de89812e5356dc0933307fd75a464064.ppt
- Количество слайдов: 33
 ITU-T Workshop on “New challenges for Telecommunication Security Standardizations" Geneva, 9(pm)-10 February 2009 Identification Services as provided by directories (X. 500 incl. X 509) Erik Andersen, Consultant, Andersen’s L-Service Q. 11/17 Rapporteur era@x 500. eu, www. x 500. eu Geneva, 9(pm)-10 February 2009 International Telecommunication Union
ITU-T Workshop on “New challenges for Telecommunication Security Standardizations" Geneva, 9(pm)-10 February 2009 Identification Services as provided by directories (X. 500 incl. X 509) Erik Andersen, Consultant, Andersen’s L-Service Q. 11/17 Rapporteur era@x 500. eu, www. x 500. eu Geneva, 9(pm)-10 February 2009 International Telecommunication Union
 Why listen to this presentation? How identification services relates to security How directories relate to identification services Why X. 500 (and LDAP) is an obvious answer to identification services Geneva, 9(pm)-10 February 2009 International Telecommunication Union 2
Why listen to this presentation? How identification services relates to security How directories relate to identification services Why X. 500 (and LDAP) is an obvious answer to identification services Geneva, 9(pm)-10 February 2009 International Telecommunication Union 2
 About the X. 500 directory specification First edition in 1988 Been under continuous expansion since to meet new requirements Developed in collaboration with ISO/IEC JTC 1/SC 6 Within ISO/IEC known as the ISO/IEC 9594 multipart standard Many highly skilled people have participated during the years Geneva, 9(pm)-10 February 2009 International Telecommunication Union 3
About the X. 500 directory specification First edition in 1988 Been under continuous expansion since to meet new requirements Developed in collaboration with ISO/IEC JTC 1/SC 6 Within ISO/IEC known as the ISO/IEC 9594 multipart standard Many highly skilled people have participated during the years Geneva, 9(pm)-10 February 2009 International Telecommunication Union 3
 About the X. 500 directory specification (cont. ) Six editions so far – the seventh edition on its way Consists of 10 parts (incl. X. 509) Defines a naming structure that allows unique naming of all entities Support for distribution and replication Lightweight Directory Access Protocol (LDAP) is a dear child of X. 500 (uses the X. 500 model) Geneva, 9(pm)-10 February 2009 International Telecommunication Union 4
About the X. 500 directory specification (cont. ) Six editions so far – the seventh edition on its way Consists of 10 parts (incl. X. 509) Defines a naming structure that allows unique naming of all entities Support for distribution and replication Lightweight Directory Access Protocol (LDAP) is a dear child of X. 500 (uses the X. 500 model) Geneva, 9(pm)-10 February 2009 International Telecommunication Union 4
 Identity and security IT Security comprises many things: Physical attacks Hacker attacks Spam Denial of service Fraud by employees --Identity related security issues Geneva, 9(pm)-10 February 2009 International Telecommunication Union 5
Identity and security IT Security comprises many things: Physical attacks Hacker attacks Spam Denial of service Fraud by employees --Identity related security issues Geneva, 9(pm)-10 February 2009 International Telecommunication Union 5
 Identity Related Security Issues Related to: Information about people and other entities Access to systems and Services Accounts Authorisation Software code Geneva, 9(pm)-10 February 2009 International Telecommunication Union 6
Identity Related Security Issues Related to: Information about people and other entities Access to systems and Services Accounts Authorisation Software code Geneva, 9(pm)-10 February 2009 International Telecommunication Union 6
 Identity Management (Id. M) includes Identification Services It is much in focus within ITU-T Study Group 17 and other committees Considered an important aspect of Next Generation Network (NGN) Not a new issue Geneva, 9(pm)-10 February 2009 International Telecommunication Union 7
Identity Management (Id. M) includes Identification Services It is much in focus within ITU-T Study Group 17 and other committees Considered an important aspect of Next Generation Network (NGN) Not a new issue Geneva, 9(pm)-10 February 2009 International Telecommunication Union 7
 X 500 is (part of) Id. M We have been in the Identity Management (Id. M) Business since 1984 We got a head start! Geneva, 9(pm)-10 February 2009 International Telecommunication Union 8
X 500 is (part of) Id. M We have been in the Identity Management (Id. M) Business since 1984 We got a head start! Geneva, 9(pm)-10 February 2009 International Telecommunication Union 8
 Butler group report X. 500/LDAP basis for most current Id. M implementations In the industry often called Identity and Access Management (IAM) Geneva, 9(pm)-10 February 2009 International Telecommunication Union 9
Butler group report X. 500/LDAP basis for most current Id. M implementations In the industry often called Identity and Access Management (IAM) Geneva, 9(pm)-10 February 2009 International Telecommunication Union 9
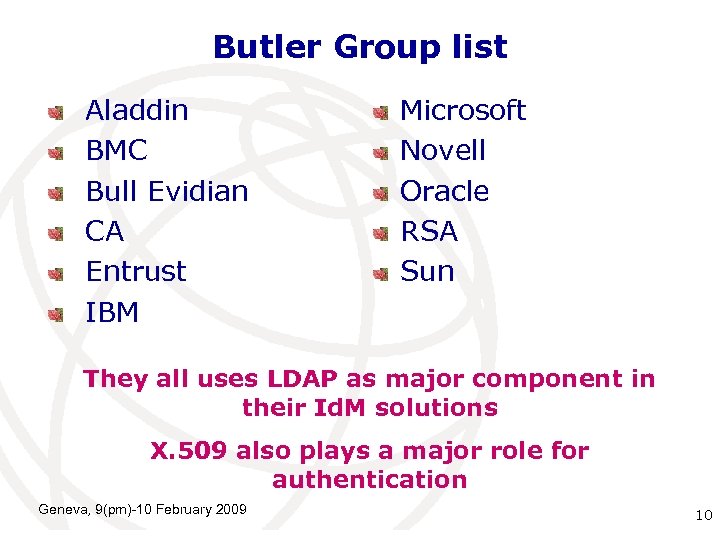 Butler Group list Aladdin BMC Bull Evidian CA Entrust IBM Microsoft Novell Oracle RSA Sun They all uses LDAP as major component in their Id. M solutions X. 509 also plays a major role for authentication Geneva, 9(pm)-10 February 2009 International Telecommunication 10 Union
Butler Group list Aladdin BMC Bull Evidian CA Entrust IBM Microsoft Novell Oracle RSA Sun They all uses LDAP as major component in their Id. M solutions X. 509 also plays a major role for authentication Geneva, 9(pm)-10 February 2009 International Telecommunication 10 Union
 Other vendors Isode Siemens e. B 2 Bcom Critical Path Etc. Geneva, 9(pm)-10 February 2009 International Telecommunication 11 Union
Other vendors Isode Siemens e. B 2 Bcom Critical Path Etc. Geneva, 9(pm)-10 February 2009 International Telecommunication 11 Union
 The requirement for authentication Before giving access to services and information, the identity of the accessing entity must be established Different levels of authentication The required level depends on Sensitivity of service or information Whether interrogation or update Geneva, 9(pm)-10 February 2009 International Telecommunication 12 Union
The requirement for authentication Before giving access to services and information, the identity of the accessing entity must be established Different levels of authentication The required level depends on Sensitivity of service or information Whether interrogation or update Geneva, 9(pm)-10 February 2009 International Telecommunication 12 Union
 Scope of X. 500 identity services Storage of identity information Protection of the information in the directory Use of X. 509 capabilities outside directories (e. g. required by SSL, used my SAML 2, etc. Geneva, 9(pm)-10 February 2009 International Telecommunication 13 Union
Scope of X. 500 identity services Storage of identity information Protection of the information in the directory Use of X. 509 capabilities outside directories (e. g. required by SSL, used my SAML 2, etc. Geneva, 9(pm)-10 February 2009 International Telecommunication 13 Union
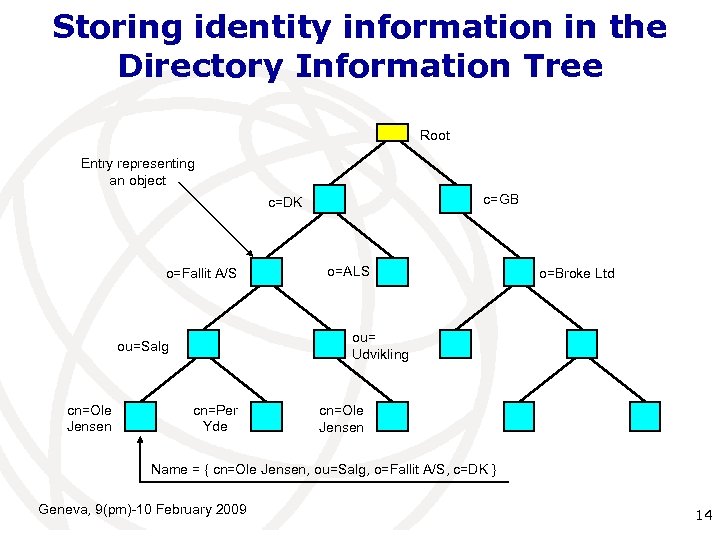 Storing identity information in the Directory Information Tree Root Entry representing an object c=GB c=DK o=Fallit A/S o=Broke Ltd ou= Udvikling ou=Salg cn=Ole Jensen o=ALS cn=Per Yde cn=Ole Jensen Name = { cn=Ole Jensen, ou=Salg, o=Fallit A/S, c=DK } Geneva, 9(pm)-10 February 2009 International Telecommunication 14 Union
Storing identity information in the Directory Information Tree Root Entry representing an object c=GB c=DK o=Fallit A/S o=Broke Ltd ou= Udvikling ou=Salg cn=Ole Jensen o=ALS cn=Per Yde cn=Ole Jensen Name = { cn=Ole Jensen, ou=Salg, o=Fallit A/S, c=DK } Geneva, 9(pm)-10 February 2009 International Telecommunication 14 Union
 Protecting Directory Identity Information Geneva, 9(pm)-10 February 2009 International Telecommunication 15 Union
Protecting Directory Identity Information Geneva, 9(pm)-10 February 2009 International Telecommunication 15 Union
 Levels of authentication X. 500 allows the following means of authentication: None Directory Name and Password Simple Authentication and Security Layer (SASL) (Also used by LDAP) SPKM - Simple Public-Key Mechanism Strong authentication (use of X. 509) Geneva, 9(pm)-10 February 2009 International Telecommunication 16 Union
Levels of authentication X. 500 allows the following means of authentication: None Directory Name and Password Simple Authentication and Security Layer (SASL) (Also used by LDAP) SPKM - Simple Public-Key Mechanism Strong authentication (use of X. 509) Geneva, 9(pm)-10 February 2009 International Telecommunication 16 Union
 Use of Password is widely used for identity authentication If transmitted over encrypted connection (e. g. SSL) and stored encrypted in the directory, it gives a reasonable protection in many situations Work on Password management and policy is in progress within X. 500 to be also ported to LDAP Geneva, 9(pm)-10 February 2009 International Telecommunication 17 Union
Use of Password is widely used for identity authentication If transmitted over encrypted connection (e. g. SSL) and stored encrypted in the directory, it gives a reasonable protection in many situations Work on Password management and policy is in progress within X. 500 to be also ported to LDAP Geneva, 9(pm)-10 February 2009 International Telecommunication 17 Union
 Strong authentication Based on electronic signatures Requires the presence of a Public Key Infrastructure (PKI) ITU-T X. 509 is here the key specification Geneva, 9(pm)-10 February 2009 International Telecommunication 18 Union
Strong authentication Based on electronic signatures Requires the presence of a Public Key Infrastructure (PKI) ITU-T X. 509 is here the key specification Geneva, 9(pm)-10 February 2009 International Telecommunication 18 Union
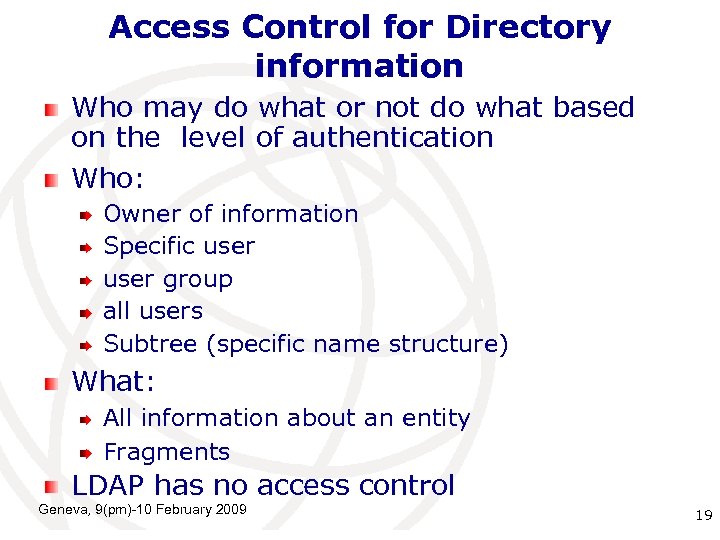 Access Control for Directory information Who may do what or not do what based on the level of authentication Who: Owner of information Specific user group all users Subtree (specific name structure) What: All information about an entity Fragments LDAP has no access control Geneva, 9(pm)-10 February 2009 International Telecommunication 19 Union
Access Control for Directory information Who may do what or not do what based on the level of authentication Who: Owner of information Specific user group all users Subtree (specific name structure) What: All information about an entity Fragments LDAP has no access control Geneva, 9(pm)-10 February 2009 International Telecommunication 19 Union
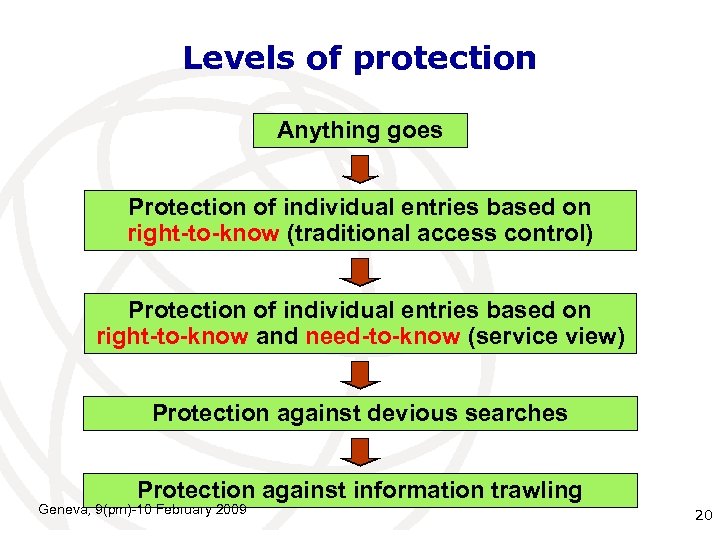 Levels of protection Anything goes Protection of individual entries based on right-to-know (traditional access control) Protection of individual entries based on right-to-know and need-to-know (service view) Protection against devious searches Protection against information trawling Geneva, 9(pm)-10 February 2009 International Telecommunication 20 Union
Levels of protection Anything goes Protection of individual entries based on right-to-know (traditional access control) Protection of individual entries based on right-to-know and need-to-know (service view) Protection against devious searches Protection against information trawling Geneva, 9(pm)-10 February 2009 International Telecommunication 20 Union
 Protection by X. 509 Geneva, 9(pm)-10 February 2009 International Telecommunication 21 Union
Protection by X. 509 Geneva, 9(pm)-10 February 2009 International Telecommunication 21 Union
 Basic X. 509 Concepts Public-key concept Public-Key Infrastructure (PKI) Privilege Management Infrastructure (PMI) Certificates Public-key certificates (part of PKI) Attribute certificates (part of PMI) Digital Signatures Geneva, 9(pm)-10 February 2009 International Telecommunication 22 Union
Basic X. 509 Concepts Public-key concept Public-Key Infrastructure (PKI) Privilege Management Infrastructure (PMI) Certificates Public-key certificates (part of PKI) Attribute certificates (part of PMI) Digital Signatures Geneva, 9(pm)-10 February 2009 International Telecommunication 22 Union
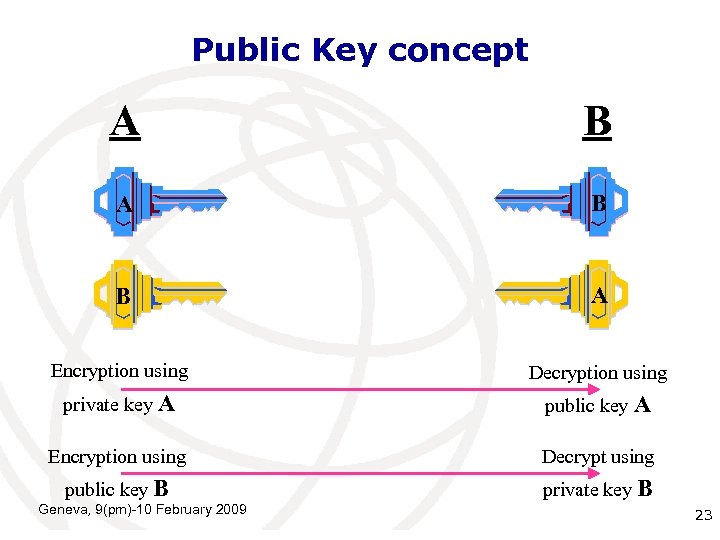 Public Key concept A B B A Encryption using Decryption using private key A public key A Encryption using Decrypt using public key B private key B International Geneva, 9(pm)-10 February 2009 Telecommunication 23 Union
Public Key concept A B B A Encryption using Decryption using private key A public key A Encryption using Decrypt using public key B private key B International Geneva, 9(pm)-10 February 2009 Telecommunication 23 Union
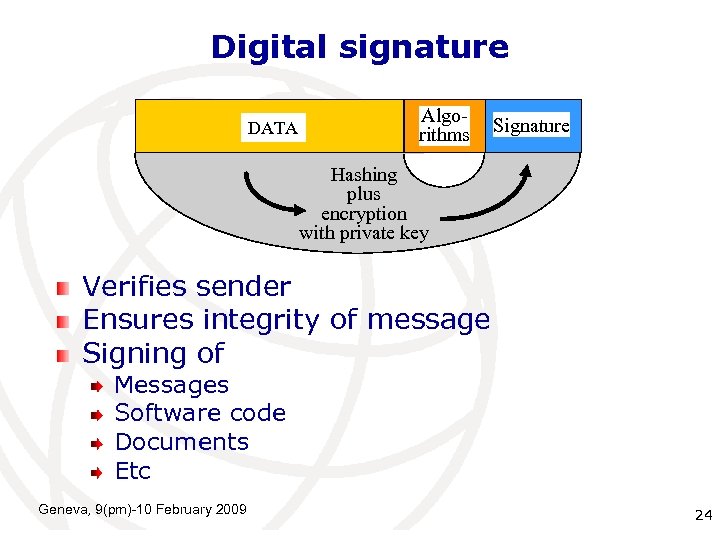 Digital signature DATA Algorithms Signature Hashing plus encryption with private key Verifies sender Ensures integrity of message Signing of Messages Software code Documents Etc Geneva, 9(pm)-10 February 2009 International Telecommunication 24 Union
Digital signature DATA Algorithms Signature Hashing plus encryption with private key Verifies sender Ensures integrity of message Signing of Messages Software code Documents Etc Geneva, 9(pm)-10 February 2009 International Telecommunication 24 Union
 Certifying the identity using public-key certificates Certification Authority Geneva, 9(pm)-10 February 2009 International Telecommunication 25 Union
Certifying the identity using public-key certificates Certification Authority Geneva, 9(pm)-10 February 2009 International Telecommunication 25 Union
 Checking the credentials A passport is a type of certificate binding a picture to an ID Has to be issued by a trustworthy authority A passport may be false It is checked by the “service provider”, also called the relying party A certificate is issued by a Certification Authority (CA) Geneva, 9(pm)-10 February 2009 International Telecommunication 26 Union
Checking the credentials A passport is a type of certificate binding a picture to an ID Has to be issued by a trustworthy authority A passport may be false It is checked by the “service provider”, also called the relying party A certificate is issued by a Certification Authority (CA) Geneva, 9(pm)-10 February 2009 International Telecommunication 26 Union
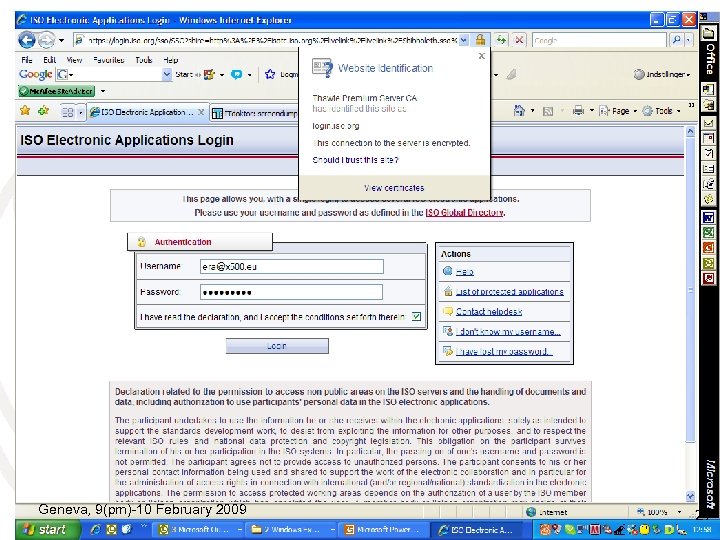 X. 509 at work - 1 Geneva, 9(pm)-10 February 2009 International Telecommunication 27 Union
X. 509 at work - 1 Geneva, 9(pm)-10 February 2009 International Telecommunication 27 Union
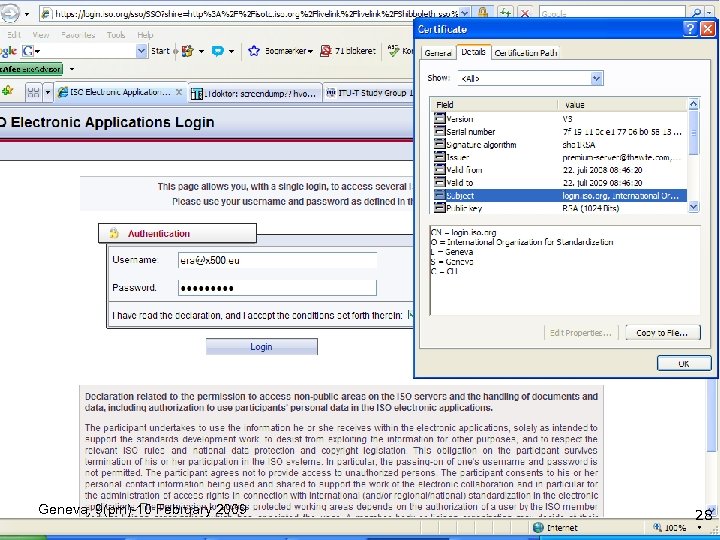 X. 509 at work - 2 Geneva, 9(pm)-10 February 2009 International Telecommunication 28 Union
X. 509 at work - 2 Geneva, 9(pm)-10 February 2009 International Telecommunication 28 Union
 Establishing the infrastructure To validate a certificate a Public-Key Infrastructure (PKI) is required: To establish a trust anchor To establish a repository for revoked certificates The X. 509 provides a framework for PKI Supplementary specifications required Geneva, 9(pm)-10 February 2009 International Telecommunication 29 Union
Establishing the infrastructure To validate a certificate a Public-Key Infrastructure (PKI) is required: To establish a trust anchor To establish a repository for revoked certificates The X. 509 provides a framework for PKI Supplementary specifications required Geneva, 9(pm)-10 February 2009 International Telecommunication 29 Union
 PKI forums and peer groups Electronic Signatures and Infrastructures (ESI) by ETSI Certification Authority/Browser Forum Public-Key Infrastructure (X. 509) (PKIX) within IETF Geneva, 9(pm)-10 February 2009 International Telecommunication 30 Union
PKI forums and peer groups Electronic Signatures and Infrastructures (ESI) by ETSI Certification Authority/Browser Forum Public-Key Infrastructure (X. 509) (PKIX) within IETF Geneva, 9(pm)-10 February 2009 International Telecommunication 30 Union
 Privilege Management Attribute certificates are used for assigning privileges to the holder of the certificate The holder is identified, e. g. , by a pointer to a public-key certificate An attribute certificate is issued by an Attribute Authority (AA) A special Privilege Management Infrastructure (PMI) may be established Recent work allows privileges established in one domain to be applied in other domains Geneva, 9(pm)-10 February 2009 International Telecommunication 31 Union
Privilege Management Attribute certificates are used for assigning privileges to the holder of the certificate The holder is identified, e. g. , by a pointer to a public-key certificate An attribute certificate is issued by an Attribute Authority (AA) A special Privilege Management Infrastructure (PMI) may be established Recent work allows privileges established in one domain to be applied in other domains Geneva, 9(pm)-10 February 2009 International Telecommunication 31 Union
 The challenges Extending X. 500 support to meet new identity management requirements Make the community aware of the X. 500 capabilities Get new blood into the process At times up against the NIH syndrome NIH – Not Invented Here Geneva, 9(pm)-10 February 2009 International Telecommunication 32 Union
The challenges Extending X. 500 support to meet new identity management requirements Make the community aware of the X. 500 capabilities Get new blood into the process At times up against the NIH syndrome NIH – Not Invented Here Geneva, 9(pm)-10 February 2009 International Telecommunication 32 Union
 Where to go The central source for information on the X. 500 Directory Standard. www. x 500 standard. com Identity Management Geneva, 9(pm)-10 February 2009 X. 500 International Telecommunication 33 Union
Where to go The central source for information on the X. 500 Directory Standard. www. x 500 standard. com Identity Management Geneva, 9(pm)-10 February 2009 X. 500 International Telecommunication 33 Union


