e6678bab86ef7f37337bb44f8741e287.ppt
- Количество слайдов: 19
 Kommunikatsiooniteenuste arendus IRT 0080 Loeng 5 Avo Ots telekommunikatsiooni õppetool, TTÜ raadio- ja sidetehnika inst. avo. ots@ttu. ee 1
Kommunikatsiooniteenuste arendus IRT 0080 Loeng 5 Avo Ots telekommunikatsiooni õppetool, TTÜ raadio- ja sidetehnika inst. avo. ots@ttu. ee 1
 Lingid http: //www. cs. columbia. edu/sip/ What_is_SIP. ppt http: //www. ietf. org/rfc 3261. txt? number=3261 http: //www. ietf. org/rfc 2633. txt? number=2633 2
Lingid http: //www. cs. columbia. edu/sip/ What_is_SIP. ppt http: //www. ietf. org/rfc 3261. txt? number=3261 http: //www. ietf. org/rfc 2633. txt? number=2633 2
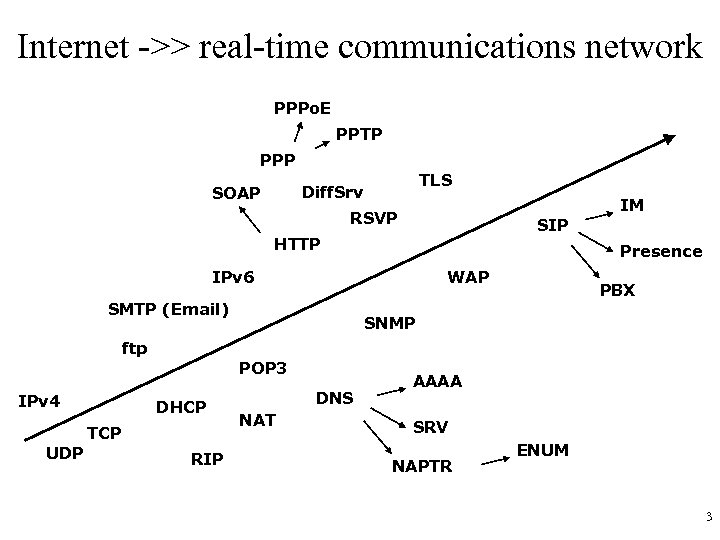 Internet ->> real-time communications network PPPo. E PPTP PPP TLS Diff. Srv SOAP IM RSVP SIP HTTP Presence IPv 6 WAP SMTP (Email) PBX SNMP ftp POP 3 IPv 4 DHCP TCP UDP RIP DNS NAT AAAA SRV NAPTR ENUM 3
Internet ->> real-time communications network PPPo. E PPTP PPP TLS Diff. Srv SOAP IM RSVP SIP HTTP Presence IPv 6 WAP SMTP (Email) PBX SNMP ftp POP 3 IPv 4 DHCP TCP UDP RIP DNS NAT AAAA SRV NAPTR ENUM 3
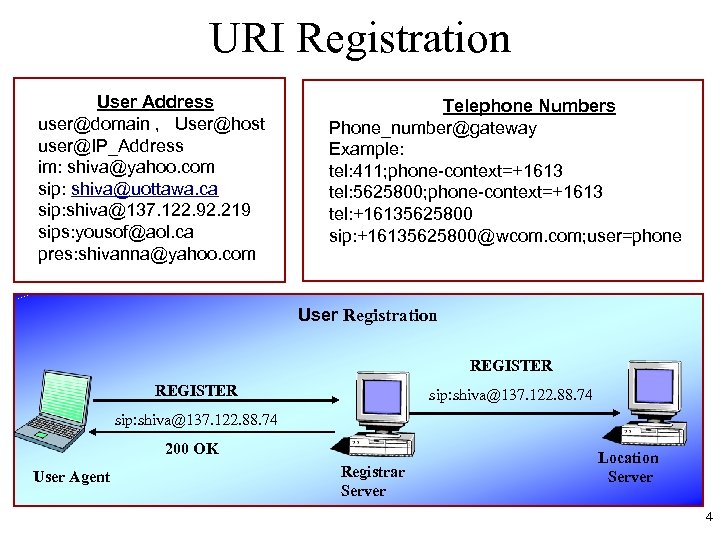 URI Registration User Address user@domain , User@host user@IP_Address im: shiva@yahoo. com sip: shiva@uottawa. ca sip: shiva@137. 122. 92. 219 sips: yousof@aol. ca pres: shivanna@yahoo. com Telephone Numbers Phone_number@gateway Example: tel: 411; phone-context=+1613 tel: 5625800; phone-context=+1613 tel: +16135625800 sip: +16135625800@wcom. com; user=phone User Registration REGISTER sip: shiva@137. 122. 88. 74 200 OK User Agent Registrar Server Location server Server 4
URI Registration User Address user@domain , User@host user@IP_Address im: shiva@yahoo. com sip: shiva@uottawa. ca sip: shiva@137. 122. 92. 219 sips: yousof@aol. ca pres: shivanna@yahoo. com Telephone Numbers Phone_number@gateway Example: tel: 411; phone-context=+1613 tel: 5625800; phone-context=+1613 tel: +16135625800 sip: +16135625800@wcom. com; user=phone User Registration REGISTER sip: shiva@137. 122. 88. 74 200 OK User Agent Registrar Server Location server Server 4
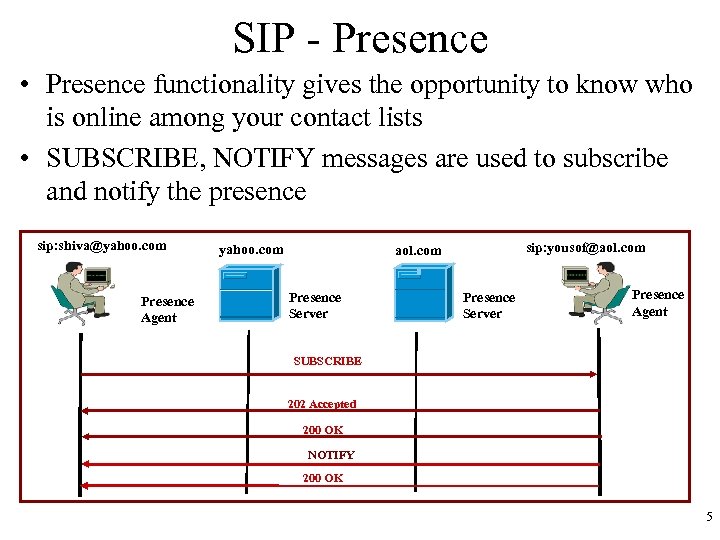 SIP - Presence • Presence functionality gives the opportunity to know who is online among your contact lists • SUBSCRIBE, NOTIFY messages are used to subscribe and notify the presence sip: shiva@yahoo. com Presence Agent yahoo. com sip: yousof@aol. com Presence Server Presence Agent SUBSCRIBE 202 Accepted 200 OK NOTIFY 200 OK 5
SIP - Presence • Presence functionality gives the opportunity to know who is online among your contact lists • SUBSCRIBE, NOTIFY messages are used to subscribe and notify the presence sip: shiva@yahoo. com Presence Agent yahoo. com sip: yousof@aol. com Presence Server Presence Agent SUBSCRIBE 202 Accepted 200 OK NOTIFY 200 OK 5
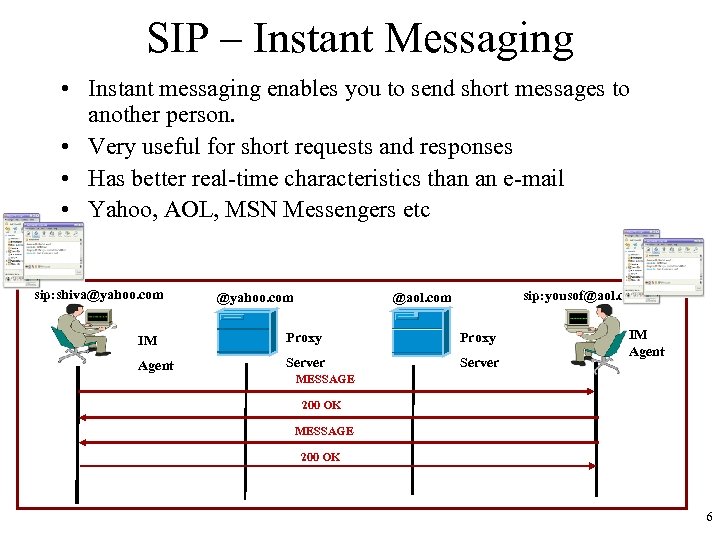 SIP – Instant Messaging • Instant messaging enables you to send short messages to another person. • Very useful for short requests and responses • Has better real-time characteristics than an e-mail • Yahoo, AOL, MSN Messengers etc sip: shiva@yahoo. com sip: yousof@aol. com IM Proxy Agent Server IM Agent MESSAGE 200 OK 6
SIP – Instant Messaging • Instant messaging enables you to send short messages to another person. • Very useful for short requests and responses • Has better real-time characteristics than an e-mail • Yahoo, AOL, MSN Messengers etc sip: shiva@yahoo. com sip: yousof@aol. com IM Proxy Agent Server IM Agent MESSAGE 200 OK 6
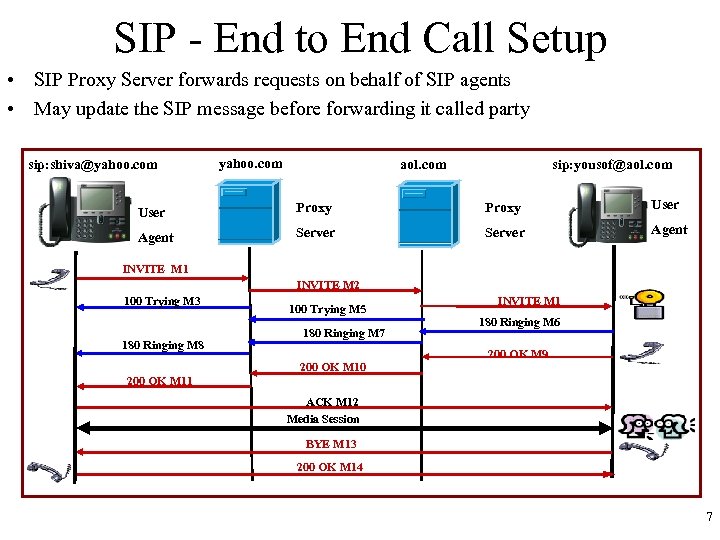 SIP - End to End Call Setup • SIP Proxy Server forwards requests on behalf of SIP agents • May update the SIP message before forwarding it called party sip: shiva@yahoo. com aol. com sip: yousof@aol. com User Proxy User Agent Server Agent INVITE M 1 INVITE M 2 100 Trying M 3 180 Ringing M 8 200 OK M 11 100 Trying M 5 180 Ringing M 7 200 OK M 10 INVITE M 1 180 Ringing M 6 200 OK M 9 ACK M 12 Media Session BYE M 13 200 OK M 14 7
SIP - End to End Call Setup • SIP Proxy Server forwards requests on behalf of SIP agents • May update the SIP message before forwarding it called party sip: shiva@yahoo. com aol. com sip: yousof@aol. com User Proxy User Agent Server Agent INVITE M 1 INVITE M 2 100 Trying M 3 180 Ringing M 8 200 OK M 11 100 Trying M 5 180 Ringing M 7 200 OK M 10 INVITE M 1 180 Ringing M 6 200 OK M 9 ACK M 12 Media Session BYE M 13 200 OK M 14 7
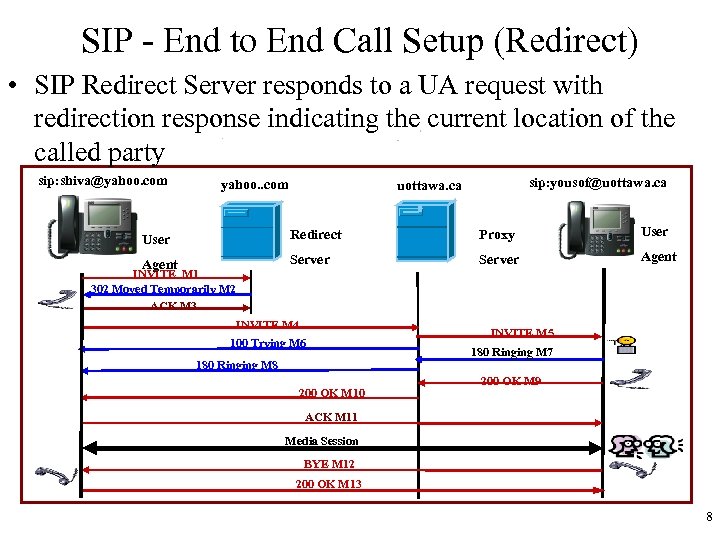 SIP - End to End Call Setup (Redirect) • SIP Redirect Server responds to a UA request with redirection response indicating the current location of the called party sip: shiva@yahoo. com yahoo. . com sip: yousof@uottawa. ca User Redirect Proxy User Agent Server Agent INVITE M 1 302 Moved Temporarily M 2 ACK M 3 INVITE M 4 100 Trying M 6 INVITE M 5 180 Ringing M 7 180 Ringing M 8 200 OK M 10 200 OK M 9 ACK M 11 Media Session BYE M 12 200 OK M 13 8
SIP - End to End Call Setup (Redirect) • SIP Redirect Server responds to a UA request with redirection response indicating the current location of the called party sip: shiva@yahoo. com yahoo. . com sip: yousof@uottawa. ca User Redirect Proxy User Agent Server Agent INVITE M 1 302 Moved Temporarily M 2 ACK M 3 INVITE M 4 100 Trying M 6 INVITE M 5 180 Ringing M 7 180 Ringing M 8 200 OK M 10 200 OK M 9 ACK M 11 Media Session BYE M 12 200 OK M 13 8
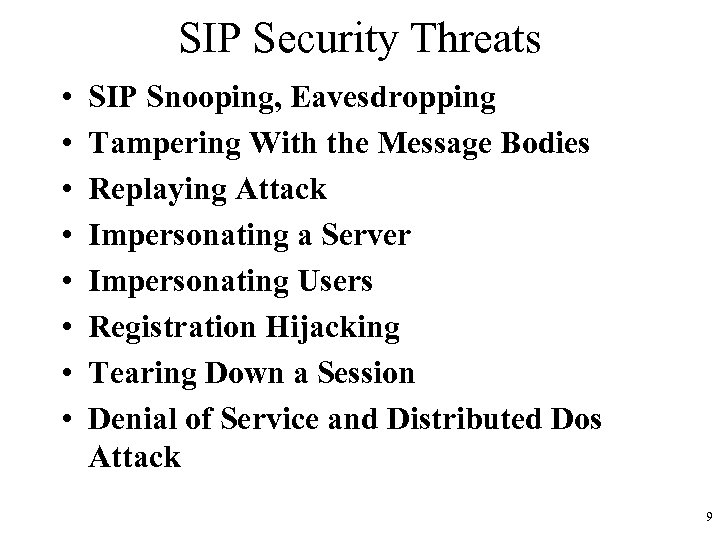 SIP Security Threats • • SIP Snooping, Eavesdropping Tampering With the Message Bodies Replaying Attack Impersonating a Server Impersonating Users Registration Hijacking Tearing Down a Session Denial of Service and Distributed Dos Attack 9
SIP Security Threats • • SIP Snooping, Eavesdropping Tampering With the Message Bodies Replaying Attack Impersonating a Server Impersonating Users Registration Hijacking Tearing Down a Session Denial of Service and Distributed Dos Attack 9
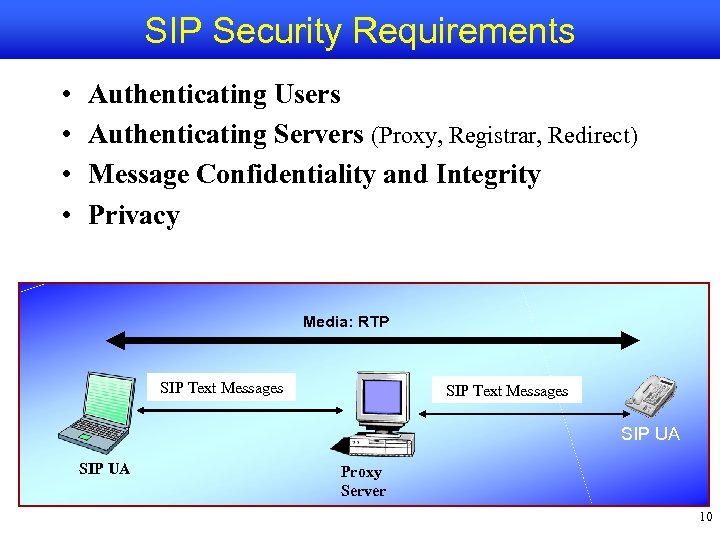 SIP Security Requirements • • Authenticating Users Authenticating Servers (Proxy, Registrar, Redirect) Message Confidentiality and Integrity Privacy Media: RTP SIP Text Messages SIP UA Proxy Server Location server 10
SIP Security Requirements • • Authenticating Users Authenticating Servers (Proxy, Registrar, Redirect) Message Confidentiality and Integrity Privacy Media: RTP SIP Text Messages SIP UA Proxy Server Location server 10
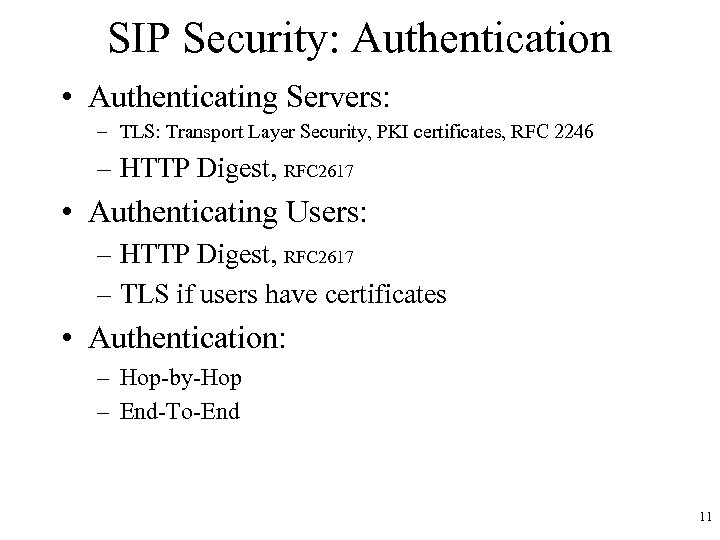 SIP Security: Authentication • Authenticating Servers: – TLS: Transport Layer Security, PKI certificates, RFC 2246 – HTTP Digest, RFC 2617 • Authenticating Users: – HTTP Digest, RFC 2617 – TLS if users have certificates • Authentication: – Hop-by-Hop – End-To-End 11
SIP Security: Authentication • Authenticating Servers: – TLS: Transport Layer Security, PKI certificates, RFC 2246 – HTTP Digest, RFC 2617 • Authenticating Users: – HTTP Digest, RFC 2617 – TLS if users have certificates • Authentication: – Hop-by-Hop – End-To-End 11
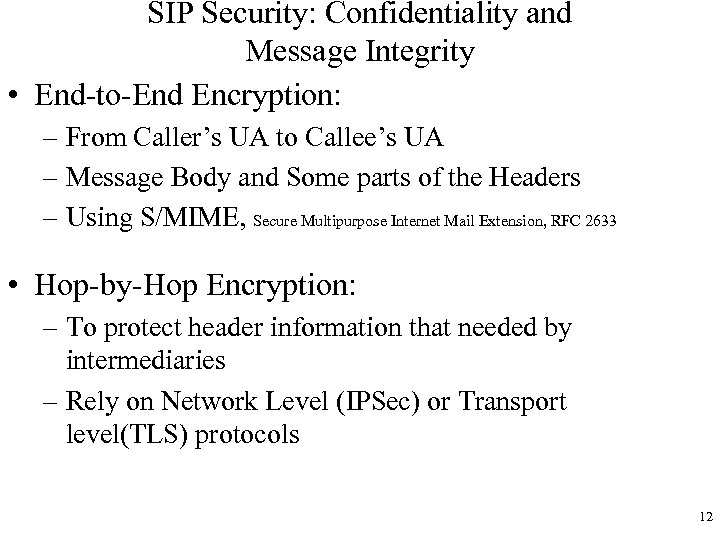 SIP Security: Confidentiality and Message Integrity • End-to-End Encryption: – From Caller’s UA to Callee’s UA – Message Body and Some parts of the Headers – Using S/MIME, Secure Multipurpose Internet Mail Extension, RFC 2633 • Hop-by-Hop Encryption: – To protect header information that needed by intermediaries – Rely on Network Level (IPSec) or Transport level(TLS) protocols 12
SIP Security: Confidentiality and Message Integrity • End-to-End Encryption: – From Caller’s UA to Callee’s UA – Message Body and Some parts of the Headers – Using S/MIME, Secure Multipurpose Internet Mail Extension, RFC 2633 • Hop-by-Hop Encryption: – To protect header information that needed by intermediaries – Rely on Network Level (IPSec) or Transport level(TLS) protocols 12
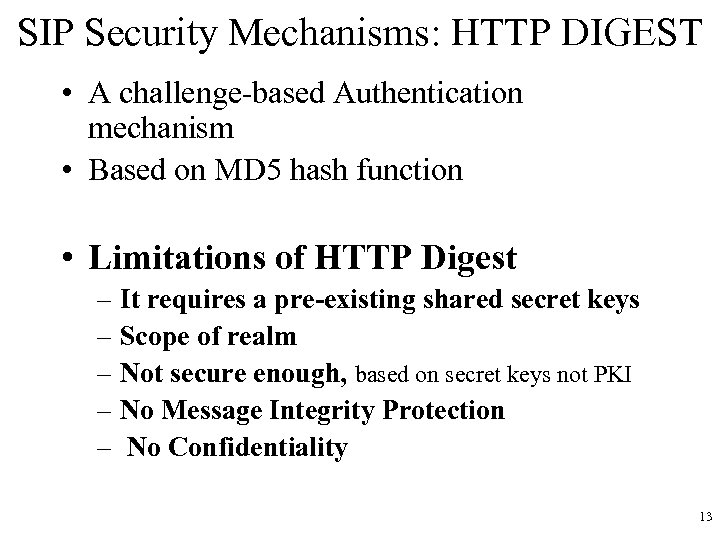 SIP Security Mechanisms: HTTP DIGEST • A challenge-based Authentication mechanism • Based on MD 5 hash function • Limitations of HTTP Digest – It requires a pre-existing shared secret keys – Scope of realm – Not secure enough, based on secret keys not PKI – No Message Integrity Protection – No Confidentiality 13
SIP Security Mechanisms: HTTP DIGEST • A challenge-based Authentication mechanism • Based on MD 5 hash function • Limitations of HTTP Digest – It requires a pre-existing shared secret keys – Scope of realm – Not secure enough, based on secret keys not PKI – No Message Integrity Protection – No Confidentiality 13
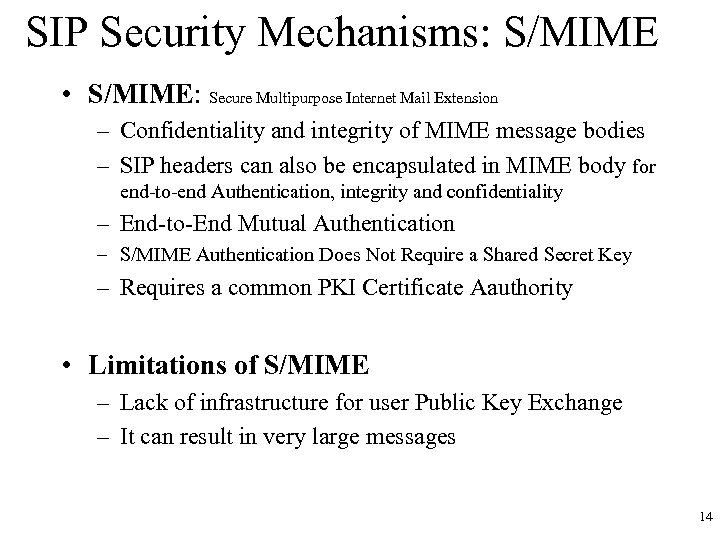 SIP Security Mechanisms: S/MIME • S/MIME: Secure Multipurpose Internet Mail Extension – Confidentiality and integrity of MIME message bodies – SIP headers can also be encapsulated in MIME body for end-to-end Authentication, integrity and confidentiality – End-to-End Mutual Authentication – S/MIME Authentication Does Not Require a Shared Secret Key – Requires a common PKI Certificate Aauthority • Limitations of S/MIME – Lack of infrastructure for user Public Key Exchange – It can result in very large messages 14
SIP Security Mechanisms: S/MIME • S/MIME: Secure Multipurpose Internet Mail Extension – Confidentiality and integrity of MIME message bodies – SIP headers can also be encapsulated in MIME body for end-to-end Authentication, integrity and confidentiality – End-to-End Mutual Authentication – S/MIME Authentication Does Not Require a Shared Secret Key – Requires a common PKI Certificate Aauthority • Limitations of S/MIME – Lack of infrastructure for user Public Key Exchange – It can result in very large messages 14
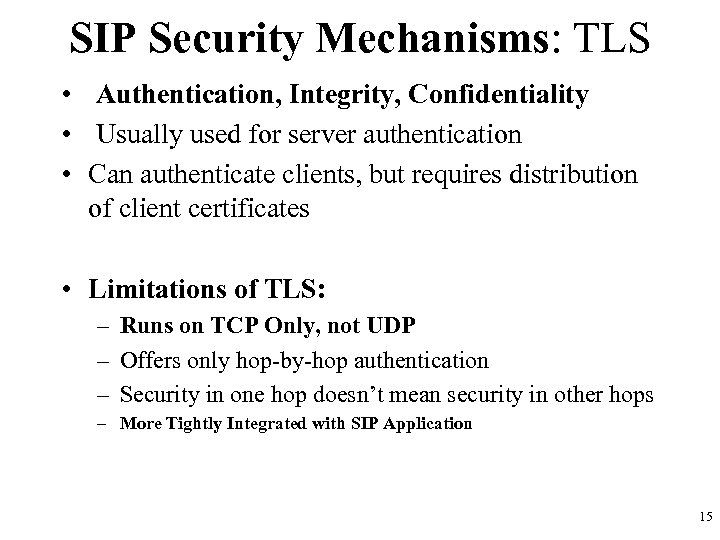 SIP Security Mechanisms: TLS • Authentication, Integrity, Confidentiality • Usually used for server authentication • Can authenticate clients, but requires distribution of client certificates • Limitations of TLS: – Runs on TCP Only, not UDP – Offers only hop-by-hop authentication – Security in one hop doesn’t mean security in other hops – More Tightly Integrated with SIP Application 15
SIP Security Mechanisms: TLS • Authentication, Integrity, Confidentiality • Usually used for server authentication • Can authenticate clients, but requires distribution of client certificates • Limitations of TLS: – Runs on TCP Only, not UDP – Offers only hop-by-hop authentication – Security in one hop doesn’t mean security in other hops – More Tightly Integrated with SIP Application 15
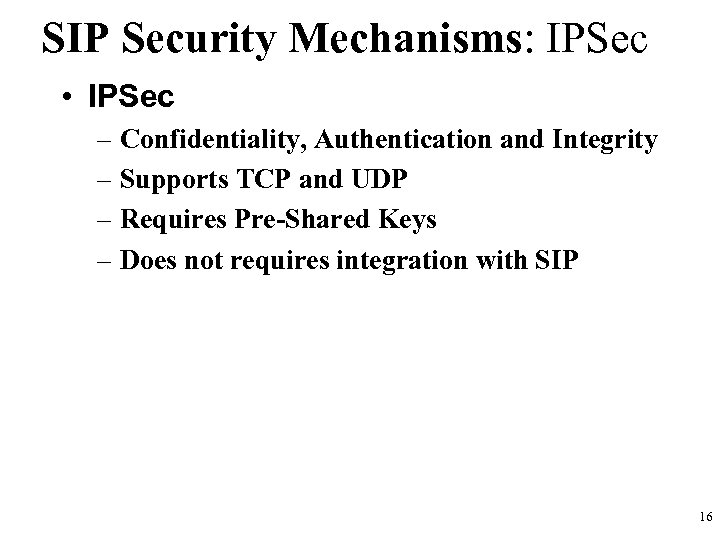 SIP Security Mechanisms: IPSec • IPSec – Confidentiality, Authentication and Integrity – Supports TCP and UDP – Requires Pre-Shared Keys – Does not requires integration with SIP 16
SIP Security Mechanisms: IPSec • IPSec – Confidentiality, Authentication and Integrity – Supports TCP and UDP – Requires Pre-Shared Keys – Does not requires integration with SIP 16
 Secure SIP URI Scheme • SIPS URI Scheme – New URI Scheme – SIPS: user@example. com – MUST Implement If You Support TLS – If Request-URI Is SIPS, All Hops MUST Be Secure – If a hop cannot be secured, the transaction fails 17
Secure SIP URI Scheme • SIPS URI Scheme – New URI Scheme – SIPS: user@example. com – MUST Implement If You Support TLS – If Request-URI Is SIPS, All Hops MUST Be Secure – If a hop cannot be secured, the transaction fails 17
 SIP and Firewall • Challenges for SIP • Problem for the Media Stream – RTP will be blocked by FWs • Solutions: – FW must understand SIP and open ‘pin-holes’ for the RTP – Use Application-Level Gateways(ALG) trusted by FW – Some FWs have built-in ALG – Auth’n and Security policy controlled by ALG, not FW – ALG is B 2 BUA which proxies both the SIP signalling and Media Stream 18
SIP and Firewall • Challenges for SIP • Problem for the Media Stream – RTP will be blocked by FWs • Solutions: – FW must understand SIP and open ‘pin-holes’ for the RTP – Use Application-Level Gateways(ALG) trusted by FW – Some FWs have built-in ALG – Auth’n and Security policy controlled by ALG, not FW – ALG is B 2 BUA which proxies both the SIP signalling and Media Stream 18
 SIP and NAT • Network Address Translators: Serious problems for SIP ! • Changes IP Addresses and Port Numbers – SIP messages not routable ! Solutions: • SIP has a mechanism to detect presence of NAT – UAs and Proxy Sever can fix the IP addresses – This solves SIP signaling problem but NOT the Media Stream problem ! • New Protocols and Extensions for NAT traversal under development: STUN, ICE, rport, symmetric RTP, TURN, connection reuse, SDP attribute for RTCP, and others. 19
SIP and NAT • Network Address Translators: Serious problems for SIP ! • Changes IP Addresses and Port Numbers – SIP messages not routable ! Solutions: • SIP has a mechanism to detect presence of NAT – UAs and Proxy Sever can fix the IP addresses – This solves SIP signaling problem but NOT the Media Stream problem ! • New Protocols and Extensions for NAT traversal under development: STUN, ICE, rport, symmetric RTP, TURN, connection reuse, SDP attribute for RTCP, and others. 19


