e70318e84243d3584f6cca82ea15aaca.ppt
- Количество слайдов: 19
 Measurement Jennifer Rexford Fall 2014 (TTh 3: 00 -4: 20 in CS 105) COS 561: Advanced Computer Networks http: //www. cs. princeton. edu/courses/archive/fall 14/cos 561/
Measurement Jennifer Rexford Fall 2014 (TTh 3: 00 -4: 20 in CS 105) COS 561: Advanced Computer Networks http: //www. cs. princeton. edu/courses/archive/fall 14/cos 561/
 Why Measure? • Managing protocols – Generating reports – Diagnosing problems – Tuning network configuration – Planning future capacity • Evaluating protocols – Characterizing protocol behavior in the wild – Creating realistic models to drive protocol evaluation
Why Measure? • Managing protocols – Generating reports – Diagnosing problems – Tuning network configuration – Planning future capacity • Evaluating protocols – Characterizing protocol behavior in the wild – Creating realistic models to drive protocol evaluation
 What to Measure • Traffic • Routing • Topology • Performance 3
What to Measure • Traffic • Routing • Topology • Performance 3
 Traffic Measurement 4
Traffic Measurement 4
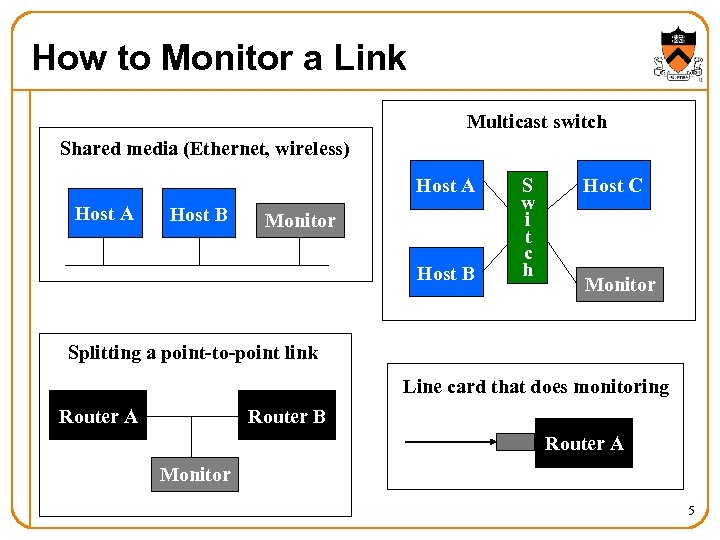 How to Monitor a Link Multicast switch Shared media (Ethernet, wireless) Host A Host B Monitor Host B S w i t c h Host C Monitor Splitting a point-to-point link Line card that does monitoring Router A Router B Router A Monitor 5
How to Monitor a Link Multicast switch Shared media (Ethernet, wireless) Host A Host B Monitor Host B S w i t c h Host C Monitor Splitting a point-to-point link Line card that does monitoring Router A Router B Router A Monitor 5
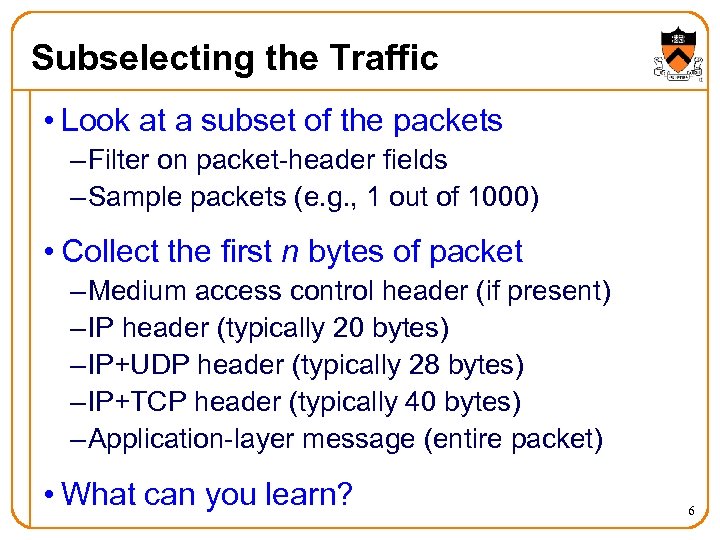 Subselecting the Traffic • Look at a subset of the packets – Filter on packet-header fields – Sample packets (e. g. , 1 out of 1000) • Collect the first n bytes of packet – Medium access control header (if present) – IP header (typically 20 bytes) – IP+UDP header (typically 28 bytes) – IP+TCP header (typically 40 bytes) – Application-layer message (entire packet) • What can you learn? 6
Subselecting the Traffic • Look at a subset of the packets – Filter on packet-header fields – Sample packets (e. g. , 1 out of 1000) • Collect the first n bytes of packet – Medium access control header (if present) – IP header (typically 20 bytes) – IP+UDP header (typically 28 bytes) – IP+TCP header (typically 40 bytes) – Application-layer message (entire packet) • What can you learn? 6
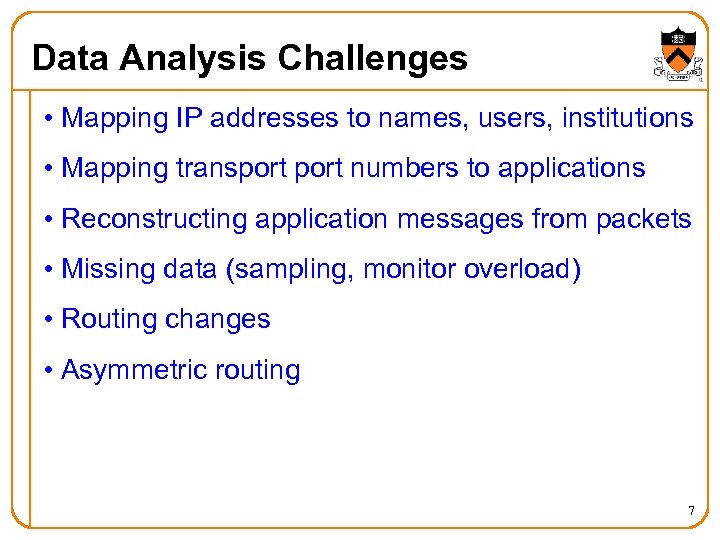 Data Analysis Challenges • Mapping IP addresses to names, users, institutions • Mapping transport numbers to applications • Reconstructing application messages from packets • Missing data (sampling, monitor overload) • Routing changes • Asymmetric routing 7
Data Analysis Challenges • Mapping IP addresses to names, users, institutions • Mapping transport numbers to applications • Reconstructing application messages from packets • Missing data (sampling, monitor overload) • Routing changes • Asymmetric routing 7
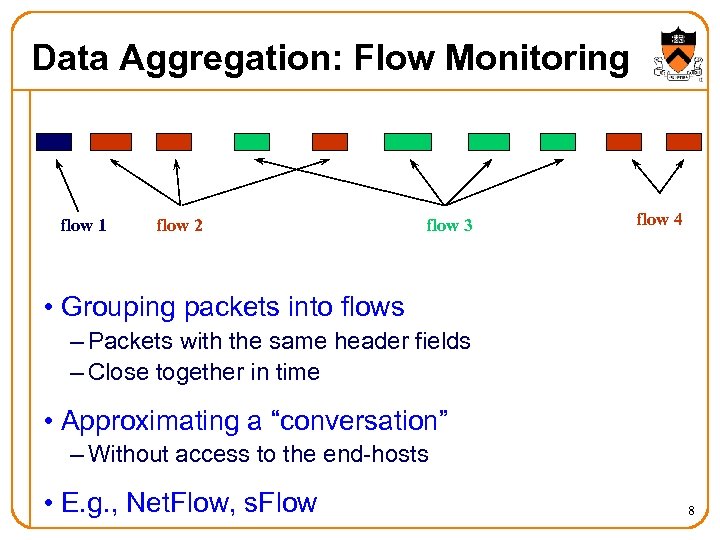 Data Aggregation: Flow Monitoring flow 1 flow 2 flow 3 flow 4 • Grouping packets into flows – Packets with the same header fields – Close together in time • Approximating a “conversation” – Without access to the end-hosts • E. g. , Net. Flow, s. Flow 8
Data Aggregation: Flow Monitoring flow 1 flow 2 flow 3 flow 4 • Grouping packets into flows – Packets with the same header fields – Close together in time • Approximating a “conversation” – Without access to the end-hosts • E. g. , Net. Flow, s. Flow 8
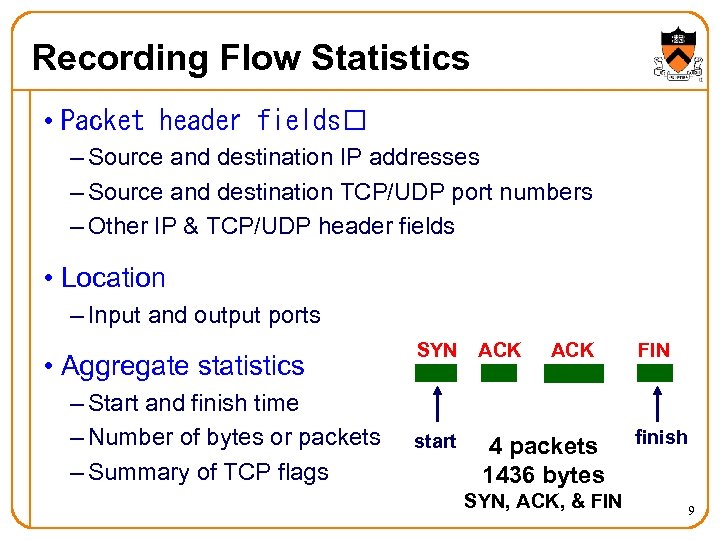 Recording Flow Statistics • Packet header fields – Source and destination IP addresses – Source and destination TCP/UDP port numbers – Other IP & TCP/UDP header fields • Location – Input and output ports • Aggregate statistics – Start and finish time – Number of bytes or packets – Summary of TCP flags SYN ACK start 4 packets 1436 bytes ACK SYN, ACK, & FIN finish 9
Recording Flow Statistics • Packet header fields – Source and destination IP addresses – Source and destination TCP/UDP port numbers – Other IP & TCP/UDP header fields • Location – Input and output ports • Aggregate statistics – Start and finish time – Number of bytes or packets – Summary of TCP flags SYN ACK start 4 packets 1436 bytes ACK SYN, ACK, & FIN finish 9
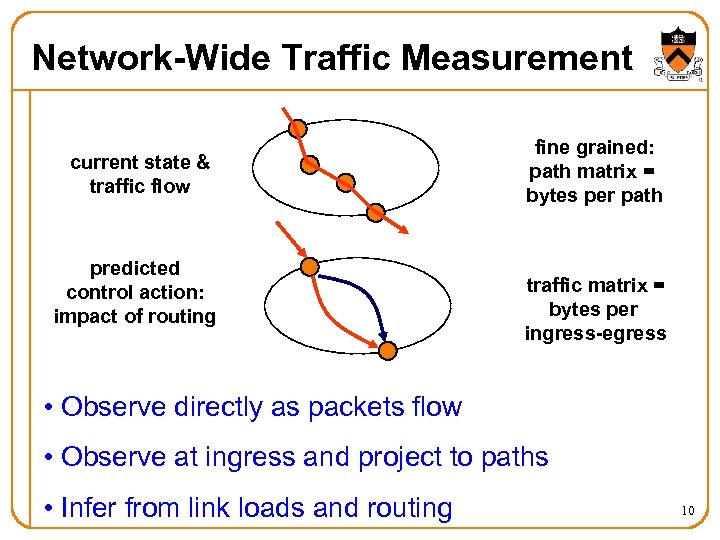 Network-Wide Traffic Measurement current state & traffic flow predicted control action: impact of routing fine grained: path matrix = bytes per path traffic matrix = bytes per ingress-egress • Observe directly as packets flow • Observe at ingress and project to paths • Infer from link loads and routing 10
Network-Wide Traffic Measurement current state & traffic flow predicted control action: impact of routing fine grained: path matrix = bytes per path traffic matrix = bytes per ingress-egress • Observe directly as packets flow • Observe at ingress and project to paths • Infer from link loads and routing 10
 Routing 11
Routing 11
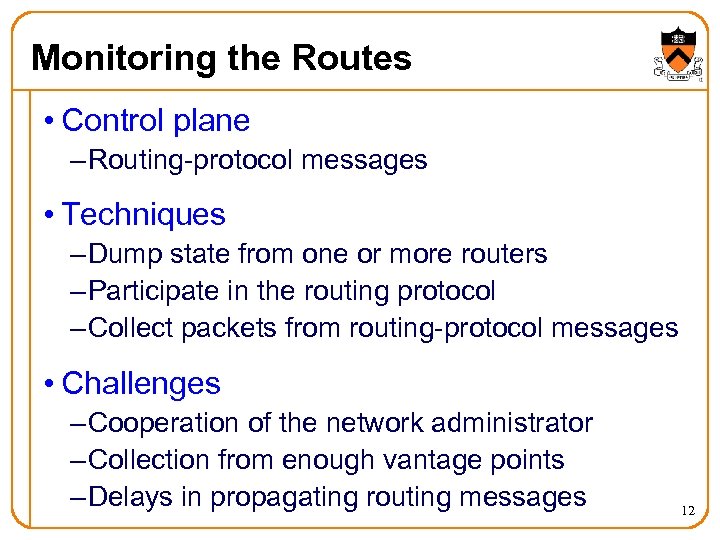 Monitoring the Routes • Control plane – Routing-protocol messages • Techniques – Dump state from one or more routers – Participate in the routing protocol – Collect packets from routing-protocol messages • Challenges – Cooperation of the network administrator – Collection from enough vantage points – Delays in propagating routing messages 12
Monitoring the Routes • Control plane – Routing-protocol messages • Techniques – Dump state from one or more routers – Participate in the routing protocol – Collect packets from routing-protocol messages • Challenges – Cooperation of the network administrator – Collection from enough vantage points – Delays in propagating routing messages 12
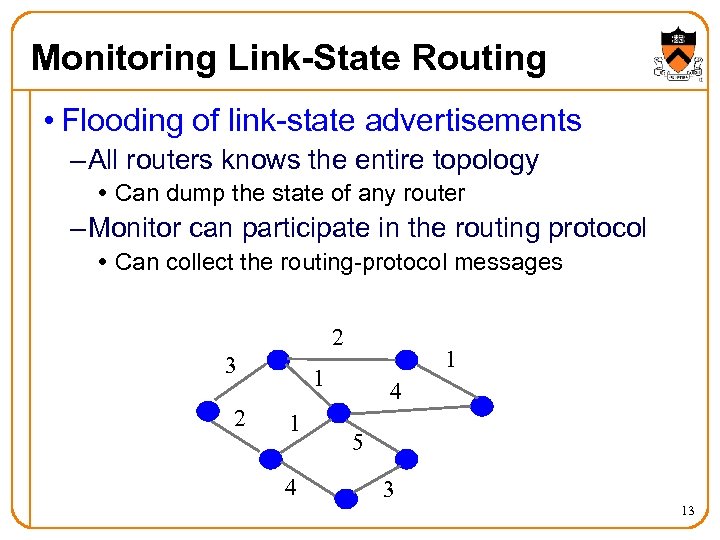 Monitoring Link-State Routing • Flooding of link-state advertisements – All routers knows the entire topology Can dump the state of any router – Monitor can participate in the routing protocol Can collect the routing-protocol messages 2 3 2 1 1 1 4 4 5 3 13
Monitoring Link-State Routing • Flooding of link-state advertisements – All routers knows the entire topology Can dump the state of any router – Monitor can participate in the routing protocol Can collect the routing-protocol messages 2 3 2 1 1 1 4 4 5 3 13
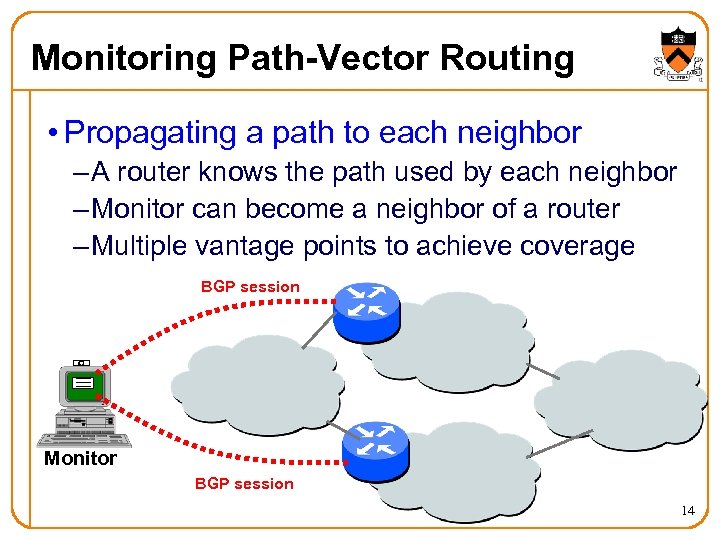 Monitoring Path-Vector Routing • Propagating a path to each neighbor – A router knows the path used by each neighbor – Monitor can become a neighbor of a router – Multiple vantage points to achieve coverage BGP session Monitor BGP session 14
Monitoring Path-Vector Routing • Propagating a path to each neighbor – A router knows the path used by each neighbor – Monitor can become a neighbor of a router – Multiple vantage points to achieve coverage BGP session Monitor BGP session 14
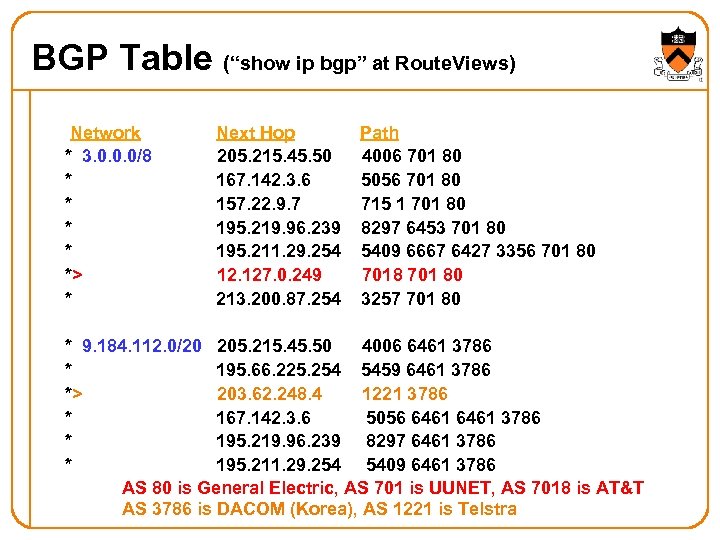 BGP Table (“show ip bgp” at Route. Views) Network * 3. 0. 0. 0/8 * * *> * Next Hop 205. 215. 45. 50 167. 142. 3. 6 157. 22. 9. 7 195. 219. 96. 239 195. 211. 29. 254 12. 127. 0. 249 213. 200. 87. 254 Path 4006 701 80 5056 701 80 715 1 701 80 8297 6453 701 80 5409 6667 6427 3356 701 80 7018 701 80 3257 701 80 * 9. 184. 112. 0/20 205. 215. 45. 50 4006 6461 3786 * 195. 66. 225. 254 5459 6461 3786 *> 203. 62. 248. 4 1221 3786 * 167. 142. 3. 6 5056 6461 3786 * 195. 219. 96. 239 8297 6461 3786 * 195. 211. 29. 254 5409 6461 3786 AS 80 is General Electric, AS 701 is UUNET, AS 7018 is AT&T AS 3786 is DACOM (Korea), AS 1221 is Telstra
BGP Table (“show ip bgp” at Route. Views) Network * 3. 0. 0. 0/8 * * *> * Next Hop 205. 215. 45. 50 167. 142. 3. 6 157. 22. 9. 7 195. 219. 96. 239 195. 211. 29. 254 12. 127. 0. 249 213. 200. 87. 254 Path 4006 701 80 5056 701 80 715 1 701 80 8297 6453 701 80 5409 6667 6427 3356 701 80 7018 701 80 3257 701 80 * 9. 184. 112. 0/20 205. 215. 45. 50 4006 6461 3786 * 195. 66. 225. 254 5459 6461 3786 *> 203. 62. 248. 4 1221 3786 * 167. 142. 3. 6 5056 6461 3786 * 195. 219. 96. 239 8297 6461 3786 * 195. 211. 29. 254 5409 6461 3786 AS 80 is General Electric, AS 701 is UUNET, AS 7018 is AT&T AS 3786 is DACOM (Korea), AS 1221 is Telstra
 Measuring the Forwarding Path • Data plane – What path is the traffic taking • Techniques – Extract the forwarding-table state – Record the path as the packet travels – Infer the path from end-to-end measurements • Challenges – Cooperation of the network administrator – Routing changes during the measurement – Overhead of collecting the data 16
Measuring the Forwarding Path • Data plane – What path is the traffic taking • Techniques – Extract the forwarding-table state – Record the path as the packet travels – Infer the path from end-to-end measurements • Challenges – Cooperation of the network administrator – Routing changes during the measurement – Overhead of collecting the data 16
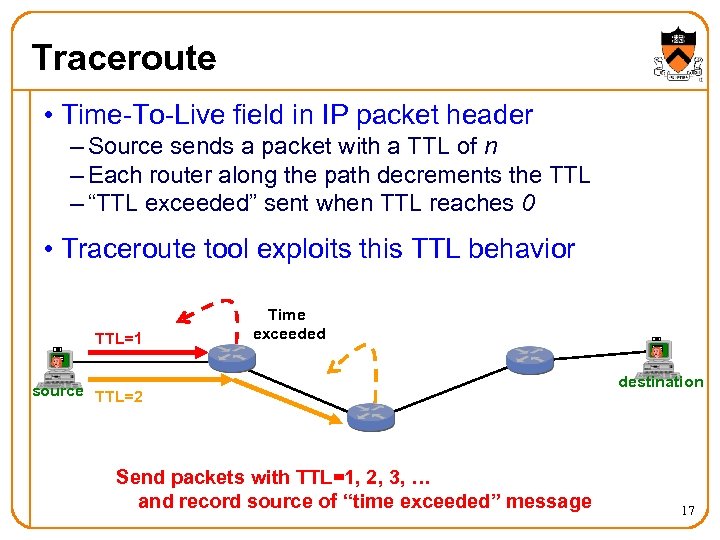 Traceroute • Time-To-Live field in IP packet header – Source sends a packet with a TTL of n – Each router along the path decrements the TTL – “TTL exceeded” sent when TTL reaches 0 • Traceroute tool exploits this TTL behavior TTL=1 Time exceeded source TTL=2 Send packets with TTL=1, 2, 3, … and record source of “time exceeded” message destination 17
Traceroute • Time-To-Live field in IP packet header – Source sends a packet with a TTL of n – Each router along the path decrements the TTL – “TTL exceeded” sent when TTL reaches 0 • Traceroute tool exploits this TTL behavior TTL=1 Time exceeded source TTL=2 Send packets with TTL=1, 2, 3, … and record source of “time exceeded” message destination 17
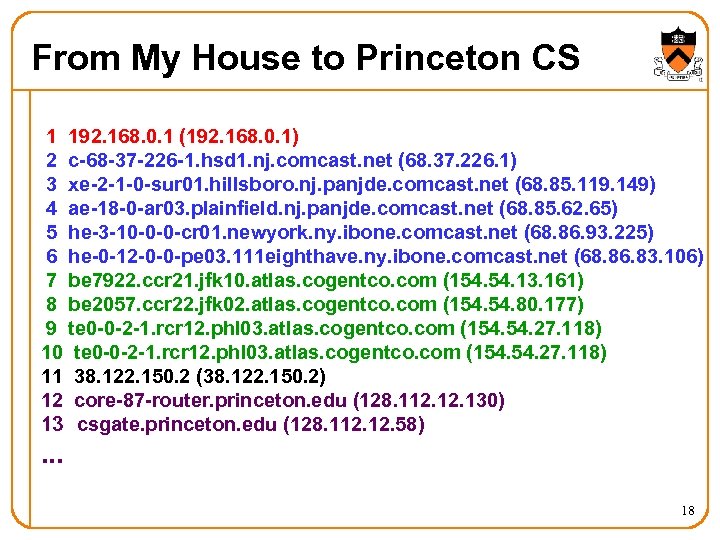 From My House to Princeton CS 1 192. 168. 0. 1 (192. 168. 0. 1) 2 c-68 -37 -226 -1. hsd 1. nj. comcast. net (68. 37. 226. 1) 3 xe-2 -1 -0 -sur 01. hillsboro. nj. panjde. comcast. net (68. 85. 119. 149) 4 ae-18 -0 -ar 03. plainfield. nj. panjde. comcast. net (68. 85. 62. 65) 5 he-3 -10 -0 -0 -cr 01. newyork. ny. ibone. comcast. net (68. 86. 93. 225) 6 he-0 -12 -0 -0 -pe 03. 111 eighthave. ny. ibone. comcast. net (68. 86. 83. 106) 7 be 7922. ccr 21. jfk 10. atlas. cogentco. com (154. 13. 161) 8 be 2057. ccr 22. jfk 02. atlas. cogentco. com (154. 80. 177) 9 te 0 -0 -2 -1. rcr 12. phl 03. atlas. cogentco. com (154. 27. 118) 10 te 0 -0 -2 -1. rcr 12. phl 03. atlas. cogentco. com (154. 27. 118) 11 38. 122. 150. 2 (38. 122. 150. 2) 12 core-87 -router. princeton. edu (128. 112. 130) 13 csgate. princeton. edu (128. 112. 58) . . . 18
From My House to Princeton CS 1 192. 168. 0. 1 (192. 168. 0. 1) 2 c-68 -37 -226 -1. hsd 1. nj. comcast. net (68. 37. 226. 1) 3 xe-2 -1 -0 -sur 01. hillsboro. nj. panjde. comcast. net (68. 85. 119. 149) 4 ae-18 -0 -ar 03. plainfield. nj. panjde. comcast. net (68. 85. 62. 65) 5 he-3 -10 -0 -0 -cr 01. newyork. ny. ibone. comcast. net (68. 86. 93. 225) 6 he-0 -12 -0 -0 -pe 03. 111 eighthave. ny. ibone. comcast. net (68. 86. 83. 106) 7 be 7922. ccr 21. jfk 10. atlas. cogentco. com (154. 13. 161) 8 be 2057. ccr 22. jfk 02. atlas. cogentco. com (154. 80. 177) 9 te 0 -0 -2 -1. rcr 12. phl 03. atlas. cogentco. com (154. 27. 118) 10 te 0 -0 -2 -1. rcr 12. phl 03. atlas. cogentco. com (154. 27. 118) 11 38. 122. 150. 2 (38. 122. 150. 2) 12 core-87 -router. princeton. edu (128. 112. 130) 13 csgate. princeton. edu (128. 112. 58) . . . 18
 Rocket. Fuel Paper Discussion 19
Rocket. Fuel Paper Discussion 19


