c1f5c31b398c5abb672cd8e85e5e529b.ppt
- Количество слайдов: 27
Mobile ad hoc networking: imperatives and challenges
Agendas Wireless networks Ad hoc networks Mobile ad hoc networks (MANET) MANET applications Enabling technologies Security issues Conclusions Questions
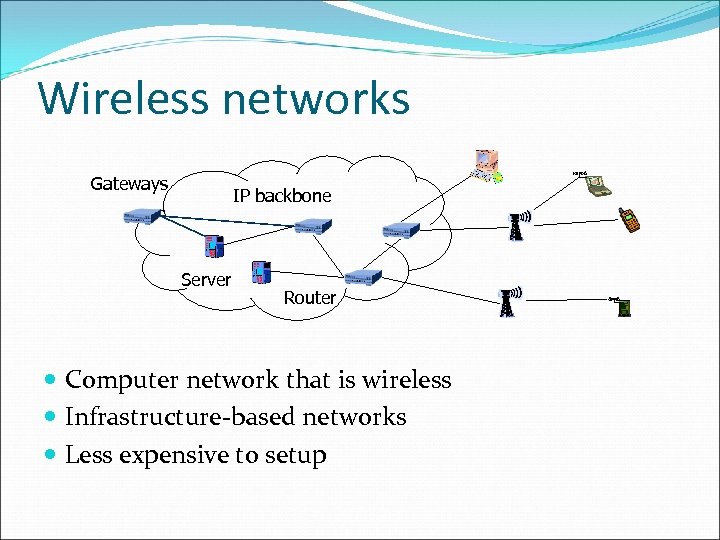
Wireless networks Gateways IP backbone Server Router Computer network that is wireless Infrastructure-based networks Less expensive to setup
Disadvantages Disaster areas no infrastructure Large construction sites Too expensive Inconvenient Military operations Less time to setup
Solution? ? ? Mobile ad hoc network (MANET), or simply ad hoc network, comprises nodes that freely and dynamically self-organize into arbitrary and temporary network topology without any infrastructure support. (Chlamtac, Conti, and Liu, 2003)
MANET Formed by wireless hosts Without using pre-installed infrastructure Routes between hops may contain multiple hops Does not use centralized administration MANETs are often referred to as multihop wireless and hoc networks
Key Elements of MANETs Formed dynamically through independent nodes Nodes do not have any pre-specified nodes Make decision based on the current network situation Nodes are expected to behave as routers As routers, nodes must assist in discovery and maintenance of network routes
MANET applications Tactical Networks Military communication, operation Automated Battlefields Sensor Networks Home applications: allow users to manage home device locally and remotely Environment applications: tracking the movements of animals
MANET applications (continued) Emergency Services Replacement of a fixed infrastructure in case of earthquake, hurricanes Home and Enterprise Networking Shared whiteboard applications Use PDA to print anywhere Entertainment Multi-user games Robotic pets
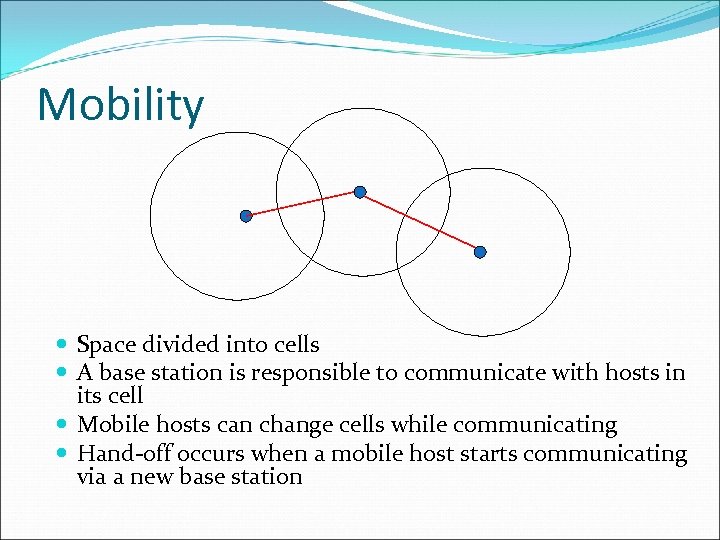
Mobility Space divided into cells A base station is responsible to communicate with hosts in its cell Mobile hosts can change cells while communicating Hand-off occurs when a mobile host starts communicating via a new base station
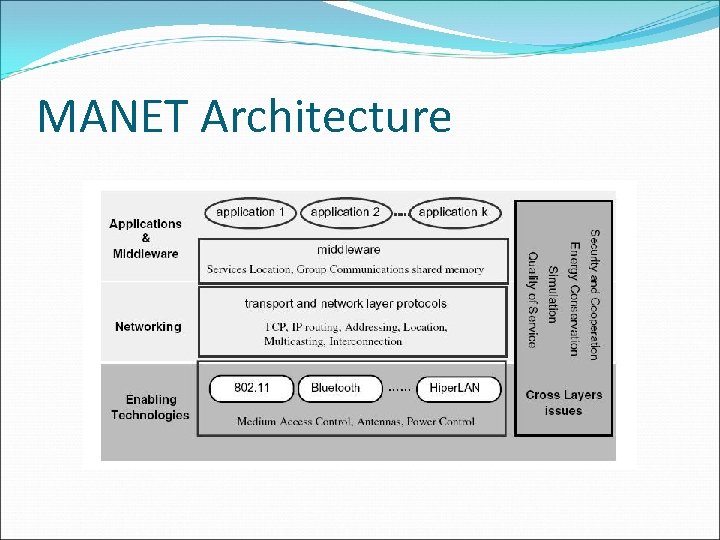
MANET Architecture
MANET Research activities Based on its architecture, research activities are grouped into three main areas Enabling technologies Networking Middleware and application
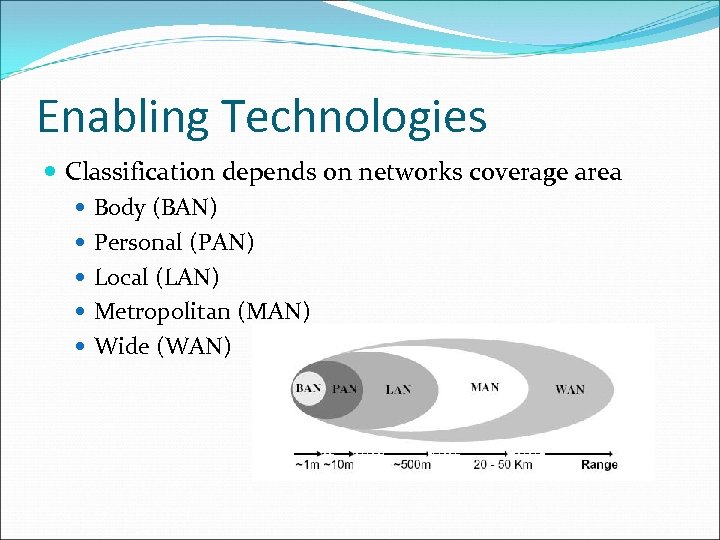
Enabling Technologies Classification depends on networks coverage area Body (BAN) Personal (PAN) Local (LAN) Metropolitan (MAN) Wide (WAN)
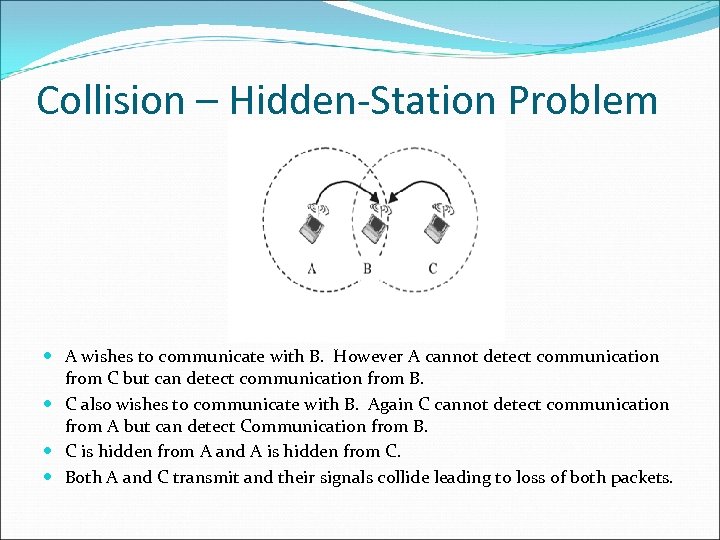
Collision – Hidden-Station Problem A wishes to communicate with B. However A cannot detect communication from C but can detect communication from B. C also wishes to communicate with B. Again C cannot detect communication from A but can detect Communication from B. C is hidden from A and A is hidden from C. Both A and C transmit and their signals collide leading to loss of both packets.
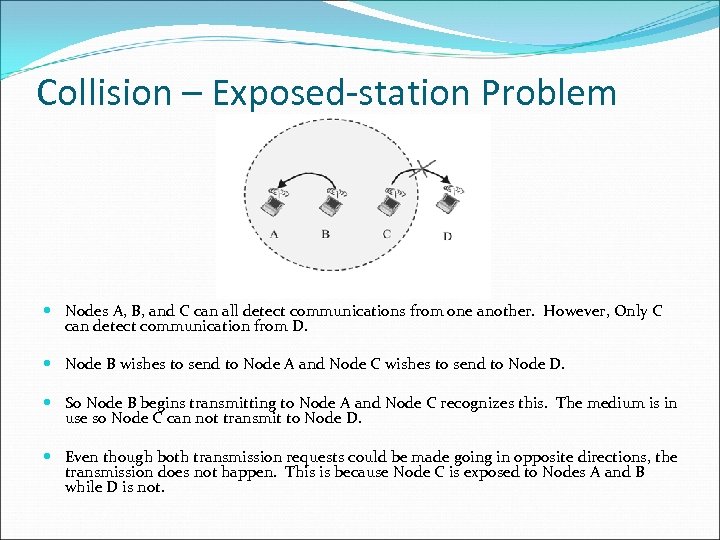
Collision – Exposed-station Problem Nodes A, B, and C can all detect communications from one another. However, Only C can detect communication from D. Node B wishes to send to Node A and Node C wishes to send to Node D. So Node B begins transmitting to Node A and Node C recognizes this. The medium is in use so Node C can not transmit to Node D. Even though both transmission requests could be made going in opposite directions, the transmission does not happen. This is because Node C is exposed to Nodes A and B while D is not.
Research issues Energy conservation Network security and cooperation Simulation and performance evaluation Quality of service
Energy conservation Battery power is finite Limits services and applications that the network can support Solution Topology management – goal is to reduce overall network power consumption Routing protocols – minimize routing paths
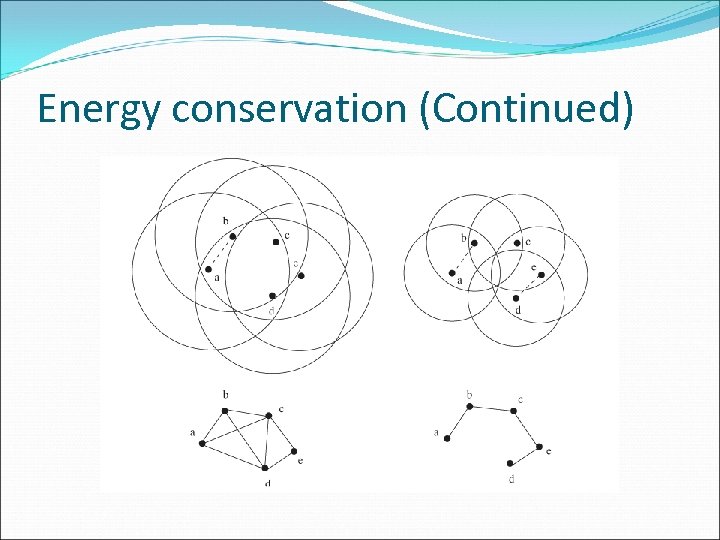
Energy conservation (Continued)
Network Security - MANET Physically insecure network Network security requirements Confidentiality Authentication Integrity Non-repudiation Availability
Eavesdropping A B C Who has a radio receiver Same frequency used by the ad hoc network Man-in-the-middle attack
Impersonation - Security Attacks Nodes join to the network undetectably Black hole attack Malicious node uses the same routing protocol Advertise itself as having the shortest path Worm hole attack Create a tunnel(wormhole link) between two malicious nodes Captures wireless transmission from one end Sends them to the other end through that tunnel
Denial of Service - Security Attacks Attempts to create routes to non-existent node The attacker attempts to consume batteries of other nodes by requesting routes Forwards unnecessary packets Causes a system to be unavailability A violation of security policy
Disclosure Attack - Security Attacks Reveal the physical location of nodes Reveal the structure of the network Two security mechanisms are applied Preventive Detective Mechanisms are based on key-based cryptography Secret keys are distributed through a secure channel Public keys are distributed through certificates
Quality of Service - MANET Capability of network to provide better service Controls jitter and latency Manages and minimizes network congestion Sharps network traffic Sets network traffic priorities
Conclusion MANETs is challenging and promising system concepts Requires new type of architectures and protocols Popular research topic Open areas Secure routing protocol Quality of service Low power consumption
Questions
References I Chlamtac, M Conti, JJN Liu, "Mobile ad hoc networking: imperatives and challenges. " Ad Hoc Networks, 1(1), pp. 13 -64, 2003. http: //cs. utsa. edu/faculty/boppana/6393/ www. ietf. org/html. charters/manet-charter. html http: //www. antd. nist. gov/wahn_mahn. shtml
c1f5c31b398c5abb672cd8e85e5e529b.ppt