ed8a16a17ad61c09d8b00bba28676631.ppt
- Количество слайдов: 51
 ISO Layer and TCP Fundamentals Rich Carlson Internet 2 e. VLBI workshop – TCP Fundamentals September 17, 2006
ISO Layer and TCP Fundamentals Rich Carlson Internet 2 e. VLBI workshop – TCP Fundamentals September 17, 2006
 Outline • A Brief history of networking • The OSI reference model • The TCP/IP architecture • TCP Fundamentals 2
Outline • A Brief history of networking • The OSI reference model • The TCP/IP architecture • TCP Fundamentals 2
 Arpanet • 1962 - ARPA pursues new Interactive Computing paradigm • Focus is on computers as a communications device • Industry focused on computers as arithmetic calculators 3
Arpanet • 1962 - ARPA pursues new Interactive Computing paradigm • Focus is on computers as a communications device • Industry focused on computers as arithmetic calculators 3
 IMPs & TIPs • 1969 – A 4 node network is built using Interface Message Processors (IMPs) • UCLA, SRI, UCSB, Univ of Utah • 1971 – BBN develops a Terminal IPM (TIP) supports up to 64 terminals 4
IMPs & TIPs • 1969 – A 4 node network is built using Interface Message Processors (IMPs) • UCLA, SRI, UCSB, Univ of Utah • 1971 – BBN develops a Terminal IPM (TIP) supports up to 64 terminals 4
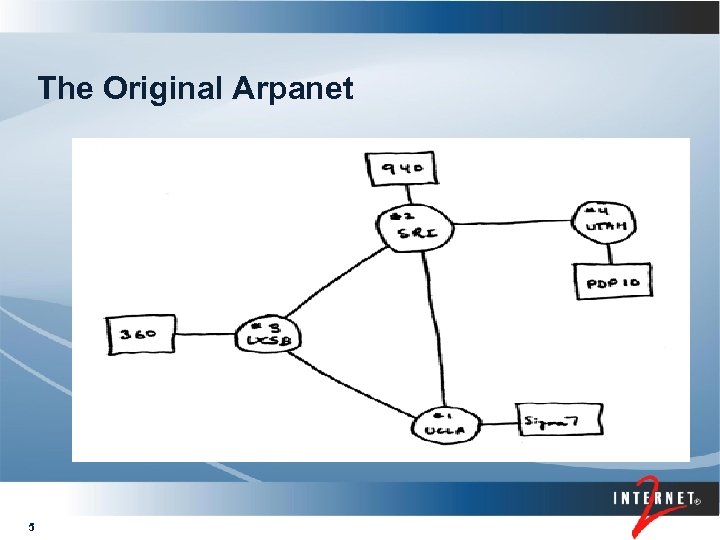 The Original Arpanet 5
The Original Arpanet 5
 Networks Proliferate • 1974 – BBN opens Telenet • 1975 – DEC develops DECnet • 1976 – UUCP (Unix-to-Unix Co. Py) • 1977 – Tymshare opens Tymnet • 1981 – CUNY develops BITnet 6
Networks Proliferate • 1974 – BBN opens Telenet • 1975 – DEC develops DECnet • 1976 – UUCP (Unix-to-Unix Co. Py) • 1977 – Tymshare opens Tymnet • 1981 – CUNY develops BITnet 6
 Federal Agencies get in the Act • ARPA - ARPAnet • DOE – MFENet and HEPNet created • NASA – SPAN created • NSF – CSNet created 7
Federal Agencies get in the Act • ARPA - ARPAnet • DOE – MFENet and HEPNet created • NASA – SPAN created • NSF – CSNet created 7
 ISO OSI networks International Organization for Standardization (ISO) • Open Systems Interconnection (OSI) • 1979 - 7 layer reference model defined • 1982 – ISO begins deliberations on specific protocols for each layer • 1990 – U. S. mandates all gov. purchased computers must be GOSIP compliant • 1995 – GOSIP requirement rescinded 8
ISO OSI networks International Organization for Standardization (ISO) • Open Systems Interconnection (OSI) • 1979 - 7 layer reference model defined • 1982 – ISO begins deliberations on specific protocols for each layer • 1990 – U. S. mandates all gov. purchased computers must be GOSIP compliant • 1995 – GOSIP requirement rescinded 8
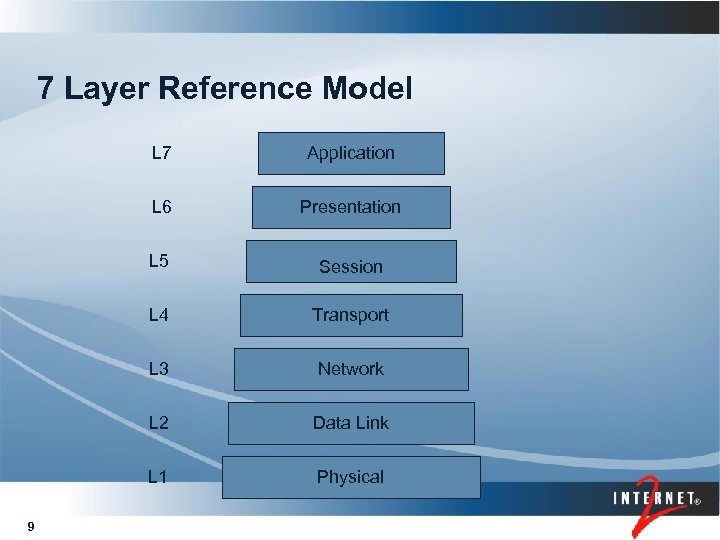 7 Layer Reference Model L 7 L 6 Presentation L 5 Session L 4 Transport L 3 Network L 2 Data Link L 1 9 Application Physical
7 Layer Reference Model L 7 L 6 Presentation L 5 Session L 4 Transport L 3 Network L 2 Data Link L 1 9 Application Physical
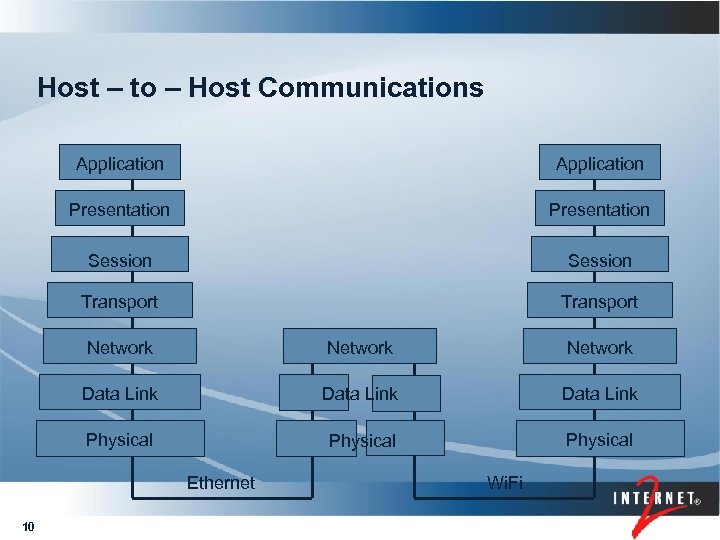 Host – to – Host Communications Application Presentation Session Transport Network Data Link Physical Ethernet 10 Wi. Fi
Host – to – Host Communications Application Presentation Session Transport Network Data Link Physical Ethernet 10 Wi. Fi
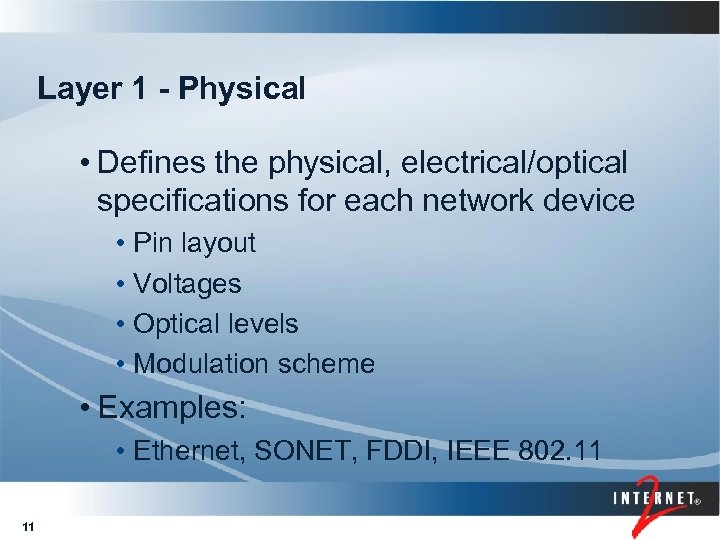 Layer 1 - Physical • Defines the physical, electrical/optical specifications for each network device • Pin layout • Voltages • Optical levels • Modulation scheme • Examples: • Ethernet, SONET, FDDI, IEEE 802. 11 11
Layer 1 - Physical • Defines the physical, electrical/optical specifications for each network device • Pin layout • Voltages • Optical levels • Modulation scheme • Examples: • Ethernet, SONET, FDDI, IEEE 802. 11 11
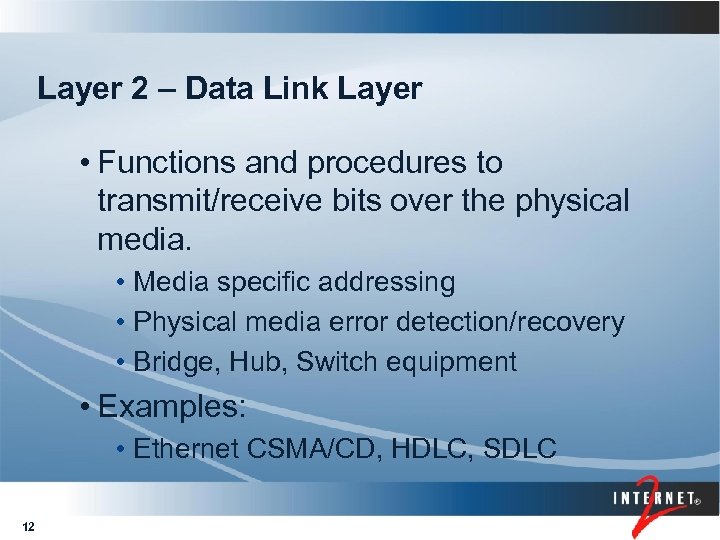 Layer 2 – Data Link Layer • Functions and procedures to transmit/receive bits over the physical media. • Media specific addressing • Physical media error detection/recovery • Bridge, Hub, Switch equipment • Examples: • Ethernet CSMA/CD, HDLC, SDLC 12
Layer 2 – Data Link Layer • Functions and procedures to transmit/receive bits over the physical media. • Media specific addressing • Physical media error detection/recovery • Bridge, Hub, Switch equipment • Examples: • Ethernet CSMA/CD, HDLC, SDLC 12
 Layer 3 – Network Layer • Functions and procedures needed to transmit data throughout a global network • Routing functions • Segmentation / reassembly • Global addressing • Example: • IP addresses 13
Layer 3 – Network Layer • Functions and procedures needed to transmit data throughout a global network • Routing functions • Segmentation / reassembly • Global addressing • Example: • IP addresses 13
 Layer 4 – Transport Layer • Functions to support the transparent transfer of data between end users • Reliability • Error detection and recovery • Flow control • Examples: • TCP, UDP, SCTP 14
Layer 4 – Transport Layer • Functions to support the transparent transfer of data between end users • Reliability • Error detection and recovery • Flow control • Examples: • TCP, UDP, SCTP 14
 Layer 5 – Session Layer • Control sessions between computers • Establish, maintain, terminate connections • Duplex operation (full or half) • Checkpointing and restart procedures 15
Layer 5 – Session Layer • Control sessions between computers • Establish, maintain, terminate connections • Duplex operation (full or half) • Checkpointing and restart procedures 15
 Layer 6 – Presentation Layer • Transforms data to/from a common format • Encoding • Compression • Encryption • Examples: • MIME, XML 16
Layer 6 – Presentation Layer • Transforms data to/from a common format • Encoding • Compression • Encryption • Examples: • MIME, XML 16
 Layer 7 – Application Layer • Program used to interact with computer and data • Specific application for each task • GUI or command line interface • Examples: • SSH, SCP, HTTP, email 17
Layer 7 – Application Layer • Program used to interact with computer and data • Specific application for each task • GUI or command line interface • Examples: • SSH, SCP, HTTP, email 17
 OSI Quick Summary • OSI reference model defines modular ‘stack’ that allows multi-vendor interoperations. • Input/output details specified • Internal details left up to individual vendors • Usually implemented by a series of function calls 18
OSI Quick Summary • OSI reference model defines modular ‘stack’ that allows multi-vendor interoperations. • Input/output details specified • Internal details left up to individual vendors • Usually implemented by a series of function calls 18
 TCP/P Internet • Direct descendant of ARPAnet • Provides Global packet switched network services • ‘Standard’ protocol shipped by most vendors • Still under active development • IPv 6 • TCP modifications 19
TCP/P Internet • Direct descendant of ARPAnet • Provides Global packet switched network services • ‘Standard’ protocol shipped by most vendors • Still under active development • IPv 6 • TCP modifications 19
 NCP to TCP transition • NCP (Network Control Protocol) a host-to -host protocol for the Arpanet • Handled multiple functions • Separate network and transmission functions into 2 distinct protocols • IP handles addressing and routing functions • TCP handles reliability functions • 1 year transition period • Flag day specified as 1 -Jan-1983 20
NCP to TCP transition • NCP (Network Control Protocol) a host-to -host protocol for the Arpanet • Handled multiple functions • Separate network and transmission functions into 2 distinct protocols • IP handles addressing and routing functions • TCP handles reliability functions • 1 year transition period • Flag day specified as 1 -Jan-1983 20
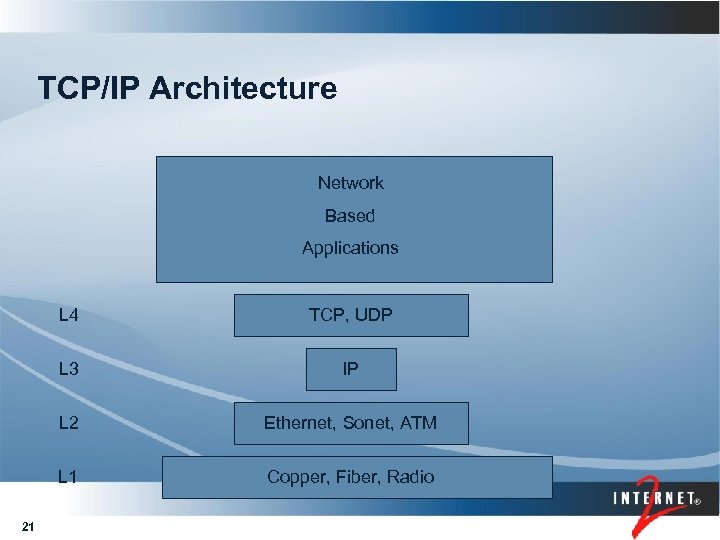 TCP/IP Architecture Network Based Applications L 4 L 3 IP L 2 Ethernet, Sonet, ATM L 1 21 TCP, UDP Copper, Fiber, Radio
TCP/IP Architecture Network Based Applications L 4 L 3 IP L 2 Ethernet, Sonet, ATM L 1 21 TCP, UDP Copper, Fiber, Radio
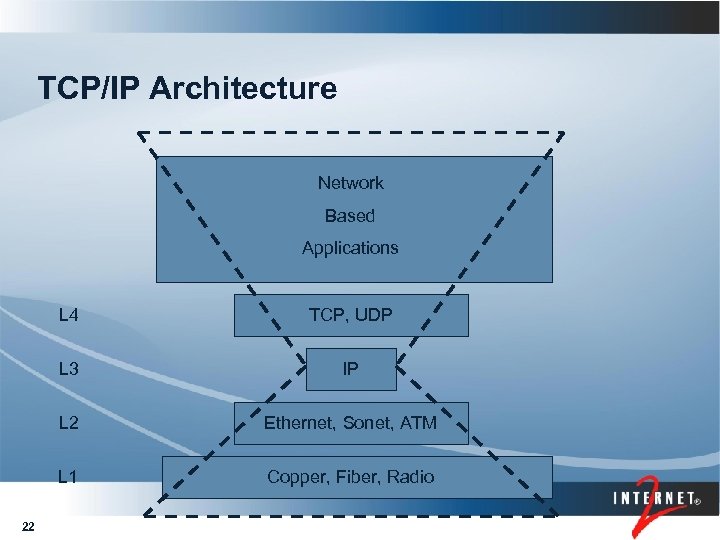 TCP/IP Architecture Network Based Applications L 4 L 3 IP L 2 Ethernet, Sonet, ATM L 1 22 TCP, UDP Copper, Fiber, Radio
TCP/IP Architecture Network Based Applications L 4 L 3 IP L 2 Ethernet, Sonet, ATM L 1 22 TCP, UDP Copper, Fiber, Radio
 TCP/IP Quick Summary • Grew out of ARPA funded research program • Free wide spread deployment in BSD 4. 2 OS • TCP/IP protocols form the Internet 23
TCP/IP Quick Summary • Grew out of ARPA funded research program • Free wide spread deployment in BSD 4. 2 OS • TCP/IP protocols form the Internet 23
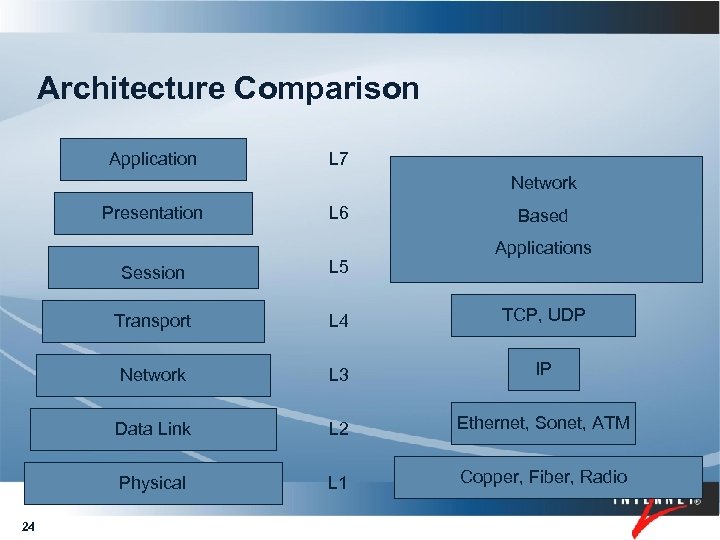 Architecture Comparison Application L 7 Network Presentation L 6 Based Applications Session Transport L 4 TCP, UDP Network L 3 IP Data Link L 2 Ethernet, Sonet, ATM Physical 24 L 5 L 1 Copper, Fiber, Radio
Architecture Comparison Application L 7 Network Presentation L 6 Based Applications Session Transport L 4 TCP, UDP Network L 3 IP Data Link L 2 Ethernet, Sonet, ATM Physical 24 L 5 L 1 Copper, Fiber, Radio
 IP Protocol • IP is a connectionless datagram delivery service • Unreliable Delivery • • No concept of order No concept of loss No concept of late TTL field to ‘Kill Off’ packets • Each packet treated separately • Operates over numerous data-link and physical networks 25
IP Protocol • IP is a connectionless datagram delivery service • Unreliable Delivery • • No concept of order No concept of loss No concept of late TTL field to ‘Kill Off’ packets • Each packet treated separately • Operates over numerous data-link and physical networks 25
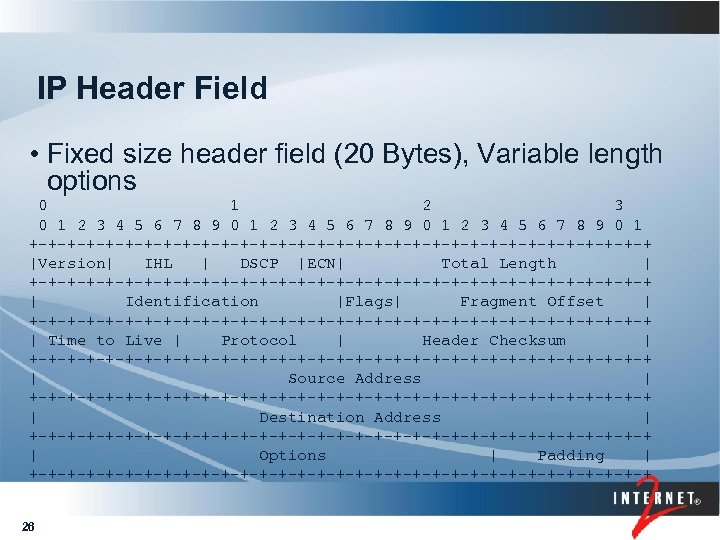 IP Header Field • Fixed size header field (20 Bytes), Variable length options 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ |Version| IHL | DSCP |ECN| Total Length | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Identification |Flags| Fragment Offset | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Time to Live | Protocol | Header Checksum | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Source Address | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Destination Address | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Options | Padding | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ 26
IP Header Field • Fixed size header field (20 Bytes), Variable length options 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ |Version| IHL | DSCP |ECN| Total Length | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Identification |Flags| Fragment Offset | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Time to Live | Protocol | Header Checksum | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Source Address | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Destination Address | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Options | Padding | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ 26
 IP Address • 32 bit unsigned number • Network portion • Host portion used for global routing used to identify specific host • Usually expressed in “dot quad” format • 192. 168. 1. 1 • 192. 168. 1. 0/24 27 specifics specific host specifies subnet of hosts
IP Address • 32 bit unsigned number • Network portion • Host portion used for global routing used to identify specific host • Usually expressed in “dot quad” format • 192. 168. 1. 1 • 192. 168. 1. 0/24 27 specifics specific host specifies subnet of hosts
 CIDR Rules • IP address is ANDed with bit mask to extract network portion • Classless Inter-domain Routing (CIDR) • Specifies length of bit mask • Example 192. 168. 2. 10/23 • C 0 A 8020 A + FFFFFE 00 = C 0 A 80100 • Range is 192. 168. 1. 0 – 192. 168. 2. 255 • First and last addresses in subnet are reserved 28
CIDR Rules • IP address is ANDed with bit mask to extract network portion • Classless Inter-domain Routing (CIDR) • Specifies length of bit mask • Example 192. 168. 2. 10/23 • C 0 A 8020 A + FFFFFE 00 = C 0 A 80100 • Range is 192. 168. 1. 0 – 192. 168. 2. 255 • First and last addresses in subnet are reserved 28
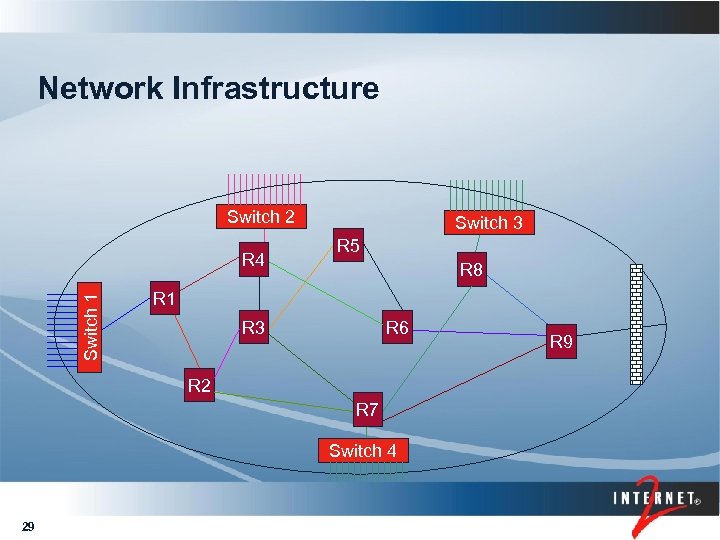 Network Infrastructure Switch 2 Switch 1 R 4 Switch 3 R 5 R 8 R 1 R 3 R 6 R 2 R 7 Switch 4 29 R 9
Network Infrastructure Switch 2 Switch 1 R 4 Switch 3 R 5 R 8 R 1 R 3 R 6 R 2 R 7 Switch 4 29 R 9
 IP Fragmentation • Routers may break packets into smaller chunks (fragmentation) • Destination host is responsible for reassembling all fragments into original packet • Performance impact on modern (ASIC based) routers 30
IP Fragmentation • Routers may break packets into smaller chunks (fragmentation) • Destination host is responsible for reassembling all fragments into original packet • Performance impact on modern (ASIC based) routers 30
 IP Don’t Fragment • Flag in header to indicate that packet should be discarded instead of fragmented • Basis for Path MTU Discovery protocol • Find the largest packet that can transit the entire end-to-end path • Router may return an ICMP error message when it discards the packet • PMTU black holes can occur 31
IP Don’t Fragment • Flag in header to indicate that packet should be discarded instead of fragmented • Basis for Path MTU Discovery protocol • Find the largest packet that can transit the entire end-to-end path • Router may return an ICMP error message when it discards the packet • PMTU black holes can occur 31
 TCP Protocol • TCP provides connection orientated delivery service • Reliable Delivery • • In-order guarantee Loss detection and recovery Flow control Error detection • Hides network details from applications 32
TCP Protocol • TCP provides connection orientated delivery service • Reliable Delivery • • In-order guarantee Loss detection and recovery Flow control Error detection • Hides network details from applications 32
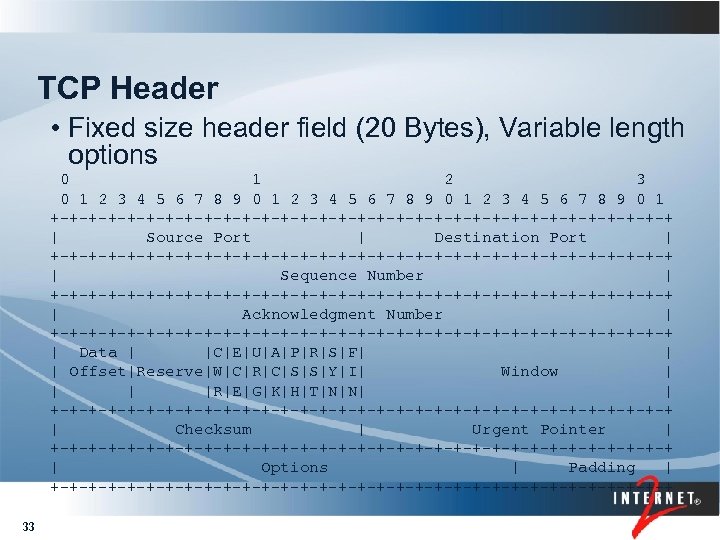 TCP Header • Fixed size header field (20 Bytes), Variable length options 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Source Port | Destination Port | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Sequence Number | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Acknowledgment Number | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Data | |C|E|U|A|P|R|S|F| | | Offset|Reserve|W|C|R|C|S|S|Y|I| Window | |R|E|G|K|H|T|N|N| | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Checksum | Urgent Pointer | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Options | Padding | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ 33
TCP Header • Fixed size header field (20 Bytes), Variable length options 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Source Port | Destination Port | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Sequence Number | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Acknowledgment Number | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Data | |C|E|U|A|P|R|S|F| | | Offset|Reserve|W|C|R|C|S|S|Y|I| Window | |R|E|G|K|H|T|N|N| | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Checksum | Urgent Pointer | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Options | Padding | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ 33
 TCP Connection Setup • Host in “Listen” state does passive open • Host in “Connect” state does active open • Hosts complete a 3 -way handshake to complete open (move to “Established” state • Full Duplex connection established, hosts can transfer data in either direction 34
TCP Connection Setup • Host in “Listen” state does passive open • Host in “Connect” state does active open • Hosts complete a 3 -way handshake to complete open (move to “Established” state • Full Duplex connection established, hosts can transfer data in either direction 34
 TCP Flow Control • Original design relied on TCP Window size to control number of packets entering the network • Real world experience showed that network could experience congestion collapse and new mechanisms were needed • Slow Start after connection is opened • Exponential Growth algorithm • Congestion Avoidance once loss is detected • Linear Growth algorithm 35
TCP Flow Control • Original design relied on TCP Window size to control number of packets entering the network • Real world experience showed that network could experience congestion collapse and new mechanisms were needed • Slow Start after connection is opened • Exponential Growth algorithm • Congestion Avoidance once loss is detected • Linear Growth algorithm 35
 TCP Reno • Most common version of TCP today • Loss based detection to switch from Slow Start to Congestion Avoidance flow control • Transmit and Receive windows to guarantee reliability 36
TCP Reno • Most common version of TCP today • Loss based detection to switch from Slow Start to Congestion Avoidance flow control • Transmit and Receive windows to guarantee reliability 36
![TCP and RTT / Loss Speed = [C * Pkt Size]/[RTT * Sqrt(loss)] Distance TCP and RTT / Loss Speed = [C * Pkt Size]/[RTT * Sqrt(loss)] Distance](https://present5.com/presentation/ed8a16a17ad61c09d8b00bba28676631/image-37.jpg) TCP and RTT / Loss Speed = [C * Pkt Size]/[RTT * Sqrt(loss)] Distance RTT Loss Speed (msec) LAN Metro Transcontinental Global 1 8 70 70 500 (Mbps) 1 E-8 1 E-3 1 E-6 Uses standard Ethernet Size TCP segment (1480 bytes) Formula from Mathis et. al. 37 82, 880. 0 10, 360. 0 1, 184. 0 3. 7 16. 6
TCP and RTT / Loss Speed = [C * Pkt Size]/[RTT * Sqrt(loss)] Distance RTT Loss Speed (msec) LAN Metro Transcontinental Global 1 8 70 70 500 (Mbps) 1 E-8 1 E-3 1 E-6 Uses standard Ethernet Size TCP segment (1480 bytes) Formula from Mathis et. al. 37 82, 880. 0 10, 360. 0 1, 184. 0 3. 7 16. 6
![TCP and Jumbo Frames • Speed = [C * Pkt Size]/[RTT * Sqrt(loss)] • TCP and Jumbo Frames • Speed = [C * Pkt Size]/[RTT * Sqrt(loss)] •](https://present5.com/presentation/ed8a16a17ad61c09d8b00bba28676631/image-38.jpg) TCP and Jumbo Frames • Speed = [C * Pkt Size]/[RTT * Sqrt(loss)] • Jumbo Frames are a non-standard Ethernet feature Distance Use 1 E-6 loss rate Formula from Mathis et. al. 38 Pkt Size Speed (msec) Transcontinental RTT (Bytes) (Mbps) 70 70 1500 9000 120. 0 720. 0
TCP and Jumbo Frames • Speed = [C * Pkt Size]/[RTT * Sqrt(loss)] • Jumbo Frames are a non-standard Ethernet feature Distance Use 1 E-6 loss rate Formula from Mathis et. al. 38 Pkt Size Speed (msec) Transcontinental RTT (Bytes) (Mbps) 70 70 1500 9000 120. 0 720. 0
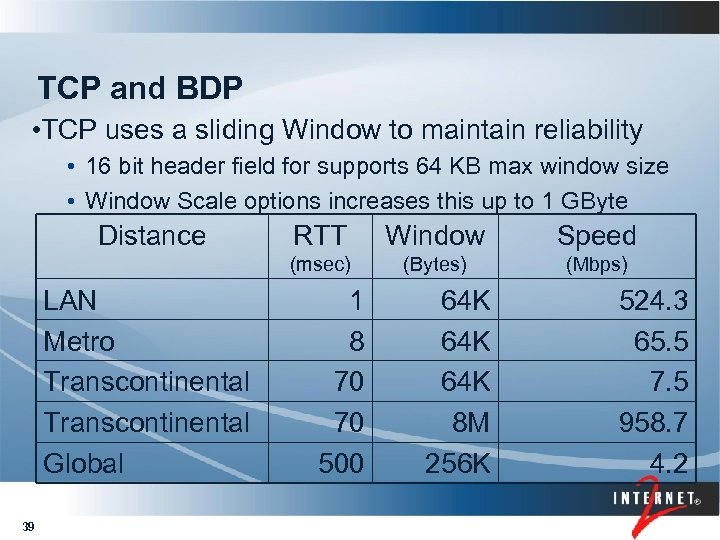 TCP and BDP • TCP uses a sliding Window to maintain reliability • 16 bit header field for supports 64 KB max window size • Window Scale options increases this up to 1 GByte Distance 39 Window Speed (msec) LAN Metro Transcontinental Global RTT (Bytes) (Mbps) 1 8 70 70 500 64 K 64 K 8 M 256 K 524. 3 65. 5 7. 5 958. 7 4. 2
TCP and BDP • TCP uses a sliding Window to maintain reliability • 16 bit header field for supports 64 KB max window size • Window Scale options increases this up to 1 GByte Distance 39 Window Speed (msec) LAN Metro Transcontinental Global RTT (Bytes) (Mbps) 1 8 70 70 500 64 K 64 K 8 M 256 K 524. 3 65. 5 7. 5 958. 7 4. 2
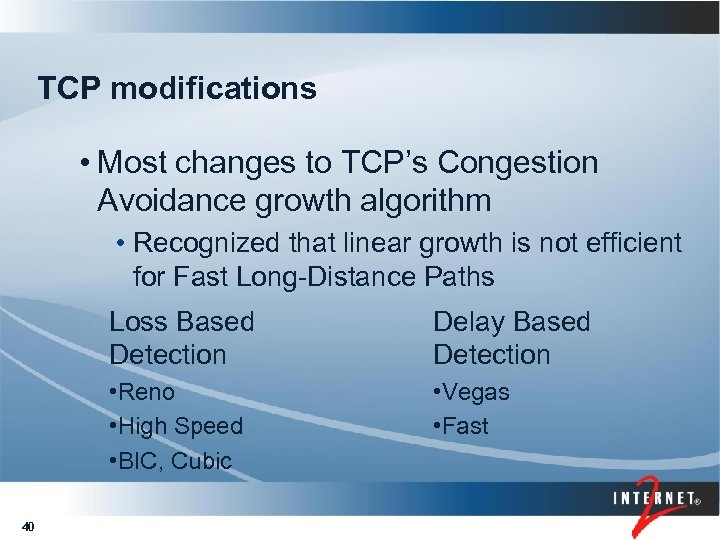 TCP modifications • Most changes to TCP’s Congestion Avoidance growth algorithm • Recognized that linear growth is not efficient for Fast Long-Distance Paths Loss Based Detection • Reno • High Speed • BIC, Cubic 40 Delay Based Detection • Vegas • Fast
TCP modifications • Most changes to TCP’s Congestion Avoidance growth algorithm • Recognized that linear growth is not efficient for Fast Long-Distance Paths Loss Based Detection • Reno • High Speed • BIC, Cubic 40 Delay Based Detection • Vegas • Fast
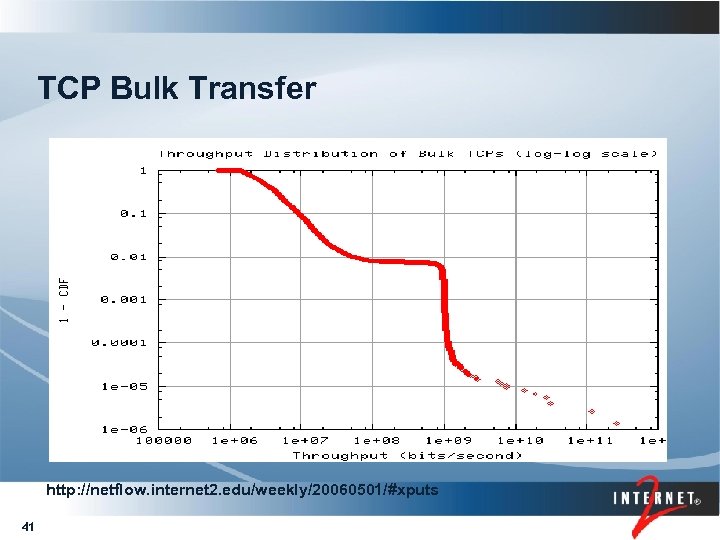 TCP Bulk Transfer http: //netflow. internet 2. edu/weekly/20060501/#xputs 41
TCP Bulk Transfer http: //netflow. internet 2. edu/weekly/20060501/#xputs 41
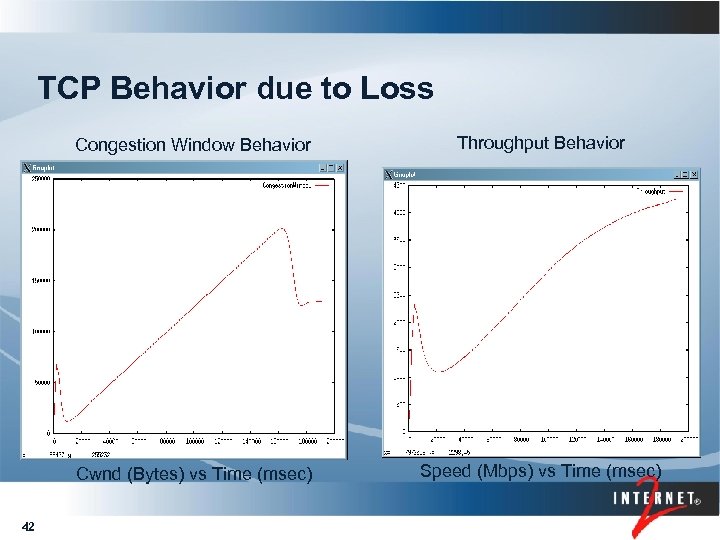 TCP Behavior due to Loss Congestion Window Behavior Cwnd (Bytes) vs Time (msec) 42 Throughput Behavior Speed (Mbps) vs Time (msec)
TCP Behavior due to Loss Congestion Window Behavior Cwnd (Bytes) vs Time (msec) 42 Throughput Behavior Speed (Mbps) vs Time (msec)
 UDP Protocol • UDP – User Datagram Protocol • Application must provide • Reliability • Flow Control • Useful for short messages • DNS • Real Time audio/video 43
UDP Protocol • UDP – User Datagram Protocol • Application must provide • Reliability • Flow Control • Useful for short messages • DNS • Real Time audio/video 43
 Domain Name System • DNS – Domain Name System • Translates Fully Qualified Domain Name (FQDN) into IP address • A Globally distributed database • Hierarchical naming structure • Supports both Authoritative and Caching servers • Requires a minimum of 2 packets and 1 RTT for each resolution 44
Domain Name System • DNS – Domain Name System • Translates Fully Qualified Domain Name (FQDN) into IP address • A Globally distributed database • Hierarchical naming structure • Supports both Authoritative and Caching servers • Requires a minimum of 2 packets and 1 RTT for each resolution 44
 Real-time Transport Protocol • RTP – Real-time Transport Protocol • Carries data with real-time properties • Used for Audio and Video streams • Header contains sequence number and timestamp to provide receiver with pkt info • RTCP – RTP Control Protocol • Carries control information about the stream from receiver back to sender 45
Real-time Transport Protocol • RTP – Real-time Transport Protocol • Carries data with real-time properties • Used for Audio and Video streams • Header contains sequence number and timestamp to provide receiver with pkt info • RTCP – RTP Control Protocol • Carries control information about the stream from receiver back to sender 45
 Unicast vs Multicast • Unicast packets - 1 source & 1 destination • Multicast packets • • IP addresses (224. 0. 0. 0 – 239. 255) Single source, multiple receivers Multiple sources, multiple receivers Routers and Switches must support multicast to prevent unwanted packets from flooding the network • Multiple unicast streams can be used to emulate a multicast session 46
Unicast vs Multicast • Unicast packets - 1 source & 1 destination • Multicast packets • • IP addresses (224. 0. 0. 0 – 239. 255) Single source, multiple receivers Multiple sources, multiple receivers Routers and Switches must support multicast to prevent unwanted packets from flooding the network • Multiple unicast streams can be used to emulate a multicast session 46
 Multicast Traffic • Source starts sending packets using a multicast IP address • Local router/switch uses control messages to advertise traffics availability • Receivers send request-to-join messages • New path from receiver to “merge point” is created and traffic flow begins 47
Multicast Traffic • Source starts sending packets using a multicast IP address • Local router/switch uses control messages to advertise traffics availability • Receivers send request-to-join messages • New path from receiver to “merge point” is created and traffic flow begins 47
 Conclusions • Global packet switching began with the ARPAnet • TCP/IP packet switching is the defacto standard for today’s networks • Smart hosts, dumb infrastructure • New and existing applications support end-to-end communications between people 48
Conclusions • Global packet switching began with the ARPAnet • TCP/IP packet switching is the defacto standard for today’s networks • Smart hosts, dumb infrastructure • New and existing applications support end-to-end communications between people 48
 49
49
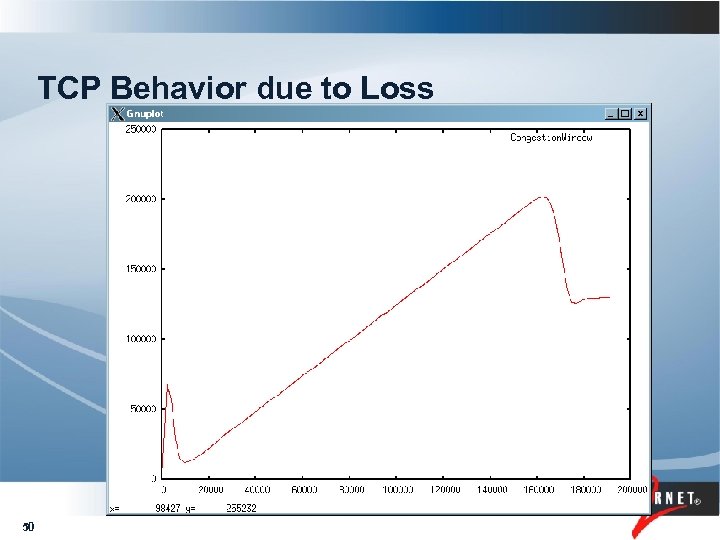 TCP Behavior due to Loss 50
TCP Behavior due to Loss 50
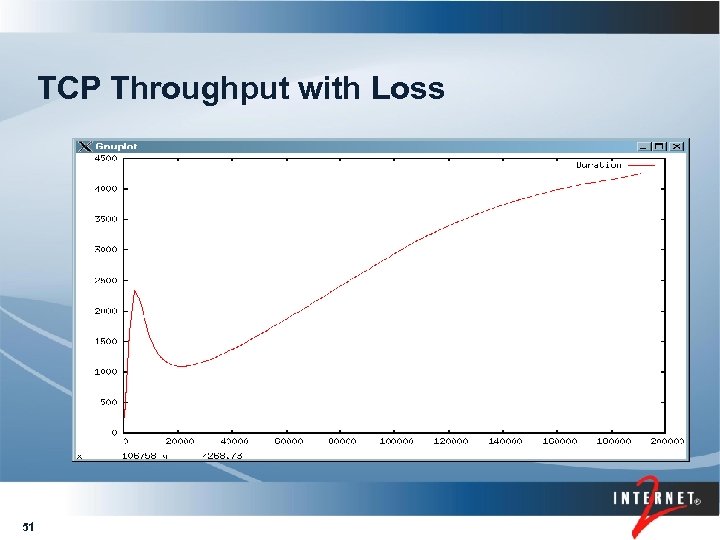 TCP Throughput with Loss 51
TCP Throughput with Loss 51


