8fa732825eb159c049fa9b04c14c3886.ppt
- Количество слайдов: 74
Kerberos • 雅典娜计划的一部分 (MIT)。 • 可信的第三方认证方案。 • 假定主机是不可信的 • 要求每个client (对每次业务请求 ) 证明 其身份. • 不要求用户每次业务请求都输入密码! Netprog 2002 - Kerberos 1
Kerberos Design • 用户必须在 作站会话开始的时候验证 自己 (登录会话). • 密码永远不在网络中明文传输 (或在存储 器中存储) Netprog 2002 - Kerberos 2
Kerberos Design (cont. ) • 每个用户有一个口令. • 每个业务有一个口令. • 知道所有口令的唯一实体是认证 服务器. Netprog 2002 - Kerberos 3
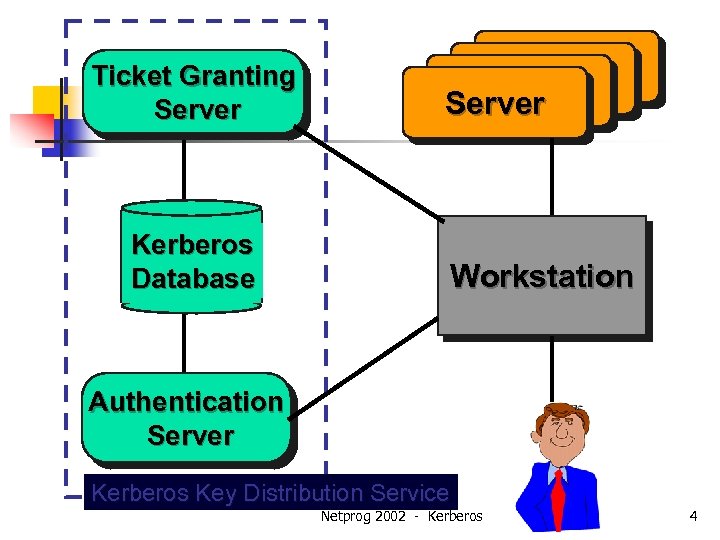
Ticket Granting Server Kerberos Database Server Workstation Authentication Server Kerberos Key Distribution Service Netprog 2002 - Kerberos 4
Tickets • 每个业务请求需要一个 ticket. • 一个 只能用于单个用户访问单个服务器. Netprog 2002 - Kerberos 5
Tickets (cont. ) • Tickets 由 “Ticket Granting Server” (TGS)分发, TGS有所有的加密密钥. • Tickets 对clients是无意义的, clients只是 用他们接入服务器. Netprog 2002 - Kerberos 6
Tickets (cont. ) • TGS 用服务器的加密密钥加密每个 ticket • 加密的tickets可在网上安全传输,只有服 务器可以解密. • 每一 ticket有有限的生存期 (几个小时). Netprog 2002 - Kerberos 7
Ticket Contents • Client名 (用户登陆名) • Server 名 • Client 主机网络地址 • Client/Server会话密钥 • Ticket 生存期 • 产生时戳 Netprog 2002 - Kerberos 8
会话密钥 • 分配给会话的随机数. • 会话密钥用于加密client和server间的请 求和响应 Netprog 2002 - Kerberos 9

Authenticators • 信任状证明client身份. • 包括 n n n Client 用户名. Client 网络地址. 时戳. • 信任状以 session key加密. Netprog 2002 - Kerberos 10

Bootstrap • 每次client要访问要申请新的ticket. • 为了从 TGS获得ticket, client 必须已经 有 TG ticket和一个会话密钥与TGS通信! Netprog 2002 - Kerberos 11

Authentication Server • Client向AS 发送明文请求以获得一个 ticket用于和TGS通信。 • 请求: n login name n TGS name 由于这个请求只包括公开的名字,不需要 加密. Netprog 2002 - Kerberos 12
Authentication Server • AS 找到与登陆名和TGS 名对应的密钥. • AS 生成一个ticket: n login name n TGS name n Client网络地址 TGS 会话密钥 • AS 以TGS 秘密密钥加密此ticket. n Netprog 2002 - Kerberos 13

Authentication Server Response • AS 同时产生一个随机会话密钥供client 和TGS 使用. • 会话密钥和加密的ticket 以用户的秘密密 钥加密. Sealed with TGS key Ticket: login name TGS session key net address TGS session key Sealed with user key Netprog 2002 - Kerberos 14

Accessing the TGS • Client以用户口令作为秘密密钥解密消息. • Client这时获得了会话密钥和与 TGS 通 信的ticket. • Client看不到ticket内部的内容, 因为client 不知道TGS 的秘密密钥. Netprog 2002 - Kerberos 15
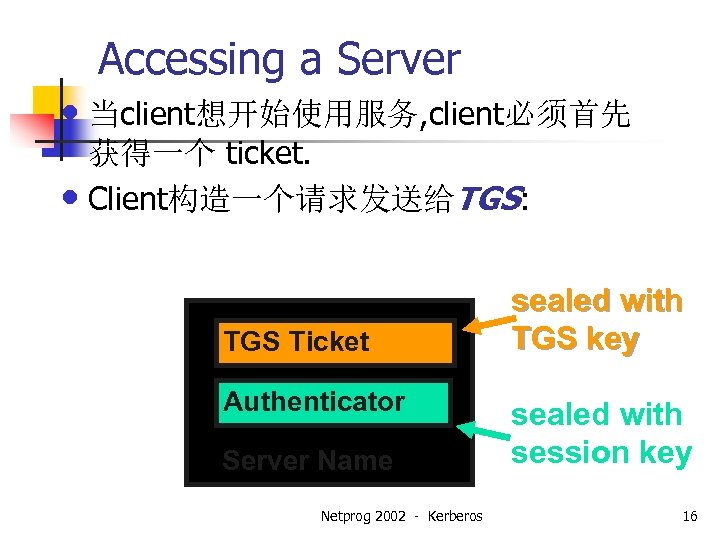
Accessing a Server • 当client想开始使用服务, client必须首先 获得一个 ticket. • Client构造一个请求发送给TGS: TGS Ticket Authenticator Server Name Netprog 2002 - Kerberos sealed with TGS key sealed with session key 16

TGS response • TGS 用其秘密密钥解密ticket获得TGS会话 密钥. • TGS 用会话密钥解密信任状. • TGS 检查验证登陆名,client地址和 TGS server名都正确. • TGS 验证信任状是最新的. Netprog 2002 - Kerberos 17
TGS Response 一旦所有验证通过,TGS: • 产生一个ticket使client用于请求的server. Ticket用server密钥加密. • 产生一个会话密钥 • 以TGS会话密钥加密整个消息发回给 client. Netprog 2002 - Kerberos 18
Client accesses Server • Client以TGS会话密钥解密TGS响应. • Client现在获得了与服务器通信的会话密 钥和ticket. • client 用与和访问TGS一样格式的数据访 问服务器。 Netprog 2002 - Kerberos 19
Kerberos Summary • 每业务请求需要一个 ticket. • Tickets 来源于TGS (除了访问TGS的 ticket). • 作站不能解密用服务器密钥加密的 tickets. • 每个 ticket有个相应的session key. • Tickets 不能重用. Netprog 2002 - Kerberos 20

Kerberos Summary (cont. ) • Tickets有有限的生命期. • 信任状只能使用一次. • 信任状失效的更快 ! • 服务器维护一个信任状列表 Netprog 2002 - Kerberos 21
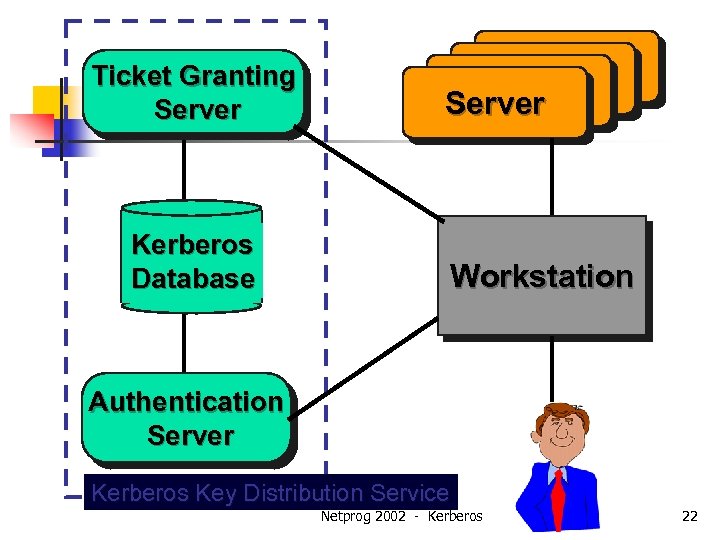
Ticket Granting Server Kerberos Database Server Workstation Authentication Server Kerberos Key Distribution Service Netprog 2002 - Kerberos 22
SSL Protocol Version 3. 0 and Open. SSL-0. 9. 6 a Viraj Bhat mail : virajb@caip. rutgers. edu Netprog 2002 - Kerberos 23
SSL Protocol Goals of the SSL protocol v 3. 0 in the order of their priority n Cryptographic security n Interoperability n Extensibility n Relative Efficiency Netprog 2002 - Kerberos 24

SSL Protocol Layer SSL protocol runs on the TCP/IP and below the HTTP and IMAP HTTP LDAP IMAP Application Layer Network Layer Secure Sockets Layer TCP/IP Layer Netprog 2002 - Kerberos 25

SSL Handshake 1)Client sends SSL version number, Cipher Settings, randomly generated data 2)Server sends SSL version number, Cipher Settings, randomly generated data 3)Client uses the info of STEP 2 for SERVER AUTHENTICATION if Failed TERMINATE if Successful go to STEP 4 5)If Server Requested for CLIENT AUTHENTICATION: Client Sends Signed Data & Encrypted Pre. Master Secret (This is Optional) 6)Server Authenticates Client, if failure TERMINATE else decrypt PREMASTER SECRET to generate MASTER SECRET SERVER CLIENT 4)Pre. Master Secret Generated for the session, encrypts it with the Server’s Public Key 7)Both the Client and Server use the Master Secret to Generate Session keys 8) and 9)Client and Server sends messages to each other that Handshake is finished Netprog 2002 - Kerberos 26
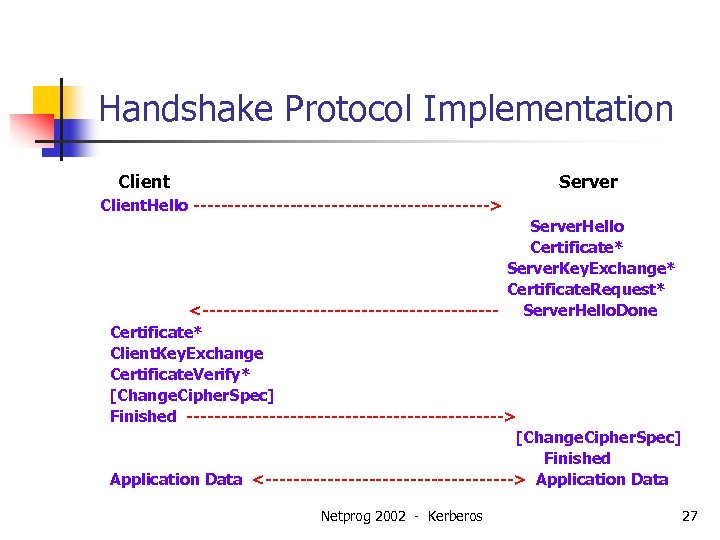
Handshake Protocol Implementation Client Server Client. Hello ----------------------> Server. Hello Certificate* Server. Key. Exchange* Certificate. Request* <---------------------- Server. Hello. Done Certificate* Client. Key. Exchange Certificate. Verify* [Change. Cipher. Spec] Finished -----------------------> [Change. Cipher. Spec] Finished Application Data <------------------> Application Data Netprog 2002 - Kerberos 27
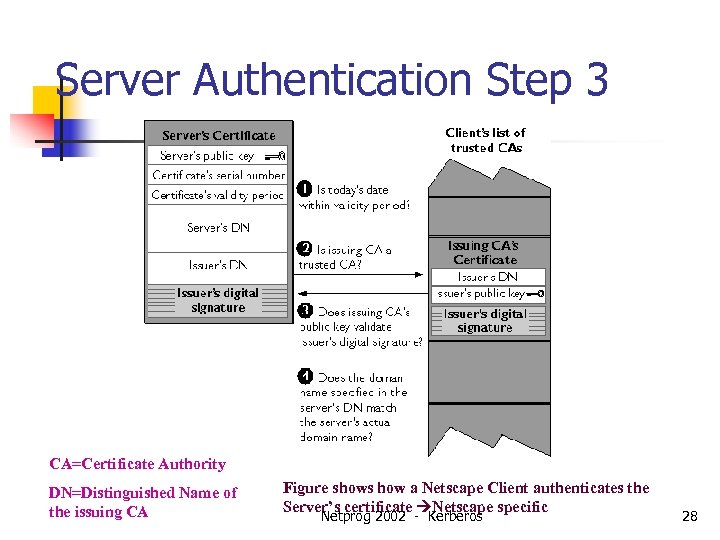
Server Authentication Step 3 CA=Certificate Authority DN=Distinguished Name of the issuing CA Figure shows how a Netscape Client authenticates the Server’s certificate Netscape specific Netprog 2002 - Kerberos 28
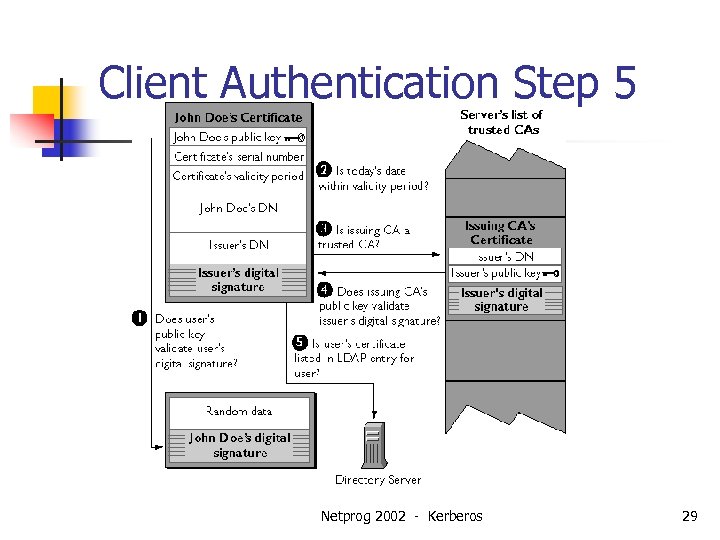
Client Authentication Step 5 Netprog 2002 - Kerberos 29
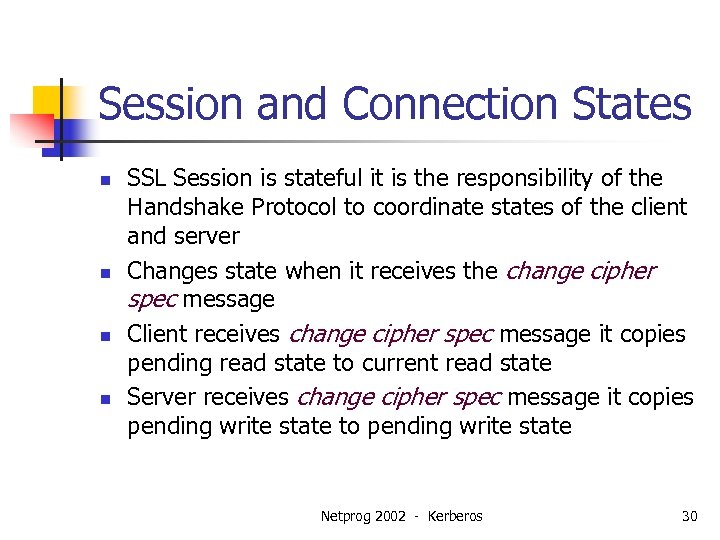
Session and Connection States n n SSL Session is stateful it is the responsibility of the Handshake Protocol to coordinate states of the client and server Changes state when it receives the change cipher spec message Client receives change cipher spec message it copies pending read state to current read state Server receives change cipher spec message it copies pending write state to pending write state Netprog 2002 - Kerberos 30

SSL Session States n SSL Session may include multiple secure connections. This state includes the following elements: n n n session identifier: an arbitrary byte sequence peer certificate: X 509. v 3 certificate of the peer compression method: compress data prior to encryption cipher spec: specifies bulk data encryption algorithm and a MAC(message authentication codes) algorithm master secret : 48 byte secret is resumable : a flag to indicate whether a new session can be instantiated Netprog 2002 - Kerberos 31
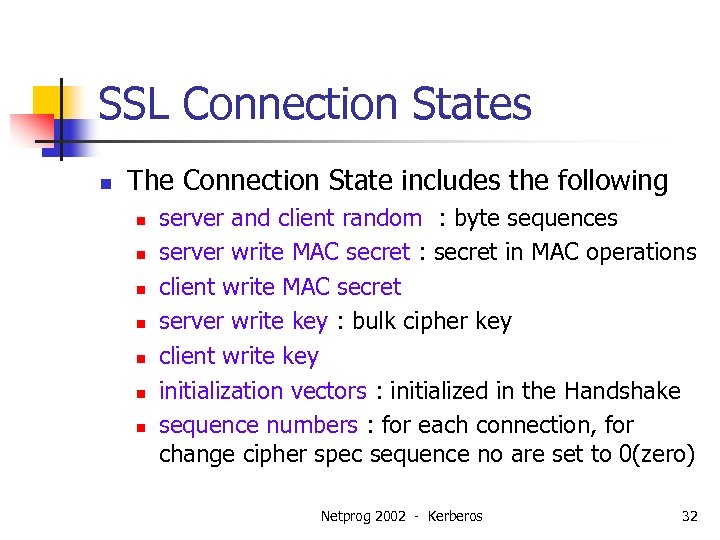
SSL Connection States n The Connection State includes the following n n n n server and client random : byte sequences server write MAC secret : secret in MAC operations client write MAC secret server write key : bulk cipher key client write key initialization vectors : initialized in the Handshake sequence numbers : for each connection, for change cipher spec sequence no are set to 0(zero) Netprog 2002 - Kerberos 32
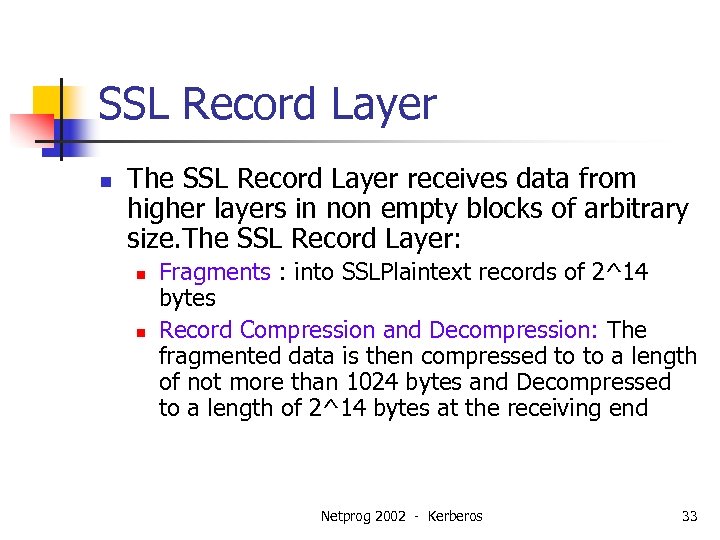
SSL Record Layer n The SSL Record Layer receives data from higher layers in non empty blocks of arbitrary size. The SSL Record Layer: n n Fragments : into SSLPlaintext records of 2^14 bytes Record Compression and Decompression: The fragmented data is then compressed to to a length of not more than 1024 bytes and Decompressed to a length of 2^14 bytes at the receiving end Netprog 2002 - Kerberos 33
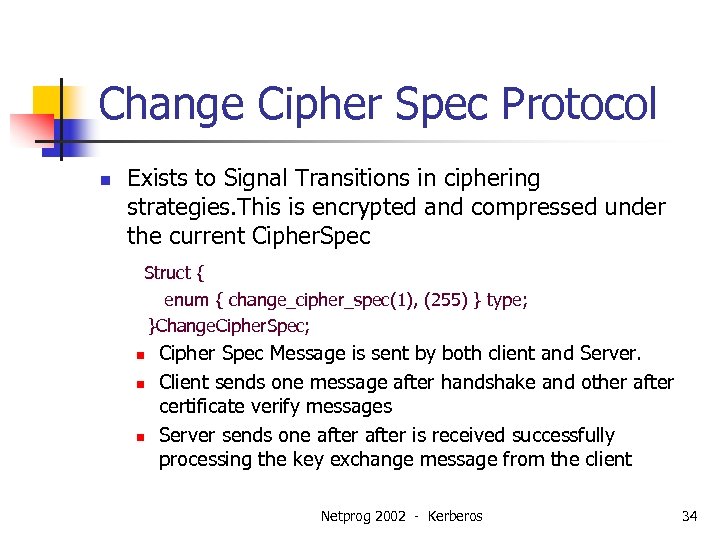
Change Cipher Spec Protocol n Exists to Signal Transitions in ciphering strategies. This is encrypted and compressed under the current Cipher. Spec Struct { enum { change_cipher_spec(1), (255) } type; }Change. Cipher. Spec; n n n Cipher Spec Message is sent by both client and Server. Client sends one message after handshake and other after certificate verify messages Server sends one after is received successfully processing the key exchange message from the client Netprog 2002 - Kerberos 34
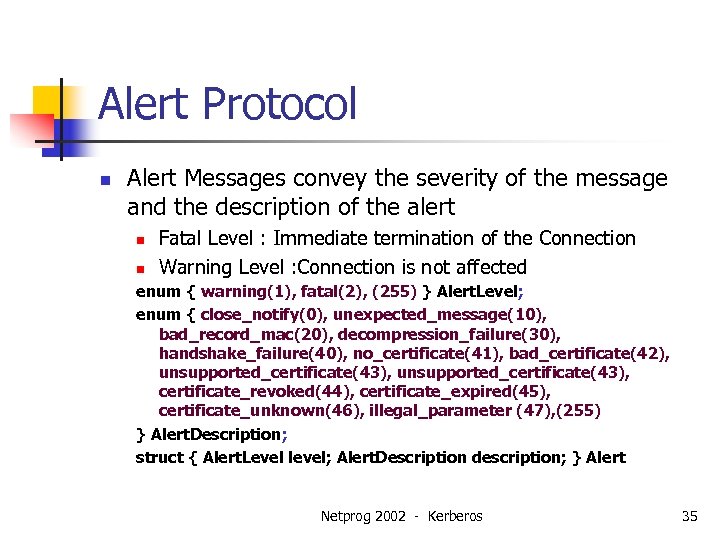
Alert Protocol n Alert Messages convey the severity of the message and the description of the alert n n Fatal Level : Immediate termination of the Connection Warning Level : Connection is not affected enum { warning(1), fatal(2), (255) } Alert. Level; enum { close_notify(0), unexpected_message(10), bad_record_mac(20), decompression_failure(30), handshake_failure(40), no_certificate(41), bad_certificate(42), unsupported_certificate(43), certificate_revoked(44), certificate_expired(45), certificate_unknown(46), illegal_parameter (47), (255) } Alert. Description; struct { Alert. Level level; Alert. Description description; } Alert Netprog 2002 - Kerberos 35
Encryption and Decryption n n Encryption: Process of transforming information so that is is unintelligible to anyone except the intended recipient Cryptographic Algorithm/Cipher is a mathematical function used for encryption and decryption Commonly used techniques for encryption and decryption are: n n Symmetric Key Encryption Public Key Encryption(Asymmetric Encryption) Netprog 2002 - Kerberos 36
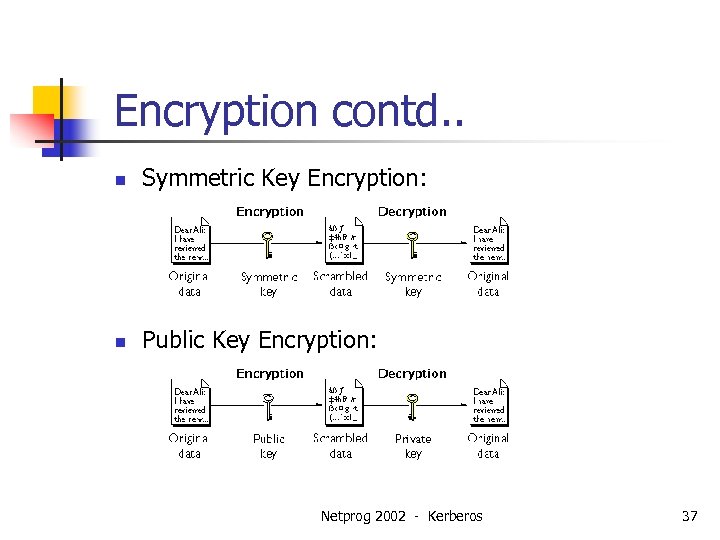
Encryption contd. . n Symmetric Key Encryption: n Public Key Encryption: Netprog 2002 - Kerberos 37

RSA Public Cryptosystem n n It is based on the dramatic difference between the ease of finding large prime numbers and difficulty of factoring the product of two large prime numbers Algorithm for the RSA Public-key crypto system 1)Select at random 2 large prime numbers p and q are 100 decimal digits each 2)Compute n = p * q 3)Select small odd integer e relatively prime to (n) which equals (p-1)(q-1) 4)Compute d as multiplicative inverse of e, modulo (n) 5)Publish pair P=(e, n) as his RSA public key 6)Keep pair S=(d, n) as his RSA secret key Netprog 2002 - Kerberos 38
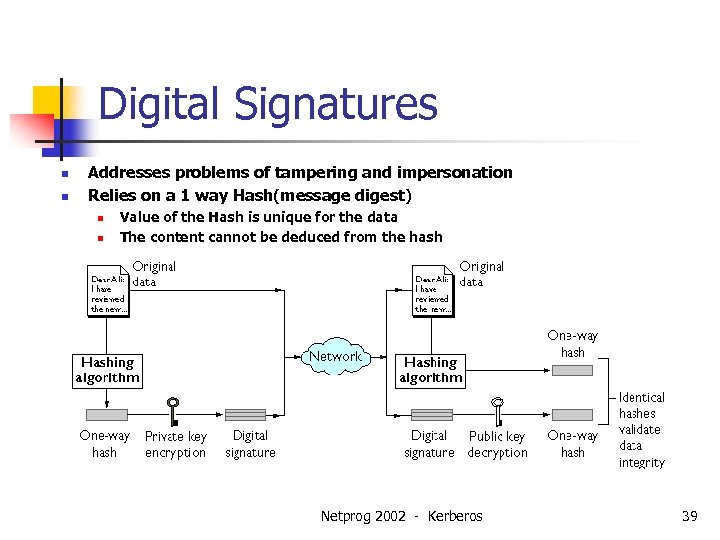
Digital Signatures n n Addresses problems of tampering and impersonation Relies on a 1 way Hash(message digest) n n Value of the Hash is unique for the data The content cannot be deduced from the hash Netprog 2002 - Kerberos 39
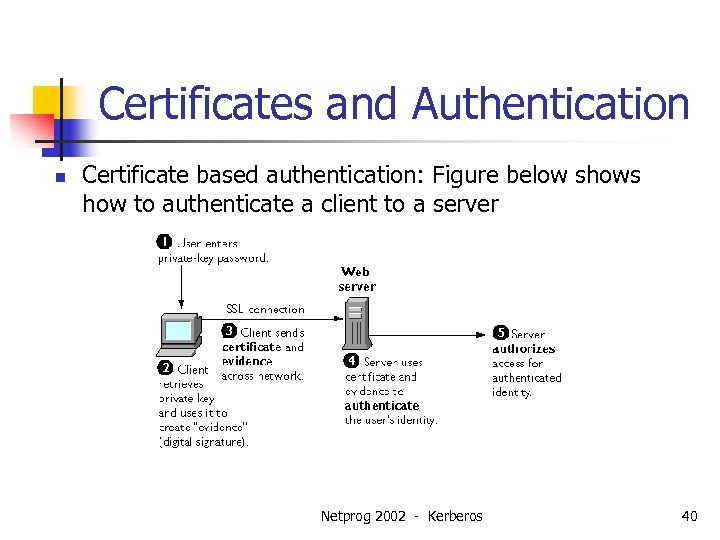
Certificates and Authentication n Certificate based authentication: Figure below shows how to authenticate a client to a server Netprog 2002 - Kerberos 40
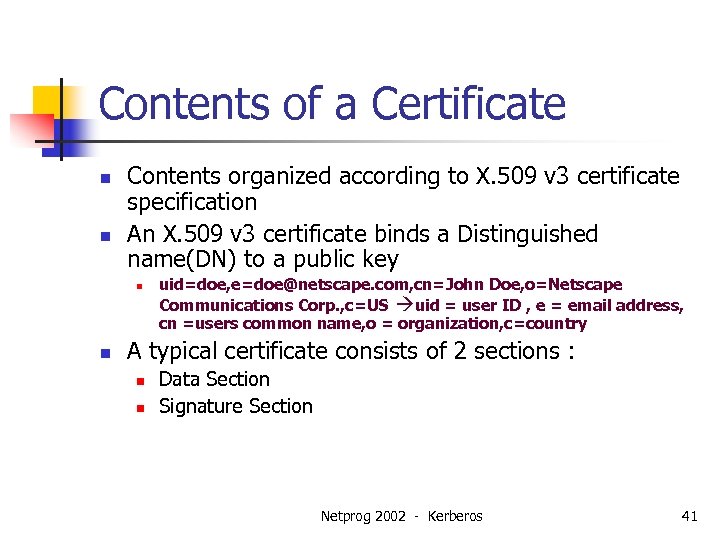
Contents of a Certificate n n Contents organized according to X. 509 v 3 certificate specification An X. 509 v 3 certificate binds a Distinguished name(DN) to a public key n n uid=doe, e=doe@netscape. com, cn=John Doe, o=Netscape Communications Corp. , c=US uid = user ID , e = email address, cn =users common name, o = organization, c=country A typical certificate consists of 2 sections : n n Data Section Signature Section Netprog 2002 - Kerberos 41

Certificate Contents n Data Section n n n n Version Number of the X. 509 standard Certificate’s Serial Number Information Info about users public key + algorithm + Rep of the key DN of the CA Validity Period DN of the certificate subject Optional Certificate Extensions Signature Section n n Cryptographic Algorithm used by the issuing CA CA’s digital Signature = Data in Certificate+CA’s Private key Netprog 2002 - Kerberos 42

How CA Certificates Are Used to Established the Truth ? n n By the way of CA hierarchies and Certificate Chains Verifying a Certificate Chain Netprog 2002 - Kerberos 43

Open. SSL n Open. SSL project is a collaborative effort to develop a robust commercial grade, full featured Open Source toolkit n n Implementing the Secure Sockets Layer SSL v 2 and v 3 Transport Layer Security v 1 Full Strength general purpose cryptographic libraries Based on the SSLeay library developed by Eric A Young and Tim J Hudson Netprog 2002 - Kerberos 44
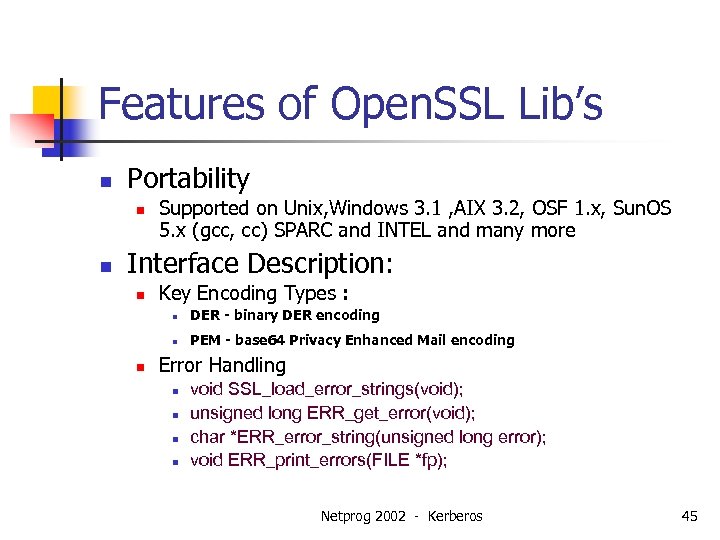
Features of Open. SSL Lib’s n Portability n n Supported on Unix, Windows 3. 1 , AIX 3. 2, OSF 1. x, Sun. OS 5. x (gcc, cc) SPARC and INTEL and many more Interface Description: n Key Encoding Types : n n n DER - binary DER encoding PEM - base 64 Privacy Enhanced Mail encoding Error Handling n n void SSL_load_error_strings(void); unsigned long ERR_get_error(void); char *ERR_error_string(unsigned long error); void ERR_print_errors(FILE *fp); Netprog 2002 - Kerberos 45
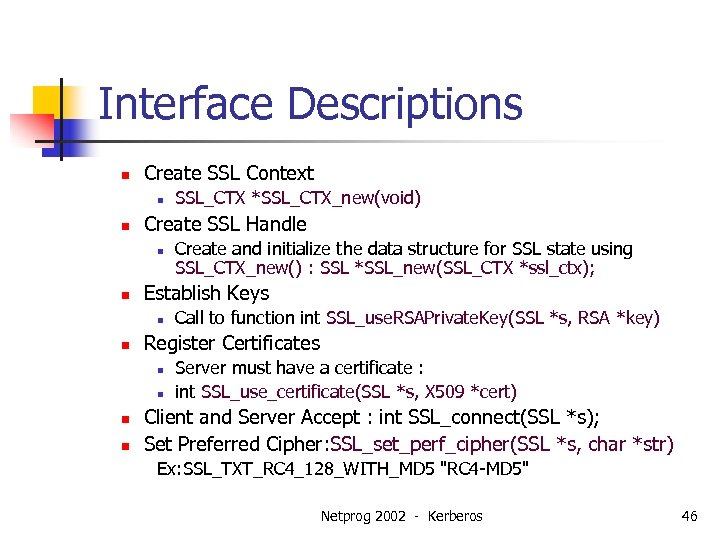
Interface Descriptions n Create SSL Context n n Create SSL Handle n n Call to function int SSL_use. RSAPrivate. Key(SSL *s, RSA *key) Register Certificates n n Create and initialize the data structure for SSL state using SSL_CTX_new() : SSL *SSL_new(SSL_CTX *ssl_ctx); Establish Keys n n SSL_CTX *SSL_CTX_new(void) Server must have a certificate : int SSL_use_certificate(SSL *s, X 509 *cert) Client and Server Accept : int SSL_connect(SSL *s); Set Preferred Cipher: SSL_set_perf_cipher(SSL *s, char *str) Ex: SSL_TXT_RC 4_128_WITH_MD 5 "RC 4 -MD 5" Netprog 2002 - Kerberos 46
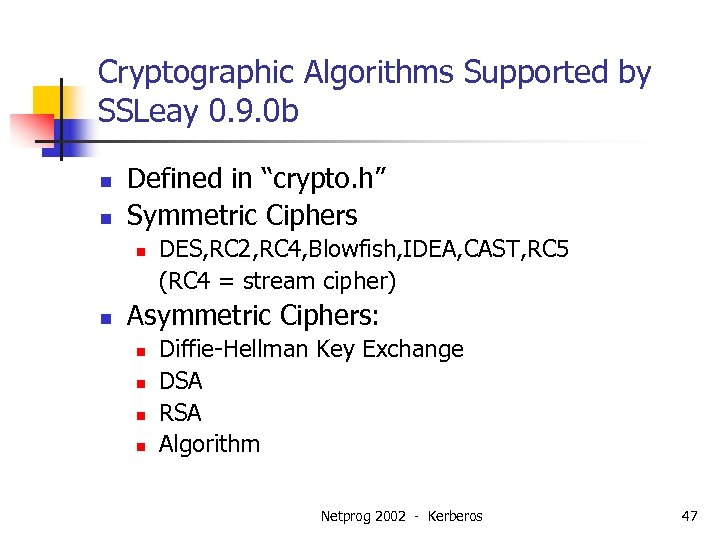
Cryptographic Algorithms Supported by SSLeay 0. 9. 0 b n n Defined in “crypto. h” Symmetric Ciphers n n DES, RC 2, RC 4, Blowfish, IDEA, CAST, RC 5 (RC 4 = stream cipher) Asymmetric Ciphers: n n Diffie-Hellman Key Exchange DSA RSA Algorithm Netprog 2002 - Kerberos 47
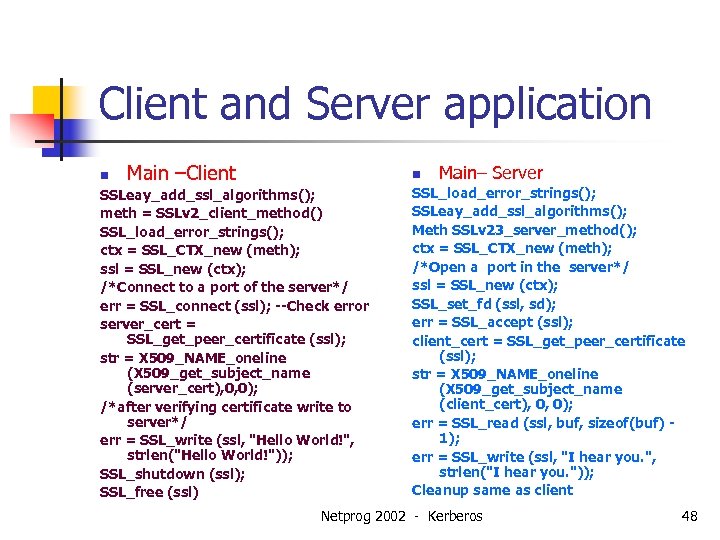
Client and Server application n Main –Client n SSLeay_add_ssl_algorithms(); meth = SSLv 2_client_method() SSL_load_error_strings(); ctx = SSL_CTX_new (meth); ssl = SSL_new (ctx); /*Connect to a port of the server*/ err = SSL_connect (ssl); --Check error server_cert = SSL_get_peer_certificate (ssl); str = X 509_NAME_oneline (X 509_get_subject_name (server_cert), 0, 0); /*after verifying certificate write to server*/ err = SSL_write (ssl, "Hello World!", strlen("Hello World!")); SSL_shutdown (ssl); SSL_free (ssl) Main– Server SSL_load_error_strings(); SSLeay_add_ssl_algorithms(); Meth SSLv 23_server_method(); ctx = SSL_CTX_new (meth); /*Open a port in the server*/ ssl = SSL_new (ctx); SSL_set_fd (ssl, sd); err = SSL_accept (ssl); client_cert = SSL_get_peer_certificate (ssl); str = X 509_NAME_oneline (X 509_get_subject_name (client_cert), 0, 0); err = SSL_read (ssl, buf, sizeof(buf) 1); err = SSL_write (ssl, "I hear you. ", strlen("I hear you. ")); Cleanup same as client Netprog 2002 - Kerberos 48
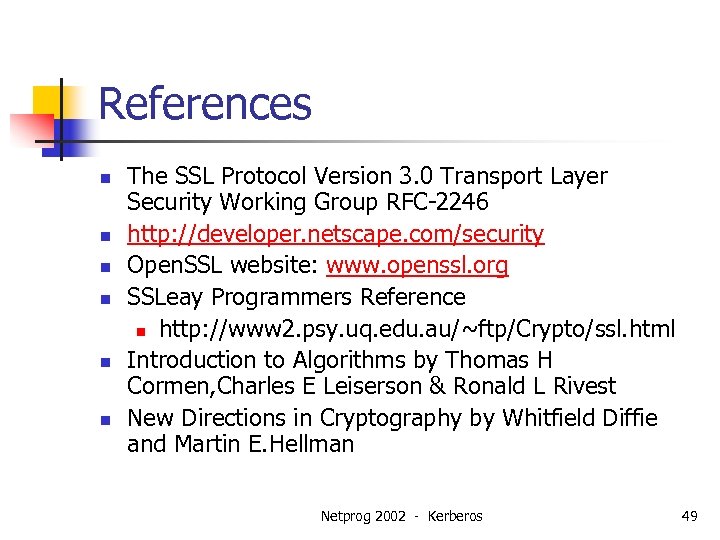
References n n n The SSL Protocol Version 3. 0 Transport Layer Security Working Group RFC-2246 http: //developer. netscape. com/security Open. SSL website: www. openssl. org SSLeay Programmers Reference n http: //www 2. psy. uq. edu. au/~ftp/Crypto/ssl. html Introduction to Algorithms by Thomas H Cormen, Charles E Leiserson & Ronald L Rivest New Directions in Cryptography by Whitfield Diffie and Martin E. Hellman Netprog 2002 - Kerberos 49

IPsec介绍 Netprog 2002 - Kerberos 50

提要 • • • IPsec 概述 安全关联Security Associations (SA) & SPI’s 认证头Authentication Header (AH)协议 封装安全载荷--Encapsulating Security Payload (ESP)协议 网间密钥交换 Internet Key Exchange (IKE) IPsec 缺陷 Netprog 2002 - Kerberos 51
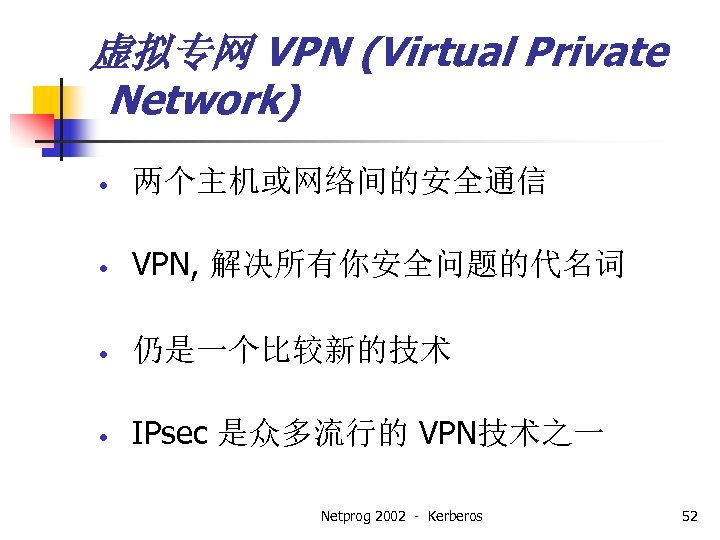
虚拟专网 VPN (Virtual Private Network) • 两个主机或网络间的安全通信 • VPN, 解决所有你安全问题的代名词 • 仍是一个比较新的技术 • IPsec 是众多流行的 VPN技术之一 Netprog 2002 - Kerberos 52
IPSEC能做什么 • • 认证 完整性 • 接入控制 • 机密性 • 重放保护 (部分) Netprog 2002 - Kerberos 53

通信的类型 • 主机到主机 • 主机到安全网关 • 安全网关到安全网关 • • 安全网关 = 防火墙 也称为网络到网络 Netprog 2002 - Kerberos 54
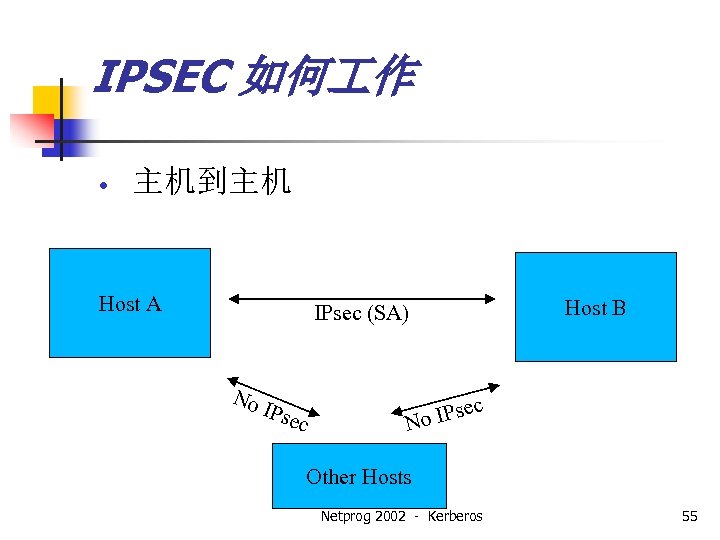
IPSEC 如何 作 • 主机到主机 Host A Host B IPsec (SA) No IP sec ec s No IP Other Hosts Netprog 2002 - Kerberos 55
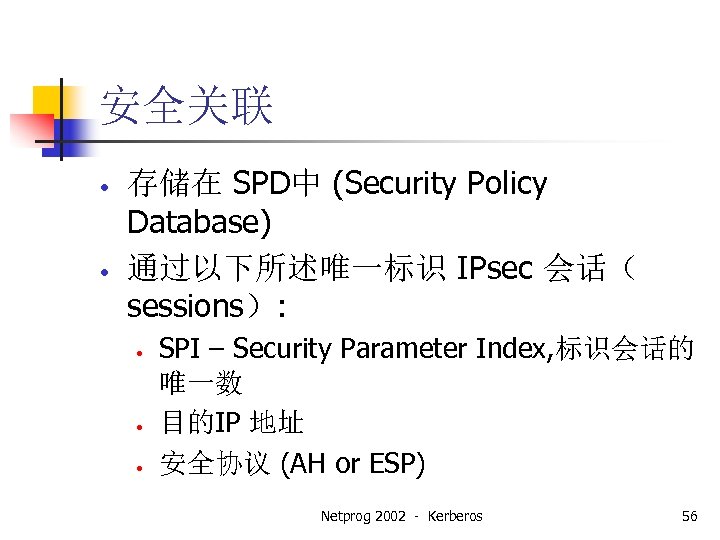
安全关联 • • 存储在 SPD中 (Security Policy Database) 通过以下所述唯一标识 IPsec 会话( sessions): • • • SPI – Security Parameter Index, 标识会话的 唯一数 目的IP 地址 安全协议 (AH or ESP) Netprog 2002 - Kerberos 56
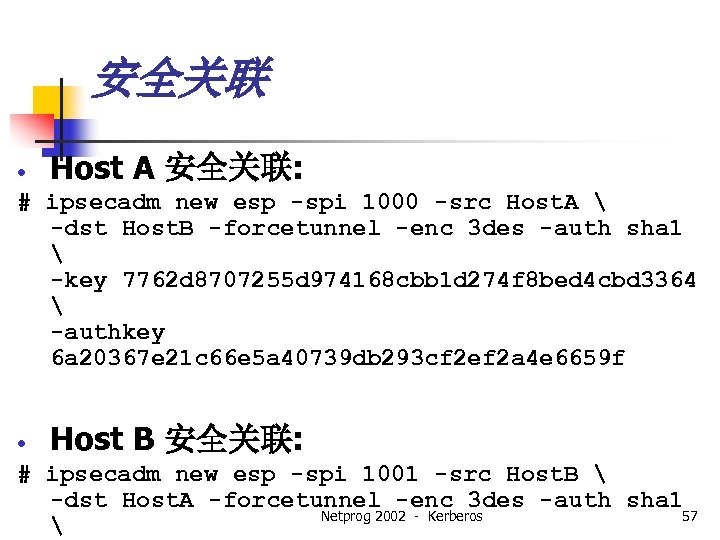
安全关联 • Host A 安全关联: # ipsecadm new esp -spi 1000 -src Host. A -dst Host. B -forcetunnel -enc 3 des -auth sha 1 -key 7762 d 8707255 d 974168 cbb 1 d 274 f 8 bed 4 cbd 3364 -authkey 6 a 20367 e 21 c 66 e 5 a 40739 db 293 cf 2 ef 2 a 4 e 6659 f • Host B 安全关联: # ipsecadm new esp -spi 1001 -src Host. B -dst Host. A -forcetunnel -enc 3 des -auth sha 1 Netprog 2002 - Kerberos 57
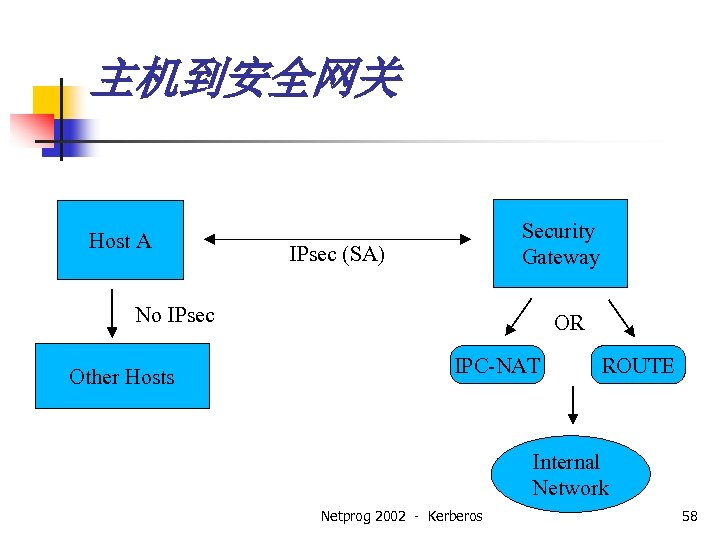
主机到安全网关 Host A Security Gateway IPsec (SA) No IPsec Other Hosts OR IPC-NAT ROUTE Internal Network Netprog 2002 - Kerberos 58
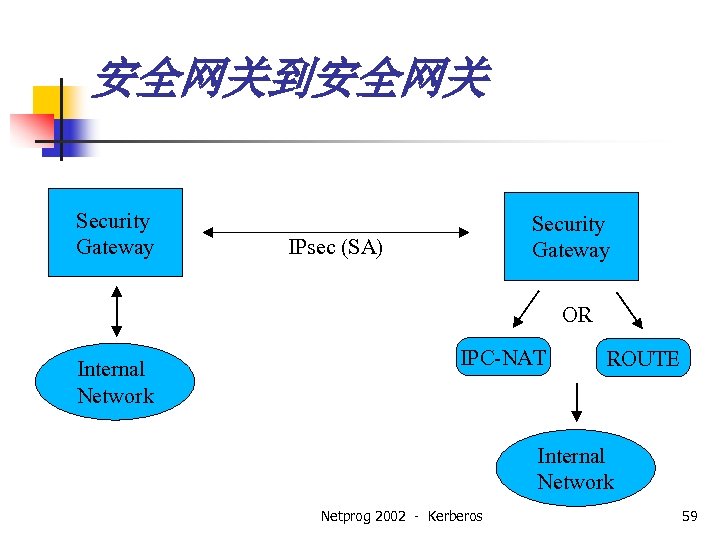
安全网关到安全网关 Security Gateway IPsec (SA) OR Internal Network IPC-NAT ROUTE Internal Network Netprog 2002 - Kerberos 59
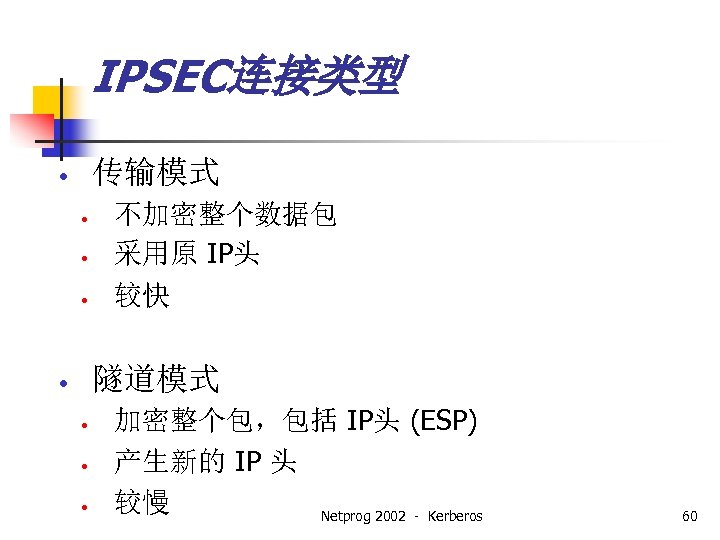
IPSEC连接类型 传输模式 • • 不加密整个数据包 采用原 IP头 较快 隧道模式 • • 加密整个包,包括 IP头 (ESP) 产生新的 IP 头 较慢 Netprog 2002 - Kerberos 60

通常的 TCP/IP 包 应用层 (5 -7) / 数据 TCP/UDP 头 (Layer 4) IP 头 (Layer 3) 帧层 (Layer 2) 或 帧头 IP 头 TCP/UDP Netprog 2002 - Kerberos 数据 61

AH (认证头) • • • IP 协议 51 提供包的认证 不加密载荷 传输模式 IP 头 IP Hdr AH TCP/UDP Data 数据 AH 原 IP 头 TCP/UDP Tunnel Mode 新IP头 IP Hdr Netprog 2002 - Kerberos 数据 62

ESP (封装安全载荷) • • • IP 协议 50 加密载荷 提供加密和认证 Transport Mode IP Hdr IP 头 AH ESP TCP/UDP Data 数据 AH ESP 原 IP 头 TCP/UDP Tunnel Mode 新 IP 头 Netprog 2002 - Kerberos 数据 63
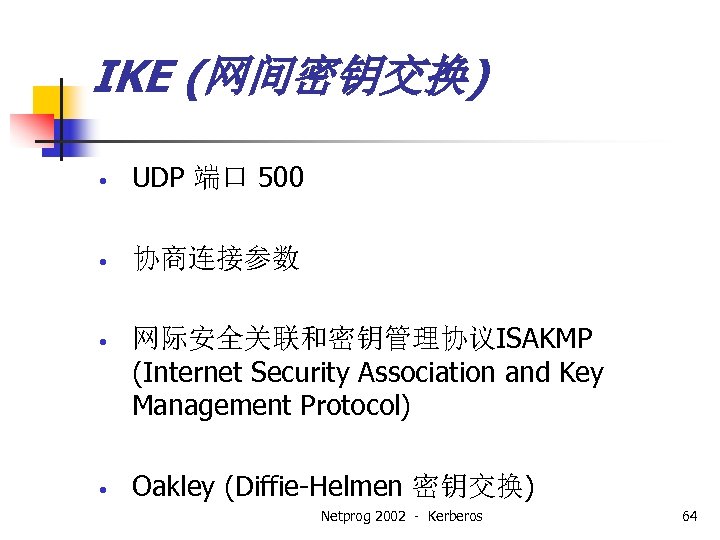
IKE (网间密钥交换) • UDP 端口 500 • 协商连接参数 • 网际安全关联和密钥管理协议ISAKMP (Internet Security Association and Key Management Protocol) • Oakley (Diffie-Helmen 密钥交换) Netprog 2002 - Kerberos 64
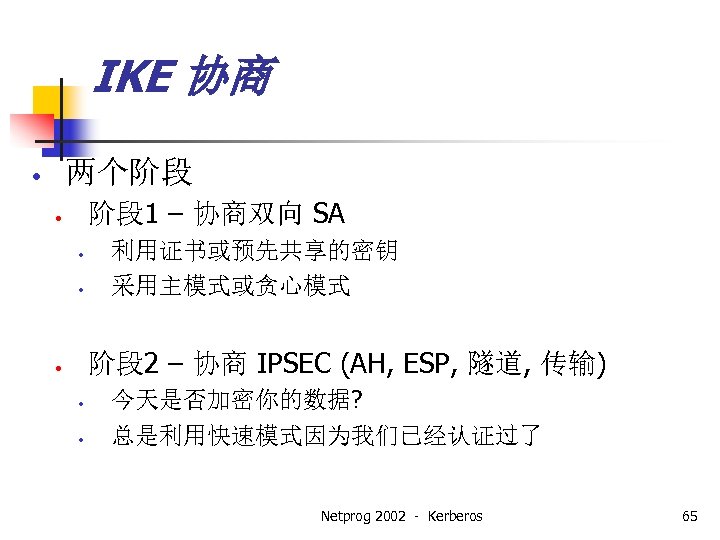
IKE 协商 两个阶段 • 阶段 1 – 协商双向 SA • • • 利用证书或预先共享的密钥 采用主模式或贪心模式 阶段 2 – 协商 IPSEC (AH, ESP, 隧道, 传输) • • • 今天是否加密你的数据? 总是利用快速模式因为我们已经认证过了 Netprog 2002 - Kerberos 65
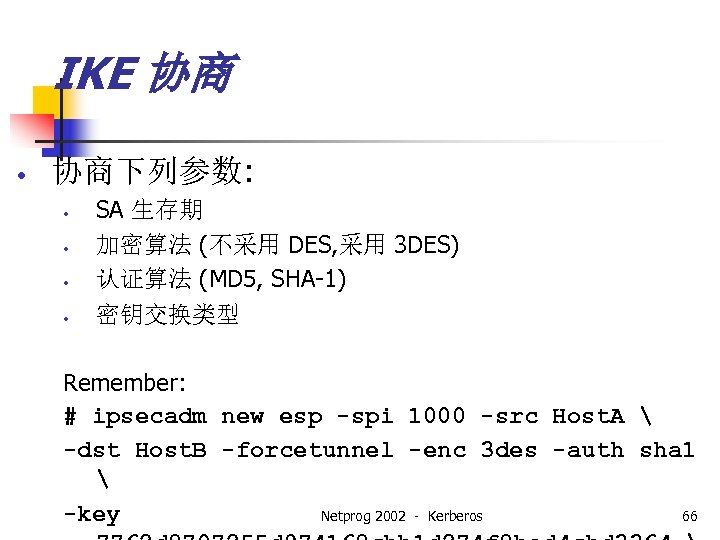
IKE 协商 • 协商下列参数: • • SA 生存期 加密算法 (不采用 DES, 采用 3 DES) 认证算法 (MD 5, SHA-1) 密钥交换类型 Remember: # ipsecadm new esp -spi 1000 -src Host. A -dst Host. B -forcetunnel -enc 3 des -auth sha 1 -key Netprog 2002 - Kerberos 66
IPSec 举例 • 只使用ESP • 在同一网络的两个主机: • • Jerry 192. 168. 0. 11 - Open. BSD 2. 8 Tom 192. 168. 0. 17 – Open. BSD 2. 7 Netprog 2002 - Kerberos 67
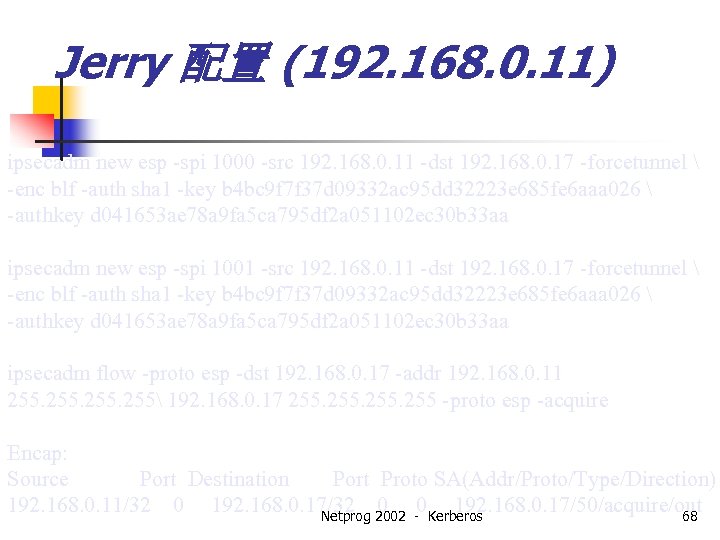
Jerry 配置 (192. 168. 0. 11) ipsecadm new esp -spi 1000 -src 192. 168. 0. 11 -dst 192. 168. 0. 17 -forcetunnel -enc blf -auth sha 1 -key b 4 bc 9 f 7 f 37 d 09332 ac 95 dd 32223 e 685 fe 6 aaa 026 -authkey d 041653 ae 78 a 9 fa 5 ca 795 df 2 a 051102 ec 30 b 33 aa ipsecadm new esp -spi 1001 -src 192. 168. 0. 11 -dst 192. 168. 0. 17 -forcetunnel -enc blf -auth sha 1 -key b 4 bc 9 f 7 f 37 d 09332 ac 95 dd 32223 e 685 fe 6 aaa 026 -authkey d 041653 ae 78 a 9 fa 5 ca 795 df 2 a 051102 ec 30 b 33 aa ipsecadm flow -proto esp -dst 192. 168. 0. 17 -addr 192. 168. 0. 11 255 192. 168. 0. 17 255 -proto esp -acquire Encap: Source Port Destination Port Proto SA(Addr/Proto/Type/Direction) 192. 168. 0. 11/32 0 192. 168. 0. 17/32 2002 -0 Kerberos 0 192. 168. 0. 17/50/acquire/out Netprog 68
Tom Configuration (192. 168. 0. 17) ipsecadm new esp -spi 1001 -src 192. 168. 0. 17 -dst 192. 168. 0. 11 -forcetunnel -enc blf -auth sha 1 -key b 4 bc 9 f 7 f 37 d 09332 ac 95 dd 32223 e 685 fe 6 aaa 026 -authkey d 041653 ae 78 a 9 fa 5 ca 795 df 2 a 051102 ec 30 b 33 aa ipsecadm new esp -spi 1000 -src 192. 168. 0. 17 -dst 192. 168. 0. 11 -forcetunnel -enc blf -auth sha 1 -key b 4 bc 9 f 7 f 37 d 09332 ac 95 dd 32223 e 685 fe 6 aaa 026 -authkey d 041653 ae 78 a 9 fa 5 ca 795 df 2 a 051102 ec 30 b 33 aa ipsecadm flow -proto esp -dst 192. 168. 0. 11 -spi 1001 -addr 192. 168. 0. 17 255 192. 168. 0. 11 255 Encap: Source Port Destination Port Proto SA(Address/SPI/Proto) 192. 168. 0. 17/32 0 192. 168. 0. 11/32 2002 - 0 Kerberos 0 192. 168. 0. 11/00001001/50 Netprog 69
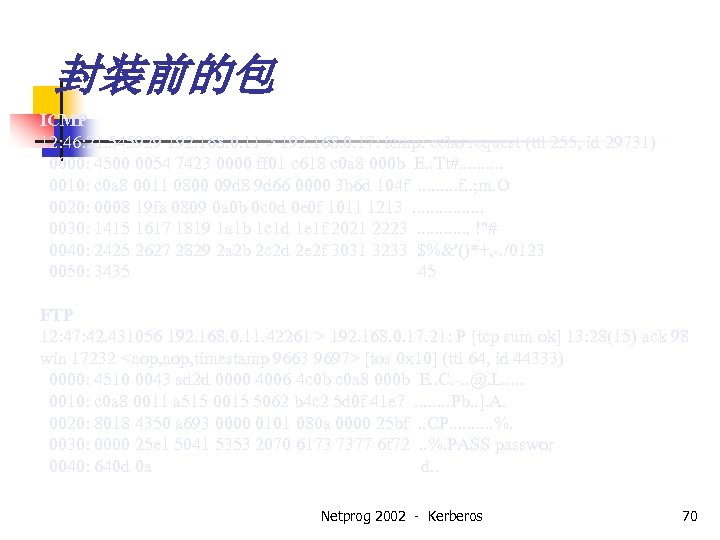
封装前的包 ICMP 12: 46: 21. 545929 192. 168. 0. 11 > 192. 168. 0. 17: icmp: echo request (ttl 255, id 29731) 0000: 4500 0054 7423 0000 ff 01 c 618 c 0 a 8 000 b E. . Tt#. . 0010: c 0 a 8 0011 0800 09 d 8 9 d 66 0000 3 b 6 d 104 f. . ; m. O 0020: 0008 19 fa 0809 0 a 0 b 0 c 0 d 0 e 0 f 1011 1213. . . . 0030: 1415 1617 1819 1 a 1 b 1 c 1 d 1 e 1 f 2021 2223. . . !"# 0040: 2425 2627 2829 2 a 2 b 2 c 2 d 2 e 2 f 3031 3233 $%&'()*+, -. /0123 0050: 3435 45 FTP 12: 47: 42. 431056 192. 168. 0. 11. 42261 > 192. 168. 0. 17. 21: P [tcp sum ok] 13: 28(15) ack 98 win 17232 <nop, timestamp 9663 9697> [tos 0 x 10] (ttl 64, id 44333) 0000: 4510 0043 ad 2 d 0000 4006 4 c 0 b c 0 a 8 000 b E. . C. -. . @. L. . . 0010: c 0 a 8 0011 a 515 0015 5062 b 4 c 2 5 d 0 f 41 e 7. . . . Pb. . ]. A. 0020: 8018 4350 a 693 0000 0101 080 a 0000 25 bf. . CP. . %. 0030: 0000 25 e 1 5041 5353 2070 6173 7377 6 f 72. . %. PASS passwor 0040: 640 d 0 a d. . Netprog 2002 - Kerberos 70
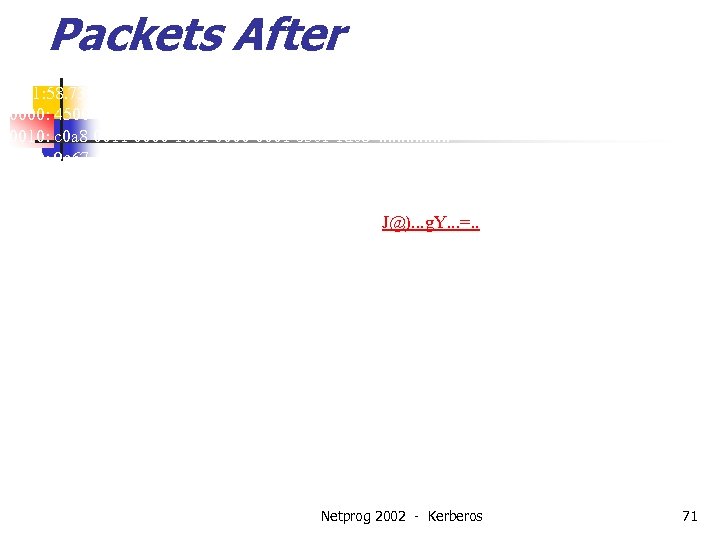
Packets After ICMP 12: 51: 58. 736930 esp 192. 168. 0. 11 > 192. 168. 0. 17 spi 0 x 00001001 seq 1 len 116 (ttl 64, id 16933) 0000: 4500 0088 4225 0000 4032 b 6 b 2 c 0 a 8 000 b E. . . B%. . @2. . . 0010: c 0 a 8 0011 0000 1001 0000 0001 b 5 c 1 1 de 8. . . . 0020: 9 e 67 4463 cab 1 f 496 2970 e 7 d 9 267 c 0 cef. g. Dc. . )p. . &|. . 0030: 6 bfc a 5 d 6 6 f 6 a 9 f 51 0 e 95 20 fe c 930 0 e 77 k. . . oj. Q. . 0. w 0040: 2918 6 c 92 d 7 ac 6 c 13 f 9 f 1 de 8 b 1674 fd 42 ). l. . . . t. B 0050: be 98 4 a 40 29 e 8 9 ecb 6759 cfbe 993 d 1001. . J@). . . g. Y. . . =. . 0060: 0 f 11 0 b 8 b 5 e 93 8852 dc 28 786 b 2479 465 d. . ^. . R. (xk$y. F] 0070: 5 a 67 d 503 6 b 51 ff 0 b 074 c 0076 6 d 03 a 1 ec Zg. . k. Q. . . L. vm. . . 0080: 5 b 14 765 f cb 06 51 f 8 [. v_. . Q. FTP 12: 52: 29. 730868 esp 192. 168. 0. 11 > 192. 168. 0. 17 spi 0 x 00001001 seq 2 len 100 (ttl 64, id 28675) 0000: 4500 0078 7003 0000 4032 88 e 4 c 0 a 8 000 b E. . xp. . . @2. . . 0010: c 0 a 8 0011 0000 1001 0000 0002 6 b 51 ff 0 b. . . k. Q. . 0020: 074 c 0076 30 fa 28 c 7 ef 53 592 a 7 b 13 a 068. L. v 0. (. . SY*{. . h 0030: 06 bf 071 d 81 a 0 98 de ddd 8 0174 b 637 2 b 9 a. . . t. 7+. 0040: f 1 d 2 a 36 e d 83 a 08 ec 59 bf 5341 a 4 b 3 7 ae 5. . . n. : . . Y. SA. . z. 0050: bbc 3 000 b d 2 b 1 e 93 c e 086 cf 69 71 d 6 dcf 5. . . . <. . . iq. . . 0060: 8498 13 d 7 8930 2451 f 43 b b 6 fc 4 abc da 2 c. . . 0$Q. ; . . J. . , Netprog 2002 - Kerberos 71 0070: 77 c 5 91 dd ab 2 e ba 11 w. . . .
IPsec 缺点 • • • 太复杂, 有许多不同的配置方式 可能配置的不安全 客户端安全是个问题 Netprog 2002 - Kerberos 72

IPSec 相对于 SSL/TLS的优点 • 加密整个包,包括IP头 • 可以加密整个协议 • 当使用网关到网关方式时不影响用户 • 有独立的 IP 地址 Netprog 2002 - Kerberos 73
支持 IPsec的操作系统 • • Open. BSD, Free. BSD, Net. BSD Linux Solaris Windows 2000 (Native) Windows NT/95/98/Me (Add-on) Cisco IOS (PIX and Routers) Others as well. . Netprog 2002 - Kerberos 74
8fa732825eb159c049fa9b04c14c3886.ppt