f1d7198124533357c4b345c836b5bcd9.ppt
- Количество слайдов: 31
IT Asset Management Norman Pugh-Newby Deloitte
IT Asset Management — Definition & Objectives IT Asset Management (ITAM) • The integrated management of an organization’s IT asset inventory, policies, processes, tools, and resources in order to support life cycle management of Information Technology assets Objectives: • Establish and maintain physical accountability of IT assets • Allocate assets as efficiently and productively as possible • Provide accurate configuration status of assets in accordance with defined standards • Maintain full compliance with software licensing agreements • Establish a centralized and complete asset information repository to support day-to-day IT operations and maintenance functions, plus IT asset life cycle management ITAM provides visibility of IT assets and how they relate to mission needs.
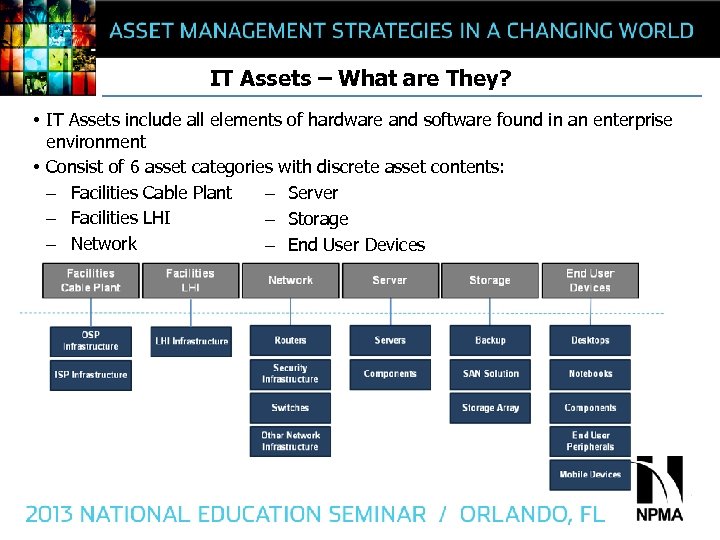
IT Assets – What are They? • IT Assets include all elements of hardware and software found in an enterprise environment • Consist of 6 asset categories with discrete asset contents: – Facilities Cable Plant – Server – Facilities LHI – Storage – Network – End User Devices
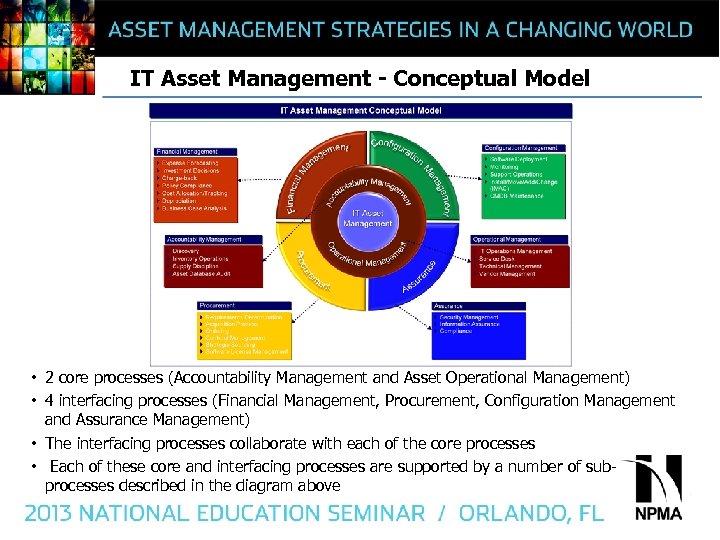
IT Asset Management - Conceptual Model • 2 core processes (Accountability Management and Asset Operational Management) • 4 interfacing processes (Financial Management, Procurement, Configuration Management and Assurance Management) • The interfacing processes collaborate with each of the core processes • Each of these core and interfacing processes are supported by a number of subprocesses described in the diagram above
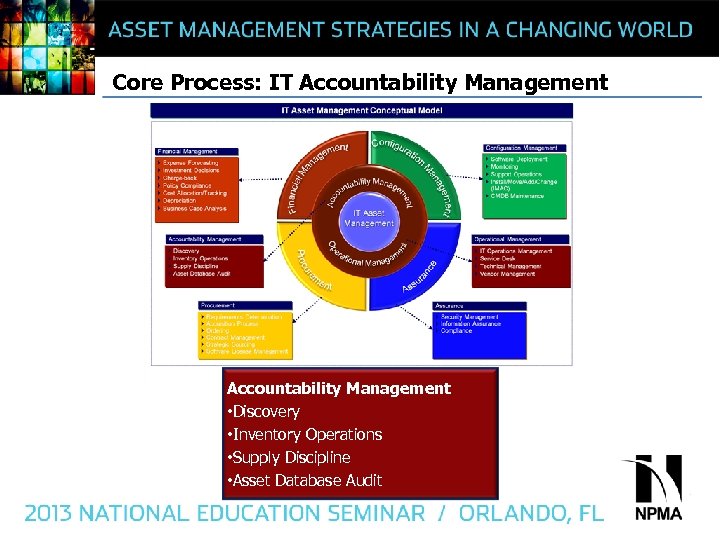
Core Process: IT Accountability Management • Discovery • Inventory Operations • Supply Discipline • Asset Database Audit
IT Asset Accountability Management • IT Asset accountability management is the process of establishing and maintaining accurate accountability records of the IT assets under your control – Managing IT asset costs requires tracking IT assets across the entire asset lifecycle until they are no longer of capital or regulatory value. • Effective asset accountability management requires the support of automated tools – 3 distinct types of automated tools are typically used to support an effective asset accountability program: 1. Auto-discovery 2. Repository 3. Usage
IT Asset Discovery is the process of identifying all the IT assets that are in the network • Assets are typically comprised of servers, network equipment, storage devices, computers, printers, monitors, external peripherals, cable, and leasehold improvements • The discovery of IT assets can be automated via the use of auto discovery tools which generally work in two distinct methods: – Agentless Tools: Agentless tools discover network devices automatically by scanning an Internet Protocol (IP) address range – Agent-based Tools: Agent-based tools require the installation of an agent on the networked device • One pitfall of auto discovery tools is that they are often encumbered by firewalls or governing security policies
Inventory Operations • Inventory is the periodic and systematic counting and verification of the total assets on hand. Some key business management benefits of the inventory function include: – Maximizing use of existing assets resulting in a lower overall inventory cost – Minimizing operating support costs – Maintaining compliancy with regulatory guidance • The inventory is housed in a repository tool which consolidates the physical IUID, serial number, model number, financial (e. g. , purchase price, depreciation and book value) and contract (e. g. , terms and conditions, warranties, service levels and entitlements) information associated with enterprise IT assets • Inventory repositories facilitate a full-service approach to IT asset life cycle planning, including implementation, management processes, retirement, and disposal • Discovery tools feed information into the repository tool • Repository tool typically integrated with Software Usage Tool (SUT) which maintains an inventory of software usage
Supply Discipline / Asset Database Audit Supply Discipline is a process by which IT asset managers hand receipt property down to the lowest level user to establish responsibility and then manually inventory the assets periodically to confirm and sustain accountability. Key roles and responsibilities should include the following: • Asset Managers – Asset Managers have responsibility for ensuring that all personal property is properly maintained, safeguarded, accounted for and accurately reported • Accountable Property Officers – Individuals who, based on their training, knowledge, and experience in property management, accountability and control procedures, are appointed by proper authority to establish and maintain an organization’s accountable property records, systems, and/or financial records • Property Custodians – Individuals who are appointed by the Accountable Property Officer who accepts custodial responsibility for property, typically by signing a hand receipt Asset Database Audit Process • On a regular basis, an audit of the assets in the repository tool data base should be conducted via reconciliation with the Accountable Property Officer records
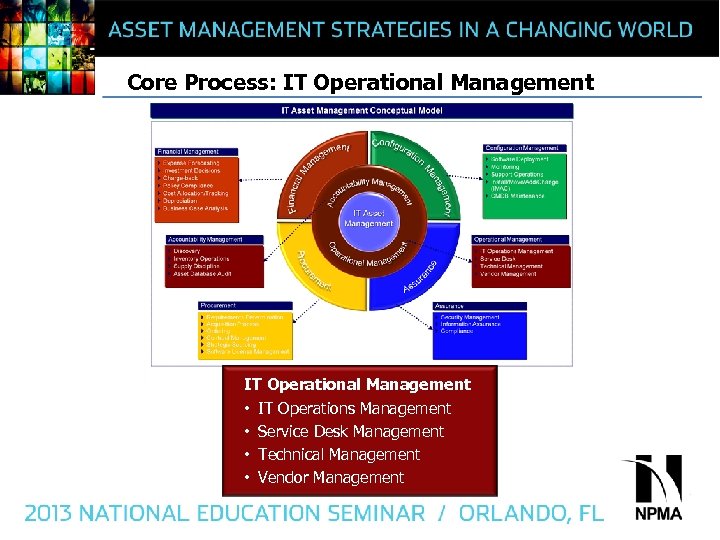
Core Process: IT Operational Management • IT Operations Management • Service Desk Management • Technical Management • Vendor Management
Asset Operational Management • The purpose of Asset Operations Management is to coordinate and carry out the day to day activities associated with IT Asset Management • High level activities include functional management of the following elements involved in making the system in its entirety work together: – People – Processes and procedures – Technology – Data elements
IT Operations Mgt. / Service Desk Management • IT Operations Management is responsible for the execution of operational processes that are necessary to manage the IT asset lifecycle. • The processes below are responsible for monitoring business requirements and coordinating the appropriate resources to meet organizational needs: – Software License Management – Change Management – Problem Management – Capacity Management – Availability Management • Service Desk management is the primary point of contact for users when there is a disruption in the operation of an IT asset • The Service Desk also serves as a point of coordination between different IT groups in an organization when the need arises
Technical Management / Vendor Management • Technical Management – Responsible for making sure IT assets ate placed into service with the most resilient and cost effective technology available – Diagnose and resolve complex technical issues beyond the capability of the service desk – Serve as guardian of technical knowledge for design, testing, operation and optimization of IT assets • Vendor Management – Responsible for making sure that appropriate access is available to contract support for all IT assets to include replacement equipment for assets reaching end of life – Responsible for ensuring that contractual performance requirements are met
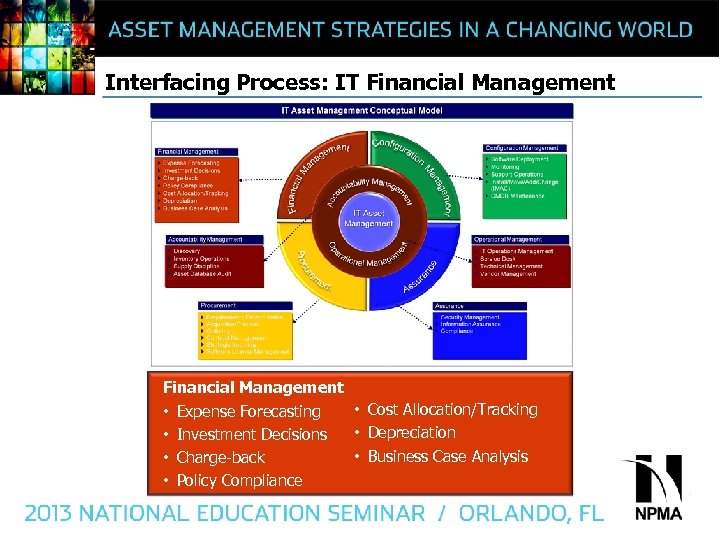
Interfacing Process: IT Financial Management • Cost Allocation/Tracking • Expense Forecasting • Depreciation • Investment Decisions • Business Case Analysis • Charge-back • Policy Compliance
Financial Management • The process used to plan and manage cost allocations across departments for asset procurement, maintenance, and related services • It enables control and accountability for spending at the organizational and departmental levels, based on actual need • Aids in reducing waste and increasing efficiencies in spending and usage associated with assets and services Financial Management includes: • Expense Forecasting – labor and asset resources needed for baseline plan • Investment Decisions – based on framework of costs vs. benefits • Charge-back – charging IT costs back to the using departments • Policy Compliance – e. g. , Do. D FMR Vol 4, Ch 6, Accounting for PP&E • Cost Allocation/Tracking – Supports cost control and governance. • Depreciation – Allocates cost over useful life of assets • Business Case Analysis – Foundational analysis for justifying IT investment $$$
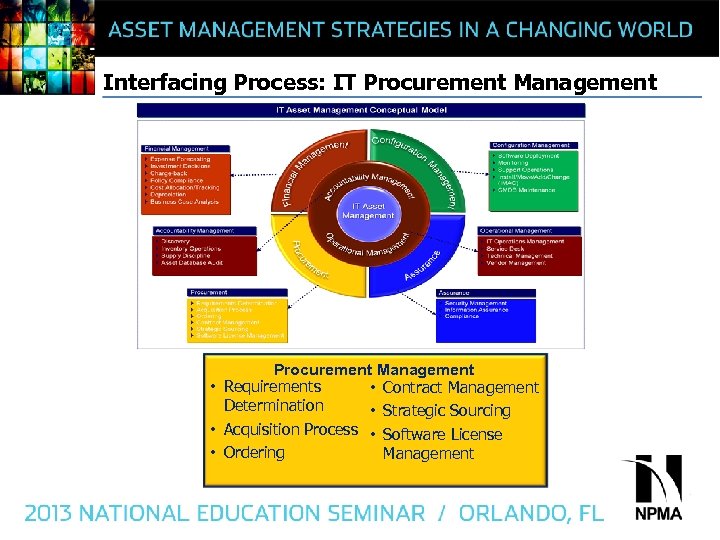
Interfacing Process: IT Procurement Management • Requirements • Contract Management Determination • Strategic Sourcing • Acquisition Process • Software License • Ordering Management
Procurement • The procurement function involves the acquisition of network components and services with the following considerations to benefit the network operators and customers: – – – Best possible total cost of ownership Right quantity and quality Right time Right place Right source • The procurement process typically involves risk in either the cost or benefits and is a good business practice to make use of economic analysis methods such as cost-benefit-analysis or cost-utility analysis • An Information Services Procurement Library is a best practice library for the management of IT related acquisition processes which enables: – – The customer and supplier organization to achieve the desired quality Constructing the request for proposal Constructing the contract and delivery plan Monitoring the delivery phase
Ordering • Procurement personnel should select an ordering management capability that delivers requisition, quotation, vendor, purchase order, and contract information to allow them to proactively plan work and systems deployments • Streamline the ordering, payment, and invoicing process and utilize a common data model so that data can be shared among order and invoice tools and applications • Order and Invoice tools should also provide a process for working and updating Order Modifications • Asset managers should understand this process and be able to use the system to validate that the right number of type of components were ordered
Requirements Determination • Requirements determination is the process of determining the business justification, requirements, specifications and approvals needed to proceed with the procurement process • Requirements determination involves processes such as organizing project teams, using cost-benefit analysis or other analytic techniques to justify alternatives, assessing relative risk and benefits defining specifications, and obtaining necessary approvals to proceed with the procurement process • Key requirements planning issues that need to be addressed include: – How should project teams be configured for different types of acquisitions (appropriate internal and external resources, project leader, etc. )? – What are the important costs versus budget considerations? – What will be your process for separating requirements from wants? – How will you capture performance specifications and other outputs for use in later phases such as quality management?
Acquisition Process • The acquisition process involves evaluating and selecting appropriate suppliers and completing procurement arrangements for the required products and services • The acquisition process includes identifying sourcing alternatives, generating communications (such as RFPs and RFQs) to suppliers, evaluating supplier proposals, and negotiating contracts with suppliers • Key considerations for the acquisition process include: – Which acquisition processes can be automated or minimized? – Which tools can you use to automate and optimize the procurement process (e. g. , Electronic Data Interchange (EDI), Autofax)? – What are the appropriate roles of users, legal, purchasing and information security in the procurement process? – Should any or all of the procurement process be outsourced?
Contract Management • Contract management can be summarized as the process of systematically and efficiently managing contract creation, execution, and analysis for the purpose of maximizing financial and operational performance and minimizing risk • Contract management should ensure that products and services covered under the contract are provided in the required quality and quality, and within the prescribed timeframes • Understanding, predicting and being able to effectively mitigate risk are critical to effective contract management • Help yourself to mitigate risk by creating a historical database with details of critical issues associated with previous contracts such as: – Real costs and duration versus budget and planning schedule – Problems/solutions to include contract decision point challenges – Effectiveness of suppliers and delivery plans – Quality of supplies and services
Strategic Sourcing • Strategic sourcing is an objective-driven procurement process that can systematically improve and evaluate purchasing activities • A strategic sourcing methodology contributes to optimization of the procurement process by taking the following steps: – Analyzing current spends (what is procured and where) – Identifying internal requirements (quality requirements, product specifications, service expectations) – Analyzing the market (market conditions, supply base, emerging products) – Develop/Implement strategy (best suppliers given supply/demand/risk factors, managed negotiations, contract award, track performance metrics)
Software License Management • The effective procurement and management of software licenses is an important special area of procurement management • Software license management requires an understanding of where licenses are consumed, identifying potential savings, and aggregating costs • An important goal of Software License Management is to eliminate software overbuying and illegal use • Failure to harvest licenses for reuse or to ensure license compliancy leads to software overbuy and/or illegal deployment • Reports available in the IT Asset Management repository tool should include software compliance
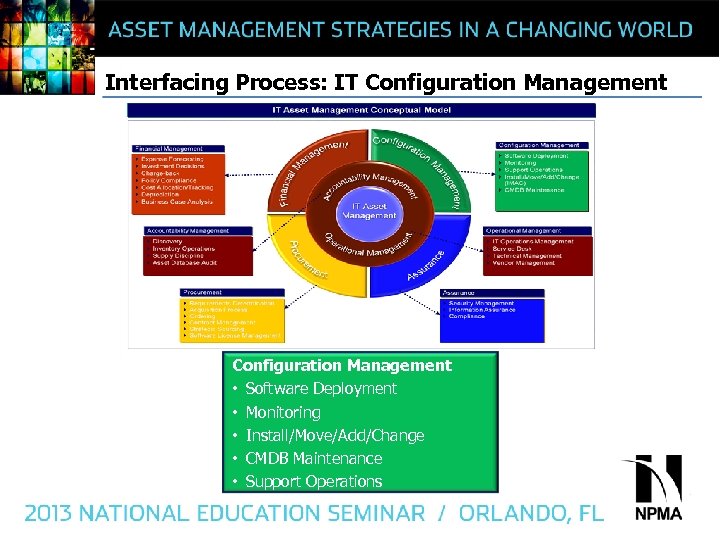
Interfacing Process: IT Configuration Management • Software Deployment • Monitoring • Install/Move/Add/Change • CMDB Maintenance • Support Operations
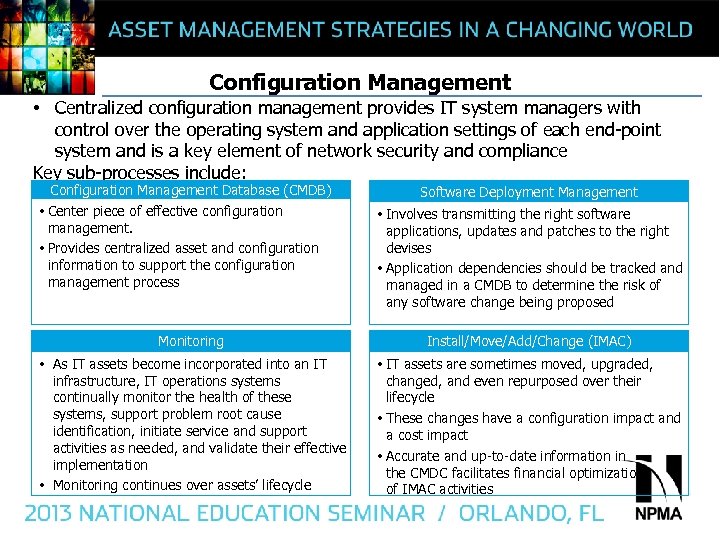
Configuration Management • Centralized configuration management provides IT system managers with control over the operating system and application settings of each end-point system and is a key element of network security and compliance Key sub-processes include: Configuration Management Database (CMDB) • Center piece of effective configuration management. • Provides centralized asset and configuration information to support the configuration management process Software Deployment Management • Involves transmitting the right software applications, updates and patches to the right devises • Application dependencies should be tracked and managed in a CMDB to determine the risk of any software change being proposed Monitoring Install/Move/Add/Change (IMAC) • As IT assets become incorporated into an IT infrastructure, IT operations systems continually monitor the health of these systems, support problem root cause identification, initiate service and support activities as needed, and validate their effective implementation • Monitoring continues over assets’ lifecycle • IT assets are sometimes moved, upgraded, changed, and even repurposed over their lifecycle • These changes have a configuration impact and a cost impact • Accurate and up-to-date information in the CMDC facilitates financial optimization of IMAC activities
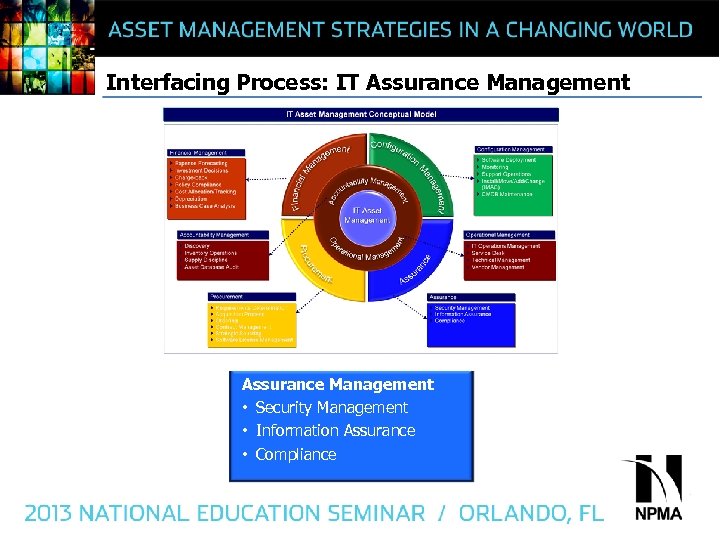
Interfacing Process: IT Assurance Management • Security Management • Information Assurance • Compliance
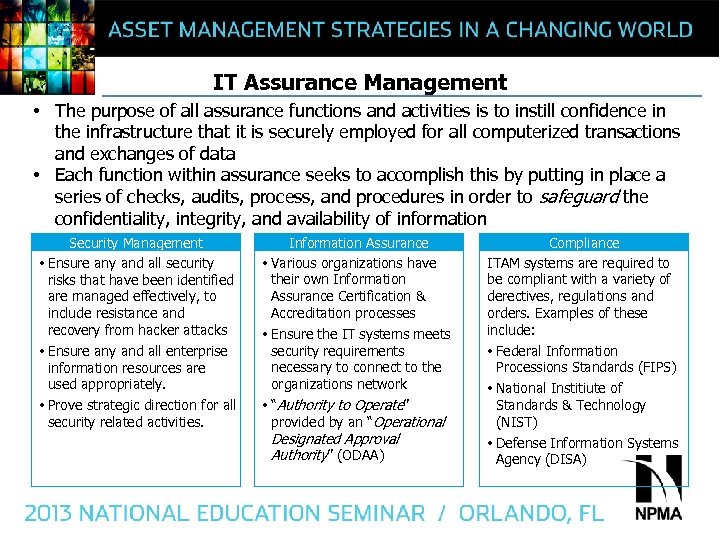
IT Assurance Management • The purpose of all assurance functions and activities is to instill confidence in the infrastructure that it is securely employed for all computerized transactions and exchanges of data • Each function within assurance seeks to accomplish this by putting in place a series of checks, audits, process, and procedures in order to safeguard the confidentiality, integrity, and availability of information Security Management • Ensure any and all security risks that have been identified are managed effectively, to include resistance and recovery from hacker attacks • Ensure any and all enterprise information resources are used appropriately. • Prove strategic direction for all security related activities. Information Assurance • Various organizations have their own Information Assurance Certification & Accreditation processes • Ensure the IT systems meets security requirements necessary to connect to the organizations network • “Authority to Operate” provided by an “Operational Designated Approval Authority” (ODAA) Compliance ITAM systems are required to be compliant with a variety of derectives, regulations and orders. Examples of these include: • Federal Information Processions Standards (FIPS) • National Institiute of Standards & Technology (NIST) • Defense Information Systems Agency (DISA)
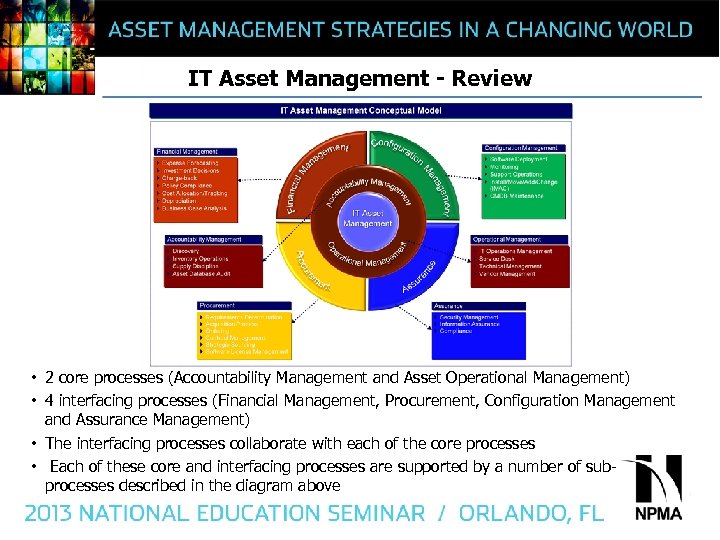
IT Asset Management - Review • 2 core processes (Accountability Management and Asset Operational Management) • 4 interfacing processes (Financial Management, Procurement, Configuration Management and Assurance Management) • The interfacing processes collaborate with each of the core processes • Each of these core and interfacing processes are supported by a number of subprocesses described in the diagram above
How Effective is Your ITAM Program? • ITAM effectiveness normally correlated to ITAM maturity • ITAM maturity measured using Gartner ITAM Maturity Model • Maturity model defines five levels of ITAM maturity – Basic – Reactive – Proactive – Service – Value Creation • Gartner facilitate an understanding of each level by defining the characteristics of each level with regard to people, processes, and technology. • Reaching the Value Creation maturity level requires an iterative approach of continuous improvement over the course of many years • The proper planning and considerations need to be in place to leverage the requisite ITAL tools and strategies
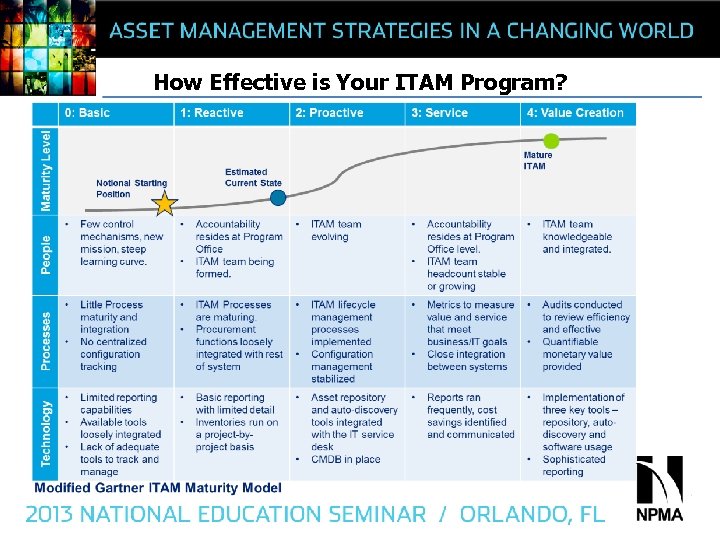
How Effective is Your ITAM Program?
Questions? Please Contact: Norman Pugh-Newby, CPPA, PMP Manager Deloitte (M) 571 -212 -5084 npughnewby@deloitte. com
f1d7198124533357c4b345c836b5bcd9.ppt