d735aac28325ae951c708537a4eccf9a.ppt
- Количество слайдов: 30
 Mod. Security "The Core Rule Set": Generic detection of application layer attacks 6 th OWASP App. Sec Conference Milan - May 2007 Ofer Shezaf, OWASP Israel Chapter Leader Chief Technology Officer, Breach Security ofers@breach. com +972 -54 -4431119 Copyright © 2007 - The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the Creative Commons Attribution-Share. Alike 2. 5 License. To view this license, visit http: //creativecommons. org/licenses/by-sa/2. 5/ The OWASP Foundation http: //www. owasp. org/
Mod. Security "The Core Rule Set": Generic detection of application layer attacks 6 th OWASP App. Sec Conference Milan - May 2007 Ofer Shezaf, OWASP Israel Chapter Leader Chief Technology Officer, Breach Security ofers@breach. com +972 -54 -4431119 Copyright © 2007 - The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the Creative Commons Attribution-Share. Alike 2. 5 License. To view this license, visit http: //creativecommons. org/licenses/by-sa/2. 5/ The OWASP Foundation http: //www. owasp. org/
 About The Speaker
About The Speaker
 What are we going to talk about
What are we going to talk about
 "The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com About Application Firewalls The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
"The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com About Application Firewalls The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
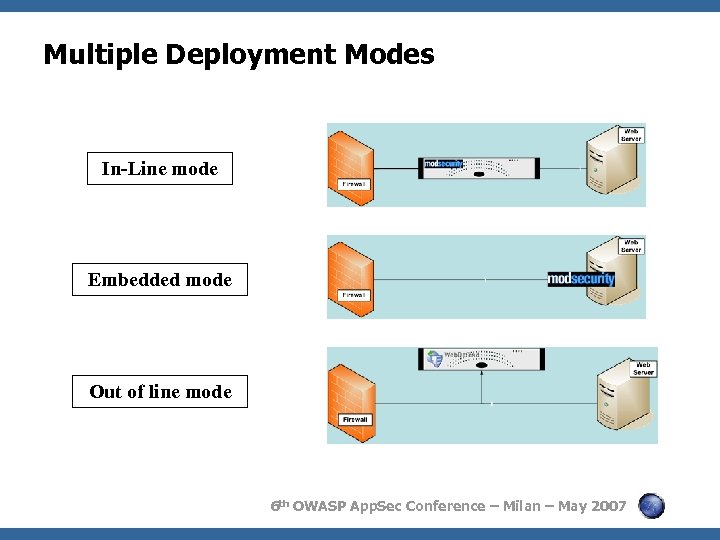 Multiple Deployment Modes In-Line mode Embedded mode Out of line mode 6 th OWASP App. Sec Conference – Milan – May 2007
Multiple Deployment Modes In-Line mode Embedded mode Out of line mode 6 th OWASP App. Sec Conference – Milan – May 2007
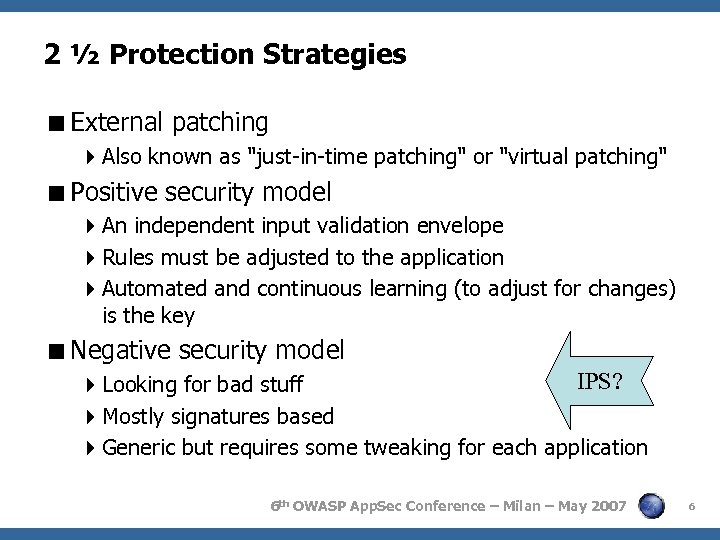 2 ½ Protection Strategies
2 ½ Protection Strategies
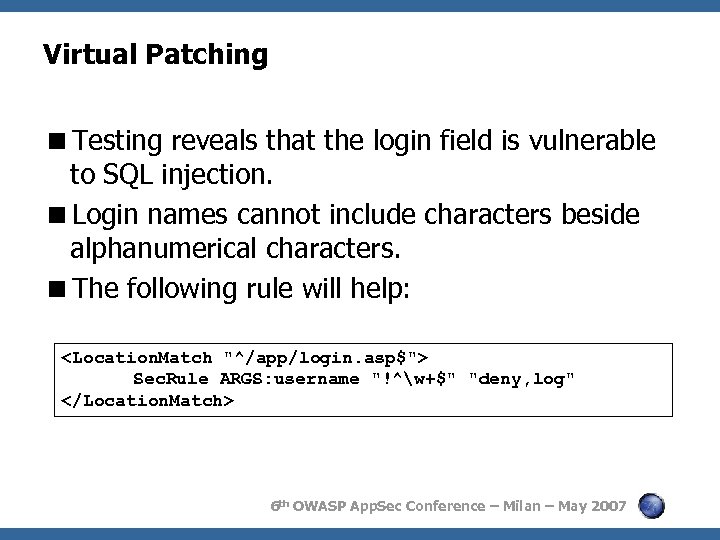 Virtual Patching
Virtual Patching
Sec. Default. Action "log, deny, t: lowercase" Sec." src="https://present5.com/presentation/d735aac28325ae951c708537a4eccf9a/image-8.jpg" alt="Positive Security
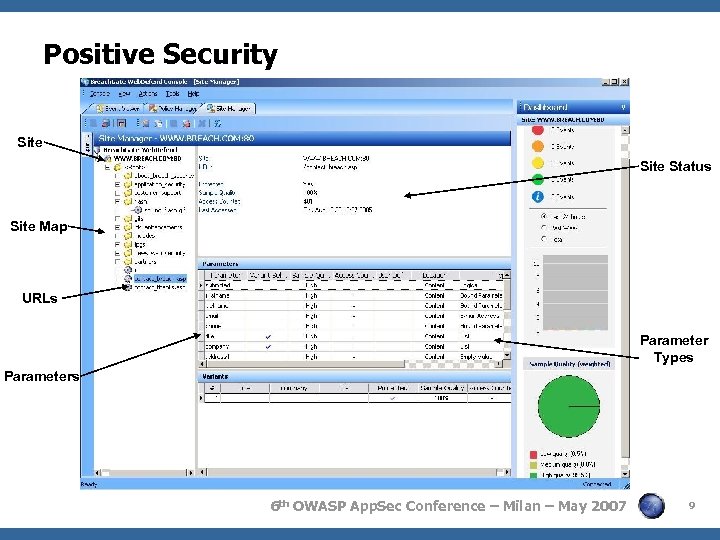 Positive Security Site Status Site Map URLs Parameter Types Parameters 6 th OWASP App. Sec Conference – Milan – May 2007 9
Positive Security Site Status Site Map URLs Parameter Types Parameters 6 th OWASP App. Sec Conference – Milan – May 2007 9
 "The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com Web Application Firewalls vs. Intrusion Prevention Systems The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
"The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com Web Application Firewalls vs. Intrusion Prevention Systems The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
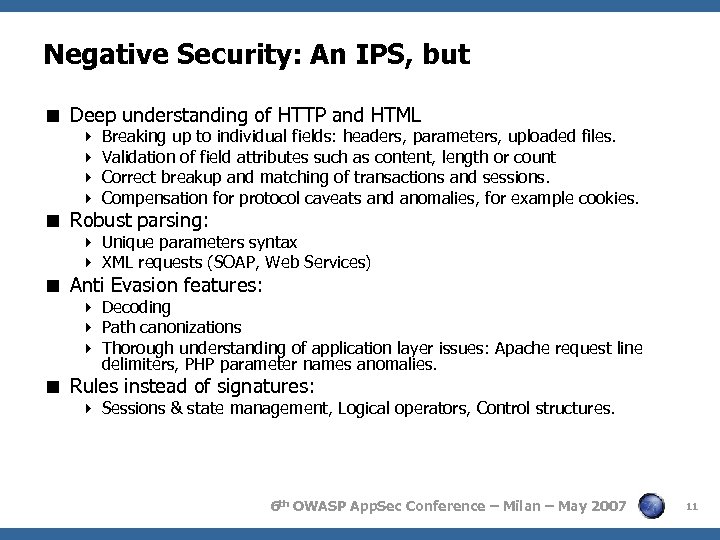 Negative Security: An IPS, but < Deep understanding of HTTP and HTML 4 Breaking up to individual fields: headers, parameters, uploaded files. 4 Validation of field attributes such as content, length or count 4 Correct breakup and matching of transactions and sessions. 4 Compensation for protocol caveats and anomalies, for example cookies. < Robust parsing: 4 Unique parameters syntax 4 XML requests (SOAP, Web Services) < Anti Evasion features: 4 Decoding 4 Path canonizations 4 Thorough understanding of application layer issues: Apache request line delimiters, PHP parameter names anomalies. < Rules instead of signatures: 4 Sessions & state management, Logical operators, Control structures. 6 th OWASP App. Sec Conference – Milan – May 2007 11
Negative Security: An IPS, but < Deep understanding of HTTP and HTML 4 Breaking up to individual fields: headers, parameters, uploaded files. 4 Validation of field attributes such as content, length or count 4 Correct breakup and matching of transactions and sessions. 4 Compensation for protocol caveats and anomalies, for example cookies. < Robust parsing: 4 Unique parameters syntax 4 XML requests (SOAP, Web Services) < Anti Evasion features: 4 Decoding 4 Path canonizations 4 Thorough understanding of application layer issues: Apache request line delimiters, PHP parameter names anomalies. < Rules instead of signatures: 4 Sessions & state management, Logical operators, Control structures. 6 th OWASP App. Sec Conference – Milan – May 2007 11
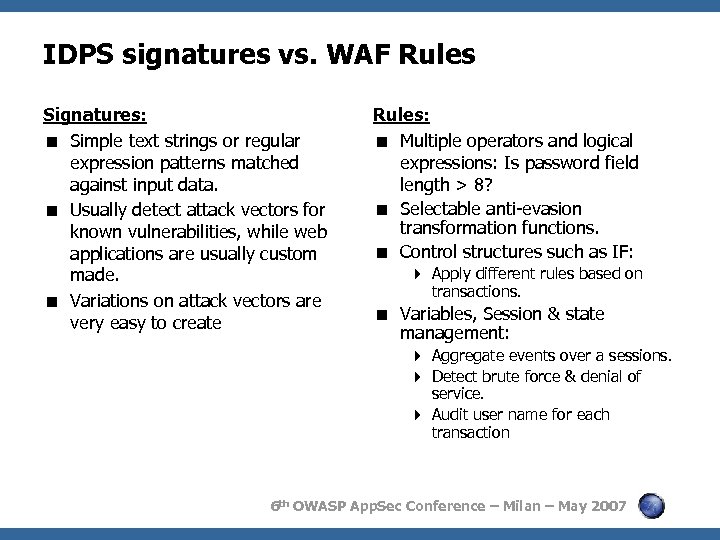 IDPS signatures vs. WAF Rules Signatures: < Simple text strings or regular expression patterns matched against input data. < Usually detect attack vectors for known vulnerabilities, while web applications are usually custom made. < Variations on attack vectors are very easy to create Rules: < Multiple operators and logical expressions: Is password field length > 8? < Selectable anti-evasion transformation functions. < Control structures such as IF: 4 Apply different rules based on transactions. < Variables, Session & state management: 4 Aggregate events over a sessions. 4 Detect brute force & denial of service. 4 Audit user name for each transaction 6 th OWASP App. Sec Conference – Milan – May 2007
IDPS signatures vs. WAF Rules Signatures: < Simple text strings or regular expression patterns matched against input data. < Usually detect attack vectors for known vulnerabilities, while web applications are usually custom made. < Variations on attack vectors are very easy to create Rules: < Multiple operators and logical expressions: Is password field length > 8? < Selectable anti-evasion transformation functions. < Control structures such as IF: 4 Apply different rules based on transactions. < Variables, Session & state management: 4 Aggregate events over a sessions. 4 Detect brute force & denial of service. 4 Audit user name for each transaction 6 th OWASP App. Sec Conference – Milan – May 2007
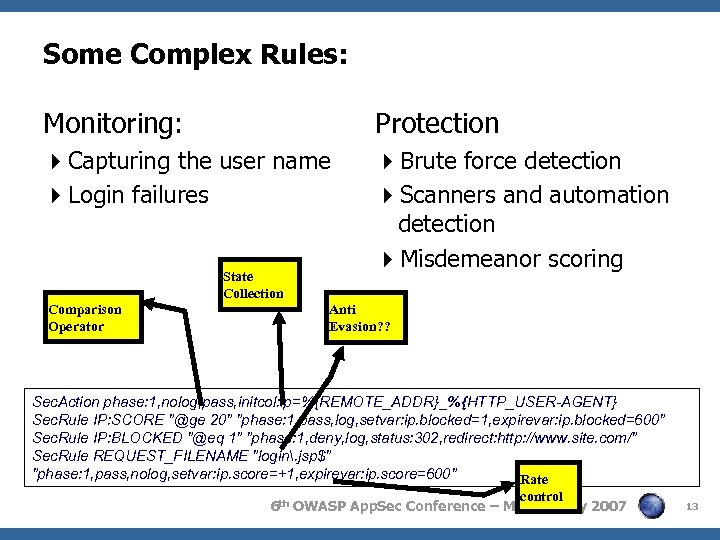 Some Complex Rules: Monitoring: Protection 4 Capturing the user name 4 Login failures 4 Brute force detection 4 Scanners and automation detection 4 Misdemeanor scoring State Collection Comparison Operator Anti Evasion? ? Sec. Action phase: 1, nolog, pass, initcol: ip=%{REMOTE_ADDR}_%{HTTP_USER-AGENT} Sec. Rule IP: SCORE "@ge 20" "phase: 1, pass, log, setvar: ip. blocked=1, expirevar: ip. blocked=600" Sec. Rule IP: BLOCKED "@eq 1" "phase: 1, deny, log, status: 302, redirect: http: //www. site. com/" Sec. Rule REQUEST_FILENAME "login. jsp$" "phase: 1, pass, nolog, setvar: ip. score=+1, expirevar: ip. score=600" Rate control 6 th OWASP App. Sec Conference – Milan – May 2007 13
Some Complex Rules: Monitoring: Protection 4 Capturing the user name 4 Login failures 4 Brute force detection 4 Scanners and automation detection 4 Misdemeanor scoring State Collection Comparison Operator Anti Evasion? ? Sec. Action phase: 1, nolog, pass, initcol: ip=%{REMOTE_ADDR}_%{HTTP_USER-AGENT} Sec. Rule IP: SCORE "@ge 20" "phase: 1, pass, log, setvar: ip. blocked=1, expirevar: ip. blocked=600" Sec. Rule IP: BLOCKED "@eq 1" "phase: 1, deny, log, status: 302, redirect: http: //www. site. com/" Sec. Rule REQUEST_FILENAME "login. jsp$" "phase: 1, pass, nolog, setvar: ip. score=+1, expirevar: ip. score=600" Rate control 6 th OWASP App. Sec Conference – Milan – May 2007 13
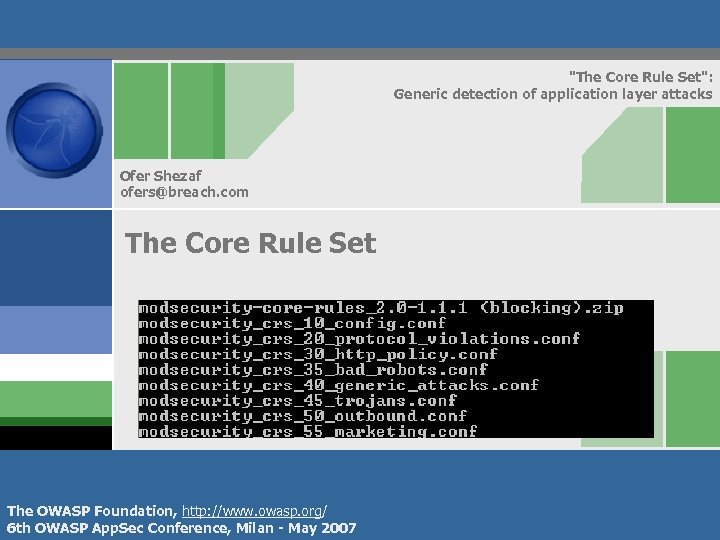 "The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com The Core Rule Set The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
"The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com The Core Rule Set The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
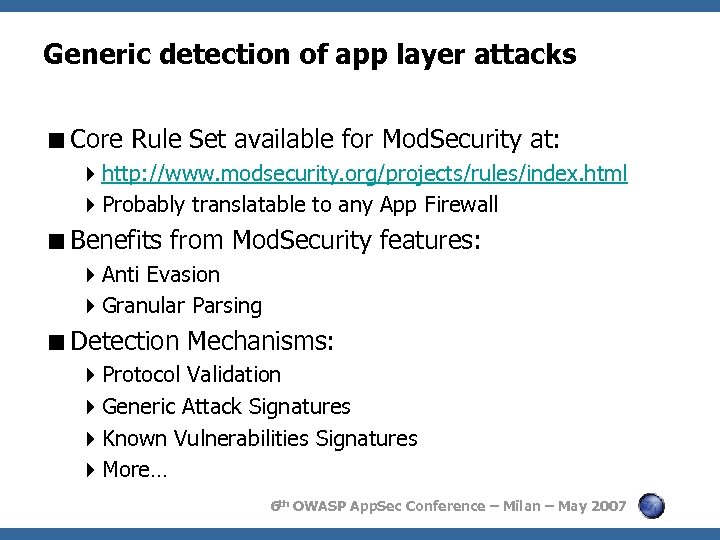 Generic detection of app layer attacks
Generic detection of app layer attacks
 "The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com Protocol Validation The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
"The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com Protocol Validation The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
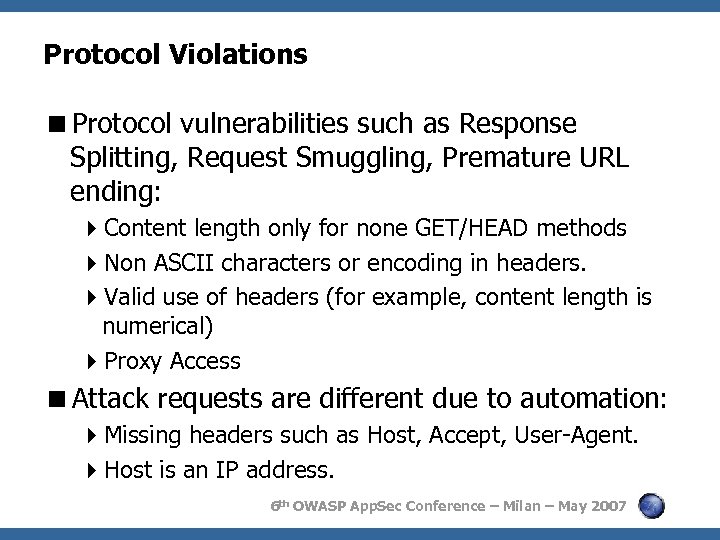 Protocol Violations
Protocol Violations
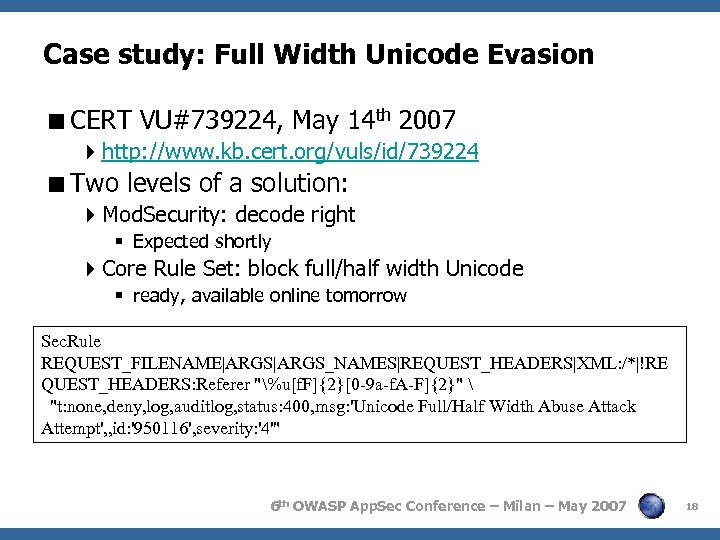 Case study: Full Width Unicode Evasion
Case study: Full Width Unicode Evasion
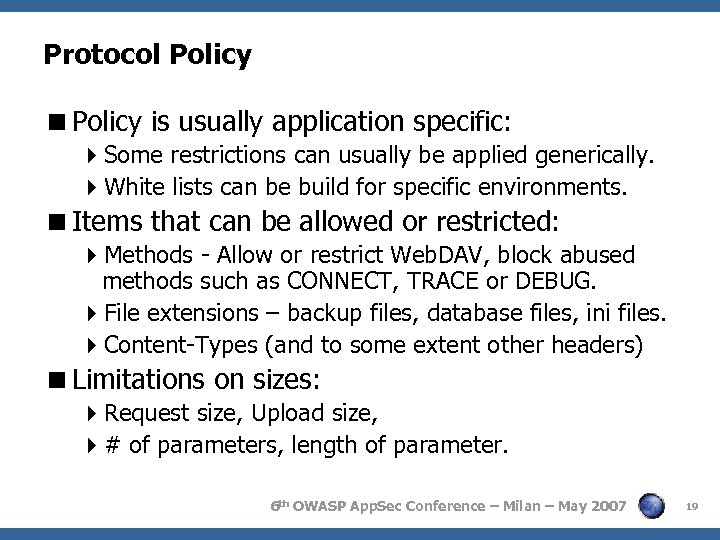 Protocol Policy
Protocol Policy
 "The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com Application Layer Signatures The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
"The Core Rule Set": Generic detection of application layer attacks Ofer Shezaf ofers@breach. com Application Layer Signatures The OWASP Foundation, http: //www. owasp. org/ 6 th OWASP App. Sec Conference, Milan - May 2007
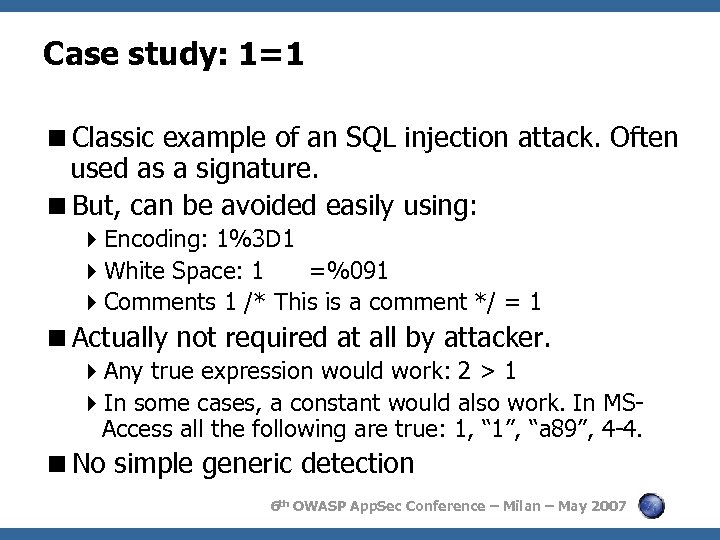 Case study: 1=1
Case study: 1=1
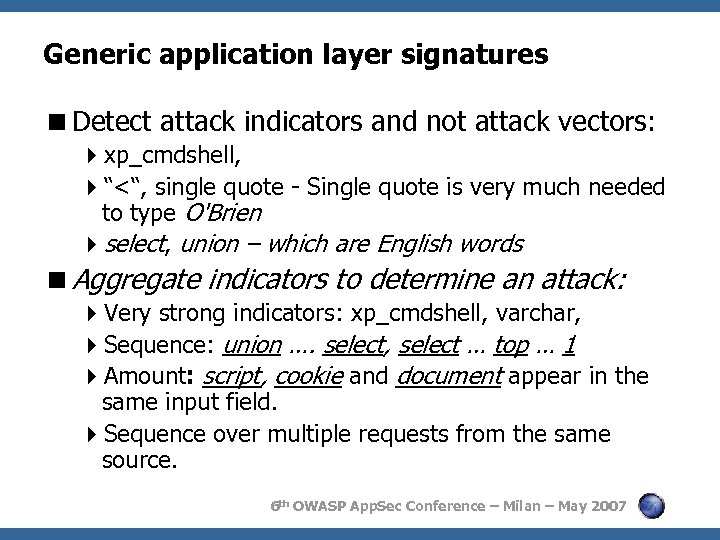 Generic application layer signatures
Generic application layer signatures
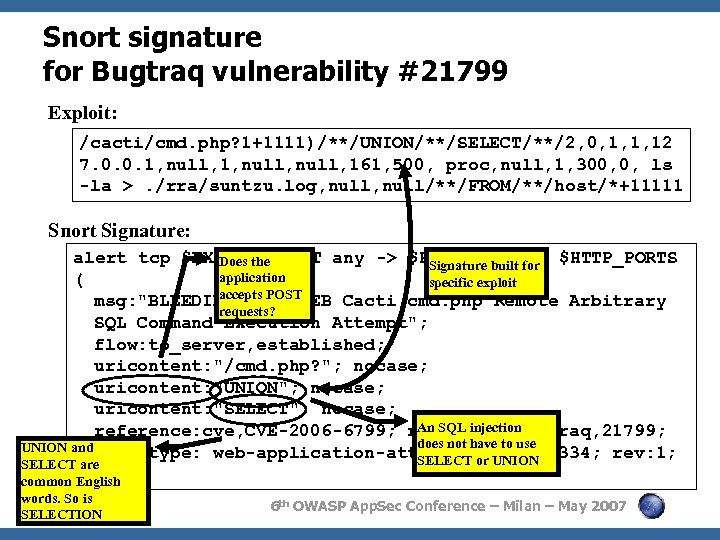 Snort signature for Bugtraq vulnerability #21799 Exploit: /cacti/cmd. php? 1+1111)/**/UNION/**/SELECT/**/2, 0, 1, 1, 12 7. 0. 0. 1, null, 161, 500, proc, null, 1, 300, 0, ls -la >. /rra/suntzu. log, null/**/FROM/**/host/*+11111 Snort Signature: alert tcp $EXTERNAL_NET any -> $HTTP_SERVERS $HTTP_PORTS Does the Signature built for application ( specific exploit accepts POST msg: "BLEEDING-EDGE WEB Cacti cmd. php Remote Arbitrary requests? SQL Command Execution Attempt"; flow: to_server, established; uricontent: "/cmd. php? "; nocase; uricontent: "UNION"; nocase; uricontent: "SELECT"; nocase; An SQL injection reference: cve, CVE-2006 -6799; reference: bugtraq, 21799; does not UNION and classtype: web-application-attack; have to use sid: 2003334; rev: 1; SELECT or UNION SELECT are common ) English words. So is SELECTION 6 th OWASP App. Sec Conference – Milan – May 2007
Snort signature for Bugtraq vulnerability #21799 Exploit: /cacti/cmd. php? 1+1111)/**/UNION/**/SELECT/**/2, 0, 1, 1, 12 7. 0. 0. 1, null, 161, 500, proc, null, 1, 300, 0, ls -la >. /rra/suntzu. log, null/**/FROM/**/host/*+11111 Snort Signature: alert tcp $EXTERNAL_NET any -> $HTTP_SERVERS $HTTP_PORTS Does the Signature built for application ( specific exploit accepts POST msg: "BLEEDING-EDGE WEB Cacti cmd. php Remote Arbitrary requests? SQL Command Execution Attempt"; flow: to_server, established; uricontent: "/cmd. php? "; nocase; uricontent: "UNION"; nocase; uricontent: "SELECT"; nocase; An SQL injection reference: cve, CVE-2006 -6799; reference: bugtraq, 21799; does not UNION and classtype: web-application-attack; have to use sid: 2003334; rev: 1; SELECT or UNION SELECT are common ) English words. So is SELECTION 6 th OWASP App. Sec Conference – Milan – May 2007
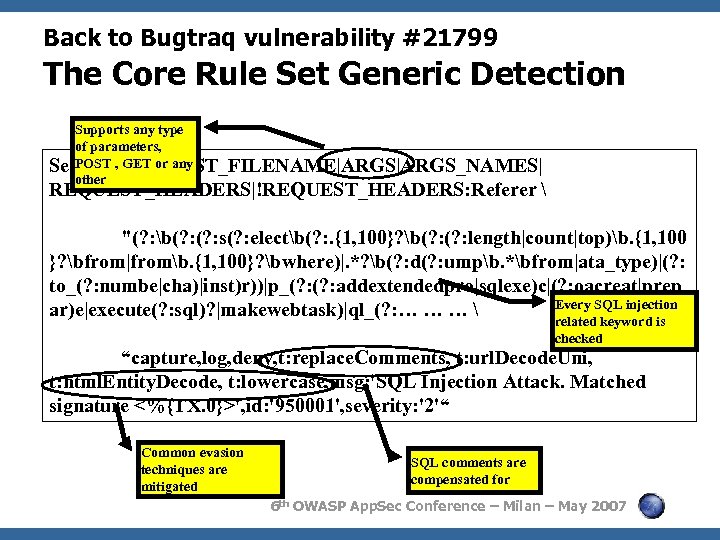 Back to Bugtraq vulnerability #21799 The Core Rule Set Generic Detection Supports any type of parameters, POST REQUEST_FILENAME|ARGS_NAMES| Sec. Rule, GET or any other REQUEST_HEADERS|!REQUEST_HEADERS: Referer "(? : b(? : s(? : electb(? : . {1, 100}? b(? : length|count|top)b. {1, 100 }? bfrom|fromb. {1, 100}? bwhere)|. *? b(? : d(? : umpb. *bfrom|ata_type)|(? : to_(? : numbe|cha)|inst)r))|p_(? : addextendedpro|sqlexe)c|(? : oacreat|prep Every SQL injection ar)e|execute(? : sql)? |makewebtask)|ql_(? : … … … related keyword is checked “capture, log, deny, t: replace. Comments, t: url. Decode. Uni, t: html. Entity. Decode, t: lowercase, msg: 'SQL Injection Attack. Matched signature <%{TX. 0}>', id: '950001', severity: '2'“ Common evasion techniques are mitigated SQL comments are compensated for 6 th OWASP App. Sec Conference – Milan – May 2007
Back to Bugtraq vulnerability #21799 The Core Rule Set Generic Detection Supports any type of parameters, POST REQUEST_FILENAME|ARGS_NAMES| Sec. Rule, GET or any other REQUEST_HEADERS|!REQUEST_HEADERS: Referer "(? : b(? : s(? : electb(? : . {1, 100}? b(? : length|count|top)b. {1, 100 }? bfrom|fromb. {1, 100}? bwhere)|. *? b(? : d(? : umpb. *bfrom|ata_type)|(? : to_(? : numbe|cha)|inst)r))|p_(? : addextendedpro|sqlexe)c|(? : oacreat|prep Every SQL injection ar)e|execute(? : sql)? |makewebtask)|ql_(? : … … … related keyword is checked “capture, log, deny, t: replace. Comments, t: url. Decode. Uni, t: html. Entity. Decode, t: lowercase, msg: 'SQL Injection Attack. Matched signature <%{TX. 0}>', id: '950001', severity: '2'“ Common evasion techniques are mitigated SQL comments are compensated for 6 th OWASP App. Sec Conference – Milan – May 2007
Sec. Rule" src="https://present5.com/presentation/d735aac28325ae951c708537a4eccf9a/image-25.jpg" alt="Back to Bugtraq vulnerability #21799 Virtual Patching
 Odds and Ends 6 th OWASP App. Sec Conference Milan - May 2007 Copyright © 2007 - The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the Creative Commons Attribution-Share. Alike 2. 5 License. To view this license, visit http: //creativecommons. org/licenses/by-sa/2. 5/ The OWASP Foundation http: //www. owasp. org/
Odds and Ends 6 th OWASP App. Sec Conference Milan - May 2007 Copyright © 2007 - The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the Creative Commons Attribution-Share. Alike 2. 5 License. To view this license, visit http: //creativecommons. org/licenses/by-sa/2. 5/ The OWASP Foundation http: //www. owasp. org/
 Malicious Robots < Detection of malicious robots: 4 Unique request attributes: User-Agent header, URL, Headers 4 Black list of IP addresses 4 Rate based detection < Not aimed against targeted attacks, but against general malicious internet activity: 4 Offloads a lot of cyberspace junk & noise 4 Effective against comment spam. 4 Reduce event count. < In addition: 4 Detection of security scanners 4 Detection of non malicious robots (such as search engines). 4 Confusing security testing software (HTTPrint) 6 th OWASP App. Sec Conference – Milan – May 2007 27
Malicious Robots < Detection of malicious robots: 4 Unique request attributes: User-Agent header, URL, Headers 4 Black list of IP addresses 4 Rate based detection < Not aimed against targeted attacks, but against general malicious internet activity: 4 Offloads a lot of cyberspace junk & noise 4 Effective against comment spam. 4 Reduce event count. < In addition: 4 Detection of security scanners 4 Detection of non malicious robots (such as search engines). 4 Confusing security testing software (HTTPrint) 6 th OWASP App. Sec Conference – Milan – May 2007 27
 Trojans and Viruses
Trojans and Viruses
 Error conditions
Error conditions
 Thank You! Ofer Shezaf ofers@breach. com 6 th OWASP App. Sec Conference Milan - May 2007 Copyright © 2007 - The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the Creative Commons Attribution-Share. Alike 2. 5 License. To view this license, visit http: //creativecommons. org/licenses/by-sa/2. 5/ The OWASP Foundation http: //www. owasp. org/
Thank You! Ofer Shezaf ofers@breach. com 6 th OWASP App. Sec Conference Milan - May 2007 Copyright © 2007 - The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the Creative Commons Attribution-Share. Alike 2. 5 License. To view this license, visit http: //creativecommons. org/licenses/by-sa/2. 5/ The OWASP Foundation http: //www. owasp. org/


