80a1a8c93da17834445258765b6dca35.ppt
- Количество слайдов: 21
 Medical and Workplace Privacy Michael I. Shamos, Ph. D. , J. D. Institute for Software Research International Carnegie Mellon University
Medical and Workplace Privacy Michael I. Shamos, Ph. D. , J. D. Institute for Software Research International Carnegie Mellon University
 Outline • Medical privacy stakeholders: – patient – heath care provider – insurer – federal government – (sometimes) employer – What is the basis for privacy? • Workplace privacy stakeholders: – employee – employer – basis for privacy?
Outline • Medical privacy stakeholders: – patient – heath care provider – insurer – federal government – (sometimes) employer – What is the basis for privacy? • Workplace privacy stakeholders: – employee – employer – basis for privacy?
 U. S. Privacy Law • Privacy law is a patchwork of state and federal statutes and judicial decisions • The Federal government has limited powers to protect privacy – “Interstate commerce” (Federal Trade Commission) • There are three Federally protected categories of personal data: – financial (Gramm-Leech-Bliley) – educational (FERPA) – medical (HIPAA) • Plus some narrow protections, e. g. video rental data
U. S. Privacy Law • Privacy law is a patchwork of state and federal statutes and judicial decisions • The Federal government has limited powers to protect privacy – “Interstate commerce” (Federal Trade Commission) • There are three Federally protected categories of personal data: – financial (Gramm-Leech-Bliley) – educational (FERPA) – medical (HIPAA) • Plus some narrow protections, e. g. video rental data
 Cliff Notes Version of HIPAA • Covered Entities (healthcare providers, health plans, insurance companies, healthcare clearinghouses) • May Not Use or Disclose Protected Health Information (PHI) • Except with the Written Consent or Authorization of the Employee • Or Unless Required or Permitted by Law • or to the Minimum Extent Necessary or Allowed to Accomplish the Purpose of Treatment SOURCE: LITTLER, MENDELSON 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Cliff Notes Version of HIPAA • Covered Entities (healthcare providers, health plans, insurance companies, healthcare clearinghouses) • May Not Use or Disclose Protected Health Information (PHI) • Except with the Written Consent or Authorization of the Employee • Or Unless Required or Permitted by Law • or to the Minimum Extent Necessary or Allowed to Accomplish the Purpose of Treatment SOURCE: LITTLER, MENDELSON 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
 Protected Health Information (PHI) • Information created or received by a health plan or healthcare provider; and • Relates to the condition or care of an individual; or • Relates to the payment for care; and • Permits identification of the individual (or creates a reasonable basis upon which to identify the individual) 45 CFR § 164. 501 SOURCE: LITTLER, MENDELSON 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Protected Health Information (PHI) • Information created or received by a health plan or healthcare provider; and • Relates to the condition or care of an individual; or • Relates to the payment for care; and • Permits identification of the individual (or creates a reasonable basis upon which to identify the individual) 45 CFR § 164. 501 SOURCE: LITTLER, MENDELSON 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
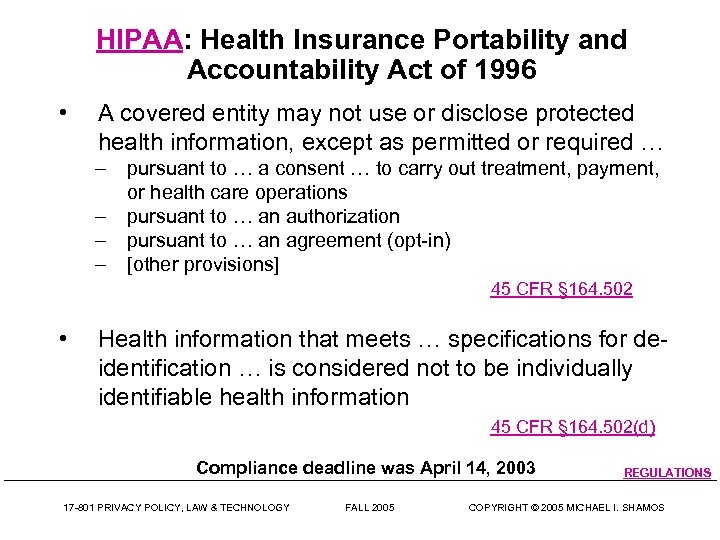 HIPAA: Health Insurance Portability and Accountability Act of 1996 • A covered entity may not use or disclose protected health information, except as permitted or required … – – pursuant to … a consent … to carry out treatment, payment, or health care operations pursuant to … an authorization pursuant to … an agreement (opt-in) [other provisions] 45 CFR § 164. 502 • Health information that meets … specifications for deidentification … is considered not to be individually identifiable health information 45 CFR § 164. 502(d) Compliance deadline was April 14, 2003 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 REGULATIONS COPYRIGHT © 2005 MICHAEL I. SHAMOS
HIPAA: Health Insurance Portability and Accountability Act of 1996 • A covered entity may not use or disclose protected health information, except as permitted or required … – – pursuant to … a consent … to carry out treatment, payment, or health care operations pursuant to … an authorization pursuant to … an agreement (opt-in) [other provisions] 45 CFR § 164. 502 • Health information that meets … specifications for deidentification … is considered not to be individually identifiable health information 45 CFR § 164. 502(d) Compliance deadline was April 14, 2003 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 REGULATIONS COPYRIGHT © 2005 MICHAEL I. SHAMOS
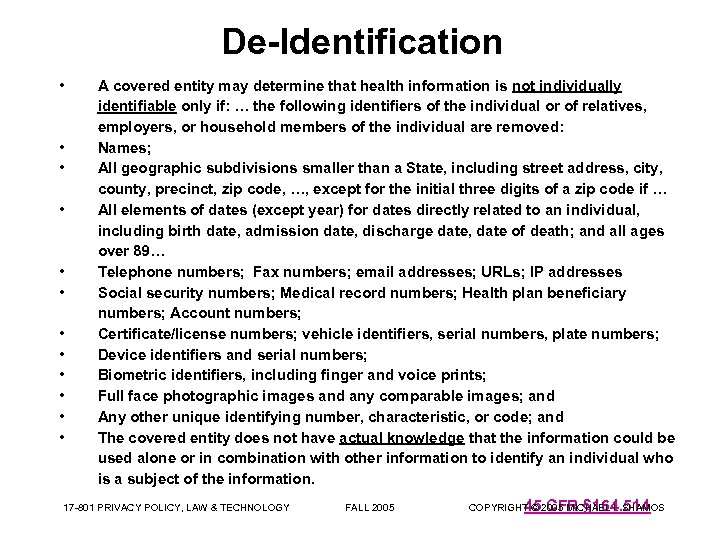 De-Identification • • • A covered entity may determine that health information is not individually identifiable only if: … the following identifiers of the individual or of relatives, employers, or household members of the individual are removed: Names; All geographic subdivisions smaller than a State, including street address, city, county, precinct, zip code, …, except for the initial three digits of a zip code if … All elements of dates (except year) for dates directly related to an individual, including birth date, admission date, discharge date, date of death; and all ages over 89… Telephone numbers; Fax numbers; email addresses; URLs; IP addresses Social security numbers; Medical record numbers; Health plan beneficiary numbers; Account numbers; Certificate/license numbers; vehicle identifiers, serial numbers, plate numbers; Device identifiers and serial numbers; Biometric identifiers, including finger and voice prints; Full face photographic images and any comparable images; and Any other unique identifying number, characteristic, or code; and The covered entity does not have actual knowledge that the information could be used alone or in combination with other information to identify an individual who is a subject of the information. 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 45 CFR § 164. 514 COPYRIGHT © 2005 MICHAEL I. SHAMOS
De-Identification • • • A covered entity may determine that health information is not individually identifiable only if: … the following identifiers of the individual or of relatives, employers, or household members of the individual are removed: Names; All geographic subdivisions smaller than a State, including street address, city, county, precinct, zip code, …, except for the initial three digits of a zip code if … All elements of dates (except year) for dates directly related to an individual, including birth date, admission date, discharge date, date of death; and all ages over 89… Telephone numbers; Fax numbers; email addresses; URLs; IP addresses Social security numbers; Medical record numbers; Health plan beneficiary numbers; Account numbers; Certificate/license numbers; vehicle identifiers, serial numbers, plate numbers; Device identifiers and serial numbers; Biometric identifiers, including finger and voice prints; Full face photographic images and any comparable images; and Any other unique identifying number, characteristic, or code; and The covered entity does not have actual knowledge that the information could be used alone or in combination with other information to identify an individual who is a subject of the information. 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 45 CFR § 164. 514 COPYRIGHT © 2005 MICHAEL I. SHAMOS
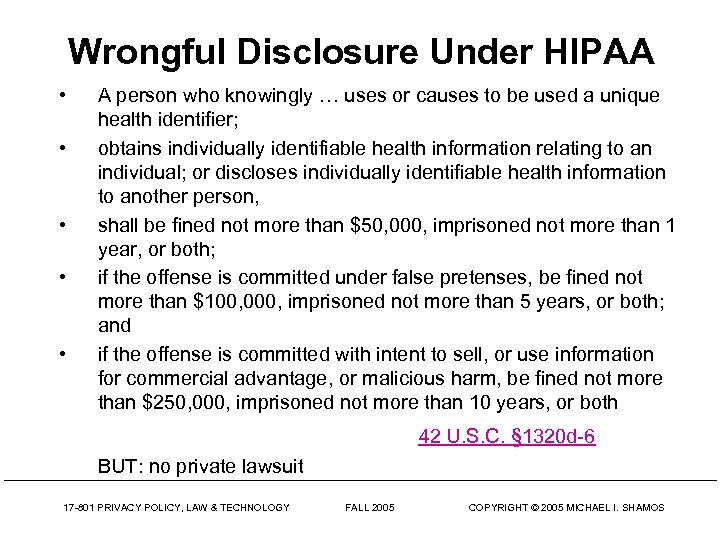 Wrongful Disclosure Under HIPAA • • • A person who knowingly … uses or causes to be used a unique health identifier; obtains individually identifiable health information relating to an individual; or discloses individually identifiable health information to another person, shall be fined not more than $50, 000, imprisoned not more than 1 year, or both; if the offense is committed under false pretenses, be fined not more than $100, 000, imprisoned not more than 5 years, or both; and if the offense is committed with intent to sell, or use information for commercial advantage, or malicious harm, be fined not more than $250, 000, imprisoned not more than 10 years, or both 42 U. S. C. § 1320 d-6 BUT: no private lawsuit 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Wrongful Disclosure Under HIPAA • • • A person who knowingly … uses or causes to be used a unique health identifier; obtains individually identifiable health information relating to an individual; or discloses individually identifiable health information to another person, shall be fined not more than $50, 000, imprisoned not more than 1 year, or both; if the offense is committed under false pretenses, be fined not more than $100, 000, imprisoned not more than 5 years, or both; and if the offense is committed with intent to sell, or use information for commercial advantage, or malicious harm, be fined not more than $250, 000, imprisoned not more than 10 years, or both 42 U. S. C. § 1320 d-6 BUT: no private lawsuit 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
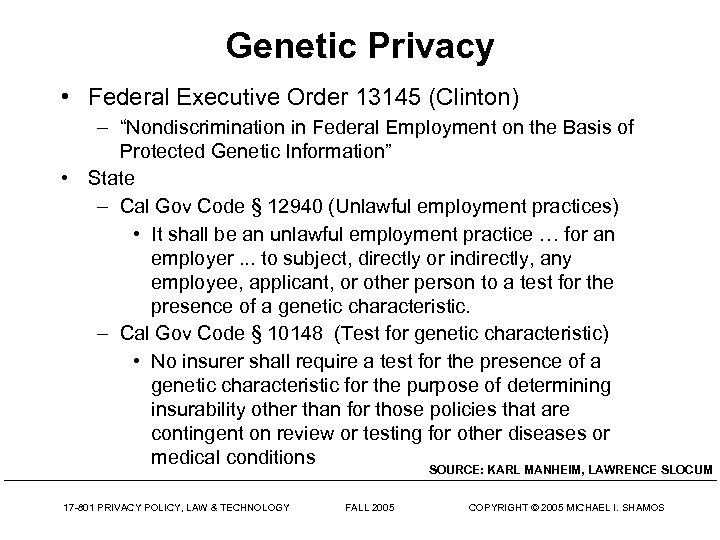 Genetic Privacy • Federal Executive Order 13145 (Clinton) – “Nondiscrimination in Federal Employment on the Basis of Protected Genetic Information” • State – Cal Gov Code § 12940 (Unlawful employment practices) • It shall be an unlawful employment practice … for an employer. . . to subject, directly or indirectly, any employee, applicant, or other person to a test for the presence of a genetic characteristic. – Cal Gov Code § 10148 (Test for genetic characteristic) • No insurer shall require a test for the presence of a genetic characteristic for the purpose of determining insurability other than for those policies that are contingent on review or testing for other diseases or medical conditions SOURCE: KARL MANHEIM, LAWRENCE SLOCUM 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Genetic Privacy • Federal Executive Order 13145 (Clinton) – “Nondiscrimination in Federal Employment on the Basis of Protected Genetic Information” • State – Cal Gov Code § 12940 (Unlawful employment practices) • It shall be an unlawful employment practice … for an employer. . . to subject, directly or indirectly, any employee, applicant, or other person to a test for the presence of a genetic characteristic. – Cal Gov Code § 10148 (Test for genetic characteristic) • No insurer shall require a test for the presence of a genetic characteristic for the purpose of determining insurability other than for those policies that are contingent on review or testing for other diseases or medical conditions SOURCE: KARL MANHEIM, LAWRENCE SLOCUM 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
 Employee Polygraph Protection Act • Make it illegal for an employer in interstate commerce to require an employee or prospective employee to take a lie detector test • to use the results of a lie detector test • to use the refusal to take a test to discharge the employee • Exceptions: – governments – employer investigations of theft where the employer has reasonable suspicions the employee was involved – security personnel 29 U. S. C. § 2002
Employee Polygraph Protection Act • Make it illegal for an employer in interstate commerce to require an employee or prospective employee to take a lie detector test • to use the results of a lie detector test • to use the refusal to take a test to discharge the employee • Exceptions: – governments – employer investigations of theft where the employer has reasonable suspicions the employee was involved – security personnel 29 U. S. C. § 2002
 O’Connor vs. Ortega, 480 U. S. 709 (1987) • Search warrants not needed by employers – Why? What about the Fourth Amendment? • Executive director O’Connor of a state hospital suspected Dr. Ortega of management improprieties • Searched his office, found incriminating evidence • Was his expectation of privacy violated? • Reality of workplace may vitiate some expectations Standard of “reasonableness” is sufficient for workrelated intrusions by public employers • 5 -4 decision by the Supreme Court 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
O’Connor vs. Ortega, 480 U. S. 709 (1987) • Search warrants not needed by employers – Why? What about the Fourth Amendment? • Executive director O’Connor of a state hospital suspected Dr. Ortega of management improprieties • Searched his office, found incriminating evidence • Was his expectation of privacy violated? • Reality of workplace may vitiate some expectations Standard of “reasonableness” is sufficient for workrelated intrusions by public employers • 5 -4 decision by the Supreme Court 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
 Fourth Amendment • “The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated, and no Warrants shall issue, but upon probable cause, supported by Oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized. ” Adopted December 15, 1791 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Fourth Amendment • “The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated, and no Warrants shall issue, but upon probable cause, supported by Oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized. ” Adopted December 15, 1791 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
 Skinner vs. Railway Labor Executives Assoc. , 489 U. S. 602 (1989) • Federal Railroad Administration (FRA) implemented regulations requiring mandatory blood and urine tests of employees involved in certain train accidents • Expectations of privacy by employees engaged in an industry regulated to ensure safety are diminished • Testing procedures pose only limited threats • Rights of the individual are superseded by the rights of the organization to conduct business. • Government's interest in assuring safety on the nation's railroads constitutes a “special need” SOURCE: CAYLEN TICHENOR 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Skinner vs. Railway Labor Executives Assoc. , 489 U. S. 602 (1989) • Federal Railroad Administration (FRA) implemented regulations requiring mandatory blood and urine tests of employees involved in certain train accidents • Expectations of privacy by employees engaged in an industry regulated to ensure safety are diminished • Testing procedures pose only limited threats • Rights of the individual are superseded by the rights of the organization to conduct business. • Government's interest in assuring safety on the nation's railroads constitutes a “special need” SOURCE: CAYLEN TICHENOR 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
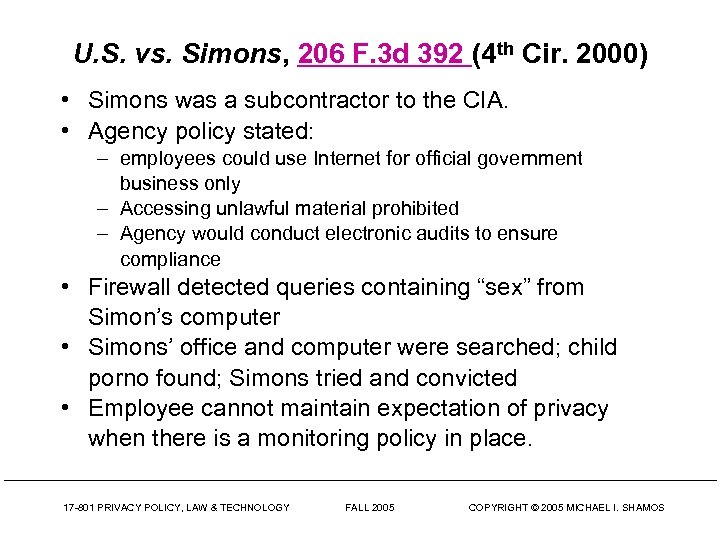 U. S. vs. Simons, 206 F. 3 d 392 (4 th Cir. 2000) • Simons was a subcontractor to the CIA. • Agency policy stated: – employees could use Internet for official government business only – Accessing unlawful material prohibited – Agency would conduct electronic audits to ensure compliance • Firewall detected queries containing “sex” from Simon’s computer • Simons’ office and computer were searched; child porno found; Simons tried and convicted • Employee cannot maintain expectation of privacy when there is a monitoring policy in place. 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
U. S. vs. Simons, 206 F. 3 d 392 (4 th Cir. 2000) • Simons was a subcontractor to the CIA. • Agency policy stated: – employees could use Internet for official government business only – Accessing unlawful material prohibited – Agency would conduct electronic audits to ensure compliance • Firewall detected queries containing “sex” from Simon’s computer • Simons’ office and computer were searched; child porno found; Simons tried and convicted • Employee cannot maintain expectation of privacy when there is a monitoring policy in place. 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
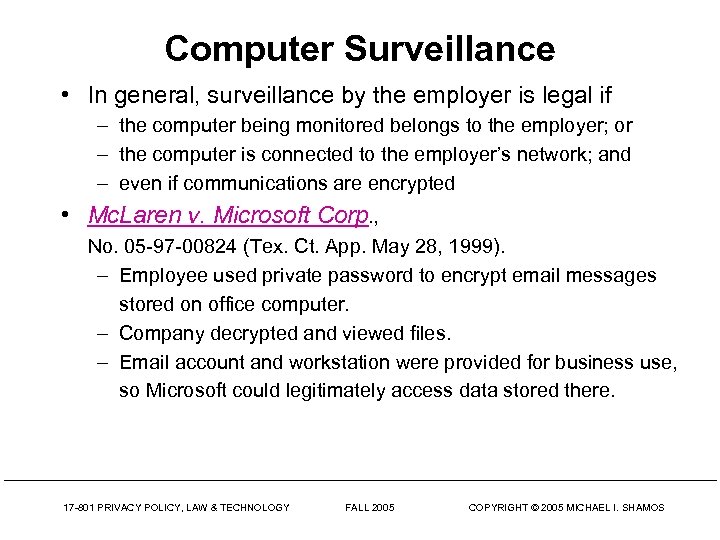 Computer Surveillance • In general, surveillance by the employer is legal if – the computer being monitored belongs to the employer; or – the computer is connected to the employer’s network; and – even if communications are encrypted • Mc. Laren v. Microsoft Corp. , No. 05 -97 -00824 (Tex. Ct. App. May 28, 1999). – Employee used private password to encrypt email messages stored on office computer. – Company decrypted and viewed files. – Email account and workstation were provided for business use, so Microsoft could legitimately access data stored there. 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Computer Surveillance • In general, surveillance by the employer is legal if – the computer being monitored belongs to the employer; or – the computer is connected to the employer’s network; and – even if communications are encrypted • Mc. Laren v. Microsoft Corp. , No. 05 -97 -00824 (Tex. Ct. App. May 28, 1999). – Employee used private password to encrypt email messages stored on office computer. – Company decrypted and viewed files. – Email account and workstation were provided for business use, so Microsoft could legitimately access data stored there. 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
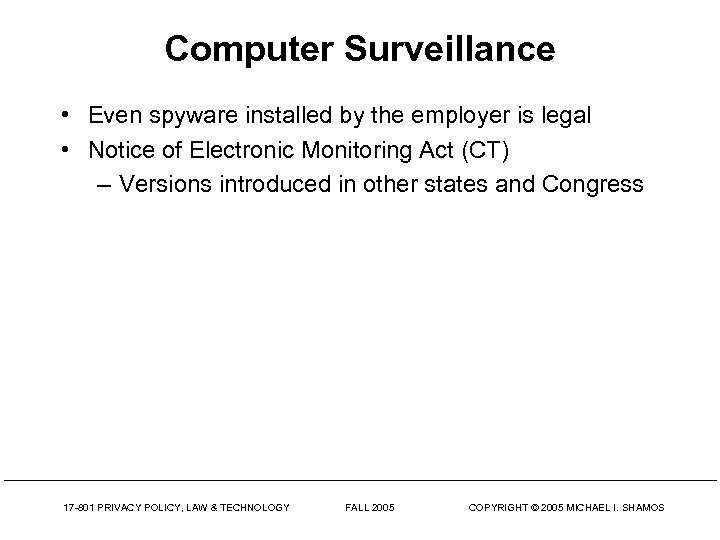 Computer Surveillance • Even spyware installed by the employer is legal • Notice of Electronic Monitoring Act (CT) – Versions introduced in other states and Congress 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Computer Surveillance • Even spyware installed by the employer is legal • Notice of Electronic Monitoring Act (CT) – Versions introduced in other states and Congress 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
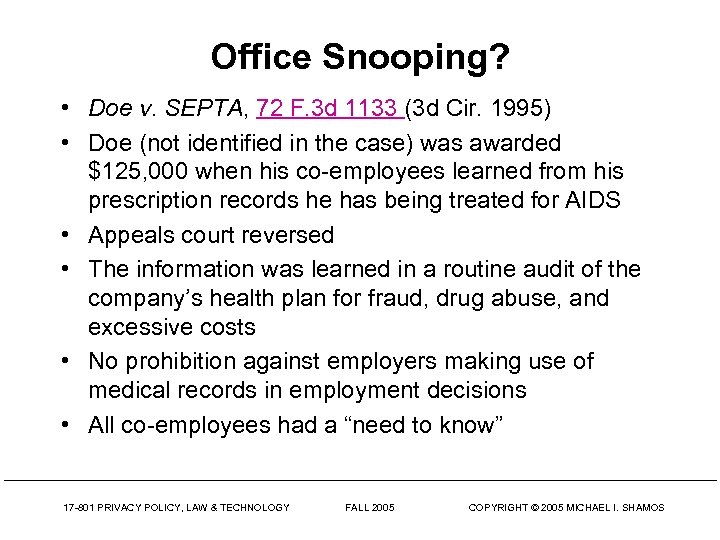 Office Snooping? • Doe v. SEPTA, 72 F. 3 d 1133 (3 d Cir. 1995) • Doe (not identified in the case) was awarded $125, 000 when his co-employees learned from his prescription records he has being treated for AIDS • Appeals court reversed • The information was learned in a routine audit of the company’s health plan for fraud, drug abuse, and excessive costs • No prohibition against employers making use of medical records in employment decisions • All co-employees had a “need to know” 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Office Snooping? • Doe v. SEPTA, 72 F. 3 d 1133 (3 d Cir. 1995) • Doe (not identified in the case) was awarded $125, 000 when his co-employees learned from his prescription records he has being treated for AIDS • Appeals court reversed • The information was learned in a routine audit of the company’s health plan for fraud, drug abuse, and excessive costs • No prohibition against employers making use of medical records in employment decisions • All co-employees had a “need to know” 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
 CMU Policy on the Privacy of Faculty Offices • The employer may give up its rights by contract • “No one may enter a faculty member's office, or search a faculty member's files, or examine or remove work products or documentary material (e. g. , research data, notes on interviews, drafts of publications or lectures, notes used in the preparation of publications or lectures, audio and visual tapes, films, outtakes, mental impressions, opinion and other material intended for dissemination of information to students, colleagues or the general public) without permission, even if the faculty member is absent. ” • “Exceptions: employee terminated, building maintenance, space planning, emergencies, retrieval of joint work or routine documents where the faculty member is not readily available to grant permission. ” • “Under any conditions of entry the occupant of the office shall immediately afterwards be furnished a list of, and/or copies of, the property or things copied FALL taken, if any. ” or 2005 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY COPYRIGHT © 2005 MICHAEL I. SHAMOS
CMU Policy on the Privacy of Faculty Offices • The employer may give up its rights by contract • “No one may enter a faculty member's office, or search a faculty member's files, or examine or remove work products or documentary material (e. g. , research data, notes on interviews, drafts of publications or lectures, notes used in the preparation of publications or lectures, audio and visual tapes, films, outtakes, mental impressions, opinion and other material intended for dissemination of information to students, colleagues or the general public) without permission, even if the faculty member is absent. ” • “Exceptions: employee terminated, building maintenance, space planning, emergencies, retrieval of joint work or routine documents where the faculty member is not readily available to grant permission. ” • “Under any conditions of entry the occupant of the office shall immediately afterwards be furnished a list of, and/or copies of, the property or things copied FALL taken, if any. ” or 2005 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY COPYRIGHT © 2005 MICHAEL I. SHAMOS
 Phone Calls and Email • Omnibus Crime Control Act of 1968 prohibits monitoring of employee phone calls unless – it occurs in the regular course of business; or – the employee consents to the monitoring • 1986 Electronic Communications and Privacy Act – Allows employers the same access to employee emails on the job – If employees are informed that their emails can and will be monitored there is no reasonable expectation of privacy 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Phone Calls and Email • Omnibus Crime Control Act of 1968 prohibits monitoring of employee phone calls unless – it occurs in the regular course of business; or – the employee consents to the monitoring • 1986 Electronic Communications and Privacy Act – Allows employers the same access to employee emails on the job – If employees are informed that their emails can and will be monitored there is no reasonable expectation of privacy 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
 Tiberino v. Spokane County 13 P. 3 d 1104 (2000) • Gina Tiberino worked for Spokane County, WA • She misused her office computer for personal email and was fired • She threatened to sue; Spokane printed out her email (551 messages; 467 were personal) • The media requested copies • Tiberino sued to prevent disclosure • Held, the emails were “public records” but the contents were exempt from disclosure. The fact of the emails, not their contents, were of public interest
Tiberino v. Spokane County 13 P. 3 d 1104 (2000) • Gina Tiberino worked for Spokane County, WA • She misused her office computer for personal email and was fired • She threatened to sue; Spokane printed out her email (551 messages; 467 were personal) • The media requested copies • Tiberino sued to prevent disclosure • Held, the emails were “public records” but the contents were exempt from disclosure. The fact of the emails, not their contents, were of public interest
 Q&A 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS
Q&A 17 -801 PRIVACY POLICY, LAW & TECHNOLOGY FALL 2005 COPYRIGHT © 2005 MICHAEL I. SHAMOS


