granted to SIDs define the domain of permitted data flows C: foo. dat User Write file Administrator Read file § User is granted access to write data § Administrator is granted access to read data § Thus, data can flow from User to Administrator through the file C: foo. dat
Capturing securable object access rights § Two strategies are required to get a complete picture § Persistent object rights can be captured using the Windows API Ø Ø Defined prior to boot, non-volatile Files, registry keys, services § Dynamic object rights can be captured using dynamic instrumentation Ø Ø Ø Defined after boot, volatile and non-volatile Sections, events, processes, and all other object types Provides context info & can detect subtle race conditions
Dynamic instrumentation § Securable objects are managed by the object manager in the Windows kernel § A device driver can use dynamic instrumentation to capture granted access rights and execution context Ø Process context, security tokens, call stack, and so on § Three key points must be instrumented Ø Ø Ø Object definition Object use Object security descriptor update
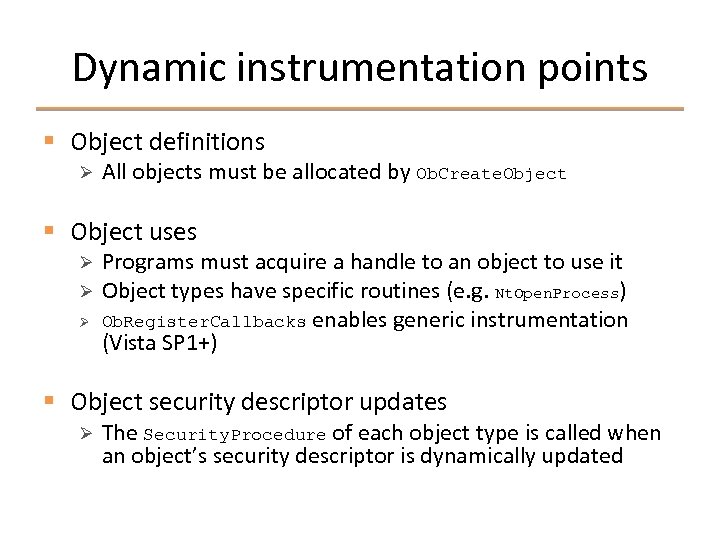
Dynamic instrumentation points § Object definitions Ø All objects must be allocated by Ob. Create. Object § Object uses Ø Ø Ø Programs must acquire a handle to an object to use it Object types have specific routines (e. g. Nt. Open. Process) Ob. Register. Callbacks enables generic instrumentation (Vista SP 1+) § Object security descriptor updates Ø The Security. Procedure of each object type is called when an object’s security descriptor is dynamically updated
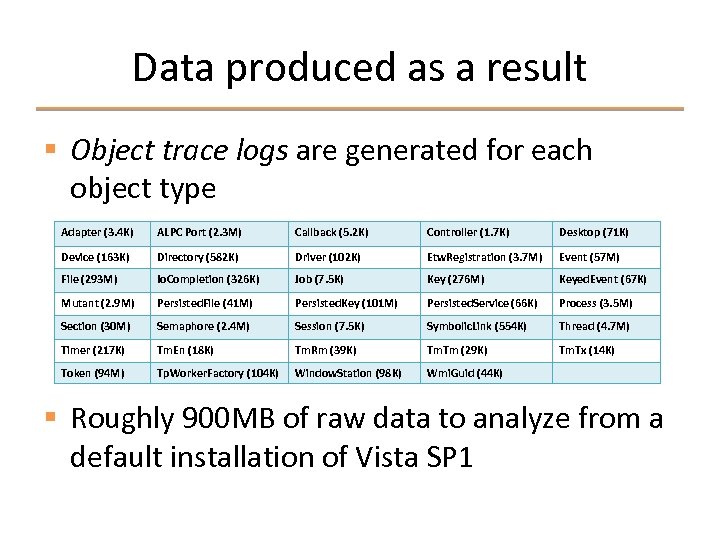
Data produced as a result § Object trace logs are generated for each object type Adapter (3. 4 K) ALPC Port (2. 3 M) Callback (5. 2 K) Controller (1. 7 K) Desktop (71 K) Device (163 K) Directory (582 K) Driver (102 K) Etw. Registration (3. 7 M) Event (57 M) File (293 M) Io. Completion (326 K) Job (7. 5 K) Key (276 M) Keyed. Event (67 K) Mutant (2. 9 M) Persisted. File (41 M) Persisted. Key (101 M) Persisted. Service (66 K) Process (3. 5 M) Section (30 M) Semaphore (2. 4 M) Session (7. 5 K) Symbolic. Link (554 K) Thread (4. 7 M) Timer (217 K) Tm. En (18 K) Tm. Rm (39 K) Tm. Tm (29 K) Tm. Tx (14 K) Token (94 M) Tp. Worker. Factory (104 K) Window. Station (98 K) Wmi. Guid (44 K) § Roughly 900 MB of raw data to analyze from a default installation of Vista SP 1
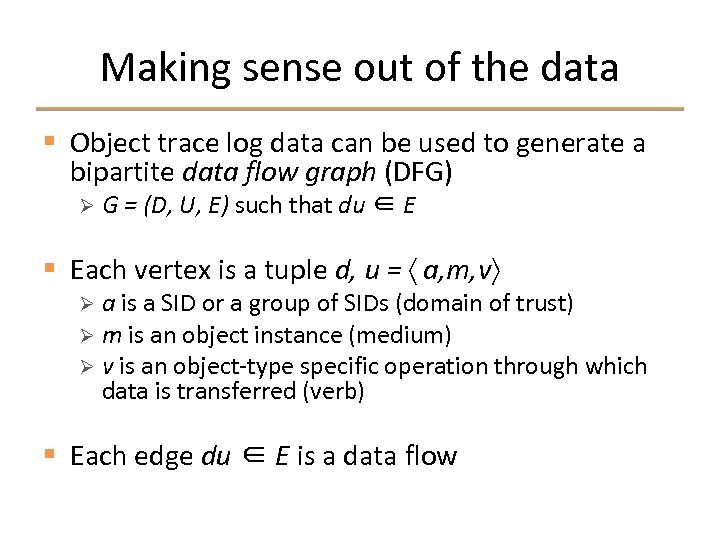
Making sense out of the data § Object trace log data can be used to generate a bipartite data flow graph (DFG) Ø G = (D, U, E) such that du ∈ E § Each vertex is a tuple d, u = 〈 a, m, v〉 a is a SID or a group of SIDs (domain of trust) Ø m is an object instance (medium) Ø v is an object-type specific operation through which data is transferred (verb) Ø § Each edge du ∈ E is a data flow
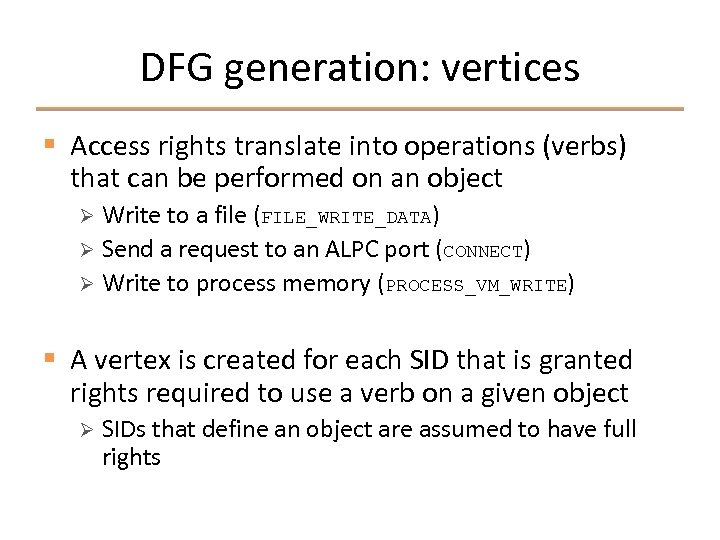
DFG generation: vertices § Access rights translate into operations (verbs) that can be performed on an object Write to a file (FILE_WRITE_DATA) Ø Send a request to an ALPC port (CONNECT) Ø Write to process memory (PROCESS_VM_WRITE) Ø § A vertex is created for each SID that is granted rights required to use a verb on a given object Ø SIDs that define an object are assumed to have full rights
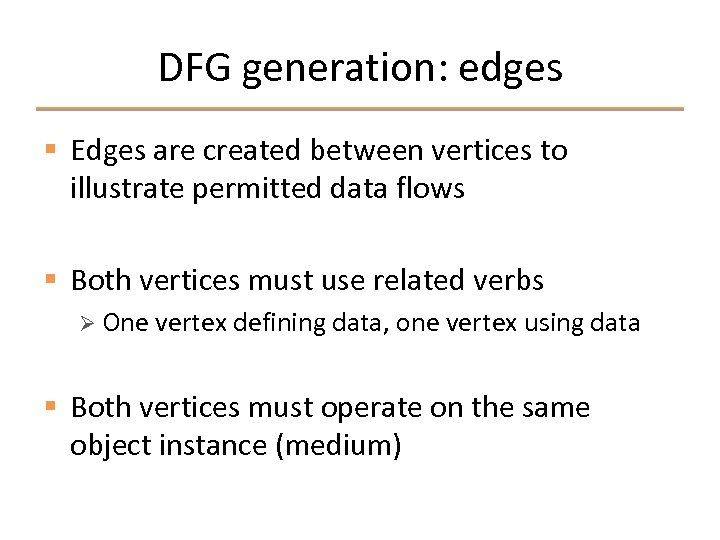
DFG generation: edges § Edges are created between vertices to illustrate permitted data flows § Both vertices must use related verbs Ø One vertex defining data, one vertex using data § Both vertices must operate on the same object instance (medium)
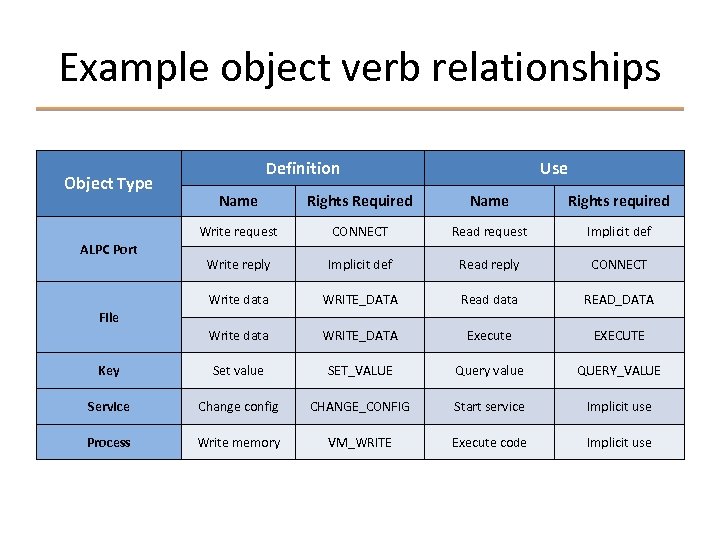
Example object verb relationships Object Type Definition Use Name Rights Required Name Rights required Write request CONNECT Read request Implicit def Write reply Implicit def Read reply CONNECT Write data WRITE_DATA Read data READ_DATA Write data WRITE_DATA Execute EXECUTE Key Set value SET_VALUE Query value QUERY_VALUE Service Change config CHANGE_CONFIG Start service Implicit use Process Write memory VM_WRITE Execute code Implicit use ALPC Port File
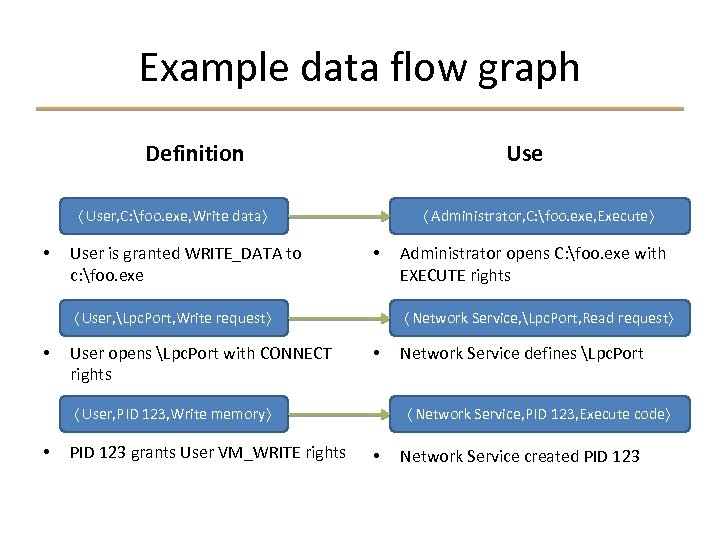
Example data flow graph Definition Use 〈 User, C: foo. exe, Write data〉 • User is granted WRITE_DATA to c: foo. exe 〈 Administrator, C: foo. exe, Execute〉 • 〈 User, Lpc. Port, Write request〉 • User opens Lpc. Port with CONNECT rights 〈 Network Service, Lpc. Port, Read request〉 • 〈 User, PID 123, Write memory〉 • PID 123 grants User VM_WRITE rights Administrator opens C: foo. exe with EXECUTE rights Network Service defines Lpc. Port 〈 Network Service, PID 123, Execute code〉 • Network Service created PID 123
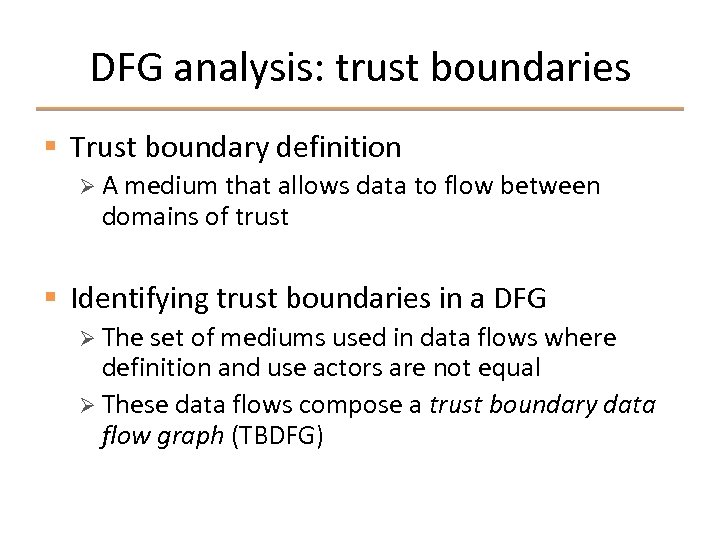
DFG analysis: trust boundaries § Trust boundary definition Ø A medium that allows data to flow between domains of trust § Identifying trust boundaries in a DFG Ø The set of mediums used in data flows where definition and use actors are not equal Ø These data flows compose a trust boundary data flow graph (TBDFG)
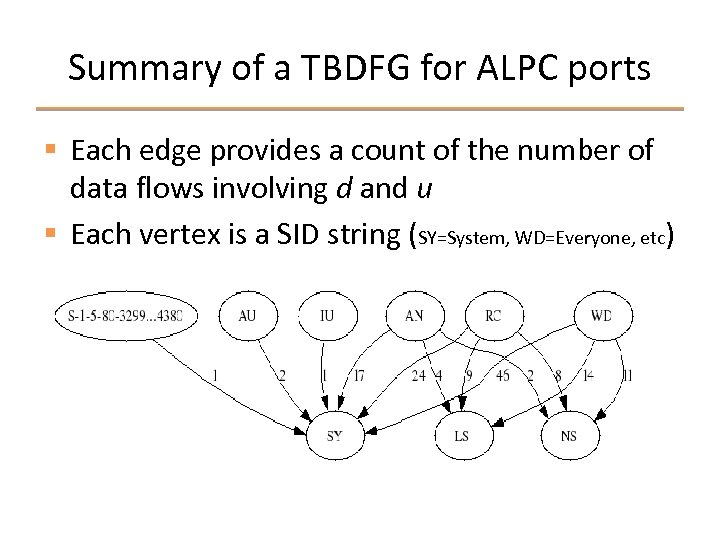
Summary of a TBDFG for ALPC ports § Each edge provides a count of the number of data flows involving d and u § Each vertex is a SID string (SY=System, WD=Everyone, etc)
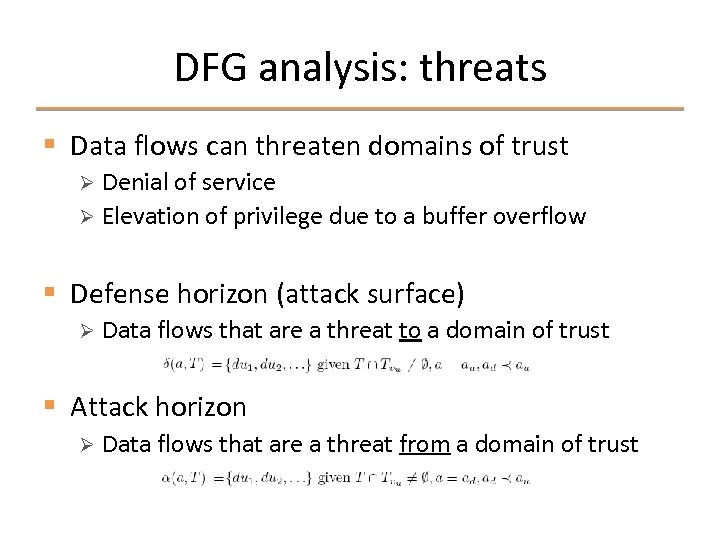
DFG analysis: threats § Data flows can threaten domains of trust Denial of service Ø Elevation of privilege due to a buffer overflow Ø § Defense horizon (attack surface) Ø Data flows that are a threat to a domain of trust § Attack horizon Ø Data flows that are a threat from a domain of trust
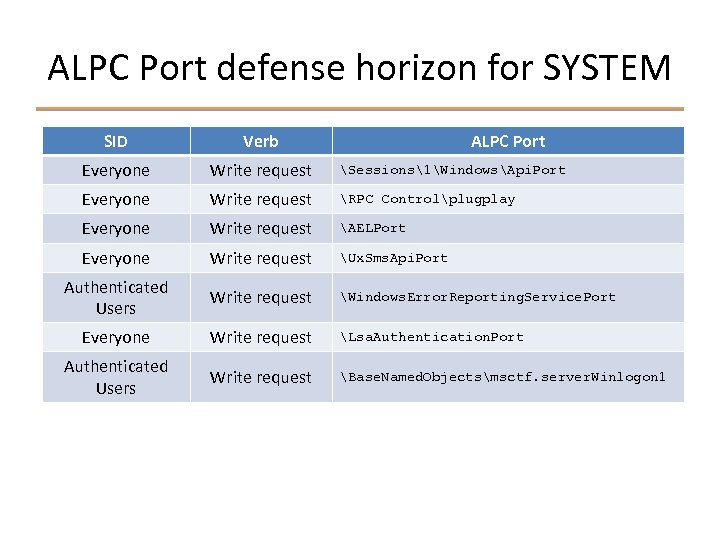
ALPC Port defense horizon for SYSTEM SID Verb ALPC Port Everyone Write request Sessions1WindowsApi. Port Everyone Write request RPC Controlplugplay Everyone Write request AELPort Everyone Write request Ux. Sms. Api. Port Authenticated Users Write request Windows. Error. Reporting. Service. Port Everyone Write request Lsa. Authentication. Port Authenticated Users Write request Base. Named. Objectsmsctf. server. Winlogon 1
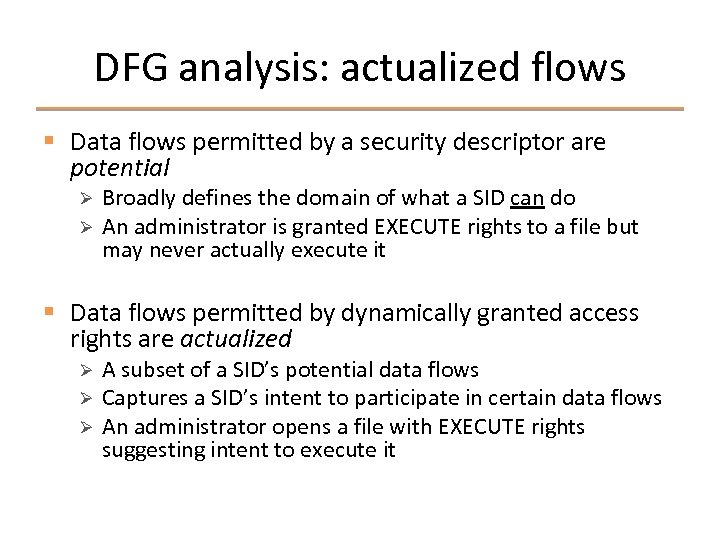
DFG analysis: actualized flows § Data flows permitted by a security descriptor are potential Ø Ø Broadly defines the domain of what a SID can do An administrator is granted EXECUTE rights to a file but may never actually execute it § Data flows permitted by dynamically granted access rights are actualized Ø Ø Ø A subset of a SID’s potential data flows Captures a SID’s intent to participate in certain data flows An administrator opens a file with EXECUTE rights suggesting intent to execute it
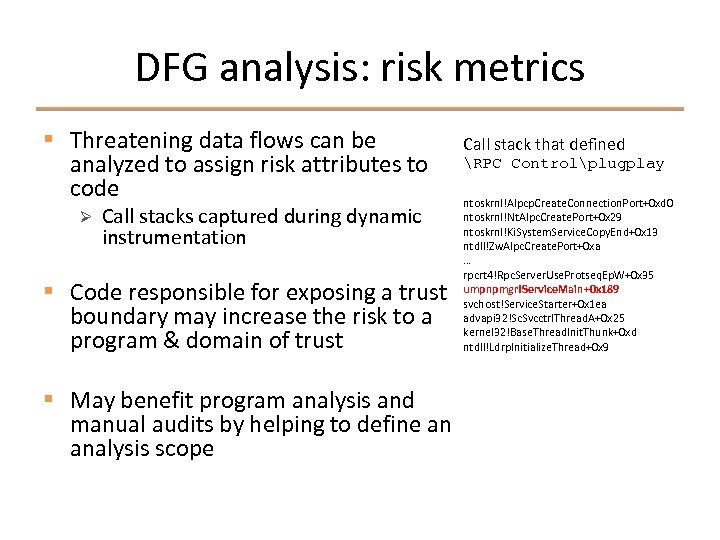
DFG analysis: risk metrics § Threatening data flows can be analyzed to assign risk attributes to code Ø Call stacks captured during dynamic instrumentation § Code responsible for exposing a trust boundary may increase the risk to a program & domain of trust § May benefit program analysis and manual audits by helping to define an analysis scope Call stack that defined RPC Controlplugplay ntoskrnl!Alpcp. Create. Connection. Port+0 xd 0 ntoskrnl!Nt. Alpc. Create. Port+0 x 29 ntoskrnl!Ki. System. Service. Copy. End+0 x 13 ntdll!Zw. Alpc. Create. Port+0 xa … rpcrt 4!Rpc. Server. Use. Protseq. Ep. W+0 x 35 umpnpmgr!Service. Main+0 x 189 svchost!Service. Starter+0 x 1 ea advapi 32!Sc. Svcctrl. Thread. A+0 x 25 kernel 32!Base. Thread. Init. Thunk+0 xd ntdll!Ldrp. Initialize. Thread+0 x 9
Offensive applications § Identify potential privilege elevation paths Ø Quickly identify code that should be audited Ø Includes privilege inversions (administrator using a user-defined object) § Identify weak ACLs & race conditions Ø NULL DACLs Ø Insecure use of WRITE_DAC
Defensive applications § Same as offensive applications § Harden object ACLs Ø Minimize defense horizon for TCB Ø Defense in depth § Support the verification of threat model conformance Ø Reflexion models & other specifications
Limitations & future work § Limitations Dynamic instrumentation limits visibility Ø Driver currently only compatible with Vista/Srv 08 x 64 Ø Model only describes how data can flow, not does flow Ø § Future work Pursue a larger case study to evaluate the effectiveness of this model Ø Investigate automated techniques for other trust boundaries (networking, system calls, etc) Ø
Conclusion § Trust boundaries must be identified to understand a program’s risks Ø Trust boundaries expose vulnerabilities § Access rights granted to securable objects allow data to flow between domains of trust § Dynamic instrumentation & a data flow model can help to understand the trust boundaries, threats, and potential elevation paths
Thanks for attending Questions?
13f2c478c5673253a7b40c532701a7b2.ppt