73abb999d0c4cd25c9ab65d4f5baff16.ppt
- Количество слайдов: 22
 LCAS and LCMAPS David Groep, Oscar Koeroo, Wim Som de Cerff, Martijn Steenbakkers, Gerben Venekamp NIKHEF grid meeting 1 December 2003
LCAS and LCMAPS David Groep, Oscar Koeroo, Wim Som de Cerff, Martijn Steenbakkers, Gerben Venekamp NIKHEF grid meeting 1 December 2003
 Talk Outline u Introduction n on Auth. N & Auth. Z in EDG Why do we need VOMS, LCAS, LCMAPS … ? u Gridification architecture u LCAS n Architecture, plug-ins, examples u LCMAPS n Architecture, plug-ins n Policy languange (PDL) n examples u Job Repository u Status and Future Developments NIKHEF Grid meeting – LCAS and LCMAPS – n° 2
Talk Outline u Introduction n on Auth. N & Auth. Z in EDG Why do we need VOMS, LCAS, LCMAPS … ? u Gridification architecture u LCAS n Architecture, plug-ins, examples u LCMAPS n Architecture, plug-ins n Policy languange (PDL) n examples u Job Repository u Status and Future Developments NIKHEF Grid meeting – LCAS and LCMAPS – n° 2
 Auth. N & Auth. Z in EDG (1) u GLOBUS n Authentication: Grid Security Infrastructure (GSI) s s s n X 509 certificates (PKI), Certificate Authorities Mutual authentication Single sign-on, proxy delegation Authorization: grid-mapfile s s Grid credentials (user’s Certificate) to local credentials (unix account) mapping “Boolean” authorization Information provided via VO-LDAP servers (EDG) Managed “manually” by the resource admin (via mkgridmap, EDG) u Problems n No centralization n No scalability n Lack of flexibility u Problems addressed by VOMS, LCAS/LCMAPS NIKHEF Grid meeting – LCAS and LCMAPS – n° 3
Auth. N & Auth. Z in EDG (1) u GLOBUS n Authentication: Grid Security Infrastructure (GSI) s s s n X 509 certificates (PKI), Certificate Authorities Mutual authentication Single sign-on, proxy delegation Authorization: grid-mapfile s s Grid credentials (user’s Certificate) to local credentials (unix account) mapping “Boolean” authorization Information provided via VO-LDAP servers (EDG) Managed “manually” by the resource admin (via mkgridmap, EDG) u Problems n No centralization n No scalability n Lack of flexibility u Problems addressed by VOMS, LCAS/LCMAPS NIKHEF Grid meeting – LCAS and LCMAPS – n° 3
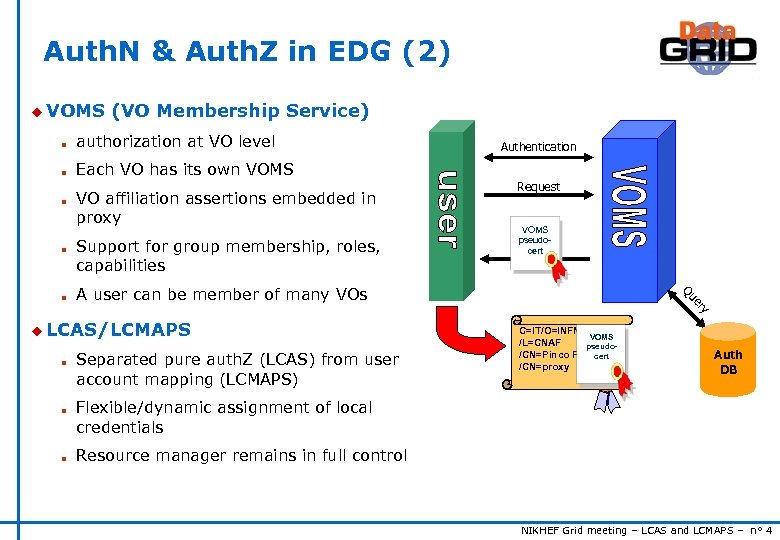 Auth. N & Auth. Z in EDG (2) u VOMS (VO Membership Service) n authorization at VO level n Each VO has its own VOMS n n Support for group membership, roles, capabilities Request VOMS pseudocert A user can be member of many VOs y er Qu n VO affiliation assertions embedded in proxy Authentication u LCAS/LCMAPS n n n Separated pure auth. Z (LCAS) from user account mapping (LCMAPS) C=IT/O=INFN VOMS /L=CNAF pseudo/CN=Pinco Pallacert /CN=proxy Auth DB Flexible/dynamic assignment of local credentials Resource manager remains in full control NIKHEF Grid meeting – LCAS and LCMAPS – n° 4
Auth. N & Auth. Z in EDG (2) u VOMS (VO Membership Service) n authorization at VO level n Each VO has its own VOMS n n Support for group membership, roles, capabilities Request VOMS pseudocert A user can be member of many VOs y er Qu n VO affiliation assertions embedded in proxy Authentication u LCAS/LCMAPS n n n Separated pure auth. Z (LCAS) from user account mapping (LCMAPS) C=IT/O=INFN VOMS /L=CNAF pseudo/CN=Pinco Pallacert /CN=proxy Auth DB Flexible/dynamic assignment of local credentials Resource manager remains in full control NIKHEF Grid meeting – LCAS and LCMAPS – n° 4
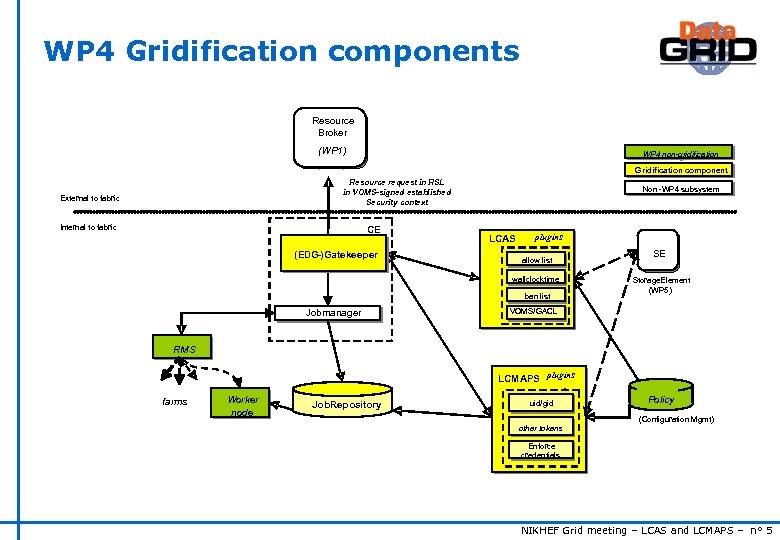 WP 4 Gridification components Resource Broker Resource (WP 1) Broker (WP 1) WP 4 non-gridification Gridification component Resource request in RSL in VOMS-signed established Security context External to fabric Internal to fabric CE (EDG-)Gatekeeper Non -WP 4 subsystem LCAS plugins - allow list wallclocktime ban list Jobmanager SE SE Storage. Element (WP 5) VOMS/GACL RMS LCMAPS plugins farms Worker node Job. Repository uid/gid Policy (Configuration Mgmt) other tokens Enforce credentials NIKHEF Grid meeting – LCAS and LCMAPS – n° 5
WP 4 Gridification components Resource Broker Resource (WP 1) Broker (WP 1) WP 4 non-gridification Gridification component Resource request in RSL in VOMS-signed established Security context External to fabric Internal to fabric CE (EDG-)Gatekeeper Non -WP 4 subsystem LCAS plugins - allow list wallclocktime ban list Jobmanager SE SE Storage. Element (WP 5) VOMS/GACL RMS LCMAPS plugins farms Worker node Job. Repository uid/gid Policy (Configuration Mgmt) other tokens Enforce credentials NIKHEF Grid meeting – LCAS and LCMAPS – n° 5
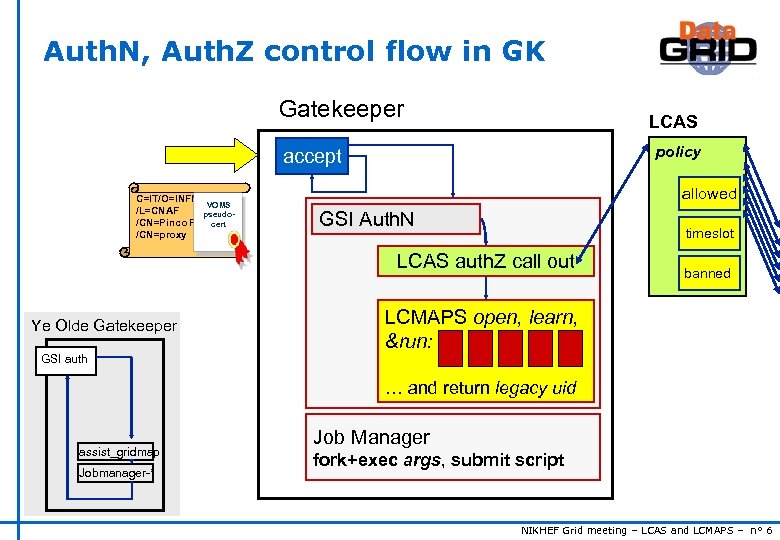 Auth. N, Auth. Z control flow in GK Gatekeeper LCAS policy accept C=IT/O=INFN VOMS /L=CNAF pseudo/CN=Pinco Pallacert /CN=proxy allowed GSI Auth. N timeslot LCAS auth. Z call out Ye Olde Gatekeeper banned LCMAPS open, learn, &run: GSI auth … and return legacy uid assist_gridmap Jobmanager-* Job Manager fork+exec args, submit script NIKHEF Grid meeting – LCAS and LCMAPS – n° 6
Auth. N, Auth. Z control flow in GK Gatekeeper LCAS policy accept C=IT/O=INFN VOMS /L=CNAF pseudo/CN=Pinco Pallacert /CN=proxy allowed GSI Auth. N timeslot LCAS auth. Z call out Ye Olde Gatekeeper banned LCMAPS open, learn, &run: GSI auth … and return legacy uid assist_gridmap Jobmanager-* Job Manager fork+exec args, submit script NIKHEF Grid meeting – LCAS and LCMAPS – n° 6
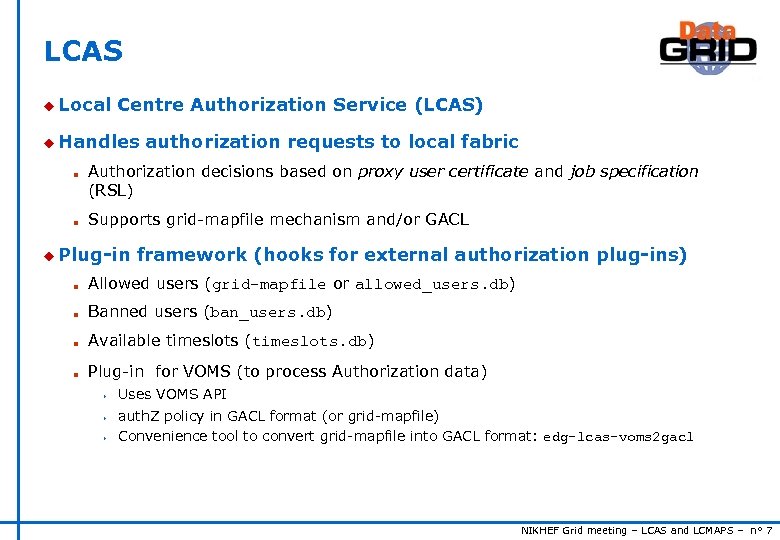 LCAS u Local Centre Authorization Service (LCAS) u Handles n n authorization requests to local fabric Authorization decisions based on proxy user certificate and job specification (RSL) Supports grid-mapfile mechanism and/or GACL u Plug-in framework (hooks for external authorization plug-ins) n Allowed users (grid-mapfile or allowed_users. db) n Banned users (ban_users. db) n Available timeslots (timeslots. db) n Plug-in for VOMS (to process Authorization data) s s s Uses VOMS API auth. Z policy in GACL format (or grid-mapfile) Convenience tool to convert grid-mapfile into GACL format: edg-lcas-voms 2 gacl NIKHEF Grid meeting – LCAS and LCMAPS – n° 7
LCAS u Local Centre Authorization Service (LCAS) u Handles n n authorization requests to local fabric Authorization decisions based on proxy user certificate and job specification (RSL) Supports grid-mapfile mechanism and/or GACL u Plug-in framework (hooks for external authorization plug-ins) n Allowed users (grid-mapfile or allowed_users. db) n Banned users (ban_users. db) n Available timeslots (timeslots. db) n Plug-in for VOMS (to process Authorization data) s s s Uses VOMS API auth. Z policy in GACL format (or grid-mapfile) Convenience tool to convert grid-mapfile into GACL format: edg-lcas-voms 2 gacl NIKHEF Grid meeting – LCAS and LCMAPS – n° 7
 LCAS - ban_user. db # This file contains the globus user ids that are BANNED from this fabric "/O=dutchgrid/O=users/O=nikhef/CN=Jeffrey Templon" NIKHEF Grid meeting – LCAS and LCMAPS – n° 8
LCAS - ban_user. db # This file contains the globus user ids that are BANNED from this fabric "/O=dutchgrid/O=users/O=nikhef/CN=Jeffrey Templon" NIKHEF Grid meeting – LCAS and LCMAPS – n° 8
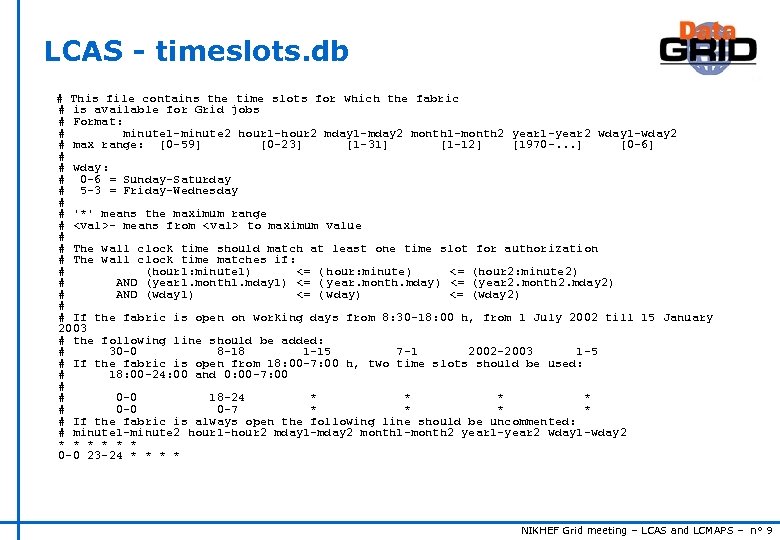 LCAS - timeslots. db # This file contains the time slots for which the fabric # is available for Grid jobs # Format: # minute 1 -minute 2 hour 1 -hour 2 mday 1 -mday 2 month 1 -month 2 year 1 -year 2 wday 1 -wday 2 # max range: [0 -59] [0 -23] [1 -31] [1 -12] [1970 -. . . ] [0 -6] # # wday: # 0 -6 = Sunday-Saturday # 5 -3 = Friday-Wednesday # # '*' means the maximum range #
LCAS - timeslots. db # This file contains the time slots for which the fabric # is available for Grid jobs # Format: # minute 1 -minute 2 hour 1 -hour 2 mday 1 -mday 2 month 1 -month 2 year 1 -year 2 wday 1 -wday 2 # max range: [0 -59] [0 -23] [1 -31] [1 -12] [1970 -. . . ] [0 -6] # # wday: # 0 -6 = Sunday-Saturday # 5 -3 = Friday-Wednesday # # '*' means the maximum range #
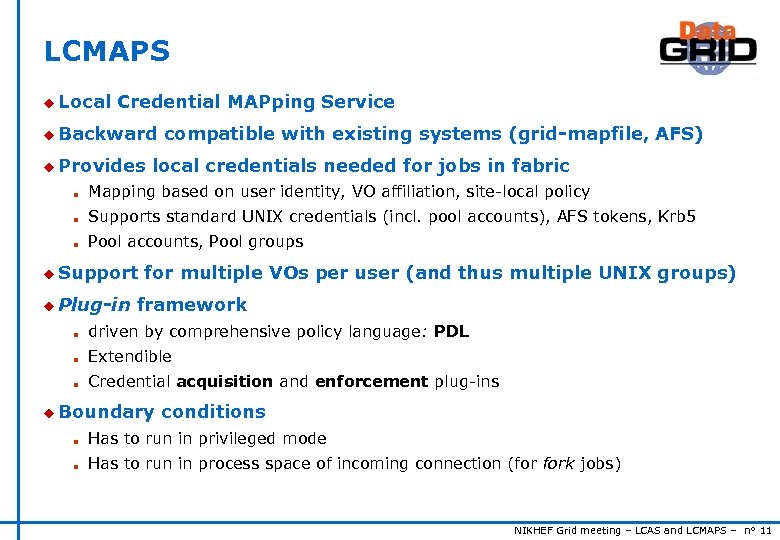 LCMAPS u Local Credential MAPping Service u Backward u Provides compatible with existing systems (grid-mapfile, AFS) local credentials needed for jobs in fabric n Mapping based on user identity, VO affiliation, site-local policy n Supports standard UNIX credentials (incl. pool accounts), AFS tokens, Krb 5 n Pool accounts, Pool groups u Support u Plug-in for multiple VOs per user (and thus multiple UNIX groups) framework n driven by comprehensive policy language: PDL n Extendible n Credential acquisition and enforcement plug-ins u Boundary conditions n Has to run in privileged mode n Has to run in process space of incoming connection (for fork jobs) NIKHEF Grid meeting – LCAS and LCMAPS – n° 11
LCMAPS u Local Credential MAPping Service u Backward u Provides compatible with existing systems (grid-mapfile, AFS) local credentials needed for jobs in fabric n Mapping based on user identity, VO affiliation, site-local policy n Supports standard UNIX credentials (incl. pool accounts), AFS tokens, Krb 5 n Pool accounts, Pool groups u Support u Plug-in for multiple VOs per user (and thus multiple UNIX groups) framework n driven by comprehensive policy language: PDL n Extendible n Credential acquisition and enforcement plug-ins u Boundary conditions n Has to run in privileged mode n Has to run in process space of incoming connection (for fork jobs) NIKHEF Grid meeting – LCAS and LCMAPS – n° 11
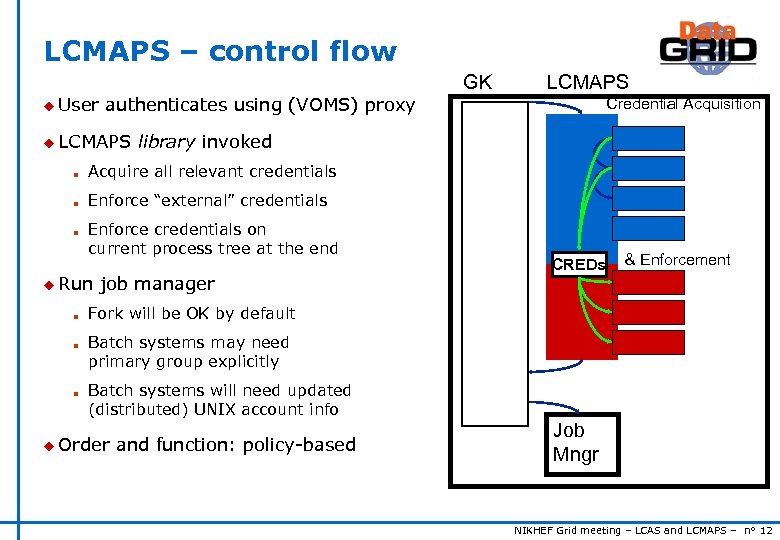 LCMAPS – control flow GK u User LCMAPS authenticates using (VOMS) proxy u LCMAPS Credential Acquisition library invoked n Acquire all relevant credentials n Enforce “external” credentials n Enforce credentials on current process tree at the end u Run n job manager CREDs & Enforcement Fork will be OK by default Batch systems may need primary group explicitly Batch systems will need updated (distributed) UNIX account info u Order and function: policy-based Job Mngr NIKHEF Grid meeting – LCAS and LCMAPS – n° 12
LCMAPS – control flow GK u User LCMAPS authenticates using (VOMS) proxy u LCMAPS Credential Acquisition library invoked n Acquire all relevant credentials n Enforce “external” credentials n Enforce credentials on current process tree at the end u Run n job manager CREDs & Enforcement Fork will be OK by default Batch systems may need primary group explicitly Batch systems will need updated (distributed) UNIX account info u Order and function: policy-based Job Mngr NIKHEF Grid meeting – LCAS and LCMAPS – n° 12
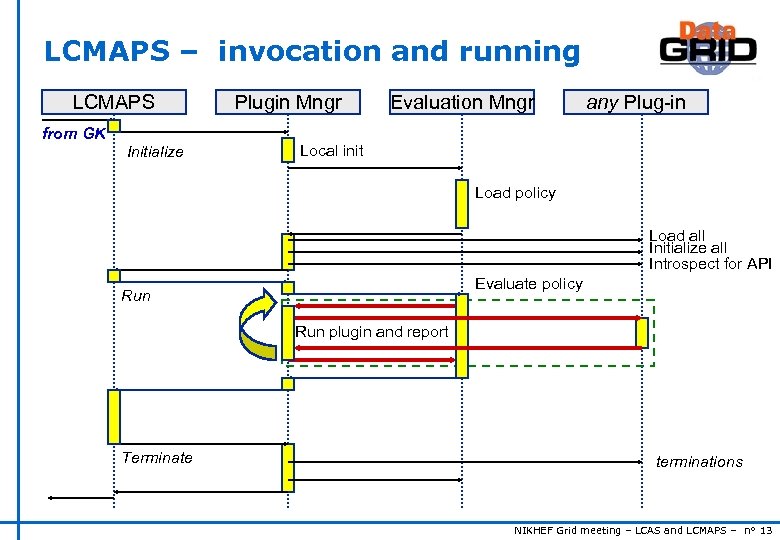 LCMAPS – invocation and running LCMAPS from GK Initialize Plugin Mngr Evaluation Mngr any Plug-in Local init Load policy Load all Initialize all Introspect for API Evaluate policy Run plugin and report Terminate terminations NIKHEF Grid meeting – LCAS and LCMAPS – n° 13
LCMAPS – invocation and running LCMAPS from GK Initialize Plugin Mngr Evaluation Mngr any Plug-in Local init Load policy Load all Initialize all Introspect for API Evaluate policy Run plugin and report Terminate terminations NIKHEF Grid meeting – LCAS and LCMAPS – n° 13
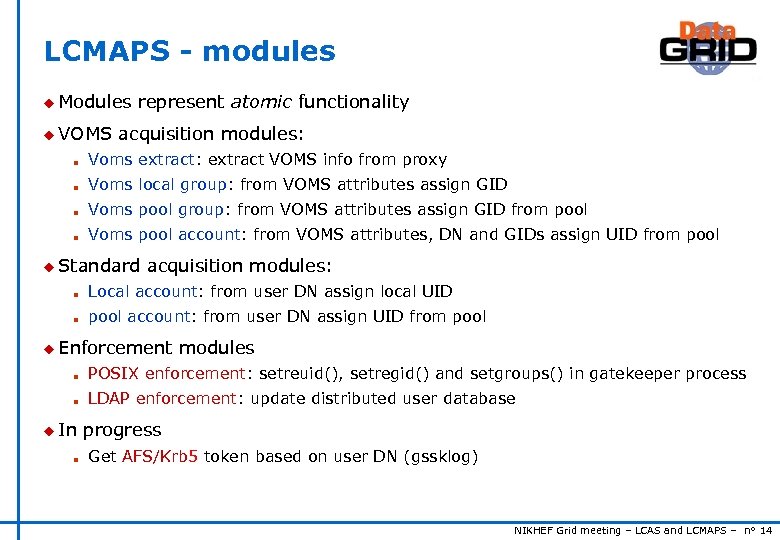 LCMAPS - modules u Modules u VOMS represent atomic functionality acquisition modules: n Voms extract: extract VOMS info from proxy n Voms local group: from VOMS attributes assign GID n Voms pool group: from VOMS attributes assign GID from pool n Voms pool account: from VOMS attributes, DN and GIDs assign UID from pool u Standard acquisition modules: n Local account: from user DN assign local UID n pool account: from user DN assign UID from pool u Enforcement modules n POSIX enforcement: setreuid(), setregid() and setgroups() in gatekeeper process n LDAP enforcement: update distributed user database u In n progress Get AFS/Krb 5 token based on user DN (gssklog) NIKHEF Grid meeting – LCAS and LCMAPS – n° 14
LCMAPS - modules u Modules u VOMS represent atomic functionality acquisition modules: n Voms extract: extract VOMS info from proxy n Voms local group: from VOMS attributes assign GID n Voms pool group: from VOMS attributes assign GID from pool n Voms pool account: from VOMS attributes, DN and GIDs assign UID from pool u Standard acquisition modules: n Local account: from user DN assign local UID n pool account: from user DN assign UID from pool u Enforcement modules n POSIX enforcement: setreuid(), setregid() and setgroups() in gatekeeper process n LDAP enforcement: update distributed user database u In n progress Get AFS/Krb 5 token based on user DN (gssklog) NIKHEF Grid meeting – LCAS and LCMAPS – n° 14
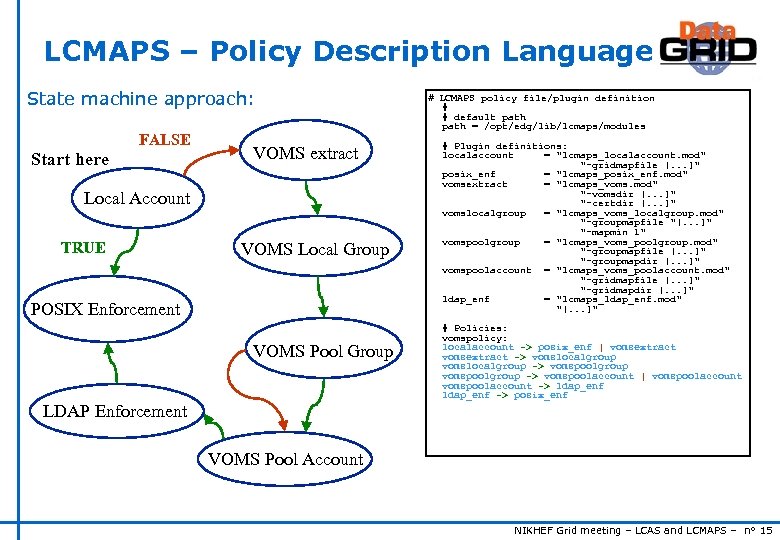 LCMAPS – Policy Description Language State machine approach: FALSE Start here VOMS extract Local Account TRUE VOMS Local Group POSIX Enforcement VOMS Pool Group LDAP Enforcement # LCMAPS policy file/plugin definition # # default path = /opt/edg/lib/lcmaps/modules # Plugin definitions: localaccount = "lcmaps_localaccount. mod" "-gridmapfile [. . . ]" posix_enf = "lcmaps_posix_enf. mod" vomsextract = "lcmaps_voms. mod" "-vomsdir [. . . ]" "-certdir [. . . ]" vomslocalgroup = "lcmaps_voms_localgroup. mod" "-groupmapfile "[. . . ]" "-mapmin 1" vomspoolgroup = "lcmaps_voms_poolgroup. mod" "-groupmapfile [. . . ]" "-groupmapdir [. . . ]" vomspoolaccount = "lcmaps_voms_poolaccount. mod" "-gridmapfile [. . . ]" "-gridmapdir [. . . ]" ldap_enf = "lcmaps_ldap_enf. mod" "[. . . ]" # Policies: vomspolicy: localaccount -> posix_enf | vomsextract -> vomslocalgroup -> vomspoolgroup -> vomspoolaccount | vomspoolaccount -> ldap_enf -> posix_enf VOMS Pool Account NIKHEF Grid meeting – LCAS and LCMAPS – n° 15
LCMAPS – Policy Description Language State machine approach: FALSE Start here VOMS extract Local Account TRUE VOMS Local Group POSIX Enforcement VOMS Pool Group LDAP Enforcement # LCMAPS policy file/plugin definition # # default path = /opt/edg/lib/lcmaps/modules # Plugin definitions: localaccount = "lcmaps_localaccount. mod" "-gridmapfile [. . . ]" posix_enf = "lcmaps_posix_enf. mod" vomsextract = "lcmaps_voms. mod" "-vomsdir [. . . ]" "-certdir [. . . ]" vomslocalgroup = "lcmaps_voms_localgroup. mod" "-groupmapfile "[. . . ]" "-mapmin 1" vomspoolgroup = "lcmaps_voms_poolgroup. mod" "-groupmapfile [. . . ]" "-groupmapdir [. . . ]" vomspoolaccount = "lcmaps_voms_poolaccount. mod" "-gridmapfile [. . . ]" "-gridmapdir [. . . ]" ldap_enf = "lcmaps_ldap_enf. mod" "[. . . ]" # Policies: vomspolicy: localaccount -> posix_enf | vomsextract -> vomslocalgroup -> vomspoolgroup -> vomspoolaccount | vomspoolaccount -> ldap_enf -> posix_enf VOMS Pool Account NIKHEF Grid meeting – LCAS and LCMAPS – n° 15
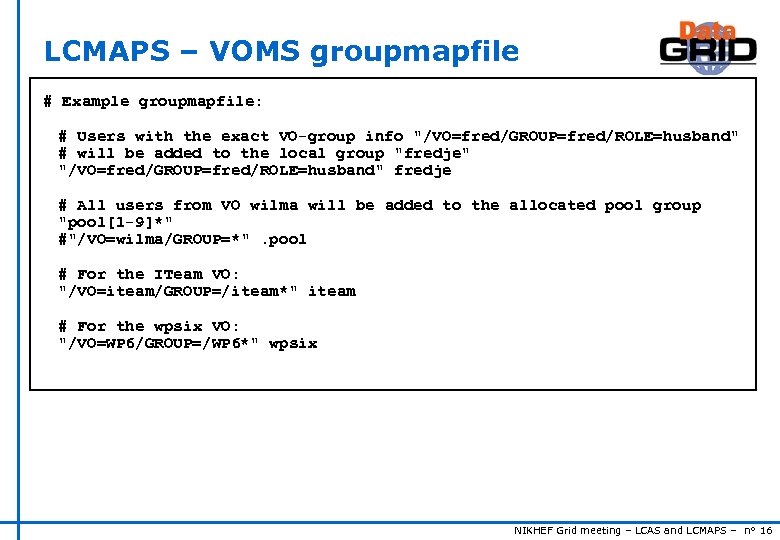 LCMAPS – VOMS groupmapfile # Example groupmapfile: # Users with the exact VO-group info "/VO=fred/GROUP=fred/ROLE=husband" # will be added to the local group "fredje" "/VO=fred/GROUP=fred/ROLE=husband" fredje # All users from VO wilma will be added to the allocated pool group "pool[1 -9]*" #"/VO=wilma/GROUP=*". pool # For the ITeam VO: "/VO=iteam/GROUP=/iteam*" iteam # For the wpsix VO: "/VO=WP 6/GROUP=/WP 6*" wpsix NIKHEF Grid meeting – LCAS and LCMAPS – n° 16
LCMAPS – VOMS groupmapfile # Example groupmapfile: # Users with the exact VO-group info "/VO=fred/GROUP=fred/ROLE=husband" # will be added to the local group "fredje" "/VO=fred/GROUP=fred/ROLE=husband" fredje # All users from VO wilma will be added to the allocated pool group "pool[1 -9]*" #"/VO=wilma/GROUP=*". pool # For the ITeam VO: "/VO=iteam/GROUP=/iteam*" iteam # For the wpsix VO: "/VO=WP 6/GROUP=/WP 6*" wpsix NIKHEF Grid meeting – LCAS and LCMAPS – n° 16
 LCMAPS – LDAP and AFS u LDAP enforcement plug-in n Updates a central LDAP user directory n Secure (as opposed to NIS) n more flexible u AFS plug-in n Gives local AFS access n Uses gssklog to obtain AFS token n Requires gssklog daemon to run on the AFS server n Mapping DN to AFS user maintained in gssklog mapfile NIKHEF Grid meeting – LCAS and LCMAPS – n° 17
LCMAPS – LDAP and AFS u LDAP enforcement plug-in n Updates a central LDAP user directory n Secure (as opposed to NIS) n more flexible u AFS plug-in n Gives local AFS access n Uses gssklog to obtain AFS token n Requires gssklog daemon to run on the AFS server n Mapping DN to AFS user maintained in gssklog mapfile NIKHEF Grid meeting – LCAS and LCMAPS – n° 17
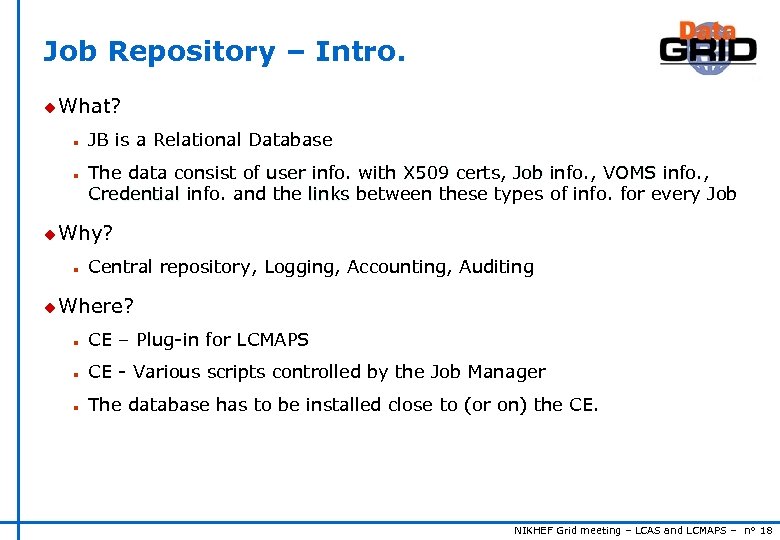 Job Repository – Intro. u What? n n JB is a Relational Database The data consist of user info. with X 509 certs, Job info. , VOMS info. , Credential info. and the links between these types of info. for every Job u Why? n Central repository, Logging, Accounting, Auditing u Where? n CE – Plug-in for LCMAPS n CE - Various scripts controlled by the Job Manager n The database has to be installed close to (or on) the CE. NIKHEF Grid meeting – LCAS and LCMAPS – n° 18
Job Repository – Intro. u What? n n JB is a Relational Database The data consist of user info. with X 509 certs, Job info. , VOMS info. , Credential info. and the links between these types of info. for every Job u Why? n Central repository, Logging, Accounting, Auditing u Where? n CE – Plug-in for LCMAPS n CE - Various scripts controlled by the Job Manager n The database has to be installed close to (or on) the CE. NIKHEF Grid meeting – LCAS and LCMAPS – n° 18
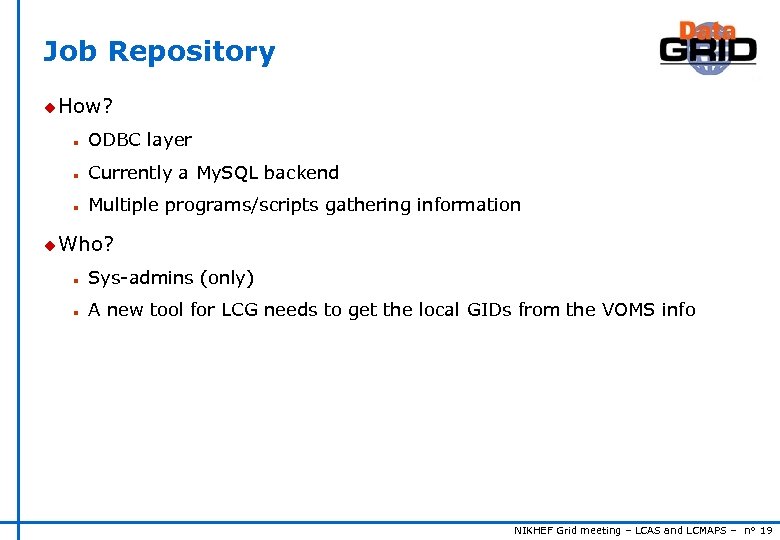 Job Repository u How? n ODBC layer n Currently a My. SQL backend n Multiple programs/scripts gathering information u Who? n Sys-admins (only) n A new tool for LCG needs to get the local GIDs from the VOMS info NIKHEF Grid meeting – LCAS and LCMAPS – n° 19
Job Repository u How? n ODBC layer n Currently a My. SQL backend n Multiple programs/scripts gathering information u Who? n Sys-admins (only) n A new tool for LCG needs to get the local GIDs from the VOMS info NIKHEF Grid meeting – LCAS and LCMAPS – n° 19
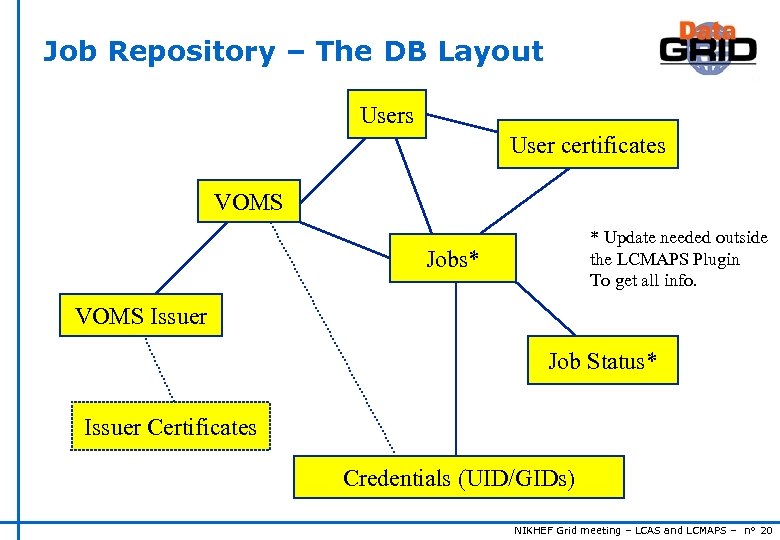 Job Repository – The DB Layout Users User certificates VOMS * Update needed outside the LCMAPS Plugin To get all info. Jobs* VOMS Issuer Job Status* Issuer Certificates Credentials (UID/GIDs) NIKHEF Grid meeting – LCAS and LCMAPS – n° 20
Job Repository – The DB Layout Users User certificates VOMS * Update needed outside the LCMAPS Plugin To get all info. Jobs* VOMS Issuer Job Status* Issuer Certificates Credentials (UID/GIDs) NIKHEF Grid meeting – LCAS and LCMAPS – n° 20
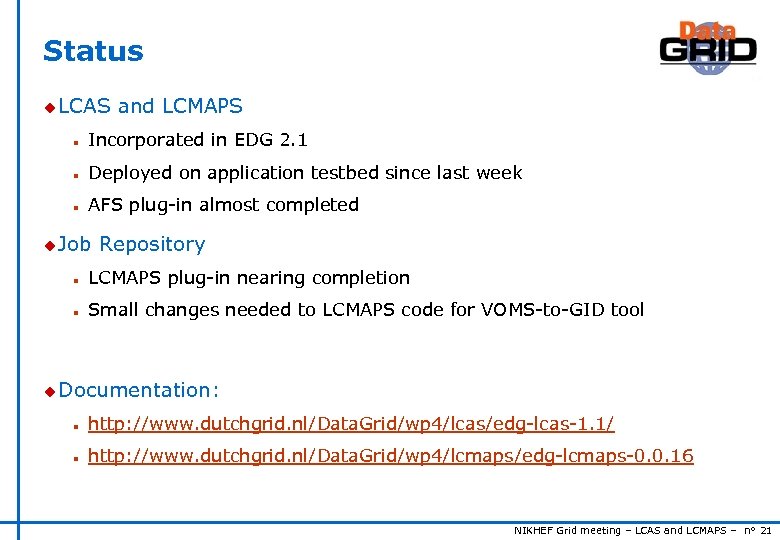 Status u LCAS and LCMAPS n Incorporated in EDG 2. 1 n Deployed on application testbed since last week n AFS plug-in almost completed u Job Repository n LCMAPS plug-in nearing completion n Small changes needed to LCMAPS code for VOMS-to-GID tool u Documentation: n http: //www. dutchgrid. nl/Data. Grid/wp 4/lcas/edg-lcas-1. 1/ n http: //www. dutchgrid. nl/Data. Grid/wp 4/lcmaps/edg-lcmaps-0. 0. 16 NIKHEF Grid meeting – LCAS and LCMAPS – n° 21
Status u LCAS and LCMAPS n Incorporated in EDG 2. 1 n Deployed on application testbed since last week n AFS plug-in almost completed u Job Repository n LCMAPS plug-in nearing completion n Small changes needed to LCMAPS code for VOMS-to-GID tool u Documentation: n http: //www. dutchgrid. nl/Data. Grid/wp 4/lcas/edg-lcas-1. 1/ n http: //www. dutchgrid. nl/Data. Grid/wp 4/lcmaps/edg-lcmaps-0. 0. 16 NIKHEF Grid meeting – LCAS and LCMAPS – n° 21
 Future developments u LCAS, LCMAPS (and the Job. Rep? ) will be part of EGEE u grid. FTP will be patched to use LCAS and LCMAPS u LCAS will evolve into an authorization service and take on the use of XACML to express VO access control u DAGGR u LCAS (? ): Authorization Decision Service and LCMAPS will also interface to the Auth. Z call-outs in GT 3 NIKHEF Grid meeting – LCAS and LCMAPS – n° 22
Future developments u LCAS, LCMAPS (and the Job. Rep? ) will be part of EGEE u grid. FTP will be patched to use LCAS and LCMAPS u LCAS will evolve into an authorization service and take on the use of XACML to express VO access control u DAGGR u LCAS (? ): Authorization Decision Service and LCMAPS will also interface to the Auth. Z call-outs in GT 3 NIKHEF Grid meeting – LCAS and LCMAPS – n° 22


