fb51cc2972359526f32912cd4b20a9f4.ppt
- Количество слайдов: 57
 Lecture 24 Secure Communications CPE 401 / 601 Computer Network Systems Slides are modified from Jim Kurose & Keith Ross
Lecture 24 Secure Communications CPE 401 / 601 Computer Network Systems Slides are modified from Jim Kurose & Keith Ross
 Message Integrity • Allows communicating parties to verify that received messages are authentic – Content of message has not been altered – Source of message is who/what you think it is – Message has not been replayed – Sequence of messages is maintained 2
Message Integrity • Allows communicating parties to verify that received messages are authentic – Content of message has not been altered – Source of message is who/what you think it is – Message has not been replayed – Sequence of messages is maintained 2
 Message Digests • Function H( ) that takes as input an arbitrary length message and outputs a fixed-length string: “message signature” – Note that H( ) is a many-to-1 function • Desirable properties: Message m H: Hash Function – Easy to calculate – Irreversibility: Can’t determine m from H(m) – Collision resistance: Computationally difficult to produce m and m’ such that H(m) = H(m’) – Seemingly random output 3
Message Digests • Function H( ) that takes as input an arbitrary length message and outputs a fixed-length string: “message signature” – Note that H( ) is a many-to-1 function • Desirable properties: Message m H: Hash Function – Easy to calculate – Irreversibility: Can’t determine m from H(m) – Collision resistance: Computationally difficult to produce m and m’ such that H(m) = H(m’) – Seemingly random output 3
 Hash Function Algorithms • MD 5 hash function widely used (RFC 1321) – computes 128 -bit message digest in 4 -step process • SHA-1 is also used – US standard [NIST, FIPS PUB 180 -1] – 160 -bit message digest 4
Hash Function Algorithms • MD 5 hash function widely used (RFC 1321) – computes 128 -bit message digest in 4 -step process • SHA-1 is also used – US standard [NIST, FIPS PUB 180 -1] – 160 -bit message digest 4
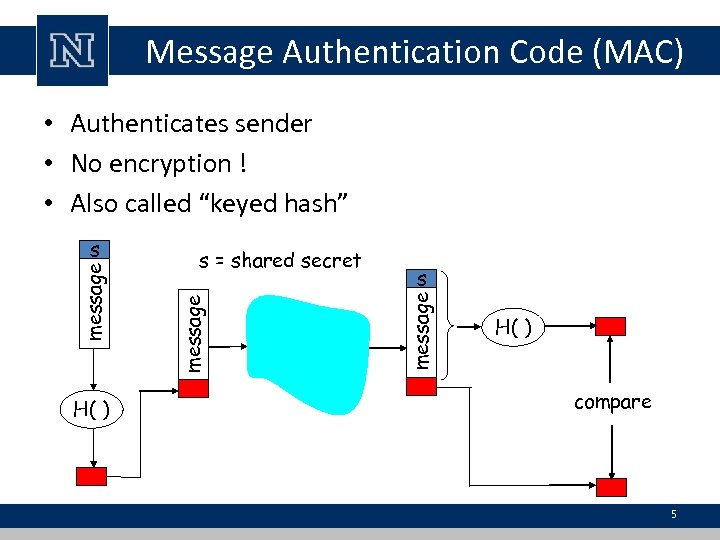 Message Authentication Code (MAC) • Authenticates sender • No encryption ! • Also called “keyed hash” H( ) s message s = shared secret message s H( ) compare 5
Message Authentication Code (MAC) • Authenticates sender • No encryption ! • Also called “keyed hash” H( ) s message s = shared secret message s H( ) compare 5
 End-point authentication • Want to be sure of the originator of the message – end-point authentication • Assuming Alice and Bob have a shared secret, will MAC provide end-point authentication – We do know that Alice created the message – But did she send it? 6
End-point authentication • Want to be sure of the originator of the message – end-point authentication • Assuming Alice and Bob have a shared secret, will MAC provide end-point authentication – We do know that Alice created the message – But did she send it? 6
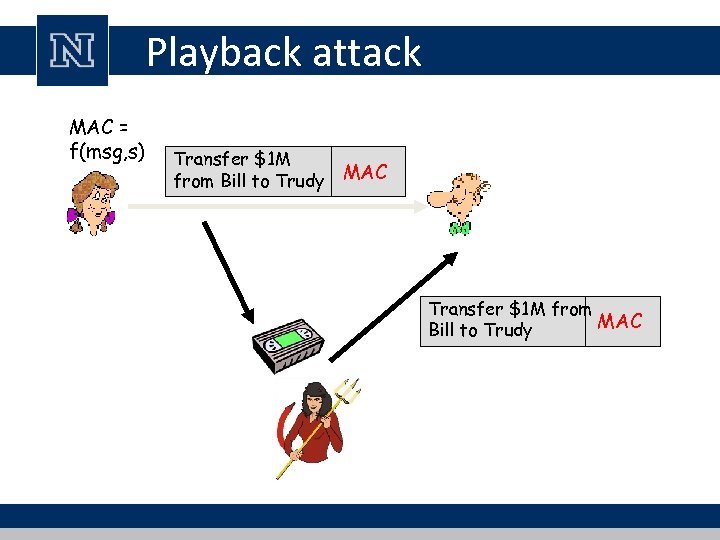 Playback attack MAC = f(msg, s) Transfer $1 M from Bill to Trudy MAC Transfer $1 M from MAC Bill to Trudy
Playback attack MAC = f(msg, s) Transfer $1 M from Bill to Trudy MAC Transfer $1 M from MAC Bill to Trudy
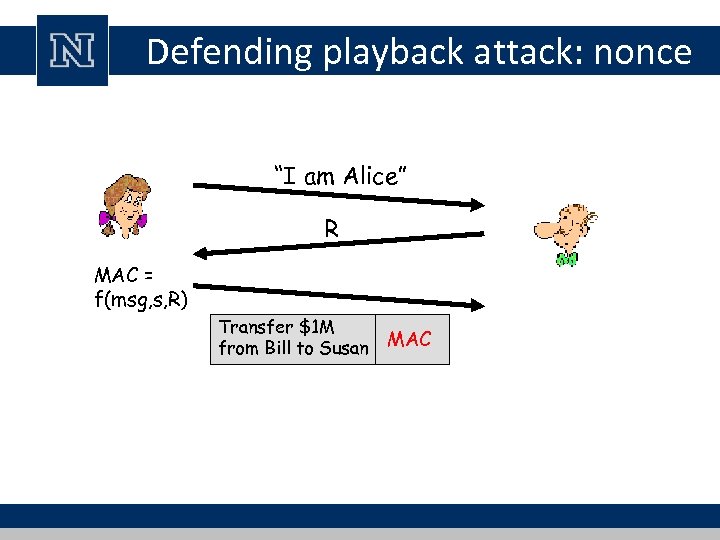 Defending playback attack: nonce “I am Alice” R MAC = f(msg, s, R) Transfer $1 M from Bill to Susan MAC
Defending playback attack: nonce “I am Alice” R MAC = f(msg, s, R) Transfer $1 M from Bill to Susan MAC
 Digital Signatures • Cryptographic technique analogous to handwritten signatures • Goal is similar to that of a MAC, – except now use public-key cryptography • sender (Bob) digitally signs document, – establishing he is document owner/creator • verifiable, nonforgeable: – recipient (Alice) can prove to someone that Bob, and no one else (including Alice), must have signed document 9
Digital Signatures • Cryptographic technique analogous to handwritten signatures • Goal is similar to that of a MAC, – except now use public-key cryptography • sender (Bob) digitally signs document, – establishing he is document owner/creator • verifiable, nonforgeable: – recipient (Alice) can prove to someone that Bob, and no one else (including Alice), must have signed document 9
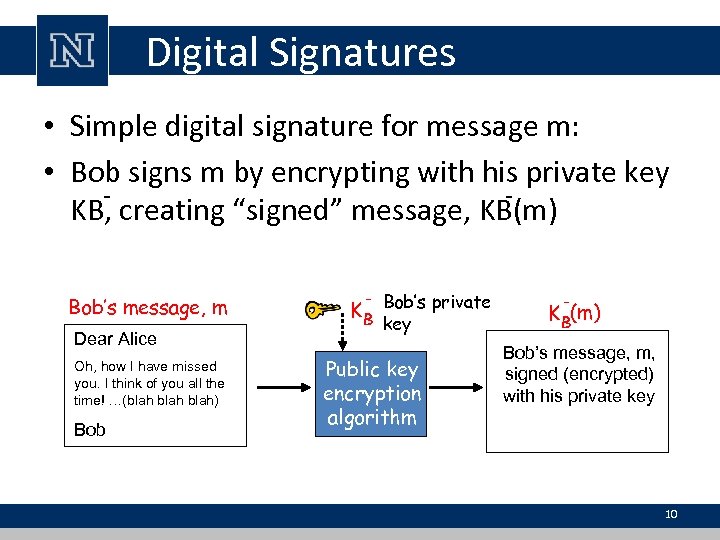 Digital Signatures • Simple digital signature for message m: • Bob signs m by encrypting with his private key KB, creating “signed” message, KB(m) Bob’s message, m Dear Alice Oh, how I have missed you. I think of you all the time! …(blah) Bob - Bob’s private KB key Public key encryption algorithm - K B(m) Bob’s message, m, signed (encrypted) with his private key 10
Digital Signatures • Simple digital signature for message m: • Bob signs m by encrypting with his private key KB, creating “signed” message, KB(m) Bob’s message, m Dear Alice Oh, how I have missed you. I think of you all the time! …(blah) Bob - Bob’s private KB key Public key encryption algorithm - K B(m) Bob’s message, m, signed (encrypted) with his private key 10
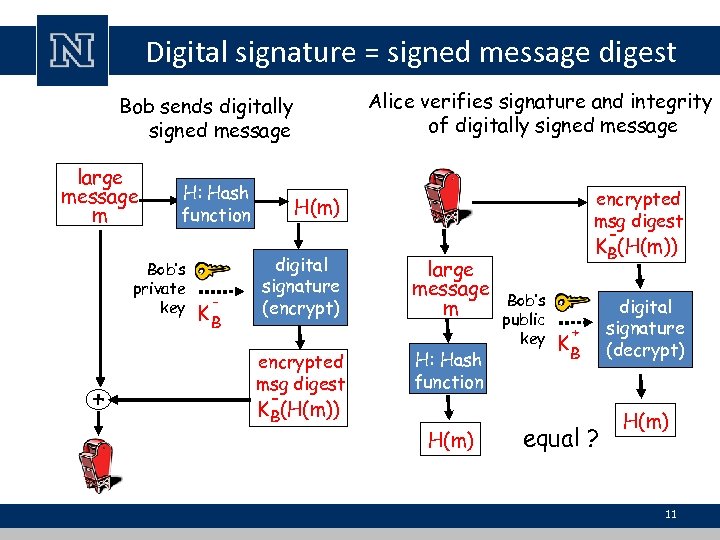 Digital signature = signed message digest Alice verifies signature and integrity of digitally signed message Bob sends digitally signed message large message m H: Hash function Bob’s private key + - KB encrypted msg digest H(m) digital signature (encrypt) encrypted msg digest KB(H(m)) large message m H: Hash function H(m) KB(H(m)) Bob’s public key + KB equal ? digital signature (decrypt) H(m) 11
Digital signature = signed message digest Alice verifies signature and integrity of digitally signed message Bob sends digitally signed message large message m H: Hash function Bob’s private key + - KB encrypted msg digest H(m) digital signature (encrypt) encrypted msg digest KB(H(m)) large message m H: Hash function H(m) KB(H(m)) Bob’s public key + KB equal ? digital signature (decrypt) H(m) 11
 Digital Signatures (more) • Suppose Alice receives msg m with digital signature KB-(m) • Alice verifies m signed by Bob by applying Bob’s public key KB+ to KB-(m) then checks KB+(KB-(m) ) = m. – If KB+(KB-(m) ) = m, whoever signed m must have used Bob’s private key 12
Digital Signatures (more) • Suppose Alice receives msg m with digital signature KB-(m) • Alice verifies m signed by Bob by applying Bob’s public key KB+ to KB-(m) then checks KB+(KB-(m) ) = m. – If KB+(KB-(m) ) = m, whoever signed m must have used Bob’s private key 12
 Digital Signatures (more) • Alice thus verifies that: – Bob signed m. – No one else signed m. – Bob signed m and not m’. • Non-repudiation: – Alice can take m, and signature KB(m) to court and prove that Bob signed m. 13
Digital Signatures (more) • Alice thus verifies that: – Bob signed m. – No one else signed m. – Bob signed m and not m’. • Non-repudiation: – Alice can take m, and signature KB(m) to court and prove that Bob signed m. 13
 Public-key certification • Motivation: Trudy plays pizza prank on Bob – Trudy creates e-mail order: Dear Pizza Store, Please deliver to me four pepperoni pizzas. Thank you, Bob – Trudy signs order with her private key – Trudy sends order to Pizza Store – Trudy sends to Pizza Store her public key, but says it’s Bob’s public key – Pizza Store verifies signature; then delivers four pizzas to Bob 14
Public-key certification • Motivation: Trudy plays pizza prank on Bob – Trudy creates e-mail order: Dear Pizza Store, Please deliver to me four pepperoni pizzas. Thank you, Bob – Trudy signs order with her private key – Trudy sends order to Pizza Store – Trudy sends to Pizza Store her public key, but says it’s Bob’s public key – Pizza Store verifies signature; then delivers four pizzas to Bob 14
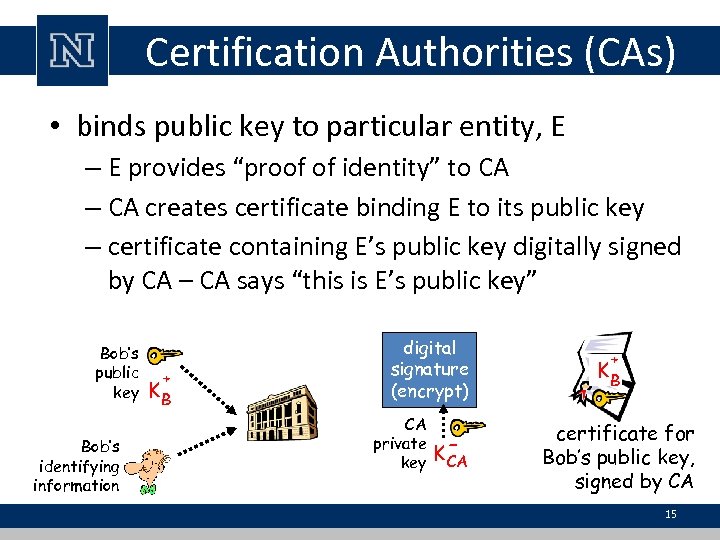 Certification Authorities (CAs) • binds public key to particular entity, E – E provides “proof of identity” to CA – CA creates certificate binding E to its public key – certificate containing E’s public key digitally signed by CA – CA says “this is E’s public key” Bob’s public key Bob’s identifying information + KB digital signature (encrypt) CA private key K- CA + KB certificate for Bob’s public key, signed by CA 15
Certification Authorities (CAs) • binds public key to particular entity, E – E provides “proof of identity” to CA – CA creates certificate binding E to its public key – certificate containing E’s public key digitally signed by CA – CA says “this is E’s public key” Bob’s public key Bob’s identifying information + KB digital signature (encrypt) CA private key K- CA + KB certificate for Bob’s public key, signed by CA 15
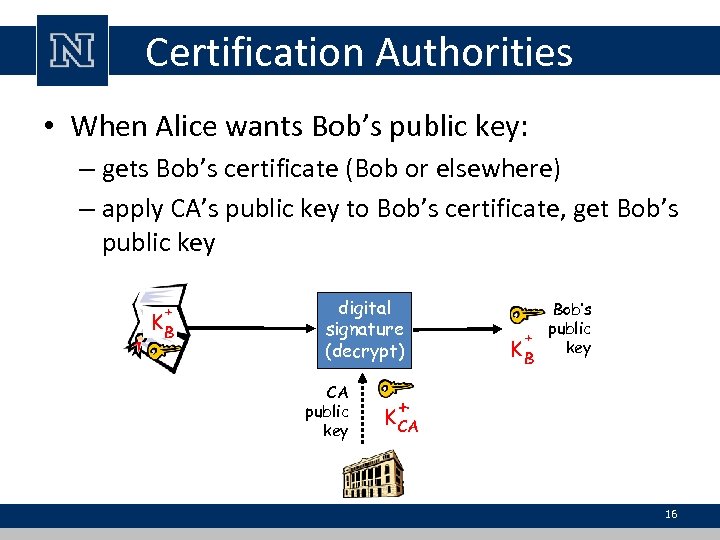 Certification Authorities • When Alice wants Bob’s public key: – gets Bob’s certificate (Bob or elsewhere) – apply CA’s public key to Bob’s certificate, get Bob’s public key + KB digital signature (decrypt) CA public key Bob’s public + key KB + K CA 16
Certification Authorities • When Alice wants Bob’s public key: – gets Bob’s certificate (Bob or elsewhere) – apply CA’s public key to Bob’s certificate, get Bob’s public key + KB digital signature (decrypt) CA public key Bob’s public + key KB + K CA 16
 Certificates • Primary standard X. 509 (RFC 2459) • Certificate contains: – Issuer name – Entity name, address, domain name, etc. – Entity’s public key – Digital signature (signed with issuer’s private key) • Public-Key Infrastructure (PKI) – Certificates and certification authorities 17
Certificates • Primary standard X. 509 (RFC 2459) • Certificate contains: – Issuer name – Entity name, address, domain name, etc. – Entity’s public key – Digital signature (signed with issuer’s private key) • Public-Key Infrastructure (PKI) – Certificates and certification authorities 17
 Secure Sockets Layer
Secure Sockets Layer
 SSL: Secure Sockets Layer • Widely deployed security protocol – Supported by almost all browsers and web servers – Tens of billions $ spent per year over SSL – Originally designed by Netscape in 1993 • Number of variations: – TLS: transport layer security, RFC 2246 • Provides confidentiality, integrity, and authentication 19
SSL: Secure Sockets Layer • Widely deployed security protocol – Supported by almost all browsers and web servers – Tens of billions $ spent per year over SSL – Originally designed by Netscape in 1993 • Number of variations: – TLS: transport layer security, RFC 2246 • Provides confidentiality, integrity, and authentication 19
 SSL: Secure Sockets Layer • Original goals: – Had Web e-commerce transactions in mind – Encryption (especially credit-card numbers) – Web-server authentication – Optional client authentication – Minimum hassle in doing business with new merchant • Available to all TCP applications – Secure socket interface 20
SSL: Secure Sockets Layer • Original goals: – Had Web e-commerce transactions in mind – Encryption (especially credit-card numbers) – Web-server authentication – Optional client authentication – Minimum hassle in doing business with new merchant • Available to all TCP applications – Secure socket interface 20
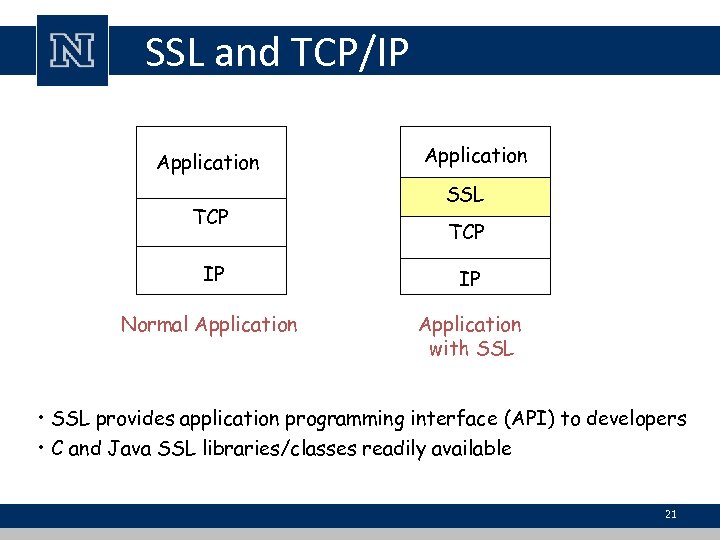 SSL and TCP/IP Application TCP Application SSL TCP IP IP Normal Application with SSL • SSL provides application programming interface (API) to developers • C and Java SSL libraries/classes readily available 21
SSL and TCP/IP Application TCP Application SSL TCP IP IP Normal Application with SSL • SSL provides application programming interface (API) to developers • C and Java SSL libraries/classes readily available 21
 Toy SSL: a simple secure channel • Handshake: Alice and Bob use their certificates and private keys to authenticate each other and exchange shared secret • Key Derivation: Alice and Bob use shared secret to derive set of keys • Data Transfer: Data to be transferred is broken up into a series of records • Connection Closure: Special messages to securely close connection 22
Toy SSL: a simple secure channel • Handshake: Alice and Bob use their certificates and private keys to authenticate each other and exchange shared secret • Key Derivation: Alice and Bob use shared secret to derive set of keys • Data Transfer: Data to be transferred is broken up into a series of records • Connection Closure: Special messages to securely close connection 22
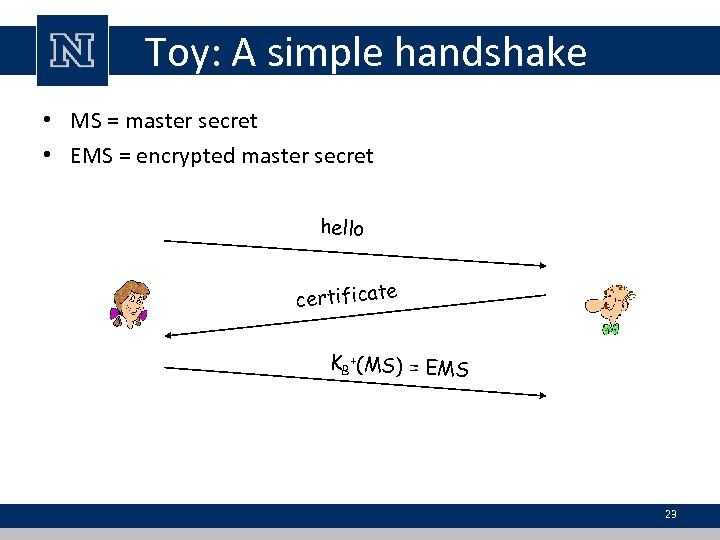 Toy: A simple handshake • MS = master secret • EMS = encrypted master secret hello certificate KB +(MS) = EMS 23
Toy: A simple handshake • MS = master secret • EMS = encrypted master secret hello certificate KB +(MS) = EMS 23
 Toy: Key derivation • Use different keys for message authentication code (MAC) and encryption – – Kc = encryption key for data sent from client to server Mc = MAC key for data sent from client to server Ks = encryption key for data sent from server to client Ms = MAC key for data sent from server to client • Keys derived from key derivation function (KDF) – Takes master secret and (possibly) some additional random data and creates the keys 24
Toy: Key derivation • Use different keys for message authentication code (MAC) and encryption – – Kc = encryption key for data sent from client to server Mc = MAC key for data sent from client to server Ks = encryption key for data sent from server to client Ms = MAC key for data sent from server to client • Keys derived from key derivation function (KDF) – Takes master secret and (possibly) some additional random data and creates the keys 24
 Toy: Data Records • Why not encrypt data in constant stream as we write it to TCP? – Where would we put the MAC? • If at end, no message integrity until all data processed – For example, with instant messaging, how can we do integrity check over all bytes sent before displaying? 25
Toy: Data Records • Why not encrypt data in constant stream as we write it to TCP? – Where would we put the MAC? • If at end, no message integrity until all data processed – For example, with instant messaging, how can we do integrity check over all bytes sent before displaying? 25
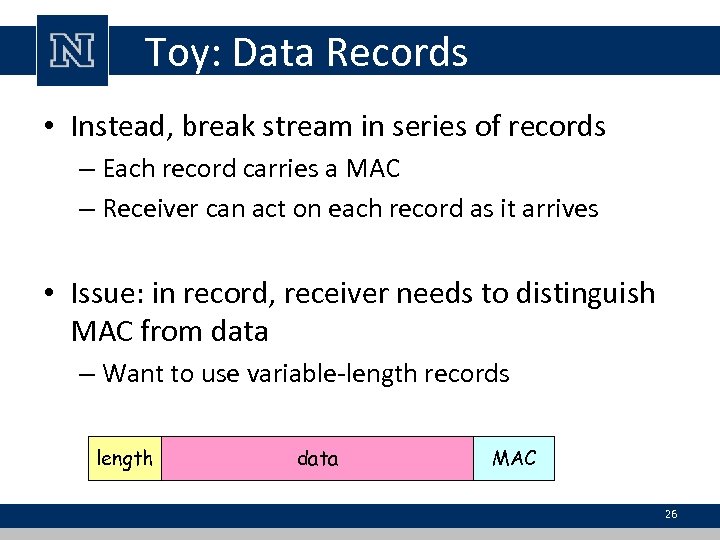 Toy: Data Records • Instead, break stream in series of records – Each record carries a MAC – Receiver can act on each record as it arrives • Issue: in record, receiver needs to distinguish MAC from data – Want to use variable-length records length data MAC 26
Toy: Data Records • Instead, break stream in series of records – Each record carries a MAC – Receiver can act on each record as it arrives • Issue: in record, receiver needs to distinguish MAC from data – Want to use variable-length records length data MAC 26
 Toy: Sequence Numbers • Attacker can capture and replay record or reorder records • Solution: put sequence number into MAC: – MAC = MAC(Mx, sequence||data) – Note: no sequence number field • Attacker could still replay all of the records – Use random nonce 27
Toy: Sequence Numbers • Attacker can capture and replay record or reorder records • Solution: put sequence number into MAC: – MAC = MAC(Mx, sequence||data) – Note: no sequence number field • Attacker could still replay all of the records – Use random nonce 27
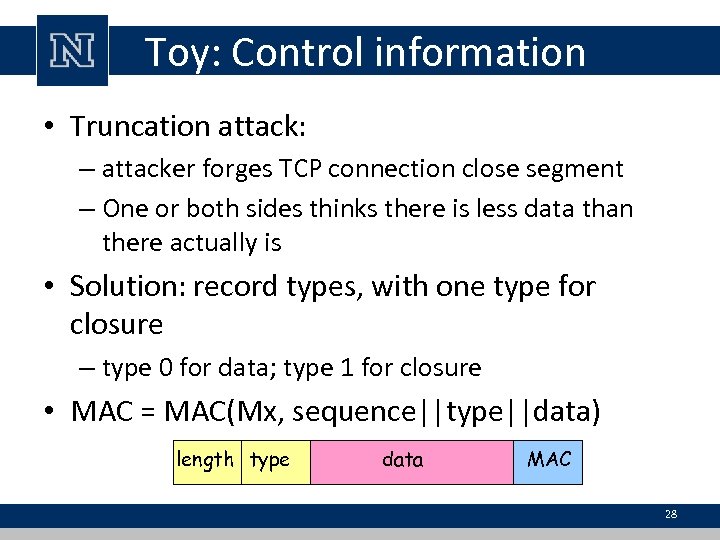 Toy: Control information • Truncation attack: – attacker forges TCP connection close segment – One or both sides thinks there is less data than there actually is • Solution: record types, with one type for closure – type 0 for data; type 1 for closure • MAC = MAC(Mx, sequence||type||data) length type data MAC 28
Toy: Control information • Truncation attack: – attacker forges TCP connection close segment – One or both sides thinks there is less data than there actually is • Solution: record types, with one type for closure – type 0 for data; type 1 for closure • MAC = MAC(Mx, sequence||type||data) length type data MAC 28
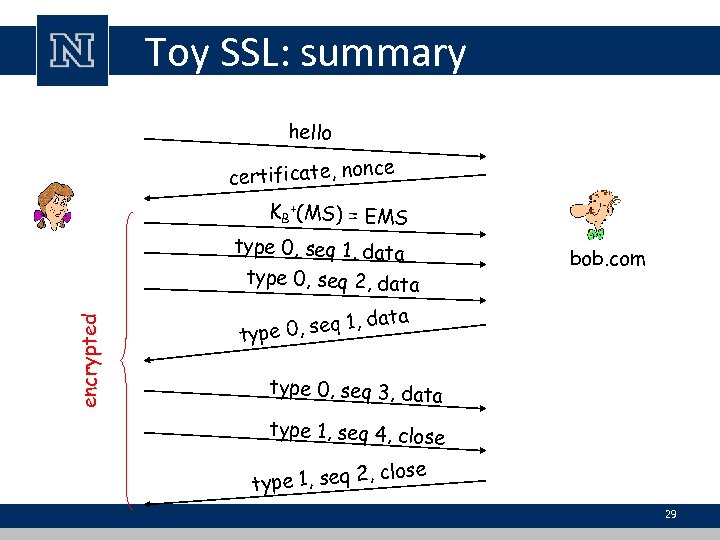 Toy SSL: summary hello ce certificate, non KB +(MS) = EMS type 0, seq 1, data encrypted type 0, seq 2, data bob. com ta , seq 1, da type 0, seq 3, data type 1, seq 4, close type 1, seq 2 29
Toy SSL: summary hello ce certificate, non KB +(MS) = EMS type 0, seq 1, data encrypted type 0, seq 2, data bob. com ta , seq 1, da type 0, seq 3, data type 1, seq 4, close type 1, seq 2 29
 Toy SSL isn’t complete • How long are the fields? • What encryption protocols? • No negotiation – Allow client and server to support different encryption algorithms – Allow client and server to choose together specific algorithm before data transfer 30
Toy SSL isn’t complete • How long are the fields? • What encryption protocols? • No negotiation – Allow client and server to support different encryption algorithms – Allow client and server to choose together specific algorithm before data transfer 30
 Common symmetric ciphers in SSL • • DES – Data Encryption Standard: block 3 DES – Triple strength: block RC 2 – Rivest Cipher 2: block RC 4 – Rivest Cipher 4: stream • Public key encryption • RSA 31
Common symmetric ciphers in SSL • • DES – Data Encryption Standard: block 3 DES – Triple strength: block RC 2 – Rivest Cipher 2: block RC 4 – Rivest Cipher 4: stream • Public key encryption • RSA 31
 SSL Cipher Suite • Cipher Suite – Public-key algorithm – Symmetric encryption algorithm – MAC algorithm • SSL supports a variety of cipher suites • Negotiation: client and server must agree on cipher suite • Client offers choice; server picks one 32
SSL Cipher Suite • Cipher Suite – Public-key algorithm – Symmetric encryption algorithm – MAC algorithm • SSL supports a variety of cipher suites • Negotiation: client and server must agree on cipher suite • Client offers choice; server picks one 32
 Real SSL: Handshake • Purpose – Server authentication – Negotiation: agree on crypto algorithms – Establish keys – Client authentication (optional) • Client sends list of algorithms it supports, along with client nonce • Server chooses algorithms from list; sends back: choice + certificate + server nonce 33
Real SSL: Handshake • Purpose – Server authentication – Negotiation: agree on crypto algorithms – Establish keys – Client authentication (optional) • Client sends list of algorithms it supports, along with client nonce • Server chooses algorithms from list; sends back: choice + certificate + server nonce 33
 Real SSL: Handshake • Client verifies certificate, extracts server’s public key, generates pre_master_secret, encrypts with server’s public key, sends to server • Client and server independently compute encryption and MAC keys from pre_master_secret and nonces • Client sends a MAC of all handshake messages • Server sends a MAC of all handshake messages 34
Real SSL: Handshake • Client verifies certificate, extracts server’s public key, generates pre_master_secret, encrypts with server’s public key, sends to server • Client and server independently compute encryption and MAC keys from pre_master_secret and nonces • Client sends a MAC of all handshake messages • Server sends a MAC of all handshake messages 34
 Real SSL: Handshaking • Last 2 steps protect handshake from tampering • Client typically offers range of algorithms, some strong, some weak • Man-in-the middle could delete the stronger algorithms from list – Last 2 steps prevent this – Last two messages are encrypted 35
Real SSL: Handshaking • Last 2 steps protect handshake from tampering • Client typically offers range of algorithms, some strong, some weak • Man-in-the middle could delete the stronger algorithms from list – Last 2 steps prevent this – Last two messages are encrypted 35
 Real SSL: Handshaking • Why two random nonces? • Suppose Trudy sniffs all messages • Next day, Trudy sets up TCP connection with Bob, sends exact same sequence of records – Bob (Amazon) thinks Alice made two separate orders for the same thing • Solution: Bob sends different random nonce for each connection – Causes encryption keys to be different – Trudy’s messages will fail Bob’s integrity check 36
Real SSL: Handshaking • Why two random nonces? • Suppose Trudy sniffs all messages • Next day, Trudy sets up TCP connection with Bob, sends exact same sequence of records – Bob (Amazon) thinks Alice made two separate orders for the same thing • Solution: Bob sends different random nonce for each connection – Causes encryption keys to be different – Trudy’s messages will fail Bob’s integrity check 36
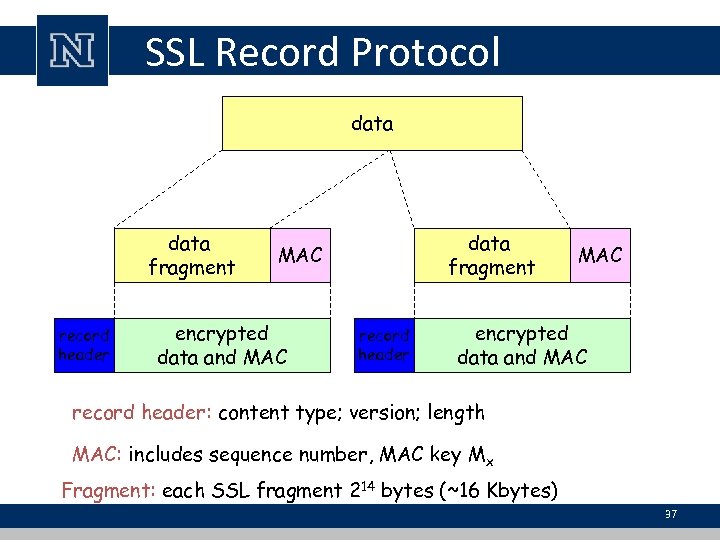 SSL Record Protocol data fragment record header data fragment MAC encrypted data and MAC record header: content type; version; length MAC: includes sequence number, MAC key Mx Fragment: each SSL fragment 214 bytes (~16 Kbytes) 37
SSL Record Protocol data fragment record header data fragment MAC encrypted data and MAC record header: content type; version; length MAC: includes sequence number, MAC key Mx Fragment: each SSL fragment 214 bytes (~16 Kbytes) 37
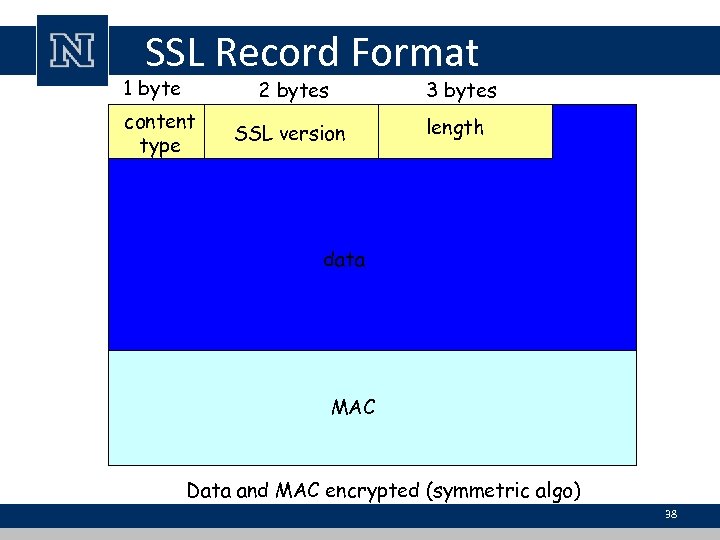 SSL Record Format 1 byte 2 bytes content type 3 bytes SSL version length data MAC Data and MAC encrypted (symmetric algo) 38
SSL Record Format 1 byte 2 bytes content type 3 bytes SSL version length data MAC Data and MAC encrypted (symmetric algo) 38
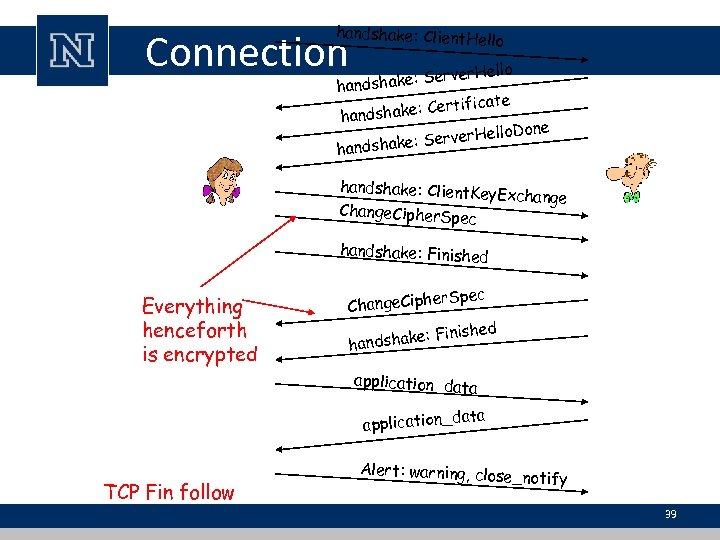 handshake: Client. Hel lo Connection er. Hello hake: Serv hands rtificate dshake: Ce han ello. Done e: Server. H handshake: Client. Key Exchange Change. Cipher. Sp ec handshake: Finished Everything henceforth is encrypted r. Spec Change. Ciphe inished dshake: F han application_data application_d TCP Fin follow Alert: warning, close_ notify 39
handshake: Client. Hel lo Connection er. Hello hake: Serv hands rtificate dshake: Ce han ello. Done e: Server. H handshake: Client. Key Exchange Change. Cipher. Sp ec handshake: Finished Everything henceforth is encrypted r. Spec Change. Ciphe inished dshake: F han application_data application_d TCP Fin follow Alert: warning, close_ notify 39
 IPsec
IPsec
 What is confidentiality at network-layer? • Between two network entities: • Sending entity encrypts the payloads of datagrams – Payload could be TCP segment, UDP segment, ICMP message, OSPF message, and so on • All data sent from one entity to the other would be hidden – Web pages, e-mail, P 2 P file transfers, TCP SYN packets, and so on • That is, “blanket coverage” 41
What is confidentiality at network-layer? • Between two network entities: • Sending entity encrypts the payloads of datagrams – Payload could be TCP segment, UDP segment, ICMP message, OSPF message, and so on • All data sent from one entity to the other would be hidden – Web pages, e-mail, P 2 P file transfers, TCP SYN packets, and so on • That is, “blanket coverage” 41
 Virtual Private Networks (VPNs) • Institutions often want private networks for security. – Costly! Separate routers, links, DNS infrastructure • With a VPN, institution’s inter-office traffic is sent over public Internet instead – But inter-office traffic is encrypted before entering public Internet 42
Virtual Private Networks (VPNs) • Institutions often want private networks for security. – Costly! Separate routers, links, DNS infrastructure • With a VPN, institution’s inter-office traffic is sent over public Internet instead – But inter-office traffic is encrypted before entering public Internet 42
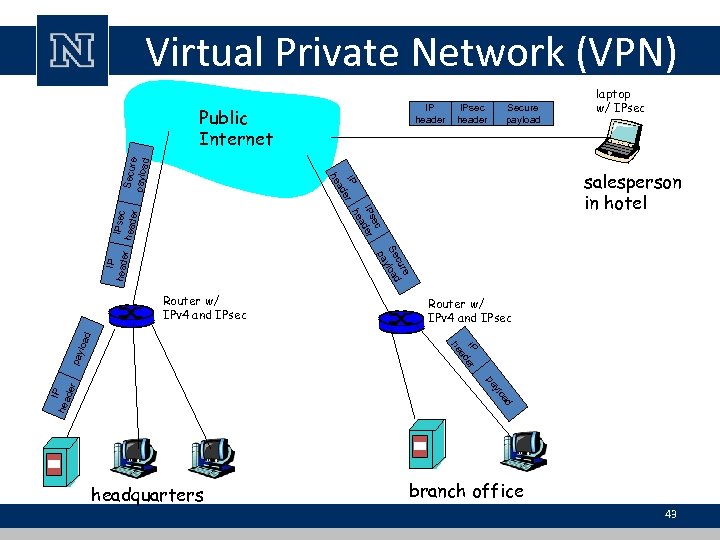 Virtual Private Network (VPN) IP header Secure payload IP er ad ec IPs der a he IPsec heade r laptop w/ IPsec salesperson in hotel he Secur e payloa d Public Internet IPsec header IP heade r re cu Se load y pa IP er ad pay Router w/ IPv 4 and IPsec he loa d Router w/ IPv 4 and IPsec ylo IP hea der pa ad headquarters branch office 43
Virtual Private Network (VPN) IP header Secure payload IP er ad ec IPs der a he IPsec heade r laptop w/ IPsec salesperson in hotel he Secur e payloa d Public Internet IPsec header IP heade r re cu Se load y pa IP er ad pay Router w/ IPv 4 and IPsec he loa d Router w/ IPv 4 and IPsec ylo IP hea der pa ad headquarters branch office 43
 IPsec services • • Data integrity Origin authentication Replay attack prevention Confidentiality • Two protocols providing different service models: – Authentication Header – Encapsulation Security Protocol 44
IPsec services • • Data integrity Origin authentication Replay attack prevention Confidentiality • Two protocols providing different service models: – Authentication Header – Encapsulation Security Protocol 44
 IPsec Transport Mode • IPsec datagram emitted and received by endsystem • Protects upper level protocols IPsec 45
IPsec Transport Mode • IPsec datagram emitted and received by endsystem • Protects upper level protocols IPsec 45
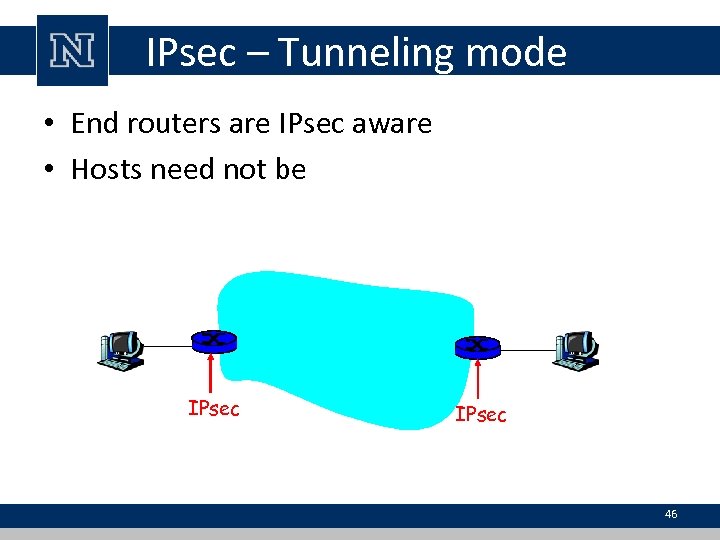 IPsec – Tunneling mode • End routers are IPsec aware • Hosts need not be IPsec 46
IPsec – Tunneling mode • End routers are IPsec aware • Hosts need not be IPsec 46
 Two protocols • Authentication Header (AH) protocol – provides source authentication & data integrity but not confidentiality • Encapsulation Security Protocol (ESP) – provides source authentication, data integrity, and confidentiality – more widely used than AH 47
Two protocols • Authentication Header (AH) protocol – provides source authentication & data integrity but not confidentiality • Encapsulation Security Protocol (ESP) – provides source authentication, data integrity, and confidentiality – more widely used than AH 47
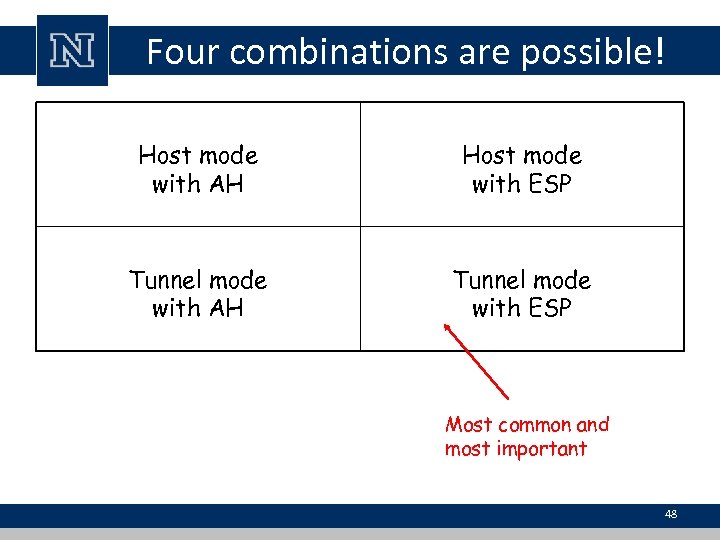 Four combinations are possible! Host mode with AH Host mode with ESP Tunnel mode with AH Tunnel mode with ESP Most common and most important 48
Four combinations are possible! Host mode with AH Host mode with ESP Tunnel mode with AH Tunnel mode with ESP Most common and most important 48
 Security associations (SAs) • Before sending data, a virtual connection is established from sending entity to receiving entity • Called “security association (SA)” – SAs are simplex: for only one direction • Both sending and receiving entites maintain state information about the SA – TCP endpoints also maintain state information – IP is connectionless; – IPsec is connection-oriented! 49
Security associations (SAs) • Before sending data, a virtual connection is established from sending entity to receiving entity • Called “security association (SA)” – SAs are simplex: for only one direction • Both sending and receiving entites maintain state information about the SA – TCP endpoints also maintain state information – IP is connectionless; – IPsec is connection-oriented! 49
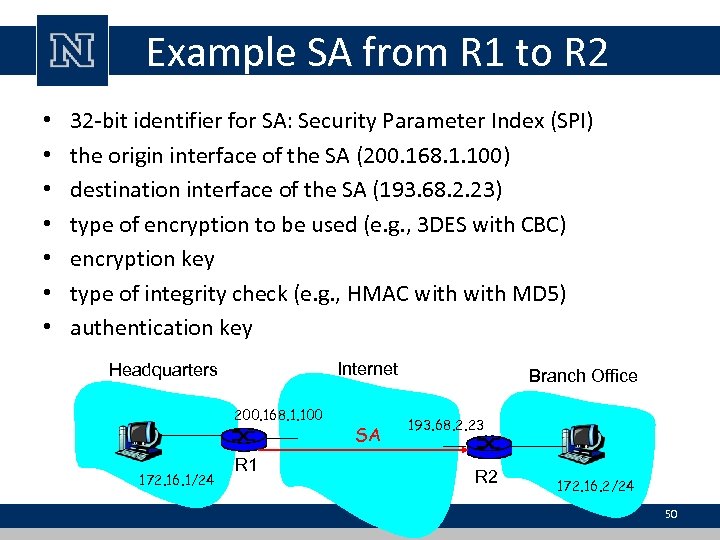 Example SA from R 1 to R 2 • • 32 -bit identifier for SA: Security Parameter Index (SPI) the origin interface of the SA (200. 168. 1. 100) destination interface of the SA (193. 68. 2. 23) type of encryption to be used (e. g. , 3 DES with CBC) encryption key type of integrity check (e. g. , HMAC with MD 5) authentication key Internet Headquarters 200. 168. 1. 100 172. 16. 1/24 R 1 SA Branch Office 193. 68. 2. 23 R 2 172. 16. 2/24 50
Example SA from R 1 to R 2 • • 32 -bit identifier for SA: Security Parameter Index (SPI) the origin interface of the SA (200. 168. 1. 100) destination interface of the SA (193. 68. 2. 23) type of encryption to be used (e. g. , 3 DES with CBC) encryption key type of integrity check (e. g. , HMAC with MD 5) authentication key Internet Headquarters 200. 168. 1. 100 172. 16. 1/24 R 1 SA Branch Office 193. 68. 2. 23 R 2 172. 16. 2/24 50
 Security Association Database (SAD) • Endpoint holds state of its SAs in a SAD, – where it can locate them during processing • When sending IPsec datagram – R 1 accesses SAD to determine how to process datagram • When IPsec datagram arrives to R 2 – R 2 examines SPI in IPsec datagram – indexes SAD with SPI – processes datagram accordingly 51
Security Association Database (SAD) • Endpoint holds state of its SAs in a SAD, – where it can locate them during processing • When sending IPsec datagram – R 1 accesses SAD to determine how to process datagram • When IPsec datagram arrives to R 2 – R 2 examines SPI in IPsec datagram – indexes SAD with SPI – processes datagram accordingly 51
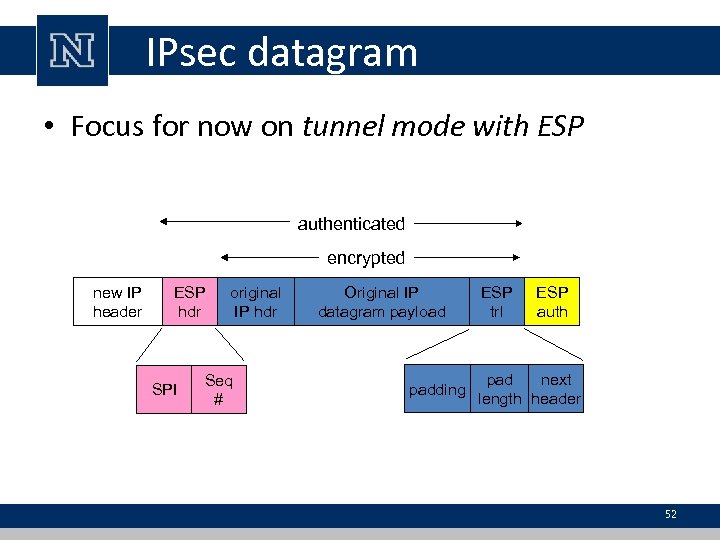 IPsec datagram • Focus for now on tunnel mode with ESP authenticated encrypted new IP header ESP hdr SPI original IP hdr Seq # Original IP datagram payload padding ESP trl ESP auth pad next length header 52
IPsec datagram • Focus for now on tunnel mode with ESP authenticated encrypted new IP header ESP hdr SPI original IP hdr Seq # Original IP datagram payload padding ESP trl ESP auth pad next length header 52
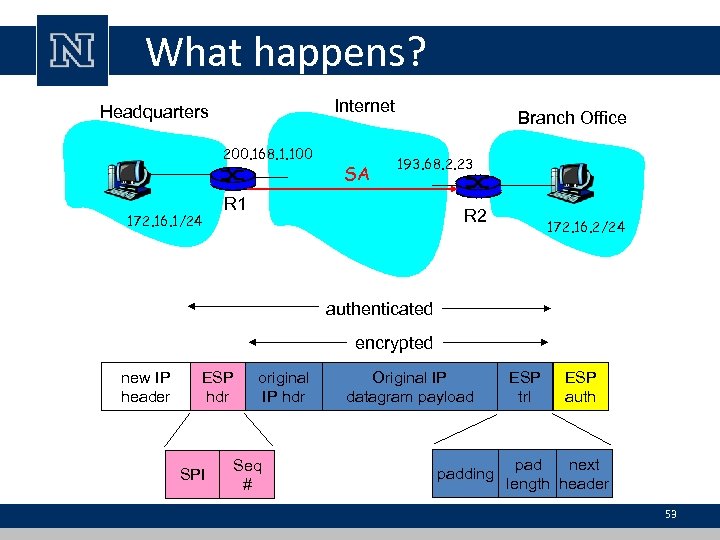 What happens? Internet Headquarters 200. 168. 1. 100 172. 16. 1/24 SA Branch Office 193. 68. 2. 23 R 1 R 2 172. 16. 2/24 authenticated encrypted new IP header ESP hdr SPI original IP hdr Seq # Original IP datagram payload padding ESP trl ESP auth pad next length header 53
What happens? Internet Headquarters 200. 168. 1. 100 172. 16. 1/24 SA Branch Office 193. 68. 2. 23 R 1 R 2 172. 16. 2/24 authenticated encrypted new IP header ESP hdr SPI original IP hdr Seq # Original IP datagram payload padding ESP trl ESP auth pad next length header 53
 R 1 converts IP into IPsec datagram • Appends “ESP trailer” to back of original datagram – already includes original header fields! • Encrypts result using algorithm & key specified by SA • Appends to front of this encrypted quantity the “ESP header” • Creates authentication MAC over whole datagram, using algorithm and key specified in SA • Appends MAC to back of datagram, forming payload • Creates brand new IP header, with all classic header fields – which it appends before payload 54
R 1 converts IP into IPsec datagram • Appends “ESP trailer” to back of original datagram – already includes original header fields! • Encrypts result using algorithm & key specified by SA • Appends to front of this encrypted quantity the “ESP header” • Creates authentication MAC over whole datagram, using algorithm and key specified in SA • Appends MAC to back of datagram, forming payload • Creates brand new IP header, with all classic header fields – which it appends before payload 54
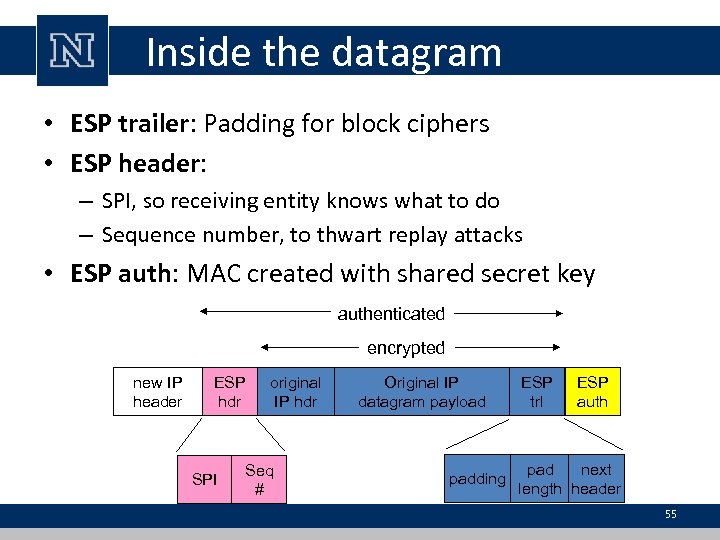 Inside the datagram • ESP trailer: Padding for block ciphers • ESP header: – SPI, so receiving entity knows what to do – Sequence number, to thwart replay attacks • ESP auth: MAC created with shared secret key authenticated encrypted new IP header ESP hdr SPI original IP hdr Seq # Original IP datagram payload padding ESP trl ESP auth pad next length header 55
Inside the datagram • ESP trailer: Padding for block ciphers • ESP header: – SPI, so receiving entity knows what to do – Sequence number, to thwart replay attacks • ESP auth: MAC created with shared secret key authenticated encrypted new IP header ESP hdr SPI original IP hdr Seq # Original IP datagram payload padding ESP trl ESP auth pad next length header 55
 Security Policy Database (SPD) • Policy: For a given datagram, sending entity needs to know if it should use IPsec • Needs also to know which SA to use – May use: source and destination IP address; protocol number • Info in SPD indicates “what” to do with arriving datagram • Info in the SAD indicates “how” to do it 56
Security Policy Database (SPD) • Policy: For a given datagram, sending entity needs to know if it should use IPsec • Needs also to know which SA to use – May use: source and destination IP address; protocol number • Info in SPD indicates “what” to do with arriving datagram • Info in the SAD indicates “how” to do it 56
 Summary: IPsec services • Suppose Trudy sits somewhere between R 1 and R 2. She doesn’t know the keys. – Will Trudy be able to see contents of original datagram? – How about source, dest IP address, transport protocol, application port? – Flip bits without detection? – Masquerade as R 1 using R 1’s IP address? – Replay a datagram? 57
Summary: IPsec services • Suppose Trudy sits somewhere between R 1 and R 2. She doesn’t know the keys. – Will Trudy be able to see contents of original datagram? – How about source, dest IP address, transport protocol, application port? – Flip bits without detection? – Masquerade as R 1 using R 1’s IP address? – Replay a datagram? 57


