e54715e19ca6d0f2c67be473e5b0ca74.ppt
- Количество слайдов: 23
IP Spoofing Bao Ho Toan. Tai Vu CS 265 - Security Engineering Spring 2003 San Jose State University IP Spoofing, CS 265 1
Presentation Outline Introduction, Background n Attacks with IP Spoofing n Counter Measures n Summary n IP Spoofing, CS 265 2
IP Spoofing n IP Spoofing is a technique used to gain unauthorized access to computers. – IP: Internet Protocol – Spoofing: using somebdody else’s information n Exploits the trust relationships n Intruder sends messages to a computer with an IP address of a trusted host. IP Spoofing, CS 265 3
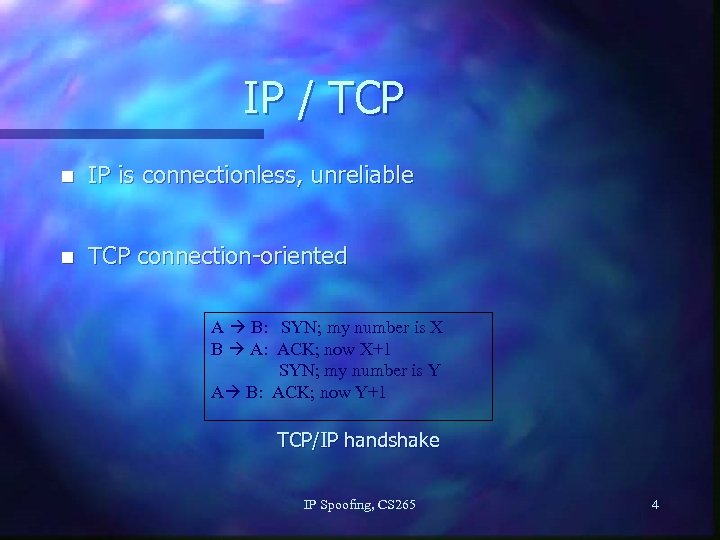
IP / TCP n IP is connectionless, unreliable n TCP connection-oriented A B: SYN; my number is X B A: ACK; now X+1 SYN; my number is Y A B: ACK; now Y+1 TCP/IP handshake IP Spoofing, CS 265 4
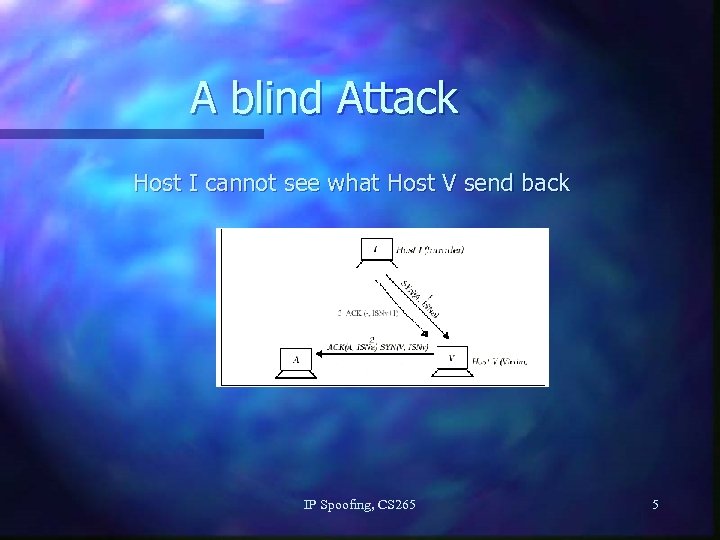
A blind Attack Host I cannot see what Host V send back IP Spoofing, CS 265 5
IP Spoofing Steps n n n Selecting a target host (the victim) Identify a host that the target “trust” Disable the trusted host, sampled the target’s TCP sequence The trusted host is impersonated and the ISN forged. Connection attempt to a service that only requires address-based authentication. If successfully connected, executes a simple command to leave a backdoor. IP Spoofing, CS 265 6
IP Spoofing Attacks n Man in the middle n Routing n Flooding / Smurfing IP Spoofing, CS 265 7
Attacks Man - in - the - middle: Packet sniffs on link between the two endpoints, and therefore can pretend to be one end of the connection. IP Spoofing, CS 265 8
Attacks n Routing re-direct: redirects routing information from the original host to the attacker’s host. n Source routing: The attacker redirects individual packets by the hacker’s host. IP Spoofing, CS 265 9
Attacks n Flooding: SYN flood fills up the receive queue from random source addresses. n Smurfing: ICMP packet spoofed to originate from the victim, destined for the broadcast address, causing all hosts on the network to respond to the victim at once. IP Spoofing, CS 265 10
IP-Spoofing Facts n IP protocol is inherently weak n Makes no assumption about sender/recipient n Nodes on path do not check sender’s identity n There is no way to completely eliminate IP spoofing n Can only reduce the possibility of attack IP Spoofing, CS 265 11
IP-Spoofing Counter-measures n No insecure authenticated services n Disable commands like ping n Use encryption n Strengthen TCP/IP protocol n Firewall n IP traceback IP Spoofing, CS 265 12
No insecure authenticated services n n n r* services are hostname-based or IP-based Other more secure alternatives, i. e. , ssh Remove binary files Disable in inet, xinet Clean up. rhost files and /etc/host. equiv No application with hostname/IP-based authentication, if possible IP Spoofing, CS 265 13
Disable ping command n ping command has rare use n Can be used to trigger a DOS attack by flooding the victim with ICMP packets n This attack does not crash victim, but consume network bandwidth and system resources n Victim fails to provide other services, and halts if runs out of memory IP Spoofing, CS 265 14
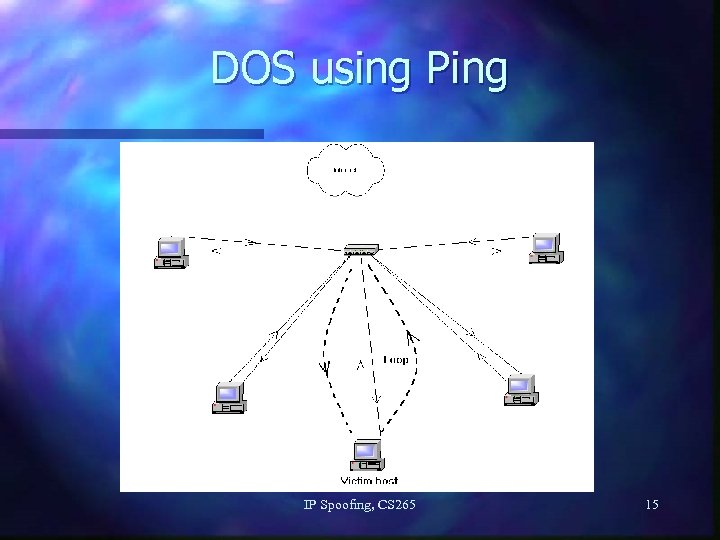
DOS using Ping IP Spoofing, CS 265 15
Use Encryption n Encrypt traffic, especially TCP/IP packets and Initial Sequence Numbers n Kerberos is free, and is built-in with OS n Limit session time n Digital signature can be used to identify the sender of the TCP/IP packet. IP Spoofing, CS 265 16
Strengthen TCP/IP protocol n n n Use good random number generators to generate ISN Shorten time-out value in TCP/IP request Increase request queue size Cannot completely prevent TCP/IP half-openconnection attack Can only buy more time, in hope that the attack will be noticed. IP Spoofing, CS 265 17
Firewall n Limit traffic to services that are offered n Control access from within the network n Free software: ipchains, iptables n Commercial firewall software n Packet filters: router with firewall built-in n Multiple layer of firewall IP Spoofing, CS 265 18
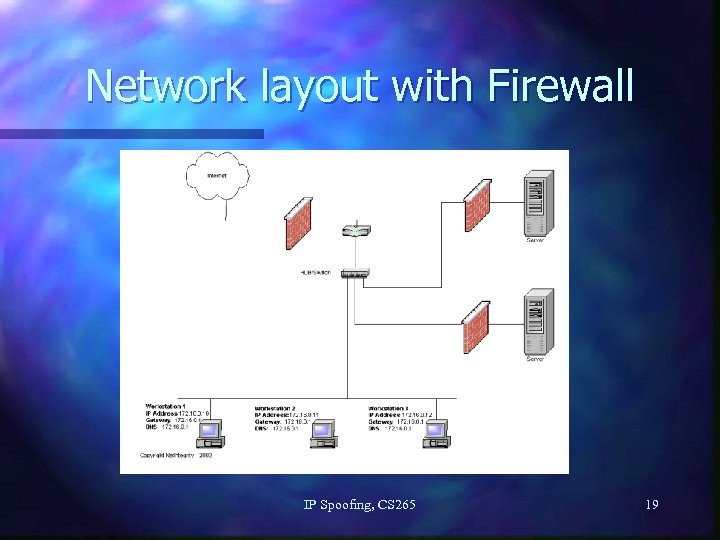
Network layout with Firewall IP Spoofing, CS 265 19
IP Trace-back n To trace back as close to the attacker’s location as possible n Limited in reliability and efficiency n Require cooperation of many other network operators along the routing path n Generally does not receive much attention from network operators IP Spoofing, CS 265 20
Summary/Conclusion n IP spoofing attacks is unavoidable. n Understanding how and why spoofing attacks are used, combined with a few simple prevention methods, can help protect your network from these malicious cloaking and cracking techniques. IP Spoofing, CS 265 21
References n n n IP-spoofing Demystified (Trust-Relationship Exploitation), Phrack Magazine Review, Vol. 7, No. 48, pp. 4814, www. networkcommand. com/docs/ipspoof. txt Security Enginerring : A Guide to Building Dependable Distributed Systems , Ross Anderson, pp. 371 Introduction to IP Spoofing, Victor Velasco, November 21, 2000, www. sans. org/rr/threats/intro_spoofing. php A Large-scale Distributed Intrusion Detection Framework Based on Attack Strategy Analysis, Ming-Yuh Huang, Thomas M. Wicks, Applied Research and Technology , The Boeing Company Internet Vulnerabilities Related to TCP/IP and T/TCP, ACM SIGCOMM, Computer Communication Review IP Spoofing, www. linuxgazette. com/issue 63/sharma. html Distributed System: Concepts and Design , Chapter 7, by Coulouris, Dollimore, and Kindberg Free. BSD IP Spoofing, www. securityfocus. com/advisories/2703 IP Spoofing Attacks and Hijacked Terminal Connections, www. cert. org/advisories/CA-1995 -01. html Network support for IP trace-back, IEEE/ACM Transactions on Networking , Vol. 9, No. 3, June 2001 An Algebraic Approach to IP Trace-back, ACM Transactions on Information and System Security , Vol. 5, No. 2, May 2002 Web Spoofing. An Internet Con Game, http: //bau 2. uibk. ac. at/matic/spoofing. htm IP Spoofing, CS 265 22
Questions / Answers IP Spoofing, CS 265 23
e54715e19ca6d0f2c67be473e5b0ca74.ppt