0a7fac64979a914db63ed5c2b1d31c50.ppt
- Количество слайдов: 35
Metrics
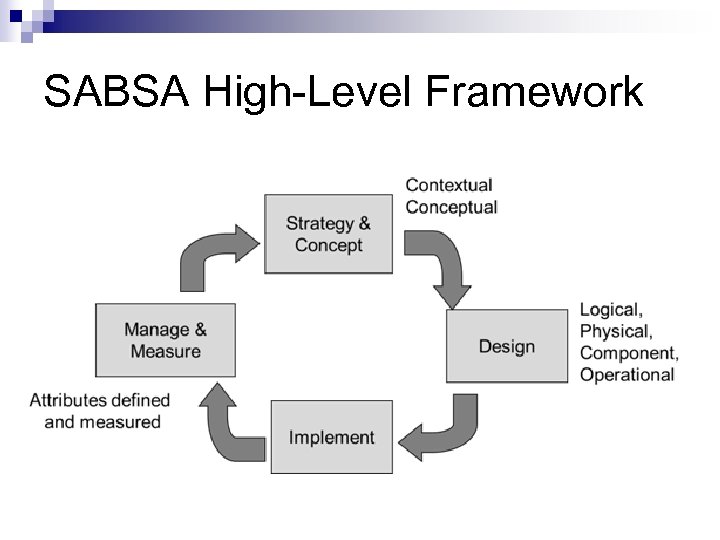
SABSA High-Level Framework
Gap Analysis The difference between where you are and where you want to be: n # malware infections/month n Rate of finding illegal software, hardware n Security awareness training averages
SEI/COBIT Level 4 Monitoring: Includes Metrics inform management (and independent auditors) of the effectiveness of the security program n Monitoring achievement of control objective may be more important than perfecting security procedures n
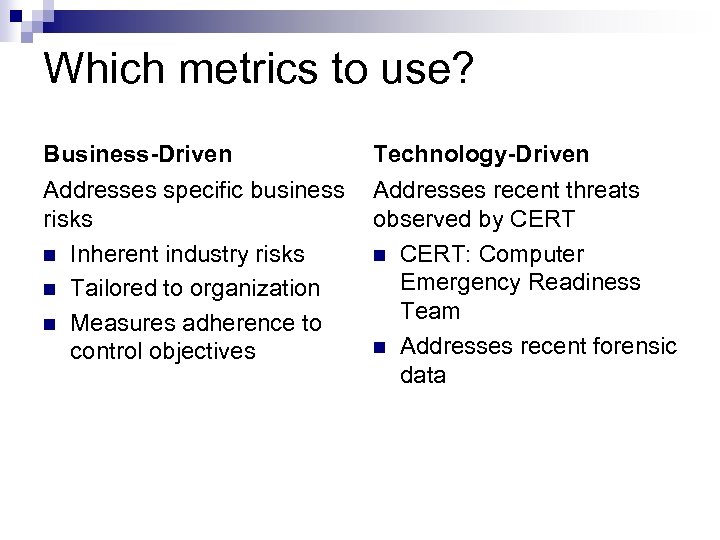
Which metrics to use? Business-Driven Technology-Driven Addresses specific business risks n Inherent industry risks n Tailored to organization n Measures adherence to control objectives Addresses recent threats observed by CERT n CERT: Computer Emergency Readiness Team n Addresses recent forensic data
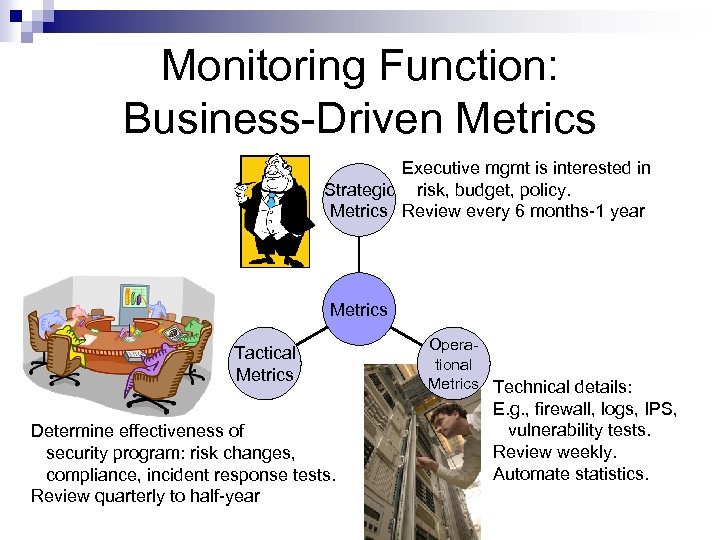
Monitoring Function: Business-Driven Metrics Executive mgmt is interested in Strategic risk, budget, policy. Metrics Review every 6 months-1 year Metrics Tactical Metrics Determine effectiveness of security program: risk changes, compliance, incident response tests. Review quarterly to half-year Operational Metrics Technical details: E. g. , firewall, logs, IPS, vulnerability tests. Review weekly. Automate statistics.
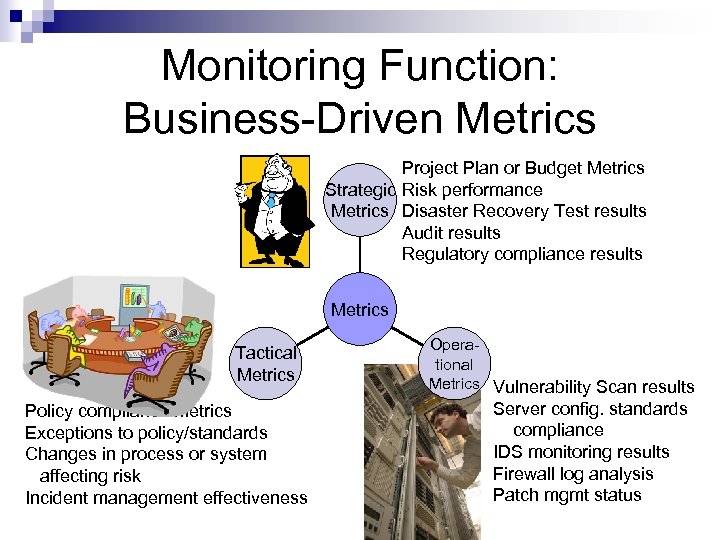
Monitoring Function: Business-Driven Metrics Project Plan or Budget Metrics Strategic Risk performance Metrics Disaster Recovery Test results Audit results Regulatory compliance results Metrics Tactical Metrics Policy compliance metrics Exceptions to policy/standards Changes in process or system affecting risk Incident management effectiveness Operational Metrics Vulnerability Scan results Server config. standards compliance IDS monitoring results Firewall log analysis Patch mgmt status
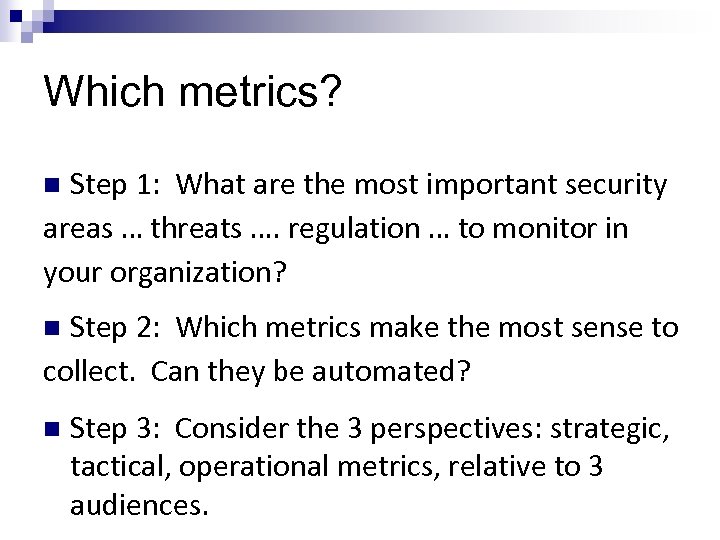
Which metrics? Step 1: What are the most important security areas … threats …. regulation … to monitor in your organization? n Step 2: Which metrics make the most sense to collect. Can they be automated? n n Step 3: Consider the 3 perspectives: strategic, tactical, operational metrics, relative to 3 audiences.
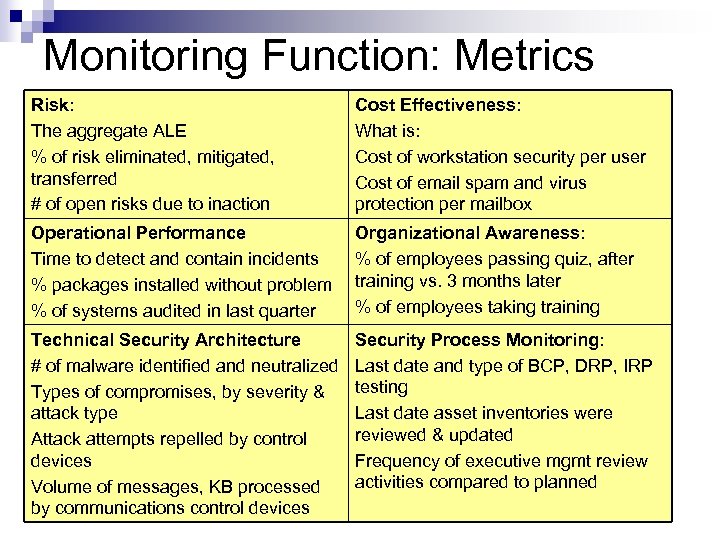
Monitoring Function: Metrics Risk: The aggregate ALE % of risk eliminated, mitigated, transferred # of open risks due to inaction Cost Effectiveness: What is: Cost of workstation security per user Cost of email spam and virus protection per mailbox Operational Performance Time to detect and contain incidents % packages installed without problem % of systems audited in last quarter Organizational Awareness: % of employees passing quiz, after training vs. 3 months later % of employees taking training Technical Security Architecture # of malware identified and neutralized Types of compromises, by severity & attack type Attack attempts repelled by control devices Volume of messages, KB processed by communications control devices Security Process Monitoring: Last date and type of BCP, DRP, IRP testing Last date asset inventories were reviewed & updated Frequency of executive mgmt review activities compared to planned
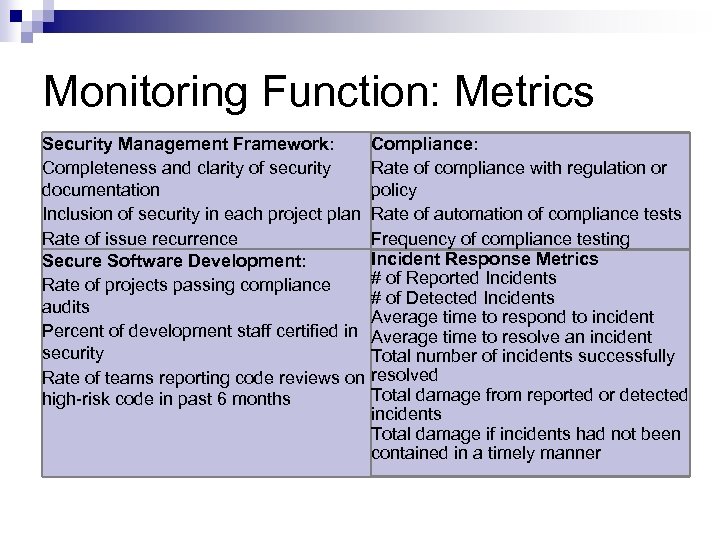
Monitoring Function: Metrics Security Management Framework: Completeness and clarity of security documentation Inclusion of security in each project plan Rate of issue recurrence Secure Software Development: Rate of projects passing compliance audits Percent of development staff certified in security Rate of teams reporting code reviews on high-risk code in past 6 months Compliance: Rate of compliance with regulation or policy Rate of automation of compliance tests Frequency of compliance testing Incident Response Metrics # of Reported Incidents # of Detected Incidents Average time to respond to incident Average time to resolve an incident Total number of incidents successfully resolved Total damage from reported or detected incidents Total damage if incidents had not been contained in a timely manner
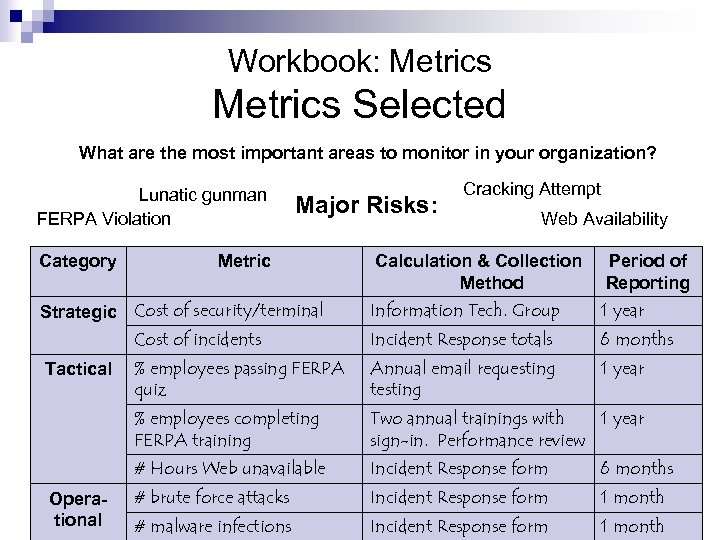
Workbook: Metrics Selected What are the most important areas to monitor in your organization? Lunatic gunman FERPA Violation Category Major Risks: Metric Cracking Attempt Web Availability Calculation & Collection Method Period of Reporting Information Tech. Group 1 year Cost of incidents Incident Response totals 6 months % employees passing FERPA quiz Annual email requesting testing 1 year % employees completing FERPA training Two annual trainings with 1 year sign-in. Performance review # Hours Web unavailable Incident Response form 6 months # brute force attacks Incident Response form 1 month # malware infections Incident Response form 1 month Strategic Cost of security/terminal Tactical Operational
SANS-Recommended Critical Controls for Effective Cyber Defense TECHNOLOGY-DRIVEN METRICS
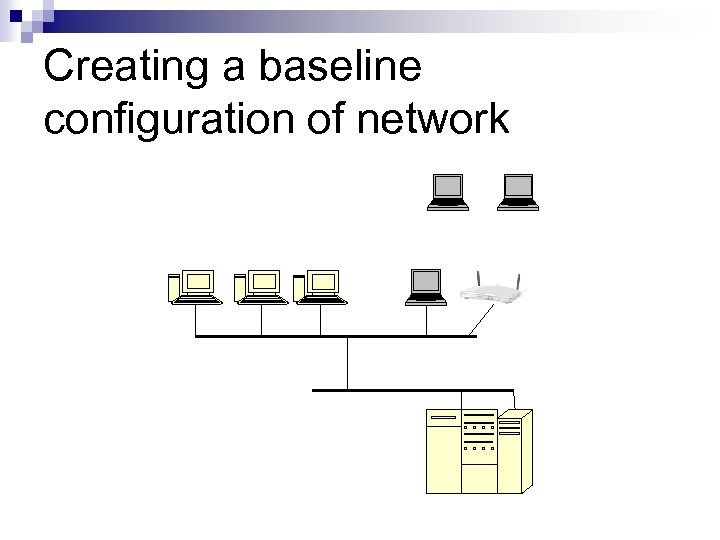
Creating a baseline configuration of network
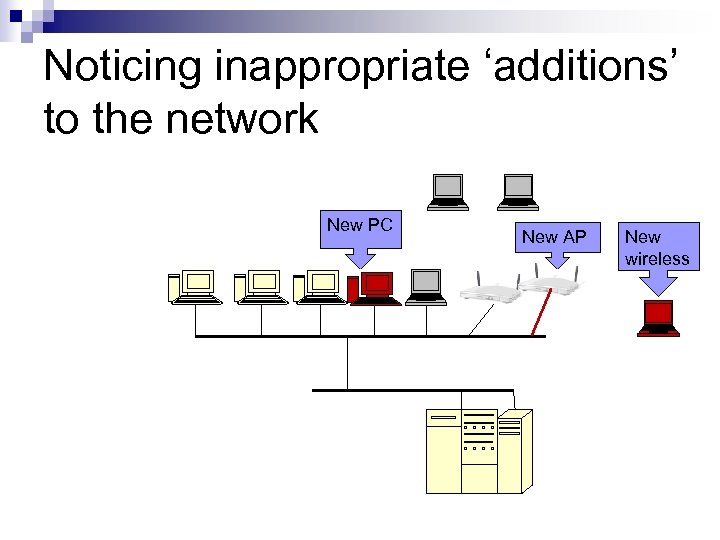
Noticing inappropriate ‘additions’ to the network New PC New AP New wireless
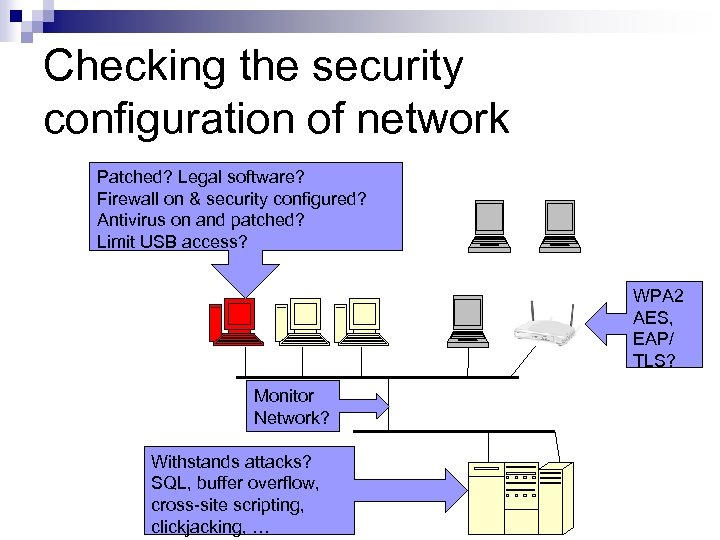
Checking the security configuration of network Patched? Legal software? Firewall on & security configured? Antivirus on and patched? Limit USB access? WPA 2 AES, EAP/ TLS? Monitor Network? Withstands attacks? SQL, buffer overflow, cross-site scripting, clickjacking, …
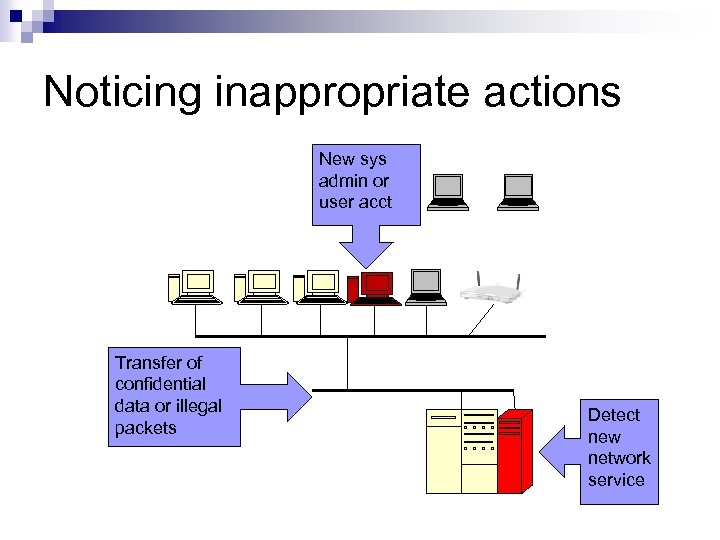
Noticing inappropriate actions New sys admin or user acct Transfer of confidential data or illegal packets Detect new network service
SANS: Critical Controls for Effective Cyber Defense Metric: Temporarily install unauthorized software/hardware on a device. It should be: n found within 24 hours (or 2 minutes? ) n isolated within one hour confirmed by alert/email n reported every 24 hours until device is removed.
SANS Critical Control 1: Inventory of Authorized Devices Ensure all devices (with IP address) on network are known, configured properly, and patched. n Scan network daily or use DHCP reports or passive monitoring. n Compare results with baseline configuration. n Metric: Temporarily install unauthorized device.
SANS: Critical Control 2: Inventory of Authorized Software Ensure all software is approved and recently patched Whitelist defines the permitted list of software. Blacklist defines illegal software (e. g. , IT tools). Endpoint Security Suites (ESS) contain antivirus, antispyware, firewall, IDS/IPS, s/w white/blacklisting. Metric: Temporarily install unauthorized software on a device.
SANS Critical Control 3: Secure Configurations for Hardware & Software n n n All devices are hardened using recommended security configurations Illegal software list exists, includes Telnet, VNC, RDP New software is quarantined and monitored. Imaged software is maintained in an updated state. Build secure images, and use configuration checking tools daily. Metric: Temporarily attempt to change a set of random configurations.
SANS Critical Control 4: Continuous Vulnerability Assessment Run vulnerability scans on all systems at least weekly, preferably daily. Problem fixes are verified through additional scans. Vulnerability scanning tools (updated) for: wireless, server, endpoint, etc. Automated patch management tools notify via email when all systems have been patched. Metric: If the scan does not complete in 24 hours, an email notification occurs.
SANS Critical Control 5: Malware Defense Antivirus/antispyware is always updated n Run against all data ¨ n Additional controls: blocking social media, limiting external devices (USB), using web proxy gateways, network monitoring. ¨ n shared files, server data, mobile data. Endpoint security suites can report tool is updated and active on all systems Metric: For benign malware (e. g. , security/hacking tool) install, antivirus prevents installation or execution or quarantines software ¨ sends an alert/email within one hour indicating specific device and owner
SANS Critical Control 6: Application S/W Security New application software is tested for security vulnerabilities: n Web vulnerabilities: buffer overflow, SQL injection, cross-site scripting, cross-site request forgery, clickjacking of code, and performance during DDOS attacks. n S/W validates input for size, type n S/W does not report system error messages directly n Automated testing includes static code analyzers and automated web scanning. n Configurations include application firewalls and hardened databases. n Metric: An attack on the software generates a log/email within 24 hours (or less). ¨ Automated web scanning occurs weekly or daily
SANS Critical Control 7: Wireless Device Control Wireless access points are securely configured with WPA 2 protocol and AES encryption. n Extensible Authentication Protocol-Transport Layer Security (EAP/TLS) provides mutual authentication. n Only registered, security-approved devices are able to connect n Wireless networks are configured for the minimum required radio footprint. n Metrics: Wireless intrusion detection systems detect available wireless access points and deactivate rogue access points within 1 hour n Vulnerability scanners can detect unauthorized wireless access points connected to the Internet.
SANS Critical Control 8: Data Recovery Capability Backups are maintained at least weekly and more often for critical data. n Backups are encrypted and securely stored. n Multiple staff can perform backup/recovery. n Metric: Test backups quarterly for a random sample of systems. This includes operating system, software, and data restoration.
SANS Critical Control 9: Security Skills Assessment Security awareness training is required for end users, system owners. Security training is necessary for programmers, system, security and network administrators. Metric: Test security awareness understanding Periodically test social engineering tests via phishing emails and phone call Employees who fail a test must attend a class
SANS Critical Control 10: Secure Network Configurations A configuration db tracks approved configurations in config. mgmt. for network devices: firewalls, routers, switches. n Two-factor identification is used for network devices. n Tools: Tools perform rule set sanity checking for Access Control Lists. n Metric: Any change to the configuration of a network device is reported within 24 hours
SANS Critical Controls 11. Control of Network Ports, Protocols, and Services: n n n Default Deny packets. Periodically review for restriction Measure time to recognize added network service 12. Controlled Administrative Privilege: n n n Minimal elevated privileges Passwords are complex, changed periodically, 2 factor Measure time to recognize new sys admin
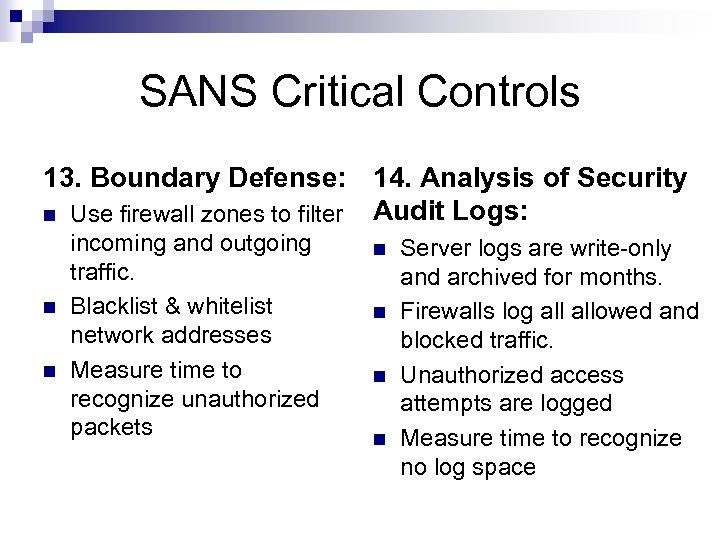
SANS Critical Controls 13. Boundary Defense: 14. Analysis of Security Audit Logs: n Use firewall zones to filter n n incoming and outgoing traffic. Blacklist & whitelist network addresses Measure time to recognize unauthorized packets n n Server logs are write-only and archived for months. Firewalls log allowed and blocked traffic. Unauthorized access attempts are logged Measure time to recognize no log space
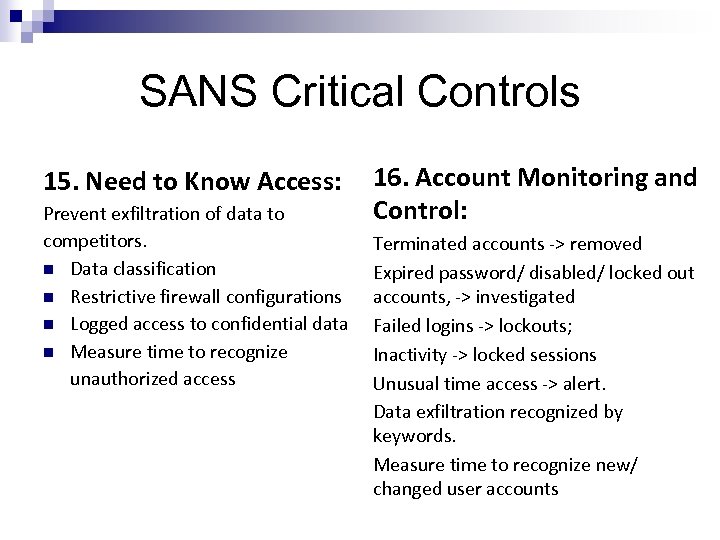
SANS Critical Controls 15. Need to Know Access: Prevent exfiltration of data to competitors. n Data classification n Restrictive firewall configurations n Logged access to confidential data n Measure time to recognize unauthorized access 16. Account Monitoring and Control: Terminated accounts -> removed Expired password/ disabled/ locked out accounts, -> investigated Failed logins -> lockouts; Inactivity -> locked sessions Unusual time access -> alert. Data exfiltration recognized by keywords. Measure time to recognize new/ changed user accounts
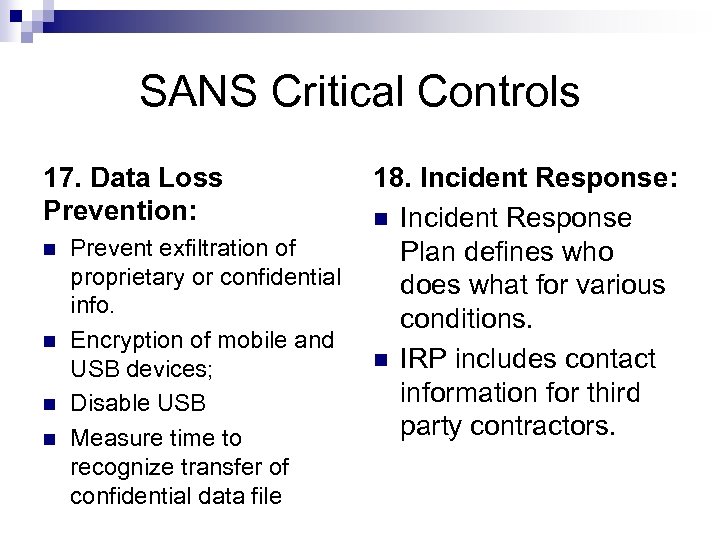
SANS Critical Controls 17. Data Loss Prevention: n n Prevent exfiltration of proprietary or confidential info. Encryption of mobile and USB devices; Disable USB Measure time to recognize transfer of confidential data file 18. Incident Response: n Incident Response Plan defines who does what for various conditions. n IRP includes contact information for third party contractors.
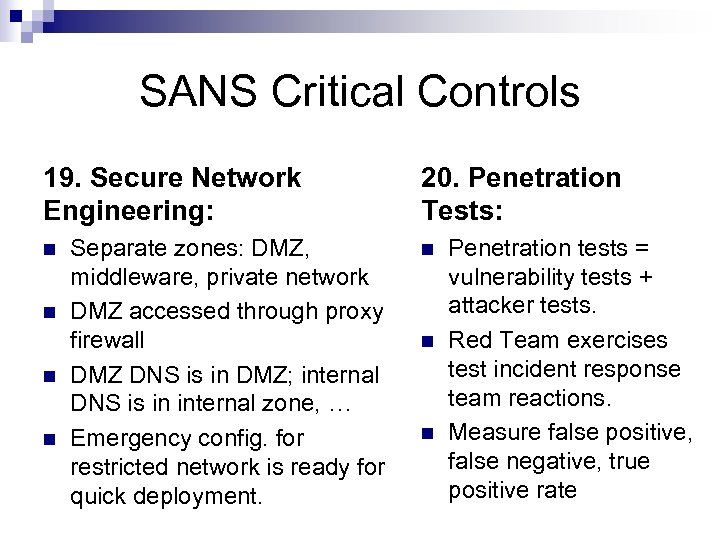
SANS Critical Controls 19. Secure Network Engineering: n n Separate zones: DMZ, middleware, private network DMZ accessed through proxy firewall DMZ DNS is in DMZ; internal DNS is in internal zone, … Emergency config. for restricted network is ready for quick deployment. 20. Penetration Tests: n n n Penetration tests = vulnerability tests + attacker tests. Red Team exercises test incident response team reactions. Measure false positive, false negative, true positive rate
Question The difference between where an organization performs and where they intend to perform is known as: 1. Gap analysis 2. Quality Control 3. Performance Measurement 4. Benchmarking
Question The MOST important metrics when measuring compliance include: 1. Metrics most easily automated 2. Metrics related to intrusion detection 3. Those recommended by best practices 4. Metrics measuring conformance to policy
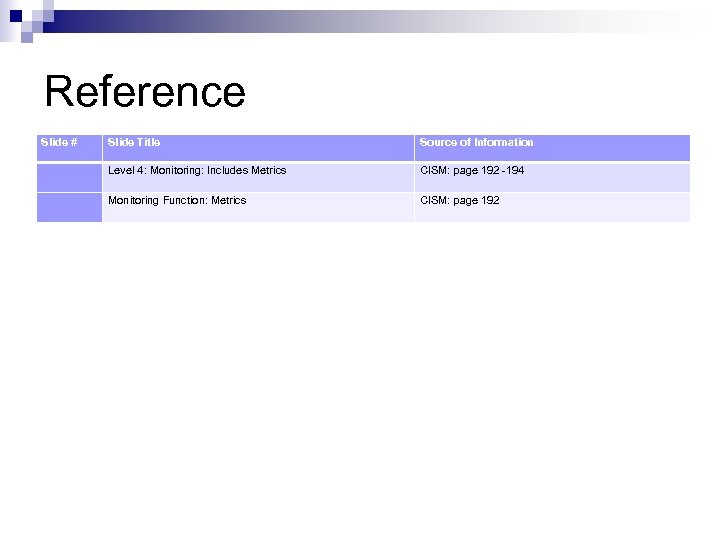
Reference Slide # Slide Title Source of Information Level 4: Monitoring: Includes Metrics CISM: page 192 -194 Monitoring Function: Metrics CISM: page 192
0a7fac64979a914db63ed5c2b1d31c50.ppt