6a6fab2c662620f22ddbad8a5f5f3225.ppt
- Количество слайдов: 31

Lecture 5 E-Banking Robert H Deng, SIS-SMU, 2005 1
Outline • Definition of e-banking • Entity authentication and secure communications • Server side architecture & security • Web client security • Web application security Robert H Deng, SIS-SMU, 2005 2

What Is E-Banking • Definition – The automated delivery of new and traditional banking products and services directly to customers through electronic, interactive communication channels. • Products and Services – – – Account information and management Bill presentation and bill payment Loan applications and approval Investment and brokerage services … Robert H Deng, SIS-SMU, 2005 3

Stages of E-Banking • Automatic Teller Machine (ATM): – An economical substitute for brick and mortar branches, longer banking hours – Services: Balance enquiry; cash withdrawal, deposit, funds transfer, payment for IPO offerings, COE bidding, etc • Tele-Banking: – Retail banking by dial a phone #, automatic voice response – all services as ATM except cash withdrawal and deposit • PC-Banking – Dial into a bank’s intranet proprietary software system to access accounts for transactions Robert H Deng, SIS-SMU, 2005 4
Stages of E-Banking: Internet-Banking • Definition: – Consumers access banking products and services over the Internet • Advantages – PC-banking were proprietary, developed just by the bank – Internet puts everyone on an equal footing. There is a wealth of 3 rd party providers – The cost per transaction through the Internet is 27 times less than through ATMs, 54 times less than that of a telephone transaction and 107 times less than that of a physical branch transaction. • The Risks – There is security risk in using any remote-access for financial services, internet banking poses the greatest risk since internet is an open and public network. Robert H Deng, SIS-SMU, 2005 5
Internet Banking - Informational Websites • Objective – Bank wants to provide information to the public and its customers – Bank wants to verify the information is correction and the web site is usually up • Risk issues – Potential liability for inaccurate information – Potential liability for spreading viruses and other malicious code to computers accessing the website – Negative public perception if the bank’s online service is disrupted or website defaced or presents offensive material Inside ABC Bank Company Information Investor Relations News Room Careers ABC Bank in the Community Doing Business with ABC Bank Help Center Contact Us ATM/Branch locations Self Services Frequently Asked Questions Robert H Deng, SIS-SMU, 2005 6
Internet Banking – • Objective – Provide banking services in a secure and reliable manner • Risk Issues – Higher risk than info website due to exchange of confidential customer info and transfer of funds – Authentication processes – Liability for unauthorized transactions – Losses from fraud if the bank fails to verify user identity – Violations of laws or regulations pertaining to consumer privacy, antimoney laundering, anti-terrorism etc – Negative public perception, customer dissatisfaction, liability resulting from failure to process 3 rdparty payments as directed or within a time frame. Transactional Websites Inside ABC Bank Company Information Investor Relations News Room Careers ABC Bank in the Community Doing Business with ABC Bank Help Center Contact Us ATM/Branch locations Self Services Frequently Asked Questions Access Accounts Personal Account Login Commercial Account Login Robert H Deng, SIS-SMU, 2005 7
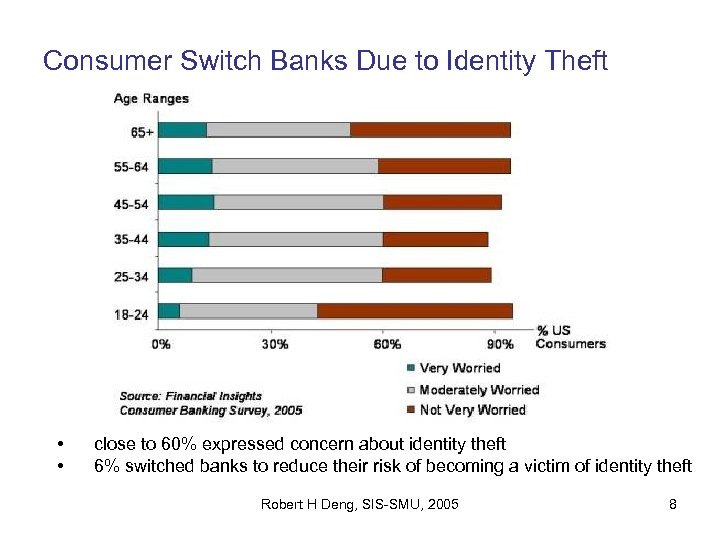
Consumer Switch Banks Due to Identity Theft • • close to 60% expressed concern about identity theft 6% switched banks to reduce their risk of becoming a victim of identity theft Robert H Deng, SIS-SMU, 2005 8
Outline • Definition of e-banking • Entity authentication and secure communications • Server side architecture & security • Web client security • Web application security Robert H Deng, SIS-SMU, 2005 9
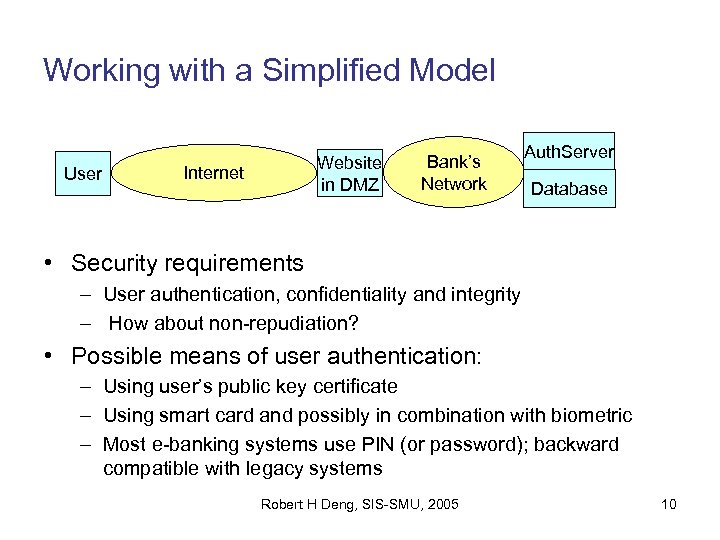
Working with a Simplified Model User Website in DMZ Internet Bank’s Network Auth. Server Database • Security requirements – User authentication, confidentiality and integrity – How about non-repudiation? • Possible means of user authentication: – Using user’s public key certificate – Using smart card and possibly in combination with biometric – Most e-banking systems use PIN (or password); backward compatible with legacy systems Robert H Deng, SIS-SMU, 2005 10

Using SSL for Internet Banking User • Website in DMZ Internet Bank’s Network Auth. Server Database Secure communication over internal network – Communication between web server and bank’s internal servers are protected using IPSEC (Internet Protocol Security) • Secure communication over the Internet – Bank obtains public key certificate from a CA – Bank’s private key kept at web server, ideally in a tamper-resistant hardware – User and web server runs SSL, authenticate server and set up a secure tunnel • Customer authentication – Customer sends PIN in clear text over the secure tunnel Robert H Deng, SIS-SMU, 2005 11
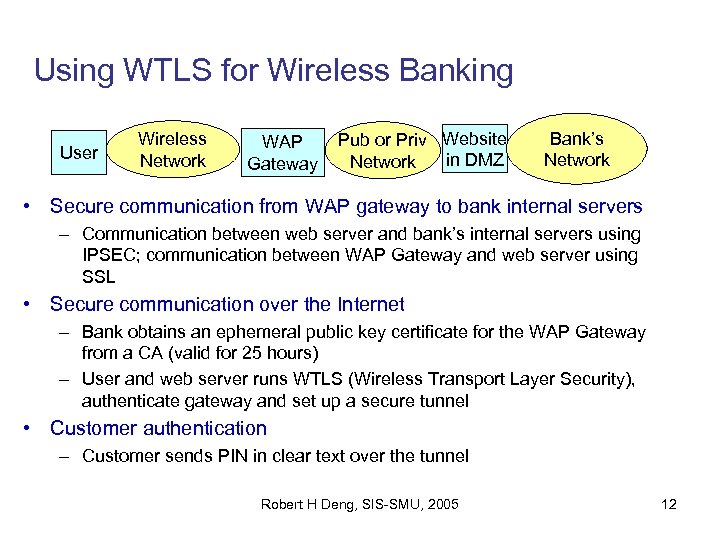
Using WTLS for Wireless Banking User Wireless Network WAP Gateway Pub or Priv Website in DMZ Network Bank’s Network • Secure communication from WAP gateway to bank internal servers – Communication between web server and bank’s internal servers using IPSEC; communication between WAP Gateway and web server using SSL • Secure communication over the Internet – Bank obtains an ephemeral public key certificate for the WAP Gateway from a CA (valid for 25 hours) – User and web server runs WTLS (Wireless Transport Layer Security), authenticate gateway and set up a secure tunnel • Customer authentication – Customer sends PIN in clear text over the tunnel Robert H Deng, SIS-SMU, 2005 12
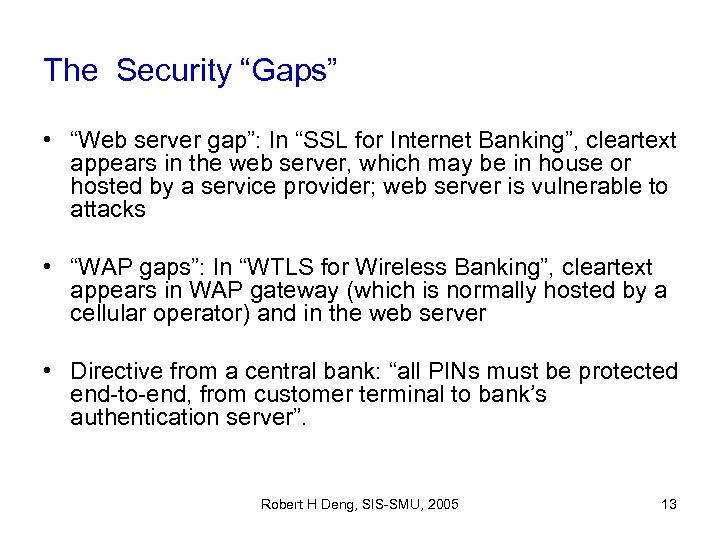
The Security “Gaps” • “Web server gap”: In “SSL for Internet Banking”, cleartext appears in the web server, which may be in house or hosted by a service provider; web server is vulnerable to attacks • “WAP gaps”: In “WTLS for Wireless Banking”, cleartext appears in WAP gateway (which is normally hosted by a cellular operator) and in the web server • Directive from a central bank: “all PINs must be protected end-to-end, from customer terminal to bank’s authentication server”. Robert H Deng, SIS-SMU, 2005 13
Outline • Definition of e-banking • Entity authentication and secure communications • Server side architecture & security • Web client security • Web application security Robert H Deng, SIS-SMU, 2005 14
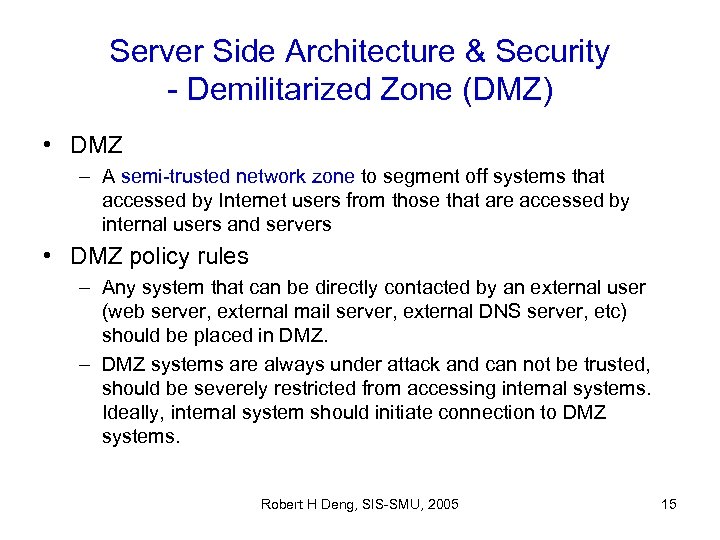
Server Side Architecture & Security - Demilitarized Zone (DMZ) • DMZ – A semi-trusted network zone to segment off systems that accessed by Internet users from those that are accessed by internal users and servers • DMZ policy rules – Any system that can be directly contacted by an external user (web server, external mail server, external DNS server, etc) should be placed in DMZ. – DMZ systems are always under attack and can not be trusted, should be severely restricted from accessing internal systems. Ideally, internal system should initiate connection to DMZ systems. Robert H Deng, SIS-SMU, 2005 15

Server Side Architecture & Security - A typical DMZ architecture Web Server External Mail Server External DNS Server DMZ Initiate connections Internal Network Response only Firewall Robert H Deng, SIS-SMU, 2005 Only services offered by DMZ systems Internet 16

A Typical E-Banking Server Side Architecture E-banking App Server Firewall 3 Firewall 2 Makes SQL queries to database server Bank Internal Network Web Server F/W only allows access ports 80 and 443 on the web server Firewall 1 Internet Database Server HSM – Hardware Security Module Robert H Deng, SIS-SMU, 2005 17
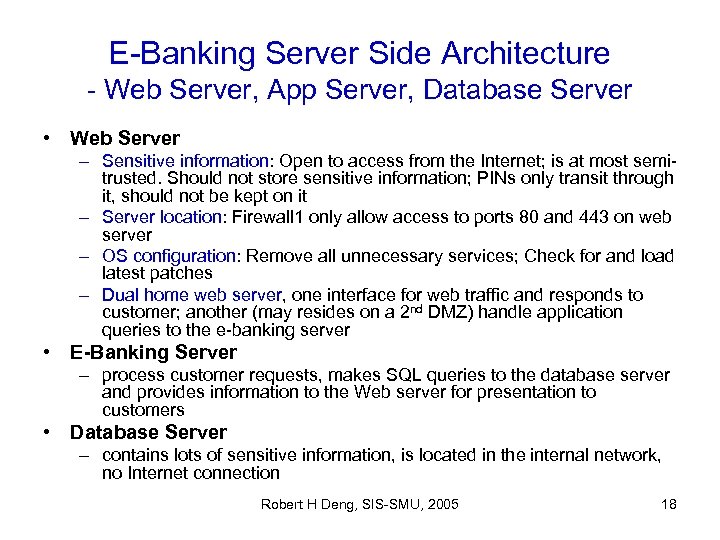
E-Banking Server Side Architecture - Web Server, App Server, Database Server • Web Server – Sensitive information: Open to access from the Internet; is at most semitrusted. Should not store sensitive information; PINs only transit through it, should not be kept on it – Server location: Firewall 1 only allow access to ports 80 and 443 on web server – OS configuration: Remove all unnecessary services; Check for and load latest patches – Dual home web server, one interface for web traffic and responds to customer; another (may resides on a 2 nd DMZ) handle application queries to the e-banking server • E-Banking Server – process customer requests, makes SQL queries to the database server and provides information to the Web server for presentation to customers • Database Server – contains lots of sensitive information, is located in the internal network, no Internet connection Robert H Deng, SIS-SMU, 2005 18
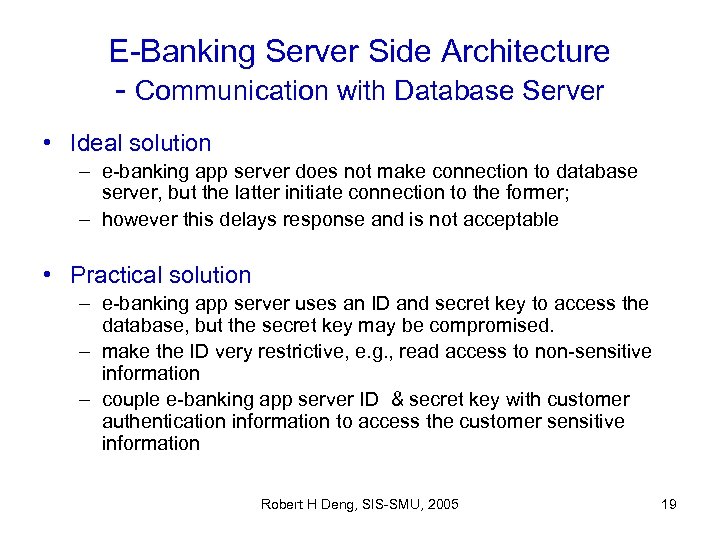
E-Banking Server Side Architecture - Communication with Database Server • Ideal solution – e-banking app server does not make connection to database server, but the latter initiate connection to the former; – however this delays response and is not acceptable • Practical solution – e-banking app server uses an ID and secret key to access the database, but the secret key may be compromised. – make the ID very restrictive, e. g. , read access to non-sensitive information – couple e-banking app server ID & secret key with customer authentication information to access the customer sensitive information Robert H Deng, SIS-SMU, 2005 19

A High Availability E-Banking Server Side Architecture App layer switches provide load sharing & fail-over across web servers Web servers App layer switch Firewall Routers & firewalls are cross-connected to switches to provide redundant paths Switch Router ISP #1 POP BGP running between ISPs Internet ISP #2 POP Internal network e-banking app servers Robert H Deng, SIS-SMU, 2005 Database server on redundant cluster 20
Outline • Definition of e-banking • Entity authentication and secure communications • Server side architecture & security • Web client security • Web application security Robert H Deng, SIS-SMU, 2005 21
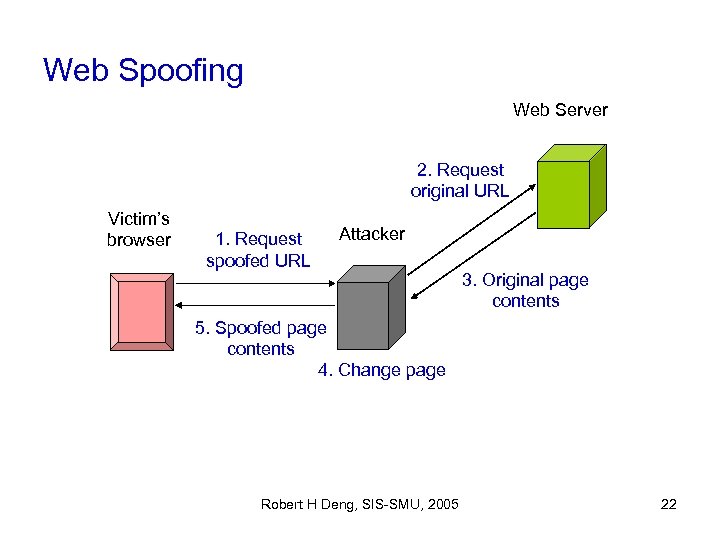
Web Spoofing Web Server 2. Request original URL Victim’s browser 1. Request spoofed URL Attacker 3. Original page contents 5. Spoofed page contents 4. Change page Robert H Deng, SIS-SMU, 2005 22
Web Spoofing • Attacker 1. 2. 3. 4. 5. • makes victim visit his web page (e. g. , by phishing attack) either sends victim a fake page or passes on the original URL request to the real web server (e. g. , function as a proxy) intercepts response may change the response sends the response to victim Consequences – • Attacker may get victim’s account and password, may spoof stock market information Difficult to counter – – Victim may not be able to recognize it’s fake. Browser’s location line and status may be changed by attacker using Java. Script Victim needs to examine SSL certificate’s owner carefully! Robert H Deng, SIS-SMU, 2005 23
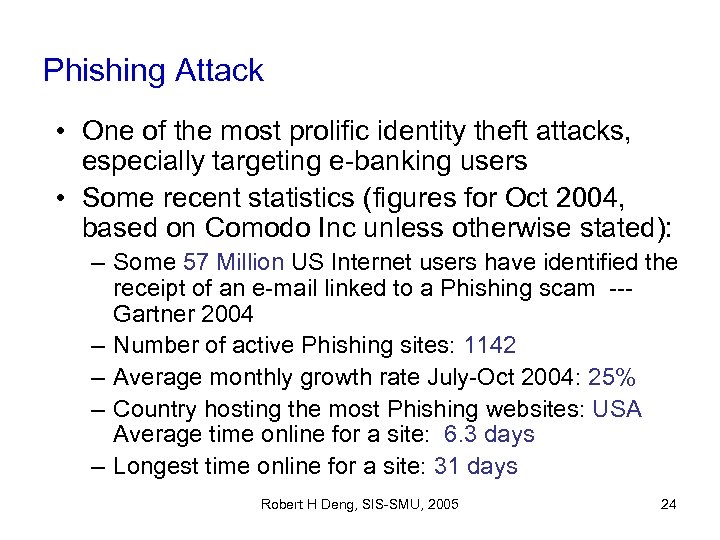
Phishing Attack • One of the most prolific identity theft attacks, especially targeting e-banking users • Some recent statistics (figures for Oct 2004, based on Comodo Inc unless otherwise stated): – Some 57 Million US Internet users have identified the receipt of an e-mail linked to a Phishing scam --Gartner 2004 – Number of active Phishing sites: 1142 – Average monthly growth rate July-Oct 2004: 25% – Country hosting the most Phishing websites: USA Average time online for a site: 6. 3 days – Longest time online for a site: 31 days Robert H Deng, SIS-SMU, 2005 24
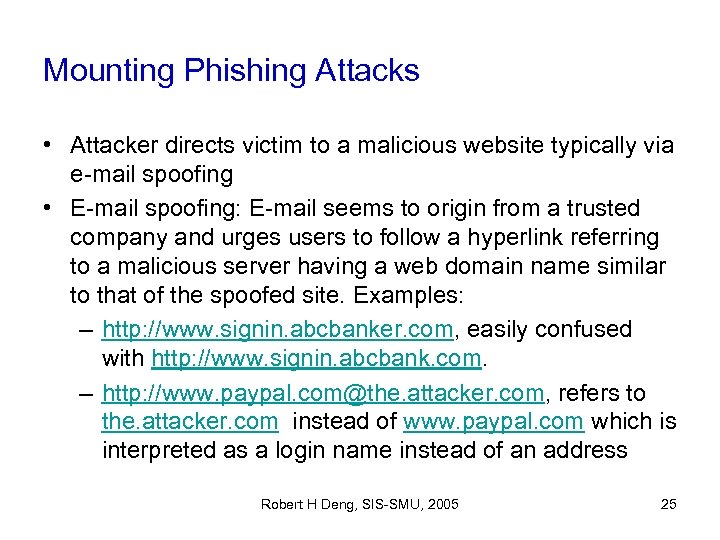
Mounting Phishing Attacks • Attacker directs victim to a malicious website typically via e-mail spoofing • E-mail spoofing: E-mail seems to origin from a trusted company and urges users to follow a hyperlink referring to a malicious server having a web domain name similar to that of the spoofed site. Examples: – http: //www. signin. abcbanker. com, easily confused with http: //www. signin. abcbank. com. – http: //www. paypal. com@the. attacker. com, refers to the. attacker. com instead of www. paypal. com which is interpreted as a login name instead of an address Robert H Deng, SIS-SMU, 2005 25
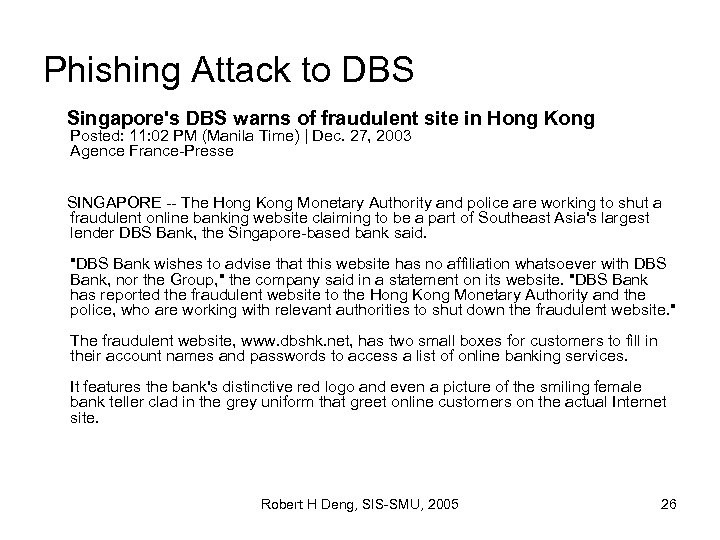
Phishing Attack to DBS Singapore's DBS warns of fraudulent site in Hong Kong Posted: 11: 02 PM (Manila Time) | Dec. 27, 2003 Agence France-Presse SINGAPORE -- The Hong Kong Monetary Authority and police are working to shut a fraudulent online banking website claiming to be a part of Southeast Asia's largest lender DBS Bank, the Singapore-based bank said. "DBS Bank wishes to advise that this website has no affiliation whatsoever with DBS Bank, nor the Group, " the company said in a statement on its website. "DBS Bank has reported the fraudulent website to the Hong Kong Monetary Authority and the police, who are working with relevant authorities to shut down the fraudulent website. " The fraudulent website, www. dbshk. net, has two small boxes for customers to fill in their account names and passwords to access a list of online banking services. It features the bank's distinctive red logo and even a picture of the smiling female bank teller clad in the grey uniform that greet online customers on the actual Internet site. Robert H Deng, SIS-SMU, 2005 26
Outline • Definition of e-banking • Entity authentication and secure communications • Server side architecture & security • Web client security • Web application security Robert H Deng, SIS-SMU, 2005 27
Web Application Security • More and more web based applications; they are becoming one of the major targets for attacks – 70% of new attacks target the web (SQL injection, buffer overflow, etc) • Network based firewalls and IDS are entirely blind to encrypted web traffic • Firewalls let in web traffic through ports 80 and 443 Robert H Deng, SIS-SMU, 2005 28
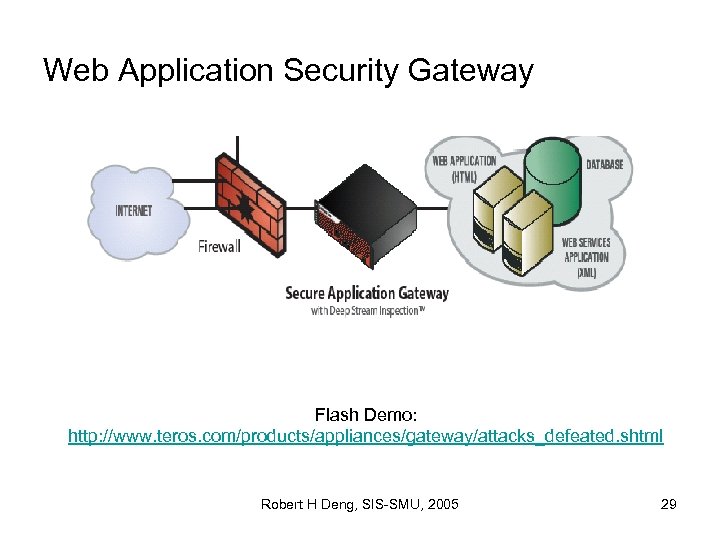
Web Application Security Gateway Flash Demo: http: //www. teros. com/products/appliances/gateway/attacks_defeated. shtml Robert H Deng, SIS-SMU, 2005 29
Summary • Definition of e-banking • Entity authentication and secure communications (the “gap” problem) • Server side architecture & security (DMZ policy rules) • Web client security • Web application security and application security gateway Robert H Deng, SIS-SMU, 2005 30

• Reading assignments: – http: //www. ffiec. gov/ffiecinfobase/html_pages/ ebanking_book_frame. htm Robert H Deng, SIS-SMU, 2005 31
6a6fab2c662620f22ddbad8a5f5f3225.ppt