144f567d6808a4371eb745ab2798c992.ppt
- Количество слайдов: 45
KULIAH II THREAT AND ATTACK (1) Imam Bukhari, S. Kom KOM 15008 Keamanan Jaringan 2012/2013
Overview • • Threat Vulnerability Attack Fase-fase serangan terhadap keamanan Phase 1: Reconaissance Phase 2: Scanning Phase 3: Gaining Access Using Application & OS Attack
Threat 1) • Threat (ancaman) dalam keamanan jaringan adalah semua hal yang dapat mengganggu operasi, fungsi, confidentiality, integrity, availability dari jaringan atau sistem. • Terdapat ancaman alamiah seperti banjir, gempa dan gunung meletus. • Terdapat ancaman sebagai akibat dari kecelakaan dan kebodohan salah satu pihak yang terkait dengan sistem. • Terdapat ancaman akibat pihak lain diluar sistem yang berniat jahat terhadap sistem. • Setiap ancaman dapat berbahaya terhadap sistem. 1) John E. Canavan, Fundamentals of Network Security, Artech House
Threat
Threat • Dalam kuliah ini kita fokus kepada ancaman akibat kecerobohan orang dalam, dan ancaman yang berasal dari pihak luar yang bermaksud jahat. • Tidak banyak yang dapat dilakukan untuk mencegah ancaman akibat bencana alam. Upaya yang dapat dilakukan antara lain, menyediakan backup data dan server di tempat lain. Banyak berdo’a mungkin solusi terbaik. : D
Vulnerability • Vulnerabilities adalah kelemahan dalam desain, konfigurasi, implementasi atau manajemen jaringan atau sistem yang membuat sistem rentan terhadap ancaman. Setiap sistem dan jaringan pasti memiliki kelemahan. 1) 1) John E. Canavan, Fundamentals of Network Security, Artech House
Attack • Serangan (Attack) adalah upaya untuk mengeksploitasi kelemahan sistem. Mengakibatkan gangguan yang berkaitan dengan Confidentiality, Integrity dan Availability. • Serangan terhadap confidentiality misalnya upaya untuk mengetahui data rahasia seseorang dengan menyadap (sniffing) percakapan pada jaringan. • Serangan terhadap Integrity misalnya upaya untuk memalsukan pesan dari atasan ke bawahan. • Serangan terhadap Availability misalnya upaya untuk membuat sistem mati. 1) John E. Canavan, Fundamentals of Network Security, Artech House
Attack • Dua tipe serangan, Aktif dan Pasif. • Serangan Aktif merupakan serangan yang menyebabkan akibat aktif dan memiliki efek yang terlihat nyata. Contoh: membuat sistem mati (down) • Serangan Pasif merupakan serangan yang diam-diam, tidak terdapat aktivitas atau akibat yang kasat mata. Contoh serangan pasif adalah penyadapan (sniffing). • Serangan Pasif lebih sulit untuk dideteksi. • Serangan Aktif lebih mudah dideteksi. Tetapi saat terdeteksi biasanya akibatnya sudah fatal. 1) John E. Canavan, Fundamentals of Network Security, Artech House
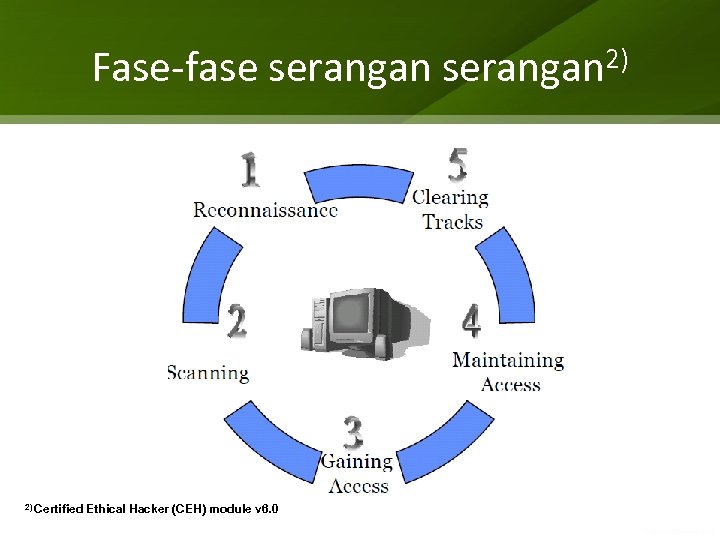
Fase-fase serangan 2) 2) Certified Ethical Hacker (CEH) module v 6. 0
1. Reconnaissance • Finding as much information about the target as possible before launching the first attack packet • Reconnaissance techniques – – 3) Ed Low tech methods General web searches Whois databases DNS Skoudis, Counter Hack Reloaded, Prentice Hall
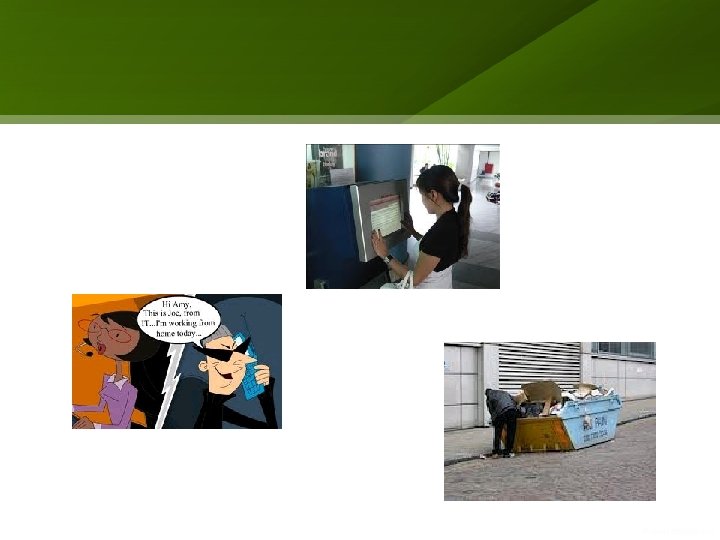
Low-Technology Reconnaissance • Social Engineering • Physical Break-In • Dumpster Diving 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Reconnaissance via Searching the Web • Searching an organization’s own web site • Using search engines • Listen in at the virtual watering hole: USENET 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Searching an Organization’s Own Web Site • • • 3) Ed Employees’ contact information and phone numbers Clues about the corporate culture and language Business partners Recent mergers and acquisitions Server and application platforms in use Skoudis, Counter Hack Reloaded, Prentice Hall
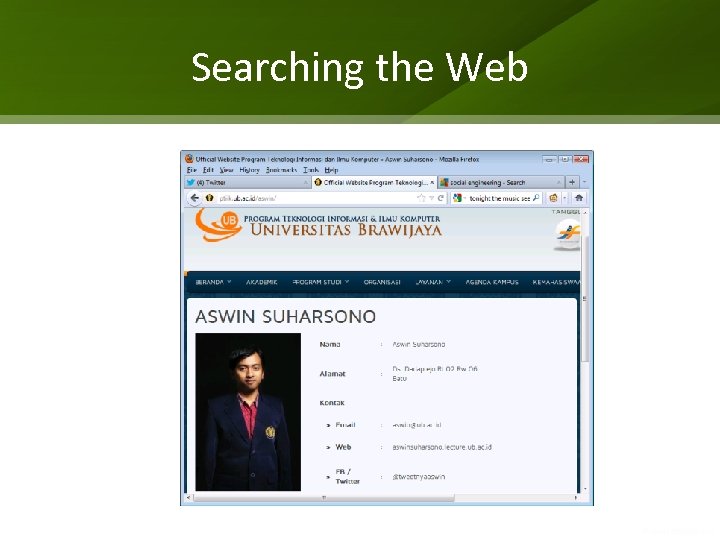
Searching the Web
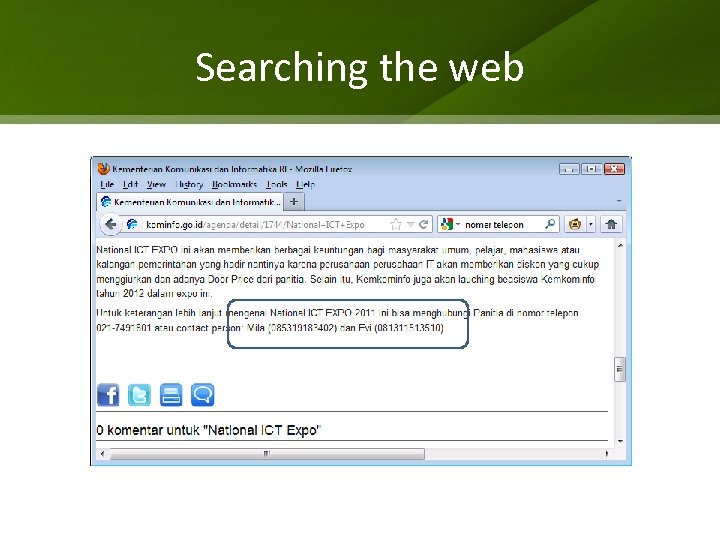
Searching the web
Searching the web
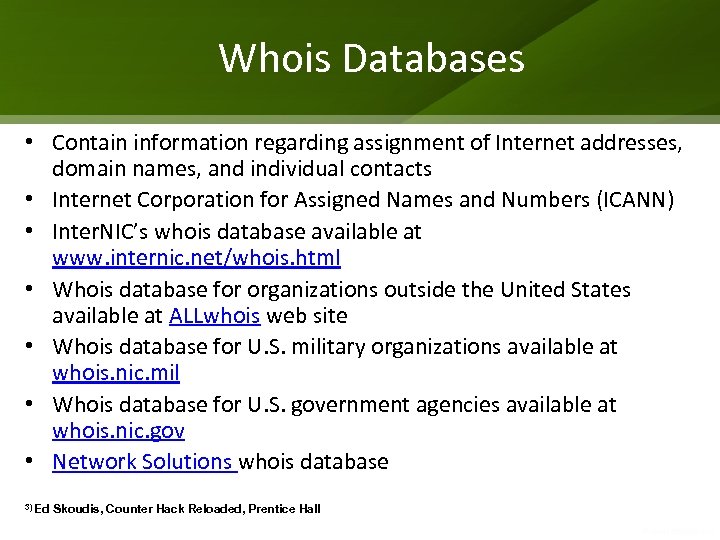
Whois Databases • Contain information regarding assignment of Internet addresses, domain names, and individual contacts • Internet Corporation for Assigned Names and Numbers (ICANN) • Inter. NIC’s whois database available at www. internic. net/whois. html • Whois database for organizations outside the United States available at ALLwhois web site • Whois database for U. S. military organizations available at whois. nic. mil • Whois database for U. S. government agencies available at whois. nic. gov • Network Solutions whois database 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
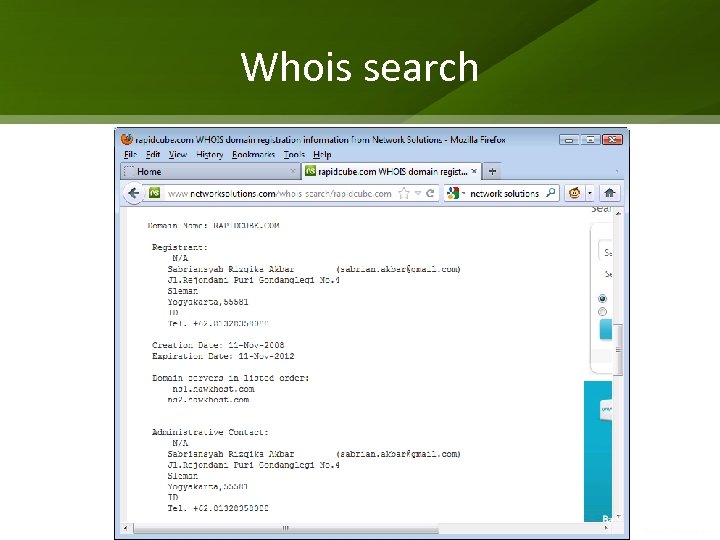
Whois search
2. Scanning After the reconnaissance phase, the attacker is armed with some vital information about the target infrastructure: a handful of telephone numbers, domain names, IP addresses, and technical contact information—a very good starting point. Most attackers then use this knowledge to scan target systems looking for openings. This scanning phase is akin to a burglar turning doorknobs and trying to open windows to find a way into a victim's house. 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
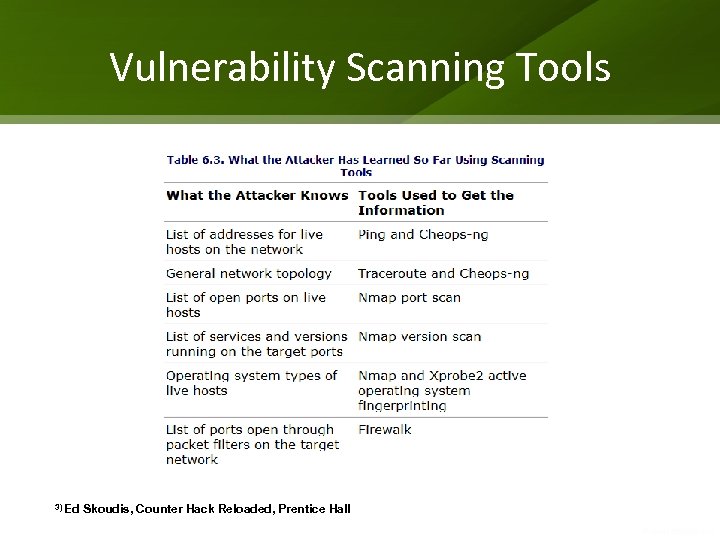
Vulnerability Scanning Tools 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Network Mapping • Finding live hosts – ICMP pings – TCP/UDP packets 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Traceroute • Traceroute utility on most Unix platforms sends out UDP packets with incremental TTL values to trigger ICMP Time Exceeded messages • Tracert utility on Microsoft platform sends out ICMP packets with incremental TTL values to trigger ICMP Time Exceeded replies 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
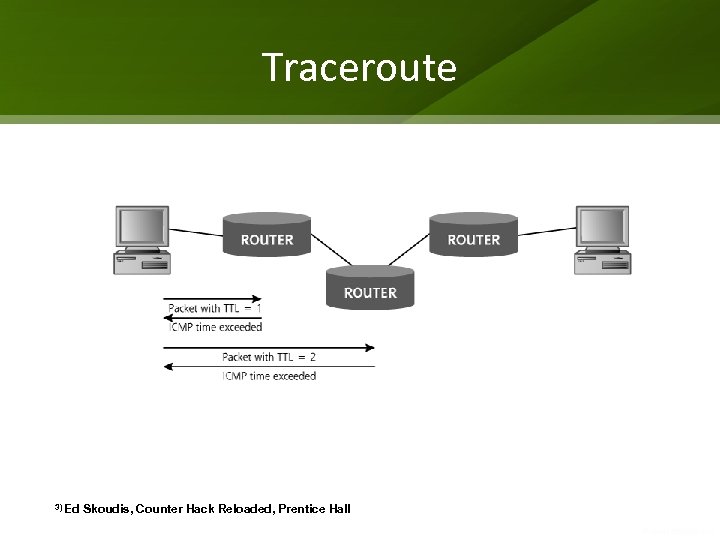
Traceroute 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
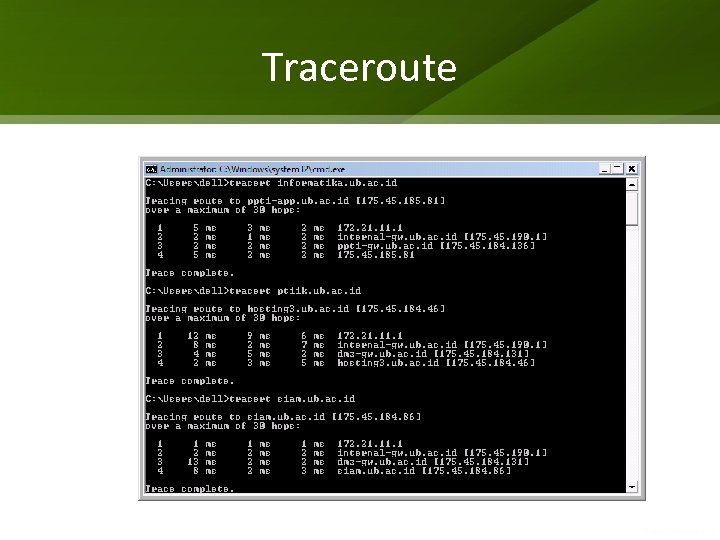
Traceroute
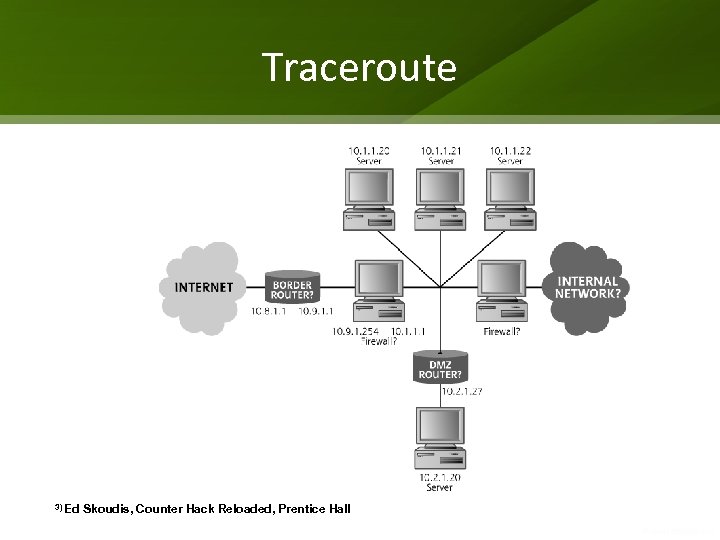
Traceroute 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Cheops A nifty network mapper tool Available at http: //www. marko. net/cheops Runs on Linux Generates network topology by using ping sweeps and traceroute • Supports remote operating system identification using TCP Stack Fingerprinting • •
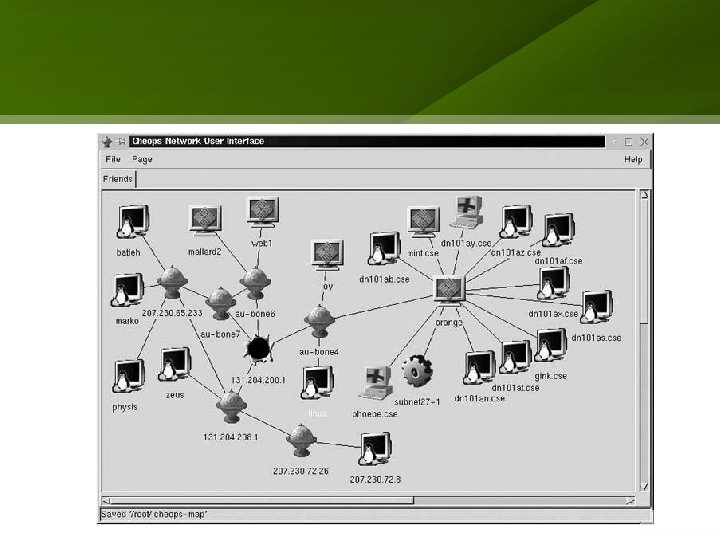
Figure 6. 5 The Cheops display
Defenses against Network Mapping • Block incoming ICMP messages at Internet gateway to make ping ineffective • Filter ICMP Time Exceeded messages leaving your network to make traceroute ineffective 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Port Scanning • Used to find open ports • Free port scanning tools – Nmap available at www. insecure. org/Nmap – Strobe at http: //packetstorm. securify. com/UNIX/scanners – Ultrascan for NT available at http: //packetstorm. securify. com/Unix/scanners 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Nmap • Full-featured port scanning tool • Unix version available at http: //www. insecure. org/Nmap • Windows NT version available at http: //www. eeye. com/html/Databases/Software/Nmapnt. ht ml 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
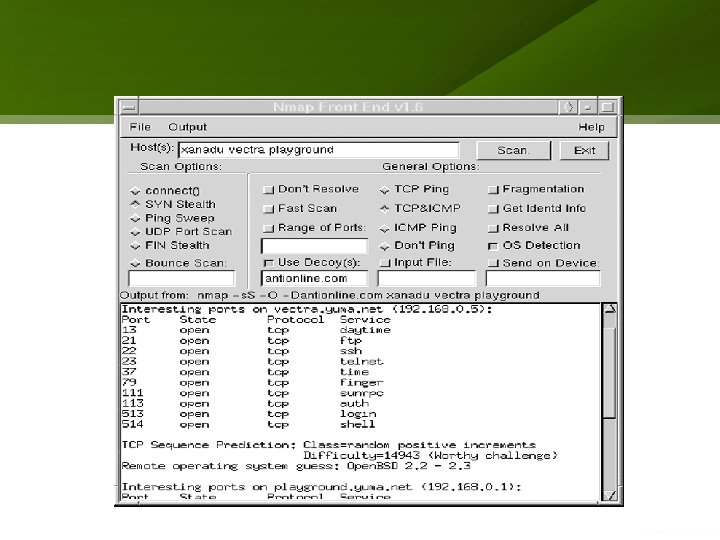
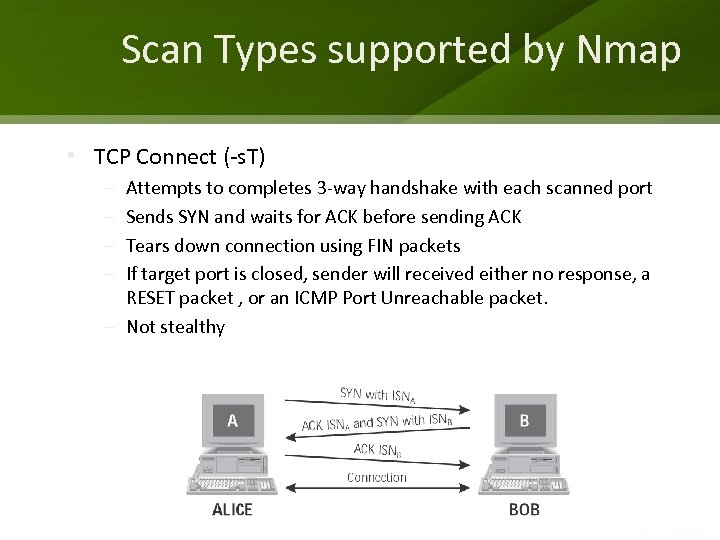
Scan Types supported by Nmap • TCP Connect (-s. T) Attempts to completes 3 -way handshake with each scanned port Sends SYN and waits for ACK before sending ACK Tears down connection using FIN packets If target port is closed, sender will received either no response, a RESET packet , or an ICMP Port Unreachable packet. – Not stealthy – –
Defenses against Port Scanning • Unix systems – remove all unneeded services in /etc/inetd. conf – Remove unneeded services in /etc/rc*. d • Windows systems – uninstall unneeded services or shut them off in the services control panel • Scan your own systems before the attackers do • Use stateful packet filter or proxy-based firewall – blocks ACK scans – Blocks FTP data source port scans 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
3. Gaining Access 3. 1 Gaining Access using OS and Application Attacks At this stage of the siege, the attacker has finished scanning the target network, developing an inventory of target systems and potential vulnerabilities on those machines. Next, the attacker wants to gain access on the target systems. The particular approach to gaining access depends heavily on the skill level of the attacker, with simple script kiddies trolling for exploits and more sophisticated attackers using highly pragmatic approaches. 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
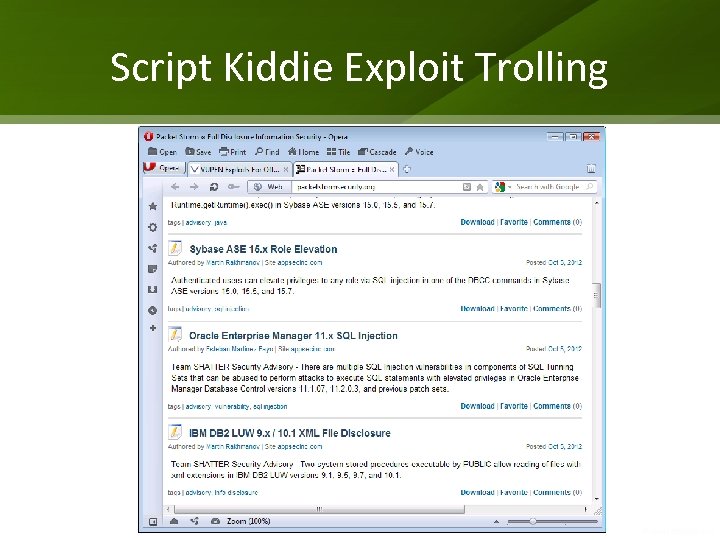
Script Kiddie Exploit Trolling
Password Guessing Attacks • Users often choose passwords that are easy to remember, but are also easily guessed • default passwords used by vendors left unchanged • Database of vendor default passwords http: //security. nerdnet. com 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
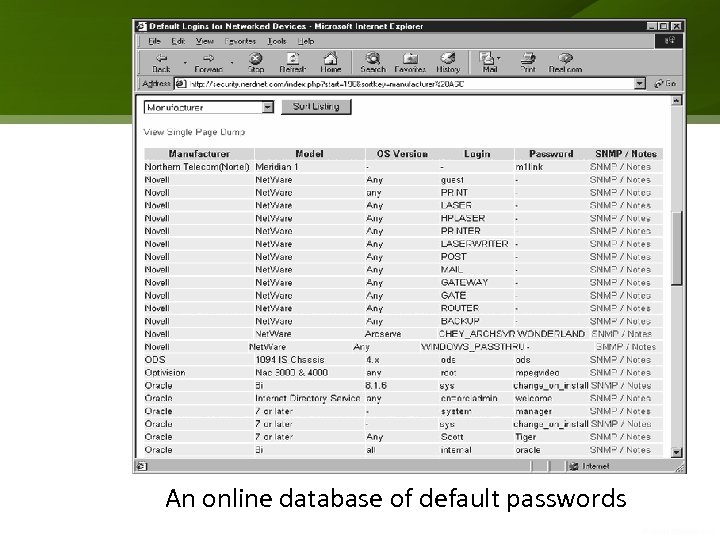
An online database of default passwords
Password Guessing through Login Scripting • THC-Login Hacker tool http: //thc. inferno. tusculum. edu • Authforce http: //kapheine. hypa. net/authforce/index. php • brute_ssl and brute_web http: //packetstrom. security. com/Exploit_Code_archive/brute_ssl. c http: //packetstrom. security. com/Exploit_Code_archive/brute_web. c • Windows NT password guessing http: //packetstorm. securify. com/NT/audit/nt. remotely. crack. nt. pass words. zip • Xavier http: //www. btinernet. com/~lithiumsoft/ • Guessing email passwords using POP 3 protocol: Hypnopaedia http: //packetstorm. securify. com/Crackers/hypno. zip • Other password guessing tools http: //packetstorm. securify. com/Crackers
Password Cracking • More sophisticated and faster than password guessing through login script • Requires access to a file containing user names and encrypted passwords • Dictionary attacks • Brute force attacks • Hybrid dictionary and brute force attacks 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Password Cracking Tools • L 0 pht. Crack, a Windows NT/2000 password cracker http: //www. l 0 pht. com/l 0 phtcrack • John the Ripper, a Unix password cracker http: //www. openwall. com/john • Crack, a Unix password cracker http: //www. users. diron. co. uk/~crypto/ • Pandora, a password cracker for Novell http: //www. nmrc. org/pandora • Palm. Crack, a Windows NT and Unix password cracker that runs on the Palm OS PDA platform http: //www. noncon. org/noncon/download. html
Web Application Attacks • Can be conducted even if the Web server uses Secure Sockets Layer (SSL) – SSL used to authenticate the Web server to the browser – SSL used to prevent an attacker from intercepting traffic – SSL can be used to authenticate the client with client-side certificates • Web attacks can occur over SSL-encrypted connection – Account harvesting – Undermining session tracking – SQL Piggybacking 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Account Harvesting • Technique used to determine legitimate user. IDs and even passwords of a vulnerable application • Targets the authentication process when application requests a user. ID and password • Works against applications that have a different error message for users who type in an incorrect user. ID 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
Account Harvesting Defenses • Make sure that error message is the same when a user types in an incorrect user. ID or password 3) Ed Skoudis, Counter Hack Reloaded, Prentice Hall
To Be Continued. .
144f567d6808a4371eb745ab2798c992.ppt