7512109dfb36e62f6f581adff0e4d55c.ppt
- Количество слайдов: 55
 IS 2150 / TEL 2810 Introduction to Security Intrusion Detection Auditing, Watermarking Dec 7, 2006 Lecture 10 1
IS 2150 / TEL 2810 Introduction to Security Intrusion Detection Auditing, Watermarking Dec 7, 2006 Lecture 10 1
 Intrusion Detection/Response n Characteristics of systems not under attack: 1. 2. 3. – Actions of users/processes conform to statistically predictable patterns Actions of users/processes do not include sequences of commands to subvert security policy Actions of processes conform to specifications describing allowable actions Denning: Systems under attack fail to meet one or more of these characteristics 2
Intrusion Detection/Response n Characteristics of systems not under attack: 1. 2. 3. – Actions of users/processes conform to statistically predictable patterns Actions of users/processes do not include sequences of commands to subvert security policy Actions of processes conform to specifications describing allowable actions Denning: Systems under attack fail to meet one or more of these characteristics 2
 Intrusion Detection n Idea: Attack can be discovered by one of the above being violated n n Problem: Definitions hard to make precise Automated attack tools n n n Designed to violate security policy Example: rootkits: sniff passwords and stay hidden Practical goals of intrusion detection systems: n n n Detect a wide variety of intrusions (known + unknown) Detect in a timely fashion Present analysis in a useful manner n n Need to monitor many components; proper interfaces needed Be (sufficiently) accurate n Minimize false positives and false negatives 3
Intrusion Detection n Idea: Attack can be discovered by one of the above being violated n n Problem: Definitions hard to make precise Automated attack tools n n n Designed to violate security policy Example: rootkits: sniff passwords and stay hidden Practical goals of intrusion detection systems: n n n Detect a wide variety of intrusions (known + unknown) Detect in a timely fashion Present analysis in a useful manner n n Need to monitor many components; proper interfaces needed Be (sufficiently) accurate n Minimize false positives and false negatives 3
 IDS Types: Anomaly Detection n Compare characteristics of system with expected values n n Threshold metric: when statistics deviate from normal by threshold, sound alarm n n E. g. , Number of failed logins Statistical moments: based on mean/standard deviation of observations n n report when statistics do not match Number of user events in a system Time periods of user activity Resource usages profiles Markov model: based on state, expected likelihood of transition to new states n If a low probability event occurs then it is considered suspicious 4
IDS Types: Anomaly Detection n Compare characteristics of system with expected values n n Threshold metric: when statistics deviate from normal by threshold, sound alarm n n E. g. , Number of failed logins Statistical moments: based on mean/standard deviation of observations n n report when statistics do not match Number of user events in a system Time periods of user activity Resource usages profiles Markov model: based on state, expected likelihood of transition to new states n If a low probability event occurs then it is considered suspicious 4
 Anomaly Detection: How do we determine normal? n Capture average over time n n Correlated events n n But system behavior isn’t always average Events may have dependencies Machine learning approaches n n Training data obtained experimentally Data should relate to as accurate normal operation as possible 5
Anomaly Detection: How do we determine normal? n Capture average over time n n Correlated events n n But system behavior isn’t always average Events may have dependencies Machine learning approaches n n Training data obtained experimentally Data should relate to as accurate normal operation as possible 5
 IDS Types: Misuse Modeling n Does sequence of instructions violate security policy? n n Problem: How do we know all violating sequences? Solution: capture known violating sequences n Generate a rule set for an intrusion signature n n n But won’t the attacker just do something different? Often, no: kiddie scripts, Rootkit, … Alternate solution: State-transition approach n n Known “bad” state transition from attack (e. g. use petri -nets) Capture when transition has occurred (user root) 6
IDS Types: Misuse Modeling n Does sequence of instructions violate security policy? n n Problem: How do we know all violating sequences? Solution: capture known violating sequences n Generate a rule set for an intrusion signature n n n But won’t the attacker just do something different? Often, no: kiddie scripts, Rootkit, … Alternate solution: State-transition approach n n Known “bad” state transition from attack (e. g. use petri -nets) Capture when transition has occurred (user root) 6
 Specification Modeling n Does sequence of instructions violate system specification? n n Need to formally specify operations of potentially critical code n n What is the system specification? trusted code Verify post-conditions met 7
Specification Modeling n Does sequence of instructions violate system specification? n n Need to formally specify operations of potentially critical code n n What is the system specification? trusted code Verify post-conditions met 7
 IDS Systems n Anomaly Detection n Misuse Detection n n Intrusion Detection Expert System (IDES) – successor is NIDES Network Security Monitor. NSM Intrusion Detection In Our Time- IDIOT (colored Petri-nets) USTAT? ASAX (Rule-based) Hybrid n n NADIR (Los Alamos) Haystack (Air force, adaptive) Hyperview (uses neural network) Distributed IDS (Haystack + NSM) 8
IDS Systems n Anomaly Detection n Misuse Detection n n Intrusion Detection Expert System (IDES) – successor is NIDES Network Security Monitor. NSM Intrusion Detection In Our Time- IDIOT (colored Petri-nets) USTAT? ASAX (Rule-based) Hybrid n n NADIR (Los Alamos) Haystack (Air force, adaptive) Hyperview (uses neural network) Distributed IDS (Haystack + NSM) 8
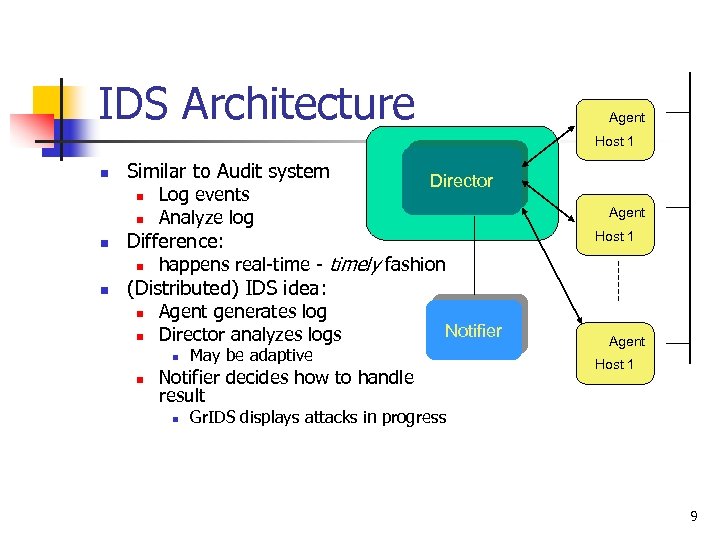 IDS Architecture Agent Host 1 n Similar to Audit system n n n Agent Host 1 Difference: n n Log events Analyze log Director happens real-time - timely fashion (Distributed) IDS idea: n n Agent generates log Director analyzes logs n n May be adaptive Notifier decides how to handle result n Notifier Agent Host 1 Gr. IDS displays attacks in progress 9
IDS Architecture Agent Host 1 n Similar to Audit system n n n Agent Host 1 Difference: n n Log events Analyze log Director happens real-time - timely fashion (Distributed) IDS idea: n n Agent generates log Director analyzes logs n n May be adaptive Notifier decides how to handle result n Notifier Agent Host 1 Gr. IDS displays attacks in progress 9
 Where is the Agent? n Host based IDS n n n watches events on the host Often uses existing audit logs Network-based IDS n n Packet sniffing Firewall logs 10
Where is the Agent? n Host based IDS n n n watches events on the host Often uses existing audit logs Network-based IDS n n Packet sniffing Firewall logs 10
 IDS Problem n IDS useless unless accurate n n n Significant fraction of intrusions detected Significant number of alarms correspond to intrusions Goal is n Reduce false positives n n Reports an attack, but no attack underway Reduce false negatives n An attack occurs but IDS fails to report 11
IDS Problem n IDS useless unless accurate n n n Significant fraction of intrusions detected Significant number of alarms correspond to intrusions Goal is n Reduce false positives n n Reports an attack, but no attack underway Reduce false negatives n An attack occurs but IDS fails to report 11
 Intrusion Response n Incident Prevention n Stop attack before it succeeds Measures to detect attacker Example: Jailing (als 0 Honepots) n n Make attacker think they are succeeding and confine to an area Intrusion handling n n n Preparation for detecting attacks Identification of an attack Contain attack Eradicate attack Recover to secure state Follow-up to the attack - Punish attacker 12
Intrusion Response n Incident Prevention n Stop attack before it succeeds Measures to detect attacker Example: Jailing (als 0 Honepots) n n Make attacker think they are succeeding and confine to an area Intrusion handling n n n Preparation for detecting attacks Identification of an attack Contain attack Eradicate attack Recover to secure state Follow-up to the attack - Punish attacker 12
 Containment n Passive monitoring n n n Track intruder actions Eases recovery and punishment Constraining access n n Downgrade attacker privileges Protect sensitive information Why not just pull the plug? Example: Honepots 13
Containment n Passive monitoring n n n Track intruder actions Eases recovery and punishment Constraining access n n Downgrade attacker privileges Protect sensitive information Why not just pull the plug? Example: Honepots 13
 Eradication n Terminate network connection Terminate processes Block future attacks n n n Close ports Disallow specific IP addresses Wrappers around attacked applications 14
Eradication n Terminate network connection Terminate processes Block future attacks n n n Close ports Disallow specific IP addresses Wrappers around attacked applications 14
 Follow-Up n Legal action n n Cut off resources n n Trace through network Notify ISP of action Counterattack n Is this a good idea? 15
Follow-Up n Legal action n n Cut off resources n n Trace through network Notify ISP of action Counterattack n Is this a good idea? 15
 Auditing 16
Auditing 16
 What is Auditing? n Logging n n Recording events or statistics to provide information about system use and performance Auditing n Analysis of log records to present information about the system in a clear, understandable manner 17
What is Auditing? n Logging n n Recording events or statistics to provide information about system use and performance Auditing n Analysis of log records to present information about the system in a clear, understandable manner 17
 Auditing goals/uses n n User accountability Damage assessment Determine causes of security violations Describe security state for monitoring critical problems n n Determine if system enters unauthorized state Evaluate effectiveness of protection mechanisms n n Determine which mechanisms are appropriate and working Deter attacks because of presence of record 18
Auditing goals/uses n n User accountability Damage assessment Determine causes of security violations Describe security state for monitoring critical problems n n Determine if system enters unauthorized state Evaluate effectiveness of protection mechanisms n n Determine which mechanisms are appropriate and working Deter attacks because of presence of record 18
 Problems n What to log? n n n looking for violations of a policy, so record at least what will show such violations Use of privileges What do you audit? n n Need not audit everything Key: what is the policy involved? 19
Problems n What to log? n n n looking for violations of a policy, so record at least what will show such violations Use of privileges What do you audit? n n Need not audit everything Key: what is the policy involved? 19
 Audit System Structure n Logger n n Analyzer n n Records information, usually controlled by parameters Analyzes logged information looking for something Notifier n Reports results of analysis 20
Audit System Structure n Logger n n Analyzer n n Records information, usually controlled by parameters Analyzes logged information looking for something Notifier n Reports results of analysis 20
 Logger n n Type, quantity of information recorded controlled by system or program configuration parameters May be human readable or not n n If not, usually viewing tools supplied Space available, portability influence storage format 21
Logger n n Type, quantity of information recorded controlled by system or program configuration parameters May be human readable or not n n If not, usually viewing tools supplied Space available, portability influence storage format 21
 Example: RACF n n n Security enhancement package for IBM’s MVS/VM Logs failed access attempts, use of privilege to change security levels, and (if desired) RACF interactions View events with LISTUSERS commands 22
Example: RACF n n n Security enhancement package for IBM’s MVS/VM Logs failed access attempts, use of privilege to change security levels, and (if desired) RACF interactions View events with LISTUSERS commands 22
 Example: Windows NT n Different logs for different types of events n n n System event logs record system crashes, component failures, and other system events Application event logs record events that applications request be recorded Security event log records security-critical events such as logging in and out, system file accesses, and other events Logs are binary; use event viewer to see them If log full, can have system shut down, logging disabled, or logs overwritten 23
Example: Windows NT n Different logs for different types of events n n n System event logs record system crashes, component failures, and other system events Application event logs record events that applications request be recorded Security event log records security-critical events such as logging in and out, system file accesses, and other events Logs are binary; use event viewer to see them If log full, can have system shut down, logging disabled, or logs overwritten 23
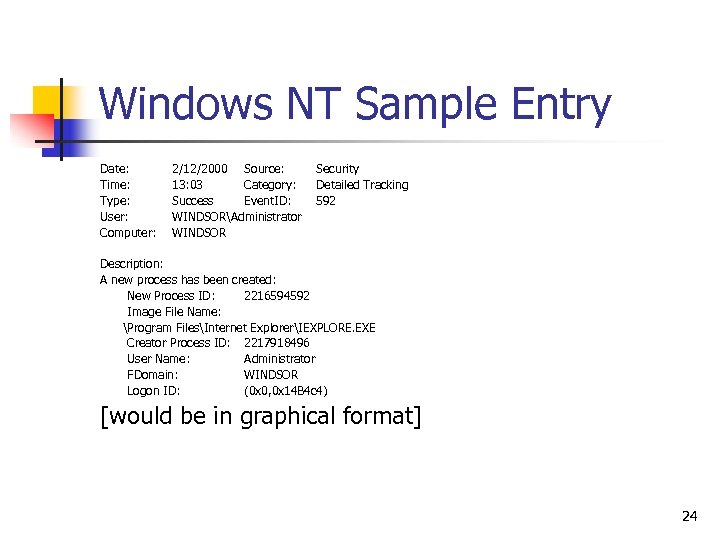 Windows NT Sample Entry Date: Time: Type: User: Computer: 2/12/2000 Source: 13: 03 Category: Success Event. ID: WINDSORAdministrator WINDSOR Security Detailed Tracking 592 Description: A new process has been created: New Process ID: 2216594592 Image File Name: Program FilesInternet ExplorerIEXPLORE. EXE Creator Process ID: 2217918496 User Name: Administrator FDomain: WINDSOR Logon ID: (0 x 0, 0 x 14 B 4 c 4) [would be in graphical format] 24
Windows NT Sample Entry Date: Time: Type: User: Computer: 2/12/2000 Source: 13: 03 Category: Success Event. ID: WINDSORAdministrator WINDSOR Security Detailed Tracking 592 Description: A new process has been created: New Process ID: 2216594592 Image File Name: Program FilesInternet ExplorerIEXPLORE. EXE Creator Process ID: 2217918496 User Name: Administrator FDomain: WINDSOR Logon ID: (0 x 0, 0 x 14 B 4 c 4) [would be in graphical format] 24
 Analyzer n Analyzes one or more logs n Logs may come from multiple systems, or a single system May lead to changes in logging May lead to a report of an event n Using swatch to find instances of telnet from tcpd logs: n n /telnet/&!/localhost/&!/*. site. com/ n Query set overlap control in databases n n If too much overlap between current query and past queries, do not answer Intrusion detection analysis engine (director) n Takes data from sensors and determines if an intrusion is occurring 25
Analyzer n Analyzes one or more logs n Logs may come from multiple systems, or a single system May lead to changes in logging May lead to a report of an event n Using swatch to find instances of telnet from tcpd logs: n n /telnet/&!/localhost/&!/*. site. com/ n Query set overlap control in databases n n If too much overlap between current query and past queries, do not answer Intrusion detection analysis engine (director) n Takes data from sensors and determines if an intrusion is occurring 25
 Notifier n n n Informs analyst, other entities of results of analysis May reconfigure logging and/or analysis on basis of results May take some action 26
Notifier n n n Informs analyst, other entities of results of analysis May reconfigure logging and/or analysis on basis of results May take some action 26
 Examples n Using swatch to notify of telnets /telnet/&!/localhost/&!/*. site. com/mail staff n Query set overlap control in databases n n Prevents response from being given if too much overlap occurs Three failed logins in a row disable user account n Notifier disables account, notifies sysadmin 27
Examples n Using swatch to notify of telnets /telnet/&!/localhost/&!/*. site. com/mail staff n Query set overlap control in databases n n Prevents response from being given if too much overlap occurs Three failed logins in a row disable user account n Notifier disables account, notifies sysadmin 27
 Designing an Audit System n n Essential component of security mechanisms Goals determine what is logged n n n Idea: auditors want to detect violations of policy, which provides a set of constraints that the set of possible actions must satisfy So, audit functions that may violate the constraints Constraint pi : action condition 28
Designing an Audit System n n Essential component of security mechanisms Goals determine what is logged n n n Idea: auditors want to detect violations of policy, which provides a set of constraints that the set of possible actions must satisfy So, audit functions that may violate the constraints Constraint pi : action condition 28
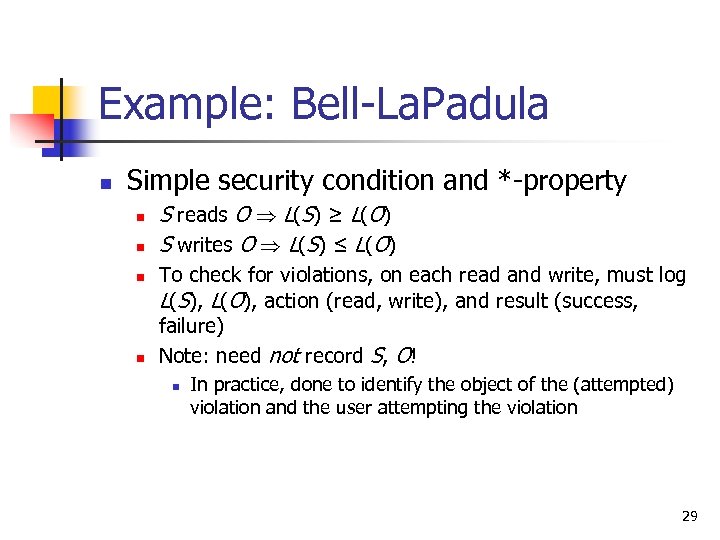 Example: Bell-La. Padula n Simple security condition and *-property n n S reads O L(S) ≥ L(O) S writes O L(S) ≤ L(O) To check for violations, on each read and write, must log L(S), L(O), action (read, write), and result (success, failure) Note: need not record S, O! n In practice, done to identify the object of the (attempted) violation and the user attempting the violation 29
Example: Bell-La. Padula n Simple security condition and *-property n n S reads O L(S) ≥ L(O) S writes O L(S) ≤ L(O) To check for violations, on each read and write, must log L(S), L(O), action (read, write), and result (success, failure) Note: need not record S, O! n In practice, done to identify the object of the (attempted) violation and the user attempting the violation 29
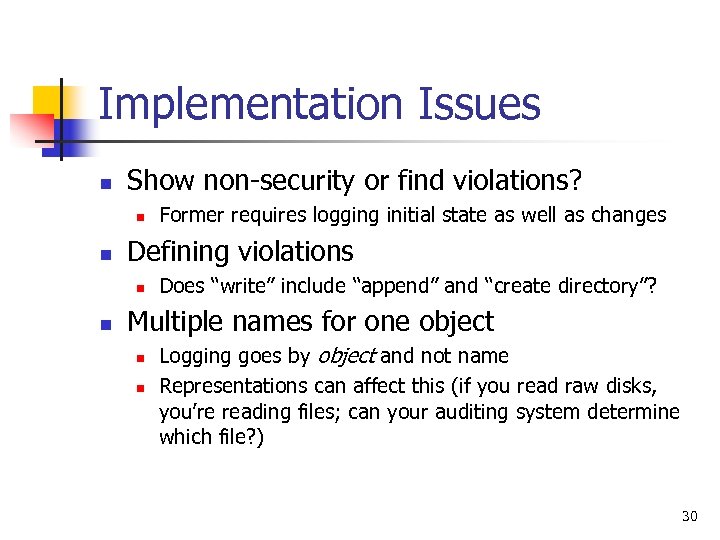 Implementation Issues n Show non-security or find violations? n n Defining violations n n Former requires logging initial state as well as changes Does “write” include “append” and “create directory”? Multiple names for one object n n Logging goes by object and not name Representations can affect this (if you read raw disks, you’re reading files; can your auditing system determine which file? ) 30
Implementation Issues n Show non-security or find violations? n n Defining violations n n Former requires logging initial state as well as changes Does “write” include “append” and “create directory”? Multiple names for one object n n Logging goes by object and not name Representations can affect this (if you read raw disks, you’re reading files; can your auditing system determine which file? ) 30
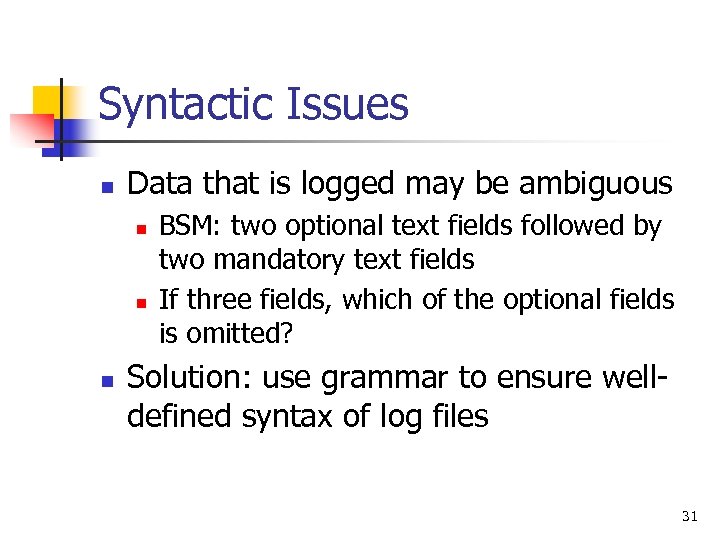 Syntactic Issues n Data that is logged may be ambiguous n n n BSM: two optional text fields followed by two mandatory text fields If three fields, which of the optional fields is omitted? Solution: use grammar to ensure welldefined syntax of log files 31
Syntactic Issues n Data that is logged may be ambiguous n n n BSM: two optional text fields followed by two mandatory text fields If three fields, which of the optional fields is omitted? Solution: use grammar to ensure welldefined syntax of log files 31
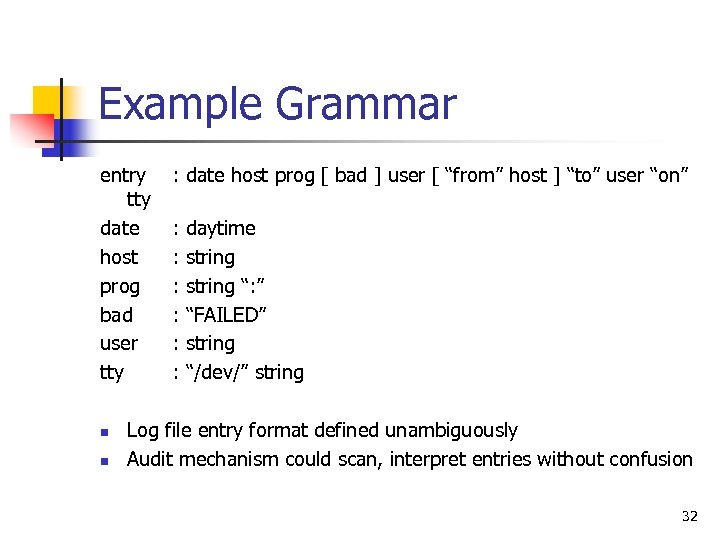 Example Grammar entry tty date host prog bad user tty n n : date host prog [ bad ] user [ “from” host ] “to” user “on” : : : daytime string “: ” “FAILED” string “/dev/” string Log file entry format defined unambiguously Audit mechanism could scan, interpret entries without confusion 32
Example Grammar entry tty date host prog bad user tty n n : date host prog [ bad ] user [ “from” host ] “to” user “on” : : : daytime string “: ” “FAILED” string “/dev/” string Log file entry format defined unambiguously Audit mechanism could scan, interpret entries without confusion 32
 More Syntactic Issues n Context n n n Unknown user uses anonymous ftp to retrieve file “/etc/passwd” Logged as such Problem: which /etc/passwd file? n n One in system /etc directory One in anonymous ftp directory /var/ftp/etc, and as ftp thinks /var/ftp is the root directory, /etc/passwd refers to /var/ftp/etc/passwd 33
More Syntactic Issues n Context n n n Unknown user uses anonymous ftp to retrieve file “/etc/passwd” Logged as such Problem: which /etc/passwd file? n n One in system /etc directory One in anonymous ftp directory /var/ftp/etc, and as ftp thinks /var/ftp is the root directory, /etc/passwd refers to /var/ftp/etc/passwd 33
 Log Sanitization n n U set of users, P policy defining set of information C(U) that U cannot see; log sanitized when all information in C(U) deleted from log Two types of P n C(U) can’t leave site n n People inside site are trusted and information not sensitive to them C(U) can’t leave system n n People inside site not trusted or (more commonly) information sensitive to them Don’t log this sensitive information 34
Log Sanitization n n U set of users, P policy defining set of information C(U) that U cannot see; log sanitized when all information in C(U) deleted from log Two types of P n C(U) can’t leave site n n People inside site are trusted and information not sensitive to them C(U) can’t leave system n n People inside site not trusted or (more commonly) information sensitive to them Don’t log this sensitive information 34
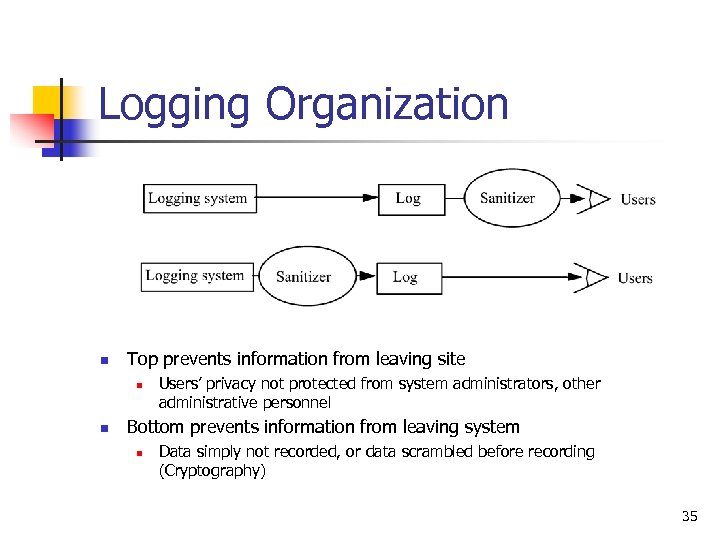 Logging Organization n Top prevents information from leaving site n n Users’ privacy not protected from system administrators, other administrative personnel Bottom prevents information from leaving system n Data simply not recorded, or data scrambled before recording (Cryptography) 35
Logging Organization n Top prevents information from leaving site n n Users’ privacy not protected from system administrators, other administrative personnel Bottom prevents information from leaving system n Data simply not recorded, or data scrambled before recording (Cryptography) 35
 Reconstruction n Anonymizing sanitizer cannot be undone n n Pseudonymizing sanitizer can be undone n n No way to recover data from this Original log can be reconstructed Importance n Suppose security analysis requires access to information that was sanitized? 36
Reconstruction n Anonymizing sanitizer cannot be undone n n Pseudonymizing sanitizer can be undone n n No way to recover data from this Original log can be reconstructed Importance n Suppose security analysis requires access to information that was sanitized? 36
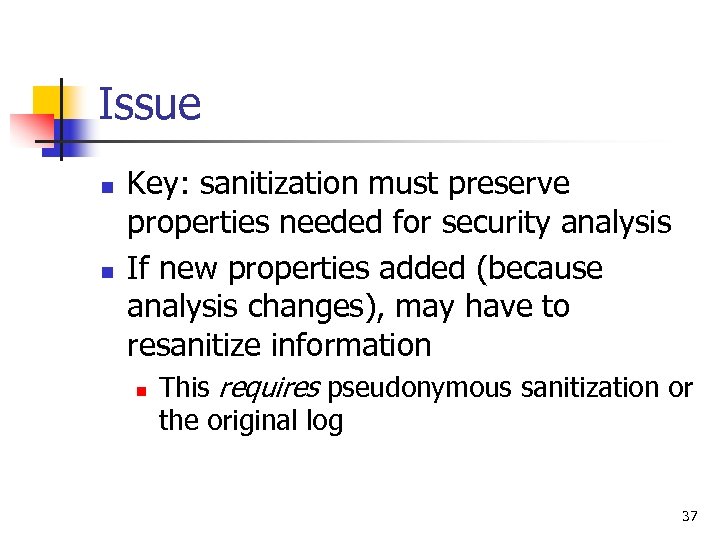 Issue n n Key: sanitization must preserve properties needed for security analysis If new properties added (because analysis changes), may have to resanitize information n This requires pseudonymous sanitization or the original log 37
Issue n n Key: sanitization must preserve properties needed for security analysis If new properties added (because analysis changes), may have to resanitize information n This requires pseudonymous sanitization or the original log 37
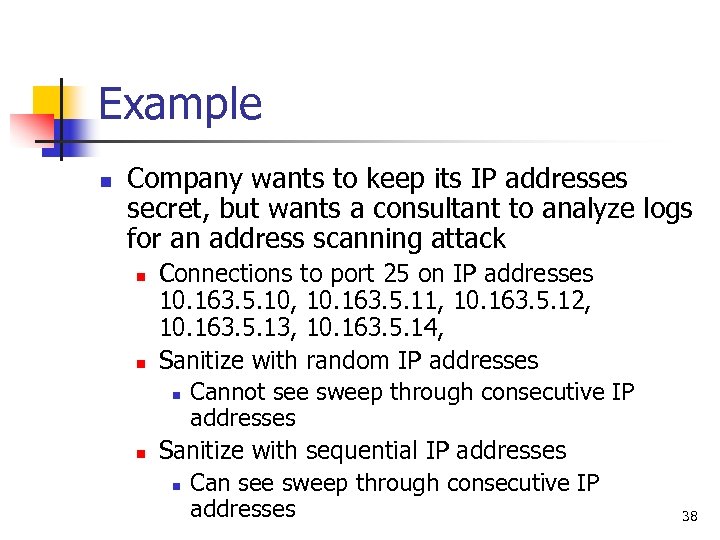 Example n Company wants to keep its IP addresses secret, but wants a consultant to analyze logs for an address scanning attack n n n Connections to port 25 on IP addresses 10. 163. 5. 10, 10. 163. 5. 11, 10. 163. 5. 12, 10. 163. 5. 13, 10. 163. 5. 14, Sanitize with random IP addresses n Cannot see sweep through consecutive IP addresses Sanitize with sequential IP addresses n Can see sweep through consecutive IP addresses 38
Example n Company wants to keep its IP addresses secret, but wants a consultant to analyze logs for an address scanning attack n n n Connections to port 25 on IP addresses 10. 163. 5. 10, 10. 163. 5. 11, 10. 163. 5. 12, 10. 163. 5. 13, 10. 163. 5. 14, Sanitize with random IP addresses n Cannot see sweep through consecutive IP addresses Sanitize with sequential IP addresses n Can see sweep through consecutive IP addresses 38
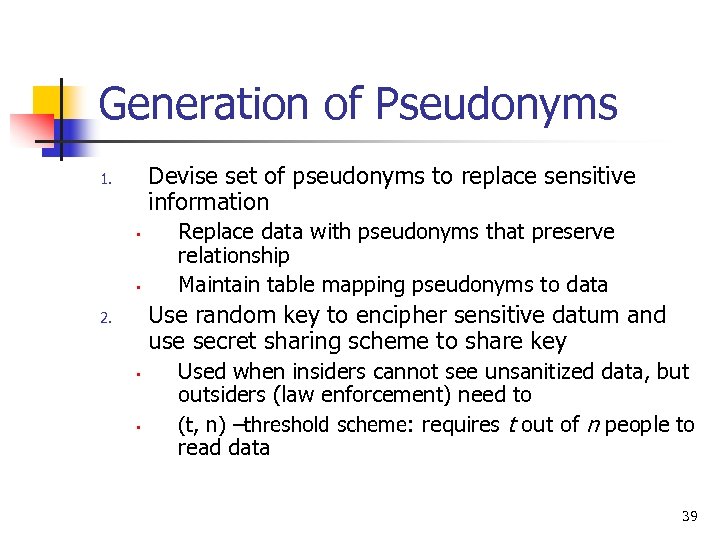 Generation of Pseudonyms Devise set of pseudonyms to replace sensitive information 1. • • Replace data with pseudonyms that preserve relationship Maintain table mapping pseudonyms to data Use random key to encipher sensitive datum and use secret sharing scheme to share key 2. • • Used when insiders cannot see unsanitized data, but outsiders (law enforcement) need to (t, n) –threshold scheme: requires t out of n people to read data 39
Generation of Pseudonyms Devise set of pseudonyms to replace sensitive information 1. • • Replace data with pseudonyms that preserve relationship Maintain table mapping pseudonyms to data Use random key to encipher sensitive datum and use secret sharing scheme to share key 2. • • Used when insiders cannot see unsanitized data, but outsiders (law enforcement) need to (t, n) –threshold scheme: requires t out of n people to read data 39
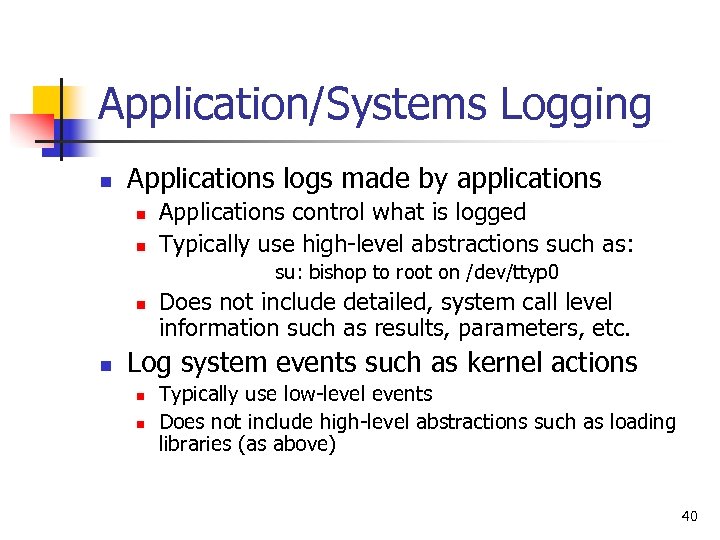 Application/Systems Logging n Applications logs made by applications n n Applications control what is logged Typically use high-level abstractions such as: su: bishop to root on /dev/ttyp 0 n n Does not include detailed, system call level information such as results, parameters, etc. Log system events such as kernel actions n n Typically use low-level events Does not include high-level abstractions such as loading libraries (as above) 40
Application/Systems Logging n Applications logs made by applications n n Applications control what is logged Typically use high-level abstractions such as: su: bishop to root on /dev/ttyp 0 n n Does not include detailed, system call level information such as results, parameters, etc. Log system events such as kernel actions n n Typically use low-level events Does not include high-level abstractions such as loading libraries (as above) 40
 Contrast n Differ in focus n n Application logging focuses on application events, like failure to supply proper password, and the broad operation (what was the reason for the access attempt? ) System logging focuses on system events, like memory mapping or file accesses, and the underlying causes (why did access fail? ) System logs usually much bigger than application logs Can do both, try to correlate them 41
Contrast n Differ in focus n n Application logging focuses on application events, like failure to supply proper password, and the broad operation (what was the reason for the access attempt? ) System logging focuses on system events, like memory mapping or file accesses, and the underlying causes (why did access fail? ) System logs usually much bigger than application logs Can do both, try to correlate them 41
 Design n A posteriori design n n Need to design auditing mechanism for system not built with security in mind Goal of auditing n Detect any violation of a stated policy n n Focus is on policy and actions designed to violate policy; specific actions may not be known Detect actions known to be part of an attempt to breach security n Focus on specific actions that have been determined to indicate attacks 42
Design n A posteriori design n n Need to design auditing mechanism for system not built with security in mind Goal of auditing n Detect any violation of a stated policy n n Focus is on policy and actions designed to violate policy; specific actions may not be known Detect actions known to be part of an attempt to breach security n Focus on specific actions that have been determined to indicate attacks 42
 Detect Violations of Known Policy n n Goal: does system enter a disallowed state? Two forms n State-based auditing n n Look at current state of system Transition-based auditing n Look at actions that transition system from one state to another 43
Detect Violations of Known Policy n n Goal: does system enter a disallowed state? Two forms n State-based auditing n n Look at current state of system Transition-based auditing n Look at actions that transition system from one state to another 43
 State-Based Auditing n Log information about state and determine if state is allowed n n n Assumption: you can get a snapshot of system state Snapshot needs to be consistent Non-distributed system needs to be quiescent 44
State-Based Auditing n Log information about state and determine if state is allowed n n n Assumption: you can get a snapshot of system state Snapshot needs to be consistent Non-distributed system needs to be quiescent 44
 Transition-Based Auditing n Log information about action, and examine current state and proposed transition to determine if new state would be disallowed n n Note: just analyzing the transition may not be enough; you may need the initial state Tend to use this when specific transitions always require analysis (for example, change of privilege) 45
Transition-Based Auditing n Log information about action, and examine current state and proposed transition to determine if new state would be disallowed n n Note: just analyzing the transition may not be enough; you may need the initial state Tend to use this when specific transitions always require analysis (for example, change of privilege) 45
 Watermarking 46
Watermarking 46
 Digital Watermarking n A digital pattern or signal is inserted into an image n n n Can serve as a digital signature Can identify the intended recipient (unique to each copy) Can identify document source (common to multiple copies) 47
Digital Watermarking n A digital pattern or signal is inserted into an image n n n Can serve as a digital signature Can identify the intended recipient (unique to each copy) Can identify document source (common to multiple copies) 47
 Watermarking n Watermarked image is transformed image n n n Original image remains intact, recognizable Persistent in viewing, printing and re-transmission and dissemination Contrast to fingerprinting and encryption n n In digital fingerprinting, original file remains but a new file is created that describes the original file (e. g. , checksum in Tripwire) Encryption transforms an image to an unrecognizable image 48
Watermarking n Watermarked image is transformed image n n n Original image remains intact, recognizable Persistent in viewing, printing and re-transmission and dissemination Contrast to fingerprinting and encryption n n In digital fingerprinting, original file remains but a new file is created that describes the original file (e. g. , checksum in Tripwire) Encryption transforms an image to an unrecognizable image 48
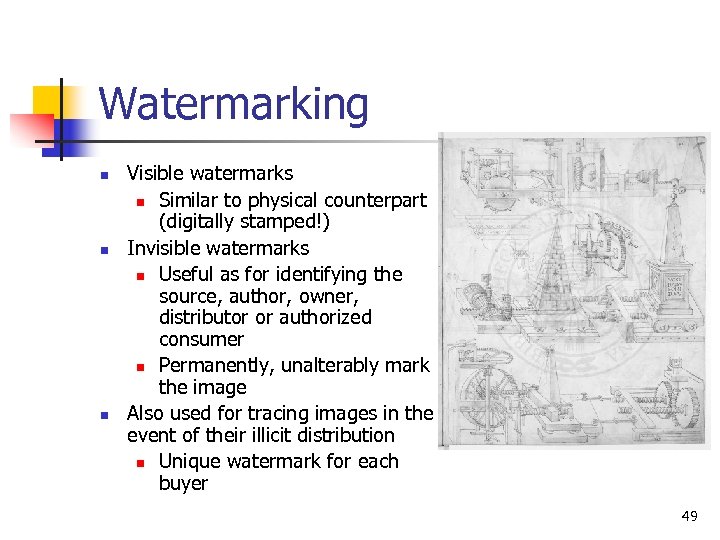 Watermarking n n n Visible watermarks n Similar to physical counterpart (digitally stamped!) Invisible watermarks n Useful as for identifying the source, author, owner, distributor or authorized consumer n Permanently, unalterably mark the image Also used for tracing images in the event of their illicit distribution n Unique watermark for each buyer 49
Watermarking n n n Visible watermarks n Similar to physical counterpart (digitally stamped!) Invisible watermarks n Useful as for identifying the source, author, owner, distributor or authorized consumer n Permanently, unalterably mark the image Also used for tracing images in the event of their illicit distribution n Unique watermark for each buyer 49
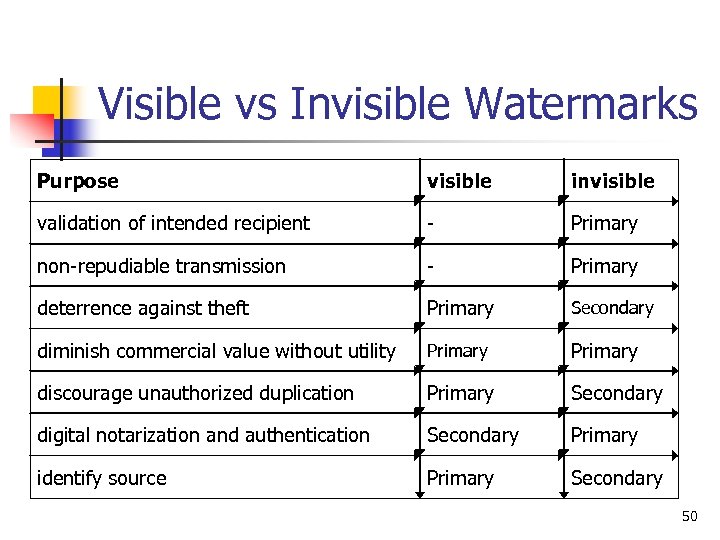 Visible vs Invisible Watermarks Purpose visible invisible validation of intended recipient - Primary non-repudiable transmission - Primary deterrence against theft Primary Secondary diminish commercial value without utility Primary discourage unauthorized duplication Primary Secondary digital notarization and authentication Secondary Primary identify source Primary Secondary 50
Visible vs Invisible Watermarks Purpose visible invisible validation of intended recipient - Primary non-repudiable transmission - Primary deterrence against theft Primary Secondary diminish commercial value without utility Primary discourage unauthorized duplication Primary Secondary digital notarization and authentication Secondary Primary identify source Primary Secondary 50
 Requirements of Watermarks n To protect intellectual property n n Watermark must be difficult or impossible to remove, at least without visibly degrading the original image Watermark must survive image modifications An invisible watermark should be imperceptible so as not to affect the experience of viewing Watermarks should be easily detectable by the proper authority 51
Requirements of Watermarks n To protect intellectual property n n Watermark must be difficult or impossible to remove, at least without visibly degrading the original image Watermark must survive image modifications An invisible watermark should be imperceptible so as not to affect the experience of viewing Watermarks should be easily detectable by the proper authority 51
 Watermarking techniques For image n Spatial domain watermarking n n n - n Simplest: flip the lowest order bit of chosen pixels Superimpose a watermark Color separation – watermark in only one color band Picture cropping can be used to eliminate some spatial watermark Frequency domain watermarking n n Use Fast Fourier Transform – alter the values of chosen frequencies Watermarks will be dispersed spatially (cropping or spatial technique will not defeat it) 52
Watermarking techniques For image n Spatial domain watermarking n n n - n Simplest: flip the lowest order bit of chosen pixels Superimpose a watermark Color separation – watermark in only one color band Picture cropping can be used to eliminate some spatial watermark Frequency domain watermarking n n Use Fast Fourier Transform – alter the values of chosen frequencies Watermarks will be dispersed spatially (cropping or spatial technique will not defeat it) 52
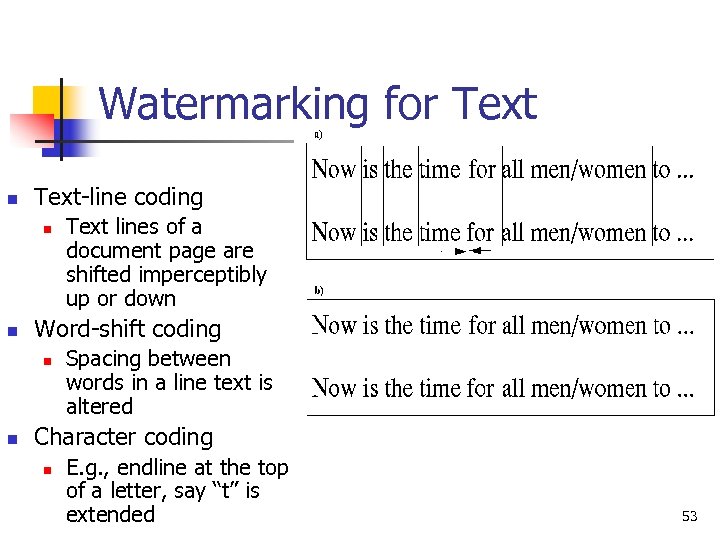 Watermarking for Text n Text-line coding n n Word-shift coding n n Text lines of a document page are shifted imperceptibly up or down Spacing between words in a line text is altered Character coding n E. g. , endline at the top of a letter, say “t” is extended 53
Watermarking for Text n Text-line coding n n Word-shift coding n n Text lines of a document page are shifted imperceptibly up or down Spacing between words in a line text is altered Character coding n E. g. , endline at the top of a letter, say “t” is extended 53
 Steganography n n n Art of hiding information in the midst of irrelevant data This is NOT cryptography Useful to hide the existence of secret communication 54
Steganography n n n Art of hiding information in the midst of irrelevant data This is NOT cryptography Useful to hide the existence of secret communication 54
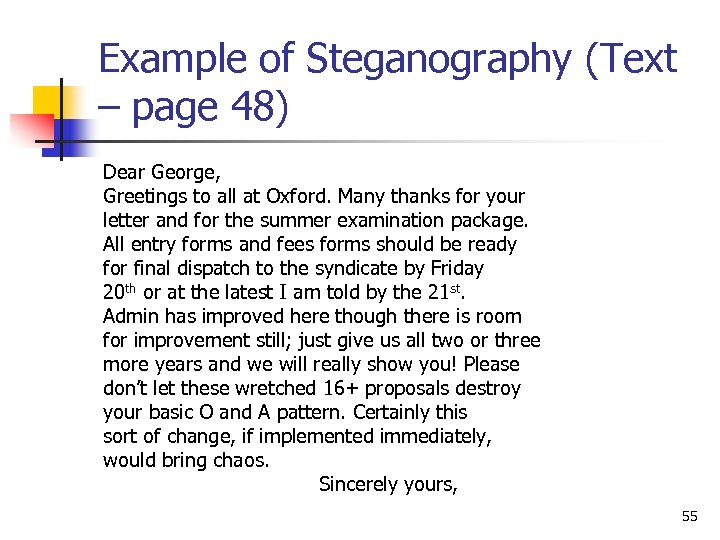 Example of Steganography (Text – page 48) Dear George, Greetings to all at Oxford. Many thanks for your letter and for the summer examination package. All entry forms and fees forms should be ready for final dispatch to the syndicate by Friday 20 th or at the latest I am told by the 21 st. Admin has improved here though there is room for improvement still; just give us all two or three more years and we will really show you! Please don’t let these wretched 16+ proposals destroy your basic O and A pattern. Certainly this sort of change, if implemented immediately, would bring chaos. Sincerely yours, 55
Example of Steganography (Text – page 48) Dear George, Greetings to all at Oxford. Many thanks for your letter and for the summer examination package. All entry forms and fees forms should be ready for final dispatch to the syndicate by Friday 20 th or at the latest I am told by the 21 st. Admin has improved here though there is room for improvement still; just give us all two or three more years and we will really show you! Please don’t let these wretched 16+ proposals destroy your basic O and A pattern. Certainly this sort of change, if implemented immediately, would bring chaos. Sincerely yours, 55


